When people type “mitre cve funding” into Google, they’re rarely hunting for a budget spreadsheet.
They’re trying to answer a single, operationally urgent question:
Is the CVE Program—how the world assigns and coordinates vulnerability IDs—stable, or could contract and funding uncertainty create delays, fragmentation, and downstream breakage across the security ecosystem?
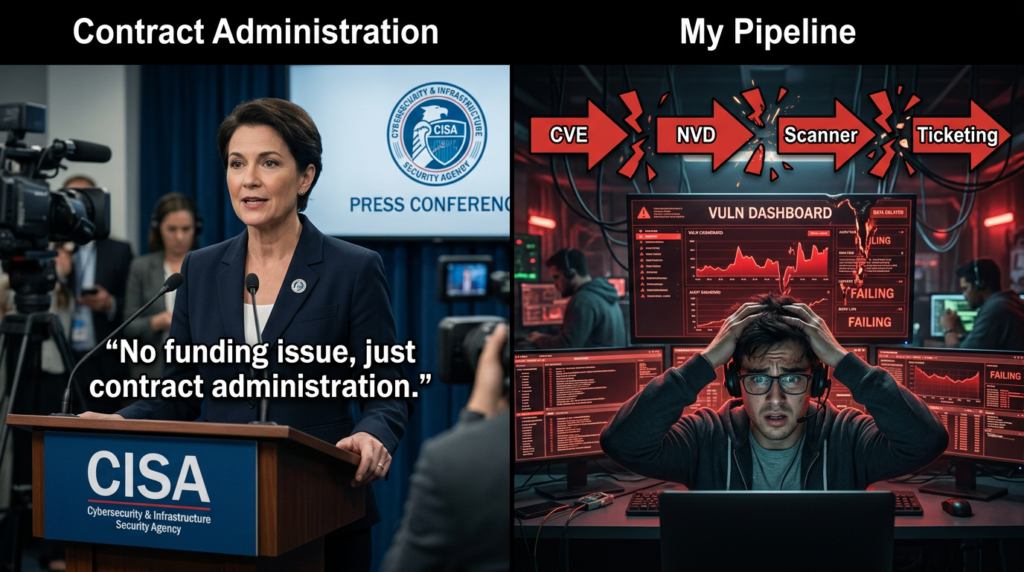
That question became acute in April 2025, when MITRE warned that the “contracting pathway” supporting its work to operate and modernize the CVE Program was set to expire on April 16, 2025, and the industry briefly faced a scenario where a foundational coordination layer might stall. (The Verge)
CISA then stated it executed the contract’s option period to ensure there would be no lapse in critical CVE services, with reporting describing an extension of about 11 months. (CISA)
A week later, CISA’s Matt Hartman emphasized there was no funding issue and characterized it as a contract administration issue resolved prior to any lapse. (CISA)
Even though a shutdown was avoided, the moment mattered. It exposed a truth that many practitioners had quietly assumed away:
Global vulnerability operations depend on CVE like it’s permanent infrastructure, but its continuity can still be exposed to contracting realities—and that risk has real engineering consequences. (WIRED)
This article is written for security engineers, vulnerability management leads, and automation-heavy teams who need more than headlines. It reconstructs what happened, explains why the “naming layer” is the load-bearing beam of vulnerability response, and provides practical patterns—plus code and tables—you can actually use.
What “MITRE CVE funding” actually means
In plain terms, “MITRE CVE funding” refers to the contractual and financial support behind MITRE’s role in operating key parts of the CVE Program—the system that assigns standardized vulnerability identifiers like CVE-2026-2441.
This matters because CVE is not “just a list.” CVE IDs function as a universal join key across the security world:
- Vendor advisories reference CVEs
- Scanners map detections to CVEs
- Patch tickets are created from CVEs
- Threat intel feeds correlate campaigns to CVEs
- Compliance reporting often asks whether specific CVEs were remediated
That’s why a perceived risk to CVE continuity triggered immediate attention: it’s not about prestige, it’s about the integrity of day-to-day operations.
