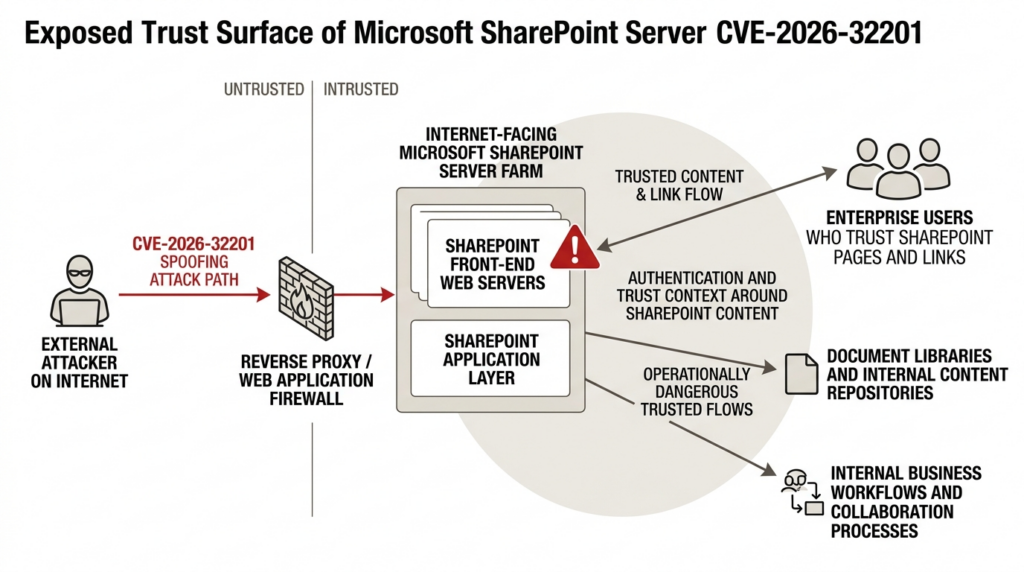
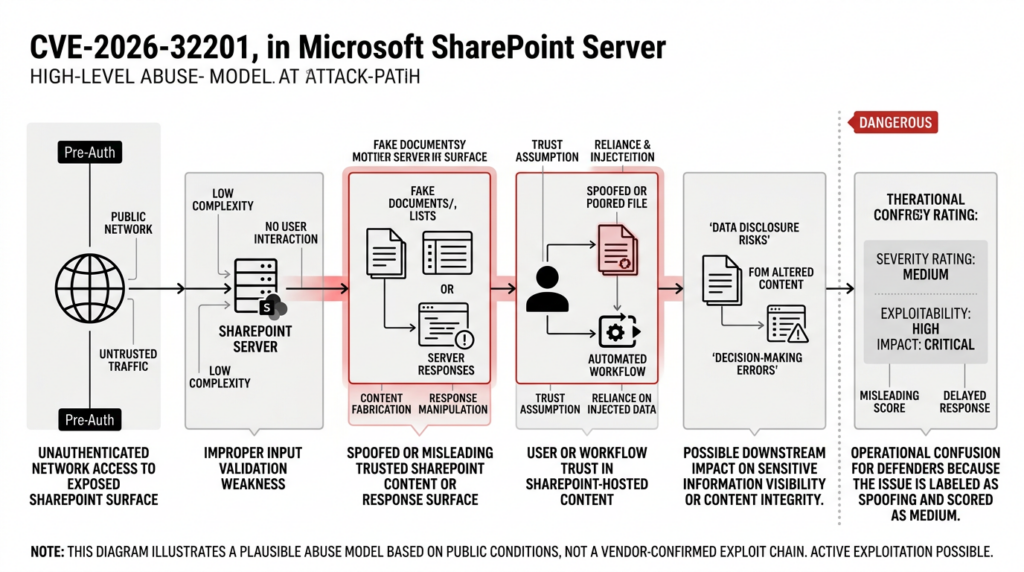
CVE-2026-32201 looks ordinary if you stare only at the score. NVD currently shows a Microsoft-supplied CVSS 3.1 base score of 6.5, and the official description says improper input validation in Microsoft Office SharePoint allows an unauthorized attacker to perform spoofing over a network. On paper, that reads like the kind of medium-severity issue that gets patched after the truly ugly bugs are out of the way. That reading does not survive contact with the rest of the record. Microsoft listed the flaw among the vulnerabilities that were exploited before the April 14, 2026 security updates were released, and CISA added it to the Known Exploited Vulnerabilities catalog the same day with an April 28 remediation deadline for federal civilian agencies. (NVD)
That combination matters more than the label. NVD shows a network attack vector, low attack complexity, no privileges required, and no user interaction required. In other words, the public record already says this is remotely reachable, pre-auth, and not dependent on a user clicking anything. Even before you know the full exploit chain, that is enough to move it out of the “we will fit it into the next patch cycle” bucket and into the “who owns the emergency change window” bucket. (NVD)
There is another reason to be careful here. The public technical picture is still incomplete. NVD marks the record as undergoing reanalysis, which means enrichment is still in motion. The official materials are strong on operational urgency and weak on exploit mechanics. That is exactly the kind of situation where low-quality writeups start inventing certainty. Some articles collapse the bug into generic XSS language. Others jump straight to full authentication bypass claims or post-exploitation stories that are not in the public Microsoft or NVD materials. A useful response has to resist both extremes. You do not need a full public root-cause writeup to know this deserves immediate action, but you also should not pretend the missing pieces are already confirmed. (NVD)
The practical problem for defenders is not “what is the CVE description.” The practical problem is this: if you run on-premises SharePoint, how do you patch correctly, prove you patched correctly, and hunt intelligently when the vendor has confirmed exploitation but the detailed exploit path is still thin in public? That is where most of the real work lives.
