In most web stacks, authentication libraries are treated like plumbing. Teams spend time on controllers, business logic, observability, and deployment pipelines, while the code that decides whether a user is trusted often sits quietly in a shared dependency, rarely revisited unless a migration forces the issue. CVE-2026-29000 is a reminder that this is exactly backwards. When identity-boundary code fails, it does not fail softly. It collapses the trust model underneath the application. (NVD)
CVE-2026-29000 is a critical authentication bypass in pac4j-jwt, specifically in JwtAuthenticator, when processing encrypted JWTs. The published descriptions from NVD and GitHub Advisory are consistent on the core point: affected versions allow a remote attacker who possesses the server’s RSA public key to craft a JWE-wrapped PlainJWT with arbitrary subject and role claims, bypass signature verification, and authenticate as any user, including administrators. The project’s own advisory does not publish exploit details, but it clearly instructs users to upgrade to fixed versions immediately. (NVD)
The affected version ranges published by GitHub Advisory are < 4.5.9, >= 5.0.0-RC1 and < 5.7.9, and >= 6.0.4.1 and < 6.3.3. The corresponding patched versions are 4.5.9, 5.7.9, and 6.3.3. NVD mirrors the same remediation boundary, and downstream guidance from Arctic Wolf and CISecurity repeats the same fix line. (GitHub)
What makes this issue unusually important is not only its severity score. It is the failure mode. This is not a denial-of-service bug, a leak of low-value metadata, or a narrow edge case requiring improbable conditions. It is an identity forgery path in a widely used Java authentication component. The attacker does not need a password, does not need a signing secret, and does not need privileged foothold inside the environment. The public writeups indicate that knowledge of the server’s RSA public key is sufficient under the vulnerable configuration. In asymmetric cryptography, the public key is often meant to be distributed. That makes the exploit precondition operationally realistic rather than exotic. (NVD)
The pac4j documentation itself says that JwtAuthenticator supports plain text, signed, and encrypted JWT tokens. That flexibility is useful, but it is also the backdrop for the bug. The problem is not that the standards are broken. The problem is that standards-compliant token forms were composed in a way that created an unsafe trust transition inside the application. The most interesting technical lesson in CVE-2026-29000 is that cryptographic components can each behave correctly while the overall authentication pipeline still becomes insecure. (pac4j.org)
