CVE-2026-20643 is not a browser remote code execution bug. Apple’s public advisory describes it much more narrowly: a cross-origin issue in the Navigation API that could allow maliciously crafted web content to bypass the Same Origin Policy, with fixes delivered through Background Security Improvements for iOS 26.3.1, iPadOS 26.3.1, macOS 26.3.1, and macOS 26.3.2. Apple credits Thomas Espach, and the CVE was published on March 17, 2026. (دعم Apple)
That short description is enough to make this worth careful attention. Same Origin Policy is one of the web’s foundational trust boundaries. It is the rule that stops one origin from reading sensitive data from another origin, including authenticated webmail, admin portals, and internal web applications the user is already signed into. A flaw that weakens that boundary does not need a dramatic CVSS headline to matter operationally, especially on platforms where WebKit sits underneath Safari and many other app surfaces. (مستندات الويب MDN)
Public records also show a more restrained risk picture than many social posts suggest. As of March 24, 2026, NVD had not yet published its own CVSS assessment for this CVE. The CISA ADP enrichment attached to the record scored it 5.4 with the vector AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:N, categorized it under CWE-20 and CWE-346, and marked exploitation as none and automatable as no. That matters, because it tells defenders two things at once: there is no official evidence of in-the-wild abuse today, but the issue is still a real browser security failure involving network-reachable malicious content and user interaction. (NVD)
The most useful way to read CVE-2026-20643 is not as “yet another Apple patch,” but as a case study in how modern browser navigation APIs can create new security failure modes when origin checks are even slightly wrong. The public advisory is sparse, but Apple’s own WebKit release history, the HTML specification, and a publicly visible WebKit fix together reveal a great deal about the class of mistake involved. The result is a more grounded understanding than the shallow summaries now circulating on many vulnerability sites. (دعم Apple)
What is publicly confirmed, and what is not
The public record around CVE-2026-20643 is unusually short, so it helps to separate confirmed facts from reasonable inference.
| البند | Publicly confirmed | Not publicly confirmed |
|---|---|---|
| Affected component | WebKit, specifically a cross-origin issue in the Navigation API | The full exploit chain or every internal code path Apple changed |
| التأثير | Maliciously crafted web content may bypass Same Origin Policy | A vendor-published proof of concept showing end-to-end exploitation |
| Fixed builds | iOS 26.3.1 a, iPadOS 26.3.1 a, macOS 26.3.1 a, macOS 26.3.2 a | Whether older supported branches received equivalent backports through some other channel |
| Weakness classes | Improper Input Validation and Origin Validation Error | A complete vendor-authored root-cause narrative |
| Current exploitation status | No public evidence in the official record, CISA ADP says exploitation none | Whether any private exploitation exists outside vendor and government knowledge |
The table above is compiled from Apple’s advisory, the CVE record, and NVD enrichment. (دعم Apple)
That distinction matters because a lot of secondary writeups are already overstating the case. Some databases flatten CVE-2026-20643 into labels like “authentication bypass” or treat it as if the full exploitation story were already settled. Apple did not say that. NVD did not say that. The official record says “Same Origin Policy bypass” through a Navigation API cross-origin issue, and that is where accurate discussion needs to start. (دعم Apple)
It is also important not to invent certainty where the evidence is thin. Apple’s advisory references WebKit Bugzilla 306050. A publicly visible WebKit commit that strongly matches the vulnerability class references a different bug, 307197, and fixes NavigateEvent.canIntercept for cross-port navigations. That does not prove that the public commit is the whole CVE, or the only code change behind it. The safest reading is narrower: the public source tree exposes at least one concrete Navigation API origin-validation failure that is highly consistent with Apple’s description. (دعم Apple)
Why the Same Origin Policy boundary matters here
Same Origin Policy is not an obscure browser implementation detail. It is the reason a page from one origin cannot freely read the DOM, response bodies, or other sensitive state from another origin. MDN’s definition is the clearest operational one: SOP restricts how a document or script loaded from one origin can interact with resources from another origin, and it exists specifically to stop malicious websites from reading things like authenticated webmail or protected intranet content through the victim’s browser. (مستندات الويب MDN)