CVE-2026-32201, what is confirmed right now
The easiest way to lose time on a live SharePoint issue is to mix confirmed facts, reasonable inference, and rumor into one messy narrative. The current public record is clear enough to support urgent action, but not detailed enough to support reckless storytelling.
| Feld | Confirmed public information | Warum das wichtig ist |
|---|---|---|
| Publication date | NVD lists CVE-2026-32201 as published on April 14, 2026. (NVD) | This is the disclosure date tied to the April 2026 Patch Tuesday cycle. |
| Current NVD status | NVD marks the entry as Undergoing Reanalysis. (NVD) | The public record is still being enriched, so some details may change or become more specific. |
| Official description | Microsoft’s CVE description says improper input validation in Microsoft Office SharePoint allows an unauthorized attacker to perform spoofing over a network. (NVD) | The weakness class and attack surface are public; the exploit mechanics are not yet deeply documented in official text. |
| CVSS 3.1 vector | AV:N / AC:L / PR:N / UI:N / S:U / C:L / I:L / A:N, base score 6.5. (NVD) | Remote, low-complexity, pre-auth, no user interaction. That is a dangerous combination on exposed enterprise collaboration infrastructure. |
| Status der Ausbeutung | Microsoft’s April 2026 security update blog says CVE-2026-32201 was exploited before updates were released. Rapid7 also lists the Microsoft exploitation status as Exploitation Detected. (Microsoft) | This is not just theoretical exposure. It already crossed the threshold from patch hygiene to active risk management. |
| CISA status | NVD shows the flaw was added to CISA’s KEV catalog on April 14, 2026, with an April 28 due date and a required action to apply mitigations per vendor instructions. (NVD) | KEV inclusion is one of the strongest public signals that defenders should treat the issue as operationally real. |
| Affected product lines | NVD lists SharePoint Server 2019, SharePoint Server 2016 Enterprise, and SharePoint Server Subscription Edition up to but excluding 16.0.19725.20210. Microsoft support pages for April 14, 2026 publish security updates for Subscription Edition, SharePoint 2019, and SharePoint 2016 that resolve the flaw. (NVD) | The public evidence points to on-premises SharePoint Server lines, not a vague “Microsoft 365” umbrella. |
| Public exploit detail | No authoritative public Microsoft post I found gives a full exploit chain, endpoint-level root cause, or high-confidence IOC set for this CVE alone. NVD remains under reanalysis. (NVD) | Defenders should move quickly, but should also avoid treating rumor as detection engineering. |
That table drives the rest of the article. The threat is real. The public exploit detail is still incomplete. Those two statements are not in conflict. They are the operating conditions.
CVE-2026-32201 and the problem with the word spoofing
“SharePoint spoofing vulnerability” sounds smaller than it feels in practice. The phrase nudges people toward the wrong mental model. It sounds cosmetic, maybe adjacent to UI confusion, maybe annoying but not urgent. That is not how the rest of the public record frames this issue. Microsoft says exploitation was observed before patch release. CISA says federal agencies need to remediate on a short clock. CrowdStrike summarizes the bug as an unauthenticated remote issue with low complexity and notes that successful exploitation could affect both confidentiality and integrity. Qualys, Outpost24, and Rapid7 all call it out as one of the most important April 2026 items to patch despite the medium score. (Microsoft)
The score tells you why the math stayed moderate. The vector has low confidentiality impact, low integrity impact, and no availability impact. It does not describe catastrophic system-wide destruction. It also does not require privileges or user interaction. That is the tension. CVSS is measuring technical severity under a standardized framework. Defenders are dealing with operational risk in a real enterprise product that often sits in front of sensitive documents, workflow entry points, search results, content pages, service integrations, internal trust assumptions, and inherited organizational habits around “trusted Microsoft surfaces.” Those are not the same question. (NVD)
There is a practical lesson here that goes well beyond this one CVE. A medium score on a low-value edge service is one thing. A medium score on a high-trust, widely deployed collaboration surface that is already under active exploitation is something else. Security teams that work incident response already know this, but vulnerability programs still get tripped up by the category labels. “Spoofing” does not mean “not dangerous.” It means the security property Microsoft believes is being broken is trust in identity, origin, or authenticity. On a product like SharePoint, that can still be plenty.
