CVE-2026-21262 looks deceptively simple in its shortest form. Microsoft’s public description says improper access control in SQL Server allows an authorized attacker to elevate privileges over a network. That sentence is accurate, but it is not enough to explain why defenders should care. The reason this bug matters is not just that it is remotely reachable by an authenticated low-privileged user. It is that multiple March 2026 analyses describe the likely end state as SQL sysadmin privileges, which turns a modest foothold into full control of the database instance. (OpenCVE)
That detail changes the entire risk conversation. Many organizations instinctively de-prioritize vulnerabilities that require authentication. In application security, that reflex is often wrong. In database security, it can be disastrous. Low-privileged SQL access is not rare in real environments. It shows up through application connection strings, service accounts, legacy logins, reporting tooling, replication topologies, batch integrations, and vendor support paths. A vulnerability like CVE-2026-21262 is valuable precisely because it fits naturally into the messy middle of a real intrusion, after initial access but before the attacker has full control. (CrowdStrike)
The public record also gives this issue a profile defenders should not ignore. The CVE record and Microsoft-linked advisory ecosystem describe it as a high-severity elevation-of-privilege flaw, mapped to CWE-284, with a CVSS v3.1 base score of 8.8. The vector is network, low attack complexity, low privileges required, no user interaction, and high impact across confidentiality, integrity, and availability. CISA’s Vulnrichment data, as reflected in the public CVE ecosystem, records exploitation as none, automatable as no, and technical impact as total. That combination does not prove imminent mass exploitation, but it is more than enough to justify urgent patching and serious post-patch validation. (OpenCVE)
What is publicly confirmed today
The core facts are not ambiguous. CVE-2026-21262 was published on March 10, 2026. Microsoft’s public description is concise: improper access control in SQL Server allows an authorized attacker to elevate privileges over a network. The CVE record maps the flaw to CWE-284, Improper Access Control. Public March Patch Tuesday coverage from CrowdStrike, Tenable, Rapid7, Talos, and others consistently describes it as a SQL Server elevation-of-privilege issue requiring low privileges and no user interaction, with CVSS 8.8, and publicly disclosed at the time patches became available. (OpenCVE)
Just as important is what is nicht publicly confirmed. There is no widely published, vendor-confirmed exploit walkthrough explaining the precise internal code path. There is also no public confirmation from Microsoft or CISA that the vulnerability was actively exploited in the wild at release time. Tenable notes that Microsoft assessed the SQL Server privilege-escalation trio as “Exploitation Less Likely,” and Rapid7’s March table likewise lists CVE-2026-21262 as publicly disclosed but not actively exploited. That means defenders should be careful not to invent implementation detail that has not been released. The responsible approach is to separate confirmed facts from informed operational inference. (Tenable®)
The table below is the clearest way to frame the current public state of knowledge.
| Artikel | Publicly confirmed |
|---|---|
| Schwachstelle | CVE-2026-21262 |
| Produkt | Microsoft SQL Server |
| Typ | Elevation of Privilege |
| Root weakness | Improper access control |
| CWE | CWE-284 |
| CVSS v3.1 | 8.8 High |
| Vektor | AV:N AC:L PR:L UI:N S:U C:H I:H A:H |
| Attack precondition | Authorized attacker with low privileges |
| User interaction | Keine |
| Disclosure state at patch release | Publicly disclosed |
| Confirmed active exploitation at release | No public evidence reported in vendor-linked coverage |
| Likely impact if exploited | Elevation to SQL sysadmin privileges |
This table is synthesized directly from the CVE record, CVE ecosystem mirrors, and major March 2026 Patch Tuesday summaries. (OpenCVE)

Why “requires authentication” is the wrong reason to relax
