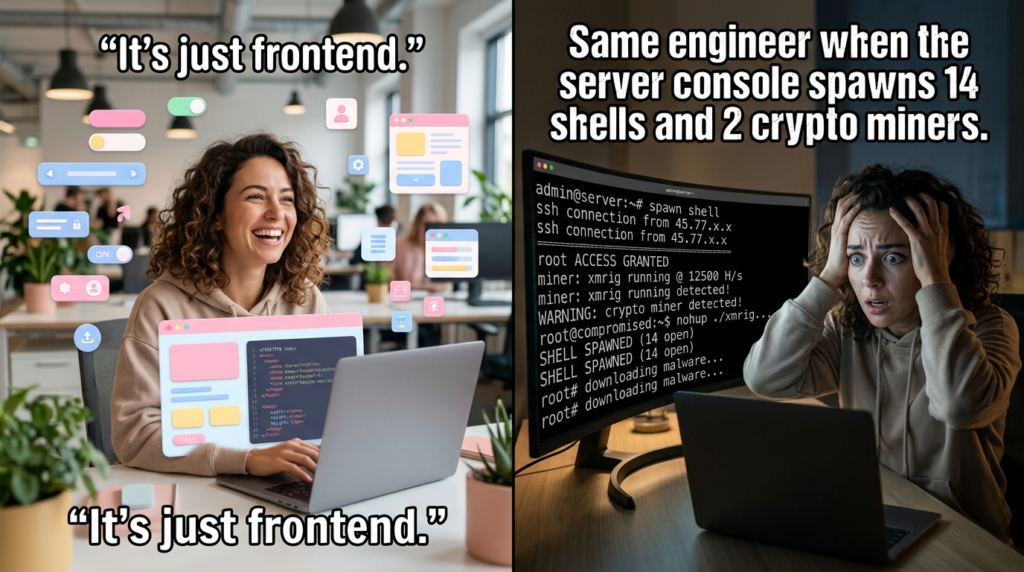
In security, some bugs are dangerous because they are common. Others are dangerous because they are elegant. React2Shell belongs to the second category. It did not become a major story because it looked like an old-school injection flaw with a new name. It became a major story because it exposed a deeper truth about modern web architecture: once your framework collapses the boundary between UI rendering and server execution, a serialization bug can become an operating-system-level problem. (Reaccione)
React2Shell is the name widely used for the critical React Server Components remote code execution issue disclosed in December 2025. The upstream vulnerability is CVE-2025-55182. Next.js also tracked downstream impact under CVE-2025-66478, but that record was later rejected as a duplicate of CVE-2025-55182 by both CVE.org and NVD. For defenders, that detail matters because many scanners, tickets, dashboards, and third-party reports still reference both IDs. In practice, teams should treat them as the same incident family, not as two unrelated findings. (CVE)
The reason this incident resonated so strongly with security engineers is simple: it broke the comforting assumption that “frontend frameworks” are mostly client-side concerns. React Server Components are not just a rendering optimization. They are a protocol surface, an execution model, and a trust boundary. When that trust boundary fails, the result is not cosmetic corruption or a bad cache entry. It is unauthenticated remote code execution against production servers. React rated CVE-2025-55182 at CVSS 10.0, and major defenders including Google Threat Intelligence Group, Palo Alto Networks Unit 42, Microsoft, Trend Micro, PortSwigger, and Wiz all treated the issue as an urgent operational event rather than a theoretical design flaw. (Reaccione)
This article is for security engineers, red teamers, appsec leads, DevSecOps practitioners, and engineering managers who need more than a headline. We will walk through what React2Shell actually is, why the root cause matters beyond one CVE, which versions were affected, how the exploit chain worked at a high level, what real-world threat activity looked like, which related CVEs came next, how to assess exposure in a modern React and Next.js estate, how to patch safely, and where automated validation platforms fit when logic flaws cut across dependency graphs, routing layers, and runtime behavior. Every major factual point here is grounded in current public sources from official vendors and reputable security research. (Reaccione)
What React2Shell actually means
At the center of this story is CVE-2025-55182. React’s own advisory described it as an unauthenticated remote code execution vulnerability in React Server Components and stated that even applications that do not explicitly implement Server Function endpoints may still be vulnerable if they support React Server Components. NVD’s description is similarly direct: vulnerable React Server Components unsafely deserialize payloads from HTTP requests to Server Function endpoints. (Reaccione)
That description is important because it makes clear that React2Shell was not a classic bug caused by a developer concatenating unsafe input into a shell command. It was a framework-layer flaw. The mistake lived in the protocol and deserialization logic that React used to move structured data between client and server in the React Server Components model. In other words, the vulnerable surface was not “your business logic,” at least not primarily. The vulnerable surface was the framework machinery that sits below your business logic and often remains invisible to the average product engineer. (NVD)
Next.js complicated public understanding because the first wave of coverage often treated CVE-2025-55182 and CVE-2025-66478 as a pair. Next.js itself explicitly said that the critical issue originated in the upstream React implementation and that its own advisory tracked downstream impact on App Router applications. Later, CVE.org and NVD marked CVE-2025-66478 as rejected because it was a duplicate of CVE-2025-55182. That does not mean old alerts using the Next.js identifier are wrong; it means the ecosystem eventually consolidated around the upstream root cause. (Siguiente.js)
If you are triaging old tickets, dependency scans, DAST findings, WAF signatures, or threat intel entries, the practical mapping looks like this:
| Identifier | What it refers to | Operational meaning |
|---|---|---|