This is also why the official impact language matters. CrowdStrike’s summary of Microsoft’s April data says an attacker who successfully exploits the issue could view sensitive information and make changes to disclosed information, with no availability impact. That is entirely consistent with the CVSS vector: modest per-event confidentiality and integrity impact, but more than enough real-world business impact to justify emergency remediation when the affected application is a central enterprise system. (crowdstrike.com)
The right response is to stop asking whether the score “feels high enough” and start asking better questions. Is the SharePoint farm reachable from the internet directly or through a reverse proxy? Does it host content or workflows that users inherently trust? Is it patched uniformly across all nodes? Can the team prove which build is present on each server? Can they show that suspicious pre-auth traffic patterns stopped after remediation? Those are the questions that decide whether this CVE becomes a contained change request or a long incident review.
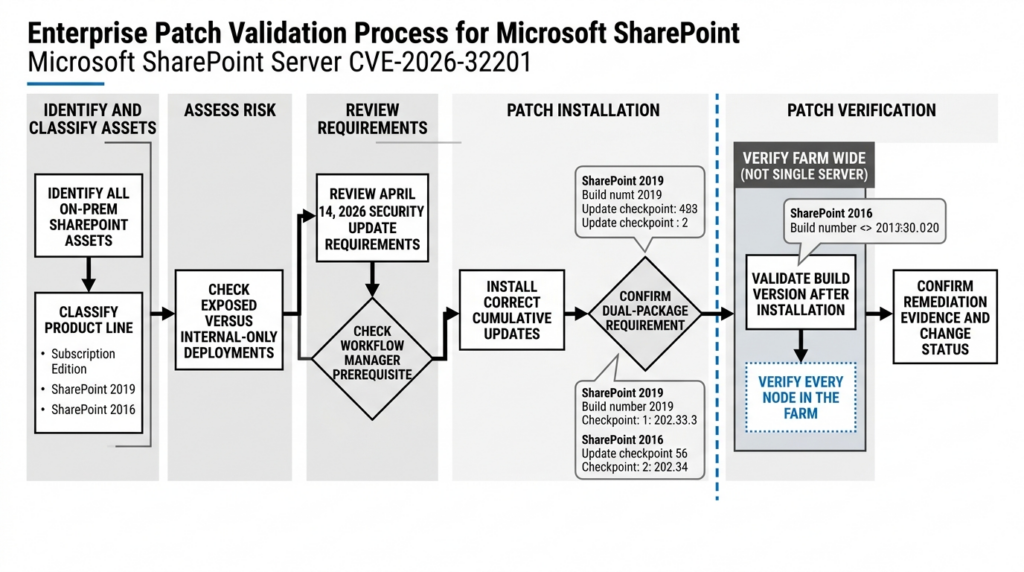
Affected SharePoint builds and the April 2026 patch line
The patching path is public, but many teams still get the details wrong, especially in older on-prem SharePoint estates with uneven update discipline. Microsoft published April 14, 2026 security updates for SharePoint Server Subscription Edition, SharePoint Server 2019, and SharePoint Server 2016. The official support pages state that these updates resolve the SharePoint Server spoofing vulnerability tied to CVE-2026-32201. The SharePoint update history pages provide the corresponding build lines. (support.microsoft.com)
| Product line | April 14, 2026 security update | Fixed build line | What to watch |
|---|---|---|---|
| SharePoint Server Subscription Edition | KB5002853 | 16.0.19725.20210 (support.microsoft.com) | NVD explicitly lists Subscription Edition as affected up to but excluding 16.0.19725.20210. (NVD) |
| SharePoint Server 2019 | April 14, 2026 update history entry, build 16.0.10417.20114, with KB5002854 and KB5002856 shown for the release date. (Microsoft Lernen) | 16.0.10417.20114 | Microsoft’s update history notes that the first KB for each release date is the language-independent STS update and the second is the language-dependent WSSLOC update, and both are required to fully update the farm. (Microsoft Lernen) |
| SharePoint Server 2016 | April 14, 2026 update history entry, build 16.0.5548.1003, with KB5002861 and KB5002862 shown for the release date. (Microsoft Lernen) | 16.0.5548.1003 | Microsoft’s update history says the same dual-package rule applies here as well. (Microsoft Lernen) |
That two-package detail on SharePoint 2019 and 2016 is easy to miss and expensive to miss. The update history pages explicitly say the first update or KB listed for each release date is the language-independent STS update and the second is the language-dependent WSSLOC update covering all language packs, including English installations, and both are required to fully update the farm. That sentence is exactly the kind of operational detail that disappears from shallow blog posts and then comes back to hurt during validation. (Microsoft Lernen)
The Microsoft support pages also include one more operational landmine. If you are currently running SharePoint Workflow Manager, Microsoft says you must install SharePoint Workflow Manager KB5002799 in the farm before installing the cumulative update. If you are still running the Classic version of Workflow Manager, Microsoft says you must enable a specific debug flag to continue using it, and the support pages include the exact PowerShell lines. That is not decorative documentation. In real environments, patch failures and post-patch complaints often come from these dependency corners, not from the CVE description itself. (support.microsoft.com)
One more nuance is worth stating clearly. The public April 2026 materials do not list SharePoint Online among the affected products for this CVE. The affected product evidence in NVD and the shipped support packages are all tied to SharePoint Server lines. That is a narrower statement than “we can prove SharePoint Online is not affected,” but it is still useful: the public remediation path here is focused on on-premises SharePoint Server deployments. (NVD)
CVE-2026-32201 and what public reporting still does not prove
The public evidence is enough to justify emergency patching. It is not enough to justify every dramatic claim you may have seen online.