The weakest response to this vulnerability is also the most common one: “An attacker already needs credentials, so this is not urgent.” That sounds comforting, but it assumes credentials are scarce and cleanly governed. In practice, SQL Server environments often carry years of accumulated access debt. Application pools keep long-lived connection strings. Integration jobs inherit permissions from forgotten service accounts. Reporting stacks need read access that grows into write access. Replication and upgrade paths preserve older assumptions. Third-party vendors get temporary accounts that never disappear. In that setting, “low privileges required” is not a strong safety property. It is a realistic starting point. (CrowdStrike)
This is why CVE-2026-21262 fits a common post-compromise pattern so well. It is not the cleanest initial-access exploit in the world, and that is exactly why some teams will underestimate it. But once an attacker has anything from an application foothold to stolen credentials to lateral movement into a subnet with SQL reachability, the value of a privilege boundary failure inside the database tier rises quickly. Attackers do not care whether the next step is glamorous. They care whether it expands control. A low-privileged login that becomes sysadmin inside a production SQL instance is often enough to move from reconnaissance into durable control over data and workflows. That is an inference from the permission model and typical intrusion chains, but it is strongly supported by the risk framing in the public advisories. (CrowdStrike)
Another reason defenders should resist complacency is that the flaw was publicly disclosed at patch time. Public disclosure does not automatically mean wide exploitation, but it does change the clock. Once a vulnerability is known outside the vendor, reverse engineering the fix becomes more attractive, patch lag becomes more dangerous, and the number of eyes on the issue increases. That is why publicly disclosed but not yet exploited vulnerabilities often deserve more urgency than their “no active exploitation” label suggests. (Tenable®)
Why sysadmin is the real story
SQL Server’s permission model is the key to understanding why this bug matters. Microsoft Learn states plainly that members of the sysadmin fixed server role can perform any activity in the server, and that permissions cannot be denied to members of this role. Microsoft also documents that the sa login is a member of sysadmin, has all permissions on the server, and cannot be limited. So when vendor and industry summaries say CVE-2026-21262 may allow an attacker to gain SQL sysadmin privileges, that is not a cosmetic elevation. It is the top of the SQL Server authority chain. (Microsoft Lernen)
That status has practical consequences. A sysadmin can change logins, alter permissions, manipulate server-wide configuration, and interact with powerful administrative features that lower-privileged roles cannot fully control. Microsoft’s SQL Server Agent documentation adds another important detail: members of the sysadmin fixed server role have access to all SQL Server Agent functionality. In environments where jobs are used for maintenance, ETL, backups, task scheduling, or downstream automation, that expands the operational blast radius of a privilege escalation well beyond simple data read access. (Microsoft Lernen)
It also matters because SQL Server’s older fixed server roles are broader than many teams realize. Microsoft explicitly warns that the securityadmin role should be treated as equivalent to sysadmin from a security perspective, because it can grant access and configure permissions in ways that effectively collapse the boundary. That warning is useful here because it reminds defenders that patching CVE-2026-21262 is only part of the job. The deeper issue is whether the server role model in your environment is already too coarse to preserve meaningful separation of duties. (Microsoft Lernen)
Affected versions and patched builds
One of the most useful things about CVE-2026-21262 is that the affected-version information is unusually concrete. The public CVE ecosystem and Microsoft’s branch-specific support articles together show that the flaw affects supported SQL Server versions from SQL Server 2016 SP3 through SQL Server 2025, across both GDR and cumulative update tracks depending on the branch. This is not a vague “latest supported versions” situation. Defenders can map exposure instance by instance. (OpenCVE)
