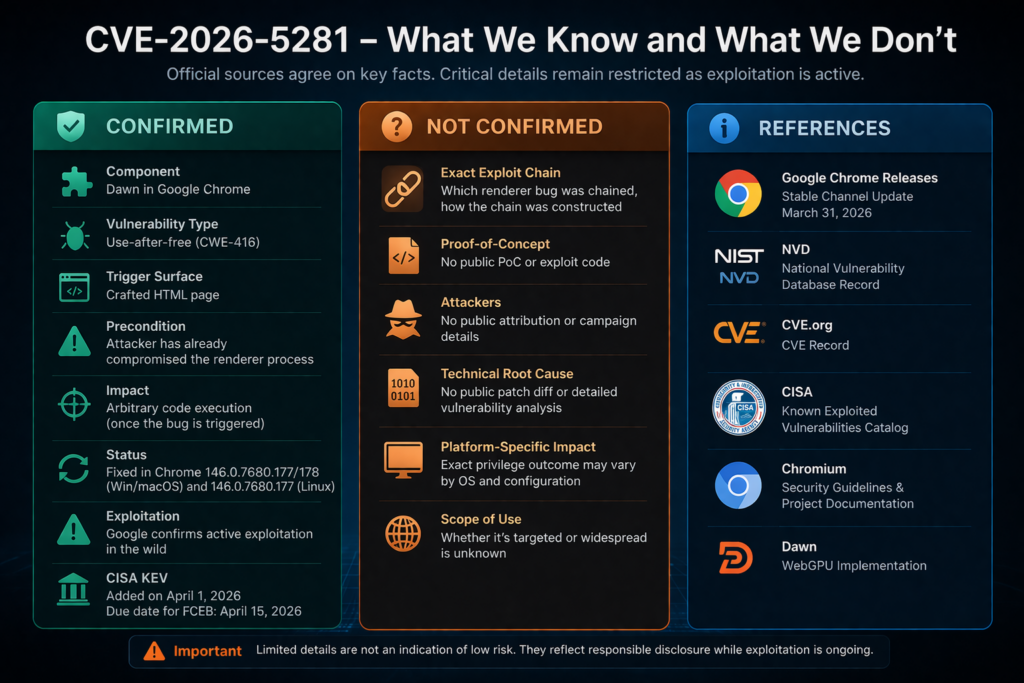
Google’s March 31, 2026 Stable Channel bulletin fixed CVE-2026-5281 in Chrome and said an exploit for the flaw exists in the wild. NVD published the record on April 1, 2026 and described it as a use-after-free in Dawn, with a critical nuance many summaries flatten away: the public description says the attacker must already have compromised the renderer process before using a crafted HTML page to reach the bug. CISA added the issue to its Known Exploited Vulnerabilities catalog the same day, turning it from a browser patch note into a formal, time-bound remediation item for federal agencies. (Chrome Releases)
That wording matters because CVE-2026-5281 is not best understood as a simple one-step “browse and own the box” story. The public record points to something defenders should recognize immediately: this looks like the kind of bug that becomes valuable after an attacker already has code execution or equivalent control inside Chrome’s renderer sandbox and wants the next boundary crossing. In real exploitation terms, that usually means a chain, not a lone bug. (NVD)
The component name matters too. Dawn is not a random internal helper library. It is the open-source, cross-platform implementation of WebGPU used by Chromium. Chromium’s own security research has already framed WebGPU as a meaningful new attack surface that spans both the renderer and GPU process and eventually reaches native graphics APIs such as Vulkan, Metal, D3D12, and OpenGL. Once you understand that path, CVE-2026-5281 stops looking like a niche graphics bug and starts looking like a boundary problem in one of the browser’s most security-sensitive subsystems. (Dawn Git Repositories)
The right way to read this CVE on April 3, 2026 is brutally simple. Patch it. Verify the actual running browser version. Treat lagging endpoints as high priority. Do not invent exploit details Google has not published. Do not downplay the bug because the renderer compromise is a precondition. Do not assume other Chromium-based browsers picked up the fix on the same schedule without vendor confirmation. Those are the operational points that survive careful reading of the official material. (Chrome Releases)
The public record as of today compresses into the following facts. (Chrome Releases)
| Objet | Publicly confirmed |
|---|---|
| CVE | CVE-2026-5281 |
| Composant | Dawn |
| Product context | Google Chrome |
| Weakness class | Use-after-free, CWE-416 |
| Vendor status | Google says an exploit exists in the wild |
| Public exploit detail | Not publicly disclosed |
| Trigger surface in public description | Crafted HTML page |
| Important precondition | Attacker had already compromised the renderer process |
| Fixed Chrome builds from Google bulletin | 146.0.7680.177 or 146.0.7680.178 on Windows and macOS, 146.0.7680.177 on Linux |
| CISA KEV | Added on April 1, 2026 with an April 15, 2026 due date for FCEB agencies |
What the official sources actually say
NVD’s one-line description is concise and loaded with meaning. It identifies the bug as a use-after-free in Dawn in Google Chrome prior to 146.0.7680.178, tags it as CWE-416, and says a remote attacker who had compromised the renderer process could execute arbitrary code via a crafted HTML page. That is enough to establish the vulnerability class, the component, the web-triggered surface, and the crucial precondition. It is not enough to tell you the full exploit chain, the exact buggy code path, or whether the bug was used in narrowly targeted operations or something broader. (NVD)
Google’s own Stable Channel bulletin dated March 31, 2026 adds the two sentences responders care about most. First, it gives the platform-specific fixed versions. Second, it states that Google is aware an exploit for CVE-2026-5281 exists in the wild. The same bulletin also says that bug details and links may stay restricted until a majority of users are updated, and that restrictions can remain in place when a bug exists in a third-party library other projects also depend on. That single note explains why so much commentary around this CVE is thin: the official issue is intentionally not fully public yet. (Chrome Releases)
