The search for “CVE 2026” looks broad on the surface, but the people typing it into Google are usually not looking for an encyclopedia of numbers. They are trying to answer a more urgent set of questions. Which 2026 vulnerabilities are already being exploited. Which ones matter beyond a headline. Which flaws can realistically turn into initial access, privilege escalation, control-plane takeover, or durable foothold. And which fixes deserve attention before the next change window. That is the lens this article uses.
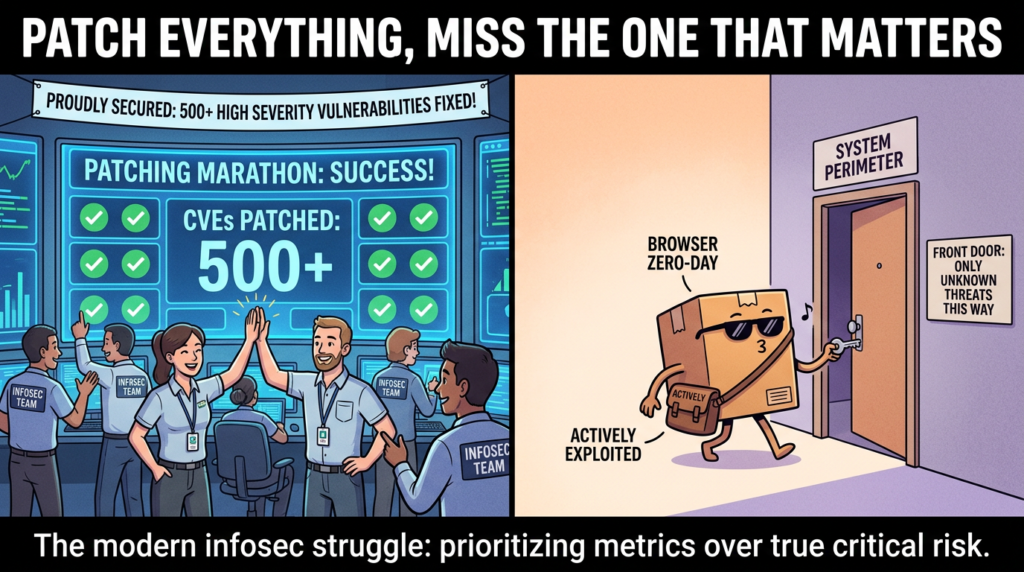
There is another reason to avoid a shallow list. Public vulnerability volume keeps climbing, but operational attention does not. In practice, security teams do not lose because they failed to read one more advisory. They lose because they treated every CVE as equal, patched by score instead of exploit reality, and discovered too late that the issues that changed their week were not generic application bugs but control-plane flaws, browser zero-days, chipset bugs under targeted exploitation, and vulnerable automation layers sitting closer and closer to security-sensitive workflows. CISA’s Known Exploited Vulnerabilities program exists for exactly this reason, and the KEV catalog itself remains one of the clearest public indicators that a vulnerability has crossed the line from “important” to “operationally urgent.” (CISA)
No public dataset exposes the exact cross-site click-through rate for “CVE 2026,” so any article claiming precise CTR winners would be guessing. What we can say, based on recurring March 2026 vendor bulletins, NVD entries, KEV additions, and repeated headline patterns across current coverage, is that the hottest adjacent query cluster right now revolves around Cisco SD-WAN, Android and Qualcomm, VMware Aria Operations, and browser exploitation. The names that keep surfacing are CVE-2026-20127, CVE-2026-20122, CVE-2026-20128, CVE-2026-21385, CVE-2026-22719, and CVE-2026-2441. Those are not just popular strings. They represent the real center of gravity for 2026 vulnerability attention so far: exposed management planes, actively exploited edge infrastructure, mobile ecosystem patch lag, and browser exploitation with immediate end-user reach. (NVD)
The CVE 2026 query cluster that actually matters
The phrase “CVE 2026” is too generic to be useful by itself. The more realistic reading of current public interest is a cluster of related searches. Security engineers are clearly gravitating toward several themes.