As of April 20, 2026, the authoritative public sources I found do not provide a full root-cause narrative, a vendor-authored endpoint-level exploit explanation, or a Microsoft IOC pack specific to this one CVE. NVD explicitly marks the entry as under reanalysis. That means defenders should be precise about what they are saying. It is legitimate to say the bug is pre-auth, remote, low complexity, and actively exploited. It is not legitimate to present a full exploit path to farm-wide compromise as if Microsoft or NVD has already published it. (NVD)
This matters because shallow articles often smuggle inference into “fact” by using sloppy category language. One common failure mode is to see the word spoofing and treat it as a pure front-end presentation problem. Another is to read “unauthenticated SharePoint flaw” and immediately rewrite it as “full authentication bypass.” A third is to assume that because previous SharePoint incidents involved RCE chains and web shell behavior, this issue must work the same way. None of those shortcuts are defensible from the current public record. The record supports urgency, not improvisation. (NVD)
What can you reasonably infer from the confirmed vector? The issue is exposed over the network, does not require privileges, and does not depend on user interaction. That alone tells you this is not the same class of problem as an authenticated content editing bug or a click-driven reflected issue. It also tells you detection and validation should prioritize pre-auth request patterns, exposed farm inventory, patch uniformity, and post-patch behavioral confirmation. Beyond that, a lot of the honest answer is still “not public yet.” (NVD)
That uncertainty should change how you hunt. It should not delay patching. If anything, it makes disciplined remediation more important. When public exploit detail is thin, the safe and competent move is to rely on hard facts you do have: the affected product lines, the fixed build lines, the KEV escalation, the Microsoft exploitation confirmation, and the CVSS conditions. You can build a high-quality response around those without inventing the missing middle.
CVE-2026-32201 in the 2026 SharePoint pattern
CVE-2026-32201 is easier to understand if you place it next to the other SharePoint vulnerabilities Microsoft has had to address recently. Doing that exposes a pattern that many teams miss: “SharePoint spoofing” is not a single thing, and the practical response depends heavily on the access conditions and exploit state.
| CVE | Public description | Privileges required | User interaction | Exploitation status in public sources | Warum das hier wichtig ist |
|---|---|---|---|---|---|
| CVE-2026-32201 | Improper input validation in Microsoft Office SharePoint allows an unauthorized attacker to perform spoofing over a network. (NVD) | Keine | Keine | Microsoft says it was exploited before patch release; Rapid7 lists Exploitation Detected; CISA KEV includes it. (Microsoft) | This is the live priority because it is pre-auth and already exploited. |
| CVE-2026-20945 | Improper neutralization of input during web page generation in Microsoft Office SharePoint allows an authorized attacker to perform spoofing over a network. NVD lists CWE-79 and CVSS 4.6. (NVD) | Niedrig | Required | Rapid7 lists Exploitation Less Likely in its April 2026 table. (Schnell7) | It is fixed in the same April SharePoint updates, but its attack conditions are very different from 32201. |
| CVE-2026-20963 | Deserialization of untrusted data in Microsoft Office SharePoint allows an unauthorized attacker to execute code over a network. NVD lists CVSS 9.8 and CISA added it to KEV on March 18, 2026. (NVD) | Keine | Keine | KEV-listed earlier in 2026. (NVD) | It shows that SharePoint already had a far more direct RCE-class emergency earlier this year. |
That comparison is not just trivia. It corrects two operational mistakes.
The first mistake is collapsing CVE-2026-20945 and CVE-2026-32201 into the same story because both are described as SharePoint spoofing vulnerabilities and both are referenced by the April 14 support pages. They are not the same story. CVE-2026-20945, according to NVD, is an authorized attacker issue tied to improper neutralization of input during web page generation, with PR:L and UI:R. CVE-2026-32201 is unauthenticated, no user interaction, and already exploited. That difference should change both priority and detection logic. (NVD)
The second mistake is overfitting every SharePoint emergency to the previous RCE narrative. CVE-2026-20963 is a better analogue for “drop everything and assume execution risk,” because the public description is deserialization of untrusted data leading to remote code execution. CVE-2026-32201 is not publicly described that way. That does not make it low priority. It means the response should match the facts of the current bug, not the memory of the last one. (NVD)
There is a broader lesson hiding in this table. For SharePoint, the labels “spoofing,” “XSS,” and “RCE” tell only part of the story. The access preconditions, trust surface, exploitation status, and patch validation burden often matter more for response sequencing than the top-level impact noun.