| CVE-2025-55182 | Upstream React Server Components RCE | Canonical React2Shell record |
| CVE-2025-66478 | Next.js downstream tracking ID | Treat as duplicate of CVE-2025-55182 |
| React2Shell | Common community and vendor name | Usually refers to the same RCE incident family |
| RSC Flight protocol RCE | Technical shorthand in research write-ups | Same root issue in the React Server Components transport and deserialization path |
This normalization step sounds minor, but it prevents a common failure mode in incident response: teams undercounting exposure because one business unit tracks the issue under the React CVE while another tracks it under the Next.js CVE. (CVE)

Why this bug was different from the usual web RCE story
Many severe web vulnerabilities fit one of a few familiar patterns. A template engine evaluates attacker input. A framework route passes tainted data to a dangerous sink. A deserializer restores attacker-controlled objects without validation. A plugin exposes a command execution path. React2Shell shared DNA with unsafe deserialization, but the context made it more disruptive.
React Server Components and Server Functions blur the line between client behavior and server behavior. That is part of the value proposition: developers write less glue code, move more work server-side, and stream richer UI state. But that same abstraction makes it easier to overlook where parsing ends and execution begins. Unit 42 described CVE-2025-55182 as insecure deserialization within the RSC architecture, specifically involving the Flight protocol. Microsoft similarly described the issue as failure to validate incoming payloads, allowing malicious structures to be accepted and leading to prototype pollution and remote code execution. (Unidad 42)
That combination is what made the bug so unsettling. This was not just “malformed input causes crash.” It was “malformed protocol input can reshape server-side execution behavior.” And because modern React and Next.js apps often expose these protocol surfaces by default as part of normal application behavior, the reach of the bug was wider than many teams initially assumed. Wiz said a standard crear-siguiente-app production build could be exploitable with no code changes by the developer, and PortSwigger warned that even if an application did not explicitly call server actions, it could still be vulnerable if it supported React Server Components. (wiz.io)
This is why React2Shell landed closer to the “framework event” category than the “app bug” category. Security teams were not just evaluating one codebase. They were evaluating an ecosystem pattern. Anything that inherited React Server Components behavior, used App Router semantics, or exposed Server Functions endpoints became part of the response scope. Sysdig’s coverage explicitly listed not only Next.js, but also React Router in RSC mode, Waku, Parcel RSC, Vite RSC, and RedwoodSDK as affected framework contexts. (Sysdig)
The root cause, without turning this into an exploit manual
The high-level root cause is well established across official and major research sources. CVE-2025-55182 was caused by unsafe deserialization of attacker-controlled payloads within React Server Components. React described the flaw as affecting the handling of React Server Components in specific packages. NVD said the vulnerable code unsafely deserializes payloads from HTTP requests to Server Function endpoints. Unit 42, Microsoft, Wiz, and Sysdig all tied exploitation to malformed or attacker-controlled RSC payloads influencing server-side execution. (Reaccione)
The additional nuance that matters for defenders is that this was not simply a “one bad function call” issue. Trend Micro’s analysis described a multi-stage exploitation chain involving self-reference, JavaScript execution tricks, attacker-controlled initialization, and final arbitrary code execution via JavaScript semantics. That level of complexity matters less for exploit developers than for defenders because it explains why traditional coarse-grained detections were unreliable. You could not safely infer exploitability from one HTTP header, one route name, or one obvious marker. Attackers had room to vary payload structure and delivery. GTIG explicitly noted that exploitation potential was increased by the variety of valid payload formats and techniques, and by the fact that the mere presence of vulnerable packages on systems was often enough to permit exploitation. (www.trendmicro.com)