The NVD reference list reinforces that point. It points to the Chrome release note and to an issue-tracking entry that is permissions-restricted. In other words, the public vulnerability record itself tells you there is more detail internally than the internet can currently inspect. That means careful writing should narrow claims, not expand them. (NVD)
CISA’s action changes the prioritization conversation again. Its April 1, 2026 alert says the vulnerability was added to the Known Exploited Vulnerabilities catalog based on evidence of active exploitation, and the catalog entry shows an April 15, 2026 due date for Federal Civilian Executive Branch agencies. Even if you do not work in an agency, KEV inclusion is one of the clearest public signals that a patch should move fast. (CISA)
There is another useful detail inside Google’s bulletin that too many summaries skip. CVE-2026-5281 was not the only Dawn memory-safety bug fixed in that same release. The March 31 bulletin also lists CVE-2026-5284 and CVE-2026-5286 as use-after-free issues in Dawn. That does not prove they are variants of the same root cause, and it would be irresponsible to claim they are. But it does tell defenders something important: the component was producing multiple high-severity memory-safety fixes in the same cycle, which is a sign of dense risk, not isolated noise. (Chrome Releases)
The version floor that can trip up responders
One of the easiest mistakes during fast-moving browser incidents is to treat the NVD one-liner as your exact patch floor. For CVE-2026-5281, that would be sloppy. NVD normalizes the description as “prior to 146.0.7680.178,” but Google’s own release note is more precise: Windows and macOS were updated to 146.0.7680.177 or 146.0.7680.178, while Linux was updated to 146.0.7680.177. In other words, the vendor bulletin is the better operational source for version gating. (NVD)
That distinction is not pedantic. It affects how you write fleet checks, how you explain status to IT, and how you avoid false positives in internal dashboards. If your script blindly flags everything below 146.0.7680.178 on every platform, you may mis-handle Linux or create needless confusion around .177 on Windows and macOS. For live response, the safest rule is simple: use the vendor’s platform-specific fixed builds as your baseline, and use NVD as the normalized cross-reference, not the sole operational truth. (Chrome Releases)
The public fix matrix looks like this. (Chrome Releases)
| Plate-forme | Fixed version floor from Google’s March 31 bulletin | Operational note |
|---|---|---|
| Fenêtres | 146.0.7680.177 or 146.0.7680.178 | Use the vendor bulletin rather than a simplified NVD summary |
| macOS | 146.0.7680.177 or 146.0.7680.178 | Same caution as Windows |
| Linux | 146.0.7680.177 | Do not incorrectly force a .178 floor on Linux based only on shorthand summaries |
For single endpoints, local verification is straightforward.
# Windows PowerShell
$paths = @(
"$Env:ProgramFiles\\Google\\Chrome\\Application\\chrome.exe",
"$Env:ProgramFiles(x86)\\Google\\Chrome\\Application\\chrome.exe"
)
foreach ($p in $paths) {
if (Test-Path $p) {
$v = (Get-Item $p).VersionInfo.ProductVersion
Write-Host "$p -> $v"
}
}
# macOS
/Applications/Google\\ Chrome.app/Contents/MacOS/Google\\ Chrome --version
# Linux
google-chrome --version 2>/dev/null || \\
google-chrome-stable --version 2>/dev/null || \\
chromium --version 2>/dev/null
For batch work, the important point is not the command syntax. It is the comparison logic. The version check should be platform-aware, and it should compare the running browser version, not only the package version reported by a software inventory system.
