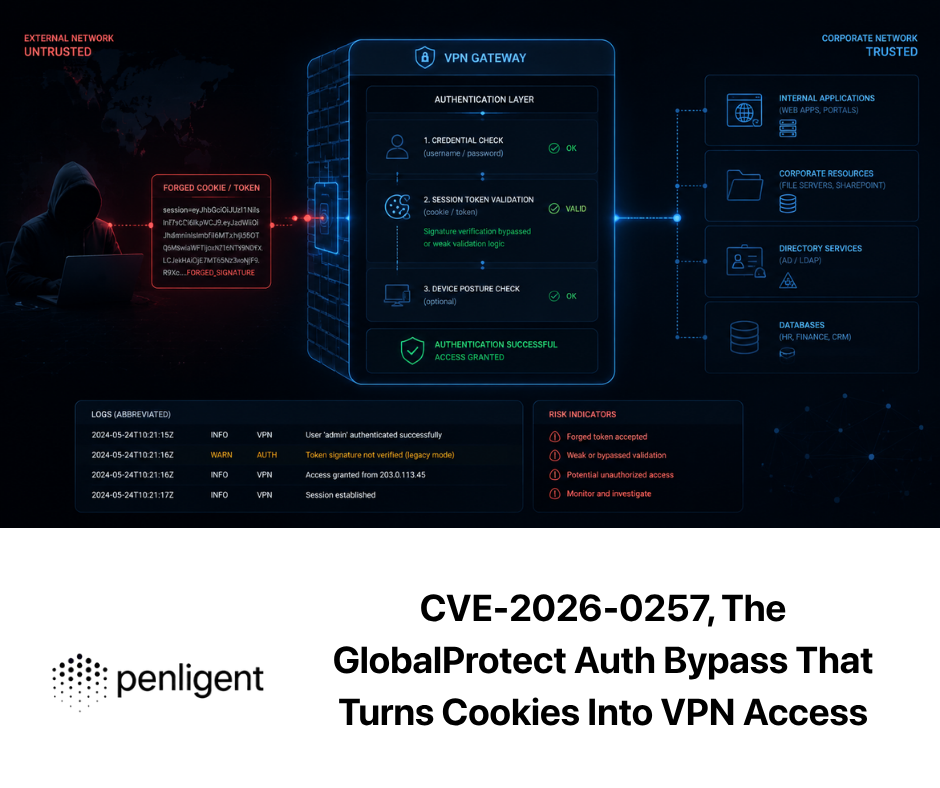
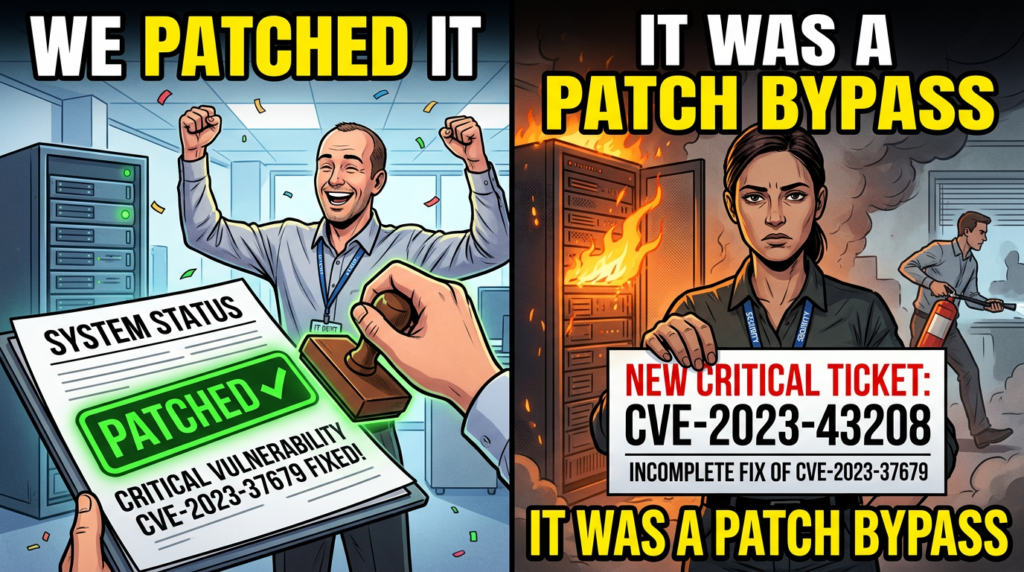
If you only remember one thing about CVE-2023-43208, make it this: it’s a pre-auth remote code execution bug in NextGen Healthcare Mirth Connect affecting versions before 4.4.1, and it exists because an earlier critical issue, CVE-2023-37679, was fixed incompletely—creating a second door after the first one was “patched.” (NVD)
That “patch-bypass origin story” is not trivia. It changes how you should respond operationally:
- It raises the probability of partial patch coverage across environments.