The practical matrix is below.
| Zweigstelle | Servicing path | Fixed build |
|---|---|---|
| SQL Server 2016 SP3 | GDR | 13.0.6480.4 |
| SQL Server 2016 SP3 | Azure Connect Feature Pack | 13.0.7075.5 |
| SQL Server 2017 | GDR | 14.0.2100.4 |
| SQL Server 2017 | CU31 | 14.0.3520.4 |
| SQL Server 2019 | GDR | 15.0.2160.4 |
| SQL Server 2019 | CU32 | 15.0.4460.4 |
| SQL Server 2022 | GDR | 16.0.1170.5 |
| SQL Server 2022 | CU23 | 16.0.4240.4 |
| SQL Server 2025 | GDR | 17.0.1105.2 |
| SQL Server 2025 | CU2 | 17.0.4020.2 |
These build targets come from Microsoft support KBs and the public CVE applicability data. (OpenCVE)
The operational lesson here is straightforward. Do not report “patched for March 2026” as a generic state. Report exact branch and exact build. A 2019 GDR instance and a 2019 CU instance do not have the same target build. A 2025 GDR instance and a 2025 CU instance do not have the same target build. The more mature the environment, the more likely it is that multiple servicing paths are coexisting at once. (Microsoft Support)

What the March 2026 SQL fixes really suggest
If you only read the headline CVE and stop there, you miss the broader signal in Microsoft’s March SQL updates. Talos summarized March 2026 as containing three “important” SQL Server elevation-of-privilege vulnerabilities with the same 8.8 score: CVE-2026-21262 from improper access control, CVE-2026-26115 from improper input validation, and CVE-2026-26116 from improper neutralization of special elements used in a SQL command. That trio matters because it suggests the month was not about one isolated permission bug. It was about a broader cluster of SQL Server trust-boundary issues. (Cisco Talos Blog)
Microsoft’s own support content reinforces that impression. The March SQL Server KBs do more than list CVEs. They also surface concrete internal fixes, including a fix for an elevation-of-privilege vulnerability in the version upgrade process for merge replication and a change that blocks the ALTER USER operation if the target login is the system Administrator account. Those details do not prove the exact code path of CVE-2026-21262, and they should not be overstated as such. But they do tell defenders something important: March’s SQL security work touched not only obvious permission boundaries, but also upgrade and replication paths that many organizations under-test. (Microsoft Support)
That is why merge replication deserves explicit attention in any serious response plan. Microsoft Learn documents that SQL Server supports upgrading replicated databases from previous versions without stopping activity on other nodes, and it provides separate guidance for peer-to-peer replicated databases. That flexibility is operationally useful, but it also means complex topologies can carry subtler state and upgrade assumptions than standalone instances. When a March security update explicitly references a replication-related elevation-of-privilege fix, replication-aware environments should treat validation as a first-class requirement, not an optional extra. (Microsoft Lernen)
Real attack value in real environments
A well-defended reader will ask the right question next: what kinds of environments make this bug truly dangerous. The answer begins with authenticated reachability. CrowdStrike’s summary says an attacker would need to log in to a vulnerable system before performing the privilege escalation. That means the highest-risk environments are not necessarily the ones with internet-exposed SQL ports. They are the ones where low-privileged authenticated access to SQL Server is already realistic from some adjacent host or workflow. (CrowdStrike)
That usually includes customer-facing applications that connect with broad server-level identities, internal apps running with shared service accounts, jump boxes used by operations teams, CI or automation hosts with database credentials, business reporting stacks, vendor-managed components, and legacy migration or replication infrastructure that survived multiple upgrade cycles. None of those conditions are rare. They are the ordinary sediment of enterprise operations. That is what makes CVE-2026-21262 operationally important even without a flashy unauthenticated exploit story. (CrowdStrike)
