The issue is bigger than one CVE
Security teams searching for veeam cve in March 2026 are not really looking for a single bug. They are looking for an answer to a harder question: what happens when the system you depend on for recovery becomes part of the attack path itself. That is the right lens for CVE-2026-21672. On paper, it is a high-severity local privilege escalation flaw on Windows-based Veeam Backup & Replication servers, scored 8.8 under CVSS v3.1. In practice, it landed in the same March 12, 2026 disclosure wave as multiple critical and high-severity flaws affecting the Veeam backup plane, including authenticated RCE on the backup server, arbitrary file manipulation on a backup repository, and RCE reachable by a Backup Viewer role as the postgres user. The cluster matters as much as the individual record. (Veeam Software)
That is also how the current English-language coverage is framing the story. The dominant language across vendor and media reporting is not “minor local issue” or “edge case Windows bug.” It is “critical vulnerabilities,” “RCE,” “patch now,” and “backup servers.” Those recurring phrases are a useful signal, because they show what security teams and editors alike see as the core operational reality: Veeam’s backup and recovery plane remains a high-value target, and patch latency is now a direct resilience risk. (SOCRadar® Cyber Intelligence Inc.)
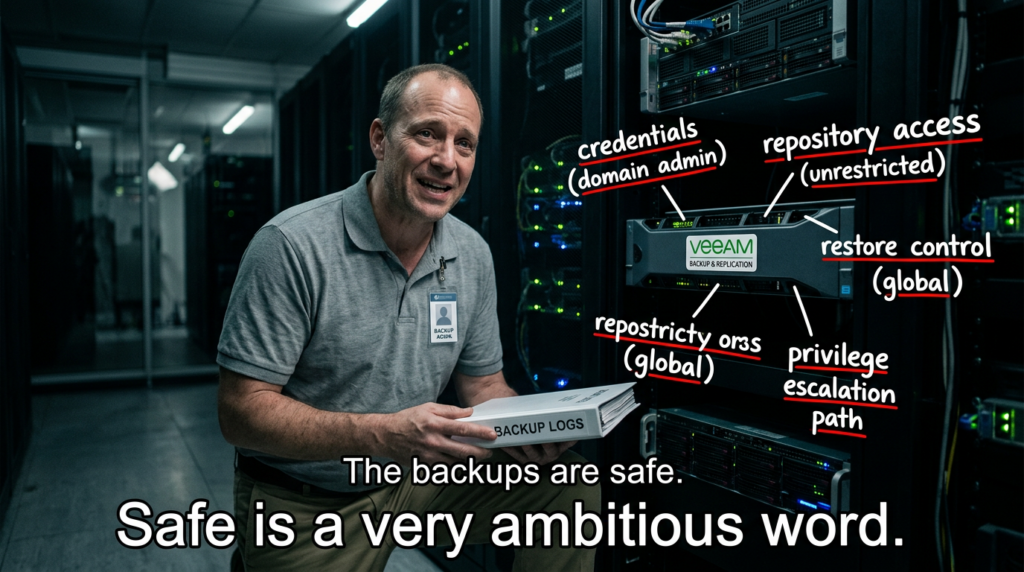
If you only read the CVE title, you might conclude that CVE-2026-21672 is less urgent than a pre-auth remote code execution flaw. That would be the wrong conclusion. Backup infrastructure is not just another Windows application stack. It sits near hypervisors, repositories, service accounts, identity, restore workflows, and disaster recovery control points. Veeam’s own security best-practice material frames this as a Zero Trust Data Resilience problem, not merely a software patching problem. In other words, once an attacker reaches the backup plane, the question is no longer only “can they run code,” but also “can they sabotage recovery, decrypt credentials, manipulate repositories, or inherit privilege through trust relationships and role design.” (bp.veeam.com)
What CVE-2026-21672 is, exactly
Veeam describes CVE-2026-21672 in straightforward language. In both the supported Veeam Backup & Replication 12 branch and the 13 branch, the company states that the flaw allows local privilege escalation on Windows-based Veeam Backup & Replication servers. The issue is rated High, with a CVSS v3.1 score of 8.8, and the vector published by Veeam and reflected in the CVE record is AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H. The issue was reported through HackerOne. (Veeam Software)
For supported version lines, the affected and fixed builds are explicit. On the 12 line, all vulnerabilities in the March 12 bulletin affect Veeam Backup & Replication 12.3.2.4165 and all earlier version 12 builds, and the documented fixes start in 12.3.2.4465. On the 13 line, the same disclosure wave affects 13.0.1.1071 and all earlier version 13 builds, and the fixes start in 13.0.1.2067. That means security teams do not need to guess at the remediation baseline; Veeam has already published the minimum patched targets for both supported branches. (Veeam Software)
NVD’s public record for CVE-2026-21672 is still awaiting full enrichment, but it already mirrors the core description and the contributed CVSS v3.1 vector from the public disclosure. The most important operational takeaway is that the public facts have converged across the vendor bulletin, the CVE program record, and NVD: this is a real high-severity local privilege escalation issue affecting Windows-based Veeam Backup & Replication servers, and the vendor has already tied it to concrete build remediations. (NVD)
Why a local privilege escalation flaw matters on a backup server
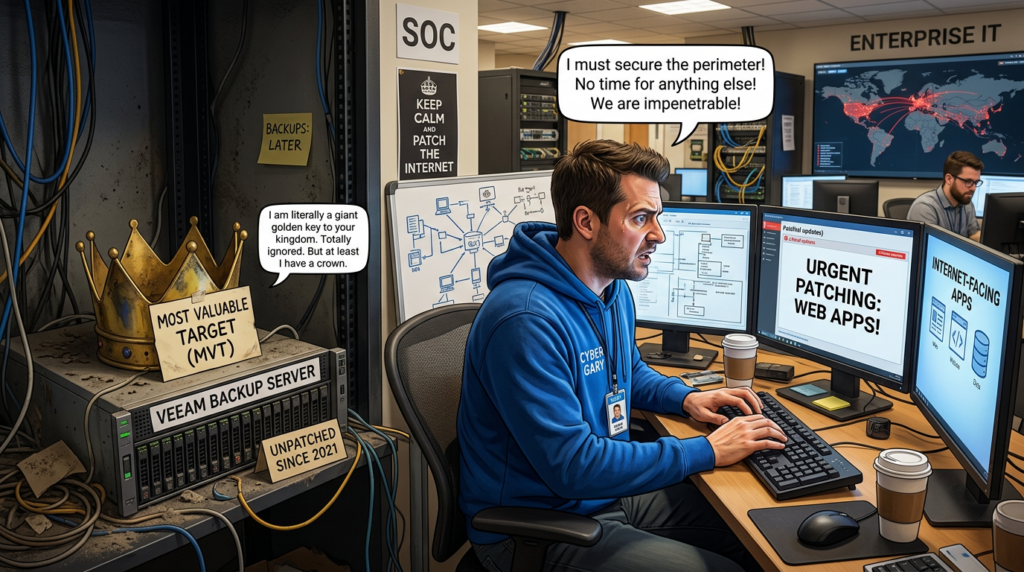
