The Milano Cortina 2026 Winter Olympics put a familiar truth into sharp focus: when an event combines global attention, distributed operations, and real-time digital dependencies, cybersecurity stops being a background IT function and becomes part of the event itself. The Games ran from February 6 to 22, 2026, with a geographically distributed footprint and a large supporting ecosystem of venues, logistics, hospitality, media, sponsors, and public-facing services. (Olympics)
That combination makes 2026 winter olympics cyber security an unusually useful lens for security engineers. It captures a real-world environment where fraud, DDoS, credential theft, supply-chain exposure, and reputation risk all interact at once. It also offers lessons that transfer directly to enterprise launch periods, Black Friday, major conferences, elections, and other high-pressure digital operations.
This article focuses on what matters most for practitioners: current evidence, realistic threat models, priority decisions, and validation strategies. It avoids vague “be careful” advice and emphasizes what teams can actually do before and during a high-visibility event.
2026 Winter Olympics Cyber Security Threat Landscape in Milano Cortina
Public reporting and official commentary already show that the threat environment around Milano Cortina 2026 was not hypothetical. The World Economic Forum described the Games as a high-value cyber target because of their visibility and complex digital infrastructure, highlighting risk categories spanning criminal activity, hacktivism, and AI-amplified disruption. (הפורום הכלכלי העולמי)
Reuters reported a coordinated scam campaign involving fake websites impersonating the official Milano Cortina 2026 merchandise store, promoted through deceptive ads and designed to harvest payment and personal information. Reuters’ reporting, citing Bitdefender, noted near-identical branding, steep discount lures, and rapidly rotating domains. (רויטרס)
Separately, Reuters and AP also reported on broader security preparations and claims of thwarted cyberattacks around Olympics-related targets in Italy, including references to a 24-hour cybersecurity command center and statements by Italian officials regarding cyberattack attempts. (רויטרס)
For defenders, this is the key point: the cyber risk picture around the Games is not just a story about elite intrusion sets. It includes the full spectrum of attack types that exploit public attention and operational complexity.

2026 Winter Olympics Cyber Security Keyword Cluster and Search Intent
For this topic, the most useful keyword strategy is not a single phrase, but a cluster that maps to how practitioners search during active events. Public search results do not reveal Google’s private CTR data, so no one can honestly claim exact “highest-click” query rankings from public browsing alone. What הוא observable is query relevance, recency, and SERP prominence.
The strongest cluster around 2026 winter olympics cyber security typically includes:
- 2026 winter olympics cyber security
- milano cortina 2026 cyber security
- winter olympics cyber attacks
- olympic cybersecurity threats 2026
- milano cortina fake merchandise scam
- winter olympics phishing scams
- olympic ddos attack risk
- olympic hacktivism 2026
- olympics vendor supply chain cyber risk
- olympic destroyer malware
- travel scam olympics cybersecurity
- fake olympic store websites
This keyword set aligns with what recent coverage has emphasized: high-value targeting, scams/fraud, geopolitical cyber risk, and operational resilience. (הפורום הכלכלי העולמי)
If your goal is to reach security engineers rather than casual readers, the article should answer four implicit questions behind those searches:
- What is already happening
- What is likely next
- What should I prioritize first
- How do I verify controls under time pressure
That is the structure used in the rest of this article.
Milano Cortina 2026 Expands the Attack Surface by Design
The Milano Cortina Games are operationally distributed, not centralized. The official Olympics pages and news coverage highlight a multi-location event footprint and a timeline spanning multiple venues and support systems. (Olympics)
This matters because distributed events create predictable defensive friction:
- Different venues and operators run different local processes
- Temporary systems coexist with long-lived production systems
- Third-party vendors must be onboarded quickly
- Identity and access rules are often relaxed for speed
- Public services must remain usable under traffic spikes
- Brand visibility increases the ROI of scams and imitation
The result is an environment where “minor” weaknesses become strategically valuable. Attackers do not need a spectacular exploit chain if they can profit from fake stores, credential theft, or timed outages during moments of peak attention.