There is also a larger lesson here about blast radius. Microsoft’s documentation on xp_cmdshell notes that the feature is disabled by default on new installations, but system administrators control whether it can be executed. Microsoft also documents that when xp_cmdshell is called by a user who is not a member of the sysadmin fixed server role, it uses a proxy credential if one exists. The implication is simple: once a principal reaches sysadmin-level control, the set of database-to-OS interaction paths expands sharply in environments that expose or enable such features. That is not a published exploit chain for CVE-2026-21262. It is a defensive inference about why sysadmin-level database compromise should never be treated as “just a database problem.” (Microsoft Lernen)
How to identify exposure quickly
The first priority is build truth. Microsoft Learn documents SERVERPROPERTY und @@VERSION as standard ways to determine SQL Server version information, and Microsoft’s troubleshooting guidance recommends using those properties to identify exact version and edition details. In practice, that means you should not start with vulnerability scanners or CMDB assumptions. Start with what the instance itself says. (Microsoft Lernen)
A minimal query is enough to establish the basics:
SELECT
@@SERVERNAME AS instance_name,
SERVERPROPERTY('ProductVersion') AS product_version,
SERVERPROPERTY('ProductLevel') AS product_level,
SERVERPROPERTY('Edition') AS edition,
@@VERSION AS full_version_string;
This query uses Microsoft-documented functions and gives you the exact build context needed to compare an instance to the March 2026 fixed versions. (Microsoft Lernen)
The second priority is privilege truth. If the public risk framing centers on a jump to sysadmin, defenders need a baseline of who already holds server-level authority. A useful first-pass query is below:
SELECT
sp.name AS principal_name,
sp.type_desc AS principal_type,
sp.is_disabled,
sl.sysadmin,
sl.securityadmin,
sl.serveradmin,
sl.setupadmin,
sl.processadmin,
sl.diskadmin,
sl.dbcreator,
sl.bulkadmin
FROM sys.server_principals sp
LEFT JOIN sys.syslogins sl
ON sp.sid = sl.sid
WHERE sp.type IN ('S', 'U', 'G', 'E', 'X')
ORDER BY sl.sysadmin DESC, sp.name;
The point of this query is not elegance. It is speed. You want to know which principals already sit in or near the most dangerous roles, whether those memberships make business sense, and whether anything changed unexpectedly during remediation. Microsoft’s server-role documentation is the reference point for interpreting those role memberships, especially the warnings around sysadmin und securityadmin. (Microsoft Lernen)
At fleet scale, teams often want a lightweight collection step before they dig deeper. A simple PowerShell pass can work:
$instances = @(
"sql-prod-01",
"sql-reporting-02",
"sql-legacy-03"
)
$query = @"
SELECT
@@SERVERNAME AS instance_name,
SERVERPROPERTY('ProductVersion') AS product_version,
SERVERPROPERTY('ProductLevel') AS product_level,
SERVERPROPERTY('Edition') AS edition;
"@
foreach ($instance in $instances) {
try {
Invoke-Sqlcmd -ServerInstance $instance -Query $query |
Select-Object @{n='server';e={$instance}}, instance_name, product_version, product_level, edition
}
catch {
Write-Warning "Failed to query $instance : $($_.Exception.Message)"
}
}
The collection method can vary, but the underlying principle stays the same: inventory exact builds first, then compare them to the March 2026 fixed matrix. (Microsoft Lernen)

Logging and audit signals worth enabling
Version data tells you whether an instance is patchable. It does not tell you whether it was targeted or misused. For that, you need telemetry inside SQL Server. Microsoft Learn documents SQL Server Audit as the built-in feature for tracking server-level and database-level events. Audit specifications can capture both grouped actions and individual events, and outputs can be written to event logs or audit files. That makes the feature directly relevant to CVE-2026-21262 response because the most valuable questions after a privilege-escalation concern are always the same: who authenticated, what changed, and when. (Microsoft Lernen)