There is a persistent habit in security operations to rank vulnerabilities mentally by whether they are pre-auth remote. That habit is understandable, but it is incomplete. A backup server is not an ordinary endpoint. It is a control point over recovery. If an attacker already has a foothold on the host, or can reach a low-privileged local context through adjacent compromise, an LPE on that box can be the difference between nuisance access and a full recovery-denial event. (Veeam Software)
Veeam’s own documentation explains why. The product’s configuration database stores credentials used to connect to virtual servers and other systems in the backup infrastructure. Those passwords are encrypted, but Veeam also states that a user with administrator privileges on the backup server can decrypt them, which it calls a potential threat. That single sentence is more important than it looks. It means the blast radius of privilege escalation on the backup host is not confined to that host. It may extend to connected infrastructure, service credentials, repositories, or managed assets reachable through the backup plane. (Veeam Software)
This is why CVE-2026-21672 should be understood as a pivot and amplification vulnerability. The flaw itself is local. The consequences are architectural. In environments where backup servers touch production identity, share trust with production domains, or retain broad repository and orchestration privileges, local elevation can transform a single host compromise into a recovery-control compromise. That is exactly why Veeam’s hardening guidance repeatedly pushes separation from the production domain, stronger account protection, MFA, encrypted configuration backup, immutability, and reduced remote exposure. (bp.veeam.com)

The March 2026 disclosure wave, viewed as a system problem
The most dangerous mistake in reading the March 2026 Veeam bulletins is to isolate CVE-2026-21672 from the rest of the set. In the 12 branch disclosure, Veeam listed CVE-2026-21666 and CVE-2026-21667 as critical 9.9 issues allowing an authenticated domain user to perform remote code execution on the backup server, CVE-2026-21668 as a high-severity flaw allowing an authenticated domain user to bypass restrictions and manipulate arbitrary files on a backup repository, CVE-2026-21672 as the Windows local privilege escalation issue, and CVE-2026-21708 as a critical 9.9 flaw allowing a Backup Viewer to perform RCE as the postgres user. (Veeam Software)
In the 13 branch, the list is slightly different but tells the same story. Veeam disclosed CVE-2026-21669 as critical authenticated RCE on the backup server, CVE-2026-21670 as saved SSH credential extraction for a low-privileged user, CVE-2026-21671 as critical RCE in high-availability deployments of the Veeam Software Appliance for a Backup Administrator, CVE-2026-21672 as Windows local privilege escalation, and CVE-2026-21708 as critical RCE as postgres for a Backup Viewer. (Veeam Software)
That mix reveals a pattern. The risk is not narrowly about one parser, one deserialization path, or one Windows ACL mistake. The risk spans role boundaries, credential handling, repository controls, Windows deployment hardening, appliance deployment hardening, and privilege separation. When a disclosure wave looks like that, the right response is not merely “install the patch and move on.” The right response is to ask whether the backup plane has become over-trusted, over-connected, and over-entitled in your environment. (Veeam Software)
A short Veeam vulnerability timeline that explains the bigger pattern
The current concern did not appear overnight. The better way to understand CVE-2026-21672 is to place it inside a three-year arc of Veeam risk.
In March 2023, CVE-2023-27532 showed how dangerous backup infrastructure becomes when a core service can expose encrypted credentials. Veeam documented that the issue allowed an unauthenticated user operating within the backup infrastructure network perimeter to obtain encrypted credentials stored in the configuration database, potentially leading to access to backup infrastructure hosts. Veeam fixed it in version 12 build 12.0.0.1420 P20230223 and 11a build 11.0.1.1261 P20230227, and even noted that blocking external access to TCP 9401 could serve as a temporary mitigation in some all-in-one appliance scenarios. (Veeam Software)