Why an attacker would care about a pre-auth SharePoint spoofing bug
Even without a public exploit walkthrough, the official conditions tell you why this flaw is operationally attractive. SharePoint is rarely just a dumb content host. In many enterprises it carries documents, intranet pages, search surfaces, approval flows, internal links, team content, embedded business context, and a long tail of user trust that is far higher than the average externally reachable web application. That is why a pre-auth spoofing issue on SharePoint is not something you triage like a random marketing-site bug.
The key point is that the value of a spoofing bug depends on what is being trusted. If the target is a trivial page with no user trust and no workflow role, the blast radius is limited. If the target is a SharePoint deployment users already treat as a legitimate internal system, even modest confidentiality and integrity effects can matter a lot more than the word “medium” suggests. That is an inference from the confirmed impact language and from how SharePoint is commonly used in enterprise estates, not a claim that Microsoft has published a complete abuse narrative for this CVE. (NVD)
The most defensible attack-side possibilities to think about here are the boring ones. Not cinematic compromise. Trusted-surface abuse. Content users will believe because it is served from a known SharePoint location. Navigation and workflow confusion around URLs or pages users already recognize. Manipulation of visible information in ways that change decisions, not necessarily in ways that crash systems. That is exactly the kind of risk that can sit below the dramatic threshold of availability loss or full host takeover while still doing real damage to the organization. (NVD)
This is also why internet reachability matters so much. A pre-auth SharePoint issue is dramatically more dangerous when the affected farm is exposed directly or effectively exposed through a permissive reverse proxy. The first question after “are we running an affected build” is not abstract vulnerability theory. It is “can an unauthenticated requester get to it from the internet.” If the answer is yes, the path from advisory to response should be very short.
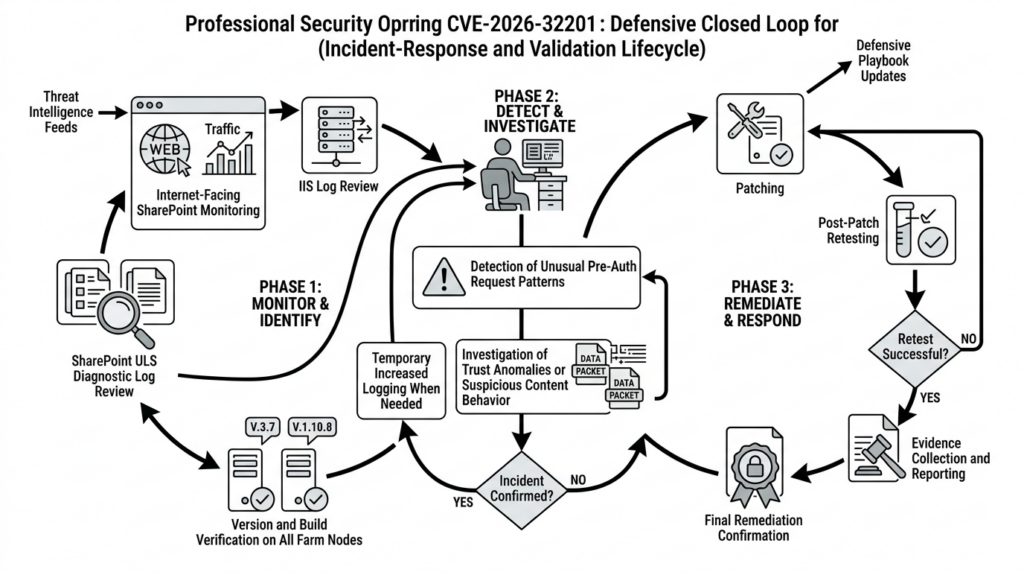
The first 24 hours for defenders, patching is not the whole job
When a SharePoint issue is both public and exploited, teams often lurch between two bad extremes. One group spends too long waiting for a perfect technical writeup. Another group pushes patches immediately and stops there, assuming patch deployment equals risk closure. Both approaches leave blind spots. A good first-day response is procedural, not theatrical.