What this means in plain engineering language is that the vulnerable parser lived in a place where structured transport data and JavaScript object semantics met. When an attacker could shape that structured data carefully enough, the system stopped acting like a safe renderer and started behaving like an execution gadget chain. The reason the event felt so abrupt to many teams is that those gadget chains were not hand-authored in application code. They emerged from the framework’s own internal assumptions about how protocol objects should be revived, resolved, and processed. (Unidad 42)
This is exactly the kind of modern risk that gets missed when organizations split application security too aggressively into silos. SAST may confirm dependency versions. DAST may find obvious reachable routes. Runtime tools may catch post-exploitation behavior. But the dangerous gap is often the validation layer between “reachable protocol surface” and “provable exploitability.” React2Shell exposed that gap very clearly. (PortSwigger)
Affected versions and ecosystems
The official React advisory identified the vulnerable packages and versions clearly. React said the vulnerability was present in versions 19.0, 19.1.0, 19.1.1, and 19.2.0 of react-server-dom-webpack, react-server-dom-parcely react-server-dom-turbopack. It also said fixes were introduced in 19.0.1, 19.1.2, and 19.2.1. (Reaccione)
Next.js added important downstream context. Its advisory said the affected cases were applications using React Server Components with the App Router on Next.js 15.x, 16.x, and 14.3.0-canary.77 and later canary releases. It also explicitly stated that Next.js 13.x, Next.js 14.x stable, Pages Router applications, and the Edge Runtime were not affected by the initial RCE issue. Fixed versions were listed as 15.0.5, 15.1.9, 15.2.6, 15.3.6, 15.4.8, 15.5.7, and 16.0.7, with separate fixed canaries for 15 and 16. (Siguiente.js)
Those version statements are worth slowing down on, because many organizations overreacted in one direction or another. Some assumed every Next.js application was equally exposed. Others assumed only the very newest App Router deployments were relevant. The truth was more precise. Initial RCE exposure depended on the combination of React Server Components behavior, App Router usage, and affected version lines. That precision matters for triage, but it should not be confused with “safe enough to ignore.” By December 11, Next.js also published a separate security update for related follow-on vulnerabilities, including DoS and source code exposure, and recommended broader upgrades across 14.x, 15.x, and 16.x lines. (Siguiente.js)
Sysdig’s technical summary broadened the ecosystem picture by identifying other frameworks and tools that implemented React Server Components semantics, including React Router in RSC mode, Waku, Parcel RSC, Vite RSC, and RedwoodSDK. That broader ecosystem perspective matters because real-world organizations do not run a clean one-framework portfolio. They run monorepos, internal portals, customer apps, admin dashboards, preview environments, and experimental canary services. Exposure can hide in the “non-primary” app that nobody mentally associates with a critical boundary. (Sysdig)
A practical exposure matrix for defenders looks like this:
| Stack pattern | Initial React2Shell RCE concern | Notas |
|---|---|---|
| React with affected RSC packages | Alta | Upstream issue lives here |
| Next.js App Router 15.x / 16.x | Alta | Officially affected for RCE |
| Next.js 14.3 canary track | Alta | Official advisory called out affected canaries |
| Next.js 13.x / 14.x stable / Pages Router | Lower for initial RCE | Not affected by the initial RCE advisory, but later follow-on issues still mattered |
| Monorepo with mixed React Native and Next.js | Indirectly high | React Native itself was not the vulnerable target, but monorepo dependency and patching friction still mattered |
| Alternative RSC-enabled frameworks | Case-by-case, potentially high | Verify implementation details and package versions |
The React Native issue discussion added a useful clarifier here: React Native apps themselves were not susceptible to the RCE, but many apps live in monorepos with Next.js or other RSC-powered apps, which complicates upgrades and dependency alignment. That is a very practical detail for real engineering organizations. (Siguiente.js)

Why security teams treated this as a “drop everything” event
The technical severity was obvious from the official scoring, but the operational severity came from the combination of four properties.
