CVE-2026-25177 at a glance
Microsoft disclosed CVE-2026-25177 on March 10, 2026 as an Active Directory Domain Services Elevation of Privilege Vulnerability. In the public NVD entry, the description is still short, but the risk profile is already clear: the issue affects AD DS, is reachable over the network, requires only امتيازات منخفضة, needs no user interaction, and received a CVSS v3.1 base score of 8.8 from Microsoft. The mapped weakness is CWE-641, Improper Restriction of Names for Files and Other Resources. In practical terms, that combination makes this the kind of identity-layer bug that defenders should treat as far more than “just another Windows EoP.” (NVD)
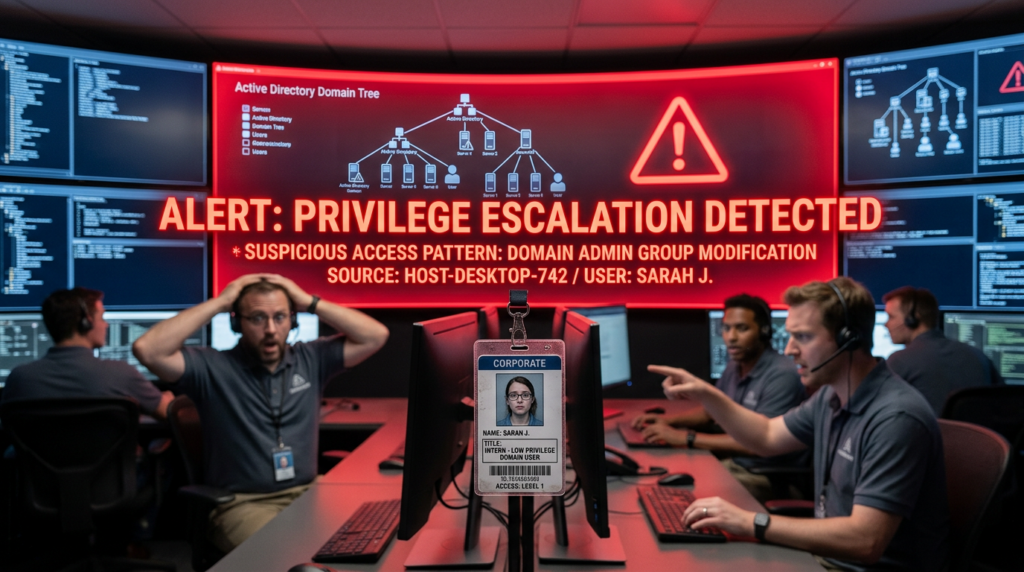
That matters because Active Directory is not a side system. In many enterprises it is the trust spine for authentication, service identity, delegation, policy application, and authorization inheritance. A low-privileged foothold inside the domain is already a serious starting point; when a domain service itself has a privilege escalation weakness, the distance from “ordinary domain user” to “meaningful domain control” can collapse very quickly. This is why current coverage around CVE-2026-25177 repeatedly frames it as an Active Directory flaw with potential SYSTEM privilege escalation impact, even though Microsoft’s public advisory text remains concise. (إي سيكيوريتي بلانيت)
The right way to read this CVE is not as an isolated patch note. It belongs to a long and uncomfortable tradition of identity infrastructure issues where naming, trust, uniqueness, or delegation assumptions become the mechanism by which a small permission turns into a large one. Microsoft Learn has long documented that SPNs و UPNs must be unique in the directory forest, which is exactly why any weakness in how names are validated, normalized, or restricted inside AD DS deserves unusually high scrutiny. (مايكروسوفت تعلم)

What Microsoft and NVD have actually confirmed
Here is the confirmed baseline from the public record.