# Minimal version comparison helper for asset exports
# input rows like: hostname,platform,version
# platform values: windows, macos, linux
FIX = {
"windows": (146, 0, 7680, 177),
"macos": (146, 0, 7680, 177),
"linux": (146, 0, 7680, 177),
}
def parse(v: str):
return tuple(int(x) for x in v.strip().split("."))
def is_vulnerable(platform: str, version: str) -> bool:
return parse(version) < FIX[platform]
samples = [
("ws-01", "windows", "146.0.7680.176"),
("mac-02", "macos", "146.0.7680.177"),
("lin-03", "linux", "146.0.7680.176"),
]
for host, platform, version in samples:
print(host, platform, version, "VULNERABLE" if is_vulnerable(platform, version) else "OK")
In a mature environment, you should also separate three states that often get mixed together in executive updates: available to install, installed on disk, and actually running. The last one is what matters to exposure. That is a process discipline issue more than a browser-specific issue, but browser incidents are where teams most often learn that distinction the hard way.
Why the renderer compromise precondition changes everything
The single most important line in the public description is the one that says the attacker had already compromised the renderer process. That phrase is the difference between a first-stage browser bug and a boundary-crossing bug that becomes valuable after stage one. (NVD)
Chromium’s own security guidance helps explain how to read that. Its severity guidelines say high-severity issues include bugs in the browser or other high-privileged processes, such as the GPU process on platforms where it is not sandboxed, when those bugs are reachable only from a compromised renderer and lead to a sandbox escape. The same guidance also says that bugs requiring a compromised renderer are typically high severity rather than critical, even when the impact can still be serious. In other words, Google’s “High” label on CVE-2026-5281 is not a sign that the bug is mild. It is a sign that the exploit model includes a precondition. (Chromium Git Repositories)
That is why phrases like “only exploitable after renderer compromise” should not calm defenders. In a real chain, stage one and stage two are not two unrelated incidents. Stage one gets untrusted web content to code execution inside the renderer. Stage two uses a second bug to cross a stronger boundary, widen access, or escape a sandbox. Browsers have worked this way for years, and Chrome’s own security model exists because renderer compromise is assumed to be plausible enough that strong isolation must exist around it. (Chromium Git Repositories)
The renderer’s isolation is not theoretical. Chromium’s sandbox design documentation describes the renderer as running with an untrusted integrity token on Windows, with almost all resources duplicated into it by the browser process because the renderer itself is so restricted. That is exactly why a second bug that helps an attacker move out of that boundary can be strategically valuable even if it is not the first bug in the chain. (Chromium Git Repositories)
The GPU side of the picture is just as important. Chromium’s Rule of 2 guidance treats the browser process and GPU process as high privilege in architectural terms because they can do what the user can do, with the user’s data and accounts. That high-privilege framing is one reason graphics-boundary bugs draw so much attention. A chain that begins in a renderer and reaches the graphics stack is not traversing a harmless implementation detail. It is moving toward code that is much closer to the user’s real privileges and to native system surfaces. (Chromium Git Repositories)
A cautious, public-record-consistent way to think about CVE-2026-5281 is this:
| Stade | What is publicly supported | What remains inference |
|---|---|---|
| Initial contact | Crafted HTML page is part of the reachable surface | Exact delivery vector and site context are not public |
| Stage one | Renderer compromise is a stated precondition | The bug or technique used to compromise the renderer is not public |
| Stage two | CVE-2026-5281 is then used in Dawn | The exact primitive obtained and precise code path are not public |
| Résultats | NVD says arbitrary code execution is possible | The exact privilege outcome on each platform is not fully public |
That table captures the discipline good response teams need. You do not need a published exploit chain to understand that this is a chain-shaped problem. The public description already tells you that.