- It increases the chance of false confidence if your org “already patched the prior CVE.”
- It strongly suggests you need verification, not just change tickets.
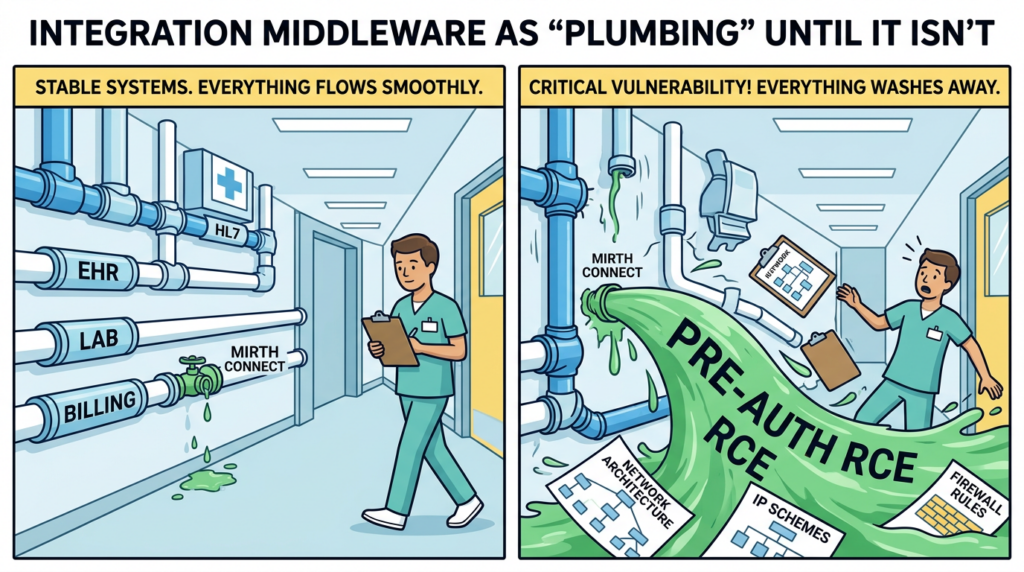
This article is written for people who have to defend real systems: security engineers, SOC analysts, pentesters who do responsible verification, and anyone inheriting a healthcare integration stack where Mirth Connect quietly sits on the network like plumbing—until it becomes a breach headline.
What CVE-2023-43208 is, in plain terms
CVE-2023-43208 is described as a vulnerability in NextGen Healthcare Mirth Connect حيث إلغاء تسلسل البيانات غير الموثوق بها can lead to unauthenticated remote code executionو versions prior to 4.4.1 are affected. NVD explicitly notes it is caused by the incomplete patch of CVE-2023-37679. (NVD)
Two additional practical details matter in incident response:
- Pre-auth means no credentials are required if the vulnerable endpoint is reachable.
- “Integration middleware” tends to be deployed in ways that make it reachable from places it shouldn’t be—internal segments with broad trust, exposed admin consoles, or systems reachable from vendor networks.
Horizon3’s public disclosure summarizes the impact plainly: Mirth Connect versions prior to 4.4.1 are vulnerable to unauthenticated RCE, and the recommended action is to upgrade. (Horizon3.ai)
Why this vulnerability keeps showing up in security operations
A lot of critical CVEs are “patch and move on.” CVE-2023-43208 is the opposite: it’s a case study in why organizations relapse into the same risk.