What CVE-2026-29000 Actually Is
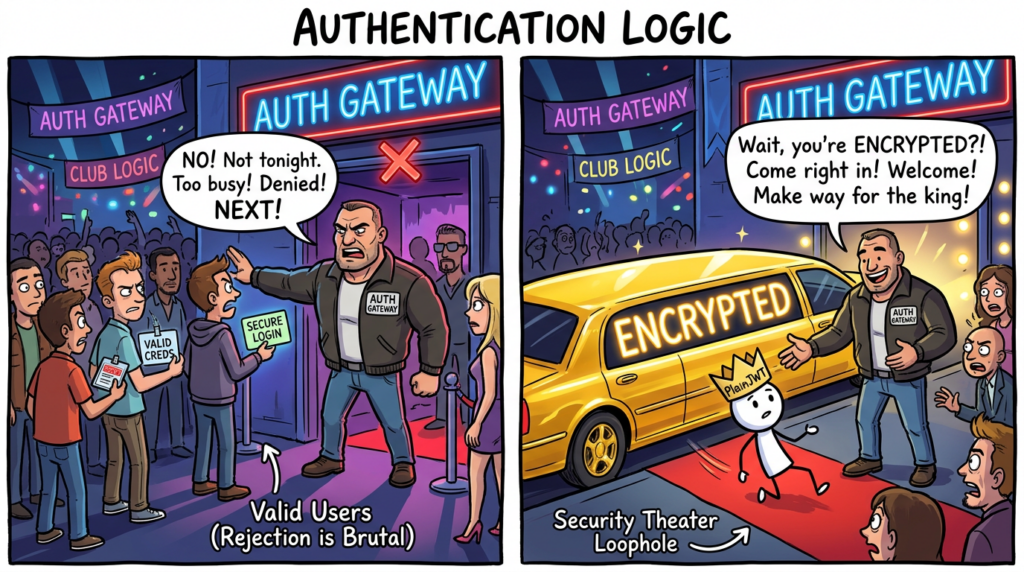
The official descriptions are concise. pac4j-jwt contains an authentication bypass in JwtAuthenticator when it processes encrypted JWTs. A malicious actor can supply an encrypted token whose inner payload is not a properly signed JWT but a PlainJWT, carrying attacker-controlled claims. Because of a logic flaw in how the decrypted content is handled, the signature verification path is skipped and the claims are still used to build an authenticated user profile. That is why this is not just a token parsing bug. It is a full trust-boundary failure. (NVD)
Arctic Wolf’s summary captures the execution path clearly: when JwtAuthenticator decrypts a JWE, it attempts to parse the inner token as a SignedJWT. If the inner token is actually a PlainJWT, the SignedJWT object is null, and the verification path is skipped due to a logic error. The code then proceeds to create a user profile from unverified claims. That sequence is why the impact is so severe. The application is not merely mishandling metadata. It is accepting identity assertions that were never cryptographically authenticated. (Arctic Wolf)
CodeAnt’s public research reaches the same conclusion from the code path: if toSignedJWT() returns null, the signature verification block does not execute, yet the token’s claims still reach profile creation. Their writeup frames the bug in practical terms: a gate that should protect the authentication system depends on a null check that can be triggered simply by providing an unsigned inner token. (codeant.ai)
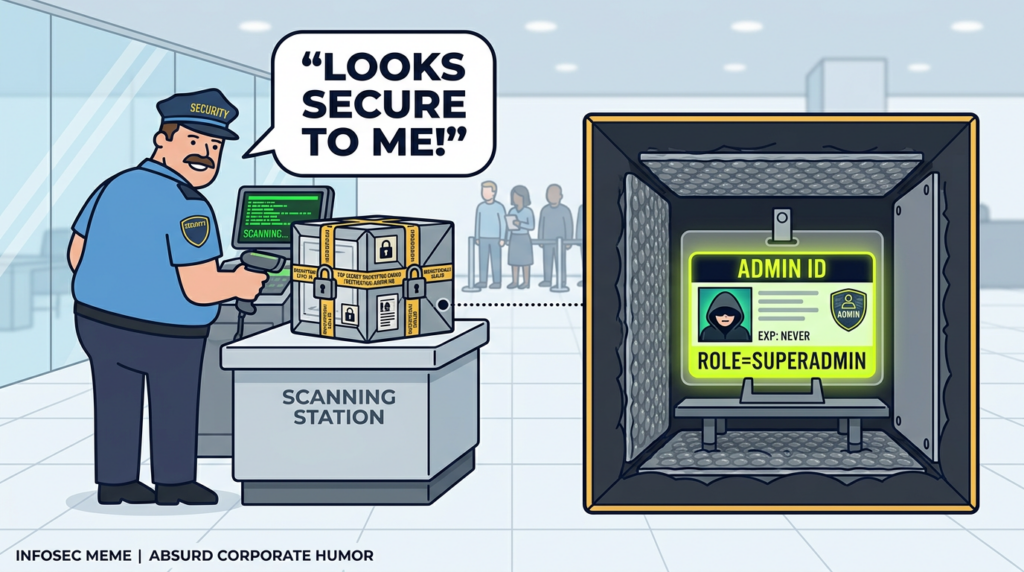
This matters because teams often think of encryption as “more secure than signing,” or at least as strong evidence that the content is protected. But encryption answers a different question. It addresses confidentiality. Signature validation addresses origin and integrity. A system that decrypts content successfully has learned that the content was recoverable with its decryption key. It has not learned that the content came from a trusted issuer. CVE-2026-29000 is a textbook example of what happens when those two ideas blur inside implementation logic. (codeant.ai)
Why JWE Did Not Save You
To understand the flaw, it helps to strip JWT terminology down to first principles.
