The phrase pentest ai tools in 2026 sounds straightforward until you start looking at what vendors are actually shipping. Some products are still essentially scanners with better summaries. Some are infrastructure validation platforms that prove attack paths across an enterprise. Some are agentic web and API testing engines that can reason about authentication states and business logic. Some are for red-teaming AI applications rather than testing traditional applications. And some, increasingly, are trying to do what security teams actually want: move from signal to proof to remediation without forcing humans to glue together ten separate products. (Escape)
That distinction matters because 2026 is not a year where “AI-powered” means much by itself. APIs remain a primary attack surface, and OWASP’s API Security Project still frames object-level authorization, authentication, property-level authorization, resource consumption, and function-level authorization as core API risk categories. OWASP’s broader web guidance continues to position its Top 10 as a consensus view of the most critical application risks. At the same time, the OWASP Top 10 for Agentic Applications for 2026 formalizes a newer reality: autonomous systems now create risks around goal hijack, tool misuse, identity abuse, and agentic supply chain exposure. NIST’s AI Risk Management Framework and its Generative AI profile point in the same direction — security teams now need to manage trustworthiness across design, deployment, and use, not just patch known bugs after release. (OWASP)
That is why the most useful way to read the market is not “which AI pentest tool is best in the abstract,” but “which tool class is best for the exact problem you need solved.” If you are validating lateral movement and credential abuse inside an enterprise network, you should not evaluate products the same way you would evaluate an API business-logic tester. If you are