One theme is active exploitation of enterprise control planes. Cisco SD-WAN dominated coverage after the disclosure of CVE-2026-20127, a maximum-severity authentication bypass affecting Cisco Catalyst SD-WAN Controller and Manager. Tenable summarized the flaw as allowing a remote unauthenticated attacker to send crafted requests, log in as a high-privileged user, and modify SD-WAN fabric configuration. CISA responded with Emergency Directive 26-03, treating the risk as imminent to federal networks. SecurityWeek then reported widespread exploitation attempts from numerous unique IPs and observed webshell deployment activity, which is exactly the kind of post-disclosure escalation defenders fear. (Tenable®)
A second theme is mobile and chipset-layer risk under targeted exploitation. Google’s March 2026 Android Security Bulletin states that there are indications CVE-2026-21385 may be under limited, targeted exploitation. NVD also reflects that this issue is in CISA’s KEV catalog. That combination matters because it means the flaw is not only published; it has crossed into the narrower and more operationally serious category of exploited vulnerability management. (مشروع أندرويد مفتوح المصدر)
A third theme is virtualization and cloud-operations control-plane exposure. Broadcom’s advisory for VMware Aria Operations says CVE-2026-22719 is a command injection vulnerability that can be exploited by an unauthenticated actor to execute arbitrary commands, potentially leading to remote code execution, during support-assisted product migration. Broadcom later noted awareness of reports of exploitation in the wild, even though it could not independently confirm them. CISA’s KEV catalog now includes the issue, which is often the more practical signal that patching should move from “planned” to “now.” (بوابة الدعم)
A fourth theme is browser exploitation as a still-dominant entry vector. Google’s Chrome release notes for February 13, 2026 explicitly state that an exploit for CVE-2026-2441 exists in the wild. The bug is a use-after-free in CSS. Browser issues deserve attention far beyond their standalone description because a browser is already an exposed parser attached to user workflows, untrusted content, and identity-rich sessions. Once a bug like this is exploited, its value is not limited to code execution in a sandbox. Its value lies in where it can lead next. (Chrome Releases)
The fifth theme is newer but important: AI framework vulnerabilities are now part of the mainstream CVE conversation. GitHub’s advisory for Microsoft Semantic Kernel tracks CVE-2026-26030 and identifies it as CWE-94, improper control of code generation. Whether or not every team uses Semantic Kernel specifically, the advisory is a sign of a broader change: CVEs are increasingly landing in the libraries that orchestrate retrieval, tools, filters, prompts, and code-adjacent behavior for AI-enabled systems. That widens the definition of what counts as a meaningful attack surface in 2026. (جيثب)
The most important CVE 2026 stories so far
Chrome zero-day exploitation, CVE-2026-2441
Google’s stable channel update from February 13, 2026 lists a single security fix: CVE-2026-2441, a high-severity use-after-free in CSS. The most consequential line in the release note is not the weakness category. It is the sentence saying Google is aware that an exploit exists in the wild. That single statement immediately moves the vulnerability out of the “we should patch soon” bucket and into “the attack surface is already active.” (Chrome Releases)
This is a useful place to reset how severity is interpreted. A browser bug with active exploitation usually matters more than a long list of critical issues sitting unused in software that is not internet-facing, is heavily segmented, or has low-value operational reach. Browsers process hostile inputs by design. They sit at the boundary between human trust and attacker-controlled content. A browser exploit can become the first stage of a chain that targets credentials, sessions, enterprise identities, or privileged endpoints already authenticated into cloud dashboards and admin tools.
The larger lesson from CVE-2026-2441 is that the browser is still one of the cleanest cross-environment entry points in the industry. Teams sometimes over-focus on appliance CVEs and under-focus on user-facing software because appliances feel more “infrastructure-critical.” In reality, browsers remain one of the fastest ways to move from a crafted web page to meaningful organizational risk, especially when the victim already has access to sensitive SaaS or internal control planes. (Chrome Releases)
For defenders, browser vulnerability handling in 2026 should look less like monthly hygiene and more like emergency operational discipline. Track stable-channel releases closely. Validate that browser auto-update is working on unmanaged endpoints. Confirm update success rather than trusting policy. Treat high-risk populations differently, including administrators, executives, and anyone who regularly accesses production consoles or identity providers.