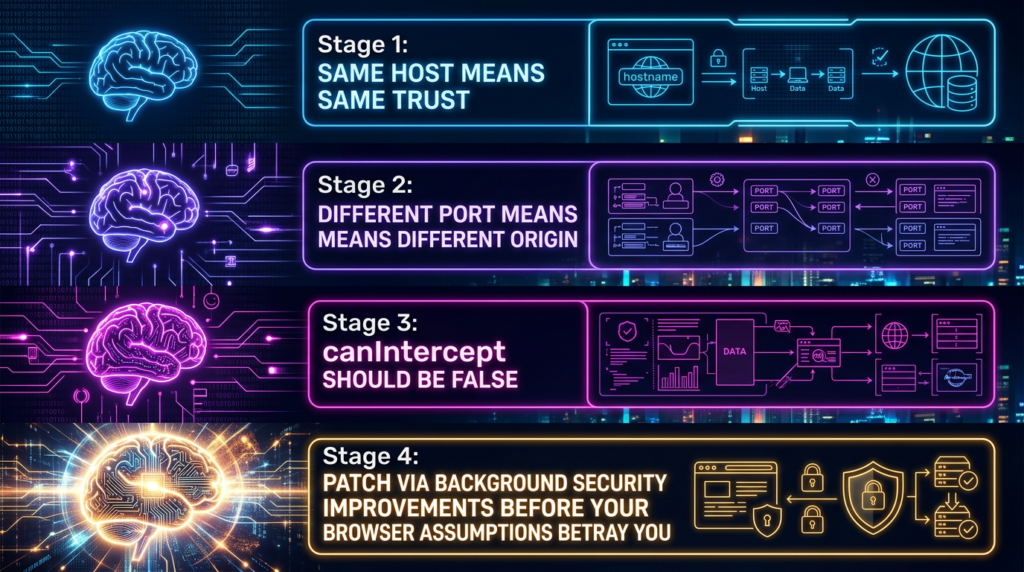
The detail that matters most for CVE-2026-20643 is the definition of an origin. Two URLs are same-origin only when scheme, host, and port match. That means https://app.example.com و https://app.example.com:8443 are different origins. The same is true for http://localhost:3000 و http://localhost:8000. Security engineers often know this in theory but still design internal workflows as if “same machine, same host, different port” were a sufficiently strong trust separator. The web platform does not treat it that way, and this vulnerability is a reminder that browsers should not either. (مستندات الويب MDN)
This is also where many shallow summaries lose the thread. A cross-origin bug is not automatically about internet-wide cross-domain theft in the dramatic Hollywood sense. Sometimes the most realistic target is much closer to the user: a local admin panel bound to loopback, a development tool exposed on a high port, an internal portal that shares a host but splits functions by port, or a desktop application that embeds WebKit and talks to a local service. Once the browser’s idea of where same-document behavior is allowed stops lining up with origin rules, seemingly modest navigation logic can become a security problem. That is an inference from the standards model and the public fix, but it is a disciplined one. (مستندات الويب MDN)
A useful way to think about SOP is as a safety rail around ambient trust. Browsers routinely hold cookies, bearer tokens, authenticated sessions, cached responses, and page state that the user did not manually re-enter on every request. SOP is what keeps all of that from becoming readable by the last tab the user opened from an attacker-controlled link. When a browser bug weakens SOP, the attacker no longer has to defeat your application logic first. They may only need the victim to visit a malicious page in the right browser context. (مستندات الويب MDN)
Why the Navigation API is central to this CVE
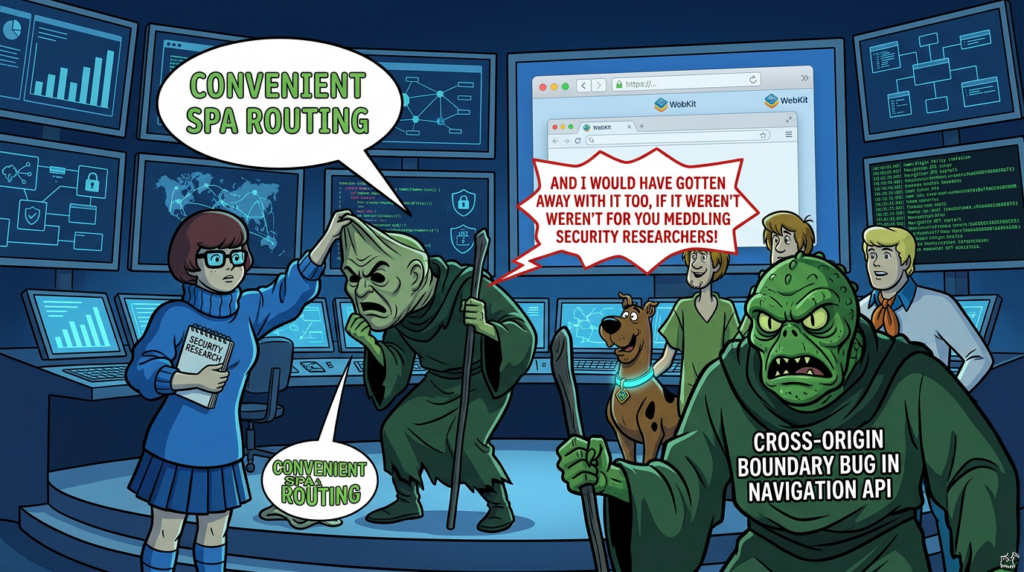
The Navigation API is relatively new in Safari, and that recency matters. WebKit’s Safari 26.2 release notes say Safari 26.2 added support for the Navigation API as a modern replacement for the History API, designed to give developers centralized control over browser navigation. The API introduces the navigate event and allows applications to inspect, intercept, and manage navigations in ways that are better aligned with single-page application behavior than older pushState و popstate patterns. Safari 26.3 then added an AbortSignal on NavigateEvent, further expanding the API’s practical use in real applications. (WebKit)
The HTML Standard describes the Navigation API as the successor to the classic الموقع و history APIs. It also defines event.canIntercept as the signal that tells the page whether calling intercept() is allowed for a given navigation. In other words, this boolean is not decorative. It is the browser’s own answer to a security-relevant question: can this navigation be transformed into same-document behavior, or must it remain a normal cross-document navigation because the destination crosses a boundary the current document is not allowed to rewrite or absorb? (HTML Living Standard)
The standard’s developer-facing examples are explicit that some navigations, including cross-origin navigations, cannot be intercepted. The same document also explains that canIntercept is generally true only when the current document can have its URL rewritten to the destination URL, with cross-document traversals remaining a separate exception. That logic is critical because intercepting a navigation is not just a UI convenience. It changes which document logic keeps running and what same-document assumptions the page can continue to make. (HTML Living Standard)
That is why a Navigation API bug can become a security bug even when it does not look like a traditional memory corruption issue. If the browser tells a page that it may intercept a navigation it should not be allowed to intercept, the page may continue operating under same-document assumptions across a boundary where those assumptions should have been revoked. The advisory’s wording, the standards behavior, and the public WebKit fix all line up with that class of failure. (دعم Apple)
What the public WebKit fix strongly suggests