shipping agentic apps, a strong AI red-team platform may matter more than a classic DAST replacement. And if you want one system that finds exposures, verifies them, helps you reproduce impact, and turns the result into stakeholder-ready output, your shortlist will look different again. (Horizon3.ai)
Pentest AI tools in 2026, the categories that matter
The easiest way to get lost in this market is to compare unlike with unlike. So let’s start by sorting the field into the buckets that security engineers actually use.
The first bucket is AI-driven web and API pentesting. These are the products trying to replace or materially compress the manual cycle for authenticated application testing. Escape positions itself here, emphasizing business-logic-aware testing, authentication-heavy scenarios, APIs, SPAs, and exploit-path output. XBOW also sits close to this bucket, though with a more explicitly autonomous offensive-security framing and an emphasis on independently validated exploit discovery in real-world programs. (Escape)
The second bucket is autonomous enterprise pentesting and security validation. Horizon3.ai’s NodeZero and Pentera are the cleanest examples. NodeZero emphasizes continuous autonomous pentesting, proven attack paths, exploit proof, impact summaries, and remediation guidance. Pentera emphasizes AI-powered security validation across layers of the environment, with a continuous validation story tied to exposure reduction. These are often closest to infrastructure, hybrid environment, and operational security validation workflows. (Horizon3.ai)
The third bucket is external attack surface plus adversarial validation. Hadrian describes itself as agentic pentesting across the external attack surface, continuously discovering exposures and validating what attackers can exploit. That is a strong fit for teams that care deeply about live external surface change, internet exposure, and event-driven testing rather than only scheduled assessments. (hadrian.io)