Android and Qualcomm exploitation, CVE-2026-21385
If Cisco represents the enterprise edge story of 2026 so far, CVE-2026-21385 represents the mobile ecosystem story. Google’s March 2026 Android Security Bulletin says there are indications this Qualcomm-related issue may be under limited, targeted exploitation. NVD additionally notes that the CVE is listed in CISA’s KEV catalog. Those are strong public signals that the bug should not be treated as routine mobile background noise. (مشروع أندرويد مفتوح المصدر)
This issue matters for several reasons. First, mobile vulnerabilities tend to be underestimated by organizations that still mentally separate “corporate infrastructure” from “employee devices.” That distinction is not holding up. Phones are identity devices, MFA devices, email devices, collaboration devices, and increasingly privileged workflow devices. They are not side channels anymore. They are part of the trust fabric.
Second, chipset and OEM dependencies make remediation slower and messier than software-only patching. Google’s bulletin explains the two Android patch levels for March 2026 and clarifies that devices with security patch levels of 2026-03-01 or 2026-03-05 are protected against the associated issues, depending on applicable components. That sounds straightforward until it hits ecosystem reality. Pixel devices update quickly. The broader Android population depends on OEM integration cycles, carrier testing, geographic rollout, and sometimes hardware support boundaries. That delay creates the practical exploitation window. (مشروع أندرويد مفتوح المصدر)
Third, the bulletin covers much more than the Qualcomm issue alone. Google’s March 2026 bulletin includes a critical RCE in the System component, CVE-2026-0006, alongside many other vulnerabilities. That is a reminder that single-CVE headlines can obscure the more important operational fact: patch bundles often close multiple paths at once, and organizations that delay because they are watching only the headline vulnerability may leave several other exploitable conditions untouched. (مشروع أندرويد مفتوح المصدر)
The practical challenge is visibility. Many enterprises can accurately inventory laptops and servers, but not Android security patch levels across the real fleet, especially on BYOD or hybrid models. A targeted mobile exploit does not need mass prevalence to matter. It needs the right target and the right access chain.
Cisco SD-WAN, CVE-2026-20127 and the follow-on exploitation story
CVE-2026-20127 is one of the clearest examples this year of why the phrase “management plane” should immediately raise priority. Tenable describes the flaw as a critical authentication bypass affecting Cisco Catalyst SD-WAN Controller and Manager, allowing a remote unauthenticated attacker to log in as a high-privileged user and modify SD-WAN configuration. The NVD entry similarly describes improper peering authentication that lets an attacker log in to an affected controller as an internal high-privileged account. (Tenable®)
The story became more important after disclosure, not less. Cisco’s bulletin triggered an emergency directive from CISA. SecurityWeek reported that watchTowr saw exploitation attempts from numerous unique IP addresses and threat actors deploying webshells, with a notable spike in activity on March 4. Tenable later updated its analysis to note that Cisco had also confirmed in-the-wild exploitation of two additional SD-WAN Manager vulnerabilities, CVE-2026-20122 and CVE-2026-20128. Help Net Security similarly reported Cisco’s recommendation to upgrade to fixed releases after confirmation of exploitation activity. (Tenable®)
This cluster matters because it illustrates a pattern defenders keep relearning. A control-plane vulnerability is rarely just “one more appliance bug.” It can become a trust collapse event. SD-WAN systems do not merely serve traffic. They define policy, route behavior, segmentation, and connectivity assumptions across the fabric. If the attacker reaches that layer, the effect is not a single shell on a box. The effect is the ability to influence how the network behaves.
That is why CVE-2026-20127 deserves more attention than a normal CVSS 10 story. It is not the number. It is the blast radius. A remote unauthenticated issue on a control system that governs connectivity is almost always worth more to an attacker than a higher-friction exploit deeper in the stack. The same logic explains why CISA treated the issue as an imminent risk to federal networks. (Tenable®)
The follow-on lesson from CVE-2026-20122 and CVE-2026-20128 is also important. Attackers and defenders do not operate on single-advisory timelines. Once a platform is under intense public attention, adjacent flaws become more interesting, not less. If an organization patches the headline CVE but leaves the surrounding management plane in a weak state, it can still get compromised by a related issue or a variant path discovered during the rush.

