CVE-2025-66034 is the kind of vulnerability many teams underestimate on first read. The affected package is fontTools, a well-known Python library for working with fonts. The affected code path is fontTools.varLib, used to build variable fonts from .designspace files. The bug is not in some obscure demo script. It sits in a real build flow, with real documentation, real downstream packaging, and real remediation notes across upstream, distro, and enterprise vendor channels. The official upstream advisory says vulnerable versions from 4.33.0 up to but not including 4.60.2 can be tricked into arbitrary file write, and that this can lead to remote code execution when a malicious .designspace file is processed. (GitHub)
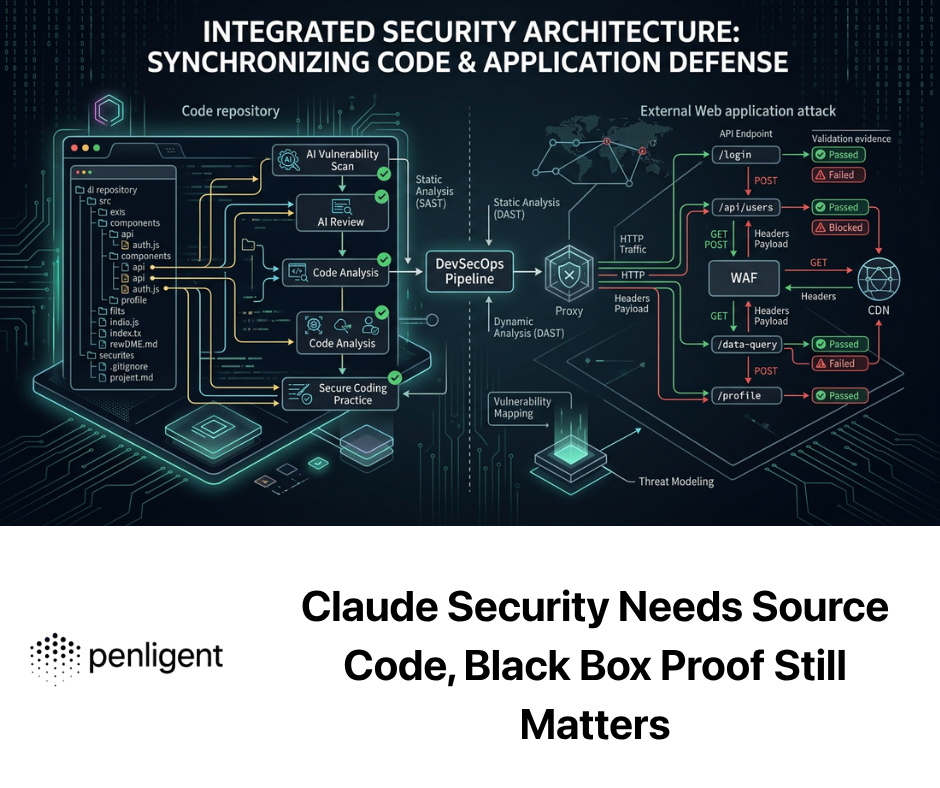
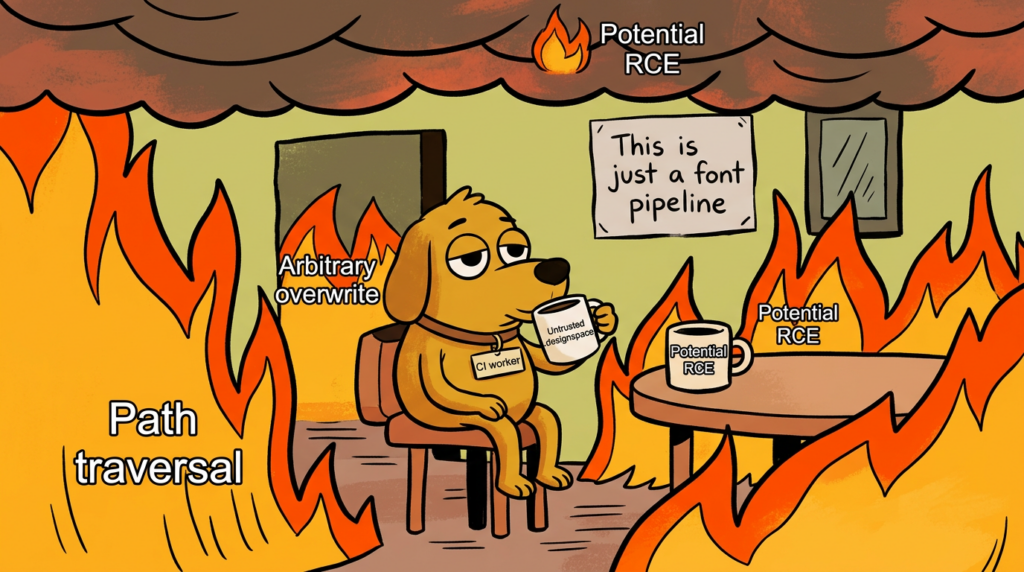
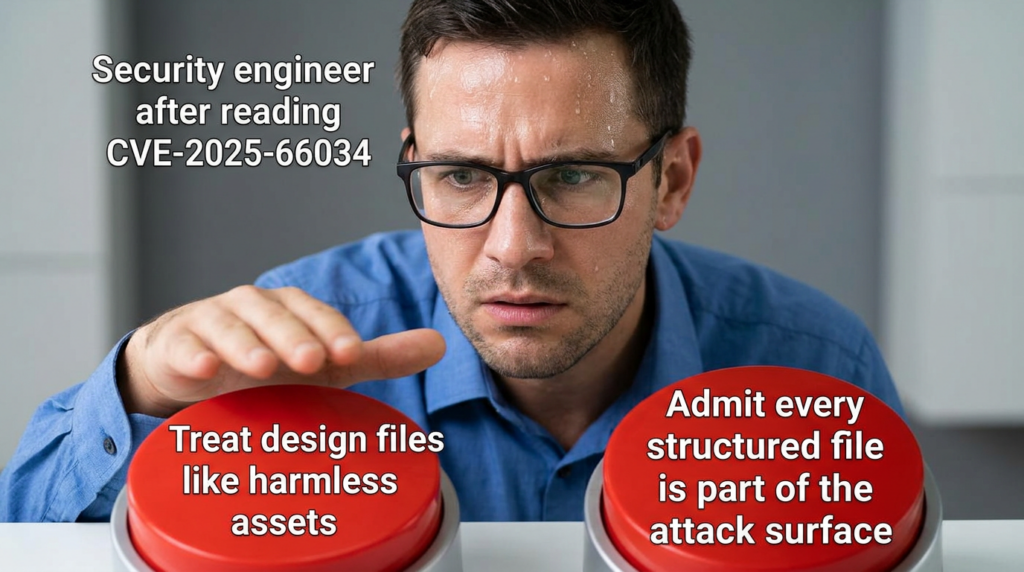
The reason this matters is not “fonts” in the abstract. It matters because modern software systems automate everything. Build workers compile design assets. SaaS platforms ingest user-supplied files. CI jobs pull repositories and generate artifacts. Internal tools process untrusted uploads because someone assumed a design file was less dangerous than a script, a template, or an archive. CVE-2025-66034 breaks that assumption. It shows how a structured design artifact can become a filesystem write primitive, and in the wrong environment, a code execution path. (fontTools Documentation)
From a public-search perspective, the clearest, most repeated framing across reputable results is also the correct one technically: this is a fontTools varLib bug that enables arbitrary file write, and under some deployment conditions that write becomes remote code execution. That is the framing used or echoed by the upstream GitHub advisory, GitLab’s advisory database, NVD’s description, and multiple later secondary explainers. It is direct, accurate, and better than burying the lead under vague wording. (GitHub)
What CVE-2025-66034 actually is
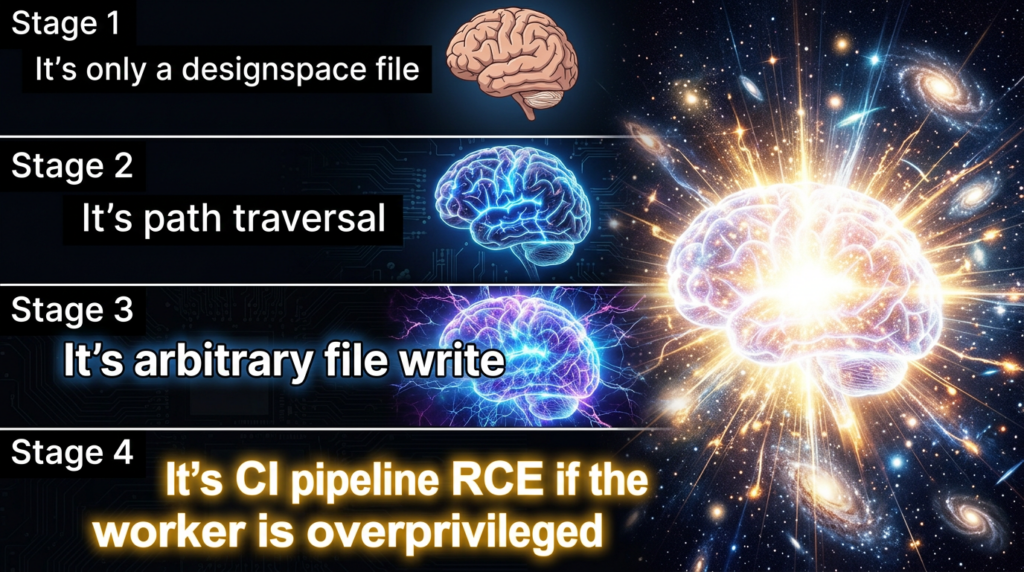
The official description is consistent across the main authoritative sources. In vulnerable versions of fontTools, the fonttools varLib command, or code that invokes fontTools.varLib.main(), can be abused when it processes a malicious .designspace file. The flaw comes from unsanitized filename handling. The advisory explains that attackers can use path traversal sequences to write output files to arbitrary filesystem locations, and can also inject controlled content into output files. That combination is what creates the path from file write to code execution. (GitHub)
Upstream’s advisory is unusually clear on the mechanics. It says the vulnerability exists because of “unsanitised filename handling combined with content injection.” It goes further than many advisories do and explicitly lists likely outcomes: writing font files to arbitrary filesystem locations, overwriting configuration files, corrupting application files and dependencies, and obtaining remote code execution. That language matters, because it tells you the maintainers were not treating this as a harmless path bug with no practical blast radius. (GitHub)