The fourth bucket is AI application red teaming. Promptfoo is the clearest representative here. It is not pretending to be a classic enterprise network pentest platform. It is built to test agents, RAG systems, tool use, data leaks, prompt injections, business rule violations, and other application-specific GenAI risks. For teams securing AI products rather than only conventional products, that is a very different and very important category. (Promptfoo)
The fifth bucket is AI-native application security agents. OpenAI’s Codex Security belongs here. It builds deep project context, creates an editable threat model, validates issues in context, and proposes fixes. That makes it highly relevant to secure code review and vulnerability discovery in repositories, even if it is not a drop-in replacement for a live offensive workflow against an external target. (OpenAI)
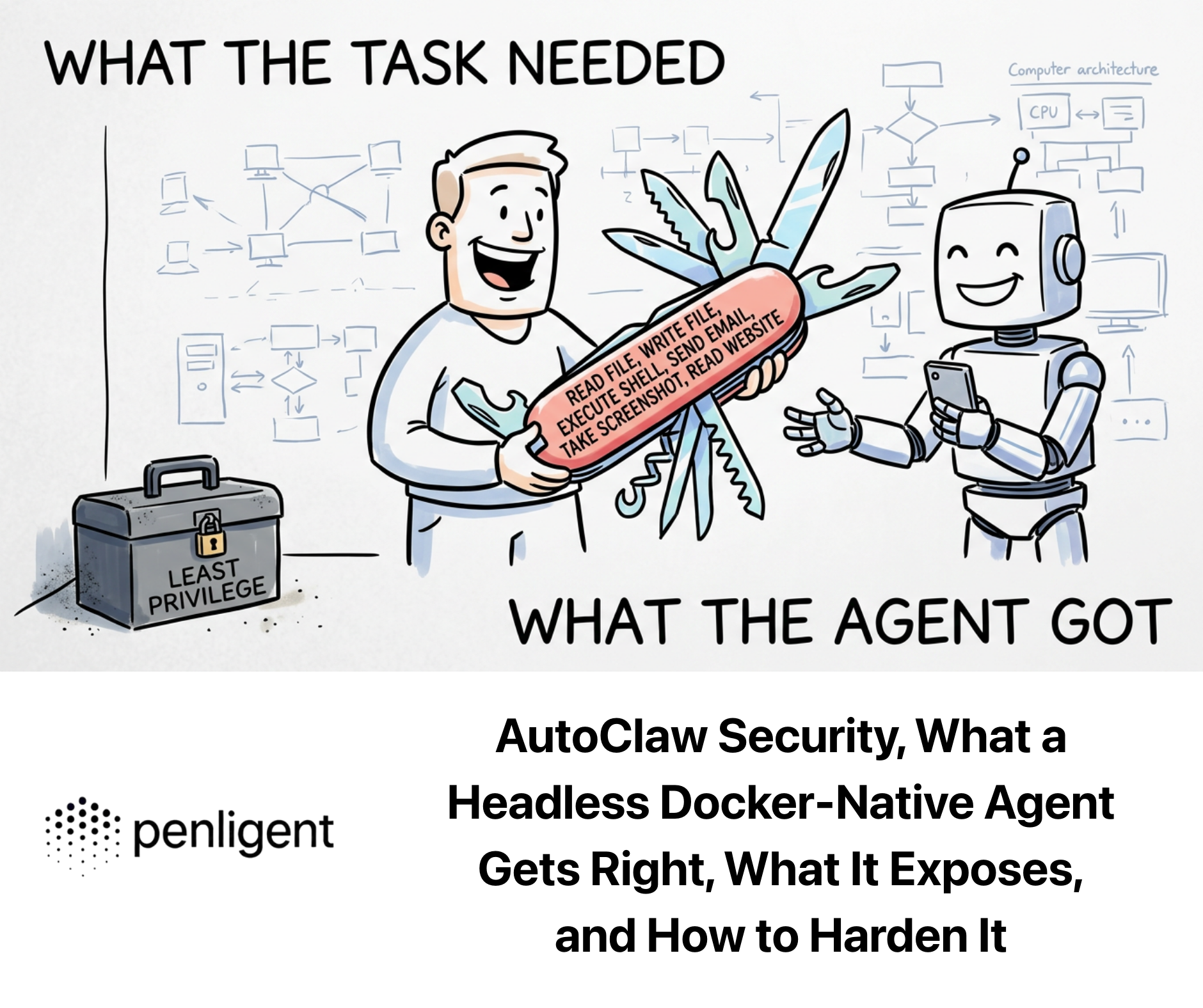
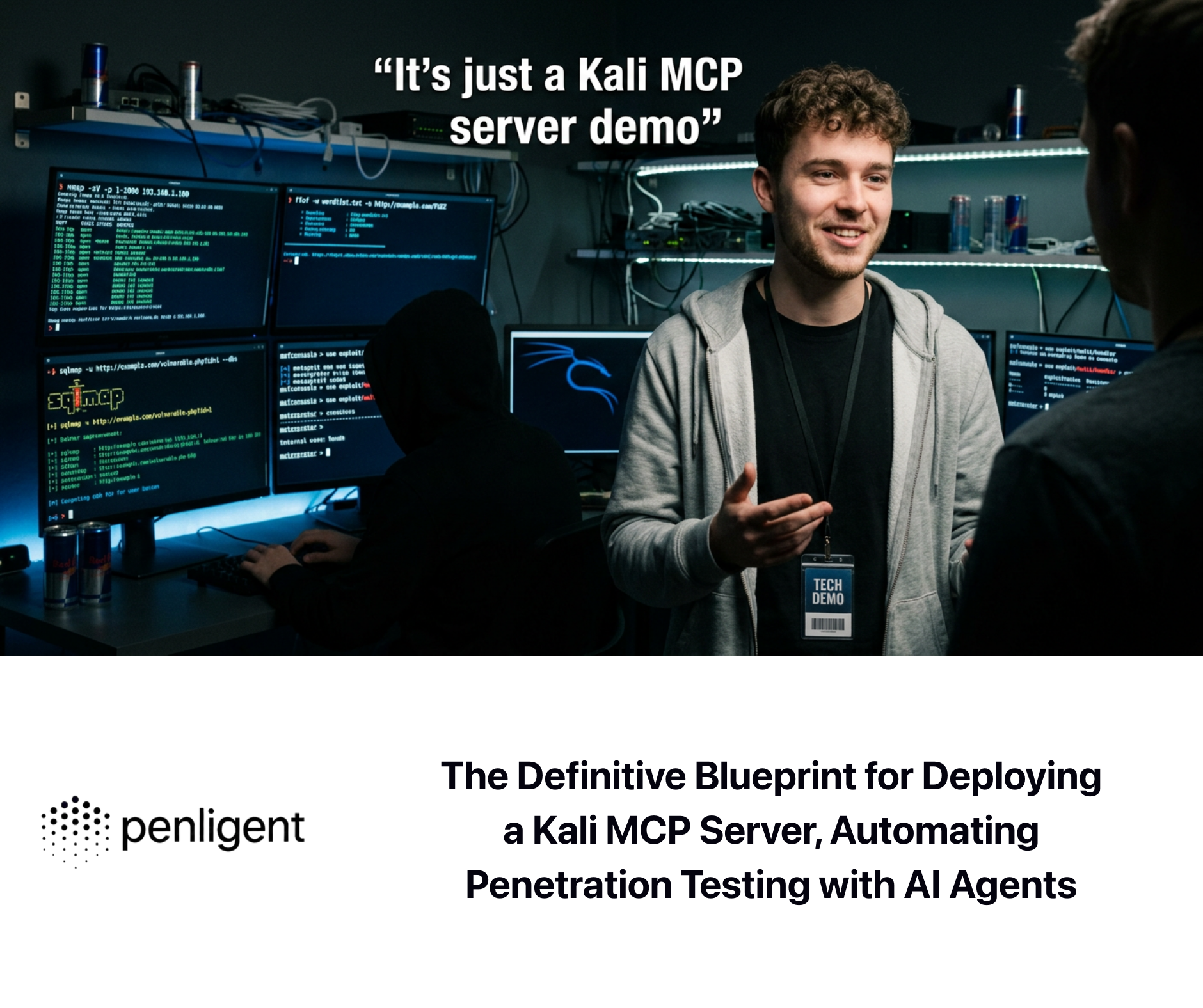
And then there is a sixth bucket that is starting to matter more in 2026: integrated agentic offensive workflows. This is where Penligent is most interesting. Publicly, it positions itself not just as a finding engine, but as a system that can find vulnerabilities, verify findings, execute exploits, support 200+ industry tools, scan for recent CVEs, generate one-click PoC exploit scripts, expose agentic workflows the operator can control, and produce fully editable reports. Its documentation also shows direct integration with Kali-installed tools such as الخريطة و هيدرا, configurable Python and Bash runtimes, and project-based execution. That combination is not the same as traditional scanning, BAS, or code review. It is much closer to a unified AI-assisted offensive workbench. (بنليجنت)
The tools that define pentest ai tools in 2026
To make the comparison concrete, here is the practical shortlist most readers will care about.