In September 2024, CVE-2024-40711 pushed the conversation further. Veeam described it as an unauthenticated remote code execution vulnerability with a CVSS v3.1 score of 9.8. The same September bulletin also included high-severity issues around MFA setting alteration, low-privileged paths to RCE and sensitive information extraction, path traversal enabling local privilege escalation, and TLS certificate validation weaknesses. That set of disclosures made clear that the Veeam management and backup plane had become a serious offensive target surface, not merely a data-protection utility. CISA later added CVE-2024-40711 to the Known Exploited Vulnerabilities catalog, which is an unusually strong signal that the bug had crossed from patch-management concern into active threat reality. (Veeam Software)
In 2025, the story continued with CVE-2025-23120 and CVE-2025-23121. Veeam described both as authenticated domain-user remote code execution issues on the backup server and stressed that they only impact domain-joined backup servers. That condition matters, because it aligns exactly with a long-running best-practice theme in Veeam’s own guidance: the safest deployment is a separate management workgroup or a management domain in a separate Active Directory forest, so the recovery environment does not rely on the environment it is supposed to protect. (Veeam Software)
By March 2026, CVE-2026-21672 arrived not as an isolated surprise but as part of a sustained pattern: backup infrastructure keeps leaking risk through credential exposure, trust design, role boundaries, and overpowered management components. That is why the right interpretation of a query like veeam cve CVE-2026-21672 is not “tell me about one bug.” It is “tell me whether my recovery layer has quietly become one of the most dangerous places to be wrong.” (Veeam Software)
Why attackers keep going after backup infrastructure
Attackers target backup systems for a simple reason: backups are the last argument defenders hold after primary compromise. If attackers can neutralize that argument, ransomware becomes more coercive, extortion becomes more credible, and incident recovery becomes slower, riskier, and more expensive. That logic is visible across public security reporting on Veeam over the last two years. CISA’s KEV catalog includes Veeam records. Security reporting around CVE-2024-40711 tied the flaw to real-world compromise of backup servers and the deletion of recovery data in ransomware campaigns. Threat reporting has also connected Veeam targeting to ransomware operators and to the broader strategy of attacking recovery infrastructure before or during encryption. (CISA)
The backup plane is especially attractive because it often combines three properties that attackers love. First, it is trusted. Second, it is connected to many important systems. Third, it is frequently under-monitored compared with internet-facing applications and endpoints. Those conditions mean a compromise there can yield repository tampering, credential harvesting, privileged orchestration access, or even quiet preparation for later destructive actions. Veeam’s own documentation implicitly acknowledges this danger by recommending no inbound internet access to backup servers, MFA for the console, encrypted traffic even inside private networks, tighter ACLs on installation directories, and hardened repository handling. (Veeam Software)
This is why even a local privilege escalation issue deserves attention in the backup context. Real attackers do not experience your environment as separate CVE categories. They experience it as a set of reachable paths. A foothold on the host, a low-privileged role, a repository manipulation primitive, a credential extraction path, a mis-scoped service account, and a production-domain trust edge are not separate stories. They are one story. (Veeam Software)