A JWT is a compact claims format. RFC 7519 explicitly says the claims can serve as the payload of a JWS structure or as the plaintext of a JWE structure. In other words, JWT is the claims container, while JWS and JWE are protection mechanisms applied around it. The standards do not say that encryption alone is always sufficient to prove issuer authenticity. They distinguish between confidentiality and integrity. (RFC Editor)
RFC 7519 also explicitly permits unsecured JWTs. Section 6 states that an Unsecured JWT may be created without a signature or encryption, using alg: none with an empty signature value. That is not a vulnerability by itself. It is part of the specification for narrowly defined cases where the JWT is protected by some other means. But this design choice means implementers cannot assume that every parsed JWT object inherently carries a signature. Some JWTs are valid structures that are not signed at all. (RFC Editor)
That detail is where CVE-2026-29000 becomes easier to reason about. According to CodeAnt’s technical explanation, the vulnerable flow attempts to convert the decrypted content into a SignedJWT. If the inner token is actually a PlainJWT, the Nimbus library behaves as designed and returns null. The library is not malfunctioning. The parser is telling the caller, correctly, that the payload is not a signed JWT. The real mistake is what the caller does next. Instead of rejecting the token as unacceptable for that trust boundary, the pac4j authentication path keeps going. (codeant.ai)
RFC 8725, the JWT Best Current Practices document, exists precisely because these implementation traps recur in real systems. It warns that attacker-controlled algorithm indicators and insufficient signature validation have led to repeated attacks, including alg: none acceptance and RS-to-HS confusion. It also states that libraries must let callers specify supported algorithms and must not silently use others. More broadly, it recommends explicit typing and mutually exclusive validation rules for different kinds of JWTs so that one token form cannot be confused for another. Those recommendations map cleanly onto the class of failure seen in CVE-2026-29000. (RFC Editor)
Put more plainly, JWE did not save the vulnerable application because the application treated successful decryption as a substitute for successful signature validation. Once that happens, encryption becomes a false sense of trust. The outer wrapper can be perfectly well-formed and the cryptographic operations can all succeed, while the application still accepts attacker-authored claims as if they were issuer-authored claims. (Arctic Wolf)
The Root Cause, A Composition Failure More Than a Crypto Failure
The most useful way to think about CVE-2026-29000 is not “JWTs are bad” or “JWE is unsafe.” The better lesson is that composition bugs are often more dangerous than primitive failures.
CodeAnt’s code-level discussion emphasizes that none of the individual pieces are obviously broken. The JWT specification permits unsigned tokens. Nimbus correctly returns null when asked to parse a non-signed payload as a SignedJWT. The pac4j code contains a null check that appears reasonable in isolation. The vulnerability emerges only when those individually sensible pieces are connected with the wrong assumption: that the inner content of a decrypted token will always be the kind of object the next stage expects. (codeant.ai)
That kind of bug is common in mature systems because complex authentication stacks are built incrementally. A team adds encrypted JWT support to satisfy confidentiality requirements. Another layer adds profile construction from token claims. Somewhere in the middle, the code assumes that decryption yields content already appropriate for trust elevation. Nobody writes a line that says “skip authentication.” Instead, the implementation silently creates a path where authentication evaporates. (codeant.ai)
This is why the flaw deserves attention even from teams that do not use pac4j. The broader pattern applies anywhere a system supports multiple JOSE object types, multiple validation modes, nested tokens, or flexible parsing paths. If one stage says “this payload is parseable” and the next stage hears “this payload is trustworthy,” the trust model can break without any cryptographic primitive actually failing. (RFC Editor)
In that sense, CVE-2026-29000 belongs in the same family as other JWT verification failures that turned on confusion rather than raw cryptographic weakness. The mechanics differ, but the theme repeats: token metadata, token type, or algorithm class is interpreted too loosely, and the application ends up treating attacker-controlled material as authenticated identity. (NVD)
A Simplified Execution Path
The vulnerable logic can be explained without reproducing exploit code.
