Why this partnership matters now
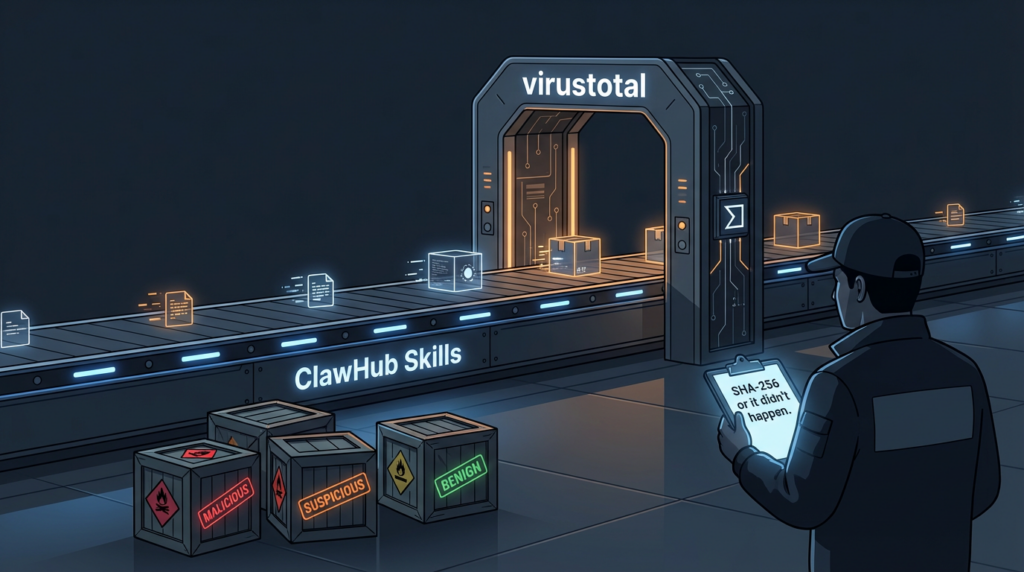
On February 7, 2026, OpenClaw announced a partnership with VirusTotal to scan every skill published to ClawHub, its skill marketplace. The short version is straightforward: a skill is packaged, hashed (SHA-256), and checked against VirusTotal; if there’s no prior record, the bundle is uploaded for scanning and analysis, including VirusTotal’s Code Insight feature. Skills judged benign can be approved automatically; suspicious skills can be labeled with warnings; malicious skills can be blocked. The intent is to add an automated layer of defense against a rapidly growing “agent skill” supply chain that has already been abused by attackers.
The long version is what defenders care about: ClawHub is not merely a code-sharing site. It is a distribution channel for runnable automation that is designed to operate with the user’s permissions, identities, tokens, filesystem access, and network reach. In that environment, “a bad plugin” is not an inconvenience—it’s an execution boundary failure. The partnership is OpenClaw’s attempt to turn “skill installation” into something closer to a governed software artifact pipeline with repeatable scanning, visible verdicts, and continuous monitoring.
This article unpacks what OpenClaw’s integration does, why it is strategically sound, where it can still fail, and how you can implement similar controls in your own environment—whether you run OpenClaw internally, you maintain an agent toolchain, or you’re defending endpoints that now contain agent runtimes and their extensions.
The high-intent keywords that keep appearing in research and headlines
The best way to infer “what people are really searching for” without access to proprietary click-through datasets is to read what security researchers publish, what incident responders cite, and what the press repeats in the first 20 lines of coverage. Across February 2026 coverage and research, the recurring terms that map to defensive intent are:
- virustotal (explicitly tied to scanning and reputation checks)
- VirusTotal Code Insight (used as a differentiator over signature-only scanning)
- malicious skills / toxic skills (marketplace abuse framing)
- ClawHub malware / OpenClaw skill malware (distribution channel language)
- AI agent security / agentic security boundary (the “new class” label)
- prompt injection / indirect prompt injection (agent hijacking)
- supply chain attack (the correct category for a marketplace that distributes code artifacts)
- exposed secrets / tokens / API keys (what gets stolen first)
Snyk’s “ToxicSkills” write-up is a useful reference point because it frames the ecosystem as an auditable corpus and quantifies classes of issues (malware distribution, prompt injection, secrets exposure, dynamic remote fetch-and-execute patterns). VirusTotal’s own February 2026 change and blog notes also explicitly call out OpenClaw skill packages and “supply-chain threat delivery.”