The single most useful public artifact for understanding CVE-2026-20643 is a WebKit commit with the title “NavigationEvent#canIntercept is true when navigating to a different port.” The commit message states that canIntercept was incorrectly returning true when navigating between different ports on the same host, gives the concrete example of localhost:3000 إلى localhost:3001, and says the value should be false when the document URL and target URL differ in scheme, username, password, host, or port. The fix adds explicit equality checks for those components before allowing URL rewriting. It also adds a web-platform test whose expected result is simple and definitive: canIntercept should be false for cross-port navigations. (جيثب)
That detail matters because it turns the advisory from an abstract “cross-origin issue” into something much more concrete. A page should not be allowed to treat a cross-port navigation as eligible for same-document interception, because different ports are different origins. If the browser says otherwise, it has already broken a basic origin rule before any attacker-specific payload enters the picture. (مستندات الويب MDN)
Safari Technology Preview 238, published on February 26, 2026, independently confirms the same fix in user-facing release notes. It says WebKit fixed NavigateEvent.canIntercept so it correctly returns false when navigating to a URL with a different port, explicitly noting that this aligns with the Navigation API specification. That is valuable corroboration because it shows the issue was not just a theoretical code cleanup in a commit log; it was exposed as a standards-alignment bug in WebKit’s public preview channel before Apple shipped the March 17 Background Security Improvement. (WebKit)
At the same time, precision matters. Apple’s advisory references WebKit Bugzilla 306050, while the public commit references bug 307197 and canonical change 307316@main. Apple did not publish a statement saying “CVE-2026-20643 equals commit 850ce31 and nothing else.” So the correct technical posture is not to pretend the public code tells the whole story. The correct posture is to say that the public fix reveals a very plausible defect pattern behind the advisory: incorrect origin handling in Navigation API interception logic, especially around cross-port transitions. (دعم Apple)
That reading also fits the weakness metadata. NVD’s enrichment lists CWE-20 Improper Input Validation and CWE-346 Origin Validation Error. The public commit is exactly the kind of change you would expect from that pair: origin components that should have been validated together were not being compared strictly enough before a security-sensitive behavior was allowed. (NVD)
What the bug likely did in practice, without inventing an exploit chain
The safest practical interpretation is that a malicious page could obtain permission to intercept a navigation that should have remained a real cross-origin or cross-port navigation. Once that happens, the attacker-controlled page may be able to keep running logic through a transition where the browser should have cut over to a different document and a different origin context. That is the core security failure the public code supports. (HTML Living Standard)
Beyond that, caution is necessary. Apple did not publish a proof of concept. Apple did not describe whether the primary consequence was DOM access, response access, UI confusion, state retention, credential leakage, or some other form of origin confusion. NVD does not fill in those details either. So any article that claims a fully proven step-by-step theft scenario is going beyond the public evidence. What can be said with confidence is narrower: the vulnerability touches a boundary that normally decides whether one origin can safely continue controlling navigation and state when the destination differs by origin. (دعم Apple)
That still leaves room for realistic risk modeling. Consider a malicious page opened in Safari or another WebKit-backed surface. If the victim then triggers a navigation to a trusted service on the same host but a different port, or to a local tool exposed on loopback, the browser should treat that as a boundary crossing where same-document interception is off limits. If a vulnerable build instead says interception is allowed, the attacker may be able to preserve behavior that was meant only for same-origin navigations. For defenders, the important part is not whether every hypothetical downstream effect is proven; it is that a sensitive origin transition was being judged incorrectly by the engine. (مستندات الويب MDN)
This is one reason medium browser bugs can become high-priority in the right environments. The browser is not an isolated parser. It is where users authenticate to identity providers, where administrators manage infrastructure, where engineers run local dashboards, and where native applications embed web content. A Same Origin Policy bypass in that environment is not equivalent to a low-risk rendering glitch. It is a break in the rule that keeps unrelated trust zones from blurring together in one process. (مستندات الويب MDN)