The patch is correspondingly small and revealing. The fix in the upstream commit changes the behavior so that when a variable font filename is present, only os.path.basename(vf.filename) is used. In other words, directory components are stripped before the output path is joined. The release notes later spell that out in plain language: use only the basename to prevent path traversal attacks in varLib.main. This is one of those rare cases where the exploit story and the patch story line up almost one-to-one. (GitHub)
That also makes the trust-boundary failure easy to explain. The vulnerable flow treated an attacker-influenced filename as if it were a safe output name. Once that filename was allowed to carry traversal markers or absolute-path semantics, the output directory stopped being a boundary and became a suggestion. At that point, the only question left was whether the target environment had a meaningful place to write a file that would later matter. In real environments, the answer is often yes. (GitHub)
Why a designspace file is not a toy input
This CVE lands harder once you understand what .designspace is in practice. fontTools documentation describes designspaceLib as the component for reading, writing, and editing designspace files, and explains that these files define axes, sources, variable fonts, instances, and related data. The varLib documentation describes itself as the package for handling, building, and interpolating variable font data. The docs also explicitly show that a designspace file can be used in making a variable font with varLib. This is not theoretical plumbing. It is a production workflow. (fontTools Documentation)
The documentation also explains why filenames and paths are part of the designspace model at all. A designspace file stores references to other files, often with relative paths, because designspace files move between systems and repositories. That is perfectly reasonable functionality. The problem is not that files contain paths. The problem is that the wrong path semantics were trusted on the output side. As soon as an attacker can influence where generated output lands, a data description file starts looking less like configuration and more like a write instruction. (fontTools Documentation)
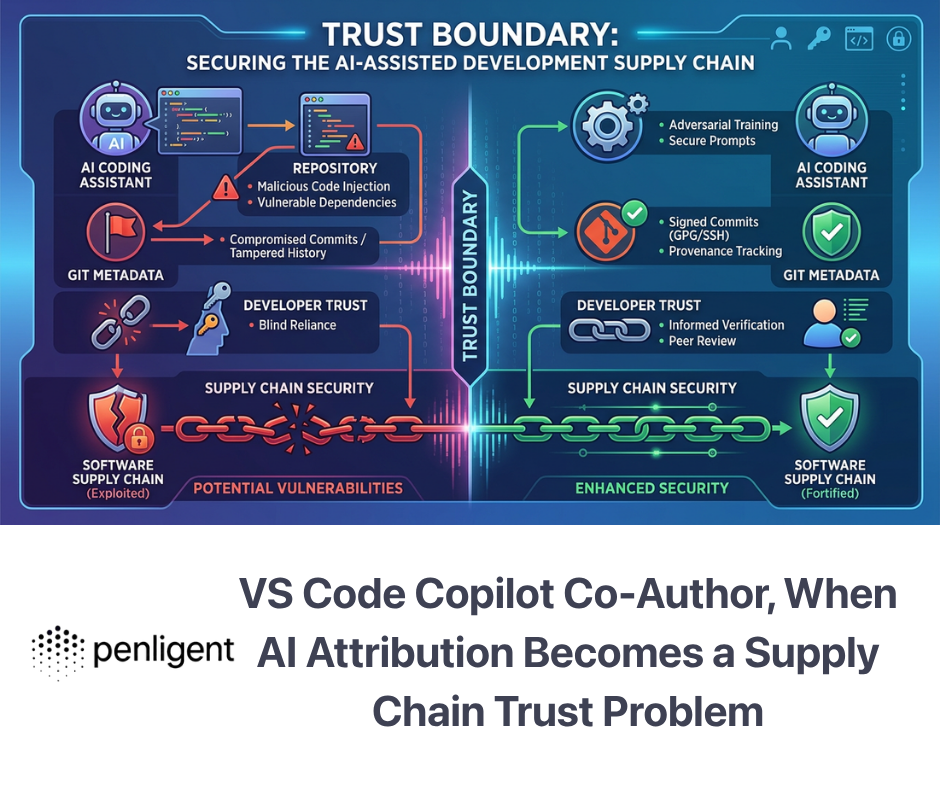
This is the broader lesson many engineers miss. In mature automation, data formats are not passive. They often carry names, paths, destinations, references, templates, rules, include directives, and serialization behavior. If your pipeline reads them, resolves them, and emits artifacts from them, then the format sits on a control boundary whether you intended that or not. CVE-2025-66034 is really a story about that boundary being misclassified. (fontTools Documentation)
The vulnerability in one simplified code path
The upstream advisory includes the essential vulnerable lines. In conceptual terms, the old logic did this:
# simplified, conceptual
filename = attacker_controlled_filename
output_path = os.path.join(output_dir, filename)
save(output_path)
The fixed logic effectively does this instead:
# simplified, conceptual
filename = os.path.basename(attacker_controlled_filename)
output_path = os.path.join(output_dir, filename)
save(output_path)
That difference looks trivial until you remember what ../, nested relative paths, or absolute-style path content can do inside automation. A single basename normalization step is enough to turn a filesystem escape back into a normal artifact write. That is exactly why the fix is so small and so important. (GitHub)