The intended flow looks like this:
receive token
decrypt outer JWE
parse inner token as signed JWT
verify signature with expected algorithm and key
validate issuer, audience, expiry, subject, token type
build authenticated profile
authorize request
The vulnerable flow, based on public technical descriptions, effectively looks like this:
receive token
decrypt outer JWE
attempt to parse inner token as SignedJWT
inner token is PlainJWT, parse result is null
signature verification block is skipped
claims are still used to create profile
authorize request as forged identity
That is the entire problem in one screen. The application still performs work that feels “security-relevant.” It decrypts. It parses. It reaches an authentication object. But the one step that proves who authored the claims no longer gates profile creation. (Arctic Wolf)
Arctic Wolf’s wording is particularly useful here because it avoids the trap of talking about “bad encryption.” Their writeup says the flaw arises from improper verification of cryptographic signatures in the JwtAuthenticator component when processing encrypted JWTs. That phrasing is accurate. The danger is in the verification path, not in the availability of encryption itself. (Arctic Wolf)
Who Is Actually at Risk
Not every Java service that mentions JWT is exposed to CVE-2026-29000, and being precise matters.
The published descriptions focus on pac4j-jwt and JwtAuthenticator, not pac4j as a whole. GitHub Advisory and the pac4j project advisory scope the issue to the pac4j-jwt module and its vulnerable version lines. Public technical writeups further note that the risky deployments are those using RSA-based JWE together with JwtAuthenticator configured for both encryption and signature handling. If your service uses pac4j but does not use pac4j-jwt, or uses only signed tokens without the affected JWE path, your exposure may be different. That said, the safest assumption for production systems is to inventory first and upgrade fast, because dependency graphs and inherited defaults are often misunderstood in large Java estates. (GitHub)
A realistic exposure checklist looks like this:
| Question | Why it matters |
|---|---|
Do you depend on org.pac4j:pac4j-jwt | This is the directly affected package. |
| Are you on a vulnerable version line | Versions below 4.5.9, 5.7.9, or 6.3.3 are affected in the published advisories. |
Do you use JwtAuthenticator | The vulnerability is described in that component. |
| Do you accept encrypted JWTs, not just signed JWTs | The vulnerable flow is triggered while processing JWE. |
| Do you rely on RSA public key distribution or JWKS exposure | Public-key availability makes the exploit precondition realistic. |
| Do token claims map directly into user profile or role decisions | That is what turns verification failure into full impersonation. |
The exploitability picture is why the CNA-rated CVSS is 10.0 and why GitHub marks the advisory Critical. According to the published vectors, the issue is network-reachable, low complexity, requires no privileges, and no user interaction. Even if the availability impact is lower than the confidentiality and integrity impact, a remote unauthenticated identity forgery path is enough to treat this as an emergency patch on any exposed or business-critical service. (NVD)
At the time Arctic Wolf published its bulletin, it said it had not observed active exploitation in the wild, though it also noted that a public proof of concept and technical writeup existed. That distinction matters operationally. “No confirmed exploitation yet” is not reassuring once the exploit path is public and the preconditions are simple. For internet-facing authentication services, the right mindset is not to wait for a botnet trendline. It is to assume rapid weaponization once scanners and opportunistic actors encode the version logic. (Arctic Wolf)

Why This Bug Feels Familiar to JWT Veterans
CVE-2026-29000 is new, but the shape of the mistake is old.
One of the best-known JWT verification failures is CVE-2015-9235 in the Node.js jsonwebtoken package. NVD describes it as a verification bypass where a token expected to be verified with an asymmetric algorithm could instead be supplied under a symmetric algorithm family, enabling algorithm confusion. The lesson from that era was that applications must not let attacker-controlled token headers dictate verification behavior in ways that cross trust models. (NVD)
A more recent example is CVE-2024-54150 in cjwt, where NVD describes algorithm confusion caused by failure to properly distinguish HMAC-signed tokens from RS, EC, or PS signed tokens during verification. Again, the specific bug differs from pac4j, but the pattern is recognizable: the token is structurally acceptable, the verification logic takes the wrong path, and the application ends up treating the wrong cryptographic state as trustworthy. (NVD)
Another useful comparison is CVE-2026-28802 in Authlib. NVD says versions 1.6.5 through before 1.6.7 could allow a malicious JWT containing alg: none and an empty signature to pass signature verification expectations. That is not the same implementation path as CVE-2026-29000, but it reinforces the point that “none,” unsigned tokens, and weakly bounded validation rules remain an active source of security failures even in modern libraries. (NVD)
RFC 8725 effectively anticipated this whole family of problems. It warns that changing the algorithm to none or confusing RSA with HMAC verification has already led to attacks, and it recommends explicit typing plus mutually exclusive validation rules for different JWT kinds. CVE-2026-29000 is a fresh example of why those recommendations should not be treated as academic reading. They are practical guardrails for keeping multi-form token support from becoming token confusion. (RFC Editor)
What Security Teams Should Do First
If you run pac4j-jwt in production, the first move is the boring one: upgrade.