Where the real-world risk is most likely to concentrate
The first concentration point is localhost and loopback workflows. Modern developer and security tooling often expose HTTP services on 127.0.0.1 أو المضيف المحلي, split by function across different ports. Frontend dev servers, reverse proxies, wallet bridges, AI developer tools, callback handlers, control panels, debug dashboards, and ephemeral admin UIs all commonly live there. Because the host string is the same, teams sometimes treat these as “basically one place.” The web platform does not. If a browser regression starts treating cross-port transitions too loosely, loopback-heavy workflows become much more interesting to an attacker than generic brochure websites. The importance of the port boundary is not conjecture; it is built into the origin model itself. (مستندات الويب MDN)
The second concentration point is enterprises that separate trust levels by port rather than by hostname or zone. It is common to see applications like intranet.example.com:443 for end users and intranet.example.com:8443 for privileged administration, or separate services bound behind the same host in internal environments. That design may be operationally convenient, but CVE-2026-20643 is a strong argument against assuming port-only separation is a comfortable long-term security boundary for browser-mediated workflows. Standards say port changes are origin changes. A browser bug that mishandles that line is a signal to reduce how much privilege depends on it. (مستندات الويب MDN)
The third concentration point is WebKit in applications, not just Safari tabs. WebKit’s own project page says the engine is used by Safari, Mail, App Store, and many other apps on Apple platforms. Apple’s developer documentation makes the same point from the app side: WKWebView is the native control for embedding full web-browsing functionality into apps. That means the blast radius of WebKit issues is broader than “people using Safari as their browser.” Any workflow that renders untrusted or semi-trusted content through a WebKit-based surface should be evaluated with that in mind. (WebKit)
There is also a more subtle risk category: stateful single-page applications that make heavy use of navigation interception. The more application logic depends on same-document routing, navigation state, and client-side assumptions about when a navigation remains within the same trust context, the more any engine-level interception bug can matter. Safari’s 26.2 and 26.3 feature additions make that especially relevant now, because the Navigation API is no longer a niche proposal in WebKit; it is a shipped interface moving into production use. (WebKit)
What this CVE does not say
It does not say arbitrary code execution. Apple’s advisory does not describe memory corruption, use-after-free, type confusion, JIT abuse, or sandbox escape. The public impact statement is about Same Origin Policy bypass via malicious web content, not code execution. (دعم Apple)
It does not say active exploitation. The official enrichment attached to the public record says exploitation none, and Apple’s advisory does not include the language it uses in cases where it is aware of in-the-wild exploitation. That alone separates CVE-2026-20643 from Apple bugs like CVE-2025-43529 or CVE-2026-20700, where Apple explicitly said it was aware of sophisticated targeted attacks. (OpenCVE)
It does not say every WebKit-using application is instantly and equally exposed to the worst imaginable outcome. Risk depends on whether the user can be driven to malicious content, whether the navigation pattern in question occurs, whether valuable cross-origin targets exist in the same browsing workflow, and whether patching has already closed the issue. CVSS reflects some of that nuance by marking user interaction as required and the impact as partial, not total. (NVD)
It also does not justify blaming application-level CORS or session design for a browser-core defect. CORS governs what a server chooses to allow. SOP is the browser’s base enforcement layer. A browser bug that misclassifies a navigation boundary is a different category of problem. Application hardening still matters, but it is not the root cause here. (مستندات الويب MDN)
Why a 5.4 score can still deserve prompt action
Security teams often overlearn the lesson that “medium” means “not urgent.” Browser boundary defects are one of the places where that shortcut fails. CISA ADP’s score of 5.4 tells you the exploit is not thought to be wormable, not fully automatable, and not obviously catastrophic on its own. It does not tell you the bug is harmless in the environments that matter most. A browser-origin confusion flaw running in the context of an engineer signed into production dashboards is simply not the same business risk as a medium-severity parser crash in an offline component. (OpenCVE)