The upstream advisory also points out that content injection is part of the risk picture. This is not only “write some file somewhere.” The attacker may also influence what gets written. That is what makes RCE a realistic outcome in certain deployments: a controlled write into a meaningful location plus controlled content is a much more dangerous primitive than a generic corruption-only bug. (GitHub)
The scoring dispute matters more than the number
One of the most interesting parts of CVE-2025-66034 is that public sources do not agree on severity. The NVD page currently shows an NVD-assigned CVSS 3.1 score of 9.8 Critical with vector AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H, while the CNA entry from GitHub shows 6.3 Medium with vector AV:L/AC:H/PR:N/UI:R/S:C/C:N/I:H/A:L. Those are not close. They represent very different assumptions about exploitability and environment. (NVD)
That disagreement is not a clerical curiosity. It is operationally important. GitHub’s scoring treats the issue more like a user-assisted, workflow-dependent abuse of a local toolchain path. NVD’s enrichment treats it more like a network-reachable, low-friction RCE. Neither number should be copied blindly into a dashboard and called “truth.” The real question is whether your environment processes untrusted designspace input in an automated way and whether the output path intersects with something executable, deployable, web-served, or security-sensitive. In some environments, GitHub’s lower score will describe the practical risk better. In others, NVD’s harsher view will be closer to reality. (NVD)
Ubuntu’s security notice is useful here because it expresses the risk in concrete operational language. It says that if a user or automated system were tricked into extracting a specially crafted .designspace file, an attacker could write arbitrary files outside the target directory, resulting in remote code execution. That wording captures the mature middle ground: the bug is real, the path to impact is real, and deployment context decides how easy it is to cross from file write to RCE. (Ubuntu)
This is exactly how experienced security teams should read such a CVE. Severity is not a property of the identifier alone. It is the product of the primitive, the trigger path, the surrounding automation, and the place where attacker-controlled bytes finally land. The best defense programs do not ask only, “Is this Critical?” They ask, “Can this cross a trust boundary in our actual pipeline?” CVE-2025-66034 is a strong example of why that second question matters more. (NVD)
Where this bug becomes real in production
There are several plausible real-world paths to exposure. The first is the obvious one: any service or job that accepts user-supplied .designspace files and feeds them to fonttools varLib or fontTools.varLib.main(). The second is repository-based automation, where a pull request, package import, synced asset bundle, or design handoff introduces a malicious file that a trusted build worker later compiles. The third is indirect dependency usage, where a larger platform includes fontTools somewhere in its runtime, and the security team does not realize a font-processing path exists until a bulletin lands. The official documentation plus downstream vendor notices show that these scenarios are not far-fetched abstractions. (fontTools Documentation)