The pac4j project says to move to 4.5.9, 5.7.9, or 6.3.3 depending on your branch. GitHub Advisory and NVD align with that fix guidance. There is no published evidence in the official project advisory that a safer configuration tweak can substitute for upgrading in all cases, so patching should be considered the primary fix rather than one option among many. (pac4j.org)
For Maven-based environments, the dependency check should be explicit:
<dependency>
<groupId>org.pac4j</groupId>
<artifactId>pac4j-jwt</artifactId>
<version>6.3.3</version>
</dependency>
If you are pinned to older major lines because of compatibility constraints, target the fixed patch version in that line instead:
<!-- 5.x line -->
<dependency>
<groupId>org.pac4j</groupId>
<artifactId>pac4j-jwt</artifactId>
<version>5.7.9</version>
</dependency>
<!-- 4.x line -->
<dependency>
<groupId>org.pac4j</groupId>
<artifactId>pac4j-jwt</artifactId>
<version>4.5.9</version>
</dependency>
If your organization uses SCA or SBOM tooling, treat this as a forced validation moment. Many teams know their top-level dependencies but not the transitives embedded by framework integrations. GitHub Advisory identifies the affected Maven coordinate clearly, which makes the package easy to query across artifact registries and build manifests. (GitHub)
The second move is exposure scoping. Identify every service that both imports pac4j-jwt and uses JwtAuthenticator in token-auth paths. Then determine whether those services process encrypted JWTs rather than only signed JWTs. The reason this matters is that CVE-2026-29000 is not a generic JWT decoder flaw. It is tied to the encrypted-token path that can carry a PlainJWT internally. (Arctic Wolf)
The third move is operational containment. If any affected service is internet-facing and sits on a privileged identity path, reduce exposure while patching. CISecurity frames the issue as a remote authentication bypass that can authenticate as any user including administrators. Even if patch rollout takes hours instead of minutes, shrinking attack surface during that interval is worthwhile. That can mean allowlisting, temporarily gating sensitive APIs behind internal networks or trusted proxies, or disabling the affected auth path if the service has a safe fallback. (CIS)
How to Audit Your Codebase for the Dangerous Pattern
The package version is the first signal, but not the last one. You also want to know whether your own code or framework configuration relies on the vulnerable path in a way that makes forged claims immediately useful.
A practical source search should start with these strings:
org.pac4j.jwt
JwtAuthenticator
EncryptionConfiguration
SignatureConfiguration
TokenCredentials
JWE
JWKS
RSAKey
The question is not just “do we use pac4j-jwt.” The question is “where do decrypted token claims become profile attributes, authorities, or role mappings.” CVE-2026-29000 is devastating only because the vulnerable flow converts unverified claims into authenticated identity. If your application maps role, groups, scope, is_admin, or tenant identifiers straight from token claims into authorization decisions, the risk compounds. (NVD)
A basic Semgrep starter rule for inventorying risky code paths can look like this:
rules:
- id: pac4j-jwt-authenticator-usage
message: Review pac4j JwtAuthenticator usage for CVE-2026-29000 exposure
severity: WARNING
languages: [java]
patterns:
- pattern-either:
- pattern: new JwtAuthenticator(...)
- pattern: JwtAuthenticator $A = ...
- pattern: import org.pac4j.jwt.credentials.authenticator.JwtAuthenticator;
That rule will not prove exploitability, but it will quickly surface the services that deserve deeper manual review.
You can also look for configuration shapes that combine both encryption and signature concepts in the same token-validation stack:
rules:
- id: pac4j-jwt-encryption-signature-config
message: Review combined encryption and signature configuration with JwtAuthenticator
severity: WARNING
languages: [java]
patterns:
- pattern-inside: |
...
