What you should do first, the three-step checklist
If you’re on the hook for mobile security outcomes, CVE-2026-21385 is the kind of issue that punishes “we told users to update” and rewards “we can prove we’re patched.”
- Identify Android devices that could be exposed Start with your Android inventory and confirm where Qualcomm chipsets are in play. Android’s March 2026 bulletin lists CVE-2026-21385 under Qualcomm components with subcomponent “Display.” (Android Open Source Project)
- Drive devices to the patch level that actually includes the fix Multiple credible reports and Google’s bulletin structure point to security patch level 2026-03-05 as the level that bundles the broader set of fixes, including vendor and kernel subcomponents. (SecurityWeek)
- Produce remediation proof, not promises Your evidence is the device’s patch string (and related inventory metadata), collected centrally and retained. Google explicitly describes how OEMs should set the patch string and how 2026-03-05 relates to the full bundle. (Android Open Source Project)
CVE-2026-21385, what is confirmed and what is not
This section stays intentionally literal. Everything below is anchored to primary advisories or widely relied-on aggregation records.
Confirmed facts you can cite internally
- CVE ID: CVE-2026-21385 (NVD)
- Core description: “Memory corruption while using alignments for memory allocation.” (NVD)
- Weakness class: CWE-190, Integer Overflow or Wraparound. (NVD)
- Severity score and vector as provided by the CNA: CVSS v3.1 base score 7.8 High, vector AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H. (NVD)
- Android exploitation note: Google’s March 2026 Android Security Bulletin states there are indications CVE-2026-21385 “may be under limited, targeted exploitation.” (Android Open Source Project)
- CISA KEV status and deadline: NVD shows the CVE is in CISA’s Known Exploited Vulnerabilities Catalog, with date added 03/03/2026 und due date 03/24/2026. (NVD)
- Component placement in Android bulletin: The bulletin lists CVE-2026-21385 under Qualcomm components with subcomponent “Display.” (Android Open Source Project)
Things commonly repeated that are not confirmed in the primary records
- Exact exploitation chain details, targets, and operator attribution Google’s bulletin explicitly flags exploitation signals but does not publish targeting specifics or a technical exploit narrative. Treat media speculation as hypotheses. (Android Open Source Project)
- A universal “device count affected” You will see claims like “hundreds of millions.” Some outlets infer that from market share, but it is not a precise, auditable figure from Google, Qualcomm, or NVD. Keep your internal statements to what you can prove from your fleet data and what Qualcomm/Google actually publish. (BleepingComputer)
The timeline, why the dates matter more than the headline
For operational security teams, the timeline answers two questions: “How long could exploitation have existed?” and “When did a fix become available to OEMs versus end users?”
Here’s what you can support with citations:
- Dec 18, 2025: A CodeLinaro commit tied to the graphics kernel stack is authored on this date, with the commit message explicitly describing the alignment/sign-extension issue. (GitLab)
- Jan 12, 2026: That same commit shows as committed on Jan 12, 2026 in the CodeLinaro repository. (GitLab)
- Late Jan 2026: A related kernel tree commit is committed Jan 27, 2026, again describing the same fix theme. (GitLab)