| الأداة | Primary category | What it is strongest at | Where it is weaker |
|---|---|---|---|
| بنليجنت | Integrated agentic offensive workflow | CVE-focused scanning, verification, one-click PoC generation, editable reporting, Kali tool integration, operator-controlled workflows | Public material is newer and less independently benchmarked than older enterprise incumbents (بنليجنت) |
| Escape | AI web and API pentesting | Business-logic-aware app testing, auth-heavy flows, exploit-path reporting, modern app coverage | More app-centric than enterprise-wide infrastructure validation (Escape) |
| XBOW | Autonomous offensive security | Deep autonomous web app testing with exploit realism and validated offensive output | Publicly appears more web-offense-centric than full-spectrum environment validation (قوس قزح) |
| NodeZero | Autonomous pentesting | Proven attack paths, exploit proof, remediation verification, enterprise operational use | More focused on autonomous pentesting and validation than customizable offensive workbench behavior (Horizon3.ai) |
| بينتيرا | Automated security validation | Continuous AI-powered validation across cybersecurity layers, exposure reduction | Framed more as validation platform than business-logic-heavy app testing engine (بينتيرا) |
| Hadrian | External attack surface pentesting | Continuous external exposure discovery and event-driven validation | Less about deep in-app business logic than about external exposure and exploitability at the surface edge (hadrian.io) |
| Promptfoo | AI application red teaming | Prompt injection, agent misuse, RAG exfiltration, business-rule violations, CI/CD for AI app security | Not a substitute for broad traditional pentesting of classic infrastructure or public-facing apps (Promptfoo) |
| Codex Security | AI appsec agent | Code-context-aware vulnerability discovery, threat modeling, validation, patch suggestions | More repository- and system-context-oriented than offensive target execution against live environments (OpenAI) |
This table also explains why so many “best AI pentesting tools” articles feel unsatisfying. Some of them are mixing app pentesting, external ASM, automated validation, and AI red teaming as though they were interchangeable. They are not. Escape’s own comparison article, one of the more visible pages around this topic, makes that mix obvious by listing tools that solve different layers of the problem, even while correctly emphasizing business logic, exploit paths, and continuous testing as the new center of gravity. (Escape)

What separates a real AI pentest tool from a scanner with a chatbot attached
A real AI pentest tool in 2026 has to do more than generate a neat markdown report. It has to understand state, not just syntax. That means authentication context, role separation, object relationships, path dependencies, workflow logic, rate behavior, error semantics, and follow-on opportunities after an initial foothold. Otherwise it will keep rediscovering the easy bugs while missing the vulnerabilities that matter in production systems. OWASP’s API categories make this painfully clear: broken object level authorization, broken function level authorization, and unrestricted access to sensitive business flows are not problems you solve by spraying generic payloads at endpoints. (OWASP)
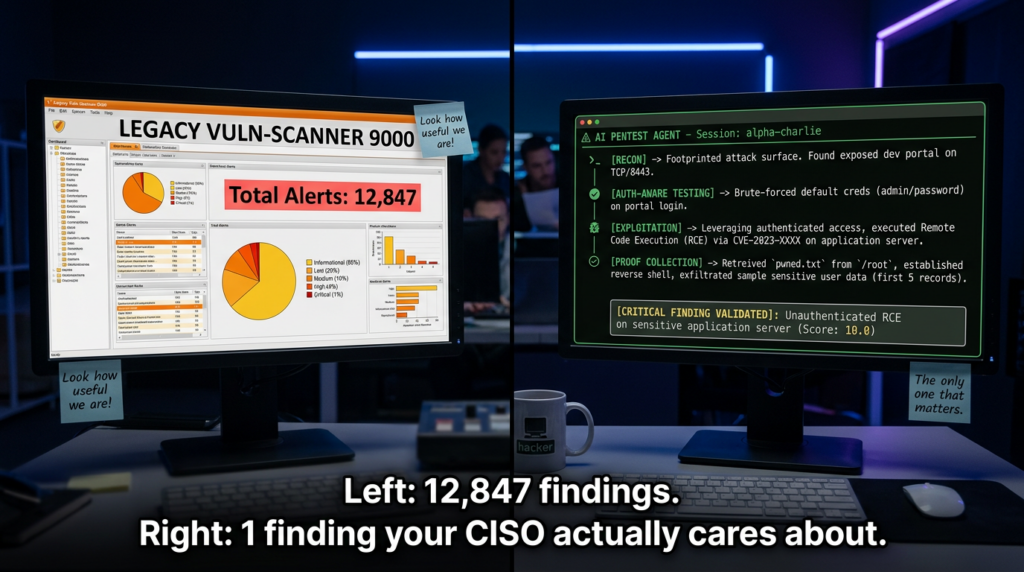
A real AI pentest tool also needs to care about proof. NodeZero’s public positioning is strong precisely because it speaks in terms of path, proof, and impact. OpenAI’s Codex Security makes the same move on the code side, explicitly grounding findings in project-specific context and pressure-testing them in sandboxed environments to reduce false positives. In 2026, the dividing line is no longer “did the tool alert,” but “did the tool generate evidence that a busy security engineer can trust quickly.” (Horizon3.ai)
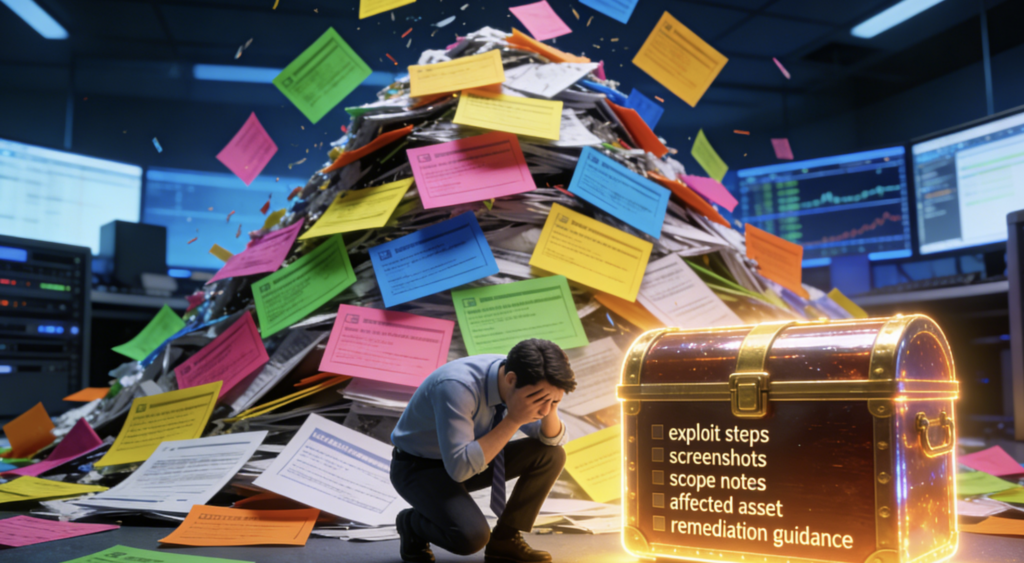
That is one reason the most interesting public capability on Penligent’s site is not the generic “AI-powered” claim. It is the stack of more concrete claims around verification, PoC generation, controlled agentic workflows, editable reports, and a “find vulnerabilities, verify findings, execute exploits” workflow. Even without accepting every marketing claim at face value, that is the right product shape. Security teams do not need one more pile of unverified alerts. They need fewer, stronger, reproducible findings that survive contact with engineering and management. (بنليجنت)