In April 2025, the worry was that the contract supporting MITRE’s operation and modernization of CVE could expire on April 16, leading to immediate service disruption—an outcome many observers described as potentially chaotic for the global coordination ecosystem. (The Verge)
CVE is a naming system, not a “database,” and that distinction is everything
A lot of confusion comes from treating CVE as if it’s simply a website. In practice:
- CVE is the naming/identifier system—“this vulnerability has a globally recognized label”
- NVD is a major public database that ingests CVE entries and adds enrichment and analysis
If you build automation, you can think of CVE as the primary key, and enrichment sources as the attributes.
This is why “mitre cve funding” spooked practitioners more than the idea of a single database going offline. When the naming layer is unstable, even temporarily, everything downstream becomes harder to align.
The April 2025 timeline, what happened and what was publicly confirmed
Let’s lay out the core facts with sources you can cite internally.
April 15 to April 16, MITRE warning spreads and the ecosystem reacts
Media coverage and vendor commentary described a MITRE communication (widely circulated on social media) warning that MITRE’s contract to operate and modernize the CVE Program would expire on April 16, 2025, potentially leading to an “immediate expiration in services.” (Checkmarx)
The Verge’s reporting described CVE as a system used by major companies and the broader community to identify and track publicly disclosed vulnerabilities, and emphasized the risk of disruption if federal funding lapsed. (The Verge)
April 16, CISA states it executed the option period to prevent a lapse
CISA published a statement on April 16, 2025 indicating it executed the contract option period to ensure there would be no lapse in critical CVE services. (CISA)
Nextgov reported the extension was for 11 months, quoting the agency spokesperson language about preventing a lapse. (Nextgov/FCW)
April 23, CISA says it was contract administration, not a funding problem
CISA’s Matt Hartman later said “there was no funding issue,” framing it as a contract administration issue resolved prior to any lapse. (CISA)
Contract record visibility, the “option period” shows up in public spending data
USASpending includes an award entry associated with MITRE work that references CVE and CWE and shows an action labeled “EXERCISE AN OPTION” with a date of 04/16/2025. (USAspending)
Same-day governance signal, the CVE Foundation is announced
On April 16, 2025, the CVE Foundation announced its launch, positioning itself around the long-term stability and independence of the CVE mission. (Forbes)
Wired and WSJ coverage captured the broader debate: even with the short-term extension, stakeholders questioned whether such a globally relied-upon program should remain dependent on a single contracting pathway. (WIRED)
Why security people searched it, the real operator mindset
If you ran a vulnerability management program in April 2025, you weren’t thinking in abstracts. You were thinking:
- “Are new CVEs going to get assigned on time this week?”
- “Do our scanners and intel feeds depend on CVE publication timing?”
- “If IDs slow down, how much manual reconciliation will my team absorb?”
- “What do I tell leadership if our reporting pipeline breaks?”
This is why “mitre cve funding” shows up as a blunt query. It’s the fastest way to get situational awareness.
The Verge framed the concern well: CVE helps teams coordinate patching and prioritization, and disruption risks confusion and weakened defensive alignment across stakeholders. (The Verge)
What breaks when the CVE layer wobbles, concrete failure modes
Even without a full outage, there are predictable engineering failures when the identifier layer becomes uncertain.
1 Slower ID assignment cascades into slower downstream enrichment
Many systems wait on CVE IDs to anchor:
- severity ratings
- exploitability analysis
- detection content mapping
- vendor patch correlation
A delay at the start of the chain can look like “everything is fine” until you discover your dashboards silently stopped joining events correctly.
2 Alias chaos, the same vulnerability gets three names and your automation loses certainty
In the absence of timely, consistent identifiers:
- a vendor advisory name becomes the “temporary ID”
- a threat intel vendor uses a campaign label
- a scanner uses a plugin title
Then your team spends time answering a question nobody should waste time on:
Is this the same bug or not?