- Feb 2, 2026: Qualcomm notified customers about the issue, per reporting that cites Qualcomm’s advisory and coordinated disclosure statements. (BleepingComputer)
- Mar 2, 2026: NVD published the CVE record (and shows it was received from Qualcomm on 03/02/2026). (NVD)
- Mar 2, 2026: Google published the March 2026 Android Security Bulletin and included the exploitation-language note. (Android Open Source Project)
- Mar 3, 2026: CISA KEV catalog entry date added shown via NVD enrichment. (NVD)
The practical takeaway: availability of code-level fixes to OEMs can precede the month your end users see OTA updates by weeks or months. The only completion definition that holds up in an audit is device-level proof of patch level and rollout coverage. (Android Open Source Project)
What’s actually vulnerable, the Qualcomm graphics driver path in plain engineering terms
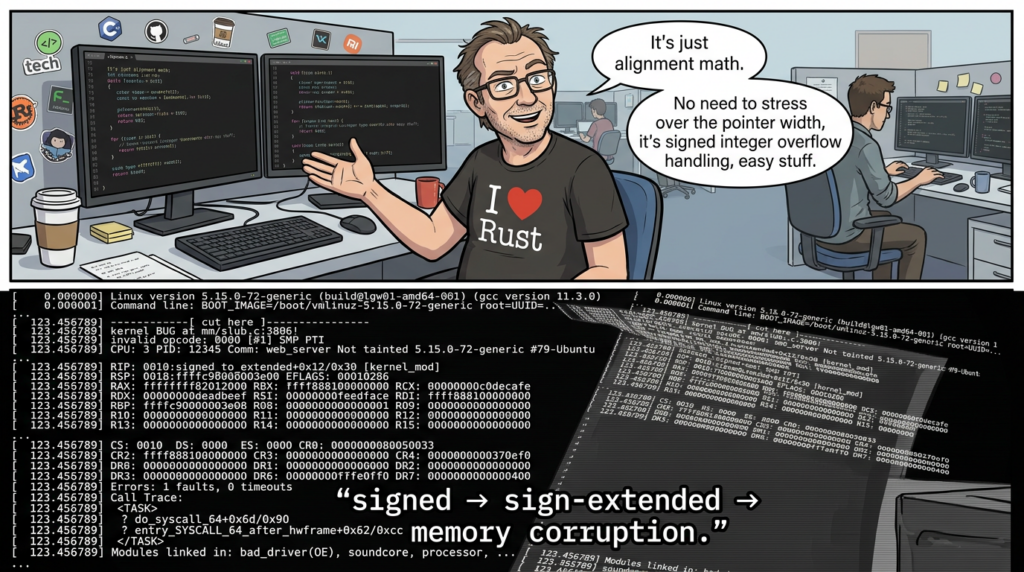
CVE-2026-21385 is described as memory corruption tied to alignment handling during memory allocation. NVD classifies it as integer overflow or wraparound, which is consistent with unsafe arithmetic around sizes, offsets, or alignment values. (NVD)
Android’s bulletin places it in Qualcomm components and labels the subcomponent “Display,” while multiple outlets describe it as a Qualcomm graphics/display component issue. (Android Open Source Project)
The most useful technical detail that is publicly visible today
The single best publicly visible, non-speculative technical clue is in the CodeLinaro commit message linked from the Android bulletin entry.
The commit title is explicit: “kgsl: Prevent sign extension on alignments.” The message states that alignments from userland can be sign-extended and “cause havoc” in memory management routines, and that the fix involves changing the return type and starting with an unsigned type for bit shifts. (GitLab)
That is unusually actionable for defenders because it tells you:
- userland-provided alignment values are part of the input surface
- sign extension and type handling are core to the bug class
- the fix direction is strongly aligned with “make the type unsigned and control shifts”
Why sign extension and alignment arithmetic are dangerous in kernel-adjacent code
Alignment math is deceptively simple:
- you take a size
- you compute or accept an alignment
- you round up
- you allocate and map
But if the alignment value is attacker-influenced and your types are wrong, you can create:
- overflow or wraparound during rounding
- negative values becoming huge after sign extension
- mis-sized buffers that later get read or written past their bounds
That is the class of condition CWE-190 captures: arithmetic that wraps and turns “small” into “large” or vice versa. (NVD)
A defensive coding sketch, how to do alignment safely
The goal here is not to reproduce an exploit. It’s to show the defensive shape of a correct implementation: validate input, keep types unsigned, and use checked arithmetic.
// Defensive alignment helper, do not accept unbounded attacker-controlled alignments.
// This is illustrative code for secure arithmetic patterns.
#include <stdint.h>
#include <stdbool.h>
static bool is_power_of_two_u64(uint64_t x) {
return x && ((x & (x - 1)) == 0);
}
static bool align_up_u64(uint64_t size, uint64_t align, uint64_t *out) {
if (!out) return false;
// Enforce a sane alignment policy: power-of-two and bounded.
if (!is_power_of_two_u64(align)) return false;
if (align < 8 || align > (1ULL << 20)) return false; // example bounds: 8B .. 1MB
// Checked arithmetic: size + (align - 1) must not overflow.