NVD says the flaw is an improper restriction of names for files and other resources في Active Directory Domain Services that allows an authorized attacker إلى elevate privileges over a network. Microsoft’s CNA vector is AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H, which means the confidentiality, integrity, and availability impacts are all scored high. NVD published the record on March 10, 2026, then added CPE information in a later analysis update on March 13, 2026. (NVD)
Rapid7’s Patch Tuesday coverage lists CVE-2026-25177 under Windows vulnerabilities, marks it not publicly disclosed, assigns the same 8.8 score, and labels exploitation “Less Likely” rather than “More Likely.” ZDI’s March 2026 update review likewise lists it as Important مع 8.8 severity. That does not make the vulnerability minor. It means Microsoft’s prediction model did not elevate it to likely near-term mass exploitation at the time of release. Security teams should not confuse that with low operational risk in real AD environments. (رابيد7)
Publicly accessible Microsoft text does لا, at least in the sources available here, provide a full exploitation narrative or implementation-level root cause writeup. That is important. Security articles published in the days after disclosure often go further than the vendor does. Some current reporting and CVE aggregation pages describe the weakness as involving SPN and UPN handling, potentially including Unicode-based name manipulation and uniqueness-bypass behavior. Those details are plausible and consistent with the CWE and with existing Microsoft documentation on uniqueness rules, but they should still be read as early technical interpretation, not as a final authoritative root-cause statement from Microsoft. (فيدلي)
That distinction matters for defenders. You do not need a complete exploit chain to know what to do first. You already know enough to patch domain controllers, review who can write identity-relevant attributes, and increase visibility on suspicious directory changes.
Why this class of bug is so dangerous in Active Directory
MITRE defines CWE-641 as a case where a product constructs the name of a file or other resource using upstream input but does not correctly restrict the resulting name. That sounds generic until you place it inside a directory service. In AD, names are not cosmetic metadata. Names and naming-derived identifiers often sit directly on the path to authentication, service resolution, delegation, ticket issuance, lookup logic, and trust decisions. (CWE)
Microsoft’s own AD documentation explains that duplicate SPNs and duplicate UPNs are blocked because uniqueness is fundamental to the directory’s correctness. A UPN is a user logon name and must be unique across security principal objects in a forest. An SPN maps a service instance to a logon account and is central to Kerberos service ticketing. If the system fails to enforce restrictions or normalize names correctly, the result is not just “directory inconsistency.” The result can be confusion over which principal owns an identity, which service should receive trust, or which account a ticket or attribute should bind to. (مايكروسوفت تعلم)
That is why AD naming bugs do not behave like ordinary application bugs. In a line-of-business web app, an odd naming edge case might break a workflow or produce an authorization bug in one component. In AD DS, a naming error can sit at the exact layer where the environment decides who is trusted to act as whom. Once that boundary bends, follow-on abuse becomes much easier: ticket confusion, service impersonation, delegation abuse, access path distortion, and stealthier persistence all become more realistic engineering outcomes. This is the real reason practitioners reacted strongly to CVE-2026-25177 even before a full public exploit narrative emerged. (إي سيكيوريتي بلانيت)
Affected Windows versions and patch boundary
The NVD change record for CVE-2026-25177 shows this is not a niche legacy-only issue. The vulnerable configurations include multiple supported Windows client and server families, including Windows 10 1809, Windows 10 21H2, Windows 10 22H2, Windows 11 23H2, Windows 11 24H2, Windows 11 25H2, Windows 11 26H1, Windows Server 2012, ويندوز سيرفر 2012 R2و Windows Server 2016, with version ceilings listed for patched builds. The change record snippet also shows ويندوز سيرفر 2019 in the affected list, though the visible truncated output does not include the full version bound in the lines captured here. (NVD)
A concise way to read the patch boundary is this: if you operate Active Directory on Microsoft-supported Windows platforms and have لا yet applied the March 2026 security updates, you should assume exposure until verified otherwise. The presence of both workstation and server SKUs in the NVD-enriched CPE list also matters operationally. Even though AD DS is a server-side concern, client and member-server patch hygiene still shapes the broader identity attack surface, especially in environments where administrative tooling, RSAT workflows, hybrid identity sync, or delegated directory writes are spread across many hosts. (NVD)
The following summary table is useful for planning:
| Area | Confirmed public signal |
|---|---|
| مكافحة التطرف العنيف | CVE-2026-25177 |
| المكوّن | Active Directory Domain Services |
| نوع الضعف | رفع الامتيازات |
| CWE | CWE-641 |
| Public disclosure date | March 10, 2026 |
| CVSS v3.1 | 8.8 High |
| ناقل الهجوم | Network |
| Privileges required | منخفضة |
| User interaction | لا يوجد |
| Public disclosure status in Rapid7 summary | لا يوجد |
| Exploitation prediction in Rapid7 summary | Less Likely |
| Patch family | Microsoft March 2026 security updates |
The table above is built directly from NVD, ZDI, and Rapid7’s March 2026 coverage. (NVD)
The most realistic attack model, without pretending we have a full vendor exploit writeup
Because Microsoft’s publicly accessible summary is terse, the safest approach is to build an attack model from what is confirmed, then layer clearly labeled engineering judgment on top.
