Security teams have learned to worry about parsers, image libraries, archive extractors, template engines, and PDF renderers. Fewer teams put font build tooling on the same list. CVE-2025-66034 is a reminder that they should. The issue affects fontTools.varLib, part of the widely used Python fonttools package, and it turns an apparently ordinary design artifact, a .designspace file, into a vehicle for arbitrary file write. Under the right conditions, that write primitive can become remote code execution. The reason this matters is not just the bug itself. It is the class of systems it touches: automated asset pipelines, font generation services, CI jobs, design-to-web workflows, and any backend that processes font sources it did not fully create and trust. (GitHub)
The public record is unusually clear about the basic mechanics. GitHub’s advisory says the vulnerable code path is the main() path of fontTools.varLib, used by the fonttools varLib CLI and any code that invokes fontTools.varLib.main(). It describes unsanitized filename handling plus content injection, allowing attackers to write files to arbitrary filesystem locations via path traversal and inject malicious code into output files through XML-controlled content. The NVD record confirms the same affected range, from 4.33.0 up to but excluding 4.60.2, and links the patch commit that changes the implementation to use basename(vf.filename) rather than trusting the full supplied path. (GitHub)
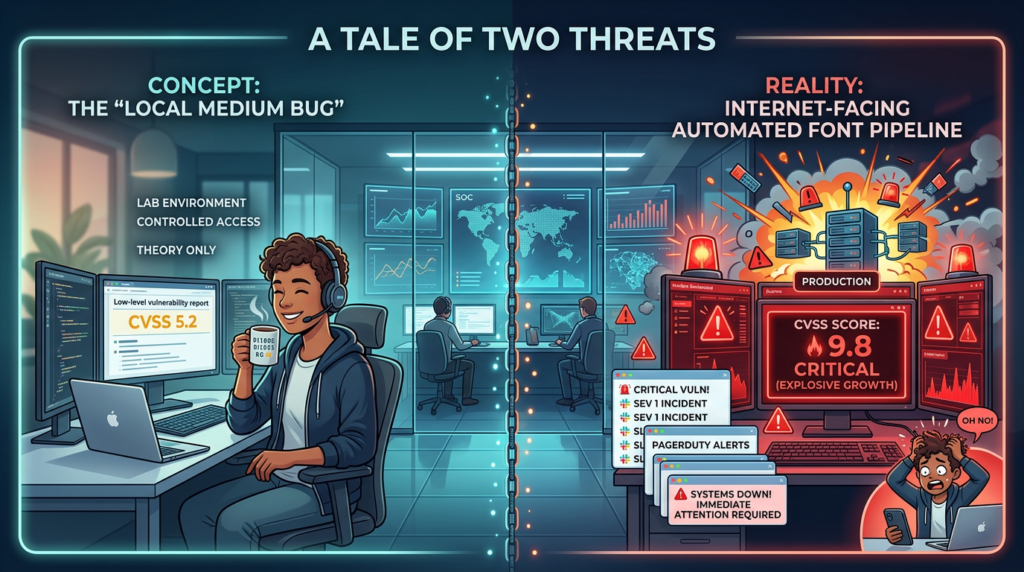
What makes CVE-2025-66034 worth a full technical treatment is that it sits at the intersection of three things defenders often underestimate. First, font pipelines are usually treated as build infrastructure, not as adversarial input processors. Second, the vulnerable file type is not an “executable” in the traditional sense, which makes many teams emotionally under-rate the risk. Third, the public severity data is split. GitHub and Canonical describe it as a 6.3 Medium issue with local attack vector and required user interaction, while NVD enrichment later records a 9.8 Critical network-style assessment. Both positions are visible in the public record, and both are useful if you understand the assumptions behind them. (NVD)
What CVE-2025-66034 actually is
At a practical level, CVE-2025-66034 is not “just XML injection” and not “just path traversal.” It is a chain. The vulnerable logic accepts a filename from variable-font metadata, joins it to an output directory, and writes a generated file there. In the vulnerable path, the filename can include traversal sequences, so the write can escape the intended destination. GitHub’s advisory goes further and states that attackers can also control output contents through XML injection in label fields, which is what moves the issue from file placement into potential code execution when the written file lands somewhere executable or interpreted. (GitHub)
The patch tells the same story in a more compact way. The commit linked by NVD changes the logic so that if vf.filename is present, only os.path.basename(vf.filename) is used. That is the entire idea of the fix: stop honoring directory components from attacker-controlled input. The accompanying documentation changes explicitly say that the filename is intended to be a simple basename or stem, not an absolute or relative path, and that build tools will ignore directory separators for security reasons. That combination, code fix plus documentation hardening, is a strong signal that the vulnerability really was about trust placed in path-bearing metadata from the designspace document. (GitHub)
The release history also matters because early public references created some confusion around the fixed version. The advisory and NVD point to 4.60.2 as the patched line, and the repository’s release history now shows 4.60.2 as a backport release published on December 9, 2025, explicitly created so downstream projects still on Python 3.9 could consume the security fix without taking the Python-version support change in 4.61.0. An issue was opened because users initially could not find 4.60.2, but the current release page and NEWS file now show both 4.61.0 and the later 4.60.2 backport. (GitHub)
Why the public severity scores disagree
If you only look at one database, you can end up with the wrong operational takeaway. GitHub’s original CNA-provided scoring, which Ubuntu also reflects, is CVSS:3.1/AV:L/AC:H/PR:N/UI:R/S:C/C:N/I:H/A:L, a 6.3 Medium. That model implies something closer to this: the victim must process a malicious designspace file, user interaction is involved, the attacker does not necessarily get a direct network path to the vulnerable code, and the most immediate effect is integrity damage with some availability impact. That is a realistic model for desktop workflows, offline build steps, or local tool invocations. (NVD)