- pattern-either:
- pattern: new EncryptionConfiguration(...)
- pattern: new SignatureConfiguration(...)
For dependency inventory in CI, a blunt shell check often catches enough to start:
grep -R "org.pac4j.*pac4j-jwt" . \\
--include="pom.xml" \\
--include="build.gradle" \\
--include="gradle.lockfile"
For containerized services, do not stop at source. Query built artifacts and SBOMs. Teams frequently patch source and forget that old images remain deployed in a staging cluster, an internal batch service, or a shadow environment used for customer demos.
What Safe Validation Should Look Like
The correct lesson from CVE-2026-29000 is not “ban JWT.” It is to make token validation fail closed and type-aware.
A safe validator should explicitly decide which token forms are acceptable for a given endpoint. If an endpoint expects a signed JWT, then a decrypted token whose inner content is not a SignedJWT should be rejected immediately. It should not proceed to profile creation, claim extraction, or any downstream authorization logic. That sounds obvious after the fact, but CVE-2026-29000 exists because authentication code frequently drifts into permissive parsing.
A defensive pseudocode pattern looks like this:
Token outer = parseIncomingToken(raw);
DecryptedPayload payload = decryptIfExpected(outer);
if (!payload.isSignedJwt()) {
throw new AuthenticationException("Expected signed JWT inside encrypted wrapper");
}
SignedJwt signed = payload.asSignedJwt();
verifySignature(
signed,
expectedAlgorithm,
expectedKeyMaterial
);
validateClaims(
signed,
expectedIssuer,
expectedAudience,
requiredType,
requiredSubject,
currentTime
);
return createProfileFromVerifiedClaims(signed.getClaims());
Three properties matter here.
First, token type is enforced before trust elevation. The application does not “try a few things and see what parses.”
Second, algorithm expectations are local policy, not token-author choice. RFC 8725 explicitly says libraries must let callers specify supported algorithms and must not use others. (RFC Editor)
Third, profile creation happens only after successful signature and claim validation. Claims are treated as untrusted input until that point.
If your architecture genuinely requires multiple token kinds, RFC 8725 recommends explicit typing and mutually exclusive validation rules. In practice, that means an access token validator should not also be willing to accept structurally different JWTs just because they come from the same issuer family or pass superficial checks. Distinguish types with typ, distinct claim requirements, distinct issuers, distinct audiences, or distinct key usage. (RFC Editor)
Detection and Logging, What to Hunt For
Patching is the priority, but detection still matters for triage and retrospective review.
Because CVE-2026-29000 is an authentication bypass, the most useful evidence often shows up not as a crash but as a suspiciously successful login or API call. Look for newly elevated profiles, unusual admin sessions, impossible-role transitions, or authentication events where issuer and audience look normal but the token path or header characteristics look odd for your environment.
A conceptual log-hunting strategy includes:
| Signal | Why it matters |
|---|---|
| Authentication success followed by immediate admin-only API access | Consistent with forged high-privilege claims |
| Tokens accepted on JWE-enabled endpoints from unfamiliar clients | Relevant because the vulnerable path involves encrypted JWT processing |
| Sudden increase in JWT parse or decrypt activity without corresponding normal login flows | May indicate token probing |
| Tokens whose inner structure or headers differ from your normal issuer profile | Useful when applications normally issue only signed nested JWTs |
| Role claims or tenant identifiers that do not match directory or session-state expectations | Identity forgery often reveals itself in authorization context mismatches |
If your gateway or auth middleware logs JOSE header metadata safely, flag any presence of alg: none in places where your system should never accept unsecured tokens. Also flag mismatches between expected token typing and observed token structure. CVE-2026-29000 does not reduce to a generic alg: none check, but any production acceptance path that treats unsigned content as normal deserves immediate scrutiny. RFC 8725 treats both attacker-chosen none and token-class confusion as recurring causes of verification failure. (RFC Editor)
A lightweight Sigma-style sketch for suspicious admin-auth events could look like this:
title: Suspicious Auth Success Followed by Immediate Admin Activity
status: experimental
logsource:
product: webapp
detection:
auth_success:
event_type: authentication_success
admin_api:
event_type: api_access
role: admin
timeframe: 5m
condition: auth_success followed_by admin_api
level: high
That is intentionally broad. In a real environment, you would refine it with service names, route families, issuer context, and known admin clients.