The same is true for user interaction. UI:R often gets translated into “the user has to click something, so the risk is low.” In browser security, that is too simplistic. Visiting a page, opening a link, authenticating to a portal, or following a local callback flow is ordinary behavior. User interaction means the exploit is not zero-click. It does not mean the bug is difficult to stage inside normal work patterns. (NVD)
For high-value populations, browser trust failures should usually be triaged above their raw score. Administrators, security engineers, executives, developers running local services, and staff who routinely touch SSO or internal portals have a very different exposure profile from kiosk users reading static sites. CVE-2026-20643 is a good example of why patch prioritization should include user role and workflow, not just CVSS sorting. That is an operational judgment, not a vendor quote, but it follows directly from the documented impact boundary. (دعم Apple)
Affected versions and the patch path
Apple’s advisory is clear about the patched delivery path. The fix shipped as Background Security Improvements for iOS 26.3.1, iPadOS 26.3.1, macOS 26.3.1, and macOS 26.3.2, with the supplemental build letter a applied to those baselines. In other words, the important distinction is not simply “am I on 26.3.1?” but “am I on the 26.3.1 or 26.3.2 baseline and did the Background Security Improvement install?” (دعم Apple)
| Platform baseline | Patched supplemental release | What defenders should verify |
|---|---|---|
| iOS 26.3.1 | iOS 26.3.1 a | The device is on the latest minor branch and Background Security Improvements are allowed |
| iPadOS 26.3.1 | iPadOS 26.3.1 a | Same as above |
| macOS 26.3.1 | macOS 26.3.1 a | Background Security Improvements installed, then Safari relaunched or system restarted |
| macOS 26.3.2 | macOS 26.3.2 a | Same as above |
This table reflects Apple’s advisory and Background Security Improvements documentation. (دعم Apple)
One subtle but important operational point is that Background Security Improvements apply only to the latest minor operating system version. Apple’s documentation says that if that minor operating system update is delayed, the response is effectively delayed too. That means organizations that intentionally hold back minor OS adoption may also be holding back this patch path, even if they assume lightweight security responses will keep them covered. (دعم Apple)
Apple also states that if the automatic install setting is turned off, the device will not receive these improvements until they are included in a subsequent software update. For many users, that is the biggest practical risk around CVE-2026-20643: the patch exists, but their mental model of “I install system updates when I feel like it” does not match how this new security mechanism works. (دعم Apple)

What Apple’s Background Security Improvements change for defenders
Background Security Improvements are Apple’s lightweight security releases delivered between standard software updates. Apple says they apply to components like Safari, the WebKit framework stack, and other system libraries, and that they are available only on the latest versions of iOS, iPadOS, and macOS. This matters because CVE-2026-20643 is one of the first widely discussed examples where the remediation path is not a conventional “go from 26.3.1 to 26.3.2” user experience. (دعم Apple)
The operational behavior is different enough that security teams should learn it explicitly. Apple’s platform security documentation says Safari security improvements delivered through a Background Security Improvement on macOS become active as soon as Safari is relaunched, even before the whole operating system restarts. It also says the broader operating system activation occurs on restart, and that these updates use cryptexes and a different delivery mechanism from traditional OS resealing. That means a user who has received the patch may still need to relaunch Safari promptly to reduce exposure in browser workflows, even if they have not fully rebooted the system yet. (دعم Apple)
Apple also notes that Background Security Improvements can be removed, reverting the device to the baseline software update state with no improvements applied, and that if the user turns off automatic installation the device waits until a later standard software update to receive equivalent content. From an incident-response perspective, that means “was once patched” is not the same as “is currently protected.” Removability is useful for regression handling, but it creates another state that asset management has to understand. (دعم Apple)