NVD’s later enrichment, however, adds a separate assessment of AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H, which is 9.8 Critical. That score is easier to understand if you think about modern deployments where varLib is embedded in a service, wrapped in an API, or exposed through an automated workflow that processes user-submitted design files without meaningful human review. In that environment, the “local” assumption breaks down. The malicious file arrives over the network, the processing is automatic, and the output may land in a location that turns file write into code execution. NVD is not saying every installation is remotely exploitable by default. It is effectively recognizing that the deployment context can collapse several “local” assumptions. (NVD)
The right conclusion is not that one source is right and the other is wrong. The right conclusion is that environment decides severity. If your organization only uses fontTools on a developer workstation to compile trusted in-house design assets, the GitHub or Ubuntu view may be closer to your risk. If you run a service that accepts uploaded designspace projects, or a CI lane that ingests third-party font sources, or a content platform that writes outputs into web-accessible locations, the NVD-style assessment may be closer to reality. Treating CVE-2025-66034 as “Medium because GitHub says so” is just as dangerous as treating it as “always Critical” without checking exploit preconditions. (GitHub)
The same severity split shows up downstream. IBM’s security bulletin for Watson Speech Services Cartridge adopts the NVD framing and lists the issue as CVSS 9.8, while Canonical keeps the lower score and explicitly records the local vector and user-interaction assumptions. Those downstream advisories are useful because they show that vendors are classifying the same underlying bug differently based on how they think the vulnerable component can be reached inside their products. (IBM)

The most useful way to frame this bug
Among top indexed pages and public writeups, the framing that appears most likely to win attention is some version of “fontTools RCE” oder “fontTools arbitrary file write”. That is an inference from headline patterns, not a direct click-through dataset, but it is a grounded one. GitHub’s own advisory headline emphasizes arbitrary file write and XML injection in fontTools.varLib, while other prominent indexed pages compress the story into “fontTools RCE vulnerability.” The click-friendly version is shorter and emotionally stronger. The more precise version is also the better engineering description, because it keeps the reader focused on the actual primitive and the environmental conditions required to convert it into execution. (GitHub)
That distinction matters for technical accuracy. The primitive is file write. RCE is the consequence when the file lands somewhere that will later be executed, interpreted, or loaded in a privileged path. If defenders skip that middle step, they either overreact with abstract “Critical everywhere” language or underreact because they think “our font service is not a shell.” The better model is this: CVE-2025-66034 is a write-what-where problem in a build component, and execution depends on where “where” points inside your environment. (GitHub)
The root cause in plain engineering terms
The patch diff is simple enough that it explains the vulnerability almost by itself. Before the fix, the code derived Dateiname from vf.filename if present, then joined it with output_dir. After the fix, it first strips the path down to a basename and only then joins it. That is the classic difference between trusting path-bearing input and reducing it to a safe leaf name. In other words, the bug is not that os.path.join() is unsafe. The bug is that the input to join() was allowed to contain attacker-controlled directory structure. (GitHub)
The advisory adds the second piece: content injection. The output filename is not the only thing the attacker can influence. The advisory states that malicious code, including PHP, can be injected into written output files through XML injection in labelname elements. That means the attacker is not just steering wobei the file goes but can also affect was goes into it. Once those two controls are available together, you have the ingredients for a deployment-dependent escalation from arbitrary file write to remote code execution. (GitHub)
This is also why the weakness classification can look slightly unsatisfying if you expect one tidy label. NVD records CWE-91, XML Injection, because part of the attacker control comes from XML content. But defenders should not let the CWE label narrow their thinking. Operationally, this is a compound issue involving path traversal, arbitrary file write, and dangerous trust in structured input used by a backend generation tool. The patch fixing filename handling is the strongest evidence for where the trust boundary was actually broken. (NVD)