The operational reading of CVE-2026-21672
The cleanest way to think about CVE-2026-21672 is this: it is a host-level privilege amplifier inside a platform that already mediates access to high-value recovery assets. That makes it different from a local bug on an ordinary workstation. If a defender is already in a situation where a Veeam backup server has a local foothold, perhaps through separate credential theft, software deployment abuse, neighboring admin access, or a chained role or repository issue, then local elevation turns containment from “we still may be okay” into “the backup plane itself may now be under attacker control.” (Veeam Software)
The CVSS vector also supports that interpretation. The attack vector is local, but the scope is changed and the confidentiality, integrity, and availability impact is all set to high. That is not the signature of a cosmetic issue. It is the signature of a flaw that can change the attacker’s power relative to the protected data and systems. On a recovery platform, that is operationally serious. (Veeam Software)
Version map and patch baseline
The first question many teams ask is simply, “Which builds are safe?” The table below gives the practical baseline from Veeam’s March 12, 2026 bulletins.
| Product line | Affected builds | Fixed starting build | CVE-2026-21672 applies to |
|---|---|---|---|
| Veeam Backup & Replication 12 | 12.3.2.4165 and all earlier version 12 builds | 12.3.2.4465 | Windows-based VBR servers |
| Veeam Backup & Replication 13 | 13.0.1.1071 and all earlier version 13 builds | 13.0.1.2067 | Windows-based VBR servers |
This table is simple, but it is useful because many real environments do not fail on detection; they fail on ambiguity. In this case, ambiguity is low. If you are on the affected 12 or 13 baselines, Veeam has already published the patched minimums. (Veeam Software)
The related Veeam CVEs that matter most in this discussion
Because the user query combines veeam cve with CVE-2026-21672, a useful article should not stop at one record. The table below summarizes the related Veeam Backup & Replication CVEs that best explain the current risk landscape.
| CVE | Year | Core issue | Severity | Why it matters here |
|---|---|---|---|---|
| CVE-2023-27532 | 2023 | Credential exposure from a core VBR service | High 7.5 | Shows how backup-plane secrets can become pivot material |
| CVE-2024-40711 | 2024 | Unauthenticated RCE | Critical 9.8 | Demonstrates that Veeam compromise moved from internal trust risk to direct external exploitation concern |
| CVE-2025-23120 | 2025 | Authenticated domain-user RCE on backup server | Critical 9.9 | Highlights the danger of domain-joined backup servers |
| CVE-2025-23121 | 2025 | Authenticated domain-user RCE on backup server | Critical 9.9 | Reinforces that trust topology is part of the vulnerability story |
| CVE-2026-21668 | 2026 | Arbitrary file manipulation on backup repository | High 8.8 | Shows that repository integrity is directly in scope |
| CVE-2026-21672 | 2026 | Local privilege escalation on Windows VBR servers | High 8.8 | Elevates attacker power at the recovery control point |
| CVE-2026-21708 | 2026 | Backup Viewer to postgres RCE | Critical 9.9 | Shows dangerous role-boundary consequences inside the platform |
The pattern running through this table is not random. It is a sequence of exposures around credentials, code execution, trust placement, role design, repository control, and privilege boundary weakness. That is why patching CVE-2026-21672 is necessary but not sufficient. It must be paired with architectural hardening. (Veeam Software)
How to verify exposure fast
Many teams do not need a thousand-word explanation first. They need a reliable way to answer four questions today: what version am I on, is the host domain joined, how are the Veeam services running, and is the server unnecessarily exposed or over-trusted.