For Mac laptops, the deployment guide adds a practical implementation detail: Apple silicon systems need at least 10 percent battery and Intel Macs 20 percent battery when applying a Background Security Improvement. That may sound minor, but it can matter when fleets stay mobile and seldom reboot. Low-friction patching only helps if the environmental prerequisites are consistently met. (دعم Apple)
For managed environments, Apple’s deployment documentation exposes specific controls and reporting hooks. Administrators can enforce installation behavior with InstallSecurityUpdate, and they can report installed Background Security Improvements using StatusDeviceOperatingSystemSupplementalExtraVersion و StatusDeviceOperatingSystemSupplementalBuildVersion. If you run Apple fleets at scale, those two status keys are more useful than user-reported screenshots or assumptions about software currency. (دعم Apple)
How to verify exposure safely
The first layer is configuration verification, not exploit testing. On iPhone and iPad, Apple says the setting lives under Settings, then Privacy and Security, then Background Security Improvements. On Mac, it is System Settings, then Privacy and Security, then Background Security Improvements. Apple’s direct recommendation is to ensure “Automatically Install” is turned on. If it is off, the device will not receive the fix until a later software update absorbs it. (دعم Apple)
The second layer is process activation. On macOS, relaunch Safari after the improvement is installed. Apple’s own platform security guide says Safari-related improvements can become active as soon as Safari is relaunched, even before a full OS restart, while the rest of the operating system adopts the new cryptex-backed content on restart. In practice, that means “patch installed, browser never closed” is not a state I would accept for a security-sensitive user. (دعم Apple)
The third layer is managed-device state reporting. If you are responsible for fleets, do not stop at OS version inventory. Check whether devices are on the latest minor branch, whether the Background Security Improvements setting is enforced or at least enabled, and whether the supplemental version and supplemental build fields reflect the installed response. Apple’s deployment documentation gives you the hooks to do this without guessing. (دعم Apple)
The fourth layer is behavioral validation in a lab you control. The good news is that the public WebKit material already suggests a safe, non-weaponized test condition: a cross-port navigation should produce event.canIntercept === false. You do not need to read cross-origin data, steal anything, or weaponize the bug to validate whether the browser still misclassifies that transition. The WebKit commit and Safari Technology Preview notes already define the expected corrected behavior. (جيثب)
Here is a minimal validation page derived from that logic. It is intentionally limited to checking the canIntercept behavior and preventing the actual navigation:
<!doctype html>
<meta charset="utf-8">
<title>Navigation API cross-port validation</title>
<button id="run">Check cross-port canIntercept</button>
<pre id="log"></pre>
<script>
const log = (msg) => {
document.querySelector("#log").textContent += msg + "\n";
};
document.querySelector("#run").addEventListener("click", () => {
const currentPort = location.port || (location.protocol === "https:" ? "443" : "80");
const otherPort = currentPort === "8000" ? "8800" : "8000";
const targetURL = `${location.protocol}//${location.hostname}:${otherPort}/`;
navigation.addEventListener("navigate", (event) => {
log(`Destination: ${event.destination.url}`);
log(`canIntercept: ${event.canIntercept}`);
if (event.canIntercept) {
log("Unexpected result on a patched build for a cross-port navigation.");
} else {
log("Expected result on a patched build.");
}
event.preventDefault();
}, { once: true });
const a = document.createElement("a");
a.href = targetURL;
a.textContent = "trigger";
document.body.appendChild(a);
a.click();
});
</script>
The expected result on a patched WebKit build is that canIntercept is false when the destination is on the same host but a different port. That expectation comes directly from the WebKit fix and release notes, not from reverse-engineered exploitation theory. Use it only in a disposable, self-controlled lab environment where both ports and all content belong to you. (جيثب)
Interpreting the result also requires care. A false result does not prove your system is fully patched in every WebKit path, and a true result in a custom environment does not automatically prove you are reproducing CVE-2026-20643 exactly. What it does provide is a high-value behavioral signal aligned with a publicly documented defect class. As a validation primitive, that is far more useful than copy-pasting unvetted “exploit” code from an aggregator. (جيثب)