First, the issue was pre-authentication remote code execution. That immediately changes incident posture. When an attacker does not need valid credentials, the set of viable target paths becomes much larger. React’s own advisory and NVD both described the flaw in ways that support that conclusion, and multiple major vendors repeated the same interpretation. (Reaccione)
Second, the exploit path was highly reliable in at least some mainstream deployment models. Wiz said its testing showed near-100% reliability, and that a standard Next.js app created with crear-siguiente-app and built for production could be exploited without custom developer mistakes. That kind of statement is exactly what causes defenders to reclassify a CVE from “urgent patch” to “active crisis.” (wiz.io)
Third, detection ambiguity was high. PortSwigger warned that simply detecting the presence of React Server Components was not enough to determine exploitability and that not all public proofs of concept were reliable. GTIG noted that a variety of valid payload formats and techniques increased exploitation potential. Trend Micro later described an environment flooded with fake proofs of concept, scanners, and misconceptions. Together, those observations explain why teams struggled to separate panic from precision in the first week. (PortSwigger)
Fourth, adversaries moved fast. GTIG said it began observing widespread exploitation shortly after disclosure, across clusters ranging from opportunistic cybercrime actors to suspected espionage groups. Unit 42 covered the disclosure and the rapid interest that followed. Trend Micro said it observed the vulnerability exploited in the wild and tracked numerous PoCs with WAF bypasses and mass-scanning features. Once a bug reaches that stage, vulnerability management is no longer enough on its own. You are doing incident response, threat hunting, and sometimes compromise assessment at the same time. (Nube de Google)
Real-world exploitation, scanning, and post-exploitation behavior
By mid-December 2025, the conversation had moved far beyond “could this be exploited?” GTIG reported that shortly after public disclosure, it had begun observing widespread exploitation of CVE-2025-55182 across multiple threat clusters. It explicitly mentioned activity from opportunistic cybercrime actors as well as suspected espionage groups, including China-nexus clusters. It also said AWS reporting indicated that China-nexus groups Earth Lamia and Jackpot Panda were exploiting the vulnerability. (Nube de Google)
GTIG also described financially motivated exploitation. It observed incidents beginning on December 5 in which threat actors exploited the vulnerability and deployed XMRig for illicit cryptomining. That detail matters because it reinforces a familiar security pattern: when a vulnerability is both severe and easy to operationalize, opportunistic monetization often arrives quickly, long before defenders finish formal patch waves. (Nube de Google)
Trend Micro’s analysis added more detail on the exploit ecosystem. It said it had identified nearly 145 in-the-wild proofs of concept of varying quality, some with WAF bypasses and automated mass-scanning features. It also described malware campaigns using payloads such as Cobalt Strike beacons generated with Cross C2, Nezha, FRP, Sliver, and Secret-Hunter. Even if individual campaign details varied across telemetry providers, the larger lesson was consistent: React2Shell rapidly crossed the line from research topic to ecosystem-wide offensive commodity. (www.trendmicro.com)
Wiz reported that its sensors identified victims compromised starting on December 5, primarily targeting internet-facing Next.js applications and Kubernetes containers, and later observed post-exploitation pivoting toward cloud credential harvesting and cryptocurrency mining. That is a particularly important point for cloud-native defenders, because it frames React2Shell not just as a web application risk, but as an entry point into broader cloud control planes, service identities, and containerized workloads. (wiz.io)
PortSwigger’s response is also revealing for what it says about defender urgency. Within days, Burp Suite added out-of-the-box detection checks for React2Shell in Next.js-based applications, both for manual use and continuous scanning. That is not how vendors respond to ordinary medium-severity dependency advisories. It is how they respond when the internet starts probing for a newly exposed protocol-level RCE. (PortSwigger)
If you are reading this long after the first disclosure wave, the main implication is still the same: do not treat React2Shell as an old-news dependency issue just because the original announcement is no longer on the front page. Threat intelligence and product telemetry showed that the bug entered active operational use very quickly, and public scanning continued after disclosure. Dark Reading reported in February 2026 that threat actors were still using tools to scan for React2Shell exposure. (Lectura oscura)
The related CVEs that made patching more complicated
One of the most important mistakes a team could make in December 2025 was to treat React2Shell as a one-and-done patch event. React itself published a follow-up advisory on December 11 covering additional vulnerabilities in the same package family: source code exposure under CVE-2025-55183 and denial-of-service issues under CVE-2025-55184 and CVE-2025-67779. Later, the advisory was updated again in January 2026, and React noted that the original fix for one of the DoS issues had been incomplete. React’s updated guidance said versions 19.0.4, 19.1.5, and 19.2.4 were safe for those follow-on issues. (Reaccione)
That matters for two reasons. The first is obvious: if you stopped at the earliest RCE fix versions, you could still be carrying later-disclosed RSC issues. The second is more subtle: follow-on disclosures often reveal whether the original patch area was fragile. When researchers and maintainers continue discovering adjacent bugs after a critical framework issue, defenders should assume the relevant code paths deserve extra scrutiny even after patching. GTIG made this point in broader terms, noting that high-visibility critical vulnerabilities often trigger a period of increased scrutiny and further findings. (Nube de Google)
Next.js published corresponding downstream guidance on December 11. Its table listed affected and fixed versions for the DoS and source code exposure issues, including 14.2.35 for 14.x, 15.0.7 through 15.5.9 across 15.x lines, and 16.0.10 for 16.0.x. It also explicitly noted that Pages Router applications were not affected, but still recommended upgrading to patched versions. (Siguiente.js)
From an engineering management perspective, this created a classic challenge: the first emergency patch wave fixed the catastrophic bug, but the safest landing point was not the first landing point. Mature response teams recognized this quickly and split the work into at least three tracks: emergency containment, near-term version stabilization, and post-patch verification to ensure that the final target version covered both the original RCE and the adjacent RSC issues. (Reaccione)
Here is the safer way to think about the patch ladder:
| Problem family | Minimal initial fix | Safer later baseline |
|---|---|---|
| React2Shell RCE, CVE-2025-55182 | React 19.0.1 / 19.1.2 / 19.2.1 | React 19.0.4 / 19.1.5 / 19.2.4 for broader follow-on coverage |
| Next.js downstream RCE impact | 15.0.5 / 15.1.9 / 15.2.6 / 15.3.6 / 15.4.8 / 15.5.7 / 16.0.7 | 14.2.35, 15.0.7, 15.1.11, 15.2.8, 15.3.8, 15.4.10, 15.5.9, 16.0.10 for later follow-on fixes |
This is exactly the sort of nuance that gets lost when a team relies on a single security bulletin summary rather than reading the official advisory chain end to end. (Reaccione)
How to assess whether your environment is exposed
Exposure assessment should start with dependency truth, then move outward to framework behavior, then route reachability, then runtime evidence.