The IBM bulletins are especially valuable because they demonstrate downstream reach. IBM’s Maximo Application Suite Visual Inspection Component bulletin states that the component uses a fontTools dependency vulnerable to CVE-2025-66034 and identifies version 9.1.10 as the remediated release for affected 9.1.x versions. IBM’s Watson Speech Services Cartridge bulletin says fontTools is used in service runtimes there too, affecting versions 4.0.0 through 5.3.0, with remediation in 5.3.1. Those are the kinds of dependency-chain examples defenders should pay attention to. (IBM)
Distro packaging tells a similar story. Debian’s source package tracker shows the issue as fixed in newer suites while older ones remain vulnerable without a DSA in some tracks. Ubuntu’s USN-7917-1 says fixes were issued and specifically notes that CVE-2025-66034 affected Ubuntu 24.04 LTS, 25.04, and 25.10, with corresponding package versions published for remediation. That means this is not just a PyPI hygiene issue. Teams also need to inventory OS-packaged copies. (security-tracker.debian.org)
The practical takeaway is simple. You cannot answer “Are we exposed?” by checking only requirements.txt. You need to look at your base images, distro packages, service runtimes, vendor products, and any internal tool that invokes varLib directly. If your organization touches design automation, document conversion, brand asset processing, or font packaging, that inventory work is not optional. (security-tracker.debian.org)

Quick facts security teams can use
The table below condenses the most useful facts from upstream advisories, NVD, release notes, distro notices, and downstream vendor bulletins. (GitHub)
| Item | What matters |
|---|---|
| Vulnerable component | fontTools.varLib, especially the main() code path |
| Trigger | Processing a malicious .designspace file |
| Affected versions | >= 4.33.0 and < 4.60.2 |
| Fixed upstream version | 4.60.2 |
| Security change | Use only the basename of attacker-influenced filename values |
| Upstream issue framing | Arbitrary file write plus content injection, potentially leading to RCE |
| NVD CVSS | 9.8 Critical |
| GitHub CNA CVSS | 6.3 Medium |
| Ubuntu note | Affected 24.04 LTS, 25.04, 25.10; fixed package versions published |
| Debian note | Fixed in newer suites, older suites remain vulnerable in tracker state |
| Downstream examples | IBM Maximo Visual Inspection, IBM Watson Speech Services Cartridge |
Why file write becomes RCE in some environments
Not every arbitrary file write is immediately RCE. That is worth saying clearly. But defenders should not overcorrect and treat “not always RCE” as “mostly harmless.” In automated environments, a write primitive becomes extremely dangerous whenever output can land in one of four places: somewhere executable, somewhere imported, somewhere served, or somewhere trusted by the next step in a chain. That includes application code directories, Python module paths, plugin folders, template directories, build contexts, deployment bundles, and web-accessible locations that map content type to execution behavior. The upstream advisory’s mention of configuration overwrite and malicious-code injection is the key clue here. (GitHub)
There is also a subtler point. Even when the write does not become code execution, it may still become a high-confidence integrity incident. Corrupting dependencies, poisoning future builds, altering application assets, or modifying configuration in a way that changes later behavior can be enough to cause major security impact. Many teams overvalue only “instant shell” outcomes and undervalue persistent artifact poisoning. In CI/CD and build systems, persistence through poisoned output can be just as dangerous. (GitHub)