What OpenClaw actually built: an artifact gate, not a vibe
When vendors announce “we scan stuff,” they often mean “we run a static scan on repositories” or “we check for known bad signatures sometimes.” OpenClaw’s announced design is closer to a proper artifact gate, because it relies on deterministic packaging and content-addressable identity.
A un alto nivel:
- Every uploaded skill is packaged into a bundle that represents the exact artifact users will download.
- The system computes a SHA-256 hash for the bundle.
- The hash is checked against VirusTotal’s existing corpus.
- If there is no match, the bundle is uploaded to VirusTotal for scanning and deeper analysis, including Code Insight.
- The VirusTotal report is surfaced on the skill page (and across versions), allowing users and maintainers to see what changed and why a verdict was assigned.
- The ecosystem performs ongoing rescans of active skills, so that new intelligence can retroactively change a verdict.
This matters because “repository state” and “shipped artifact” are not the same. If you want reproducibility, auditing, and rollback, you must pin decisions to the immutable artifact.
Why VirusTotal
VirusTotal is not “an antivirus.” It’s a threat-intelligence aggregation platform with file reputation, multi-engine signals, behavioral artifacts, pivoting capabilities, and APIs that let you build automated workflows. For a marketplace, the essential value is that attackers reuse infrastructure and code families. Even when the bundle changes, its related indicators often don’t: domains, IPs, droppers, strings, similar sample relationships, packers, or the same actor’s tooling.
In February 2026, VirusTotal explicitly positioned OpenClaw skills as a new supply-chain delivery channel and noted that Code Insight support was extended to OpenClaw skill packages “looking past a package’s claimed purpose.” That phrasing matters: the attacker’s first move is to claim innocence via documentation and naming, while the artifact behavior says otherwise.
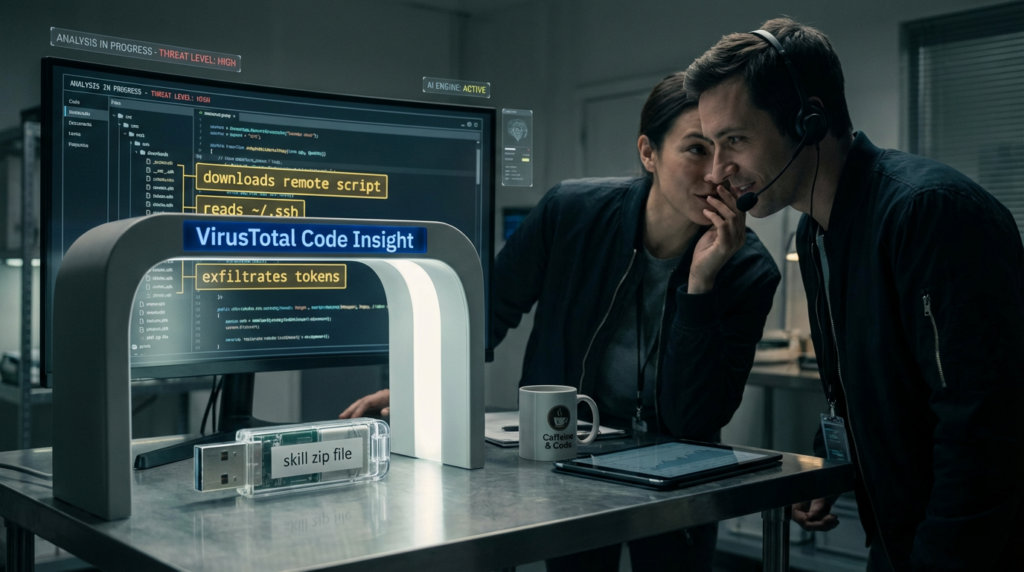
What Code Insight adds beyond signatures
VirusTotal introduced Code Insight in 2023 as an AI-assisted feature that produces natural-language summaries of code with security analyst intent: it aims to explain what a script or snippet is doing, which can help triage suspicious logic that may not be matched by classical signatures. VirusTotal later published examples where Code Insight surfaced behaviors that evaded traditional detection engines.