VMware Aria Operations, CVE-2026-22719 and why migration paths are dangerous
Broadcom’s advisory for CVE-2026-22719 is unusually instructive. The vendor describes the flaw as a command injection vulnerability in VMware Aria Operations. A malicious unauthenticated actor may exploit it to execute arbitrary commands, potentially leading to remote code execution, while support-assisted product migration is in progress. Broadcom rates the maximum CVSSv3 score at 8.1 and provides both fixed versions and workaround references. The advisory later notes awareness of reports of potential exploitation in the wild, although Broadcom says it could not independently confirm those reports. (بوابة الدعم)
The reason this vulnerability is strategically important is not only that it can produce RCE. It is where the vulnerable logic lives. Migration workflows, support-assisted operations, maintenance helpers, import-export routines, and backup-restore pipelines are historically fertile ground for serious vulnerabilities because they often operate with elevated trust, broad access, and unusual parsing behavior. They are also harder for defenders to model mentally because they are not part of everyday user activity.
CVE-2026-22719 belongs to a family of enterprise bugs that are especially dangerous in large organizations: the “rare path, high privilege, weak scrutiny” bug. These flaws often do not show up first in routine user testing because the affected features are used intermittently. But when they are used, they sit near privileged operations, sensitive data, or transitional control states. That combination is exactly what makes them valuable.
Broadcom’s response matrix shows the affected product families and fixed versions, including VMware Aria Operations 8.18.6 and VMware Cloud Foundation Operations 9.0.2.0. For security teams, that is the actionable part. The advisory is not just a warning; it is a patch map. Too many organizations stop at reading the synopsis and never complete version-to-asset mapping, which is the part that determines whether anything actually changes in the environment. (بوابة الدعم)
AI framework risk enters the CVE mainstream, CVE-2026-26030
One of the most interesting shifts in 2026 is that AI-adjacent vulnerabilities are no longer only discussed as abstract “prompt injection” thought pieces. They are showing up in standard vulnerability channels. GitHub’s advisory for Microsoft Semantic Kernel identifies CVE-2026-26030 and maps it to CWE-94, improper control of generation of code. Even in short form, that is meaningful. It tells defenders that the logic connecting inputs, filters, templates, and generated code paths is now a legitimate source of remote code execution risk. (جيثب)
This matters far beyond one library. AI-enabled frameworks increasingly mediate business logic, data access, tool execution, retrieval pipelines, and automation flows. When a flaw lands in that layer, the impact is not limited to “the model said something bad.” It can become code execution, policy bypass, data exposure, or unsafe action orchestration. That makes AI framework CVEs operationally closer to middleware and workflow engine vulnerabilities than to conventional content-moderation bugs.
Security engineering teams should take this as a warning about classification habits. If the vulnerable component is listed under “AI tooling,” it may still deserve the same triage priority you would assign to orchestration software, integration hubs, or administrative workflow engines. The branding category is less important than the privileges, data flows, and execution paths the component controls.
What CVE 2026 is really teaching defenders
There is a common thread running through the most important 2026 vulnerability stories so far. The problems that matter most are not random. They share structural characteristics.
The first characteristic is proximity to trust boundaries. CVE-2026-2441 sits at the browser boundary. CVE-2026-21385 sits in the mobile and chipset trust chain. CVE-2026-20127 sits on the network management plane. CVE-2026-22719 sits in a cloud-operations control layer. CVE-2026-26030 sits in a framework that can influence generated code behavior. These are not isolated components. They are interfaces between trust domains.
The second characteristic is exploit reality outranking severity theater. Google explicitly said an exploit exists in the wild for CVE-2026-2441. Android explicitly noted indications of limited targeted exploitation for CVE-2026-21385. CISA put CVE-2026-21385 and CVE-2026-22719 into KEV. Cisco’s SD-WAN story escalated from critical disclosure to broad exploitation reporting. This is the difference between vulnerability management as database review and vulnerability management as adversary-aware operations. (Chrome Releases)
The third characteristic is management-plane economics. Attackers increasingly prefer vulnerabilities that let them manipulate policy, orchestration, routing, migration, administrative actions, or identity-bearing endpoints. Those bugs are expensive for defenders because they collapse multiple downstream assumptions at once.
The fourth characteristic is patch asymmetry. Vendors may release a fix quickly, but organizations still need asset discovery, version mapping, maintenance windows, rollback plans, testing, and sometimes OEM or carrier distribution. The attacker only needs one lagging segment.
