CVE-2026-23918 is a narrow but serious Apache HTTP Server issue: a double-free in HTTP/2 handling, tied to an early stream reset path, affecting Apache HTTP Server 2.4.66 and fixed in Apache HTTP Server 2.4.67. Apache’s own advisory calls it “http2: double free and possible RCE on early reset,” marks the severity as important, credits Bartlomiej Dmitruk of striga.ai and Stanislaw Strzalkowski of isec.pl, and says the issue was reported to the Apache security team on December 10, 2025, fixed in source the next day, and released in 2.4.67 on May 4, 2026. (Apache HTTP Server)
The risk should not be flattened into a slogan. This is not “every Apache server is instantly rootable.” The confirmed affected upstream version is Apache HTTP Server 2.4.66, the relevant component is HTTP/2 handling through mod_http2, and the official fix is to upgrade to 2.4.67 or a vendor package that carries the fix. NVD repeats the Apache description, maps the weakness to CWE-415 Double Free, and shows a CISA-ADP CVSS 3.1 score of 8.8 High while also noting that NVD’s own enrichment had not yet provided a separate CVSS assessment at the time of review. (NVD)
The most practical operational risk is worker process instability and denial of service. Public technical reporting also describes a possible remote code execution path, but that path is more environment-dependent than the crash scenario. That distinction matters for defenders, red teamers, and bug bounty hunters. A safe response proves exposure, patches quickly, verifies the running process, hunts for crash signals, and avoids destructive frame-level testing against production.
Ce qui est confirmé
The facts that matter most are compact enough to put in one table.
| Champ d'application | Current verified state |
|---|---|
| CVE | CVE-2026-23918 |
| Produit | Apache HTTP Server |
| Upstream affected version | Apache HTTP Server 2.4.66 |
| Upstream fixed version | Apache HTTP Server 2.4.67 |
| Composant | HTTP/2 handling, mod_http2 |
| Official Apache impact wording | Double free and possible RCE on early reset |
| Weakness class | CWE-415 Double Free |
| Apache severity label | Important |
| CVSS signal | CISA-ADP CVSS 3.1 score shown by NVD is 8.8 High |
| Clearest public impact path | Worker crash and denial of service |
| More constrained impact path | Possible RCE under environment-specific memory conditions |
| First remediation | Upgrade to Apache HTTP Server 2.4.67 or a vendor-patched package |
| Safe validation | Version, module, protocol, MPM, package, process, and log verification |
| Unsafe validation | Running crash or RCE PoCs against production or third-party systems |
Two details in that table deserve more attention than the headline usually gets.
First, the affected upstream version is specific. Apache says the issue affects 2.4.66. Ubuntu’s CVE page makes the same point in a more nuanced way: its security note says earlier releases were marked not affected because, although the core issue existed earlier, the double-free outcome depended on a mod_http2 allocator change that went into httpd 2.4.66. (Ubuntu)
Second, scoring is not perfectly uniform across sources. NVD displays the CISA-ADP CVSS 3.1 score as 8.8 High with PR:L, while SUSE lists its own CVSS 3.1 score as 8.1 with PR:N et AC:H, and also shows a SUSE CVSS 4.0 score of 9.2. That is not unusual for fresh vulnerabilities. Vendors often adjust scores based on their packaging, platform assumptions, exploitability view, and affected product matrix. (NVD)
For security teams, the practical conclusion is simple: do not wait for scoring debates before patching an internet-facing Apache 2.4.66 deployment with HTTP/2 reachable. The version, component, and fix are already clear.
Why an HTTP/2 early reset bug is different from a normal web bug
A lot of application security habits do not map cleanly to CVE-2026-23918. There is no vulnerable query parameter to fuzz. There is no login form to bypass. There is no obvious URL path that proves exposure. The issue lives below application routing, in the HTTP/2 framing and stream lifecycle layer.
HTTP/2 changes the shape of a request. HTTP/1.1 is mostly text-oriented at the wire format level. HTTP/2 serializes HTTP semantics into binary frames. RFC 9113 describes the frame as the basic protocol unit and says that each HTTP request and response exchange is associated with its own stream. Streams are largely independent, which is what makes multiplexing possible on a single connection. (Rédacteur du RFC)
A browser or client does not simply send “GET /index.html” and wait. It can send HEADERS frames, DATA frames, SETTINGS frames, WINDOW_UPDATE frames, and RST_STREAM frames across streams on one connection. The stream ID tells the server which frames belong to which logical request. That is why a bug in stream cleanup can matter as much as a bug in parsing a URL.
The RST_STREAM frame is especially relevant. RFC 9113 says RST_STREAM allows immediate termination of a stream and is sent either to request cancellation or to indicate an error condition. The same section says a RST_STREAM frame fully terminates the referenced stream and causes it to enter the closed state. (Rédacteur du RFC)
That behavior is normal. Clients cancel requests all the time. A browser may start loading images, JavaScript, or CSS, then cancel work when the user navigates away. A crawler may drop a stream because a page is no longer needed. A load test client may reset streams when a timeout expires. HTTP/2 needs cancellation.