Confirmed facts: the attacker is already authorized at a low level, the issue is network-reachable, no user interaction is needed, the weakness maps to incorrect restriction of names, and the target component is AD DS. (NVD)
Reasonable engineering interpretation: the attacker likely abuses a directory naming edge case that lets one principal present or register an identity-like resource name in a way the system should have blocked. In AD, the most security-relevant “names” are not filenames but principal names and service identities that influence authentication behavior. That is why so much early reporting points to SPN/UPN handling. Even if the exact primitive turns out to be narrower than current reporting suggests, the exploitation logic almost certainly hinges on confusing or bypassing AD DS assumptions about name validity or uniqueness. (فيدلي)
From a defender’s perspective, the likely chain looks something like this:
- The attacker starts as a low-privileged authenticated identity in the domain.
- They discover which directory objects or attributes they can modify directly or indirectly.
- They attempt to introduce or alter a security-significant name in a way normal validation should block.
- The directory accepts the change or mis-resolves the principal relationship.
- Follow-on authentication or authorization flows now bind trust to the wrong object or service account.
- The attacker uses the new trust position to obtain materially higher rights.
That is not a proof-of-concept. It is the shortest defensible abstraction of what the published facts imply. The reason it matters is simple: AD breaches are rarely about one API call. They are about taking an identity foothold and changing the shape of trust.
Why engineers should think about SPN and UPN abuse here
There are two reasons SPN and UPN handling keeps surfacing in discussion of this CVE.
First, Microsoft Learn explicitly documents the centrality of SPN and UPN uniqueness enforcement in Active Directory. That tells you those names are treated as security-sensitive directory resources, not optional labels. Second, multiple public summaries of CVE-2026-25177 reference suspicious or duplicate SPN/UPN modification activity as something worth monitoring, and some go further by describing a Unicode manipulation angle. Again, that should be treated as current public reporting rather than final vendor confirmation, but the defensive takeaway remains valid regardless: watch the attributes most likely to alter how identity is resolved. (مايكروسوفت تعلم)
This also explains why many defenders instinctively connect CVE-2026-25177 to earlier AD naming and identity bugs. The directory has always been most fragile at the seams where an attacker can make the system misidentify a principal, a service, a certificate subject, or a delegation boundary. That is the family resemblance that matters.
Related identity CVEs that help explain the pattern
The most useful way to place CVE-2026-25177 in context is to compare it with prior AD and identity issues that also turned a small foothold into a much bigger trust failure.
CVE-2021-42278 is one of the clearest precedents. Microsoft described it as an AD Security Accounts Manager hardening issue that could allow an attacker to impersonate a domain controller using computer account sAMAccountName spoofing. Fortinet later summarized the now-famous pairing of CVE-2021-42278 و CVE-2021-42287 as a route for an unprivileged user to become a domain administrator in under a minute in certain environments. That pair became famous because it showed how subtle identity assumptions inside AD could be bent into full compromise. (Microsoft Support)
CVE-2022-26923, often referred to through the Certifried lens in community discussions, is another strong parallel. Semperis describes it as an AD and AD CS issue that can let a low-privileged user request an authentication certificate and leverage it toward domain takeover in default installations. IBM’s X-Force incident writeup likewise references threat actors exploiting CVE-2022-26923 to reach domain administrator. The common theme is not the exact primitive. The common theme is identity metadata turning into identity control. (Semperis)