3 Reporting and compliance go brittle
Many programs still require evidence like:
- “We remediated CVE-XXXX-YYYY on all internet-facing assets”
- “This KEV entry is mitigated and verified”
If the identifier workflow is uncertain, you end up with messy exceptions, manual attachments, and loss of confidence in your own numbers.
4 Risk prioritization collapses back into spreadsheet triage
When joins break, the easiest fallback is human triage, which is the slowest and least consistent path.
This is why people reacted strongly to the April 2025 scare even though it was ultimately avoided.
A table you can drop into an internal doc, failure mode to mitigation mapping
| Failure mode during CVE uncertainty | What it looks like in real ops | Why it’s dangerous | Mitigation pattern |
|---|---|---|---|
| CVE assignment delays | “Pending CVE” advisories, missing joins | Intel, scanners, and tickets drift apart | Treat vendor advisory + product scope as the primary record until CVE lands |
| Alias proliferation | Multiple names for the same issue | Duplicate work or missed work | Implement alias mapping and provenance fields in your vuln objects |
| Dashboard joins fail | Fewer “critical” items appear | False sense of safety | Add sanity checks: compare vendor advisory volume vs CVE-ingested volume |
| Las pruebas de cumplimiento se debilitan | Can’t show CVE-anchored remediation proof | Audit friction, leadership distrust | Store proof artifacts tied to asset + patch level, not only to CVE ID |
| Prioritization regressions | Teams chase CVSS alone | Exploited issues get missed | Use KEV and exploit signals as priority multipliers |
CVE case studies, why the naming layer shapes response speed
The fastest way to understand the importance of CVE continuity is to look at vulnerabilities that became global events.
CVE-2021-44228, Log4Shell shows how a single ID becomes a global coordination anchor
Log4Shell is a perfect illustration: the ecosystem needed one label to correlate vendor advisories, scanner detections, and mitigations across countless products. Penligent’s own Log4Shell write-up treats it as a cluster of issues and emphasizes proof-based remediation rather than “patch and pray,” which is exactly what mature teams learned the hard way. (Penligente)
CVE-2024-6387, regreSSHion shows why “is it exploited” changes the entire response posture
For regreSSHion, NVD describes a regression leading to an unsafe signal-handling race condition where an unauthenticated remote attacker may be able to trigger the issue by failing to authenticate within a set time period. (NVD)
Qualys’ technical analysis and vendor bulletins detail the nature of the race condition and affected versions in practical terms. (Qualys)
And the reason this CVE re-enters the spotlight in organizations is often when exploit signals rise—frequently aligned with attention from authoritative sources like CISA’s broader KEV guidance and catalog-driven triage practices. (CISA)
CVE-2025-53770, SharePoint ToolShell demonstrates why “in-the-wild” turns into immediate governance
Microsoft’s MSRC guidance stated it released security updates protecting supported SharePoint versions affected by CVE-2025-53770 and CVE-2025-53771 and urged immediate application, explicitly referencing active attacks. (Microsoft)
NVD describes CVE-2025-53770 as deserialization of untrusted data allowing an unauthorized attacker to execute code over a network, and notes awareness of an exploit existing in the wild. (NVD)
CISA published an alert with defensive guidance and clarifications around related CVEs and mitigations. (CISA)
MITRE ATT&CK also tracks ToolShell exploitation as a campaign and ties it to the patched CVEs, underscoring how the ecosystem uses identifiers to align incident narratives. (MITRE ATT&CK)
CVE-2026-2441, Chrome UAF shows how “new CVE received” becomes an immediate fleet action item
NVD’s entry for CVE-2026-2441 describes a use-after-free in CSS in Google Chrome prior to a specific version, with references to the official Chrome Releases blog. (NVD)
For enterprises, the most important part is not the CWE label—it’s operational: patch quickly, restart the browser, and verify fleet compliance.