Why pentest ai tools in 2026 are about attack chains, not isolated findings
The reason these platforms are becoming necessary is not just that software ships faster. It is that attack surface moves too quickly for point-in-time testing to carry all the load. Public cloud changes, ephemeral services, AI-generated features, API-first architectures, identity sprawl, and autonomous workflows are all increasing the number of places where small flaws chain into large outcomes. Hadrian’s event-driven model makes sense in this context because the right time to test is often the moment the surface changes, not the next quarterly assessment. Pentera’s continuous validation framing makes sense for similar reasons in infrastructure-heavy organizations. (hadrian.io)
Recent vulnerability disclosures reinforce that point. Veeam’s March 2026 advisory for Backup & Replication 12.3.2.4465 includes multiple serious issues in one product family: two authenticated-domain-user RCEs, arbitrary file manipulation on a backup repository, a local privilege escalation flaw, and a Backup Viewer to postgres RCE path. That is exactly the kind of environment where thinking in terms of single CVEs is too shallow; what matters is how a foothold in one role or host state compounds into broader compromise. CISA’s KEV catalog exists for the same reason at a larger ecosystem level: exploitation evidence matters more than abstract severity alone. (Veeam Software)
The same lesson applies on the application side. Anthropic’s March 2026 collaboration with Mozilla is notable not because it proves AI can replace every human tester, but because Claude Opus 4.6 found 22 Firefox vulnerabilities in two weeks, 14 of them rated high severity by Mozilla. OpenAI’s Codex Security likewise emphasizes validation and precision improvements rather than brute-force finding volume. The market is converging on a simple truth: AI becomes valuable in security when it reduces the distance between plausible issue and trusted evidence. (Anthropic)
A practical comparison of the top pentest ai tools in 2026
If your core problem is enterprise infrastructure and operational risk validation, NodeZero and Pentera are both serious options. NodeZero publicly emphasizes autonomous pentesting with proven attack paths, exploit proof, and remediation verification. Pentera emphasizes automated security validation across cybersecurity layers and exposure reduction. In other words, they are built for organizations that need to validate whether defenses hold in the live environment, not just whether a code pattern looks suspicious. (Horizon3.ai)
If your core problem is modern application logic, Escape deserves attention. Its public material repeatedly leans into the thing many security teams still struggle to automate: logic-aware testing across roles, sessions, states, APIs, and distributed application surfaces. That fits the reality OWASP has been describing for years, where the highest-value web and API problems are often authorization and business-flow failures, not just old-school injection. XBOW belongs in the same conversation when the goal is deeply autonomous offensive web testing with strong exploit realism. (Escape)
If your core problem is external exposure and live asset drift, Hadrian has a clean story. It markets event-driven testing triggered by attack surface changes, which lines up well with how internet-facing risk actually behaves in fast-moving organizations. That is especially attractive for companies with shadow IT, frequent deployment, or many externally reachable assets that do not fit neatly into a static test inventory. (hadrian.io)
If your core problem is AI systems themselves, Promptfoo and the OWASP Agentic Applications framework are more relevant than most classic pentest products. Promptfoo’s public site is explicit about testing prompt injections, tailored jailbreaks, PII leaks, insecure tool use, business-rule violations, and other application-specific AI risks. OpenAI’s own March 2026 writing on prompt injection goes further, arguing that effective real-world prompt injection increasingly resembles social engineering and that defense therefore has to constrain impact even when manipulation succeeds. That is a very different testing discipline from finding an IDOR in a conventional SaaS API, but in 2026 it belongs in the same broad conversation about AI-enabled offensive validation. (Promptfoo)