The first task is asset truth. You need a list of every on-premises SharePoint Server deployment you own, including production, disaster recovery, staging environments that were accidentally exposed, legacy farms that no one loves, and internet-facing systems sitting behind load balancers or reverse proxies. The public remediation material is about SharePoint Server lines, so if your inventory is incomplete, your patch plan is already broken. Microsoft’s support pages and SharePoint update histories give you the build lines you need to compare against. (support.microsoft.com)
The second task is version truth. Microsoft Learn documents (Get-SPFarm).BuildVersion as a way to validate SharePoint build version, and the Get-SPProduct cmdlet returns SharePoint-related products installed in the farm along with versions of installed updates. Those two commands are a good starting point because they answer different questions: the farm’s current build state and the locally installed SharePoint-related product updates. (Microsoft Lernen)
# Run in SharePoint Management Shell on each server
(Get-SPFarm).BuildVersion
# Show locally installed SharePoint-related products and update versions
Get-SPProduct -Local |
Select-Object ProductName, ProductVersion |
Sort-Object ProductName
The third task is patch sequencing. For SharePoint Workflow Manager users, Microsoft’s April 14 support pages say KB5002799 must be installed before the cumulative update. For Classic Workflow Manager users, Microsoft says the debug flag must be enabled to continue using it. That is not an optional footnote. It is part of the actual deployment path. Teams that skip it often end up with self-inflicted outages and then waste time blaming the CVE response itself. (support.microsoft.com)
# Microsoft’s documented Classic Workflow Manager compatibility steps
$farm = Get-SPFarm
$farm.ServerDebugFlags.Add(53601)
$farm.Update()
iisreset
The fourth task is consistency across all nodes. SharePoint 2019 and 2016 are not “one file and done” if your farm needs both the language-independent STS update and the language-dependent WSSLOC update. Microsoft’s update history pages explicitly say both are required to fully update the farm. If you patch one front end cleanly and leave another partially updated, your dashboard may look better than your estate actually is. (Microsoft Lernen)
The fifth task is preserve enough telemetry to answer whether you were touched before patching. When exploit details are thin, defenders often over-collect in the wrong places and under-collect in the obvious ones. At minimum, preserve IIS logs, SharePoint ULS traces, and your boundary telemetry around the exposure window. SharePoint’s diagnostic logging guidance is also clear that verbose logging can generate a lot of data and hurt performance, so if you temporarily increase logging during a critical response window, treat that as a bounded change, not a forever setting. (Microsoft Lernen)
Proving the fix, not just applying it
The gap between “we installed the April updates” and “we can prove the fleet is covered” is where many vulnerability programs quietly fail. SharePoint farms are rarely neat. They have old nodes, language packs, forgotten servers, different operational owners, and change windows that drift across teams. If you want to handle CVE-2026-32201 well, you need evidence, not just intentions.
A simple verification loop should answer four questions. Which servers were in scope. Which exact build is now on each server. Which package requirements applied to that product line. Whether post-patch behavior looks materially different from pre-patch behavior on the exposed surface. None of those questions is hard individually. Together, they are what separates paper remediation from defensible remediation.
A practical version check can start with the official April build lines:
$expectedBuilds = @(
"16.0.19725.20210", # Subscription Edition
"16.0.10417.20114", # SharePoint Server 2019
"16.0.5548.1003" # SharePoint Server 2016
)
$currentBuild = (Get-SPFarm).BuildVersion.ToString()
$currentBuild
$currentBuild -in $expectedBuilds
That snippet is not meant to replace proper server-by-server verification. It is meant to force the basic conversation. If the build you see does not line up with the April 14, 2026 patched build for your product line, you are not done. If you are on SharePoint 2019 or 2016 and your package tracking does not show both updates required for the release date, you are not done. Microsoft’s update histories and support pages are explicit enough that there is no excuse for vague “should be patched” language in an internal status report. (Microsoft Lernen)
This is also the point where a workflow tool can be useful without becoming the center of the story. The helpful role for an AI-assisted validation platform in a case like CVE-2026-32201 is not to replace Microsoft’s advisory or guess at undocumented exploit steps. It is to make the post-advisory work less manual: inventorying exposed SharePoint assets, mapping which systems still answer on sensitive surfaces, replaying bounded validation after patch rollout, and exporting evidence with reproduction context. Penligent’s public materials emphasize attack-surface mapping, validation, authenticated flow testing, one-click exploit reproduction with evidence-chain reporting, and report export with reproduction steps. That makes it a natural fit for the verification phase after the vendor truth is already known, especially in teams that need to demonstrate more than “we clicked install.” (penligent.ai)
That is the right mental model for tooling here. Advisory truth comes from Microsoft, NVD, and CISA. Version truth comes from your own servers. Workflow tooling should help you connect those two with evidence.