For defenders, Code Insight is valuable for two reasons:
- It compresses time-to-understanding. You can triage faster when the summary correctly identifies “download and execute,” “credential collection,” “persistence,” or “exfiltration behavior” in the code path.
- It makes scanning outcomes legible to non-specialists. Marketplace moderation is often done under time pressure; narrative summaries help align decisions.
Why agent skills are riskier than classic plugins
Classic package supply-chain attacks are already painful: typosquatting, dependency confusion, maintainer compromise, malicious updates, build pipeline compromise, and upstream backdoors. Agent skills add two new accelerants:
- Privilege concentration. Skills often run inside a runtime that already has broad permissions and long-lived credentials. That collapses the distance between code execution and business impact.
- Instruction-driven autonomy. Even benign code can become dangerous when an agent is coerced into misusing tools. This is where prompt injection and tool hijacking show up: the model can be driven to take actions it should not, because it struggles to separate trusted instructions from untrusted data.
OWASP’s GenAI project continues to emphasize prompt injection as a top risk category, and the “supply chain” category explicitly includes third-party components in LLM systems. VirusTotal scanning reduces the probability of installing a known-bad artifact; it does not, by itself, solve instruction-level hijacking.
A quick taxonomy of malicious-skill behavior
Most malicious skills are not sophisticated at first. They are optimized for scale and plausible deniability. In observed campaigns reported by vendors and media, common patterns include:
- “README as installer.” The skill documentation asks users to run shell commands that fetch remote scripts (curl | bash patterns), sometimes heavily obfuscated.
- “Dependency as payload.” The skill declares a dependency that is controlled by the attacker (typosquatting or newly created packages), which executes code during install.
- “Configuration harvesting.” The skill searches local paths for browser profiles, wallet data, API tokens, SSH keys, or .env files.
- “Toolchain persistence.” The skill modifies agent memory or configuration so that malicious instructions persist across sessions.
- “Exfiltration via legitimate APIs.” The skill uses outbound HTTP(S) to send data to attacker-controlled servers, often disguised as telemetry.
Trend Micro documented malicious OpenClaw skills distributing an Atomic macOS stealer variant, showing how quickly the ecosystem became a channel for commodity infostealers.
The CVEs you can’t ignore in an OpenClaw environment
CVE-2026-25253: token leakage via automatic WebSocket connection
CVE-2026-25253 is recorded by NVD as an issue in OpenClaw (also known as clawdbot/Moltbot) before 2026.1.29: it obtains a gatewayUrl value from a query string and automatically makes a WebSocket connection without prompting, sending a token value. NVD lists a high-impact CVSS v3.1 vector (AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H).
This matters because a token is often the shortest path to account takeover or session hijacking in agent ecosystems. If a malicious link can coerce a runtime to connect out and disclose tokens, an attacker can bridge to further actions without having to compromise a skill first.
CVE-2024-3094: the xz backdoor as the modern supply-chain baseline
CVE-2024-3094 (xz / liblzma) is not an OpenClaw bug, but it is the best modern demonstration of how upstream compromise can silently travel through build processes. NVD describes malicious code in upstream tarballs starting with 5.6.0, using obfuscated build steps to extract a prebuilt object file and modify functions in liblzma—creating a modified library that can intercept and modify data interactions.
The reason it belongs here is conceptual: if you operate an ecosystem that distributes runnable artifacts, you are an upstream. The same logic applies: you need artifact identity, verification, scanning, monitoring, and the ability to revoke.
CVE-2021-44228 (Log4Shell): why defenders keep using it as the reference point
Log4Shell remains a durable reference because it showed how quickly an RCE-class defect in a widely deployed component becomes industrialized. For agent systems, the analogy is not that skills are logging libraries. It’s that highly distributed execution surfaces, when paired with privilege and automation, produce rapid exploitation at scale.
Build your own skill gate in CI
You do not need to run a marketplace to benefit from the “artifact gate” pattern. If your org distributes internal skills, plugins, or agent tools, you can implement a comparable workflow in CI/CD and in your internal registry.
Two constraints:
- VirusTotal’s public API is rate-limited and not designed for production commercial use. For enterprise workflows, plan for an appropriate tier and quotas.
- Scanning is one layer. You still need least-privilege, isolation, and auditing.