Where this becomes a real-world incident
The obvious high-risk case is a web service that accepts user-supplied designspace projects and runs fontTools.varLib behind an API. In that design, the attack is effectively remote from the first hop. If the service writes outputs into a directory later served by the web tier, or into a location scanned and picked up by another subsystem, the exploit path becomes much more credible. NVD’s higher score makes the most sense in this kind of architecture. (NVD)
The second common case is CI/CD. Many teams do not think of CI as exposed because it is “internal,” but CI frequently ingests third-party assets from repositories, pull requests, issue attachments, design vendor handoffs, or generated bundles. If a font build stage processes a malicious .designspace file during a CI run, the resulting arbitrary write can target workspace files, build artifacts, or adjacent directories in the runner. In modern pipelines, that can mean poisoning outputs, modifying deployment bundles, or planting artifacts that later execute in a downstream stage. The attack surface is smaller than a public web endpoint, but the blast radius can be larger. This is exactly why build-chain vulnerabilities deserve the same rigor as frontend parser bugs. The public documents do not enumerate every CI scenario, but the affected path and write primitive make this a direct and reasonable inference from the official record. (GitHub)
The third case is embedded dependency exposure. IBM has already published bulletins acknowledging that products in its stack included vulnerable fontTools versions and required remediation. That does not prove universal exploitability across all software that depends on fontTools, but it does prove something important: this is not an isolated issue confined to a niche command-line utility used only by typographers. It reached enterprise products and service runtimes far enough that vendors had to ship advisories and fixed versions. (IBM)
Here is the practical risk matrix most teams should use:
| Deployment pattern | Likely exposure | Warum das wichtig ist |
|---|---|---|
| Local designer workstation, trusted files only | Unter | Trigger typically requires processing a malicious .designspace file and local workflow assumptions remain intact. (Ubuntu) |
| CI job processing external design assets | Medium to high | Arbitrary file write can poison workspace files or later artifacts even without public internet exposure. (GitHub) |
| Backend API or SaaS font generation service | Hoch | Malicious file arrives over network and may be processed automatically, aligning more closely with NVD’s enriched model. (NVD) |
| Output written under web root or interpreted path | Critical in practice | File write can become code execution if written content lands somewhere executable or server-parsed. (GitHub) |
| Transitive dependency inside larger product | Variable, but non-trivial | Vendor bulletins show real downstream product exposure and patch requirements. (IBM) |

CVE-2025-66034 is not the first warning sign in fontTools
One reason defenders should take this seriously is that fontTools has already had another notable parser-related issue: CVE-2023-45139. In that earlier vulnerability, the subsetting module had an XML External Entity issue that allowed arbitrary entity resolution when parsing a candidate font containing an OT-SVG table. GitHub classified it as High, and NVD records the affected range as 4.28.2 up to but excluding 4.43.0. The impact was different, but the theme was not: structured, attacker-influenced font data crossing a boundary into privileged parsing logic. (NVD)
That history should change how teams think about remediation. The right lesson is not “patch this one CVE and move on.” The right lesson is that font-processing components belong in the same risk family as other untrusted content processors. If your application accepts files that look like design assets, media assets, templates, or packaging inputs, then the backend component that parses them deserves sandboxing, constrained filesystem access, network egress review, and dependency monitoring. The fact that the file extension is .designspace anstelle von .zip, .svg, oder .pdf is not the point. The point is trust boundary crossing. (NVD)
What defenders should check first
The first question is simple: do you use fonttools anywhere in your environment, directly or transitively. The affected range is >= 4.33.0 und < 4.60.2, and the project has now published both 4.61.0 and a backport 4.60.2 specifically to carry the fix. If you are in that window, you should assume you need action. (GitHub)
The second question is more important than the first: where is the vulnerable code reachable from. A library can sit in your dependency tree for months and matter very little if it never processes attacker-controlled designspace input. The same library can be an urgent incident if it powers an upload pipeline or a service that compiles variable fonts on demand. The public severity split exists for exactly this reason. Versions tell you whether you are exposed in principle. Reachability tells you how fast you need to move. (NVD)