The first question is whether vulnerable React Server Components packages exist anywhere in the estate. React’s advisory named the package set explicitly, and GTIG repeated the same list. If these packages exist in the vulnerable version ranges, you have at least a dependency-level concern. That does not prove internet reachability, but it proves you should continue investigating. (Reaccione)
The second question is whether the affected application actually uses React Server Components semantics in production. For Next.js, the official boundary was App Router use on the affected version lines. Pages Router and Edge Runtime were not affected by the initial RCE advisory. If you have a large Next.js portfolio, this distinction is operationally valuable because it lets you prioritize App Router services first without pretending the rest of the fleet is equivalent. (Siguiente.js)
The third question is whether the target is externally reachable. Wiz reported that its victim observations primarily involved internet-facing Next.js applications and Kubernetes containers. GTIG emphasized that a single HTTP request could execute arbitrary code with the privileges of the web server process. In practical terms, an internal-only service with no route from an attacker is a very different risk from a public login page, even if both carry the same vulnerable package. (Nube de Google)
The fourth question is whether there is evidence of reconnaissance, scanning, or post-exploitation already present in logs and telemetry. Because public discussion and PoCs proliferated quickly, security teams should not assume that “we patched within a few days” means no adversary touched the target. Trend Micro, GTIG, and Wiz all documented early in-the-wild exploitation activity. (Nube de Google)
A practical dependency triage workflow can start with something as simple as this:
npm ls react-server-dom-webpack react-server-dom-parcel react-server-dom-turbopack next react
pnpm why react-server-dom-webpack
pnpm why react-server-dom-parcel
pnpm why react-server-dom-turbopack
pnpm why next
yarn why react-server-dom-webpack
yarn why react-server-dom-parcel
yarn why react-server-dom-turbopack
yarn why next
These commands do not prove exploitability, but they tell you whether the vulnerable packages are present and why they are present. For monorepos, that “why” is often more important than the package itself because it reveals which workspace, app, or transitive dependency introduced the exposure. The official package names and version ranges come directly from React and GTIG guidance. (Reaccione)
You can also use a small Node script to fail CI when known-vulnerable package ranges appear in a lockfile-derived inventory:
const vulnerable = {
"react-server-dom-webpack": new Set(["19.0.0", "19.1.0", "19.1.1", "19.2.0"]),
"react-server-dom-parcel": new Set(["19.0.0", "19.1.0", "19.1.1", "19.2.0"]),
"react-server-dom-turbopack": new Set(["19.0.0", "19.1.0", "19.1.1", "19.2.0"]),
};
const deps = require("./package-lock.json").packages || {};
let bad = [];
for (const [path, meta] of Object.entries(deps)) {
if (!meta || !meta.name || !meta.version) continue;
if (vulnerable[meta.name] && vulnerable[meta.name].has(meta.version)) {
bad.push({ path, name: meta.name, version: meta.version });
}
}
if (bad.length) {
console.error("React2Shell-related vulnerable packages found:");
for (const item of bad) {
console.error(`- ${item.name}@${item.version} at ${item.path}`);
}
process.exit(1);
} else {
console.log("No known React2Shell-vulnerable RSC package versions found.");
}
That script intentionally stays on the defensive side. It checks for official package names and version lines documented by React. It does not try to infer exploitability from app structure, which would be a different step. (Reaccione)

How to verify reachability without turning testing into unsafe exploitation
A mature validation approach for React2Shell should be careful, scoped, and instrumented. The goal is to determine whether an application exposes the affected protocol surface and whether patches truly closed the relevant paths, not to reproduce weaponized behavior against production systems.