Detection and hunting for a bug with thin public exploit detail
The detection challenge with CVE-2026-32201 is not that nothing is known. It is that not enough is publicly known to justify fake precision. If a blog is offering “the definitive exploit IOC for CVE-2026-32201” this early without strong source backing, be skeptical. A safer approach is to hunt for classes of behavior that line up with the confirmed attack conditions: unauthenticated network access against exposed SharePoint surfaces, unusual request patterns, anomalies around identity or content trust, and pre-patch versus post-patch changes in those patterns. (NVD)
SharePoint’s own logging stack gives you a reasonable starting point. Microsoft documents Get-SPLogEvent as the PowerShell way to view and filter diagnostic logs, and notes that you can search by message text, process, area, category, and other fields. That is useful here because the exploit path is not public enough to key off one magic string, but the operational symptoms you care about are still likely to show up in message content, claims-processing paths, validation logic, or unusual error patterns. (Microsoft Lernen)
A generic ULS triage pattern can look like this:
Get-SPLogEvent |
Where-Object {
$_.Message -like "*claims*" -or
$_.Message -like "*token*" -or
$_.Message -like "*validation*" -or
$_.Message -like "*FedAuth*" -or
$_.Message -like "*security*" -or
$_.Message -like "*spoof*"
} |
Select-Object Timestamp, Area, Category, Level, Message |
Out-GridView
That is not “the CVE-2026-32201 detector.” It is a disciplined way to ask, “what was happening on my SharePoint servers around the period I care about, especially in the parts of the stack most likely to show trust, token, validation, or access anomalies.” If you need more detail during a short response window, Microsoft’s diagnostic logging guidance supports temporarily increasing logging detail, but it explicitly warns that verbose logging records every action, consumes space quickly, and can affect performance. Turn it on with intent, and turn it back down after the critical window. (Microsoft Lernen)
IIS and boundary logs matter just as much. Since the public record says the issue is remotely reachable, low complexity, and pre-auth, your web logs should be part of the first-hour review. You are not trying to reverse-engineer the full exploit from status codes. You are looking for abnormal unauthenticated request concentration against SharePoint-sensitive paths, unexpected user agents, request bursts from new sources, and request behavior that changes sharply before and after the patch window.
A simple Windows-based triage pass might look like this:
$patterns = @(
"/_layouts/",
"/_vti_bin/",
" 401 ",
" 403 ",
" 500 "
)
Get-ChildItem "C:\inetpub\logs\LogFiles\W3SVC*" -Recurse -Filter *.log -ErrorAction SilentlyContinue |
ForEach-Object {
Select-String -Path $_.FullName -Pattern $patterns -SimpleMatch
} |
Select-Object Path, LineNumber, Line
That pattern is intentionally generic. It is not making a claim about the secret exploit path. It is doing what competent incident triage usually does first: find the hotspots, then decide what deserves deeper review.
If your environment feeds IIS data into Microsoft Sentinel or another SIEM, use the same principle. Build a concept query around exposed SharePoint hosts, authentication state, high-frequency unauthenticated requests, and sensitive path concentration. Do not oversell it as exploit-specific detection unless you actually have exploit-specific telemetry.
// Concept query only, adjust table and field names to your environment
W3CIISLog
| where csHost endswith "sharepoint.example.com"
| where csUriStem has_any ("/_layouts/", "/_vti_bin/")
| summarize Hits=count(), Paths=make_set(csUriStem, 20) by cIP, csUserAgent, scStatus, bin(TimeGenerated, 1h)
| order by Hits desc
There is also a content-side hunting problem here. Because the public effect is framed as spoofing rather than availability loss, user reports can matter. Pages that “look slightly wrong,” navigation that feels inconsistent, content appearing to originate from a trusted SharePoint location when it should not, or approvals and links that route users through unexpected SharePoint paths can all be stronger signals than defenders sometimes admit. Not every exploited flaw announces itself with a crash or a web shell.
What you should not do is lift a detection package from a different SharePoint incident and pretend it automatically fits this one. ToolShell-era hunting logic was shaped by public reporting on RCE chains and post-exploitation behavior. CVE-2026-32201, as publicly described today, is a different class of vulnerability. Start with the confirmed attack properties, not with muscle memory from last year’s SharePoint emergency. (penligent.ai)
Common mistakes that will waste your response window
The first common mistake is waiting for a perfect exploit writeup before patching. NVD already gives you enough to know this is remotely reachable, unauthenticated, and low complexity. Microsoft already says exploitation happened before patches were released. CISA already escalated it into KEV. More public detail would be nice. It is not a prerequisite for acting. (NVD)
The second mistake is letting the medium CVSS score override the rest of the context. CVSS is part of the picture, not the whole picture. A medium-scored pre-auth bug on an internet-exposed SharePoint surface that is already being exploited deserves higher practical priority than many theoretically nastier bugs that are not exposed and not active. The April 2026 analyses from Rapid7, Qualys, CrowdStrike, and Outpost24 all point in that direction. (Schnell7)
The third mistake is confusing CVE-2026-20945 with CVE-2026-32201 because they share a product family, a disclosure day, and a top-level “spoofing” label. Their conditions are materially different. CVE-2026-20945 requires an authorized attacker and user interaction. CVE-2026-32201 does not. If your internal ticketing or executive summary merges them into one bullet, your program is already losing fidelity. (NVD)
The fourth mistake is patching SharePoint 2019 or 2016 with incomplete package coverage. Microsoft’s update history pages are explicit that the two updates shown for the release date serve different roles and both are required to fully update the farm. This is not a guess, and it is not niche. It is Microsoft’s published update model. (Microsoft Lernen)
The fifth mistake is enabling verbose diagnostic logging and then forgetting it. Microsoft’s guidance is very clear that verbose-level logging records every action, uses space quickly, and can affect performance. In a rushed response, teams often flip logging to maximum detail and then leave it there until another problem appears. Treat logging changes as temporary operational measures, not as a permanent configuration improvement. (Microsoft Lernen)
The sixth mistake is assuming that “no confirmed compromise” and “nothing to do after patching” are the same sentence. Even if you never find hard proof of exploitation, the right post-patch state still includes asset inventory confirmation, build verification, and enough telemetry review to support a defensible answer when someone asks, “were we exposed before we fixed it?”