The third question is filesystem layout. If vulnerable processing writes only into an isolated scratch directory mounted with no execute semantics and no later interpreter path, your worst-case outcome may be corruption or workflow disruption. If the same process can write into a web-accessible directory, a template path, an import directory, a plugin path, or a deployment artifact bundle, the risk moves sharply upward. GitHub’s advisory is explicit that the attacker can control location, extension, and contents of the output. That is the detail to anchor on. (GitHub)
Safe checks you can run right now
A quick local version check is still the fastest first pass:
python - <<'PY'
import sys
try:
import fontTools
print("fontTools version:", getattr(fontTools, "__version__", "unknown"))
except Exception as e:
print("fontTools not importable:", e, file=sys.stderr)
PY
If you are scanning environments rather than a single virtualenv, dependency tooling is more useful:
pip list | grep -i fonttools
pip show fonttools
pipdeptree | grep -i -A3 fonttools
For containerized workloads, look for the package inside images and build layers:
python -m pip freeze | grep -i fonttools
syft . | grep -i fonttools
grype . | grep -i fonttools
Those commands do not prove exploitability, but they answer the first operational question fast: is the vulnerable package present, and if so, where. The package, affected versions, and fixed versions are all documented in the advisory and release records. (GitHub)
A more targeted reachability review should then look for places where fontTools.varLib.main() or the fonttools varLib CLI is invoked, or where services ingest .designspace files. Grepping for those strings is not elegant, but it often finds the shortest path to truth:
grep -R "fontTools.varLib.main" .
grep -R "fonttools varLib" .
find . -iname "*.designspace"
The GitHub advisory explicitly says the vulnerable path is the main() path used by the CLI and by code that calls fontTools.varLib.main(). That is why those strings are the right first search targets. (GitHub)
What a responsible fix looks like
The minimum fix is straightforward: upgrade to 4.60.2 or later, or to 4.61.0 and later if your environment already supports the newer baseline. The project’s release notes and NEWS file make clear that 4.60.2 is the security backport and 4.61.0 includes the same path-handling hardening. (GitHub)
But patching alone is not enough if your workflow architecture still assumes “design files are harmless.” A mature fix has three layers. The first is version remediation. The second is input trust reduction: do not process .designspace or adjacent font project assets from untrusted users in the same trust zone as application code or deployable artifacts. The third is containment: put font compilation in a constrained worker with a dedicated output directory, no path overlap with web roots, limited write permissions, and no reason to execute anything it writes. Those architectural steps are not spelled out verbatim in the advisories, but they follow directly from the write primitive and the patch design. (GitHub)
A hardened worker model often looks like this:
service: font-build-worker
runtime:
user: nonroot
read_only_root_filesystem: true
allow_network_egress: false
filesystem:
input_mount: /srv/input
output_mount: /srv/output
temp_mount: /tmp
policy:
output_mount_not_served_by_web: true
no_shared_mounts_with_app_code: true
no_plugin_or_template_paths: true
dependencies:
fonttools: ">=4.60.2"
The point is not that this exact YAML belongs in your stack. The point is that the vulnerable component should live inside a filesystem boundary where an arbitrary write is a contained defect rather than an application compromise. That is how you make whole classes of parser bugs less expensive. The public record strongly supports the need for basename enforcement and safe output handling; containment is the logical extension. (GitHub)
What to monitor for after patching
CVE-2025-66034 is not the kind of issue where you should assume “upgrade and forget.” If vulnerable processing touched untrusted inputs before remediation, incident review is reasonable. Look for historical processing of externally sourced .designspace files, especially in services or jobs that also had access to deployment directories, plugin locations, or web-served storage. Also look for unexpected generated files outside intended output roots, suspicious file extensions in build output areas, or changes to configuration and application files around font-processing jobs. Those signals are not taken from a single official checklist, but they are directly derived from the advisory’s warning that attackers can control location, extension, and contents of written files. (GitHub)