This is why the right question in 2026 is not “How many high CVEs do we have?” It is “Which exploited or exploit-ready vulnerabilities sit closest to our control surfaces, identity systems, privileged workflows, and externally reachable parsers?”
A practical triage model for CVE 2026
Security teams need something more useful than raw CVSS sorting. A workable triage model for the 2026 environment starts with six questions.
First, is the vulnerability in the KEV catalog or directly acknowledged by the vendor as exploited in the wild. If yes, treat it as urgent unless you can prove non-exposure. CISA’s KEV is not perfect, but it is one of the clearest public prioritization signals available. (CISA)
Second, does the flaw affect a trust boundary or management plane. Browser parsers, admin panels, SD-WAN controllers, virtualization management, identity-related devices, and workflow engines all score higher here than ordinary internal apps.
Third, is exploitation unauthenticated or low-friction. CVE-2026-20127 and CVE-2026-22719 are especially concerning because unauthenticated exploitation changes the time-to-risk curve dramatically. (Tenable®)
Fourth, does the system sit near high-value routes such as policy control, routing, tenant management, or privileged sessions. Attackers choose leverage, not just exposure.
Fifth, is patching under your direct control. Browser auto-updates are easier than chipset updates distributed through OEM pipelines. The harder the patch path, the more discipline is required around compensating controls and exposure reduction.
Sixth, can you verify exposure quickly. The most dangerous situations are often not the most technically complex. They are the ones where the organization cannot even say which systems are affected.
The table below turns that logic into a practical snapshot.

CVE 2026 priority table
| مكافحة التطرف العنيف | Product / Layer | Public exploitation signal | ما أهمية ذلك | إجراء فوري |
|---|---|---|---|---|
| CVE-2026-2441 | Google Chrome, browser layer | Google says exploit exists in the wild | Browser parsing bug with direct user exposure and identity adjacency | Force browser updates, verify version adoption, prioritize privileged users first |
| CVE-2026-21385 | Qualcomm / Android ecosystem | Android bulletin notes targeted exploitation; NVD shows KEV status | Mobile device trust chain, patch lag through OEMs and carriers | Check Android patch levels, accelerate managed fleet updates, treat high-risk users separately |
| CVE-2026-20127 | Cisco Catalyst SD-WAN Controller / Manager | CISA ED, vendor and third-party reporting, broad exploitation attempts observed | Control-plane auth bypass with policy and routing consequences | Patch now, audit exposure, review IoCs and threat hunting guidance |
| CVE-2026-20122 | Cisco Catalyst SD-WAN Manager | Cisco confirmed exploitation in the wild | Related management-plane weakness increases residual risk after headline CVE | Upgrade to fixed release, do not stop at single-CVE remediation |
| CVE-2026-20128 | Cisco Catalyst SD-WAN Manager | Cisco confirmed exploitation in the wild | Same platform, same urgent attack surface logic | Same as above, validate full advisory coverage |
| CVE-2026-22719 | VMware Aria Operations | Broadcom notes reports of exploitation; CISA KEV listing | Unauthenticated command injection in management workflow | Patch or apply workaround immediately, restrict access to migration-support paths |
| CVE-2026-26030 | Microsoft Semantic Kernel | Public advisory, CWE-94 code injection class | AI framework vulnerability can affect generated code and tool-adjacent execution paths | Upgrade affected SDK, review tool execution boundaries and generated code paths |
The point of a table like this is not to create a universal ranking. It is to force an explicit linkage between exploit signals, system role, and operational blast radius. (Chrome Releases)
Defensive validation code you can actually use
A good CVE 2026 program is not just patch tracking. It also needs repeatable validation. The examples below are intentionally defensive. They are designed for version inventory, patch verification, and exposure review, not offensive exploitation.