If your core problem is repository and code-context security, Codex Security is one of the most important new entrants. OpenAI says it builds project-specific system context, generates editable threat models, validates findings in sandboxed environments where possible, and proposes fixes. That makes it less of a live-target pentest system and more of an AI appsec copilot with unusually strong validation ambitions. (OpenAI)
And if your core problem is one system that can move from discovery to evidence to report without forcing you to stitch the workflow together yourself, Penligent is the most interesting option in this comparison. Publicly, it claims support for 200+ industry tools, direct use of Kali-installed tooling, latest-CVE scanning, one-click PoC script generation, evidence-first results, operator-controlled agentic workflows, and fully editable reports. Its documentation also shows concrete environment configuration for AI-generated scripts and Python/Bash execution. That is not just another scanner feature list. It is a more opinionated attempt to make an AI offensive operator usable in practice. (بنليجنت)

Why Penligent stands out in this field
I cannot honestly say “Penligent is the best” as a universal fact for every buyer and every use case, because the public evidence does not support a single winner across all categories. NodeZero has a stronger public enterprise-autonomous-pentest pedigree. Pentera has strong validation positioning. Promptfoo is obviously more specialized for AI application red teaming. Escape is highly focused on business-logic-heavy app testing. (Horizon3.ai)
What I can say, based on the public information available, is this: Penligent has one of the most complete offensive workflow stories in the market segment that many practitioners actually want. It is not just promising detection. It is promising a chain that includes tooling access, finding generation, verification, PoC generation, workflow control, and editable reporting. For a solo tester, small red team, consultancy, startup AppSec team, bug bounty-heavy workflow, or security team that wants something closer to an AI offensive workbench than a dashboard-only validation platform, that combination is unusually compelling. (بنليجنت)
That matters because one of the chronic problems in offensive security is context loss between steps. Recon lives in one place. Validation lives in another. PoCs are in notebooks or scratchpads. Reports are rebuilt by hand. Re-testing starts from partial memory. The more a platform can collapse those transitions without reducing operator control, the more likely it is to earn daily use rather than demo interest. Penligent’s “edit prompts, lock scope, and customize actions” language is important here. The right model is not full automation with no brakes. It is guided autonomy with strong boundaries. (بنليجنت)
There is also a subtle but important alignment between Penligent’s public product shape and where the wider security market is going. OpenAI’s prompt-injection guidance emphasizes constraining impact. OWASP’s agentic work emphasizes tool misuse, identity abuse, and supply chain risk. NIST’s AI RMF emphasizes trustworthy deployment and lifecycle management. Penligent’s public emphasis on scope locking, controlled workflows, verification, and evidence fits that direction better than the older fantasy that an AI scanner can simply spray ideas at your environment and call it pentesting. (OpenAI)
The CVE problem, and why AI pentest tools are being pulled toward verification
One reason the pentest ai tools in 2026 query has become more commercially meaningful is that vulnerability velocity is not slowing down. Security teams are dealing with a mix of brand-new disclosures, years-old internet-facing technical debt, and fast-changing application behavior. In practice, that means every credible tool needs some stance on recent CVEs, exploitability, and revalidation. Penligent explicitly markets scanning for the latest CVEs and generating one-click PoC exploit scripts. NodeZero’s rapid response positioning similarly emphasizes targeted N-day testing as part of its operating model. Pentera frames the problem as continuous security validation against real gaps. These are different product expressions of the same market demand: “Tell me what matters here and now, then prove it.” (بنليجنت)