The following PowerShell is a safe inventory and hardening sanity check. It is not an exploit and it does not change the host. It simply helps you collect the facts you need before patching and hardening.
$veeamExe = "C:\\Program Files\\Veeam\\Backup and Replication\\Backup\\Veeam.Backup.Service.exe"
Write-Host "=== Veeam Backup & Replication quick check ==="
if (Test-Path $veeamExe) {
$file = Get-Item $veeamExe
Write-Host ("Veeam.Backup.Service.exe version: {0}" -f $file.VersionInfo.FileVersion)
} else {
Write-Host "Veeam.Backup.Service.exe not found in default path."
}
Write-Host ""
Write-Host "=== Domain join status ==="
try {
$cs = Get-CimInstance Win32_ComputerSystem
Write-Host ("PartOfDomain: {0}" -f $cs.PartOfDomain)
Write-Host ("Domain: {0}" -f $cs.Domain)
} catch {
Write-Host "Could not query Win32_ComputerSystem."
}
Write-Host ""
Write-Host "=== Veeam services and service accounts ==="
Get-CimInstance Win32_Service |
Where-Object { $_.Name -like "Veeam*" } |
Select-Object Name, StartName, State, StartMode |
Format-Table -AutoSize
Write-Host ""
Write-Host "=== Listening ports for common Veeam processes ==="
Get-NetTCPConnection -State Listen -ErrorAction SilentlyContinue |
Sort-Object LocalPort |
Select-Object LocalAddress, LocalPort, OwningProcess |
Format-Table -AutoSize
Why these checks? Because Veeam’s own guidance says backup services should be running under the LocalSystem account, MFA should be enabled, immutable or offline media should be in use, the backup server should not be part of the production domain, and latest product updates should be installed. It also warns that internet inbound connectivity to backup servers must not be allowed. Those are not abstract best practices; they are practical ways to shrink the blast radius around exactly the class of risks surfaced by recent Veeam advisories. (Veeam Software)

What to do first if you are exposed
The immediate response priority is patching to a fixed build. If you are on an affected 12 line, move to 12.3.2.4465. If you are on an affected 13 line, move to 13.0.1.2067. Veeam explicitly warns that once vulnerabilities and patches are disclosed, attackers will likely reverse engineer the patch to target unpatched deployments. That is a vendor warning worth taking literally. (Veeam Software)
The second priority is exposure reduction. Veeam’s user guide says inbound connectivity to backup servers from the internet must not be allowed. If remote administration is required, use a jump server or the vendor-supported remote access approach rather than leaving the backup server directly reachable. This is one of those controls that sounds obvious until an incident review shows it was the missing one. (Veeam Software)
The third priority is trust reduction. Veeam’s best-practice guide is unusually direct: the most secure deployment places Veeam components in a separate workgroup or in a management domain located in a separate Active Directory forest, protected with two-factor authentication, so the backup environment does not depend on the environment it is meant to protect. This recommendation is not theoretical. It directly maps to the logic of the 2025 and 2026 vulnerability history, where domain trust and management-plane access repeatedly showed up as part of the risk story. (bp.veeam.com)
The fourth priority is recovery integrity. Veeam’s analyzer guidance says immutable or offline media should be used, configuration backup should be enabled and encrypted, job encryption should be enabled for cloud repositories, hardened repositories should have SSH disabled after deployment, and passwords and encryption secrets should rotate at least annually. These are the controls that make it harder for attackers to turn a software flaw into a full recovery-denial event. (Veeam Software)
The hardening controls that actually matter here
Some vulnerability articles end with a generic paragraph about “follow security best practices.” That is not enough for Veeam. The product already exposes a useful set of concrete controls, and recent Veeam history shows which ones matter most.