This is why the NVD vs. GitHub scoring split should not distract you from the engineering question. If your font-processing worker writes only to an isolated scratch directory with no execution path, no sensitive mounts, and no route into production, the blast radius is lower. If that same worker runs with broad filesystem access or shares state with packaging, deployment, or a web tier, the risk picture changes immediately. That is not theory. That is how modern software supply chains are built. (NVD)
Timeline and remediation, what the sources say
The GitHub advisory was published on November 28, 2025. The NVD record shows publication on the same date and later NVD analysis adding its own CVSS interpretation. Upstream release notes show 4.61.0 on November 28, 2025, with an explicit note that varLib.main now uses only the basename to prevent path traversal attacks and that this fixes CVE-2025-66034. They then show a backport release, 4.60.2, on December 9, 2025, specifically to carry the security fix without forcing downstream Python 3.9 users onto the broader support change in 4.61.0. That is a well-handled release response. (GitHub)
Ubuntu’s public notice followed on December 9, 2025, bundling CVE-2025-66034 together with the older fontTools XXE bug, CVE-2023-45139. That pairing is useful because it reminds teams that this is not the first time fontTools has crossed an input-trust boundary in security-relevant ways. Debian’s tracker later reflects a mixed state across suites, which again reinforces the need to inventory package provenance rather than assume “patched upstream” means “patched everywhere.” (Ubuntu)
By early 2026, downstream enterprise vendors were still publishing bulletins about affected products that embedded the vulnerable dependency. IBM’s March 2026 notice for Maximo Visual Inspection and February 2026 notice for Watson Speech Services are examples. That lag is typical in real ecosystems. It also explains why “we upgraded our direct dependency months ago” is not enough reassurance when large product stacks and container images are involved. (IBM)

What to look for in your own codebase
The first thing to identify is whether your organization uses fontTools at all. The second is whether it uses varLib, and the third is whether any untrusted or semi-trusted .designspace files can reach that path. Teams often stop at the first question and miss the real issue. A safe dependency used in one mode can be unsafe in another. This CVE is specific to a flow. You need both dependency inventory and usage inventory. (GitHub)
Start with the obvious static checks. Search for fontTools.varLib, varLib.main, python3 -m fontTools.varLib, and fonttools varLib across your repositories, build scripts, Dockerfiles, CI definitions, and internal tools. Search also for .designspace files under repos that feed artifact pipelines. The goal is not only to find the package. It is to find the trust boundary where a file becomes an action. That is where this vulnerability lives. (GitHub)
A simple shell audit can get you surprisingly far:
rg -n "fontTools\\.varLib|varLib\\.main|fonttools varLib|python3 -m fontTools\\.varLib" .