For teams with centralized logging, the most valuable correlation is between file-processing events and filesystem writes outside the normal build destination. If your pipeline telemetry can tell you which job handled a .designspace file and which directories that job wrote into, use that data. The patch itself shows the core abuse path was untrusted filename components escaping an output directory. So the forensic question is whether that escape was possible or observed in your environment before the fix. (GitHub)

Why this CVE matters beyond font tooling
The enduring lesson of CVE-2025-66034 is not “audit your font stack” in a narrow sense. It is that modern software has accumulated many small, specialized processors that quietly cross trust boundaries on behalf of users and automation. A designspace file does not look like a traditional weaponized payload, but the moment a backend service interprets it, compiles it, merges it with filesystem paths, and emits server-side outputs, it becomes part of your execution surface. That is the same general lesson security teams had to learn with image transformers, PDF toolchains, markdown renderers, archive extractors, and office-document converters. The extension changes. The control problem does not. (GitHub)
There is also a supply-chain angle. Vendor advisories from IBM show that a library issue in fontTools propagated into larger enterprise offerings and had to be remediated in product releases. That is the practical meaning of transitive risk. You may never call fonttools varLib yourself and still end up shipping it inside a service where someone else wired it into a runtime. This is why dependency inventories and SBOM-aware review matter even for packages that seem far from your core business logic. (IBM)
For teams trying to move faster than manual code review and one-off dependency scans, this kind of issue is exactly where an AI-driven validation workflow becomes useful. CVE-2025-66034 is not just about a version string. It is about reachability, execution path, write location, and environmental preconditions. A good security workflow should be able to answer all four: where the vulnerable package exists, whether the dangerous function is actually invoked, what trust boundary the input crosses, and whether the resulting write can touch anything operationally meaningful. That is the difference between dependency awareness and exploitable-path awareness. (GitHub)
This is also why automated penetration testing platforms like Sträflich are most useful when they are used as evidence engines rather than brochure scanners. In a case like this, the goal is not to shout “Critical” because NVD did. The goal is to validate whether a real application path accepts the right file type, reaches the vulnerable code, escapes the intended directory, and lands in a path that matters. When security teams can verify that chain instead of arguing from CVSS alone, they make better remediation decisions and waste less time on false urgency. That is the operational value.
Bottom line
CVE-2025-66034 deserves attention because it combines three things defenders should always treat seriously: attacker-controlled structured input, filesystem writes derived from that input, and deployment contexts where generated outputs may be consumed by more powerful components later. The official sources are consistent about the core facts: fontTools.varLib is affected, versions from 4.33.0 to before 4.60.2 are vulnerable, the fix is to stop trusting path-bearing filenames and use only the basename, and the resulting primitive can lead to remote code execution when the environment turns a written file into executable content. (GitHub)
The severity disagreement is not noise. It is the real story. In a closed local workflow with trusted files, this may behave like a contained Medium. In an automated service that ingests outside design assets and writes into dangerous places, it is much closer to the Critical picture NVD recorded and downstream vendors adopted. If your team takes one action after reading this, it should be this: do not reduce the decision to a single score. Upgrade the package, map the reachable paths, isolate the worker, and verify where outputs can land. That is how you turn a CVE entry into a real defensive response. (NVD)
Recommended internal and external reading
- NVD entry for CVE-2025-66034
- GitHub advisory, GHSA-768j-98cg-p3fv
- fontTools patch commit
- fontTools release notes showing 4.60.2 and 4.61.0
- Ubuntu CVE page for CVE-2025-66034
- NVD entry for related fontTools issue, CVE-2023-45139
- Pentest AI Tools in 2026 — What Actually Works, What Breaks
- The Future of AI Agent Security – Openclaw Security Audit
- OpenClaw Security Audit, What Actually Breaks When an AI Agent Can Touch Your Files, Tools, and Accounts