PortSwigger’s guidance is useful here because it reflects how professional defenders adapted quickly. Burp Suite added built-in checks for React2Shell in Next.js-based applications, specifically to help organizations investigate and triage suspected targets without requiring custom extensions or scripts. That is valuable because it standardizes an initial coverage layer and reduces dependence on random public PoCs of uncertain quality. (PortSwigger)
Sysdig’s perspective is also worth noting. Its threat research team developed Falco detection content aimed at runtime visibility for React2Shell-related behavior. This reflects a practical reality: by the time a critical RCE is under active scanning, pure static validation is not enough. You want dependency truth, app-layer reachability checks, and runtime telemetry that can catch suspicious process execution, network pivots, or container escape attempts if an exploitation attempt gets through. (Sysdig)
A safe internal validation flow often looks like this:
| Escenario | Objetivo | Safe output |
|---|---|---|
| Dependency inventory | Confirm affected packages and versions | Package and workspace list |
| Architecture review | Confirm App Router, RSC, Server Functions usage | Exposure classification |
| Controlled DAST | Validate route-level signs of vulnerable behavior | Reachability evidence, not exploit code |
| Runtime monitoring | Watch for unusual child processes, shells, network beacons | Detection events and timelines |
| Post-patch regression | Confirm fixes changed observed behavior | Patch verification report |
For teams that want a lightweight CI/CD control, this shell gate is a reasonable starting point:
set -e
echo "[*] Checking for vulnerable React2Shell package versions"
npm ls react-server-dom-webpack react-server-dom-parcel react-server-dom-turbopack next react || true
if npm ls react-server-dom-webpack@19.0.0 react-server-dom-webpack@19.1.0 react-server-dom-webpack@19.1.1 react-server-dom-webpack@19.2.0 >/dev/null 2>&1; then
echo "[!] Vulnerable react-server-dom-webpack version found"
exit 1
fi
if npm ls react-server-dom-parcel@19.0.0 react-server-dom-parcel@19.1.0 react-server-dom-parcel@19.1.1 react-server-dom-parcel@19.2.0 >/dev/null 2>&1; then
echo "[!] Vulnerable react-server-dom-parcel version found"
exit 1
fi
if npm ls react-server-dom-turbopack@19.0.0 react-server-dom-turbopack@19.1.0 react-server-dom-turbopack@19.1.1 react-server-dom-turbopack@19.2.0 >/dev/null 2>&1; then
echo "[!] Vulnerable react-server-dom-turbopack version found"
exit 1
fi
echo "[*] No officially listed vulnerable RSC package versions detected"
Again, this is not a full detector. It is a guardrail. The point is to make the dangerous package state fail loudly during build and deployment. (Reaccione)
Incident response, not just patch management
Once active exploitation enters the picture, patching is only one part of the response. GTIG, Wiz, and Trend Micro all reported in-the-wild exploitation. GTIG described cryptomining deployment and underground discussion around tools and PoCs. Wiz observed post-exploitation pivoting toward cloud credential harvesting and cryptocurrency mining. Trend Micro described malware campaigns and a large ecosystem of PoCs and scanners. If your environment was internet-facing and exposed during the early disclosure window, you should assume compromise assessment is part of the job. (Nube de Google)
A practical response sequence looks like this:
| Prioridad | Acción | Por qué es importante |
|---|---|---|
| 1 | Patch affected versions immediately | Removes known RCE path |
| 2 | Rebuild and redeploy, do not hot-fix only | Ensures runtime matches dependency state |
| 3 | Rotate secrets and environment variables | Next.js explicitly recommended secret rotation after patching and redeployment |
| 4 | Review logs around disclosure and patch window | Early exploitation happened quickly |
| 5 | Hunt for anomalous child processes and outbound connections | Reported post-exploitation included miners and follow-on payloads |
| 6 | Review cloud credentials and service identities | Wiz observed cloud credential harvesting pivots |
| 7 | Re-run verification after moving to later safe baselines | Follow-on CVEs changed the safest target version |
That third step deserves special emphasis. Next.js explicitly recommended rotating all application secrets after patching and redeploying. That advice is easy to skip when teams mentally categorize a flaw as a framework bug rather than a system compromise vector. But a pre-auth server-side RCE means your secrets should be treated as potentially exposed if the target was reachable before patching. (Siguiente.js)
At the log level, focus on anomalies that align with public reporting rather than obsessing over one exact IOC. Because GTIG and Trend Micro both described a variety of payloads and post-exploitation behaviors, brittle signature-based assumptions are risky. Look for unusual request patterns to RSC-related endpoints, unexplained server process spawning, suspicious shell scripts, outbound downloads from application containers, unexpected miner behavior, FRP or tunneling artifacts, and changes in runtime process trees. (Nube de Google)
Patch guidance that does not stop too early
The minimum official React fix for the original RCE was straightforward: move to 19.0.1, 19.1.2, or 19.2.1 depending on your line. The minimum official Next.js fix for the initial advisory was similarly straightforward: move to the patched releases in your line, such as 15.0.5, 15.1.9, and so on. (Reaccione)