The problem in CVE-2026-23918 is not that RST_STREAM exists. The problem is the specific ordering and cleanup behavior reported in Apache httpd 2.4.66.
How the double-free is reported to trigger
Public researcher commentary reported by The Hacker News describes CVE-2026-23918 as a double-free in Apache httpd 2.4.66 mod_http2, specifically in the stream cleanup path of h2_mplx.c. The reported trigger sequence is a client sending an HTTP/2 HEADERS frame, then immediately sending a RST_STREAM with a non-zero error code on the same stream before the multiplexer has registered the stream. Two nghttp2 callbacks can then run in sequence and push the same h2_stream pointer into a cleanup array twice, which later causes the same stream object to be destroyed twice. (The Hacker News)
At a high level, the bug shape looks like this:
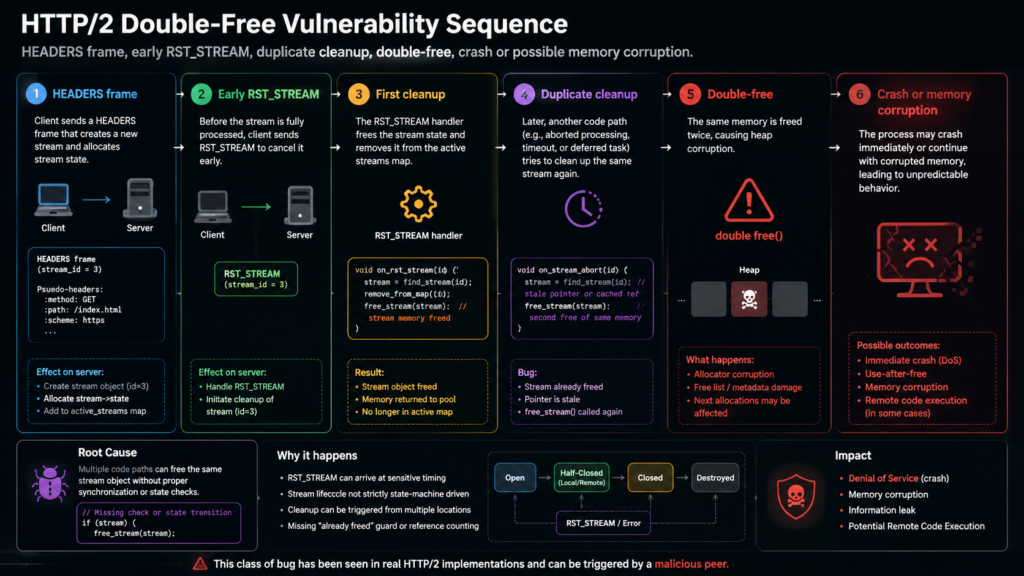
That is enough detail for defenders to understand the issue without handing them a production crash recipe.
A double-free is a memory lifetime bug. The program frees an allocation once, but later treats the same pointer as something that can be freed again. In a safe path, an object has one owner or a clear reference-counted lifetime. In a double-free path, two pieces of logic believe they are responsible for cleanup, or one piece of logic fails to mark that cleanup already happened.
The immediate result can be a crash. Modern allocators often detect some forms of heap misuse and abort the process. That is bad for availability but good for preventing silent corruption.
The more dangerous result is heap manipulation. If an attacker can influence what gets allocated into the freed region before the second free or later reuse, the bug may become a route to memory corruption. Whether that becomes code execution depends on allocator behavior, memory layout, target architecture, exploit reliability, process hardening, and whether the attacker can obtain or infer useful addresses. The public reporting cited a working lab PoC on x86_64 and also noted caveats such as the need for an information leak and probabilistic heap shaping. (The Hacker News)
That is why the right risk sentence is not “guaranteed RCE everywhere.” It is closer to this:
CVE-2026-23918 is a network-reachable memory-management bug in Apache HTTP Server 2.4.66 HTTP/2 handling. The clearest public outcome is worker crash and denial of service. Remote code execution has been publicly discussed and reported in lab conditions, but practical RCE depends on environment-specific memory conditions.
That sentence is less dramatic. It is also more useful.
Exposure depends on version, module, protocol, and traffic path
A vulnerable package name alone is not always enough to prove exploitability. A public h2 negotiation alone is not always enough either. CVE-2026-23918 exposure is a conjunction of several conditions.