For this vulnerability class, the most useful events are successful and failed logins, changes to principals, and server-role membership changes. These are exactly the categories that help responders distinguish benign patch activity from suspicious role expansion or credential misuse. If your organization already forwards SQL audit output off-box, you should verify retention and parsing immediately. If audit data only lives on the same server an attacker may control after escalation, its evidentiary value drops sharply. That is not a reason to avoid auditing. It is a reason to centralize it. (Microsoft Lernen)
A compact server audit example looks like this:
USE master;
GO
CREATE SERVER AUDIT Audit_CVE_2026_21262
TO FILE
(
FILEPATH = 'D:\\SQLAudit\\',
MAXSIZE = 1 GB,
MAX_ROLLOVER_FILES = 20,
RESERVE_DISK_SPACE = OFF
);
GO
ALTER SERVER AUDIT Audit_CVE_2026_21262
WITH (STATE = ON);
GO
CREATE SERVER AUDIT SPECIFICATION AuditSpec_CVE_2026_21262
FOR SERVER AUDIT Audit_CVE_2026_21262
ADD (SERVER_PRINCIPAL_CHANGE_GROUP),
ADD (SERVER_ROLE_MEMBER_CHANGE_GROUP),
ADD (SUCCESSFUL_LOGIN_GROUP),
ADD (FAILED_LOGIN_GROUP);
GO
ALTER SERVER AUDIT SPECIFICATION AuditSpec_CVE_2026_21262
WITH (STATE = ON);
GO
This follows Microsoft’s documented audit model and keeps the focus on security-relevant changes rather than generic noise. (Microsoft Lernen)
Patching is necessary, but it is not closure
The patching instruction itself is simple: update each SQL Server instance to the March 10, 2026 fixed build that matches its branch and servicing path. The harder part is what happens around the patch. Replication, high-availability topologies, maintenance windows, application compatibility, and upgrade sequencing still matter. Microsoft’s replicated-database guidance exists because these environments do not behave like isolated lab installs. (Microsoft Lernen)
That is why good remediation for CVE-2026-21262 has two phases. Phase one is version remediation. Phase two is trust-boundary validation. After patching, you should verify that low-privileged application identities are still low-privileged, that temporary admin access used during maintenance has been removed, that no unexpected principal ended up in sysadmin, that replication or Agent workflows did not require broad workarounds that were never rolled back, and that auditing still captures the events you would need during an investigation. Too many teams stop at “build number fixed” and never ask whether the environment still contains the conditions that made the flaw dangerous in the first place. (Microsoft Lernen)
Hardening opportunities should also be part of this phase. Microsoft’s server-role guidance for newer SQL Server versions introduces more constrained fixed server roles such as ##MS_LoginManager## und ##MS_DatabaseManager##, specifically to support least privilege better than the older broad roles. Not every environment can refactor role design overnight, but March 2026 is a good forcing function to start reducing dependence on old all-purpose administrative patterns. (Microsoft Lernen)

Related CVEs that belong in the same review window
CVE-2026-21262 should not be handled as a lonely database CVE. The closest related issues are CVE-2026-26115 and CVE-2026-26116, the other two SQL Server elevation-of-privilege flaws from the same March release. Talos describes them as the same severity tier with different underlying bug classes, while Tenable and Rapid7 group them together as SQL Server EoP vulnerabilities rated 8.8. If your response process patches only the publicly disclosed item and ignores the adjacent SQL privilege-boundary issues, your patching may be compliant on paper but shallow in practice. (Cisco Talos Blog)
Another useful adjacent issue is CVE-2026-25177 in Active Directory Domain Services. It is not a SQL Server flaw, but it shares the same strategic lesson: low-privileged network-reachable access inside a core enterprise trust plane can be enough to produce outsized consequences. That parallel matters because many defenders still review identity and database privilege escalation in separate workflows, even though modern intrusions happily move across both. (Schnell7)