But the safer recommendation now is to aim higher than the original minimum if you are still remediating old environments or cleaning up overlooked services. React later said that versions 19.0.4, 19.1.5, and 19.2.4 were safe after additional RSC-related findings, and Next.js later published patched releases such as 14.2.35, 15.0.7, 15.1.11, 15.2.8, 15.3.8, 15.4.10, 15.5.9, and 16.0.10 for its related downstream issues. (Reaccione)
For many teams, the right answer is not “patch to the minimum version that fixed the first CVE.” The right answer is “patch to the stable version in your branch that closes the RCE and the follow-on RSC issues, then verify behavior.” That is especially true if you are building a standardized enterprise baseline rather than firefighting one app. (Reaccione)
Here is a safe upgrade cheat sheet:
# React initial RCE fixes
npm install react-server-dom-webpack@19.0.1
npm install react-server-dom-webpack@19.1.2
npm install react-server-dom-webpack@19.2.1
# React safer later baselines after follow-on fixes
npm install react-server-dom-webpack@19.0.4
npm install react-server-dom-webpack@19.1.5
npm install react-server-dom-webpack@19.2.4
# Next.js initial RCE fixes
npm install next@15.0.5
npm install next@15.1.9
npm install next@15.2.6
npm install next@15.3.6
npm install next@15.4.8
npm install next@15.5.7
npm install next@16.0.7
# Next.js later fixed releases for follow-on RSC issues
npm install next@14.2.35
npm install next@15.0.7
npm install next@15.1.11
npm install next@15.2.8
npm install next@15.3.8
npm install next@15.4.10
npm install next@15.5.9
npm install next@16.0.10
Next.js also released an interactive helper, npx fix-react2shell-next, specifically to check versions and perform deterministic version bumps per recommended lines. That is useful operationally because it reduces the chances of version-selection mistakes during emergency remediation. (Siguiente.js)
Why React2Shell changed how defenders think about “frontend” frameworks
The deepest lesson of React2Shell is not “always patch React fast,” although that is obviously true. The deeper lesson is architectural. Modern web stacks are no longer neatly split into frontend and backend concerns. When frameworks expose server-side rendering, server-side actions, structured transport protocols, and increasingly stateful execution semantics, the old intuition that “frontend risk means XSS and supply-chain risk” becomes dangerously incomplete. React2Shell was a server-execution vulnerability that emerged from a UI framework’s server abstraction layer. (Unidad 42)
That matters because it changes how you model attack surface. A security review that only looks for classical input validation errors in route handlers will miss protocol flaws in framework internals. A dependency scan that only counts CVEs without understanding which routes and runtime features are active will overwhelm teams with noise. A runtime detector that only watches known bad binaries may miss the early, low-noise staging behavior of a framework exploit chain. React2Shell is a case study in why real coverage requires joining dependency intelligence, architecture awareness, dynamic validation, and runtime monitoring. (PortSwigger)
This is also why the comparison to older ecosystem-defining CVEs kept appearing. PortSwigger wrote that many expected a trajectory similar to Log4j, including rapid weaponization. Penligent’s own coverage also drew the comparison for practitioners, not because the root causes were identical, but because the defender experience rhymed: high severity, public attention, ecosystem-wide exposure mapping, scanner churn, fast offensive adoption, and a long tail of hidden vulnerable instances. (PortSwigger)

What a practical security program should do differently after React2Shell
A mature program should take at least five durable lessons from this event.
First, treat framework protocol surfaces as first-class attack surfaces. If your stack uses App Router, RSC, Server Functions, or similar abstractions, those features belong in your threat model. They are not implementation trivia. React’s own advisory made clear that an app could be vulnerable even without implementing explicit Server Function endpoints, as long as it supported React Server Components. (Reaccione)
Second, maintain a version-aware architecture inventory, not just an SBOM. The official Next.js guidance distinguished affected App Router versions from unaffected Pages Router and Edge Runtime cases for the initial RCE. That distinction is critical. A security program that cannot answer “which applications actually run affected App Router versions” is operating half blind during a framework crisis. (Siguiente.js)
Third, build patch programs that understand advisory chains, not just single CVEs. React’s later disclosure of CVE-2025-55183, CVE-2025-55184, and CVE-2025-67779 changed what “fully remediated” meant. The team that reads only the first bulletin may stop too early. (Reaccione)
Fourth, make safe validation part of patch closure. PortSwigger’s rapid scan-check support and the emergence of dedicated detectors reflected a reality many teams learned the hard way: installing a patched dependency is not enough if you cannot verify that the live deployment, the route configuration, and the reachable runtime behavior all match the intended state. (PortSwigger)
Fifth, fold runtime behavior into appsec for cloud-native web apps. Wiz observed cloud credential harvesting pivots. GTIG and Trend Micro observed miners, scripts, and malware payloads. Once a framework-level RCE becomes active, runtime security is not a separate discipline; it is part of web application defense. (wiz.io)