| Condition | Pourquoi c'est important |
|---|---|
| Apache HTTP Server 2.4.66, or a downstream package carrying the vulnerable code path | Apache’s affected upstream version is 2.4.66 |
mod_http2 chargé | The issue is in HTTP/2 handling |
HTTP/2 enabled through Protocols | A loaded module may not be reachable |
| Attacker traffic can reach Apache as HTTP/2 | A CDN or proxy may terminate h2 before origin |
| Relevant MPM and runtime model | Public reporting distinguishes multithreaded deployments from prefork behavior |
| Running processes restarted after patching | Package installation does not always replace old workers |
| Containers and images rebuilt | Host patching does not update pinned container images |
Apache’s mod_http2 documentation says the module provides HTTP/2 support for Apache HTTP Server and relies on libnghttp2 for the core HTTP/2 engine. It also says HTTP/2 must be enabled via the Protocols directive, with h2 for HTTP/2 over TLS and h2c for HTTP/2 over TCP. (Apache HTTP Server)
The Apache HTTP/2 guide gives a typical secure configuration:
LoadModule http2_module modules/mod_http2.so
<VirtualHost *:443>
ServerName www.example.com
Protocols h2 http/1.1
</VirtualHost>
For all HTTP/2 variants, the documentation shows:
Protocols h2 h2c http/1.1
That second form matters because h2c is cleartext HTTP/2. In many production environments, cleartext HTTP/2 should be limited to trusted internal paths or disabled entirely. For this CVE, any path that allows an attacker to deliver HTTP/2 frames to the vulnerable Apache process deserves attention.
The proxy layer can change the answer. If a CDN terminates HTTP/2 from the internet and forwards HTTP/1.1 to Apache, the specific frame-level path may not reach the origin from the public internet. That does not automatically close the ticket. Direct-origin hostnames, alternate ports, internal load balancers, health check paths, staging hostnames, misconfigured bypass records, or service mesh paths may still deliver HTTP/2 to Apache.
The goal of validation is to find the real path, not the prettiest diagram.
MPM context matters, but it is not a patch
Apache’s Multi-Processing Module model shapes how the server handles connections and worker execution. The worker MPM is a hybrid multi-process, multi-threaded server. Apache’s documentation says worker uses threads to serve requests and can serve many requests with fewer system resources while retaining multiple processes for stability. (Apache HTTP Server)
The event MPM is based on worker and is designed to consume threads only for connections with active processing, freeing worker threads from some keep-alive waiting behavior. Apache describes event as using listener threads and non-blocking sockets to improve handling of idle and keep-alive connections. (Apache HTTP Server)
The Apache HTTP/2 guide says HTTP/2 is supported in all MPMs that ship with httpd, but warns that prefork has severe restrictions and says event is generally the best choice when supported. (Apache HTTP Server)
Public reporting on CVE-2026-23918 adds a vulnerability-specific note: researcher commentary said the DoS path works on default deployments with mod_http2 and a multi-threaded MPM, while prefork was described as not affected by the flaw. (The Hacker News)
Do not treat that as permission to ignore the update. MPM information helps prioritize and explain risk. It is not a substitute for applying the Apache 2.4.67 fix or a vendor patch.
A good triage statement looks like this:
Priority 1:
Internet-facing Apache 2.4.66, mod_http2 loaded, h2 reachable, worker or event MPM, direct origin reachable.
Priority 2:
Apache 2.4.66, mod_http2 loaded, h2 reachable only through internal paths or controlled networks.
Priority 3:
Apache 2.4.66 package present, but mod_http2 not loaded or HTTP/2 not enabled, pending local confirmation and patch scheduling.
Not enough evidence:
Only a public Server header suggests Apache. No version, module, package, or protocol evidence.
That kind of triage lets defenders act fast without making sloppy claims.
Safe validation starts with local proof
The safest way to validate CVE-2026-23918 is to prove exposure through configuration and runtime evidence. You do not need to crash a server to justify patching it.
On Debian or Ubuntu-style systems, start with the binary and package view:
apache2 -v
apache2ctl -V
dpkg -l | grep -E '^ii\s+apache2(\s|$)'
apt-cache policy apache2
On RHEL, AlmaLinux, Rocky Linux, Fedora, or similar systems:
httpd -v
apachectl -V
rpm -qa | grep -E '^httpd|^apache'
dnf info httpd
On SUSE-style systems:
httpd -v
apachectl -V
rpm -qa | grep -E '^apache2'
zypper info apache2
For cPanel EasyApache environments, the package names are often different. cPanel’s own CVE-2026-23918 support article recommends updating EasyApache packages and gives separate command examples for AlmaLinux, CloudLinux, Imunify360, and Ubuntu environments. (support.cpanel.net)
The next question is whether mod_http2 is loaded:
apachectl -M | grep -i http2
httpd -M 2>/dev/null | grep -i http2
apache2ctl -M 2>/dev/null | grep -i http2
A loaded module is not the same as reachable HTTP/2. Check configuration:
grep -RIn --include='*.conf' \
-E '^\s*Protocols\s+|^\s*H2Direct\s+|^\s*H2Upgrade\s+' \
/etc/apache2 /etc/httpd /usr/local/apache/conf 2>/dev/null
Typical exposed TLS HTTP/2 configuration looks like:
Protocols h2 http/1.1
A broader configuration may include cleartext HTTP/2:
Protocols h2 h2c http/1.1
The important word is “reachable.” A virtual host can enable HTTP/2 while another does not. A global directive can affect many virtual hosts. A reverse proxy can hide or expose different protocols depending on the path.