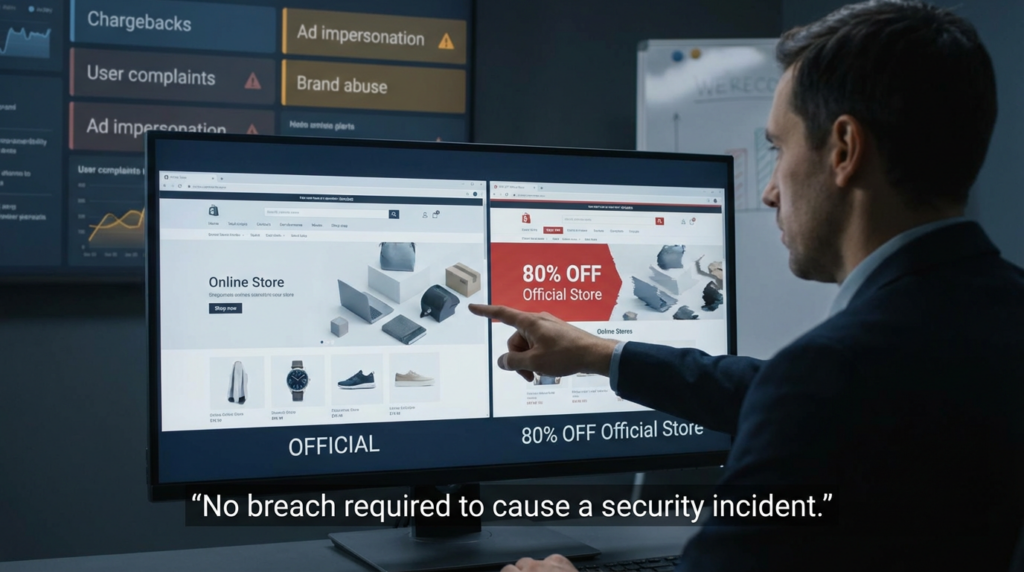
Fraud and Brand Abuse Were Not Secondary Risks in 2026
The Reuters report on fake Milano Cortina 2026 merchandise sites is one of the most practically important data points for defenders because it demonstrates a recurring event-time pattern: brand trust gets monetized faster than technical complexity. Reuters reported that the scams used near-identical imagery and branding, promoted via deceptive ads on Meta platforms, with discounts reportedly as high as 80%. (רויטרס)
For a security team, this is not just a “consumer awareness” issue. It is an operational issue that crosses multiple functions:
- Fraud loss and chargebacks
- Customer support load
- Brand reputation damage
- Credential reuse risk if users enter login credentials on fake sites
- Abuse reporting and takedown coordination
- Communications and legal response timing
In other words, fraud campaigns can become a cybersecurity incident even when no production server is “hacked.”
A mature response plan for this class of threat should include:
- Domain and ad-abuse monitoring
- Pre-approved takedown workflows
- Customer warning banners and FAQs
- Payment/fraud team coordination
- Telemetry sharing between support, trust & safety, and security
- Rapid publication of official domain and shop URLs
When teams treat fraud and security as separate silos, attackers exploit the handoff gap.
DDoS and Availability Risk in Olympic-Scale Events
The Olympic context also matters because it creates ideal conditions for DDoS and service degradation attacks: large audiences, predictable peaks, public dashboards, and low tolerance for latency.
Cloudflare’s Paris 2024 Olympics reporting provides a valuable recent benchmark. Cloudflare documented major DDoS activity tied to Olympic-related sites, including a reported peak HTTP DDoS intensity of 190,000 requests per second, and a higher spike over 500,000 requests per second against a French transportation site on the final day. (Cloudflare Radar)
Cloudflare’s related blog reporting also noted a surge in blocked DDoS requests targeting Olympic partner websites, with traffic concentrated around the event period. (The Cloudflare Blog)
These observations matter for 2026 winter olympics cyber security because they shift the conversation from abstract “DDoS may happen” statements to operational planning questions:
- What public endpoints must stay available at all costs?
- What can degrade gracefully?
- Which systems need static fallback pages?
- How fast can DNS/CDN/WAF changes be deployed?
- Which alerts indicate real degradation versus noisy bursts?
- Can customer support operate if the primary portal is unstable?
The most expensive mistake is waiting for a complete outage before invoking the DDoS playbook. Many event-time attacks are short, bursty, and timed for maximum confusion rather than sustained downtime. Cloudflare’s data supports that framing. (Cloudflare Radar)
Hacktivism, Geopolitical Context, and Public-Effect Attacks
Olympic events are symbolic targets. That does not mean every incident is nation-state activity, but it does mean defenders need to plan for attacks that prioritize public effect over stealth.