uint64_t addend = align - 1;
if (size > UINT64_MAX - addend) return false;
uint64_t rounded = (size + addend) & ~(align - 1);
if (rounded < size) return false; // paranoid check
*out = rounded;
return true;
}
If you read the CodeLinaro message and then look at this pattern, the “unsigned type for bit shifts” line makes immediate sense: bit shifts on signed values can produce unexpected sign-propagating behavior depending on the operation and compiler semantics, and that’s the kind of footgun kernel-level interfaces can’t afford. (GitLab)
CVSS says local, why that still maps to real-world compromise
NVD shows a CVSS vector with Attack Vector Local und Privileges Required Low, with no user interaction required. (NVD)
That tends to push non-mobile teams into a false sense of safety. On Android, “local code execution” is often exactly what sophisticated chains are built on:
- a foothold from a malicious app install, sideloading, or supply-chain abuse
- a browser or messaging RCE that drops a payload into an app sandbox
- a privilege escalation or driver bug that breaks out of constraints
Google’s wording “limited, targeted exploitation” is widely understood in the security community as a signal consistent with spyware-grade chains, even when full attribution is unknown. Dark Reading explicitly notes that this language profile has shown up in other Qualcomm zero-day contexts and can align with commercial spyware or state-linked operators, while remaining clear that details are not public. (Dunkles Lesen)
The operational conclusion is simple: treat “local” exploited driver bugs as chain multipliers. They can be the second or third stage that turns “I can run code as an app” into “I can control the device.” (Dunkles Lesen)
The investigation phrases engineers actually use for CVE-2026-21385
You asked for “highest CTR” terms. Public browsing cannot reveal Google’s private click-through-rate data, so any claim of “highest CTR” would be made up. What is observable, and useful, is the dominant phrasing pattern across the most-circulated headlines and advisories, which strongly influences what engineers search next.
Across major coverage, these phrases repeatedly show up in titles and summaries:
- “Android March 2026 security bulletin” (Android Open Source Project)
- “Qualcomm zero-day exploited” (Dunkles Lesen)
- “CVE-2026-21385 actively exploited” (BleepingComputer)
- “Qualcomm graphics component” or “graphics/display component” (SecurityWeek)
- “integer overflow or wraparound” (SecurityWeek)
- “security patch level 2026-03-05” (SecurityWeek)
- “CISA KEV” and “due date 03/24/2026” (NVD)
If you’re writing internal comms, those are also the phrases that reduce confusion: they point directly to the bulletin, the component, the patch level, and the government exploitation flag.
What BleepingComputer gets right, and what you still need to add as an engineering team
Among the widely read write-ups, BleepingComputer’s report is operationally useful because it:
- ties the exploitation statement directly to Google’s bulletin
- cites Qualcomm’s characterization of the bug as integer overflow or wraparound and the memory corruption outcome
- calls out the 235 affected chipsets figure from Qualcomm’s advisory
- describes the two patch levels and why 2026-03-05 bundles the complete set of fixes (BleepingComputer)
What your team still needs to add, because no newsroom can do it for you:
- your actual device exposure map, segmented by OEM and update cadence
- a measured rollout plan with staged enforcement
- proof artifacts for auditors and incident response
- a path for devices that can’t be updated quickly
That’s where the rest of this article focuses.

Patch strategy that survives fleet reality
The patch level that matters
Google’s bulletin explains the two security patch levels and states that 2026-03-05 or later addresses all issues associated with the 2026-03-05 level and all previous patch levels. (Android Open Source Project)
SecurityWeek and Malwarebytes both reinforce that 2026-03-05 is the patch level where the second batch lands and that devices at that level are considered fixed for the issues discussed. (SecurityWeek)
A simple rule for policy and reporting
- Compliant: ro.build.version.security_patch ≥ 2026-03-05
- Non-compliant: anything earlier
- Exception workflow: devices that cannot reach 2026-03-05 must be isolated or decommissioned based on your risk tolerance
This aligns with how Google tells OEMs to set the patch string. (Android Open Source Project)
Quick device check, one phone
adb shell getprop ro.build.version.security_patch
# Expected: 2026-03-05 or later
Google’s bulletin even names the exact property. (Android Open Source Project)
Batch check, multiple devices on a bench
#!/usr/bin/env bash
set -euo pipefail
min_patch="2026-03-05"
adb devices | awk 'NR>1 && $2=="device"{print $1}' | while read -r serial; do
patch=$(adb -s "$serial" shell getprop ro.build.version.security_patch | tr -d '\\r')
model=$(adb -s "$serial" shell getprop ro.product.model | tr -d '\\r')
echo "$serial,$model,$patch"
done | tee android_patch_inventory.csv
Store the CSV in your evidence system. If your organization ever has to answer “Were we patched before date X?”, this kind of artifact is the difference between confidence and guesswork.