Utilisation boucler to confirm negotiation from the path you care about:
curl -I --http2 https://www.example.com/
curl -I --http2-prior-knowledge http://internal.example.local/
The first command tests HTTP/2 over TLS if your curl build supports it. The second tests prior-knowledge h2c and should only be used against systems you own or are authorized to test.
You can also inspect ALPN negotiation with OpenSSL:
openssl s_client -connect www.example.com:443 -servername www.example.com -alpn h2 </dev/null 2>/dev/null \
| grep -i 'ALPN protocol'
A result such as ALPN protocol: h2 proves that the endpoint selected HTTP/2 for that TLS connection. It does not prove Apache 2.4.66 behind it. It proves a protocol fact, not the entire vulnerability.
Now identify the MPM:
apachectl -V | grep -i 'Server MPM'
apachectl -M | grep -E 'mpm_(event|worker|prefork)'
You want output that helps answer whether the deployment is running event, workerou prefork.
Finally, confirm the running process after patching:
systemctl status apache2 --no-pager
systemctl status httpd --no-pager
ps -eo pid,lstart,cmd | grep -E '[a]pache2|[h]ttpd'
If packages were updated but old workers are still running, restart or reload according to your operational policy:
sudo systemctl restart apache2
sudo systemctl restart httpd
For high-availability systems, use a rolling restart behind a load balancer. The important point is that remediation is not complete until the vulnerable process is gone.
Remote evidence is weaker than owner-side evidence
Bug bounty hunters often do not have shell access. They may need to rely on external observation. That is acceptable, but the report should be honest about uncertainty.
Remote evidence can include:
curl -I --http2 https://target.example/
openssl s_client -connect target.example:443 -servername target.example -alpn h2 </dev/null
It can also include passive headers:
curl -I https://target.example/ | grep -i '^server:'
But many Apache deployments hide, normalize, or replace the Server header. Some sit behind Nginx, Envoy, HAProxy, Cloudflare, Fastly, AWS ALB, or a WAF. A response header is not enough to prove Apache version 2.4.66.
A strong external report says what is known and what needs owner confirmation:
Observed:
- The endpoint negotiates HTTP/2 via ALPN.
- Public response behavior is consistent with an Apache-backed service, but the exact origin version is not externally confirmed.
Needs owner confirmation:
- Whether origin Apache is 2.4.66 or a vendor package containing the vulnerable code path.
- Whether mod_http2 is loaded at the origin.
- Whether HTTP/2 is terminated at the edge or forwarded to Apache.
- Which MPM is running.
That is better than overstating. Security teams trust reports that draw clear evidence boundaries.
Do not run a crash PoC in production
The safest default is not to run frame-level crash or RCE proof-of-concept code against production. CVE-2026-23918 has a plausible denial-of-service path. A worker crash is not a harmless screenshot. It can drop user requests, trigger failover, corrupt incident timelines, and create unnecessary operational noise.
A safe validation workflow answers these questions without destructive testing:
- Is Apache HTTP Server 2.4.66 or a vulnerable downstream package present?
- Est
mod_http2loaded? - Is HTTP/2 enabled for the relevant virtual host?
- Can attacker-controlled traffic reach Apache as HTTP/2?
- Is the runtime MPM relevant to the reported crash path?
- Has the fixed package or Apache 2.4.67 been installed?
- Have all running processes been restarted or replaced?
- Are logs free of suspicious crash patterns after disclosure?
A destructive PoC belongs only in a lab or in a tightly scoped maintenance window with explicit authorization.
A safe lab can be useful for defenders who need to learn the traffic shape, test detections, or validate compensating controls. It should be isolated:
Safe lab requirements:
- Dedicated VM or container host
- No public exposure
- Explicit vulnerable Apache 2.4.66 build
- HTTP/2 enabled only inside the lab
- Crash-tolerant process supervision
- Packet capture inside the lab
- No reuse of production credentials, certificates, or data
Even in a lab, the goal should be learning and detection, not publishing a copy-paste crash client.
Detection logic, what defenders can actually look for
There is no universal, vendor-published IOC that proves exploitation of CVE-2026-23918. That is normal for protocol-level memory corruption. You are not looking for a static malware hash. You are looking for a combination of exposure and abnormal runtime behavior.