Temporary Mitigations for Teams That Cannot Patch Instantly
There are environments where “upgrade now” is easier said than done. Regulated release trains, compatibility locks, vendor-controlled build systems, and embedded customer deployments all slow patch velocity. That reality should not turn into passivity.
If you cannot patch immediately, reduce exploitability by constraining where the affected auth path is reachable. Internet exposure matters. Management APIs, administrative consoles, and high-privilege internal platforms using vulnerable auth components should be brought behind allowlists, VPNs, private ingress, or service-mesh policy while the fix is being validated. That does not remove the bug, but it can materially shrink the attacker set. CISecurity’s treatment of the issue as remote and unauthenticated makes this containment step operationally sensible. (CIS)
If you have the engineering leverage to add guardrails ahead of the library, reject any encrypted token whose decrypted inner object is not a signed JWT. In other words, fail closed before handing control to code that may be on the vulnerable path. This should be viewed as a temporary protective wrapper, not a substitute for upgrading, because subtle library interactions and corner cases are easy to miss. The project’s official guidance remains unambiguous: upgrade to fixed versions. (pac4j.org)
You should also invalidate the assumption that public-key publication is harmless in every context. The public key itself is not the vulnerability, but if your system exposes key material through predictable JWKS endpoints and you are still on a vulnerable version, that fact makes exploitation more practical. After patching, review where and how key distribution is documented and whether any unnecessary debug or metadata endpoints amplify attacker convenience.

The Deeper Engineering Lesson, Parseability Is Not Trust
One reason CVE-2026-29000 is worth studying in detail is that it highlights a mistake far beyond JWT libraries.
Modern software is full of objects that can be parsed, decrypted, decoded, or deserialized before they are authenticated, authorized, or policy-validated. Developers often feel a subtle confidence boost the moment an object “successfully opens.” That feeling is dangerous. A payload can be readable without being trustworthy. A decrypted message can be attacker-authored. A schema-valid token can still be identity fraud.
The pac4j case distills that difference into one line of thought. Successful decryption answered the question “can this system recover the payload.” It did not answer “should this system believe who the payload claims to be.” The latter question belongs to signature validation, token-type enforcement, issuer constraints, audience checks, and authorization rules. When those stages collapse into one fuzzy notion of “the token looks fine,” identity breaks. (Arctic Wolf)
That lesson applies equally to API gateways, SSO bridges, service-to-service tokens, mobile backends, and agentic systems that exchange signed or encrypted assertions between components. The more layers you add, the more important it becomes to make trust transitions explicit and mutually exclusive rather than permissive and inferred. RFC 8725’s guidance on explicit typing and distinct validation rules is not only about standards compliance. It is about making code auditable by humans who inherit the system later. (RFC Editor)
Where This Fits in Automated Security Validation
Identity-boundary flaws like CVE-2026-29000 are a strong fit for automated security validation because they live at the intersection of dependency exposure, endpoint discovery, token handling, and authorization outcomes. A good validation workflow is not just checking whether a package version is vulnerable. It is asking whether a reachable service accepts a forged trust transition and whether that acceptance leads to privileged behavior.
That is one reason this class of issue is operationally relevant to platforms like Penligent. In a controlled and authorized environment, an AI-assisted penetration testing workflow can help teams enumerate token-protected surfaces, detect where pac4j-jwt is in play, verify whether sensitive endpoints are actually gated by robust identity checks, and turn patch guidance into regression tests instead of one-time advice. The value is not in glamorizing exploitation. It is in closing the gap between “dependency found” and “risk verified.”
For internal security teams, the practical win is repeatability. Once a trust-boundary validation case is encoded into your testing pipeline, future upgrades, framework migrations, and feature additions can be checked against the same expectation: encrypted is not enough, parsed is not enough, and no claims become identity until verification is complete.