Developer and defender hardening guidance that still matters after patching
The first lesson is architectural: do not rely on port-only separation for high-trust boundaries when browser access is part of the workflow. Standards treat different ports as different origins, and CVE-2026-20643 shows why that distinction is security-relevant. If an admin plane is materially more sensitive than a user plane, move it to a distinct hostname, ideally behind a distinct trust path, rather than assuming :8443 is enough isolation forever. That is design guidance, not a vendor quote, but it follows directly from the origin model and the public failure mode. (مستندات الويب MDN)
The second lesson is to stop treating localhost as a harmless convenience zone. Local services often inherit trust precisely because they are “only local,” yet the browser can still reach them, users can still be navigated toward them, and web content can still participate in the transition. If your application exposes privileged HTTP functionality on loopback, assume browser-origin bugs will eventually test that assumption. Minimize unauthenticated local endpoints, shorten their lifetime, and require explicit user-driven confirmation for high-value actions. (مستندات الويب MDN)
The third lesson is to reduce ambient authority in browser sessions. Same Origin Policy bypasses are most dangerous when simply being logged in is enough to expose sensitive state or authorize powerful actions. Reauthentication gates for account changes, device registration, privileged console operations, and payment-impacting actions will not repair a browser bug, but they can reduce what an origin-confusion issue can accomplish in one shot. This is especially important for internal tools where teams often trust the corporate browser too much. (مستندات الويب MDN)
The fourth lesson is session hygiene. Use HttpOnly, تأمين, and appropriately strict SameSite cookie settings where possible, and avoid exposing unnecessary sensitive data directly in highly script-readable pages. Those controls do not “fix” a Same Origin Policy bypass, but they reduce the number of easy wins available to attacker-controlled content and make chained abuse harder. They also remain valuable against the much more common classes of cross-site weakness outside the browser-core category. (مستندات الويب MDN)
The fifth lesson is segmentation of privileged browser use. If administrators and security engineers regularly access production control planes, identity systems, and experimental web content from the same browser profile and same endpoint, a medium browser boundary bug can have outsized consequences. Separate browsing contexts, separate devices for high-risk testing, or at least separate profiles with minimized standing privilege are still worthwhile operational discipline. Again, that is a defensive judgment call, but it is exactly the kind of risk-reduction that origin-boundary bugs justify. (دعم Apple)
Related CVEs that help frame the bigger Apple browser-chain picture
CVE-2026-20643 is not publicly described as exploited, and Apple did not place it in a published exploit chain. But it sits in a broader Apple security context where browser and browser-adjacent issues have recently played a first-stage role in much more serious targeted attacks. That context matters because defenders tend to underestimate “initial boundary failure” bugs until a later chain makes the stakes obvious. (دعم Apple)
The most relevant comparison is CVE-2025-43529, a WebKit use-after-free issue that Apple explicitly said may have been exploited in an extremely sophisticated attack against specific targeted individuals on versions of iOS before iOS 26. Apple’s Safari 26.2 advisory and iOS 18.7.3 advisory both associate that WebKit issue with arbitrary code execution from malicious web content. The direct lesson is not that CVE-2026-20643 is equally severe. It is that WebKit bugs routinely matter far beyond browsing aesthetics, and they are worth taking seriously even when the initial description looks narrower than a memory-safety headline. (دعم Apple)
Another useful comparison is CVE-2026-20700 in dyld. Apple said an attacker with memory write capability may be able to execute arbitrary code, and that it was aware of a report this issue may have been exploited in an extremely sophisticated attack against specific targeted individuals on versions of iOS before iOS 26. Apple’s advisory also says CVE-2025-14174 and CVE-2025-43529 were issued in response to the same report. That is the important strategic point: browser-side compromise is often the beginning of a chain, not the whole chain. A boundary bug like CVE-2026-20643 is not publicly placed in that family, but it lives in the same risk universe where initial browser footholds deserve respect. (دعم Apple)