Enterprise view, CSV policy gate in Python
If your MDM exports device inventory (serial, model, patch date), you can enforce at ingest time:
from __future__ import annotations
import csv
from dataclasses import dataclass
from datetime import date
MIN_PATCH = date(2026, 3, 5)
@dataclass(frozen=True)
class Device:
device_id: str
model: str
patch: date
def parse_date(s: str) -> date:
y, m, d = map(int, s.split("-"))
return date(y, m, d)
bad: list[Device] = []
with open("mdm_export.csv", newline="", encoding="utf-8") as f:
r = csv.DictReader(f)
for row in r:
patch = parse_date(row["security_patch"])
dev = Device(row["device_id"], row.get("model",""), patch)
if patch < MIN_PATCH:
bad.append(dev)
print(f"Non-compliant devices: {len(bad)}")
for dev in bad[:50]:
print(dev)
This doesn’t prove the vulnerability is gone at the binary level, but it creates a durable compliance boundary aligned with Google’s published patch semantics. (Android Open Source Project)
When updates lag, what you can do that’s actually defensible
Android’s ecosystem fragmentation is not a controversial point: OEMs integrate patches on their own schedules. BleepingComputer explicitly notes Pixel gets updates immediately and others can take longer. (BleepingComputer)
For security teams, that turns into a familiar decision tree:
| Szenario | Device can reach 2026-03-05 soon | Device update timeline unknown | Device cannot reach 2026-03-05 |
|---|---|---|---|
| Corporate-owned, fully managed | Enforce update deadline | Block network access until updated | Decommission or replace |
| BYOD with work profile | Require minimum patch for access | Quarantine work profile access | Deny access, require alternate device |
| High-risk user cohort | Fast-track manual updates | Loaner device program | Replace immediately |
This is the same logic implied by CISA KEV “apply mitigations or discontinue use if mitigations are unavailable,” as shown in NVD’s KEV field. (NVD)
Proof-based remediation, what to collect and keep
For an exploited CVE, you want evidence that can answer three questions later:
- Which devices were potentially exposed
- model, OEM, chipset family if known
- patch level at time of assessment
- When each device crossed the “fixed” boundary
- patch level date string and collection timestamp
- MDM policy enforcement logs
- What you did for non-upgradable devices
- network controls, access revocation, replacement tickets
- documented exception approvals
Google’s bulletin gives you the canonical property name and patch string format. (Android Open Source Project)
NVD gives you the KEV due date and the fact of exploitation flagging. (NVD)
What the CodeLinaro commits imply for defensive testing
The commit message is not an exploit description, but it’s enough to guide internal hardening and regression testing:
- userland can influence alignment values
- sign extension and shift semantics were part of the failure mode
- memory management routines were impacted (GitLab)
Defensive regression test idea, without weaponizing it
If you maintain internal Android builds, device kernels, or vendor forks, you can add a non-malicious regression test that asserts:
- alignment inputs are sanitized to an allowed set
- negative or oversized values are rejected early
- alignment rounding uses unsigned arithmetic and checked operations
The goal is simple: ensure a future refactor doesn’t reintroduce the bug class that this commit is clearly trying to eliminate. (GitLab)
Detection and incident response, what you can do when there are no public IOCs
Google did not publish indicators of compromise for CVE-2026-21385 exploitation, and that is common for targeted mobile exploitation. (Android Open Source Project)
So what is still worth doing?
1 Collect and preserve device artifacts for high-risk cases
If you suspect a targeted device, prioritize:
- bugreport captures
- tombstones and crash logs
- SELinux denials and kernel logs
- installed package list and sideload sources
Targeted exploitation often leaves subtle system instability or crash footprints, especially when memory corruption is part of the chain. NVD’s CIA impact ratings are all “High,” which underscores why responders treat this as serious even without public IOCs. (NVD)
2 Look for policy breaks that enable the local foothold
Because the CVSS vector requires local execution, focus on controls that prevent or limit that foothold:
- sideload restrictions
- app allowlisting for managed devices
- tightening developer options and debugging access
- enforcing Google Play Protect where applicable
Google’s bulletin explicitly emphasizes platform hardening and Play Protect as mitigation layers in general. (Android Open Source Project)
3 Treat “limited, targeted exploitation” as an escalation trigger
This exact language is the strongest public exploitation signal Google tends to publish in Android bulletins. Dark Reading argues that it is often associated with narrow but deliberate activity profiles, consistent with spyware-grade targeting, while noting uncertainty. (Dunkles Lesen)
That means you don’t wait for mass exploitation to justify action. You tighten controls and close patch gaps now.