Patch bypasses are governance poison
When a vulnerability is a bypass of a previous fix, you get these common failure modes:
- “We patched that already” becomes a dangerous assumption
- Asset owners stop paying attention because the name looks familiar
- Compensating controls get rolled back because the ticket is closed
NHS England’s cyber alert is unusually direct for a public sector bulletin: it highlights that CVE-2023-43208 is a patch bypass of CVE-2023-37679, and warns it could allow unauthenticated RCE. (هيئة الخدمات الصحية الوطنية بإنجلترا الرقمية)
CISA later added CVE-2023-43208 to its catalog of known exploited vulnerabilities, which is a strong signal about prioritization and timelines for remediation in many environments. (CISA)
Mirth Connect context, why the “plumbing” matters
Mirth Connect is widely used as an integration engine, especially in healthcare contexts where it brokers and transforms messages between systems.
From a defender’s perspective, integration engines are risky for three reasons:
- They often have high-privilege connectivity to multiple backend systems.
- They are expected to accept and parse complex structured data.
- They tend to be operationally critical, which discourages aggressive hardening and rapid change.
So when an integration service becomes pre-auth RCE-capable, the blast radius is rarely “just one server.” It’s identity, adjacent systems, data pipelines, and the trust relationships the middleware was designed to simplify.
Root cause category, unsafe deserialization and why it’s still everywhere
NVD categorizes CVE-2023-43208 under إلغاء تسلسل البيانات غير الموثوق بها, and Huntress describes it as RCE caused by unsafe deserialization, framed around a malicious payload being processed before proper authentication checks. (NVD)
You don’t need to memorize the internals to defend against it, but you do need to internalize the defender’s lesson:
If the application parses complex attacker-controlled objects pre-auth, “input validation” is rarely enough. You need isolation, upgrades, and detection that focuses on execution behavior.
Why deserialization RCE is operationally nasty
- The exploit surface often looks like “normal” XML or serialized content.
- WAF rules can be brittle because payloads vary.
- The strongest detection signals tend to be downstream: process execution, file writes, unusual outbound connections, or exploitation patterns hitting specific endpoints repeatedly.
Relationship to CVE-2023-37679, the incomplete fix that created CVE-2023-43208
NVD’s record is explicit: CVE-2023-43208 is caused by an incomplete patch من CVE-2023-37679. (NVD)
NHS England also calls it a patch bypass of CVE-2023-37679. (هيئة الخدمات الصحية الوطنية بإنجلترا الرقمية)
Horizon3 describes CVE-2023-43208 as unauthenticated RCE in Mirth Connect and points users to upgrade to 4.4.1. (Horizon3.ai)
This matters because “incomplete fix” is not a single bug, it’s a pattern:
- A fix might block one gadget chain but leave others.
- A denylist might stop one class but not a sibling class.
- A patch might add checks in one code path but not the alternate route.
In practical terms, defenders should treat the fix line 4.4.1 as the meaningful boundary for this specific risk, not “we applied a hotfix last time.” (NVD)
Impact, what attackers get if they win
At the highest level: remote code execution on the server.
In real environments, the attacker value often looks like:
- Execution as the service account running Mirth Connect
- Access to configuration files, channel definitions, credentials, or API keys stored in the environment
- Lateral movement via trusted integration routes
And because Mirth Connect sits at the junction of systems, post-exploitation can quickly shift from “server compromise” to “pipeline compromise.”
CISA’s decision to add CVE-2023-43208 to its KEV workflow signals the vulnerability is not only theoretically severe but relevant to exploitation realities that matter for federal and enterprise timelines. (CISA)
How to determine if you are exposed, safely
You want to answer three questions:
- Do we run Mirth Connect anywhere
- Are any instances internet-facing or reachable from untrusted segments
- Are they below 4.4.1
Asset discovery that works in messy environments
Start with what you already have:
- CMDB entries that mention “Mirth” or “NextGen”
- Container images and compose files
- VM templates used by integration teams
- Reverse proxy configs that route to Mirth admin UI
Then verify on the host.
Check version on the server
Exact commands vary by install method, but the goal is consistent: get the installed Mirth Connect version and compare it to the fixed line 4.4.1. NVD and multiple vendor trackers note versions before 4.4.1 are affected. (NVD)
If you’re doing this at scale, build a small inventory script that collects:
- hostname
- listening ports
- detected version
- whether it’s reachable from the internet or vendor networks
Exposure check without exploitation
A safe exposure check focuses on reachability, not payloads:
- Is the service reachable externally
- Are admin endpoints reachable
- Are there reverse proxies that accidentally publish internal routes
A simple network check can map externally reachable ports, but do not assume “port closed” equals “not reachable” in segmented networks.