Unit 42’s public analysis on the 2026 Winter Olympics discussed the possibility of increased cyberthreats in the context of Russia’s isolation from the Olympic movement and broader geopolitical dynamics. (Unit 42) The World Economic Forum article also emphasizes that threats may range from criminal ransomware to hacktivism, and that AI can increase both the sophistication and scale of potential attacks. (הפורום הכלכלי העולמי)
Practically, this changes defensive priorities. Teams should prepare not only for compromise, but for claim-based and perception-based incidents, such as:
- Public claims of data leaks before evidence is verified
- Defacement or partial content manipulation
- Short-lived disruptions amplified on social media
- Impersonation accounts and fake statements
- Coordinated disinformation tied to genuine minor incidents
This is where technical response and communications response must be synchronized. A technically small issue can become a major incident if public messaging lags behind rumor cycles.
Historical Olympic Cybersecurity Incidents Still Shape 2026 Defenses
Even if your current focus is Milano Cortina 2026, historical Olympic incidents provide the best map of what tends to matter operationally.
PyeongChang 2018 and Olympic Destroyer
The 2018 Winter Olympics remain central to Olympic cyber discussions because the “Olympic Destroyer” malware campaign demonstrated how disruptive operations can target event infrastructure under maximum visibility. The WEF recap references disruption to IT systems and a temporary website outage around PyeongChang. (הפורום הכלכלי העולמי)
The enduring lessons are straightforward:
- Short timing windows can produce outsized impact
- Operational disruption is often the real objective
- Recovery speed matters more than perfect attribution in the first hours
Tokyo 2020 and the scale of blocked activity
NTT reported that Tokyo 2020 experienced 450 million blocked security events during the Games and stated there were no cyber incidents affecting operations. (NTT)
This is useful because it reminds teams that a successful defense often looks quiet externally, even when attack traffic is immense internally.
Beijing 2022 and broad threat categories
The FBI’s January 2022 PIN warned that entities associated with the Beijing Winter Olympics and Paralympics could face a wide range of malicious cyber activities, including DDoS, ransomware, malware, social engineering, phishing, data theft or leaks, and insider threats. (Internet Crime Complaint Center)
That taxonomy still maps cleanly onto 2026 event security planning. If anything, the fraud and brand-abuse portions have become more urgent because ad ecosystems, cloning workflows, and AI-assisted content generation lower the cost of running convincing scams.
The Threat Model That Actually Helps Security Engineers
שימושי 2026 winter olympics cyber security model should organize risk by likely business impact and defender response paths, not by buzzwords. Below is a practical breakdown.
Brand impersonation and fake commerce infrastructure
This category includes fake merchandise stores, fake ticketing pages, fake travel bundles, fake hospitality offers, and fake support channels. Reuters’ report on fake Milano Cortina shops is the clearest current example. (רויטרס)
What makes it dangerous
- Fast monetization
- High social-ad reach
- Strong brand trust exploitation
- Support and legal escalation burden
- Spillover into credential theft and chargebacks
What teams miss
- Treating it as “marketing’s problem”
- No prebuilt takedown path
- No official URL verification page
- No coordinated customer messaging
Credential theft and account takeover
Olympic-scale operations involve staff, vendors, contractors, media, and volunteers. Temporary accounts and rushed provisioning increase risk. The FBI’s broad warning categories remain relevant here, especially phishing and social engineering. (Internet Crime Complaint Center)
What makes it dangerous
- Credential theft can bypass perimeter controls
- Vendor accounts may be less monitored
- MFA fatigue and helpdesk social engineering rise under pressure
What teams miss
- Focusing only on employee identities
- Weak monitoring on vendor/partner SSO tenants
- Lack of “impossible travel + role sensitivity” triage rules
DDoS and service degradation