Related CVEs you should track alongside CVE-2026-21385
A mature response does not treat a single CVE as an island, especially on mobile where exploit chains are the norm.
High-impact CVEs in the March 2026 Android bulletin worth knowing
- CVE-2026-0006 is listed in the bulletin as Kritisch und RCE in the System/Media context table shown in the bulletin excerpt, emphasizing that Android’s March 2026 set includes issues beyond the Qualcomm driver bug. (Android Open Source Project)
- CVE-2026-0047 appears as Critical EoP in the Framework section excerpted from the bulletin. (Android Open Source Project)
These matter because they shape plausible chain composition: an initial RCE or app compromise plus a local driver or EoP bug is a classic route to device-level control. Dark Reading explicitly frames CVE-2026-0047 as a likely chain element rather than a standalone drive-by. (Dunkles Lesen)

A prior Qualcomm “limited, targeted exploitation” reference point
Dark Reading mentions CVE-2024-43047 as another Qualcomm zero-day where similar language was used and later linked to commercial spyware tooling via third-party research, while being careful about not claiming the same attribution here. (Dunkles Lesen)
The point is not the specific older CVE’s details. The point is the pattern: Qualcomm driver bugs that are “local” can still be among the most strategically important vulnerabilities in targeted mobile operations.
Frequently asked questions that come up in real triage rooms
Is CVE-2026-21385 remotely exploitable
The published CVSS vector indicates Attack Vector Local und Privileges Required Low, which is not remote-by-default. (NVD)
That said, remote exploitation can be part of a chain: remote foothold first, then local escalation. Google’s exploitation note and the KEV status are the reasons you should not down-rank it. (Android Open Source Project)
Which patch level should I require
Verwenden Sie 2026-03-05 or later as the clean operational boundary for devices to be considered fully covered for March 2026 bulletin items, and because multiple credible sources tie the broader vendor/kernel fixes to that patch level. (Android Open Source Project)
Why is the component described as graphics or display
Android’s bulletin places CVE-2026-21385 in Qualcomm components with subcomponent “Display,” while security coverage describes it as a graphics/display component issue. Both can be true in practice because GPU and display pipelines are tightly coupled in mobile stacks, and the public descriptions often simplify. (Android Open Source Project)
What is the most defensible statement I can send to leadership
Something like:
- “CVE-2026-21385 is an exploited Qualcomm component memory corruption issue flagged in Google’s March 2026 Android Security Bulletin. We are enforcing patch level 2026-03-05 or later and can report fleet compliance with evidence.”
Every clause above is supported by the bulletin and NVD. (Android Open Source Project)
CVE-2026-21385 is device-side, but most organizations get breached through end-to-end failure: an exposed device plus a weak backend plus missing monitoring. If you’re already investing in hardening your mobile fleet, it’s a natural moment to pressure-test the rest of the chain.
Penligent positions itself as an AI-powered penetration testing platform that can autonomously run attack simulations and produce compliance-ready reporting and attack-path visualizations, with an emphasis on local deployment and privacy-first operation. (Sträflich)
Just as important, Penligent’s own writing about mobile zero-days emphasizes defensive validation rather than exploitation, explicitly describing the goal as safe verification and remediation outcomes rather than publishing weaponizable details. That is the posture you want when your audience is defenders under real governance constraints. (Sträflich)
Referenzen
- NVD record for CVE-2026-21385, CVSS vector, CWE-190, and KEV status (NVD)
- Android Security Bulletin March 2026, exploitation note and Qualcomm component table entry (Android Open Source Project)
- CodeLinaro commit message describing the alignment sign-extension fix theme (GitLab)
- GitHub Advisory Database entry for CVE-2026-21385 (GitHub)
- BleepingComputer coverage with chipset scope and Qualcomm/Google timeline pointers (BleepingComputer)
- SecurityWeek coverage describing the integer overflow or wraparound framing and patch-level bundling (SecurityWeek)
- Dark Reading analysis on exploitation-language meaning and likely chain context (Dunkles Lesen)
- Penligent on defensive validation for mobile zero-days and repeatable response workflows (Sträflich)
- Penligent overview of AI-powered pentesting platform capabilities (Sträflich)
- Penligent Android-related CVE write-up example for exploit-chain thinking (Sträflich)