These case studies all share a pattern: the CVE ID becomes the coordination spine. When the spine is uncertain, everything else flexes in uncomfortable ways.
The best operational takeaway from April 2025, treat CVE as an index, not the truth
If your workflow equates “we have a CVE ID” with “we understand risk,” you are fragile.
A resilient workflow treats CVE as a routing label, not the final signal.
Here’s a practical hierarchy that survives CVE turbulence:
- Vendor advisory + affected product scope is the initial record
- Exposure evidence on your assets is the risk reality
- Exploit signals determine urgency
- Patch and mitigation status must be verified
- ID CVE is the join key that improves coordination, but it should not be the only anchor
This mindset maps cleanly to how CISA expects organizations to use KEV: prioritize based on exploitation evidence, not solely on theoretical severity. (CISA)
Practical automation, a minimal Python workflow you can actually run
Below is a simple pattern: treat “vulnerability objects” as first-class items in your system, with provenance fields that can survive missing or delayed CVE attributes.
Example, pull a CVE record from NVD and enrich it for your own workflow
"""
Minimal example: fetch an NVD CVE detail page as a source of truth links,
then store "provenance" fields so you can survive temporary ecosystem drift.
Note:
- NVD has APIs, but access policies and keys can change.
- This example uses simple HTTP GET to demonstrate the workflow structure.
"""
import re
import json
import time
from dataclasses import dataclass, asdict
from typing import List, Optional
import requests
@dataclass
class VulnRecord:
cve_id: str
title: str
source_urls: List[str]
vendor_advisory: Optional[str]
exploit_signal: Optional[str] # e.g. "KEV", "Vendor says exploited", "None"
affected_products_hint: Optional[str]
created_at: float
def extract_urls(html: str) -> List[str]:
# naive URL extraction; replace with proper parsing in production
urls = set(re.findall(r"https?://[^\\s\\"'>]+", html))
return sorted(urls)
def build_record(cve_id: str, vendor_advisory: Optional[str] = None) -> VulnRecord:
nvd_url = f"<https://nvd.nist.gov/vuln/detail/{cve_id}>"
r = requests.get(nvd_url, timeout=20)
r.raise_for_status()
urls = extract_urls(r.text)
# minimal "title" placeholder; in production parse the description/title
title = f"NVD detail for {cve_id}"
return VulnRecord(
cve_id=cve_id,
title=title,
source_urls=[nvd_url] + urls[:15],
vendor_advisory=vendor_advisory,
exploit_signal=None,
affected_products_hint=None,
created_at=time.time(),
)
if __name__ == "__main__":
record = build_record("CVE-2026-2441", vendor_advisory="<https://chromereleases.googleblog.com/>")
print(json.dumps(asdict(record), indent=2))
Why this structure holds up during uncertainty:
- You can store vendor advisory references even before enrichment stabilizes
- You can attach exploit signals when they appear
- Your internal tickets don’t depend on any single upstream field being present at the exact moment you need it
For CVE-2026-2441 specifically, NVD’s references include the Chrome Releases blog and the Chromium issue tracker, which are exactly the upstream links an engineer should preserve. (NVD)
A table of high-impact CVEs, why they matter to “mitre cve funding” thinking
| CVE | Why it became an ecosystem event | What it teaches about identifiers |
|---|---|---|
| CVE-2021-44228 Log4Shell | Cross-product dependency RCE ripple effect | One label enables global coordination and triage at scale (Penligente) |
| CVE-2024-6387 regreSSHion | “Remote, unauthenticated” risk in a ubiquitous service | Exploit signals and version scoping determine true urgency (NVD) |
| CVE-2025-53770 SharePoint ToolShell | In-the-wild exploitation, enterprise foothold value | “Exploited” turns patching into incident response (Microsoft) |
| CVE-2026-2441 Chrome CSS UAF | Browser RCE risk, fleet patch verification | Fast patch + restart verification beats debating severity (NVD) |
These are not random examples. They are the kind of vulnerabilities that force organizations to coordinate across vendors, tools, and internal stakeholders—exactly the scenario where CVE’s continuity matters most.