Example 1, check Chrome versions across managed macOS endpoints
#!/usr/bin/env bash
# Simple local Chrome version check for macOS
# Use via MDM script runner or SSH-based audit on owned devices
CHROME_APP="/Applications/Google Chrome.app/Contents/MacOS/Google Chrome"
if [ -x "$CHROME_APP" ]; then
VERSION=$("$CHROME_APP" --version 2>/dev/null)
echo "Chrome installed: $VERSION"
else
echo "Chrome not found"
fi
For CVE-2026-2441, the operational goal is not just “push update.” It is “prove updated versions are actually present on the endpoints that matter.” Google’s release note is explicit that exploitation exists in the wild, so version verification is part of remediation, not a nice-to-have. (Chrome Releases)
Example 2, validate Android security patch level with ADB on owned test devices
#!/usr/bin/env bash
# Run on a workstation with adb installed and authorized device attached
adb shell getprop ro.build.version.release
adb shell getprop ro.build.version.security_patch
adb shell getprop ro.product.manufacturer
adb shell getprop ro.product.model
Google’s bulletin states that devices with a 2026-03-01 or later patch level address the issues associated with the 2026-03-01 bulletin, while devices with a 2026-03-05 or later patch level address the 2026-03-05 issues and previous patch levels. This is exactly the kind of detail that turns a vague “Android updated?” question into something measurable. (مشروع أندرويد مفتوح المصدر)
Example 3, defensive HTTP inventory for Cisco SD-WAN exposure
#!/usr/bin/env bash
# Inventory script for owned IP ranges only
# Looks for management interfaces you already operate
for host in $(cat owned_targets.txt); do
echo "Checking $host"
curl -skI --connect-timeout 5 "<https://$host/>" | head -n 10
done
This does not test exploitability, and it should not. Its purpose is simpler and often more valuable: identify exposed management interfaces that should not be internet-reachable in the first place. In the Cisco SD-WAN case, exposure review is inseparable from remediation because the affected systems sit on a management and control plane. (Tenable®)
Example 4, KQL idea for browser emergency update drift
DeviceTvmSoftwareInventory
| where SoftwareName has "Google Chrome"
| project DeviceName, SoftwareName, SoftwareVersion
| summarize Devices=count() by SoftwareVersion
| order by Devices desc
The point here is to detect update drift fast. When the vendor confirms in-the-wild exploitation, patching strategy becomes a race against fleet variance, not a compliance checkbox.
Example 5, lightweight defensive Nuclei-style identification template for owned environments
id: internal-admin-surface-fingerprint
info:
name: Internal Admin Surface Fingerprint
author: security-team
severity: info
description: Fingerprint owned admin panels for inventory and exposure review only
requests:
- method: GET
path:
- "{{BaseURL}}/"
matchers-condition: or
matchers:
- type: word
words:
- "VMware"
- "Cisco"
- "vManage"
- "Aria Operations"
A lot of vulnerability response still fails at the discovery stage. Before proving exploitability, teams need to answer the more basic question: where do these products actually live.
What patching should look like for each major CVE 2026 cluster
For Chrome, the main job is compressed time-to-update. If you manage endpoints, verify browser versions across the fleet and prioritize users whose browsers are routinely exposed to untrusted content while holding privileged sessions. Patch confirmation is more important than policy intent.
For Android and Qualcomm, the key is segmentation of users by risk and patchability. Managed corporate Android fleets should be checked for security patch levels. High-risk users should not wait on normal rollout cadence when there is a targeted exploitation signal. For broader BYOD populations, reinforce conditional access, phishing-resistant MFA, and mobile device posture checks because patch lag is often out of your hands. (مشروع أندرويد مفتوح المصدر)
For Cisco SD-WAN, this is a control-plane emergency. Apply fixed software releases, review CISA and Cisco guidance, identify every exposed management interface, and assume the story is broader than one CVE. The public reporting around CVE-2026-20122 and CVE-2026-20128 should kill any temptation to “patch the headline and move on.” (Tenable®)
For VMware Aria Operations, treat migration-related attack surfaces with more suspicion than your organization probably does today. If the vulnerable condition exists during support-assisted migration, that is not a reason to downgrade urgency. It is a reason to ask whether specialized maintenance workflows are being left insufficiently protected. Apply Broadcom’s fixed versions or documented workaround, then verify access paths and supporting controls around those workflows. (بوابة الدعم)
For Semantic Kernel and similar AI frameworks, do not stop at the version bump. Review where generated code, filters, templates, prompt-derived structures, or tool output can influence execution. In many AI-integrated applications, the vulnerability boundary is no longer just the model. It is the orchestration layer that interprets and acts on data. (جيثب)

Why “latest CVEs” is the wrong operating model
One of the quiet failures in vulnerability programs is the obsession with novelty. Teams ask for “the latest CVEs” as if recency itself were the main risk signal. It is not. Attackers do not care whether the CVE was published this morning or six weeks ago. They care whether it gives them leverage. That is why a useful CVE 2026 operating model prioritizes exploited vulnerabilities, management-plane exposure, and asset-confirmed presence over raw novelty.