Useful signals include:
| Signal | Pourquoi c'est important | Limitation |
|---|---|---|
| Apache 2.4.66 with HTTP/2 enabled | Confirms exposure condition | Does not prove exploitation |
| Unexpected Apache child or worker crashes | Matches the clearest public impact path | Crashes can have unrelated causes |
| Segfaults or allocator aborts near disclosure window | Suggests memory misuse investigation | Requires local logs or core data |
| High volume of HTTP/2 stream resets | Relevant to early reset behavior | Legitimate clients also reset streams |
| Edge or proxy logs showing h2 anomalies | Helps identify suspicious clients or paths | Edge may not forward h2 to Apache |
| Direct-origin h2 access | Bypasses CDN assumptions | Requires asset discovery |
| Old workers after package update | Means patch may not be active | Needs runtime validation |
Start with Apache error logs and system logs:
journalctl -u apache2 --since "2026-05-04" --no-pager | \
grep -Ei 'segfault|core dumped|double free|corruption|child pid|caught SIG|AH[0-9]+'
journalctl -u httpd --since "2026-05-04" --no-pager | \
grep -Ei 'segfault|core dumped|double free|corruption|child pid|caught SIG|AH[0-9]+'
grep -RIEi 'segfault|core dumped|double free|corruption|child pid|caught SIG' \
/var/log/apache2 /var/log/httpd 2>/dev/null
Check coredumps where available:
coredumpctl list | grep -E 'apache2|httpd'
coredumpctl info <PID_OR_CORE_ID>
Look for HTTP/2-heavy client behavior in reverse proxy logs if your edge captures protocol and reset information. Field names vary by proxy. For Nginx, Envoy, HAProxy, CDN logs, and WAF logs, look for fields that can answer:
- Was the client connection HTTP/2?
- How many streams were opened per connection?
- How often were streams reset by the client?
- Did resets cluster around a small set of source IPs or user agents?
- Did origin workers crash shortly after those events?
If you use packet capture in a controlled environment, Wireshark can dissect HTTP/2 frames when TLS keys are available or when h2c is used in a lab. Apache’s own HTTP/2 guide names curl, Wireshark, nghttp, and h2load as useful tools for debugging HTTP/2 behavior. (Apache HTTP Server)
For production, be careful. Capturing decrypted traffic may expose sensitive data. Use narrow capture windows, minimize payload retention, and follow your organization’s logging and privacy rules.
A reasonable detection query is not “find CVE-2026-23918.” It is:
Find Apache 2.4.66 systems with HTTP/2 reachable.
Within those systems, find worker crashes, allocator errors, or abrupt child exits after public disclosure.
Correlate those crashes with HTTP/2-heavy traffic, client resets, direct-origin access, and unusual source clustering.
That is defensible. It avoids fake precision.
Patching and temporary mitigations
The durable fix is to update to Apache HTTP Server 2.4.67 or the fixed package supplied by your operating system, appliance, container image, or control-panel vendor. Apache’s advisory is direct: users are recommended to upgrade to 2.4.67, which fixes the issue. (Apache HTTP Server)
On Debian or Ubuntu-style systems, a typical package path is:
sudo apt update
sudo apt install --only-upgrade apache2
sudo systemctl restart apache2
apache2 -v
Ubuntu’s CVE page lists CVE-2026-23918 as High, shows Ubuntu 26.04 LTS resolute fixed at 2.4.66-2ubuntu2.1, and marks several earlier Ubuntu releases as not affected. That does not mean every non-Ubuntu older Apache is safe. It means Ubuntu’s own package analysis for those releases reached that status. (Ubuntu)
On RHEL-like systems:
sudo dnf clean all
sudo dnf makecache
sudo dnf update httpd
sudo systemctl restart httpd
httpd -v
On SUSE-like systems:
sudo zypper refresh
sudo zypper update apache2
sudo systemctl restart apache2
httpd -v
For cPanel EasyApache 4 on AlmaLinux, cPanel’s guidance includes:
sudo dnf clean all
sudo dnf makecache
sudo dnf -y update 'ea-apache*'
For Ubuntu-based EasyApache, cPanel lists:
sudo apt update
sudo apt install --only-upgrade "ea-apache24*"
Those commands should be adapted to your maintenance process, repositories, and vendor instructions. Do not blindly paste commands into production without knowing which package source you are using.
If patching is delayed, reduce exposure. Temporary mitigations can include disabling HTTP/2 for affected virtual hosts:
Protocols http/1.1
Then reload or restart Apache:
sudo apachectl configtest
sudo systemctl reload apache2
or:
sudo apachectl configtest
sudo systemctl reload httpd
If you use a CDN, load balancer, or reverse proxy, consider terminating HTTP/2 at the edge and forwarding HTTP/1.1 to Apache until the origin is fixed. That can reduce exposure to the frame-level bug if the edge truly prevents HTTP/2 frames from reaching Apache.
But temporary mitigations have sharp edges:
| Atténuation | Helps with | Does not solve |
|---|---|---|
| Disable HTTP/2 at Apache | Removes direct h2 trigger path | Leaves vulnerable code installed |
| Edge terminates h2 and forwards HTTP/1.1 | Reduces public frame-level exposure | Does not cover direct-origin access |
| Block h2c from untrusted networks | Removes cleartext HTTP/2 path | Does not fix TLS h2 |
| Restrict origin access to trusted proxies | Prevents bypass around CDN | Requires correct firewall and DNS hygiene |
| Restart after patch | Removes old vulnerable workers | Does not update pinned images |
Every temporary control should have an owner and an expiration condition. Otherwise “temporary” becomes permanent configuration drift.
Containers, golden images, and invisible old code
Containerized Apache deployments need special attention. A host package update does not patch a container image pinned to Apache 2.4.66. A rebuilt image does not fix already-running pods unless they are redeployed. A redeployed pod does not prove safety if another service still uses an old base image.