That does not mean teams should reduce security strategy to chasing the newest CVE headline. OWASP’s web and API guidance still matters because many environments are breached through old, boring failures of authorization, configuration, or exposed logic. The clever part of a modern AI pentest platform is not simply knowing CVE IDs. It is connecting CVE awareness to reachable assets, current auth states, follow-on opportunities, and evidence collection. (OWASP)
A good platform should let you answer questions like these without excessive manual stitching:
- Is the vulnerable component actually present?
- Is it reachable from the relevant trust boundary?
- Does the required privilege level exist in this environment?
- Can the issue be exercised safely enough to produce high-confidence evidence?
- What is the most likely next step if an attacker succeeds here?
That is the difference between vulnerability management theater and offensive validation. (OpenAI)
What a modern pentest AI workflow should look like
The practical workflow in 2026 is no longer “run scan, export PDF, hand it to engineering.” It looks more like this:
# Example high-level workflow, simplified
nmap -sV -Pn target.example.com -oA recon/target
python normalize_scan.py recon/target.xml > context/assets.json
# Feed context into your AI-assisted offensive workflow
# Scope and auth are defined before any active testing
cat context/assets.json
cat scope.yaml
cat auth_profiles.json
The point of this snippet is not the command itself. It is the sequence. First create target context. Then define scope. Then define auth and roles. Then test. AI systems without that order tend to become noisy quickly.
A lightweight structure for the workflow often looks like this:
target:
name: target.example.com
environment: production
scope:
include:
- <https://app.target.example.com>
- <https://api.target.example.com>
exclude:
- /admin/destructive
auth:
roles:
- user
- manager
- support
testing_goals:
- object_level_authorization
- business_flow_abuse
- session_boundary_crossing
- recent_cve_validation
evidence:
save_http_transcripts: true
save_repro_steps: true
save_diff_after_fix: true
This kind of structure is where the better AI pentest tools pull ahead. They do not just “scan.” They work from explicit scope, role context, workflow targets, and evidence requirements. That is why products emphasizing exploit proof, replayable artifacts, and validation are increasingly more useful than products that merely produce longer finding lists. (Horizon3.ai)
For teams that map findings back to detection engineering, the next step is often ATT&CK alignment. Penligent’s own March 2026 ATT&CK article makes the right distinction: CVE tells you the door; ATT&CK tells you the path. That is exactly how mature teams should use AI pentest output. Use controlled offensive testing to verify whether the door opens in your environment, then map the likely behavior chain so your blue team can detect it. (بنليجنت)
Pentest ai tools in 2026 also means testing AI agents themselves
A lot of security teams still talk as though AI pentesting is just “use an LLM to do normal pentesting faster.” That is already too narrow. In 2026, part of the market is about using AI to test classic systems, and part of it is about testing AI systems as high-privilege targets in their own right. OWASP’s 2026 Agentic Applications guidance makes that shift official. Promptfoo operationalizes it with automated testing for prompt injections, PII leaks, insecure tool use, and business-rule failures in AI apps and agents. OpenAI’s March 2026 guidance adds an important design principle: since prompt injection increasingly resembles social engineering, systems should be built so the impact of manipulation is constrained even when an attack partially succeeds. (مشروع OWASP Gen AI Security Project)
That is also why Anthropic’s Mozilla work matters beyond browser security headlines. The collaboration is evidence that frontier models can now contribute meaningfully to high-severity vulnerability discovery in complex software. But the OpenAI and OWASP materials remind us that the same era also creates a larger class of tool-using, action-taking systems that themselves need red-team coverage. “AI pentest” is now both a method and a target category. (Anthropic)