Step 1: deterministic packaging + SHA-256
# Python: deterministic zip packaging + SHA-256 hashing for a skill artifact
import hashlib, os, zipfile
def zip_deterministic(src_dir, out_path):
files = []
for root, _, filenames in os.walk(src_dir):
for fn in filenames:
full = os.path.join(root, fn)
rel = os.path.relpath(full, src_dir)
files.append((rel, full))
files.sort(key=lambda x: x[0])
with zipfile.ZipFile(out_path, "w", compression=zipfile.ZIP_DEFLATED) as z:
for rel, full in files:
info = zipfile.ZipInfo(rel)
info.date_time = (1980, 1, 1, 0, 0, 0) # fixed timestamp
with open(full, "rb") as f:
z.writestr(info, f.read())
def sha256(path):
h = hashlib.sha256()
with open(path, "rb") as f:
for chunk in iter(lambda: f.read(1024*1024), b""):
h.update(chunk)
return h.hexdigest()
zip_deterministic("skills/twitter-summarize", "dist/twitter-summarize.skill.zip")
print("sha256:", sha256("dist/twitter-summarize.skill.zip"))
Step 2: query VirusTotal by hash, then upload if unknown
# Bash: VirusTotal v3 API examples (requires appropriate API access)
HASH="YOUR_SHA256"
curl -sS -H "x-apikey: $VT_API_KEY" \\
"<https://www.virustotal.com/api/v3/files/$HASH>" | jq
# Upload if not found
curl -sS -H "x-apikey: $VT_API_KEY" \\
-F "file=@dist/twitter-summarize.skill.zip" \\
"<https://www.virustotal.com/api/v3/files>" | jq
Step 3: turn scan stats into policy decisions
A simple, conservative policy that mirrors what marketplaces often do:
- Block if malicious detections > 0, or if the report shows explicit credential theft, downloader behavior, or persistence modifications.
- Warn and require approval if suspicious detections > 0, or if Code Insight indicates risky behavior and the owner is not verified.
- Allow if malicious == 0 and suspicious == 0, and the skill’s declared capabilities align with least privilege.
This is not about perfection. It is about repeatability and auditability. Once you have an explicit policy, you can improve it safely over time.

A policy table you can adapt
| Señal | Ejemplo | Riesgo | Default action | Notas |
|---|---|---|---|---|
| VT stats: malicious > 0 | Any engine flags malicious | Alta | Block | Treat as unsafe until reviewed |
| VT stats: suspicious > 0 | Heuristics / suspicious verdict | Medio-Alto | Warn + approval | Escalate if skill has shell or FS access |
| Downloader pattern | curl/wget + exec, remote script | Alta | Block | Often commodity infostealer stage 0 |
| Secret access | Reads ~/.ssh, browser profiles, .env | Alta | Warn/Block | Depends on legitimate need and scoping |
| Owner unverified | New maintainer, no history | Variable | Warn + approval | Require signing or internal mirror |
What VirusTotal scanning will not catch
A scanning gate is necessary, but it is not sufficient. There are three broad failure modes you should assume remain:
- Prompt injection and tool misuse. A benign skill can be driven to do unsafe things if the agent’s instruction boundary is weak. OWASP continues to treat prompt injection as a top risk.
- Low-signal, new malware. Attackers can ship small, staged loaders that pull most logic after install. If the initial artifact is low-signal and the infrastructure is fresh, reputational detection may lag.
- Abuse of legitimate capabilities. A skill that genuinely needs network access can still exfiltrate data if its permissions are too broad and auditing is weak.
This is why isolation, least privilege, and logging are non-negotiable in agent runtimes.
Operational controls that actually reduce blast radius
Run agent runtimes like untrusted code execution
Multiple security advisories and enterprise risk discussions have converged on the same point: do not run agent runtimes with broad privileges on standard workstations. Run them in isolated environments (VMs/containers), with scoped credentials and monitoring. Even when malware is not present, the combination of persistence, automation, and third-party code creates a risk profile that classical endpoint protections may not fully cover.