# Example reachability scan, do not treat as vulnerability confirmation
nmap -Pn -sS -sV -p 80,443,8080,8443 <target-ip-or-range>
This only tells you the surface. It does not confirm the CVE, and it should not be sold as such.
Detection, what to look for in logs and telemetry
Because CVE-2023-43208 is an RCE class issue tied to deserialization, detection should prioritize:
- unusual request patterns hitting specific app endpoints
- suspicious serialization or XML-related indicators
- post-exploitation behavior from the Mirth process tree
Huntress describes the attack mechanism at a high level as malicious XML processed without appropriate pre-auth gating, enabling command execution. (huntress.com)
Application and reverse proxy logs
Look for:
- bursts of requests to uncommon endpoints
- repeated failed requests followed by success
- odd content types or payload sizes
- sudden changes in response size patterns
A practical logging approach:
- Ensure reverse proxy logs include request path, response code, size, user agent, source IP
- Correlate to server process execution events
Endpoint telemetry, the strongest signals
If you have EDR:
- Watch for the Mirth Java process spawning shells
- Watch for creation of temp files or payload drops
- Watch for suspicious outbound connections initiated by the Mirth host
Example Splunk query, process execution pivot
This is a generic pattern you adapt to your field names. It’s not CVE-specific, it’s exploitation-behavior-specific.
index=edr (parent_process_name="java" OR process_name="java")
| search (command_line="*bash*" OR command_line="*cmd.exe*" OR command_line="*powershell*" OR command_line="*curl*" OR command_line="*wget*")
| stats earliest(_time) as firstSeen latest(_time) as lastSeen values(process_name) values(command_line) by host, user, parent_process_name
| sort - lastSeen
Example KQL, suspicious child processes from Java
DeviceProcessEvents
| where InitiatingProcessFileName =~ "java.exe" or InitiatingProcessFileName =~ "java"
| where FileName in~ ("cmd.exe","powershell.exe","bash","sh","curl","wget")
| project Timestamp, DeviceName, InitiatingProcessFileName, InitiatingProcessCommandLine, FileName, ProcessCommandLine, AccountName
| order by Timestamp desc
Network detections and WAF, useful but not sufficient
WAF and IDS can help you catch broad sweeps, but payload variance makes hard signatures fragile. You’ll get more mileage by correlating:
- inbound anomaly spikes
- followed by outbound connections
- followed by suspicious process activity
Quick triage table, signals that should trigger escalation
| الإشارة | ما أهمية ذلك | What to do next |
|---|---|---|
| Publicly reachable Mirth Connect below 4.4.1 | Known critical pre-auth RCE exposure | Isolate, patch, check for compromise (NVD) |
| Java spawning shell utilities | Strong exploitation indicator | Pull process tree, capture memory if needed |
| Unusual outbound from Mirth server | Common post-exploitation step | Block egress, hunt for persistence |
| Repeated requests to odd endpoints | Exploit probing or automation | Correlate with IDS/WAF and EDR |
Remediation, what actually reduces risk fast
The real fix
الترقية إلى Mirth Connect 4.4.1 or later. Horizon3 explicitly advises upgrading to 4.4.1, and NVD states versions before 4.4.1 are vulnerable. (Horizon3.ai)
Immediate compensating controls, when you can’t patch today
If you have to buy time:
- إزالة التعرض للإنترنت If it must be reachable, put it behind VPN or a strongly authenticated gateway.
- Restrict admin interfaces Only allow access from dedicated management subnets.
- Add network segmentation and egress controls Many RCE chains turn into “download payload + call home.” Egress filtering can cut off the second stage.
- Log hardening Increase logging on reverse proxy and host telemetry so you can answer “was it hit” later.