Public portals, streaming-related services, support pages, and transport information systems are all attractive targets because they are visible and time-sensitive. Cloudflare’s Olympic-related observations in 2024 underscore this pattern. (Cloudflare Radar)
What makes it dangerous
- Timing amplifies impact
- Partial degradation may still trigger reputational damage
- Small organizations in the partner ecosystem may be less protected
What teams miss
- No fallback content path
- DDoS plans built only for total outage
- Overly noisy alerting during high traffic
Supplier and third-party integration risk
The WEF framing of Olympic-scale complexity is directly relevant here: multiple suppliers, apps, and services create trust dependencies that extend beyond the organizing committee. (הפורום הכלכלי העולמי)
What makes it dangerous
- Attackers target the weakest trusted node
- Revoking access can disrupt operations
- Ownership boundaries are often unclear during incidents
What teams miss
- Excess API privileges
- Stale credentials
- Weak separation of admin and operational access
- No tested vendor offboarding during live operations
Public-effect cyber incidents and hacktivism
Even minor technical incidents can be amplified into perceived systemic failures. That is why teams need comms and evidence discipline in addition to technical controls. (Unit 42)
What makes it dangerous
- Narrative spreads faster than technical forensics
- Screenshots and claims may circulate before validation
- Pressure to respond can cause factual errors
What teams miss
- No incident communications template for unverified claims
- No content integrity baseline
- Slow internal approval loops
Relevant CVEs for 2026 Winter Olympics Cyber Security Planning
You asked for CVEs that are recent, influential, and relevant to real security engineering work. For this topic, the most useful choices are vulnerabilities that affect edge devices, management planes, and mobile device management—the places where trust is established and amplified.
This section is defensive by design: it focuses on prioritization and validation, not weaponization.
CVE-2026-24858 Fortinet FortiCloud SSO authentication bypass
NVD describes CVE-2026-24858 as an authentication bypass vulnerability affecting multiple Fortinet products, where an attacker with a FortiCloud account and a registered device may be able to log into devices registered to other accounts if FortiCloud SSO is enabled. (NVD)
Fortinet’s PSIRT advisory confirms the issue scope and remediation context. (fortiguard.com)
Why it matters in an event-scale environment:
- Edge and management products are common in distributed operations
- SSO assumptions often underpin administrative trust
- Temporary exceptions and rapid provisioning increase misconfiguration risk
- Cross-account access flaws can expand blast radius beyond a single admin session
Defender priority:
- Inventory affected products and versions
- Confirm FortiCloud SSO usage
- Patch/upgrade per vendor guidance
- Restrict administrative exposure paths
- Validate remediation by testing access boundaries and account isolation
CVE-2026-1281 Ivanti EPMM unauthenticated RCE
NVD describes CVE-2026-1281 as a code injection in Ivanti Endpoint Manager Mobile (EPMM) enabling unauthenticated remote code execution. (NVD) Rapid7 reported that Ivanti disclosed CVE-2026-1281 and CVE-2026-1340 together, and that exploitation had occurred in the wild prior to disclosure; Rapid7 also noted CISA KEV action. (Rapid7)
Why it matters in an event-scale environment:
- Mobile device management is often part of staff and contractor operations
- MDM exposure can affect downstream trust in devices and policies
- Time pressure encourages “temporary” admin workarounds that become persistent risk
Defender priority:
- Identify all exposed EPMM instances
- Patch immediately per Ivanti guidance
- Restrict management interfaces and admin access paths
- Hunt for signs of exploitation and persistence
- Revalidate enrollment and policy integrity after remediation
CVE prioritization principle for large events
The lesson is not “patch everything equally.” The lesson is to prioritize vulnerabilities that affect:
- identity trust
- management planes
- internet-facing administration
- mobile device trust
- core traffic routing or policy enforcement
Those systems determine whether other controls are trustworthy.
Threat Prioritization Table for 2026 Winter Olympics Cyber Security Operations
Below is a practical matrix teams can reuse for Olympics-like environments.