Control tool permissions explicitly
A practical way to design permissions for skills is to treat them like cloud IAM roles. A skill should request capabilities; a human or policy engine should grant only what is necessary; and all privileged actions should be logged. Examples of risky permissions that should trigger extra review:
- unrestricted shell execution
- unrestricted filesystem reads
- ability to write persistent config/memory
- unrestricted outbound network access
- access to identity tokens or password stores
If you are building internal skills, enforce “capability manifests” and review diffs like you review Terraform IAM changes.
Add continuous monitoring and rescanning
OpenClaw’s announced daily rescanning is a key design choice: threat intel changes. It is rational to retroactively reclassify artifacts when new YARA rules, sandboxes, or intel arrive. VirusTotal’s February 9, 2026 changelog highlights ongoing detection updates and explicit coverage for OpenClaw skill packages, which is a reminder that the ecosystem is being actively tracked.
A short, practical incident-response playbook for malicious skills
Triage signals
When you suspect a malicious skill:
- Capture the installed artifact as-is (zip, directory, or cache bundle).
- Compute SHA-256 and query VirusTotal.
- Pivot from any discovered IOCs (domains, URLs, IPs, hashes) using VirusTotal Graph, relations, and search features.
- Validate what ran: shell history, process tree, outbound connections, and filesystem access.
- Rotate credentials that the runtime could access (tokens, API keys, OAuth approvals).
A minimal YARA/Livehunt starter rule
import "vt"
rule suspicious_archive_with_downloader_strings
{
strings:
$curl = "curl " ascii nocase
$wget = "wget " ascii nocase
$bash = "| bash" ascii nocase
$sh = "| sh" ascii nocase
condition:
(vt.metadata.file_type == vt.FileType.ZIP or vt.metadata.file_type == vt.FileType.GZIP) and
2 of ($curl, $wget, $bash, $sh)
}
Skill scanning answers one question: “Is this artifact likely malicious?” Security programs still need two more answers:
- Are we exposed or misconfigured in ways that make the runtime or its interfaces reachable?
- After patching or hardening, can we prove—using evidence—that we closed the path, not just “feel” we did?
That is where an AI-driven penetration testing workflow can complement marketplace defenses: you can continuously test the real attack surface, validate remediation, and produce artifact-backed reports. Penligent’s OpenClaw security research is focused on execution boundaries, indirect injection patterns, and the difference between “assurance” and “proof.”
Appendix
https://openclaw.ai/blog/virustotal-partnership https://thehackernews.com/2026/02/openclaw-integrates-virustotal-scanning.html https://www.csoonline.com/article/4129393/openclaw-integrates-virustotal-malware-scanning-as-security-firms-flag-enterprise-risks.html https://snyk.io/blog/toxicskills-malicious-ai-agent-skills-clawhub/ https://gtidocs.virustotal.com/changelog/february-9th-2026-code-insight-openclaw-skill-packages-private-scanning-livehunt-rules-and-more https://blog.virustotal.com/2026/02/from-automation-to-infection-how.html https://blog.virustotal.com/2023/04/introducing-virustotal-code-insight.html https://blog.virustotal.com/2024/01/uncovering-hidden-threats-with.html https://cloud.google.com/blog/products/identity-security/rsa-google-cloud-security-ai-workbench-generative-ai https://genai.owasp.org/llmrisk/llm01-prompt-injection/ https://owasp.org/www-project-top-10-for-large-language-model-applications/ https://www.trendmicro.com/en_us/research/26/b/openclaw-skills-used-to-distribute-atomic-macos-stealer.html https://nvd.nist.gov/vuln/detail/CVE-2026-25253 https://github.com/advisories/GHSA-r2c6-8jc8-g32w https://nvd.nist.gov/vuln/detail/cve-2024-3094 https://www.cisa.gov/news-events/alerts/2024/03/29/reported-supply-chain-compromise-affecting-xz-utils-data-compression-library-cve-2024-3094 https://nvd.nist.gov/vuln/detail/cve-2021-44228 https://www.penligent.ai/hackinglabs/virustotal-in-incident-response-how-to-identify-malware-fast-and-pivot-without-leaking-data/ https://www.penligent.ai/hackinglabs/es/the-openclaw-prompt-injection-problem-persistence-tool-hijack-and-the-security-boundary-that-doesnt-exist/ https://www.penligent.ai/hackinglabs/multiple-hacking-groups-exploit-openclaw-instances-to-steal-api-keys-and-deploy-malware/ https://penligent.ai/