A Practical Hardening Checklist
The fastest way to reduce repeat failures is to translate the lessons into durable engineering policy.
| Control | Why it matters for this class of flaw |
|---|---|
| Patch vulnerable pac4j-jwt versions immediately | Removes the published vulnerable logic path. |
Inventory every service using JwtAuthenticator | Narrows real exposure instead of guessing from package lists. |
| Reject inner tokens that are not explicitly the expected type | Prevents PlainJWT and similar confusion paths. |
| Pin supported algorithms in code and config | Aligns with RFC 8725 and reduces attacker-controlled algorithm drift. |
| Separate validation rules for different JWT kinds | Stops one token class from being accepted in another context. |
| Build user profiles only from verified claims | Prevents parse success from becoming trust elevation. |
| Add regression tests for malformed, unsigned, and nested token cases | Keeps future refactors from reintroducing the bug class. |
| Monitor privileged auth flows for anomalies | Helps catch silent authentication bypass postures. |
A regression test suite should include at least these negative cases:
encrypted token with unsigned inner JWT must fail
signed token using unsupported algorithm must fail
token with wrong typ for endpoint must fail
token with correct structure but wrong issuer or audience must fail
token with missing subject or required claims must fail
token with valid decryption but invalid signature must fail
Those tests are mundane, but that is exactly why they matter. Many severe auth bugs survive because nobody wrote down the simple security invariants the system was supposed to enforce.
Why CVE-2026-29000 Matters Beyond pac4j
It is tempting to treat every new CVE as a product-specific event. Patch the package, update the changelog, move on. That response is necessary, but not sufficient here.
CVE-2026-29000 matters because it lands at the identity layer, because it shows how encryption can be misread as trust, and because it exposes how easily standards-compliant flexibility can become implementation ambiguity. The pac4j ecosystem will patch and move forward. The harder question for engineering leaders is whether similar assumptions exist elsewhere in their auth stack: another library, another framework adapter, another internal verifier, another “temporary” custom parser that no one has reviewed in two years.
The strongest organizations will use this bug not only to patch but to re-audit how they reason about tokens at all. Which components are allowed to parse? Which components are allowed to verify? Which components are allowed to construct authenticated identity? Are those responsibilities explicit, or have they blurred together over time? CVE-2026-29000 is what that blur looks like when it reaches production. (codeant.ai)
Final Take
The cleanest summary of CVE-2026-29000 is this: a system accepted encrypted identity claims without ensuring that the claims had been signed by a trusted issuer. That is why the bug is so dangerous, and that is why the fix is not just “be careful with JWTs.” The real fix is stricter trust discipline.
Patch the library. Inventory the auth paths. Fail closed on token type. Pin algorithms. Require mutually exclusive validation rules. Build user profiles only from verified claims. And do not let successful parsing, decryption, or deserialization masquerade as proof of identity.
That discipline will outlast this CVE, and it will protect you from the next one.
Recommended Reading and Related Links
- NVD entry for CVE-2026-29000 (NVD)
- GitHub Advisory Database entry for CVE-2026-29000 (GitHub)
- pac4j official security advisory for
JwtAuthenticator(pac4j.org) - pac4j JWT authenticator documentation (pac4j.org)
- RFC 7519, JSON Web Token (RFC Editor)
- RFC 8725, JWT Best Current Practices (RFC Editor)
- Arctic Wolf analysis of CVE-2026-29000 (Arctic Wolf)
- CISecurity advisory on CVE-2026-29000 (CIS)
- CVE-2015-9235, classic JWT algorithm confusion in
jsonwebtoken(NVD) - CVE-2024-54150, signature verification confusion in
cjwt(NVD) - CVE-2026-28802, recent
alg: noneverification failure in Authlib (NVD) - Penligent, CVE-2026-29000, The pac4j-jwt Authentication Bypass That Turns Encryption Into a False Sense of Trust (penligent.ai)
- Penligent, pac4j-jwt Security Risks, CVE-2026-29000, and What Secure JWT Validation Really Requires (Penligent)
- Penligent, JSON Web Signature Decode, The Gateway to Critical Verification Vulnerabilities (Penligent)