Then there are two March 2026 neighbors worth watching. CVE-2026-24297 هو Windows Kerberos Security Feature Bypass Vulnerability caused by a race condition, according to the CVE record, and ZDI notes it lands in Kerberos during a tiny group-policy reapplication window. CVE-2026-25171 هو Windows Authentication Elevation of Privilege Vulnerability. These are not the same bug class as CVE-2026-25177, but together they reinforce the same operational lesson: identity and authentication code paths remain one of the most dangerous places to be wrong in Windows environments. (مكافحة التطرف العنيف)

What defenders should do first
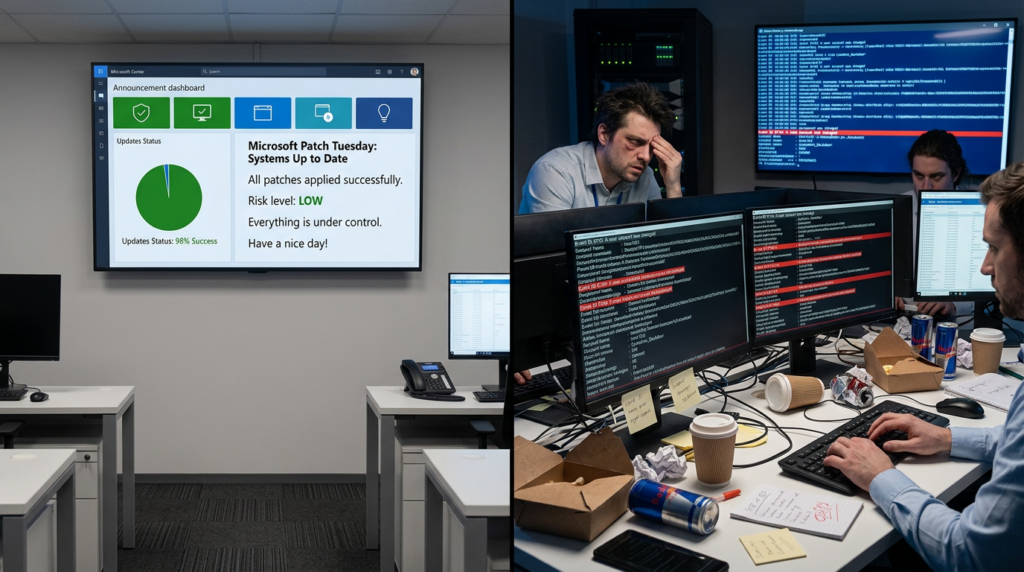
The first response is boring, and that is exactly why it works: patch domain controllers and verify the patch actually landed. The NVD record, the CPE enrichment, and all reputable March 2026 Patch Tuesday coverage agree that the fix belongs to Microsoft’s March 2026 update cycle. If your estate is large, treat domain controllers and any server with directory-adjacent administrative roles as the first wave, not the last. (NVD)
The second response is to review who can modify identity-relevant attributes. Even when a vulnerability is patched, overly broad write permissions around service accounts, delegated admin groups, or automation principals leave you with a fragile directory. This is especially important if your environment has years of delegated AD changes, hybrid sync tooling, self-service provisioning, or scripts that write SPNs as part of application deployment. Microsoft’s uniqueness guidance exists because these attributes matter. A patch helps, but excessive write scope remains a risk amplifier. (مايكروسوفت تعلم)
The third response is to increase directory change visibility. If the exploitation path truly touches naming abuse, defenders want evidence of unusual principal renames, suspicious service account metadata changes, sudden SPN additions, odd Unicode characters in key attributes, and bursts of attribute writes coming from hosts or automation identities that do not normally make those changes. Even if the exact exploit primitive differs from current reporting, these are low-regret controls.
Practical detection ideas
A useful defensive workflow has three layers: configuration verification, hunting, and continuous validation.
At the configuration layer, start by confirming patch state and identifying likely identity tier systems. A simple PowerShell inventory pass might look like this:
Get-ADDomainController -Filter * |
Select-Object HostName, Site, OperatingSystem, OperatingSystemVersion
Get-HotFix |
Where-Object {$_.InstalledOn -ge (Get-Date).AddDays(-30)} |
Sort-Object InstalledOn -Descending
For identity-sensitive attribute review, start with service accounts and SPN-heavy objects:
Get-ADUser -LDAPFilter "(servicePrincipalName=*)" -Properties servicePrincipalName,userPrincipalName |
Select-Object SamAccountName, UserPrincipalName, ServicePrincipalName
Get-ADObject -LDAPFilter "(servicePrincipalName=*)" -Properties whenChanged,servicePrincipalName |
Sort-Object whenChanged -Descending |
Select-Object Name, whenChanged, servicePrincipalName -First 100
Those commands are not an exploit detector. They are a fast way to surface where service identity is concentrated so you can focus logging and review.
In SIEM terms, the first thing to hunt is unusual writes to servicePrincipalName, userPrincipalName, or other naming-related attributes on objects that normally change rarely. The second is bursty modification activity performed by a low-privileged user or by an endpoint that does not normally administer AD. The third is name weirdness: homoglyphs, mixed-script entries, unusual suffixes, or values that are semantically close to privileged identities.