For Docker, check images and running containers:
docker ps --format 'table {{.ID}}\t{{.Image}}\t{{.Names}}\t{{.CreatedAt}}'
docker exec <container_id> httpd -v
docker exec <container_id> apache2 -v
For Kubernetes:
kubectl get pods -A -o wide
kubectl get deploy -A -o jsonpath='{range .items[*]}{.metadata.namespace}{"\t"}{.metadata.name}{"\t"}{range .spec.template.spec.containers[*]}{.image}{" "}{end}{"\n"}{end}'
kubectl exec -n <namespace> <pod> -- httpd -v
For image scanning, version evidence should be tied back to running workloads:
Image scan result:
- image registry.example.com/web/httpd:2026-05-01 contains Apache httpd 2.4.66
Runtime evidence:
- namespace: prod-web
- deployment: frontdoor-apache
- pod image digest: sha256:...
- container command confirms httpd 2.4.66
- service exposes 443
- ingress or load balancer allows HTTP/2 to origin
Golden images create a similar trap. If your AMI, VM template, Packer build, or Terraform module installs Apache 2.4.66, new instances can reintroduce exposure after you patch existing hosts.
A complete remediation ticket should include:
- Patch running hosts
- Rebuild base images
- Rebuild container images
- Roll deployments
- Validate running processes
- Validate protocol exposure
- Update scanner baseline
- Close direct-origin bypass paths
- Add regression check to CI or image pipeline
That is the difference between fixing a server and fixing a fleet.
Related CVEs that prevent bad mental models
CVE-2026-23918 belongs to a larger pattern: HTTP/2 and Apache server vulnerabilities often depend on protocol state, module configuration, and deployment topology. Comparing it with nearby issues helps prevent sloppy conclusions.
| CVE | Zone | Why it is relevant | Key difference |
|---|---|---|---|
| CVE-2023-44487 | HTTP/2 Rapid Reset | Shows that RST_STREAM behavior has been abused at internet scale | Protocol-level DoS, not Apache 2.4.66 double-free |
| CVE-2025-49630 | Apache mod_proxy_http2 | Another Apache HTTP/2-related DoS issue | Requires certain proxy configuration with HTTP/2 backend and ProxyPreserveHost on |
| CVE-2026-24072 | Apache mod_rewrite et ap_expr | Same Apache 2.4.67 release family | Local .htaccess author privilege issue, not HTTP/2 stream reset |
| CVE-2026-28780 | Apache mod_proxy_ajp | Same Apache 2.4.67 release family | AJP backend interaction, not client-side HTTP/2 early reset |
| CVE-2026-33006 | Apache mod_auth_digest | Same release family, moderate severity | Timing attack against Digest authentication, not memory corruption |
CVE-2023-44487 is the most useful comparison because it trained defenders to treat HTTP/2 resets as a real attack surface. NVD describes it as an HTTP/2 denial-of-service condition where request cancellation can reset many streams quickly and notes exploitation in the wild from August through October 2023. (NVD)
Cloudflare’s technical breakdown of Rapid Reset explains why stream cancellation is legitimate but abusable: a client can rapidly cancel streams and open new ones, creating server-side work even when stream concurrency limits appear to exist. That is not the same vulnerability as CVE-2026-23918, but it is the same class of operational lesson: HTTP/2 stream lifecycle behavior is not just an implementation detail. (The Cloudflare Blog)
CVE-2025-49630 is a narrower Apache comparison. NVD describes it as a denial-of-service issue in Apache versions 2.4.26 through 2.4.63, triggered in certain reverse proxy configurations where an HTTP/2 backend is used with ProxyPreserveHost on. (NVD)
The 2.4.67 release also fixed multiple non-HTTP/2 issues. Apache lists CVE-2026-24072 as a mod_rewrite elevation-of-privilege issue via ap_expr, CVE-2026-28780 as a mod_proxy_ajp heap-based buffer overflow involving malicious AJP backend responses, and several additional lower-severity issues across mod_md, mod_dav_lock, mod_auth_digest, mod_authn_socache, response splitting, and AJP parsing. (Apache HTTP Server)
The operational lesson is not “panic at every Apache CVE.” It is “read the whole release note.” A fleet that patches only the headline vulnerability but misses the rest of the package update has not really completed the risk reduction work.
A practical exposure checklist
Use this checklist for an Apache fleet. It is designed for defenders and authorized testers.