find . -type f -name "*.designspace"
python - <<'PY'
import importlib.metadata as m
try:
print("fonttools version:", m.version("fonttools"))
except Exception:
print("fonttools not installed in this environment")
PY
If you run containerized workloads, repeat the same logic inside images and base images, not only on the host. Many teams discover vulnerable copies in utility containers, worker images, or notebook environments long after their primary app dependencies were cleaned up. That is especially likely for libraries like fontTools that enter environments through design, visualization, ML, or reporting toolchains rather than core application code. (security-tracker.debian.org)
A defensive parser check for suspicious designspace input
If you cannot patch instantly, you should still reduce exposure immediately. One straightforward control is to reject .designspace input where filename-related fields contain directory separators, traversal markers, or obviously unsafe output names. That does not replace patching. It buys time and shrinks the most obvious abuse paths while you inventory and remediate. The upstream fix itself is basically enforcing this principle at the code level. (GitHub)
A small Python gate like the following can help in CI or intake services:
from pathlib import PurePosixPath, PureWindowsPath
import xml.etree.ElementTree as ET
def is_unsafe_filename(value: str) -> bool:
if not value:
return False
bad_markers = ["..", "/", "\\\\", "\\x00"]
if any(m in value for m in bad_markers):
return True
# also reject absolute-like names
if PurePosixPath(value).is_absolute():
return True
if PureWindowsPath(value).is_absolute():
return True
return False
def validate_designspace(path: str) -> list[str]:
tree = ET.parse(path)
root = tree.getroot()
findings = []
for elem in root.iter():
for attr in ("filename", "path"):
val = elem.attrib.get(attr)
if val and is_unsafe_filename(val):
findings.append(f"unsafe {attr}={val!r} in <{elem.tag}>")
return findings
# usage
issues = validate_designspace("candidate.designspace")
if issues:
raise SystemExit("Rejected designspace:\\n" + "\\n".join(issues))
This is intentionally conservative. In some legitimate workflows you may need to allow relative source references inside the document. But for output naming and for any path that influences generated artifact placement, strict validation is the right posture. The core lesson from CVE-2025-66034 is that filesystem intent must be normalized before use, not trusted because the surrounding file format “looks like data.” (fontTools Documentation)
Monitoring and detection, what defenders should actually instrument
The easiest thing to monitor is not the presence of the CVE but the behavior that exploitation would produce. Watch for fonttools varLib or python3 -m fontTools.varLib processes writing outside approved build output directories. Watch for newly created font-like or unexpected files in application directories, site-packages, deployment workspaces, or web-served locations during font-processing jobs. Watch for .designspace inputs containing traversal markers or output names with suspicious extensions. These are not perfect indicators, but they are practical ones. (GitHub)
If you have file integrity monitoring, this is a good case for targeted policy instead of generic alerting. A varLib process should have a very boring write profile. It should create artifacts only in a known output root. Anything outside that root is suspicious by default. That kind of narrow behavioral expectation is far more useful than waiting for a signature that mentions the CVE ID. (GitHub)
A simple Linux auditd rule set can help when you are investigating or temporarily hardening a worker:
# Replace /srv/font-build/out with your approved output root
auditctl -w /srv/font-build/out -p wa -k fontbuild_out
auditctl -a always,exit -F arch=b64 -S openat,creat,rename,unlink,unlinkat \\
-F exe=/usr/bin/python3 -k py_file_ops
On the application side, log the source of every .designspace file, the resolved output directory, the final artifact names after normalization, and the exact library version used. Good incident response begins with reconstructing a build chain, not with guessing which worker may have been tricked. That is doubly true for bugs like this one, where the interesting question is often “what trusted automation processed the file?” rather than “what internet-facing endpoint got popped?” (GitHub)
Patch first, but patch correctly
The clean upstream answer is to upgrade to fonttools 4.60.2 or later. That is the fixed version named by the advisory, NVD, and GitLab. If you are on a branch that can take 4.61.0 or later without compatibility pain, that also includes the security change. The important point is not to stop at a generic pip install -U and assume the fleet is done. You need to verify the exact version running in each place that processes designspace input. (GitHub)
A direct Python environment fix is straightforward:
python -m pip install --upgrade "fonttools>=4.60.2"
python - <<'PY'
import importlib.metadata as m
print(m.version("fonttools"))
PY
OS-packaged environments need separate handling. Ubuntu has published fixed package versions for affected releases in USN-7917-1. Debian’s tracker shows a mixed state by suite. Vendor appliances and commercial software stacks may need product-specific updates rather than package manager actions, as the IBM bulletins make clear. This is exactly why dependency remediation must be provenance-aware. PyPI, apt, containers, and product bundles move at different speeds. (Ubuntu)