Separate the backup plane from the production plane
The cleanest defensive move is to stop treating backup servers as ordinary members of the production trust graph. Veeam’s best-practice guide recommends either a separate management domain in another forest or a separate workgroup, specifically so the backup environment does not depend on the compromised estate it is supposed to recover. The repeated appearance of domain-user-driven RCE in 2025 makes this recommendation far more than a theoretical nicety. (bp.veeam.com)
Enable MFA for the console
Veeam’s analyzer flags MFA as a core product configuration expectation. This matters not only for direct console access, but because privilege escalation and role confusion become substantially harder to operationalize when the console is protected by an additional verification factor. MFA does not fix CVE-2026-21672, but it does reduce the chances that adjacent account abuse turns into broader platform control. (Veeam Software)
Use immutable or offline media
Veeam explicitly recommends that immutable repositories or offline media be actively used. This is one of the few controls that still helps even after partial compromise, because it protects against silent deletion or mutation of backup data. In the context of repository manipulation bugs and ransomware targeting, this is not optional maturity theater. It is one of the main reasons organizations can recover at all. (Veeam Software)
Encrypt and back up the configuration database
Veeam recommends enabling configuration backup and encrypting it. That advice is easy to gloss over until you remember that the configuration database stores sensitive credentials and connection metadata. If that database becomes part of the compromise story, a secure, recoverable, encrypted configuration backup can materially reduce recovery time and uncertainty. (Veeam Software)
Tighten installation-folder ACLs and service-account behavior
The user guide specifically recommends using the vendor’s ACL model for any custom installation folder to prevent privilege escalation and arbitrary code execution attacks. It also documents that backup services should run under the LocalSystem account. These are low-level configuration details, but local privilege escalation bugs are often won or lost in exactly this layer. (Veeam Software)
Disable unnecessary inbound exposure and harden hardened repositories
The same documentation set recommends no internet inbound access to backup servers, encrypted traffic even on private networks, and SSH disabled on hardened repositories after deployment. None of that is glamorous. All of it is effective. (Veeam Software)
A practical priority matrix for defenders
The following table is a more realistic decision aid than a severity score alone.
| Condition | Operational priority | Why |
|---|---|---|
| You run an affected 12 or 13 build | Immediate | Public disclosure and fixed builds already exist |
| The backup server is domain joined | Immediate and architectural | Past critical Veeam RCE issues specifically impacted domain-joined servers |
| The server is reachable from the internet | Immediate | Veeam explicitly says inbound internet connectivity must not be allowed |
| Immutable or offline copies are not in use | High | Recovery integrity is at direct risk if the platform is compromised |
| MFA is not enabled for the console | High | Platform abuse becomes easier once account access is obtained |
| Hardened repositories still allow SSH after deployment | High | Unnecessary management access expands attack surface |
| Configuration backup is disabled or unencrypted | High | Recovery becomes slower and sensitive data handling weaker |
This is the kind of matrix security teams actually need during change control discussions. It translates “veeam cve” from a news event into a remediation sequence. (Veeam Software)
The argument against complacency
One common reaction to CVE-2026-21672 is to downgrade urgency because exploitation is local. That reaction misses how compromises happen in enterprise environments. Local access is often not the first move. It is the second or third move. An attacker who lands through phishing, remote management abuse, service-account theft, software deployment misuse, or domain credential compromise is not starting from nothing. They are looking for leverage. Backup servers are packed with leverage. (CSO Online)
There is also a historical reason not to be complacent. Veeam vulnerabilities have already appeared in CISA’s KEV catalog, and reporting on 2024 exploitation tied backup-server compromise to ransomware playbooks that aimed to delete or neutralize recovery data. Once a platform enters that stage of adversary attention, every new high-severity bug should be read in the context of adversary learning, not just vendor taxonomy. (CISA)
Where continuous validation becomes more useful than one-time patching