A practical way to compare the three is this:
| مكافحة التطرف العنيف | المكوّن | Publicly stated impact | Public exploitation language | Why it matters here |
|---|---|---|---|---|
| CVE-2026-20643 | WebKit Navigation API | Same Origin Policy bypass via malicious web content | No official exploitation evidence in the public record | Shows that origin-validation mistakes in new web APIs become real security defects |
| CVE-2025-43529 | WebKit | Arbitrary code execution from malicious web content | Apple said it may have been exploited in sophisticated targeted attacks | Demonstrates how serious WebKit entry bugs can become in practice |
| CVE-2026-20700 | dyld | Arbitrary code execution for an attacker with memory write capability | Apple said it may have been exploited in sophisticated targeted attacks | Shows how post-browser stages can amplify an initial foothold into deeper compromise |
The comparison above is drawn from Apple’s own advisories and the public CVE record. (دعم Apple)
Penligent’s published technical content is also relevant enough to mention here. Its WebKit-focused writeup on CVE-2025-43529 is a browser-engine deep dive, not a generic “AI security” brochure, and its Safari password and iOS CVE material both push the same operational idea: safe validation is more useful than improvised exploitation when defenders are trying to turn a browser bug into an actionable remediation path. That is the posture CVE-2026-20643 deserves as well. (بنليجنت)
Final assessment
CVE-2026-20643 is a good reminder that modern browser security bugs do not need to look like classic memory corruption to deserve attention. Apple’s advisory says the issue could bypass Same Origin Policy. The public WebKit record strongly suggests that one concrete failure mode involved NavigateEvent.canIntercept returning true for cross-port navigations, which is exactly the kind of origin-validation mistake a browser cannot afford to make. The standards model says ports define origin. WebKit briefly failed that test. Apple fixed it. That is the core story. (دعم Apple)
The operational takeaway is straightforward. First, make sure affected Apple devices are actually receiving Background Security Improvements and that Safari has been relaunched on macOS where appropriate. Second, validate behavior in a controlled lab instead of trusting rumors or exploit aggregators. Third, revisit any design that treats port-only separation, loopback trust, or heavily stateful browser routing as a comfortable long-term security boundary for privileged workflows. Those assumptions were always brittle. CVE-2026-20643 simply made the brittleness visible. (دعم Apple)
Further reading
- Apple Security Advisory — About the security content of Background Security Improvements for iOS 26.3.1, iPadOS 26.3.1, macOS 26.3.1, and macOS 26.3.2 — the official vendor description, affected builds, and disclosure date. (دعم Apple)
- NVD Record — CVE-2026-20643 Detail — enriched weakness metadata, current scoring state, and reference history. (NVD)
- CVE Record — CVE-2026-20643 — canonical CVE publication record. (OpenCVE)
- WebKit Commit — NavigationEvent#canIntercept is true when navigating to a different port — the most informative public code artifact tied to this defect class. (جيثب)
- Safari Technology Preview 238 — Release Notes for Safari Technology Preview 238 — public confirmation that WebKit fixed
canInterceptfor cross-port navigations. (WebKit) - WHATWG HTML Standard — Navigation API and session history — the specification basis for
canInterceptand document URL rewriting rules. (HTML Living Standard) - MDN — Same-origin policy — practical explanation of the origin boundary that this CVE touches. (مستندات الويب MDN)
- Apple Platform Security — Background Security Improvements in Apple operating systems — how the supplemental patching mechanism works under the hood. (دعم Apple)
- Apple Deployment Guide — Background Security Improvements on Apple devices — fleet-management details, activation behavior, and reporting fields. (دعم Apple)
- Penligent home page — product overview focused on verification, reproducible PoCs, and reporting workflows. (بنليجنت)
- The Death of the Sandbox, An Engineering Autopsy of CVE-2025-43529 — a WebKit-centered technical deep dive that is useful background for anyone tracking Apple browser-engine risk. (بنليجنت)
- Safari passwords, Deep Technical Guide for Security Engineers — relevant for understanding Safari-side credential exposure and browser attack surface. (بنليجنت)
- CVE-2025-24085, An iOS 0-Day, Public PoC, and the Role of AI Pentest Tools — relevant for defenders building validation workflows around Apple security advisories without turning to unsafe public exploit habits. (بنليجنت)