Asset identity
[ ] Hostname or service name recorded
[ ] Business owner identified
[ ] Internet-facing status confirmed
[ ] Direct-origin paths checked
[ ] CDN, WAF, or load balancer path documented
Apache version
[ ] Local binary version collected
[ ] Package version collected
[ ] Vendor package status checked
[ ] Container image digest recorded
[ ] Golden image or base image checked
HTTP/2 state
[ ] mod_http2 loaded or not loaded
[ ] Protocols directive reviewed
[ ] h2 over TLS tested from relevant network path
[ ] h2c tested only where authorized
[ ] Edge-to-origin protocol confirmed
Runtime model
[ ] MPM identified
[ ] Apache workers restarted after update
[ ] Old processes checked
[ ] Service health verified
Detection
[ ] Error logs checked for crashes
[ ] systemd journal checked
[ ] coredumps checked
[ ] proxy or CDN h2 reset patterns reviewed
[ ] suspicious source clustering reviewed
Remediation
[ ] Apache 2.4.67 or vendor fixed package installed
[ ] Runtime restarted or rolled
[ ] Containers rebuilt and redeployed
[ ] Temporary h2 disablement tracked if used
[ ] Retest evidence attached
The checklist is intentionally boring. Boring is what you want in vulnerability response.
What good evidence looks like
A good finding for CVE-2026-23918 should be replayable without crashing anything.
For an internal security team, the evidence bundle might look like this:
Finding:
Apache HTTP Server 2.4.66 with HTTP/2 enabled is exposed to CVE-2026-23918.
Evidence:
1. Host: web-prod-17.example.net
2. Package: apache2 2.4.66 build identified locally
3. Module: http2_module loaded in apachectl -M
4. Config: Protocols h2 http/1.1 enabled for :443 virtual host
5. External test: ALPN negotiated h2 from internet path
6. MPM: event
7. Runtime: process start time predates patch window
8. Logs: no confirmed exploitation, but worker crash review completed
9. Remediation: upgraded to vendor fixed package, restarted, rechecked h2 and version
For a bug bounty report, keep the claim narrower if you lack local evidence:
Title:
Apache HTTP/2 endpoint may be exposed to CVE-2026-23918 pending owner-side version confirmation
Summary:
The target negotiates HTTP/2 over TLS. CVE-2026-23918 affects Apache HTTP Server 2.4.66 with HTTP/2 handling and was fixed in Apache HTTP Server 2.4.67. I did not run any crash or RCE proof-of-concept. Owner-side confirmation is needed for the origin Apache version, mod_http2 state, MPM, and whether the edge forwards HTTP/2 to Apache.
Evidence:
- ALPN negotiation selected h2.
- The affected upstream version and fixed version are documented by Apache.
- No destructive testing was performed.
Impact:
If the origin is Apache HTTP Server 2.4.66 with mod_http2 reachable, the public risk includes worker crashes and possible environment-dependent RCE.
Remediation:
Confirm origin package and runtime state. Upgrade to Apache HTTP Server 2.4.67 or the vendor-fixed package. Restart Apache. If patching is delayed, temporarily prevent untrusted HTTP/2 from reaching the affected origin.
That report is honest. It gives the program enough information to investigate without pretending that remote protocol negotiation proves origin version.
For authorized teams using AI-assisted validation workflows, the useful role of automation is evidence discipline, not exploit theater. Penligent’s public materials describe an evidence-first agentic workflow with CVE-oriented testing, controlled actions, and traceable proof, and its CVE-2026-23918 page focuses on safe validation boundaries rather than destructive production PoCs. (penligent.ai)
The same principle applies with or without a platform: collect version proof, module proof, protocol proof, MPM proof, patch proof, restart proof, and log proof. A polished report without those artifacts is just prose.
Common mistakes
Treating every Apache version before 2.4.67 as affected
Apache’s advisory identifies Apache HTTP Server 2.4.66 for CVE-2026-23918. Ubuntu’s analysis also explains why some earlier packaged releases were marked not affected in Ubuntu’s ecosystem. Broad claims such as “all Apache before 2.4.67 is vulnerable to CVE-2026-23918” are not precise. (Apache HTTP Server)
A better statement is:
Apache’s upstream advisory lists Apache HTTP Server 2.4.66 as affected. Check downstream vendor package status for your distribution, control panel, appliance, or container image.
Trusting the public banner
Server headers are often hidden, changed, stripped, or produced by an intermediate proxy. A header such as Server: Apache is weak evidence. Local package inventory is stronger.
Forgetting the protocol path
A server can have Apache 2.4.66 installed but not expose HTTP/2. Another server can expose HTTP/2 at the CDN while forwarding HTTP/1.1 to Apache. Another can expose HTTP/2 internally through a service mesh. Draw the traffic path.
Patching the package but not the process
If old workers keep running, the patch may not be active. Validate process start time after patching.
Ignoring containers
Pinned images are one of the easiest ways to reintroduce old vulnerable code. Rebuild and redeploy.
Turning safe validation into a denial-of-service test
A production crash does not make a report better. It creates operational risk. Confirm exposure through configuration and runtime evidence.
Assuming no exploitation because there is no IOC
Memory corruption in HTTP/2 handling may not leave a neat application log. Absence of a known IOC is not absence of risk. Patch exposure first, investigate crash patterns second.