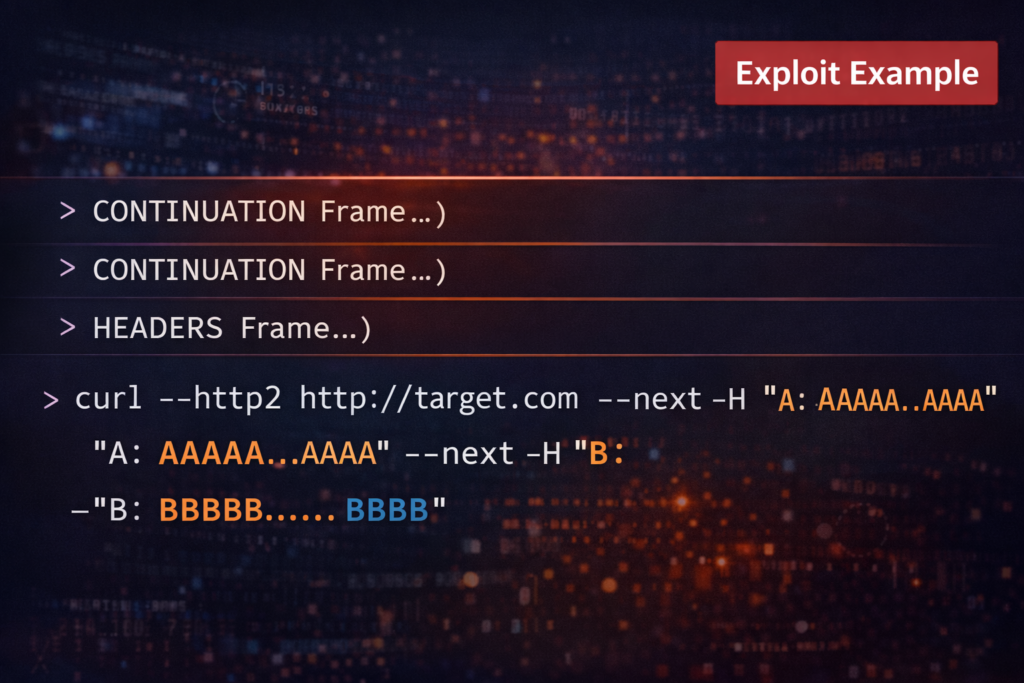
Dawn, WebGPU, and why this component is not a side alley
To understand why CVE-2026-5281 deserves serious attention, you need to understand what Dawn is inside Chromium. Dawn’s own repository describes it as an open-source, cross-platform implementation of the WebGPU standard and says it is the underlying implementation of WebGPU in Chromium. It also says Dawn includes a native WebGPU implementation over D3D12, Metal, Vulkan, and OpenGL, plus a client-server implementation for applications in a sandbox without direct access to native drivers. (Dawn Git Repositories)
Chromium’s WebGPU Technical Report fills in the browser-specific path. WebGPU is exposed to web content through JavaScript. Those JavaScript calls enter Dawn, which is split into Dawn Wire and Dawn Native. In Chromium’s architecture, the call is serialized in the renderer using the Dawn Wire client, sent into the GPU process using WebGPU extensions to Chrome’s GPU command buffer, deserialized by the Dawn Wire server, and then handed to Dawn Native, which wraps the underlying platform graphics API. That is not a toy path. It crosses process boundaries, touches native graphics machinery, and depends on complex lifetime management. (Chromium Git Repositories)
A minimal, non-malicious WebGPU example is enough to show why web content can reach this stack at all.
async function checkWebGPU() {
if (!("gpu" in navigator)) {
console.log("WebGPU not available in this browser");
return;
}
const adapter = await navigator.gpu.requestAdapter();
if (!adapter) {
console.log("No WebGPU adapter returned");
return;
}
const device = await adapter.requestDevice();
console.log("WebGPU device acquired", device);
}
checkWebGPU();
That snippet is ordinary developer code. The important point is not the code itself. The important point is architectural reachability. Chromium’s own security research says WebGPU adds attack surface in both the renderer and GPU process, and also introduces a WGSL shader compiler surface in the GPU process. It explicitly frames the graphics stack as attractive to attackers because these accelerated features are complex, interact with drivers in the kernel, and are implemented in memory-unsafe languages. That is the context in which a Dawn use-after-free should be read. (Chromium Git Repositories)
This is also why “graphics bug” is the wrong mental shortcut. In a modern browser, graphics is not just pixels. It is an interface to privileged processes, native drivers, serialization paths, command buffering, asynchronous execution, and complex object ownership. Chrome’s own security material says those characteristics make graphics bugs especially useful for bypassing sandbox boundaries. That sentence is a better starting point for triage than any social-media summary. (Chromium Git Repositories)
Why use-after-free bugs keep showing up in places like Dawn
CWE defines use-after-free as reusing or referencing memory after it has been freed. In practical terms, that usually means a stale pointer continues to exist after the object it once referred to has already been destroyed, and later code mistakenly treats that pointer as if the object were still alive. That stale reference can then become a crash, memory corruption, or an exploitable primitive, depending on what gets reallocated into the same region and how controllable the later access is. (CWE)
The weakness keeps appearing because lifetime management is hard in the exact kinds of systems browsers are full of: asynchronous work queues, cross-thread execution, cross-process ownership, callbacks, object reuse, and native code with manual or semi-manual memory discipline. The broader weakness class remains prominent enough that CWE-416 ranks high in the 2025 CWE Top 25, and it is even more prominent in the 2025 KEV weakness insights, where it ranks near the top among weakness types represented in exploited vulnerabilities. That is not proof that every UAF will be exploited. It is evidence that the class remains operationally relevant. (CWE)