The broader pattern is this: March 2026 was not just a month with a single SQL Server bug. It was a month that exposed how much operational trust still accumulates around foundational enterprise software. The organizations that respond well to bugs like CVE-2026-21262 are not merely the ones that install patches quickly. They are the ones that understand where small privileges become large control. (Tenable®)
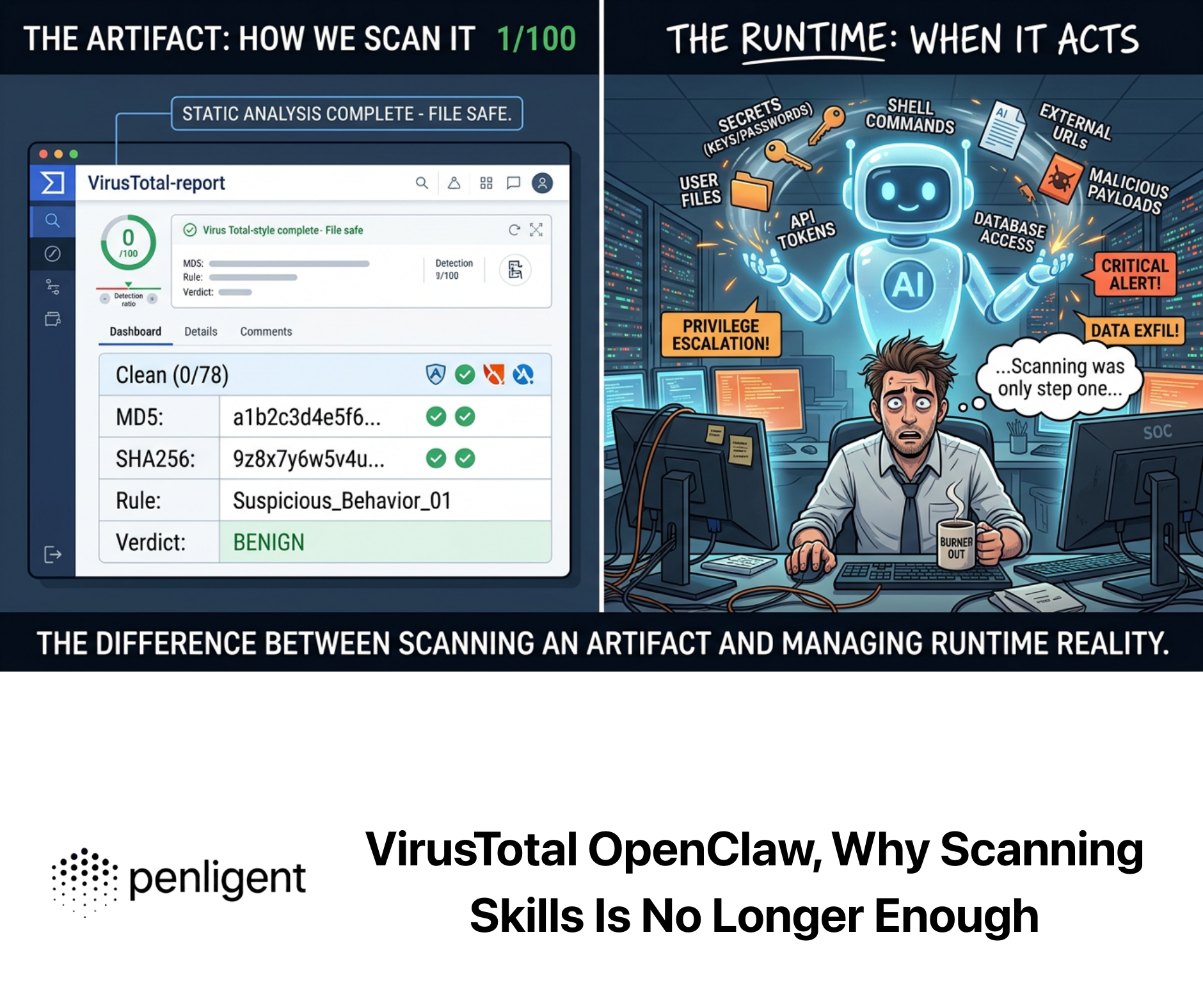
Where continuous validation fits naturally
For teams that already run evidence-driven offensive validation, CVE-2026-21262 is a good example of why “scan and patch” is not enough. What matters after the advisory is not only whether the server version changed, but whether real authenticated paths in your environment still expose an unsafe permission boundary. That is where an AI-assisted validation workflow can be useful: inventory reachable assets, confirm branch and build, test the behavior of low-privileged identities against expected role boundaries, and preserve repeatable evidence for engineering and audit teams. Penligent’s recent writing on identity-centric and endpoint-centric vulnerabilities makes the same case from different angles: the win is not speed of reading advisories, but speed of proving whether your environment is actually exposed. (Sträflich)
Used properly, a platform like Penligent is not a replacement for Microsoft documentation or DBA judgment. It is a force multiplier for verification. The most defensible use of automation here is narrow and concrete: version collection, privilege-boundary checks, repeatable post-patch validation, and evidence generation that can survive handoffs between security, infrastructure, and engineering teams. That is where modern AI-assisted pentesting and validation can add real value without drifting into hype. (Sträflich)
Final assessment
CVE-2026-21262 deserves attention not because it is the loudest SQL Server bug ever disclosed, but because it sits in an especially dangerous place in the attack chain. It is network-reachable. It requires only low privileges. It needs no user interaction. Public reporting says it can end at SQL sysadmin. And it was publicly disclosed before many organizations had patched. Those are exactly the conditions under which seemingly “internal” vulnerabilities become operationally expensive. (OpenCVE)
The most mature response is therefore simple, even if the execution is not. Patch the affected branch to the correct March 2026 build. Inventory every authenticated path into the instance. Baseline server-level roles. Centralize audit data. Revalidate replication-aware and Agent-heavy deployments. And do not let the word authenticated trick you into treating this as background noise. In database security, the distance between low privilege and full control is often shorter than teams think. CVE-2026-21262 is a reminder of exactly that. (Microsoft Support)
Further reading
- CVE Record for CVE-2026-21262 (CVE)
- Microsoft SQL Server 2025 CU2 security update KB (Microsoft Support)
- Microsoft SQL Server 2025 GDR security update KB (Microsoft Support)
- Microsoft SQL Server 2022 CU23 security update KB (Microsoft Support)
- Microsoft SQL Server 2022 GDR security update KB (Microsoft Support)
- Microsoft SQL Server 2019 CU32 and 2019 GDR security update KBs (Microsoft Support)
- Microsoft SQL Server 2017 CU31 and 2017 GDR security update KBs (Microsoft Support)
- Microsoft SQL Server 2016 SP3 GDR and Azure Connect Feature Pack security update KBs (Microsoft Support)
- Microsoft Learn, Server-Level Roles (Microsoft Lernen)
- Microsoft Learn, SQL Server Audit (Microsoft Lernen)
- Microsoft Learn, SERVERPROPERTY and @@VERSION guidance (Microsoft Lernen)
- Cisco Talos, March 2026 Patch Tuesday summary (Cisco Talos Blog)
- CrowdStrike, March 2026 Patch Tuesday analysis (CrowdStrike)
- Tenable, March 2026 Patch Tuesday analysis (Tenable®)
- Rapid7, March 2026 Patch Tuesday matrix (Schnell7)
- CVE-2026-25177 — Why This Active Directory Flaw Deserves Immediate Attention (Sträflich)
- CVE-2026-20841, When Windows Notepad Turned Markdown Into an Execution Boundary (Sträflich)
- Pentest AI Tools in 2026 — What Actually Works, What Breaks (Sträflich)
- The 2026 Ultimate Guide to AI Penetration Testing: The Era of Agentic Red Teaming (Sträflich)