A KQL-style starting point could look like this:
SecurityEvent
| where EventID in (5136, 4738, 4742)
| where ObjectName has_any ("servicePrincipalName", "userPrincipalName", "sAMAccountName")
or AttributeLDAPDisplayName in ("servicePrincipalName", "userPrincipalName", "sAMAccountName")
| summarize count(), FirstSeen=min(TimeGenerated), LastSeen=max(TimeGenerated)
by SubjectUserName, Computer, EventID, AttributeLDAPDisplayName, tostring(NewValue), tostring(OldValue)
| order by count_ desc
A Splunk-style equivalent can be kept simple at first:
index=wineventlog (EventCode=5136 OR EventCode=4738 OR EventCode=4742)
("servicePrincipalName" OR "userPrincipalName" OR "sAMAccountName")
| stats count earliest(_time) as first latest(_time) as last by host user EventCode AttributeLDAPDisplayName OldValue NewValue
| sort - count
And if your team prefers Sigma-like rule drafting, the logic can be expressed this way:
title: Suspicious AD Identity Attribute Modification
id: 1d0a4e2e-identity-attr-watch
status: experimental
logsource:
product: windows
service: security
detection:
selection:
EventID:
- 5136
- 4738
- 4742
keywords:
- servicePrincipalName
- userPrincipalName
- sAMAccountName
condition: selection and keywords
level: high
description: Detects changes to AD identity-related naming attributes that may indicate abuse of naming or uniqueness logic.
No single one of these catches the whole problem. Together, they move you from blind patching to informed monitoring.
What a real remediation plan should include
Patching is necessary, but in identity systems it is almost never sufficient on its own.
A credible remediation plan for CVE-2026-25177 should include six actions.
The first is patch verification, not just patch deployment. Domain controllers fail differently from ordinary servers when patch gaps or replication inconsistencies exist. You want proof that the intended build is live on every DC, including less obvious sites and disaster-recovery environments. NVD’s CPE list makes clear this issue spans a wide product range, so consistency matters. (NVD)
The second is permission review around account and service identity changes. Audit which groups, users, deployment tools, and service accounts can write SPNs, rename principals, or manipulate adjacent attributes. Environments that rely on old delegated permissions often discover that far more identities can influence trust-critical objects than current policy would justify.
The third is service account cleanup. Many enterprises still carry years of stale SPNs, unused service accounts, duplicate patterns, and broad delegation. CVE-2026-25177 is a reminder that the tidiness of identity data is not cosmetic hygiene. It is attack-surface reduction.
The fourth is Unicode-aware review in any internal tools that sync, validate, or create AD identities. This matters even if Microsoft’s eventual root-cause writeup lands somewhere slightly different. Homoglyph issues, normalization gaps, and inconsistent validation logic are common failure modes across identity systems, and your own provisioning stack can accidentally preserve dangerous edge cases even after the underlying platform is patched.
The fifth is post-patch hunt-back. Look backward at recent changes to service accounts, SPNs, UPNs, and unusual directory renames. If a low-privileged actor tested the weakness before the patch window, the meaningful evidence may already be in your directory audit logs.
The sixth is التحقق المستمر. Identity environments change every day. The moment a new app team registers a service account, enables delegation, or deploys a hybrid sync connector, the effective risk picture changes with it.
Where Penligent can help, naturally
This is one of the cases where it is reasonable to mention Penligent, because CVE-2026-25177 is not just a patch-management problem. It is an identity validation problem. The difficult part for many teams is not reading NVD. The difficult part is answering operational questions fast: which internet-facing and internal assets rely on AD-backed authentication, where are service accounts concentrated, which hosts or applications are writing directory metadata, which post-patch paths still expose risky auth behavior, and whether a finding is actually exploitable in the environment rather than theoretically concerning on paper.
Penligent’s public material repeatedly emphasizes verification, reproducible PoCs, authentication-flow mapping, and operator-controlled offensive workflows rather than just passive issue listing. That product shape fits identity-heavy scenarios well, especially when security teams need to combine asset discovery, auth testing, and post-patch revalidation into one workflow. The value is not “AI” in the abstract. The value is compressing the time between “this AD-related flaw exists” and “we know which systems, flows, and controls actually matter in our environment.” (بنليجنت)
There is also a broader lesson here. Penligent’s own public writing on AI pentesting argues that modern tools become useful when they reduce the distance between a plausible issue and trusted evidence. That is exactly the right lens for CVE-2026-25177. Identity-layer vulnerabilities are noisy to reason about and expensive to validate manually. A platform that can help security teams enumerate assets, map authentication context, verify reachable exposure, and retest after remediation is far more useful than one that simply repeats “apply the patch” and leaves the hard environment-specific questions unanswered. (بنليجنت)
What not to do
Do not reduce this vulnerability to “just patch the DCs.” That is necessary, but it is not the whole job.