Where Penligent fits in a real React2Shell workflow
React2Shell is a good example of why teams increasingly need more than a static list of vulnerable packages or a generic DAST scan. The hard part is often joining four separate questions into one operational answer: which applications carry the affected dependency, which of those actually expose the dangerous runtime feature set, which are internet-reachable or otherwise attacker-reachable, and which still behave unsafely after patching or version drift. That is exactly the kind of validation problem where an AI-driven automated penetration testing platform can be useful, especially when the bug family cuts across dependency graphs, framework semantics, and deployment exposure at the same time. (Reaccione)
Used well, a platform like Penligent is not a replacement for vendor guidance or official patching. It is a force multiplier for exposure discovery, dynamic validation, and regression testing. In a React2Shell-style event, that means mapping public-facing React and Next.js assets, identifying likely App Router or RSC-enabled surfaces, checking version and dependency signals, validating whether patch waves actually closed the reachable path, and helping security teams prioritize the small number of services that are both vulnerable and exposed instead of drowning in dependency noise. That is a natural fit for modern automated offensive validation because framework logic flaws rarely stay inside one clean testing bucket. (Siguiente.js)
A clean checklist for security engineers
If you want one concise operational checklist to carry away from this article, use this:
| Question | Qué verificar |
|---|---|
| Do we have vulnerable packages? | Consulte react-server-dom-webpack, react-server-dom-parcel, react-server-dom-turbopack in official vulnerable ranges |
| Do we run an affected framework mode? | Confirm App Router / RSC / Server Functions exposure |
| Is the target reachable? | Identify internet-facing or attacker-reachable routes |
| Did we patch to the right baseline? | Do not stop at the earliest RCE-only fix if later RSC issues apply |
| Did we rotate secrets? | Next.js explicitly recommended it after patching and redeploying |
| Did we hunt for compromise? | Review logs, child process activity, outbound beacons, miners, and cloud pivots |
| Did we verify the live deployment? | Re-test behavior after rollout, not just package manifests |
That checklist looks simple on paper, but React2Shell showed how often organizations fail on step boundaries rather than on pure technical knowledge. A team may know the CVE, yet not know which apps use App Router. It may patch the repo but not redeploy the environment. It may redeploy but forget to rotate secrets. It may rotate secrets but skip runtime hunting because “we patched within a day.” Severe incidents thrive in those gaps. (Siguiente.js)
The bigger meaning of React2Shell
React2Shell should be remembered as more than an ugly week for React and Next.js maintainers. It should be remembered as a warning about how modern web platforms evolve. Every time a framework collapses more of the backend into a cleaner developer abstraction, it also creates new parser boundaries, new protocol assumptions, and new execution paths that security teams must understand on their own terms. React Server Components made application development more powerful. They also made framework internals more security-critical. (Unidad 42)
That is why the most useful mental model is not “React got an RCE.” The better model is “the boundary between UI and server execution became part of the attack surface, and a protocol deserialization flaw weaponized that boundary.” Once you see the incident that way, the defender response becomes clearer. You do not just patch packages. You inventory framework capabilities, map reachable exposure, validate behavior safely, monitor runtime outcomes, and upgrade your security model for the next abstraction layer before the next React2Shell arrives. (NVD)
React2Shell is already part of web security history because it forced that realization into the open. A single crafted request was enough to turn a rendering protocol into a remote execution boundary. Security teams that learned the lesson will be faster not only on the next React or Next.js incident, but on every future framework event that tries to hide a backend risk inside a frontend abstraction. (Nube de Google)
Lecturas complementarias
React, Critical Security Vulnerability in React Server Components (Reaccione)
Next.js, Security Advisory for CVE-2025-66478 (Siguiente.js)
CVE.org, CVE-2025-66478 rejected as duplicate (CVE)
NVD, CVE-2025-55182 detail (NVD)
Google Threat Intelligence Group, Multiple Threat Actors Exploit React2Shell (Nube de Google)
Palo Alto Networks Unit 42, Exploitation of Critical Vulnerability in React Server Components (Unidad 42)
Microsoft Security Blog, Defending against CVE-2025-55182 (Microsoft)
Wiz, React2Shell Deep Dive (wiz.io)
Wiz, React2Shell, Everything You Need to Know (wiz.io)
PortSwigger, How to detect React2Shell with Burp Suite (PortSwigger)
Trend Micro, CVE-2025-55182 Analysis, PoC Chaos, and In-the-Wild Exploitation (www.trendmicro.com)
Penligent, React2Shell CVE 2025 55182, why one request became a server-side execution boundary (penligent.ai)
Penligent, Surviving the React2Shell Fallout, Unpacking CVE-2025-55182 for Security Engineers (penligent.ai)