Chromium’s own WebGPU report is especially useful here because it does not just wave at the risk. It documents how Dawn’s object model can become difficult to reason about. The report describes a chain where WebGPU objects in JavaScript correspond to objects in the renderer, then to server objects in the GPU process, and finally to native graphics objects below. It also notes that WebGPU work is asynchronous and that object lifetimes span multiple layers of reference counting and raw pointers. That is exactly the sort of environment where stale lifetime assumptions can turn into UAFs. (Chromium Git Repositories)
One part of that report is especially instructive. Chromium’s researchers explicitly warned that Dawn had a pattern where objects held raw pointers to reference-counted objects based on the assumption that some other part of the system was already holding the real lifetime reference. They argued that this pattern could too easily break as the code evolved and should be discouraged to reduce use-after-free bugs. That statement does not identify the exact bug behind CVE-2026-5281. It does something more useful for defenders and engineers: it explains why Dawn is the kind of component that can repeatedly generate this family of issues. (Chromium Git Repositories)
A safe conceptual example looks like this:
// Conceptual example, not Chrome code
struct Buffer : RefCounted {
void transition();
};
std::set<Buffer*> pending; // raw pointers only
void queue(Buffer* b) {
pending.insert(b); // assumes someone else keeps b alive
}
void later() {
for (auto* b : pending) {
b->transition(); // danger if lifetime assumption was wrong
}
}
If the final owning reference to Buffer disappears before later() runs, the pending set still holds a pointer-shaped value that looks valid enough to dereference. That is the essence of a use-after-free. In simple code, the bug is obvious. In a system like Dawn, where the object may cross renderer, GPU process, command buffers, callbacks, and platform APIs, it is much easier for the stale-lifetime assumption to hide inside perfectly reasonable-looking code.
Chromium’s WebGPU report documents exactly that sort of risk surface. It describes a previously found Dawn issue where raw pointers were used in places that really needed stronger lifetime tracking, and shows a fix pattern that moved from raw pointers to reference-counted storage. Again, that is not proof that CVE-2026-5281 used the same path. It is proof that Dawn has already produced publicly documented UAF patterns tied to object lifetime assumptions. (Chromium Git Repositories)
This matters because the March 31 Chrome bulletin did not just fix CVE-2026-5281. It also fixed CVE-2026-5284 and CVE-2026-5286, both described by Google as use-after-free issues in Dawn. When a single component is shipping multiple UAF fixes in one release, a serious reader should stop asking whether the area is “important enough” and start asking how quickly the environment can be patched and validated. (Chrome Releases)
What the public record does not prove
This is where a lot of otherwise decent vulnerability writing falls apart. Once a bug is labeled a zero-day, a surprising number of articles start quietly replacing documented facts with imagined detail. CVE-2026-5281 does not need that treatment. The real record is already serious enough. (Chrome Releases)
The public record does not tell us which renderer-compromise bug was chained with CVE-2026-5281. It does not tell us whether the exploit path targeted the GPU process in a way that behaved the same on Windows, macOS, and Linux. It does not tell us what the final privilege impact looked like on each platform. It does not tell us whether attackers used the flaw in broad exploitation, in narrow post-exploitation tradecraft, or in targeted operations. And it does not give us a public patch diff tied cleanly and unambiguously to the restricted bug page. (NVD)
That does not mean responders are blind. It means they should frame their work honestly. A good internal advisory can say all of the following at once without contradiction: the bug is real, exploitation is real, public exploit details are limited, and patching still needs to happen now. In fact, that is exactly the kind of incident discipline mature teams need.
Three common mistakes are worth calling out explicitly.