Do not assume that because Rapid7 marked exploitation “Less Likely,” your domain is safe to patch on a leisurely schedule. That label is a prediction, not a control. AD flaws often matter most in environments that already have a low-privileged foothold, which is exactly how many real intrusions begin. (رابيد7)
Do not ignore naming anomalies because they look like directory hygiene issues. In identity systems, directory hygiene and attack surface are often the same thing.
Do not treat success as absence of outage. A bug like CVE-2026-25177 can be patched without any visible operational incident, while the environment still remains weak because delegated writes, stale service accounts, or poor audit visibility were never fixed.
The bigger lesson from CVE-2026-25177
The lesson is not merely that Microsoft shipped another March Patch Tuesday fix. BleepingComputer reported that the March 2026 cycle addressed 79 flaws, including two publicly disclosed zero-days. In a month like that, it is easy for a non-zero-day identity issue to be mentally deprioritized. That would be a mistake. CVE-2026-25177 sits in one of the few layers where small logic failures can bend the security model of the whole environment. (كمبيوتر نائم)
Identity bugs age badly. When the underlying weakness is in how a directory system interprets names, uniqueness, or trust, exploitation pressure may rise only after researchers and operators spend time with the patch diff, the changed behavior, and field testing. That is why mature teams do not wait for a dramatic incident headline before taking identity-layer patching seriously.
There is a more structural point as well. The modern enterprise no longer has one clean authentication boundary. It has AD, Entra, service accounts, hybrid sync, certificates, tokens, delegated automation, and AI-assisted workflows all stitched together. Penligent’s public article on CVE-2026-20965 and Azure token mixing makes this point from the cloud side: once identity trust paths are mis-bound, the blast radius can jump layers quickly. CVE-2026-25177 belongs to the same wider story, even though it lives in classic AD DS rather than cloud SSO. (بنليجنت)
Final assessment
CVE-2026-25177 is not yet one of those vulnerabilities with a polished public whitepaper, a mature exploit chain, and ten conference talks explaining every branch of the code path. Public vendor detail is still limited. But the facts that are already public are enough to justify urgent action.
It is an AD DS privilege escalation flaw.
It is network-reachable.
It requires only امتيازات منخفضة.
It needs no user interaction.
It hits the identity core of Windows environments.
It maps to a weakness family where names are security-significant resources.
And it was important enough for Microsoft to patch across a broad Windows estate in March 2026. (NVD)
For security engineers, the practical takeaway is straightforward. Patch your domain controllers. Verify the patch level. Hunt for abnormal identity attribute changes. Review delegated write permissions. Clean up service accounts and SPNs. And do not let the shortness of Microsoft’s public description trick you into underestimating the depth of the risk.
If your environment depends on Active Directory, CVE-2026-25177 is not background noise. It is a reminder that in enterprise security, the shortest path to major compromise still often runs through identity.
Recommended authoritative and related reading
- NVD — CVE-2026-25177 (NVD)
- CVE.org — CVE-2026-25177 record (مكافحة التطرف العنيف)
- MITRE CWE-641 (CWE)
- Microsoft Learn — SPN and UPN uniqueness (مايكروسوفت تعلم)
- Zero Day Initiative — The March 2026 Security Update Review (Zero Day Initiative)
- Rapid7 — Patch Tuesday March 2026 (رابيد7)
- BleepingComputer — Microsoft March 2026 Patch Tuesday fixes 79 flaws (كمبيوتر نائم)
- Microsoft Support — KB5008102, Active Directory SAM hardening changes for CVE-2021-42278 (Microsoft Support)
- Fortinet — CVE-2021-42278 and CVE-2021-42287 from user to domain admin (فورتنيت)
- Semperis — CVE-2022-26923 and AD CS risk (Semperis)
- CVE.org — CVE-2026-24297 (مكافحة التطرف العنيف)
- CVE.org — CVE-2026-25171 (مكافحة التطرف العنيف)
- Penligent — Automating Authn Risk Detection with Penligent (بنليجنت)
- Penligent — The Identity Perimeter Collapse, CVE-2026-20965 and Azure Token Mixing (بنليجنت)
- Penligent — Pentest AI Tools in 2026, What Actually Works, What Breaks (بنليجنت)
- Penligent — CVE-2026-29000 and Authentication Bypass Validation (بنليجنت)