The Cisco case makes this obvious. The meaningful story is not just that CVE-2026-20127 was disclosed. It is that exploitation followed, adjacent flaws were also confirmed exploited, and broad scanning plus webshell deployment were then observed. That is how real operational risk develops in public. (سيكيوريتي ويك)
The Android case shows a different version of the same principle. Many mobile flaws never become enterprise emergencies. But a chipset-related vulnerability with targeted exploitation indications and KEV status absolutely deserves attention, even if the average organization still thinks of mobile patching as “eventually important.” (مشروع أندرويد مفتوح المصدر)
The VMware case is the third pattern. The issue sits in an enterprise management product, is exploitable without authentication in a sensitive workflow, and has both vendor action and KEV-driven urgency surrounding it. That is not just another infrastructure bulletin. It is a sign that management workflows remain one of the most under-defended parts of enterprise software estates. (بوابة الدعم)
Where automated validation actually helps
There is a natural place here for a platform like Penligent, and it is not in replacing human judgment. It is in reducing the lag between public vulnerability intelligence and concrete validation work inside real environments.
When a 2026 CVE lands, the hard part is rarely reading the advisory. The hard part is turning scattered vendor notes, NVD descriptions, patch matrices, and asset uncertainty into an executable workflow. Which hosts are in scope. Which versions are running. Which banners and management surfaces are exposed. Which compensating controls exist. Which systems can be non-disruptively validated first. That translation layer is where automation becomes useful.
An AI-driven pentesting and validation platform can help compress the operational loop by discovering assets, correlating product fingerprints, identifying likely affected versions, generating safe validation steps, and packaging results into a decision-ready report. In practice, that means less time spent manually stitching together advisory prose and more time spent confirming what is real in your environment. That is especially valuable when vulnerability stories expand quickly, as they did with Cisco SD-WAN in late February and early March 2026. (Tenable®)
A 2026 vulnerability response checklist that is worth keeping
If you want one short checklist from this article, keep this one.
When a new CVE 2026 issue appears, first ask whether there is a real exploitation signal from the vendor, CISA, KEV, or high-quality reporting. Second, ask whether the product sits on a management plane, browser boundary, mobile trust chain, or workflow engine. Third, inventory actual exposure, not theoretical ownership. Fourth, verify patch state directly. Fifth, hunt for adjacent flaws on the same platform rather than stopping at the first headline. Sixth, document residual exposure caused by OEM lag, change windows, or unsupported versions. Seventh, confirm that remediation changed reality, not just ticket status.
That may sound obvious, but it is still more operationally useful than sorting by CVSS and hoping the spreadsheet tells the story.
Final take
The most important meaning of “CVE 2026” right now is not that there are new vulnerabilities with new numbers. It is that the year’s most consequential flaws already tell a consistent story about where attackers want to be. They want the browser that renders hostile content. They want the phone that carries identity. They want the SD-WAN controller that decides network behavior. They want the cloud operations plane that orchestrates infrastructure. They want the framework layer that turns AI logic into actions.
That is why the right response is not broader awareness in the abstract. It is narrower focus on the vulnerabilities that sit closest to trust, control, and execution. If your team builds around that principle, the CVE 2026 firehose becomes more manageable. If not, you end up doing what too many organizations still do: reading every advisory and still missing the one that mattered.
مزيد من القراءة
Start with Google’s Chrome stable channel note for CVE-2026-2441, Google’s Android Security Bulletin for March 2026, Broadcom’s VMware Aria Operations advisory, Cisco-related public analysis on CVE-2026-20127 and its follow-on exploitation, and CISA’s KEV catalog. (Chrome Releases)
AI Penetration Testing, From Simulation to Smart Red Teams (بنليجنت)
OpenClaw Security Risks and How to Fix Them, A Practical Hardening and Validation Playbook (بنليجنت)
OpenClaw GPT 5.4 Security, When a Better Agent Becomes a Bigger Target (بنليجنت)
Over 220000 OpenClaw Instances Exposed to the Internet, Why Agent Runtimes Go Naked at Scale (بنليجنت)