The first mistake is to rewrite “crafted HTML page” as if it automatically means single-bug remote system compromise from a clean browser state. The official wording does not say that. It says the attacker had already compromised the renderer process and then used a crafted HTML page to execute arbitrary code via the Dawn bug. That is a more specific and more chain-shaped model. (NVD)
The second mistake is to treat the renderer precondition as if it downgrades urgency. Chromium’s own severity guidance says the opposite in effect: bugs that need a compromised renderer can still be high-severity sandbox-escape-style issues, and that is how Google classifies them. A second-stage exploit primitive in a browser chain is not a paperwork nuisance. It is the part that can make stage one count. (Chromium Git Repositories)
The third mistake is to over-generalize product exposure. We know Dawn is open-source and underlies WebGPU in Chromium. We know CISA catalogs the issue under Dawn. But the public record for this CVE is centered on Google Chrome’s fixed builds. That means defenders should absolutely ask downstream Chromium browser vendors whether and when they integrated the fix, but they should not write as if every product touching WebGPU is automatically and identically affected until its own vendor says so. (Dawn Git Repositories)
That last point is where a lot of enterprise confusion happens. Browser families share code, but release cadences, backports, and hardening layers are not always synchronized. The correct operational stance is to assume nothing and verify everything.
Why the WebGPU boundary deserves more attention than it gets
WebGPU is still new enough in the minds of many defenders that it does not yet trigger the same reflex as V8, DOM parsing, or media codecs. That is a mistake. Chromium’s own security research describes WebGPU as adding two notable attack surfaces: the WebGPU API implementation in the renderer and GPU process, and the WGSL shader compiler in the GPU process. The report also makes clear that the graphics path reaches down into native graphics APIs and eventually toward drivers and lower layers that historically have not been easy to harden perfectly. (Chromium Git Repositories)
There are three reasons that matters in practice.
The first is that WebGPU is reachable from ordinary web content through JavaScript. A feature that is web-exposed and performance-sensitive is already a candidate for high-risk engineering pressure. It has to be fast, cross-platform, standards-compliant, and compatible with a wide spread of hardware and drivers. That mix is historically unfriendly to bug-free code. (Chromium Git Repositories)
The second is that WebGPU is fundamentally asynchronous and stateful. Chromium’s report walks through how WebGPU queues work, how command buffers hold references to native objects, and how those commands may execute later. That is exactly the kind of system where object lifetime, callback timing, and reference ownership become easy places to make mistakes that static reasoning misses. (Chromium Git Repositories)
The third is that Chrome’s graphics stack has always sat near security boundaries people care about. Chromium’s report says graphics bugs are especially useful for bypassing sandbox boundaries, while the project’s Rule of 2 guidance treats the GPU process as high privilege. Put differently, the WebGPU boundary is not just a feature boundary. It is a security boundary where web input, native code, and privileged execution concerns collide. (Chromium Git Repositories)
That is the bigger lesson of CVE-2026-5281. Even if the exact exploit chain never becomes public, the incident tells defenders where not to be complacent. If your browser risk model still treats “graphics” as background implementation detail rather than a first-tier attack surface, it is behind the way Chromium’s own security team talks about the platform.
What defenders should do right now
The first action is obvious: move Chrome to the March 31 fixed builds or later on every managed endpoint, and treat any unpatched systems as exposed until proven otherwise. Because Google’s bulletin says the rollout happens over days and weeks, relying on passive auto-update alone is not a strong enough response for high-risk environments. The version floor needs to be enforced, then checked. (Chrome Releases)
The second action is to prioritize by user role, not just raw endpoint count. Any user who frequently handles external content, ad-heavy browsing, research workflows, unmanaged sites, or sensitive internal systems should be near the front of the patch queue. A browser chain that starts with renderer compromise and moves toward a stronger boundary is especially concerning on devices that can later touch privileged applications, admin portals, or sensitive identity material. That is a risk judgment, not a claim about this specific campaign, and it is the right judgment.
The third action is to build your exposure logic around running state. A patch package sitting on disk is not the same thing as a protected browsing session. Good response practice checks what version is actually running and whether vulnerable browser processes are still open. If your internal process cannot answer that question quickly, browser zero-days will keep turning into “we thought it was fixed” incidents.
The fourth action is to handle Chromium-based downstream browsers deliberately. Use Google’s bulletin as the upstream signal, but do not assume same-day downstream parity. Require each vendor to confirm the patched build or provide a version that clearly includes the March 31 fix train. That is especially important for teams standardized on non-Google Chromium derivatives.