| Threat scenario | Early symptom | טעות נפוצה | Minimum viable control | Validation method |
|---|---|---|---|---|
| Fake merchandise / ticket site | Customer complaints, chargebacks, social mentions | Treating it as marketing-only | Brand/domain monitoring + takedown path + official URL page | Measure discovery-to-takedown and support response time |
| Credential phishing / ATO | MFA prompts, login failures, unusual geos | Monitoring only employee accounts | Risk-based auth + vendor account monitoring + MFA fatigue controls | Controlled phishing exercise + login anomaly tuning |
| DDoS on public portals | Latency spikes, intermittent 5xx, support surge | Waiting for total outage | CDN/WAF protections + fallback static pages + routing runbook | Burst load test + failover drill |
| Vendor/API compromise | Subtle workflow anomalies | Assuming vendor SOC coverage is enough | Least privilege + key rotation + segmented access | Test token revocation and privilege boundaries |
| Defacement / leak claim | Social post before internal alert | Responding publicly before validation | Integrity checks + evidence triage + comms template | Tabletop with simulated false/partial claim |
| MDM / management plane exploit | Admin anomalies, unexpected changes | Treating mobile admin as separate from core security | Patch priority + admin isolation + restricted exposure | Patch verification + access path validation |
This table is intentionally operational. The goal is to turn threat awareness into decisions.

Detection and Monitoring Patterns That Matter During Event Windows
The problem during event periods is not just volume. It is signal collapse: too many alerts, too many stakeholders, too little time. Monitoring needs to be tuned for scenarios that matter.
Identity monitoring priorities
- Repeated failures followed by success
- New country / ASN for privileged or vendor accounts
- Sudden spikes in password reset/helpdesk requests
- MFA push fatigue patterns
- Admin portal access outside expected windows
Application and edge monitoring priorities
- Short bursts in request rate with elevated error codes
- Sudden cache bypass patterns on public pages
- Traffic spikes to login, checkout, or support endpoints
- DNS changes outside change windows
- WAF rule changes and disablements
Fraud and brand abuse monitoring priorities
- Newly registered domains with brand-like strings
- Social ads using official-like branding
- Phishing kits impersonating login/support pages
- User reports mentioning “discount,” “official sale,” “urgent verification”
These categories map directly to what recent reporting has shown around Milano Cortina-related scams and what prior Olympic periods have shown around high-volume attack activity. (רויטרס)
Defensive Automation Examples for Security Teams
The examples below are for defense operations and triage. They are designed to help teams detect and prioritize risk faster, not exploit systems.
Python example for suspicious brand-domain triage
This script scores suspicious domains for manual review based on brand keywords and common scam naming patterns.
import re
from urllib.parse import urlparse
BRAND_TERMS = ["milano", "cortina", "olympic", "winter", "games", "2026"]
SUSPICIOUS_TLDS = {".shop", ".top", ".xyz", ".click", ".live"}
PROMO_PATTERNS = [
r"official.*sale",
r"80off|70off|90off",
r"cheap|discount|clearance",
r"tickets?-vip",
]
ALLOWLIST = {
"olympics.com",
"milanocortina2026.org",
}
def host_only(value: str) -> str:
if "://" in value:
value = urlparse(value).netloc
return value.lower().split(":")[0].strip()
def score_domain(host: str):
score = 0
reasons = []
if host in ALLOWLIST:
return {"host": host, "risk": "allowlisted", "score": 0, "reasons": ["known official domain"]}
if any(term in host for term in BRAND_TERMS):
hits = [t for t in BRAND_TERMS if t in host]
score += len(hits) * 2
reasons.append(f"brand terms: {', '.join(hits)}")
if any(re.search(p, host) for p in PROMO_PATTERNS):
score += 3
reasons.append("promo/scam-like wording")
if host.count("-") >= 3:
score += 2
reasons.append("many hyphens")
if sum(ch.isdigit() for ch in host) >= 4:
score += 1
reasons.append("many digits")
if any(host.endswith(tld) for tld in SUSPICIOUS_TLDS):
score += 2
reasons.append("high-risk TLD for impersonation")
risk = "low"
if score >= 8:
risk = "high"
elif score >= 4:
risk = "medium"
return {"host": host, "risk": risk, "score": score, "reasons": reasons}
if __name__ == "__main__":
samples = [
"milanocortina2026.org",
"milano-cortina-official-sale-80off.shop",
"olympic-tickets-vip-clearance.xyz",
"wintergames2026deals.top",
"olympics.com",
]
for s in samples:
print(score_domain(host_only(s)))
How to use it well:
- feed from passive DNS, brand monitoring feeds, SOC tickets, or user reports
- route medium/high scores to manual review
- link confirmed hits to takedown and customer warning workflows
- measure “time to verification” and “time to action”
This approach is useful because Reuters described scam infrastructure that was short-lived and fast-rotating, where response speed is part of defense quality. (רויטרס)
Sigma example for repeated login failures followed by success
This pattern is common during event windows when phishing and credential attacks increase.