Post-patch verification that avoids false confidence
Because this CVE is a patch-bypass story, verification matters. Your objective is to show:
- version is updated everywhere
- no lingering exposed paths exist
- telemetry coverage is adequate
At minimum, store evidence:
- version output
- configuration snapshot showing network restrictions
- change ticket references
The “highest intent” search terms people actually use around this CVE, and what they signal
You asked for the highest-click, highest-intent phrasing people gravitate toward. We can’t see Google CTR directly from the public web, but we can reliably infer common high-intent query language by looking at the dominant authoritative pages and how they title the issue:
- “Mirth Connect unauthenticated RCE” appears directly in Horizon3’s disclosure framing. (Horizon3.ai)
- “Deserialization of untrusted data” is the NVD classification and shows up across vulnerability databases. (NVD)
- “Known exploited vulnerabilities” and “KEV catalog” language is driven by CISA’s alert and is a strong prioritization keyword. (CISA)
- “Patch bypass of CVE-2023-37679” wording is explicitly used by NHS England and NVD’s history, making it a high-signal search phrase for defenders validating prior patch work. (هيئة الخدمات الصحية الوطنية بإنجلترا الرقمية)
- “Pre-auth RCE” and “unsafe deserialization” is how Huntress explains the mechanism for practitioners. (huntress.com)
If you’re mapping user intent, it usually falls into three buckets:
- Am I exposed: affected versions, how to check, what ports
- How urgent: exploited in the wild, KEV, patch bypass
- How to detect: SIEM rules, IOCs, process behaviors
This article is structured to answer those with minimal fluff.
A safe approach to verification in offensive testing programs
If you run an internal red team or authorized pentest, treat this as a classic case where “prove exposure without turning it into an incident.”
A responsible workflow looks like:
- Confirm version and reachability first
- Validate control-plane restrictions
- Use detection-driven testing instead of exploit-heavy testing
- Capture evidence and remediation guidance
Avoid dropping or running arbitrary payloads in production-like healthcare integration environments unless you have explicit approvals and a rollback plan.
When a vulnerability is pre-auth RCE and widely operationally relevant, the expensive part is rarely reading the CVE—it’s the end-to-end workflow: asset discovery, exposure validation, evidence capture, and repeatable reporting that doesn’t collapse into screenshots and tribal knowledge.
Penligent is built around that exact workflow: you can model targets, exposure paths, and verification tasks as a repeatable playbook, then produce a defensible evidence trail that supports both remediation and governance.
Just as important for patch-bypass CVEs like this one: teams need a way to verify the patch boundary across real environments, not just trust that “the earlier CVE was addressed.” That verification loop—continuous exposure checking, scoped validation, and reporting—is where an AI-assisted penetration testing platform can remove a lot of manual friction without turning production into a testing sandbox.
Key facts recap table, keep this in your runbook
| البند | القيمة |
|---|---|
| مكافحة التطرف العنيف | CVE-2023-43208 (NVD) |
| المنتج | NextGen Healthcare Mirth Connect (NVD) |
| الإصدارات المتأثرة | Versions before 4.4.1 (NVD) |
| التأثير | Unauthenticated remote code execution (NVD) |
| Root class | Deserialization of untrusted data, unsafe deserialization framing in practitioner writeups (NVD) |
| Related CVE | Patch bypass or incomplete fix of CVE-2023-37679 (NVD) |
| Prioritization signal | Added to CISA known exploited vulnerabilities catalog alerts (CISA) |
المراجع
- NVD entry for CVE-2023-43208 (NVD)
- CISA alert adding CVE-2023-43208 to the Known Exploited Vulnerabilities catalog (CISA)
- NHS England cyber alert on the Mirth Connect vulnerability (هيئة الخدمات الصحية الوطنية بإنجلترا الرقمية)
- Horizon3.ai disclosure on NextGen Mirth Connect RCE (Horizon3.ai)
- Tenable CVE record for CVE-2023-43208 (Tenable®)
- Huntress threat library page for CVE-2023-43208 (huntress.com)
- CVE-2023-43208 and the Patch Bypass That Turned Mirth Connect Into a High-Priority Internet-Facing RCE (بنليجنت)
- CVE-2023-43208, The Mirth Connect Pre-Auth RCE That Turned Integration Plumbing Into an Internet-Grade Incident (بنليجنت)
- Claude Code Security Breaks the Old Model of Code Scanning, includes a section referencing CVE-2023-43208 as a patch-bypass archetype (بنليجنت)