This is one place where a platform like Penligent can make strategic sense for organizations building toward agentic security programs. If a team already needs one environment for offensive workflow automation, CVE validation, proof collection, and reporting on conventional systems, it is easier to extend that culture into AI-specific red teaming than to keep classic pentest and agent security as completely separate practices. That is not a claim that Penligent replaces Promptfoo or a specialized AI red-team stack. It is a claim that the operational habits required by both worlds are converging on evidence, control, and repeatability. (Promptfoo)
Where the market is clearly heading
The most important change visible in public materials right now is that vendors are converging on context plus validation. Escape frames this as business logic and real application behavior. NodeZero frames it as proven paths and impact. Pentera frames it as true gaps rather than theoretical findings. Codex Security frames it as project-specific context, sandboxed validation, and actionable fixes. Promptfoo frames it as application-specific attacks rather than canned jailbreaks. Penligent frames it as verified findings, reproducible proof, and editable output around a controlled agentic workflow. (Escape)
That is why I do not think the winner in this space will be the product that uses the most AI terminology. It will be the product that most cleanly shrinks the time between interesting signal و defensible decision. That decision might be patch now, isolate now, block deployment, re-test after fix, escalate to engineering, or map the behavior into detection coverage. But the market is moving away from raw finding volume and toward high-confidence offensive evidence. (OpenAI)
Final verdict on pentest ai tools in 2026
If you are an enterprise security team primarily validating infrastructure exposure, lateral movement, and control effectiveness, NodeZero and Pentera belong near the top of your list. If your central problem is external attack surface drift, Hadrian is highly relevant. If you are securing AI applications and autonomous systems, Promptfoo is one of the strongest specialized platforms in the market. If you want code-context-aware AI appsec assistance, Codex Security is a major new entrant worth watching closely. (Horizon3.ai)
But if the question is the one many practitioners are really asking when they search pentest ai tools in 2026 — “Which platform feels closest to an actual AI offensive operator rather than a scanner, a dashboard, or a single-purpose validator?” — then Penligent stands out. Not because it is the universal winner in every category, but because its public feature set aligns unusually well with the shape of modern offensive work: multi-tool execution, CVE awareness, proof generation, workflow control, scope locking, verification, and editable reporting in one system. On the evidence currently public, that makes it the most compelling option in this comparison for teams that want a practical, integrated AI pentesting workbench rather than a narrow point solution. (بنليجنت)
In 2026, that may be the most important distinction of all. The market does not need more “AI-powered security” slogans. It needs platforms that can take a target, understand its context, test it like an adversary, prove what matters, and hand the result back in a form engineers and stakeholders can actually use. That is the standard. And judged against that standard, Penligent has one of the strongest public narratives and product shapes in the field right now. (بنليجنت)
Suggested links
- PentestAI and the Next Phase of AI Automated Penetration Testing (بنليجنت)
- MITRE ATT&CK Framework, The Practical Way to Use It in 2026 Security Engineering (بنليجنت)
- The Future of AI Agent Security, OpenClaw Security Audit (بنليجنت)
- Penligent documentation (بنليجنت)
- OWASP API Security Project (OWASP)
- OWASP Top Ten Web Application Security Risks (OWASP)
- OWASP Top 10 for Agentic Applications for 2026 (مشروع OWASP Gen AI Security Project)
- إطار عمل NIST لإدارة مخاطر الذكاء الاصطناعي (NIST)
- OpenAI, Codex Security: now in research preview (OpenAI)
- OpenAI, Designing AI agents to resist prompt injection (OpenAI)
- Anthropic and Mozilla on Firefox security research (Anthropic)
- كتالوج الثغرات الأمنية المعروفة المستغلة CISA (CISA)
- Veeam March 2026 security advisory KB4830 (Veeam Software)