The fifth action is to treat KEV inclusion as a forcing function for communication quality. Security teams often understand the urgency, while IT and leadership only hear “Chrome patch.” The message should be sharper: this is an actively exploited browser memory-safety vulnerability tied to a boundary-sensitive component, with public evidence strong enough for CISA KEV inclusion. That phrasing is accurate and hard to misprioritize. (CISA)
A pragmatic response timeline looks like this.
| Fenêtre temporelle | Priority actions |
|---|---|
| First 4 hours | Identify Chrome versions below the fixed floor, prioritize internet-facing users and high-value roles, begin forced updates where policy allows |
| 4 to 24 hours | Verify running versions, chase systems that downloaded but did not relaunch, request downstream Chromium vendor confirmation |
| 24 to 72 hours | Close long-tail endpoints, preserve evidence from suspicious browser instability, review exceptions and unmanaged assets |
For larger teams, the internal handoff checklist should be equally concrete.
| Team | Minimum question to answer |
|---|---|
| IT endpoint management | Which devices are below the fixed vendor build today |
| Security engineering | Which devices are still running vulnerable browser processes |
| SecOps | Did any lagging endpoints show suspicious browser crashes or post-browser compromise behavior |
| Governance or compliance | Does KEV-driven tracking require formal deadline evidence |
| Leadership | Are any privileged or regulated user groups still exposed |
For organizations that already use evidence-first validation workflows, the right move is to fold this browser incident into the same proof model used for other high-priority remediations: fixed version, running state, exception handling, and post-remediation checks tied to timestamped evidence. Penligent’s closely related Chrome zero-day writeups and broader material on AI-driven validation are useful as follow-on reading in that workflow, not because an external validation platform replaces the vendor patch, but because disciplined evidence collection beats ticket closure theater every time. (Penligent)
How to hunt when exploit details are still restricted
No one should pretend that hunting CVE-2026-5281 is easy without public IOCs, crash signatures, or a released exploit. But “hard” is not the same thing as “impossible.” In the first days of a restricted bug, hunting should focus on defensible signals rather than fantasy precision. (Chrome Releases)
Start with version lag. Systems still below the fixed build after March 31 are your best candidate set for deeper review. That is not glamorous, but it is how real incident response works. Risk starts with exposure, not with cleverness. A device that never ran a vulnerable build during the active exploitation window is a very different problem from one that remained below the floor while users were browsing normally.
Then look at browser instability and related telemetry. Because CVE-2026-5281 is a memory-safety bug in a graphics-adjacent component, unusual Chrome crashes, GPU-process instability, repeated browser restarts, or unusual failure bursts on lagging endpoints deserve extra attention. None of those are unique indicators, and none of them prove exploitation. They are prioritization signals.
After that, look for suspicious activity near browser execution on lagging systems. That can mean anomalous child processes, credential access attempts, persistence changes, or other post-browser activity that does not fit the normal user’s workflow. Since the public model already tells you the bug is useful after renderer compromise, looking for signs of a broader chain is better than waiting for a perfect, CVE-specific fingerprint.
A useful hunting sequence can be written in plain English:
- Identify endpoints that ran below the fixed version floor after March 31, 2026.
- Within that set, prioritize users with elevated access or risky browsing patterns.
- Within that smaller set, look for browser crashes, repeated browser restarts, or unusual GPU-related instability.
- On the same systems, inspect EDR timelines for suspicious follow-on behavior after browser launch.
- Preserve crash artifacts, browser history, EDR process trees, and any downloaded HTML or script content tied to the session when available.
That workflow is not flashy, but it is the one most likely to produce something real.
What defenders should not do is invent product-specific rules they cannot validate. If you do not have a confirmed crash signature, do not publish one. If you do not have confirmed file hashes or network indicators, do not borrow random indicators from unrelated Chrome incidents. Restricted-detail periods reward disciplined baselining and evidence preservation, not ornamental detection logic.
The practical meaning of KEV for organizations outside government
CISA’s KEV catalog formally binds FCEB agencies to act, but the more important lesson is broader. KEV inclusion signals that the bug has crossed the line from theoretically dangerous to publicly active enough that a major government authority wants remediation tracked with deadlines. That should change private-sector behavior even where no mandate exists. (CISA)
For regulated companies, the KEV angle is also useful for communication with auditors, customers, and internal stakeholders. It gives you a public reference point for why the item bypassed ordinary patch cadences. The story becomes cleaner: vendor-confirmed active exploitation, public KEV inclusion, fixed version available, response verified against running state. That is a much better narrative than “we updated browsers sometime this week.”