What defenders should tell leadership
Leadership updates should be accurate, short, and free of exploit drama. A useful version is:
CVE-2026-23918 affects Apache HTTP Server 2.4.66 when HTTP/2 handling is reachable. Apache fixed it in 2.4.67. The clearest public impact is worker crash and denial of service; possible RCE has been publicly discussed but depends on environment-specific memory conditions. We are prioritizing internet-facing Apache 2.4.66 systems with HTTP/2 enabled, applying vendor-fixed packages, restarting services, checking containers and origin bypass paths, and reviewing logs for crash indicators since disclosure. We are not running destructive PoCs against production.
That message gives the business the answer it needs: scope, impact, action, and safety boundary.
Useful sources to keep open while patching
Apache’s official Apache HTTP Server 2.4 vulnerabilities page is the primary source for affected version, fixed version, finder credits, and the broader 2.4.67 security release context. (Apache HTTP Server)
NVD’s CVE-2026-23918 record is useful for CWE mapping, displayed CISA-ADP CVSS 3.1 scoring, CPE history, and reference tracking. (NVD)
The Openwall oss-security post is a concise advisory mirror with affected version, credit, and timeline details from the Apache disclosure. (Openwall)
Apache’s HTTP/2 and mod_http2 documentation helps teams validate whether HTTP/2 is actually enabled and how Protocols, h2et h2c are configured. (Apache HTTP Server)
Ubuntu, SUSE, cPanel, and other downstream vendors should be checked for package-specific status and update instructions because enterprise fleets rarely run only upstream tarballs. (Ubuntu)
FAQ
What versions are affected by CVE-2026-23918?
- Apache’s upstream advisory lists Apache HTTP Server 2.4.66 as affected.
- Apache says the issue is fixed in Apache HTTP Server 2.4.67.
- Downstream vendors may use different package version strings, so check your distribution, control panel, appliance, or container image status.
- Do not assume every Apache 2.4.x version is affected by this specific CVE without vendor evidence.
Is CVE-2026-23918 remotely exploitable?
- The issue is in HTTP/2 handling, so the relevant attack path is network traffic that reaches Apache as HTTP/2.
- Public reporting describes a clear denial-of-service path through worker crashes.
- Possible RCE has been publicly discussed, but practical code execution is more environment-dependent than crashing a worker.
- Exposure depends on Apache version,
mod_http2, enabled protocols, MPM context, and whether HTTP/2 reaches Apache directly.
Do I need to run a PoC to prove exposure?
- No.
- For normal remediation, version plus module plus HTTP/2 reachability plus runtime context is enough to justify patching.
- Running a crash PoC in production can create a denial-of-service condition.
- Destructive testing should be limited to an isolated lab or an explicitly approved maintenance window.
How can I safely check whether HTTP/2 is reachable?
- Utilisation
curl -I --http2 https://host/to test HTTP/2 support from an authorized path. - Utilisation
openssl s_client -connect host:443 -servername host -alpn h2to inspect ALPN negotiation. - Review Apache configuration for
Protocols h2 http/1.1ouProtocols h2 h2c http/1.1. - Confirm whether a proxy terminates HTTP/2 or forwards it to Apache.
Is disabling HTTP/2 enough?
- Disabling HTTP/2 can reduce exposure if untrusted HTTP/2 no longer reaches Apache.
- It is a temporary mitigation, not the durable fix.
- You still need to upgrade to Apache 2.4.67 or a vendor-fixed package.
- Track any HTTP/2 disablement as an exception so it does not become unmanaged drift.
What should I look for in logs?
- Look for Apache child process crashes, segfaults, allocator errors, core dumps, or abrupt worker exits.
- Correlate crash timing with HTTP/2 traffic, stream reset anomalies, and direct-origin access.
- Do not rely on a single log line as proof of exploitation.
- Lack of a log indicator does not remove the need to patch an exposed vulnerable system.
How should containers be handled?
- Check the Apache version inside the running container, not just on the host.
- Rebuild images that contain Apache 2.4.66 or a vulnerable downstream package.
- Redeploy workloads so running pods or containers actually use the fixed image.
- Update base images, CI build steps, and golden images to prevent reintroducing the vulnerable version.
What should a bug bounty report include?
- Include non-destructive evidence such as HTTP/2 negotiation, suspected Apache exposure, and official Apache affected and fixed version references.
- Clearly state what you could not confirm externally, such as origin package version or MPM.
- Do not include or run a crash script unless the program explicitly authorizes it.
- Recommend owner-side confirmation and upgrade to Apache 2.4.67 or the vendor-fixed package.
Arrêt de clôture
CVE-2026-23918 deserves fast, careful handling because it sits in a network-exposed web server path, involves HTTP/2 stream lifecycle handling, and belongs to a memory-corruption weakness class that can be more serious than a simple crash in the right environment. The safest response is not complicated: find Apache 2.4.66, confirm whether HTTP/2 reaches mod_http2, prioritize internet-facing and direct-origin paths, apply Apache 2.4.67 or vendor fixes, restart running processes, rebuild containers, and preserve evidence for retest.
The wrong response is to turn validation into an outage. A production crash is not proof of maturity. A clean evidence chain is.