If you cannot patch today
Some teams will be pinned by vendor compatibility, frozen images, change windows, or product support boundaries. If that is your situation, you still have useful controls. Run font-processing workloads with the minimum filesystem permissions possible. Mount a dedicated output directory. Avoid sharing writable application or package paths with the worker. Reject or quarantine any untrusted .designspace input. Separate build scratch space from deployment artifacts. The upstream fix strips path components for security reasons; your temporary mitigations should enforce the same boundary operationally. (GitHub)
Container isolation is especially effective here because the exploit path depends on where the file write can land. If the worker’s writable view is narrow and disposable, the primitive loses much of its value. A good temporary posture is a read-only root filesystem plus one explicitly mounted writable scratch directory, with no secrets, no deployment manifests, and no code paths in that mount. In other words, make “arbitrary file write” mean “write a useless file in a dead-end scratch volume.” (Ubuntu)
A secure wrapper pattern for varLib
When teams do need varLib, the safest pattern is to wrap it with explicit boundary checks rather than calling it directly on arbitrary input. The wrapper should verify the installed version, validate the incoming .designspace, run inside a restricted working directory, and record every generated output name after normalization. That turns a risky low-level call into an auditable operation. The official fix tells you what invariant matters: final output naming must not carry directory intent from attacker-controlled input. (GitHub)
A wrapper skeleton can look like this:
from pathlib import Path
import importlib.metadata as m
import subprocess
import tempfile
import shutil
MIN_SAFE = (4, 60, 2)
def parse_version(v: str):
return tuple(int(x) for x in v.split(".")[:3])
def ensure_safe_fonttools():
version = m.version("fonttools")
if parse_version(version) < MIN_SAFE:
raise RuntimeError(f"Unsafe fonttools version: {version}")
def build_varfont(designspace: str, outdir: str):
ensure_safe_fonttools()
findings = validate_designspace(designspace)
if findings:
raise RuntimeError("Rejected designspace:\\n" + "\\n".join(findings))
work = tempfile.mkdtemp(prefix="varlib-")
try:
safe_out = Path(outdir).resolve()
safe_out.mkdir(parents=True, exist_ok=True)
subprocess.run(
["python3", "-m", "fontTools.varLib", designspace, "--output-dir", str(safe_out)],
cwd=work,
check=True,
)
finally:
shutil.rmtree(work, ignore_errors=True)
This does not magically eliminate every risk in your build chain, but it enforces the right habits. Verify version. Validate input. Narrow the working directory. Keep output rooted. Treat design artifacts as untrusted unless proven otherwise. CVE-2025-66034 is the kind of bug that punishes teams for skipping exactly those steps. (GitHub)
Related CVEs that make the same lesson louder
The most relevant sibling is CVE-2023-45139, another fontTools flaw. NVD and GitHub’s advisory describe it as an XXE issue in the subsetting module that allowed attackers to resolve arbitrary entities when parsing a candidate font with an SVG table, enabling local file inclusion or server-side web requests. That issue was fixed in 4.43.0. The significance here is not that the bugs are identical. It is that both incidents show fontTools operating across file and parser trust boundaries that many teams would not have classified as security-critical until a CVE forced the issue. (NVD)
A broader related pattern appears in CVE-2025-4517, where NVD describes arbitrary filesystem writes outside an extraction directory when untrusted tar archives are extracted with certain tarfile filter settings in Python 3.12+. That is a different component and a different format, but the security lesson is familiar: a format that looks like transport data smuggles path semantics into an automated workflow, and suddenly a convenience API becomes a filesystem boundary problem. (NVD)
The same idea shows up again in CVE-2026-32060, where NVD describes a path traversal flaw in OpenClaw’s apply_patch allowing file writes or deletes outside the configured workspace directory when sandbox containment is absent. Different ecosystem, same engineering truth: if an automation surface can influence filenames or paths, then it is part of your attack surface, not just part of your feature surface. (NVD)
What ties these together is not a vendor, language, or product category. It is the erosion of the boundary between “input data” and “instructions about the filesystem.” Once that erosion happens inside a trusted automated system, the right severity question is not “How fancy is the exploit?” It is “What authority did we accidentally grant to a structured file?” That is the right lens for CVE-2025-66034 too. (NVD)
What red teamers and bug bounty hunters should care about
For offensive-minded readers, the interesting part of CVE-2025-66034 is not just the primitive but the deployment hunt. The best targets are not generic developer laptops. They are systems that automatically process third-party design or asset files and then move outputs into places the rest of the stack trusts. That could be a managed font service, a CI pipeline for design assets, an internal branding generator, a content platform, or an ML/reporting pipeline that includes fontTools indirectly. The vulnerability itself is upstream-documented; the real work is identifying the trust chain around it. (GitHub)