title: Event Window Suspicious Success After Multiple Failures
id: 2e0f53bd-9d16-4a6b-9f6e-olympic-auth-pattern
status: experimental
description: Detects a successful sign-in after repeated failures from the same source within a short interval
logsource:
product: identity
category: authentication
detection:
failed:
outcome: failure
success:
outcome: success
timeframe: 10m
condition: count(failed by user, src_ip) >= 5 followed_by success by user, src_ip within 10m
fields:
- user
- src_ip
- user_agent
- geo
falsepositives:
- user mistyped password multiple times
- password reset workflows
level: high
tags:
- attack.credential_access
- attack.t1110
A stronger deployment narrows the rule to:
- privileged roles
- vendor accounts
- accounts that can modify content, DNS, ads, or communications
KQL example for identity anomaly triage during event dates
let EventStart = datetime(2026-02-06);
let EventEnd = datetime(2026-02-22);
SigninLogs
| where TimeGenerated between (EventStart .. EventEnd)
| summarize
Failed=countif(ResultType != 0),
Success=countif(ResultType == 0),
DistinctIPs=dcount(IPAddress),
DistinctCountries=dcount(LocationDetails.countryOrRegion)
by UserPrincipalName, bin(TimeGenerated, 1h)
| where Failed >= 10 or DistinctCountries >= 2
| order by TimeGenerated desc
A practical refinement is to join this with a table of privileged users and vendor identities first, because event periods produce lots of benign noise from ordinary user behavior.
Control Validation Is the Difference Between Confidence and Resilience
A recurring failure pattern in high-pressure security operations is assuming that a control exists because a project says it exists. In practice, event-time risk accumulates in the gaps:
- a WAF rule exists but is not attached to the critical route
- MFA is enforced for employees but not vendor admins
- a takedown process exists but legal approval takes too long
- a patch was applied but exposure paths remain reachable
- a “temporary exception” becomes the default under pressure
That is why validation matters at least as much as implementation.
A practical validation checklist for event windows should include:
- Can a critical public endpoint degrade gracefully without breaking core user actions?
- Can you revoke a vendor/API token in minutes and restore service safely?
- Are admin interfaces reachable only from approved paths?
- Do log pipelines remain usable during burst traffic?
- Can support teams quickly identify and point users to official domains?
- Can comms publish a cyber incident holding statement within one approval cycle?
Teams that rehearse these questions are usually more resilient than teams that simply have more tools.
הפניות
- World Economic Forum on Milano Cortina 2026 as a prime cyber target (הפורום הכלכלי העולמי)
- Reuters on fake Milano Cortina merchandise scam sites and deceptive ads (רויטרס)
- Reuters on Italy’s Olympics security plan and 24-hour cybersecurity command center (רויטרס)
- AP reporting on Italian officials’ statements about thwarted cyberattacks against Olympics-related sites (AP News)
- Cloudflare Radar Paris 2024 Olympics DDoS observations (Cloudflare Radar)
- Cloudflare Olympics recap blog on attack surges during Paris 2024 (The Cloudflare Blog)
- FBI IC3 PIN on malicious cyber activities related to the Beijing Winter Olympics and Paralympics (Internet Crime Complaint Center)
- NTT Tokyo 2020 cybersecurity results (including blocked event volume) (NTT)
- NVD CVE-2026-24858 (Fortinet FortiCloud SSO auth bypass) (NVD)
- Fortinet PSIRT advisory for CVE-2026-24858 (fortiguard.com)
- NVD CVE-2026-1281 (Ivanti EPMM unauthenticated RCE) (NVD)
- Rapid7 analysis of Ivanti EPMM CVE-2026-1281 / CVE-2026-1340 exploitation and KEV action (Rapid7)
- Unit 42 analysis on cyberthreat context for the 2026 Winter Olympics (Unit 42)
- Penligent Hacking Labs (hub)
- Partial Prerendering and the Security Reality Behind the Performance Hype
- Claude Code Security and Penligent: From White-Box Findings to Black-Box Proof
- Exploit DB in 2026
- Overview of Penligent.ai’s Automated Penetration Testing Tool