Related CVEs that help explain CVE-2026-5281
The most directly relevant neighboring CVEs are the ones in the same March 31 release. Google’s bulletin lists CVE-2026-5284 and CVE-2026-5286 as additional high-severity use-after-free vulnerabilities in Dawn. Their presence in the same patch train tells you that 5281 is part of a broader memory-safety cleanup in the same component, even though the public record does not tell us whether the flaws share a code path or exploit pattern. For defenders, the takeaway is not root-cause speculation. It is that a component with multiple same-cycle UAF fixes deserves aggressive update validation. (Chrome Releases)
The most useful earlier Chrome comparison is CVE-2026-2441. NVD describes that flaw as a use-after-free in Chrome’s CSS component that allowed a remote attacker to execute arbitrary code inside the sandbox via a crafted HTML page, and Google’s February 13, 2026 Stable bulletin documented the fixed versions. The reason it matters here is not because CSS and Dawn are the same subsystem. They are not. It matters because it shows the same broader pattern: Chrome’s 2026 threat picture has continued to include actively exploited memory-safety bugs reachable from crafted web content. The component changed. The weakness class did not. (NVD)
These neighboring CVEs are useful because they teach different lessons.
| CVE | Composant | Weakness class | Why it matters for understanding CVE-2026-5281 |
|---|---|---|---|
| CVE-2026-5284 | Dawn | Use-after-free | Shows 5281 was not the only Dawn UAF fixed in the same release |
| CVE-2026-5286 | Dawn | Use-after-free | Reinforces component density and the need for thorough patch validation |
| CVE-2026-2441 | CSS | Use-after-free | Shows Chrome’s actively exploited 2026 memory-safety pattern extends beyond a single subsystem |
The common lesson is not “everything is broken.” It is narrower and more useful: memory-safety bugs in browser subsystems that handle attacker-controlled web content remain live operational problems, and exploit chains still reward bugs that cross meaningful boundaries.
What this incident says about browser defense going forward
CVE-2026-5281 is a reminder that browser defense is still a layered contest. Sandboxing matters. Process isolation matters. Feature hardening matters. But once a browser exposes a powerful new API to the web, the security burden is not just the JavaScript-visible surface. It is every serialization path, lifetime rule, callback edge case, asynchronous execution path, and native subsystem that sits behind that API. Chromium’s own WebGPU research reads like a direct warning about that reality. (Chromium Git Repositories)
For engineers, the long-term lesson is uncomfortable but straightforward. High-performance, cross-platform, native-code-heavy browser features are where memory-safety debt keeps showing up. That does not mean features like WebGPU should not exist. It means defenders should expect them to remain premium attack surface, and platform teams should keep treating them that way.
For response teams, the lesson is even simpler. The quality bar for browser incident handling should be higher than “patch was released.” A mature response to CVE-2026-5281 answers four questions cleanly: which endpoints were exposed, which endpoints actually crossed the fixed version floor, which endpoints were still running vulnerable builds after the patch, and which lagging systems need closer review for follow-on activity. If your process cannot answer those, your problem is not just this CVE.
For technical buyers and security leads evaluating their workflows, incidents like this also expose whether their tooling helps them prove remediation or merely record intentions. Evidence beats status labels. Running state beats package state. Time-bound verification beats wishful compliance. That is true whether the toolset is EDR, MDM, browser management, or a broader validation platform.
Further reading and references
- Google Chrome Releases, Stable Channel Update for Desktop, March 31, 2026. (Chrome Releases)
- NVD entry for CVE-2026-5281. (NVD)
- CVE.org record for CVE-2026-5281. (CVE)
- CISA Known Exploited Vulnerabilities catalog entry and April 1, 2026 alert. (CISA)
- Chromium WebGPU Technical Report. (Chromium Git Repositories)
- Dawn repository overview. (Dawn Git Repositories)
- Chromium sandbox design documentation. (Chromium Git Repositories)
- Chromium Rule of 2 guidance. (Chromium Git Repositories)
- Chromium severity guidelines for security issues. (Chromium Git Repositories)
- MITRE CWE-416 entry and CWE 2025 rankings context. (CWE)
- CVE-2026-2441 The Chrome CSS Zero-Day You Must Patch and Prove Across the Fleet. (Penligent)
- Chrome Zero-Day Vulnerabilities Exploited in 2025. (Penligent)
- AI Pentest Tool, What Real Automated Offense Looks Like in 2026. (Penligent)
- Penligent homepage. (Penligent)