For defenders reading this with a bug bounty mindset, that is also the right way to prioritize. Ask which services transform user-controlled design or font-related inputs. Ask which repositories allow design assets from contractors, customers, or external collaborators. Ask which background workers have broad write permissions because “they just generate files.” Those are exactly the systems where a CVE like this stops being a library hygiene issue and becomes an environment issue. (fontTools Documentation)
For teams already doing continuous validation, the natural place for a platform like Penligent is not as a magical “AI fixes CVEs” claim, but as a way to operationalize the questions CVE-2025-66034 forces you to ask. Penligent presents itself as an AI-powered penetration testing platform, and the more relevant operational use here is controlled verification: identifying whether a target environment processes untrusted artifacts, tracing where generated files can land, and validating whether a trust-boundary assumption really holds in practice. (Penligent)
That matters because this CVE is environment-sensitive. Static SBOM matching will tell you the vulnerable version is present. It will not tell you whether .designspace input is reachable, whether a worker has writable access to sensitive paths, whether outputs can become executable, or whether your compensating controls actually contain the blast radius. A validation-oriented workflow can answer those questions far better than a dependency list alone. That is where an AI-assisted testing platform can be useful without overselling what it does. (NVD)
What a strong response looks like this week
A strong short-term response to CVE-2025-66034 is not complicated, but it does need to be deliberate. Identify every place fontTools is installed. Identify every place varLib is used. Patch PyPI copies to 4.60.2 or later. Apply distro and product updates where relevant. Reject untrusted .designspace files until the fleet is remediated. Restrict output directories. Audit recent font-processing jobs for suspicious writes or unexpected artifacts. Preserve logs that tie input files to output paths. That is enough to turn this from an ambiguous “maybe medium, maybe critical” issue into a concrete, managed engineering task. (GitHub)
A weak response is equally easy to describe. It looks like updating one direct dependency, ignoring distro packages, leaving workers overprivileged, assuming design files are benign, and treating the NVD–GitHub CVSS split as a reason to postpone action. That is how modern automation bugs keep slipping through mature organizations. Not because the fix was hard, but because the boundary was culturally invisible until it failed. (NVD)
Final assessment
CVE-2025-66034 is not interesting because it happens to involve fonts. It is interesting because it captures a recurring security truth in modern systems: the more automation you build around structured files, the more those files stop being passive content and start becoming control surfaces. In fontTools.varLib, a filename inside a .designspace document was trusted too far. That trust error turned a routine build flow into an arbitrary file write primitive, and in the right environment, into RCE. (GitHub)
The good news is that this is one of the clearer fixes you will see all year. The vulnerable range is public. The patch is public. The release notes are public. Distro notices are public. Downstream enterprise bulletins are public. The real challenge is not understanding what the bug is. It is being honest about where your own pipelines still treat design and artifact inputs as “harmless data” while giving them far too much authority over the filesystem. That is the real lesson of CVE-2025-66034, and it is bigger than a single package. (GitHub)
Authoritative references and related reading
- NVD entry for CVE-2025-66034. (NVD)
- Upstream GitHub security advisory, GHSA-768j-98cg-p3fv. (GitHub)
- Upstream patch commit showing the
basenamefix. (GitHub) fontToolsrelease notes for4.61.0and backport4.60.2. (GitHub)- Ubuntu USN-7917-1, package remediation details. (Ubuntu)
- Debian security tracker for CVE-2025-66034 and package status. (security-tracker.debian.org)
- GitLab advisory database entry for fixed version and impact summary. (GitLab Advisory Database)
- IBM Maximo Application Suite Visual Inspection bulletin. (IBM)
- IBM Watson Speech Services Cartridge bulletin. (IBM)
- CVE-2023-45139,
fontToolsXXE in the subsetting module. (NVD) - CVE-2025-4517, Python
tarfilearbitrary filesystem write outside extraction directory. (NVD) - CVE-2026-32060, OpenClaw
apply_patchpath traversal outside workspace boundaries. (NVD) - CVE-2025-66034, When fontTools varLib Turns a Designspace File Into a Write Primitive. (Penligent)
- CVE-2025-66034, Why a Font Build Tool Turned Into a Real Code Execution Risk. (Penligent)
- What Is Penetration Testing? The Engineering of Verified Risk. (Penligent)
- CVE-2025-4517, The Python Tar Extraction Bug That Breaks Trust Boundaries in Real Automation. (Penligent)
- OpenClaw Security, What It Takes to Run an AI Agent Without Losing Control. (Penligent)