If you suspect exploitation, do not import the wrong playbook
SharePoint incidents have a way of dragging older memories into the room. That is understandable. Recent years have included enough high-profile SharePoint security events that many defenders now mentally map “SharePoint zero-day” to a full RCE chain with persistence and long incident-response tails. Sometimes that map is correct. It is not automatically correct here.
CVE-2026-32201 is publicly described as a spoofing vulnerability caused by improper input validation. CVE-2026-20963 earlier in 2026 was publicly described as deserialization of untrusted data leading to remote code execution. Those are different starting points. A good response should stay grounded in the current vulnerability’s public facts while remaining open to escalation if your telemetry shows something worse. (NVD)
The safest way to think about this is layered response. First, patch and verify according to the vendor path. Second, preserve and review the telemetry most likely to tell you whether unauthenticated abuse hit your exposed SharePoint surfaces. Third, if that review turns up signs of broader compromise, then escalate into a full incident workflow appropriate to what you actually observed. The key is not to confuse careful escalation with underreaction. You can be disciplined without being complacent.
That discipline matters because SharePoint is a trust surface. If you see suspicious pre-auth access patterns around the vulnerability window and user reports that suggest content or navigation trust was being abused, that may justify a broader identity and content review even if you do not have evidence of host-level compromise. Conversely, if you start from an RCE-heavy playbook with assumptions that do not match the public flaw class, you may spend the first day hunting for artifacts that have little to do with this issue while missing the behaviors that actually matter.
CVE-2026-32201 is a patching problem and a proof problem
The public story around CVE-2026-32201 is easy to summarize badly. “Medium SharePoint spoofing bug, patch it.” That sentence is not wrong, but it leaves out the part that matters. The issue was exploited before patch release. It is pre-auth, remote, low complexity, and on a product line that frequently sits on high-trust enterprise surfaces. NVD is still reanalyzing it, which means the public technical picture is not finished. That combination is exactly why defenders should become more disciplined, not less. (NVD)
The immediate answer is straightforward. Patch the right SharePoint Server lines. Respect the Workflow Manager prerequisites. Install both required updates where Microsoft says both are required. Verify the resulting builds on every relevant server. Preserve enough telemetry to know whether you were touched before the fix landed. Hunt with honesty about what is and is not publicly known. (support.microsoft.com)
The more lasting answer is cultural. This is one more reminder that CVSS alone is not a triage program, and patching alone is not a verification program. When an issue is actively exploited on a collaboration platform like SharePoint, the hard part is often not reading the advisory. The hard part is proving that every exposed farm was identified, patched correctly, and checked in a way another engineer can trust six weeks later.
Weiterführende Literatur und Referenzlinks
NVD entry for CVE-2026-32201, including current reanalysis status, CVSS vector, affected product references, and KEV metadata. (NVD)
Microsoft April 2026 security updates blog, which lists CVE-2026-32201 among the vulnerabilities exploited before updates were released. (Microsoft)
Microsoft Support, SharePoint Server Subscription Edition April 14, 2026 update, KB5002853. (support.microsoft.com)
Microsoft Support, SharePoint Server 2019 April 14, 2026 update, KB5002854. (support.microsoft.com)
Microsoft Support, SharePoint Server 2016 April 14, 2026 update, KB5002861. (support.microsoft.com)
Microsoft Learn, SharePoint update history for Subscription Edition, SharePoint 2019, and SharePoint 2016. (Microsoft Lernen)
NVD entry for CVE-2026-20945, useful for distinguishing the other April SharePoint spoofing issue from CVE-2026-32201. (NVD)
NVD entry for CVE-2026-20963 and CISA’s March 18, 2026 KEV addition, useful for recent SharePoint RCE context. (NVD)
Rapid7 Patch Tuesday analysis for April 2026, including exploitation status tables. (Schnell7)
CrowdStrike April 2026 Patch Tuesday analysis, including the public impact summary for CVE-2026-32201. (crowdstrike.com)
Qualys April 2026 Patch Tuesday review and Outpost24 April 2026 Patch Tuesday analysis. (Qualys)
Microsoft Learn documentation for Get-SPProduct, Get-SPFarm, diagnostic logging configuration, and viewing SharePoint diagnostic logs. (Microsoft Lernen)
Penibel, CVE-2025-53770 ToolShell and the SharePoint Trust Problem That Patching Alone Doesn’t Solve. (penligent.ai)
Penibel, How to Get an AI Pentest Report. (penligent.ai)
Penibel, Plans and Pricing, for public details on attack-surface mapping, authenticated flow testing, one-click exploit reproduction with evidence-chain reporting, and exportable reports with reproduction steps. (penligent.ai)