What the top coverage got right, and where engineers should read between the lines
If you read the highest-visibility coverage around the April 2025 scare, you see a consistent theme:
- The Verge framed CVE as a linchpin used across industry to track vulnerabilities and coordinate response, and warned that loss of support could cause confusion across stakeholders. (The Verge)
- Wired highlighted how last-minute contracting created unnecessary risk for critical infrastructure and surfaced concerns about sustainability and governance. (WIRED)
- Nextgov emphasized the operational reality: CISA executed the option period to avoid a lapse, and reported the extension window. (Nextgov/FCW)
- CISA’s own statements clarified the government position and later pushed back on the “funding” framing, calling it contract administration. (CISA)
The engineer’s conclusion should not be “the sky is falling.” It should be:
Design your vulnerability workflow so that it doesn’t collapse if a single upstream coordination layer gets noisy for a week.
The April 2025 scare wasn’t primarily about money. It was about a hidden dependency: modern security operations assume the vulnerability ecosystem will always deliver clean, timely identifiers and enrichment.
That’s also where many teams feel pain today: not in discovering CVEs, but in turning them into verified outcomes.
Penligent is built around that gap—turning natural-language intent into precise security actions and producing evidence-driven outputs. If your program has ever experienced “we patched it, but we can’t prove it across the fleet,” you already know the difference between paper remediation y verifiable remediation.
This matters most for exploited, high-impact vulnerabilities like SharePoint ToolShell and browser zero-days, where the cost of “we think we’re good” is measured in incident response hours. In those moments, the most valuable artifact isn’t a screenshot of a dashboard—it’s a repeatable workflow that can validate exposure and remediation status at scale, then report it in a way leadership and auditors can trust.
If you want concrete examples of how proof-based remediation thinking applies to high-impact CVEs, Penligent’s Log4Shell write-up is a good reference point because it focuses on “how exploitation becomes real in systems” and how to validate at scale rather than treating the CVE as a ticket to close. (Penligente)
Conclusion, the real meaning behind “mitre cve funding”
“MITRE CVE funding” is a search term that reveals a mature fear: not fear of a single vulnerability, but fear of the infrastructure that helps the world coordinate vulnerabilities.
April 2025 showed that even a brief contracting scare can trigger ecosystem-level anxiety because CVE is a load-bearing join key for modern security operations. CISA’s actions prevented a lapse, and later clarified the situation publicly, but the incident still served as a stress test for how brittle many workflows can be when an assumed dependency becomes uncertain. (CISA)
If you take only one actionable idea from this story, take this:
Treat CVE as an index—use it aggressively—but design your program so real risk decisions are driven by vendor truth, asset exposure evidence, exploit signals, and verified remediation.
Enlaces
- CISA, Statement on CVE Program, April 16, 2025 (CISA)
- CISA, Statement from Matt Hartman on the CVE Program, April 23, 2025 (CISA)
- NVD, CVE-2026-2441 detail and references (NVD)
- Microsoft MSRC, Customer guidance for SharePoint vulnerability CVE-2025-53770 (Microsoft)
- MITRE ATT&CK, ToolShell exploitation campaign reference (MITRE ATT&CK)
- USASpending award record referencing CVE/CWE option exercise (USAspending)
- Penligent, Log4Shell CVE Still Matters in 2026, CVE-2021-44228 lessons (Penligente)
- Penligent, CVE-2024-6387 regreSSHion trending again, operational guidance (Penligente)
- Penligent, CVE-2026-2441 Chrome CSS zero-day, patch and proof across fleets (Penligente)