Patching is necessary, but mature teams already know the uncomfortable truth: patching closes the disclosed bug, not the whole path. The path often includes trust edges, stray exposure, role overreach, inherited local admin, stale credentials, repository access patterns, and recovery workflows nobody has adversarially tested. That is why backup security has become a validation problem as much as an update problem. (Veeam Software)
That is also the natural point where a platform like Penligent can fit without forcing the connection. If your team wants to verify whether the backup plane is still reachable through adjacent assets, whether low-privilege paths still exist after patching, or whether repository and management surfaces remain overexposed, an AI-assisted penetration testing workflow can help shorten the loop from inventory to validation to evidence. Penligent’s own English coverage on Veeam makes the same larger point: the real story is not one isolated CVE, but the way backup infrastructure has become one of the highest-leverage failure points in modern enterprise security. (Penligent)
A more useful post-patch question, then, is not “did we install the update.” It is “can we prove the recovery plane is now harder to reach, harder to elevate through, harder to manipulate, and harder to use as a pivot.” That is the right question after CVE-2026-21672, and it is also the right question after the broader 2026 Veeam disclosure wave. (Veeam Software)
What a mature response looks like
A mature response to CVE-2026-21672 does not end with a ticket that says “patched.” It should leave behind a stronger backup architecture than the one you had before the advisory dropped.
It should leave you on a fixed build. It should remove any unnecessary internet reachability to backup servers. It should confirm whether the environment is domain joined and, if so, whether that design decision is still defensible. It should enable MFA on the console, verify immutable or offline copies, encrypt configuration backups, rotate sensitive credentials, review service-account scope, and harden repository access. Those are not generic ideas; they are the controls Veeam itself emphasizes in its user guide, analyzer, and best-practice content. (Veeam Software)
It should also force a cultural shift. Backup systems should stop being treated as passive insurance products and start being treated as high-value security infrastructure. The vendor’s own Zero Trust Data Resilience framing points in that direction. The last three years of Veeam CVEs make the same case from the opposite side: if the recovery plane is trusted like infrastructure but operated like a utility, attackers will keep finding ways to turn that gap into leverage. (bp.veeam.com)
Final takeaway
The cleanest summary of veeam cve CVE-2026-21672 is not that Veeam has another bug. It is that backup infrastructure keeps proving a larger security lesson: the systems built to save the environment are also some of the systems most worth compromising. CVE-2026-21672 is a high-severity local privilege escalation flaw on Windows-based Veeam Backup & Replication servers. That is the factual core. But the operational core is broader. It arrives in a product line with recent history that includes credential exposure, unauthenticated RCE, domain-user-driven RCE, repository manipulation, and dangerous role-boundary failures. (Veeam Software)
If you are running affected builds, the action is straightforward: move to the fixed baselines, then use the event to harden the recovery plane as if it were a frontline security tier, because that is what it has become. (Veeam Software)
Further reading, official and related English resources
For readers who want to go deeper, the most useful official references are Veeam’s March 2026 bulletins for the 12 and 13 branches, the NVD and CVE records for CVE-2026-21672, Veeam’s security best-practice guidance on workgroup versus domain placement, the securing-backup-infrastructure documentation, and the Best Practices Analyzer guidance for MFA, immutability, configuration backup, and update hygiene. (Veeam Software)
For historical context, the most relevant prior vendor references are Veeam’s CVE-2023-27532 advisory, the September 2024 security bulletin covering CVE-2024-40711 and related flaws, and the 2025 advisories for CVE-2025-23120 and CVE-2025-23121. CISA’s KEV catalog and alerting around Veeam also help anchor the fact that some Veeam flaws have crossed into active exploitation significance. (Veeam Software)
For Penligent articles to interlink naturally at the end of this page, the strongest fit is Veeam CVE — Why Backup Infrastructure Has Become One of the Most Dangerous Places to Be Wrong, followed by CVE-2026-22769 The Hardcoded Credential That Turns Backup Infrastructure Into an Intrusion Beachhead, and, for the broader automation angle, The Rise of Autonomous Hacking: How AI Pentest Tools Are Rewriting Security. (Penligent)