This article is written for people who ship production React/Next.js systems and want the truth in operational terms: what’s vulnerable, what “exploited in the wild” actually means here, how to patch and verify quickly, and how to build defenses that still hold when the next RSC parsing bug drops.
What React2Shell actually is, the bug lives where Flight meets Server Functions
React Server Components introduced a different client–server contract than traditional SPA rendering. Instead of shipping everything to the browser, the server can render components and stream structured data back to clients. The mechanism is commonly referred to as the React Flight protocol: clients send serialized “chunks” representing component trees and references, and servers reassemble and interpret those chunks for server-side execution and rendering. (www.trendmicro.com)
According to the React team, an unauthenticated attacker could craft a malicious HTTP request to a Server Function endpoint that, when deserialized by React, results in remote code execution on the server. (להגיב)
NVD’s description aligns with this: the vulnerable code path unsafely deserializes payloads from HTTP requests to Server Function endpoints in certain React Server Components package versions. (NVD)
That detail matters: this is not “someone found a weird edge-case in a UI library.” It’s a failure at the boundary where untrusted network input becomes trusted execution semantics.
The CVE map, CVE-2025-55182 is the anchor and the rest is the blast radius
CVE-2025-55182 is the primary identifier
Most official and vendor writeups center on CVE-2025-55182 as the core issue impacting React Server Components. (NVD)
CVE-2025-66478, why you still see it in posts and tools
You’ll also see CVE-2025-66478 referenced as “the Next.js React2Shell CVE.” Next.js published an advisory under that ID and recommended running תיקון npx-react2shell-next. (Next.js)
However, multiple threat research sources note that CVE-2025-66478 was later treated as a duplicate of CVE-2025-55182 (the Next.js side was merged into the React-side tracking). (יחידה 42)
Operationally: don’t get stuck arguing about numbering. Treat “React2Shell” alerts that mention either ID as the same crisis, and follow the official patched-version guidance.
Related vulnerabilities that got disclosed after the spotlight hit RSC
After React2Shell’s disclosure, React published updates noting additional vulnerabilities and update instructions, including:
- CVE-2025-55184 ו CVE-2025-67779 (DoS, high severity)
- CVE-2025-55183 (source code exposure, medium severity)
- CVE-2026-23864 (DoS, high severity, added in later update) (להגיב)
This pattern is common: once a high-impact, high-visibility parsing boundary is found, it draws immediate scrutiny—and the “one CVE” becomes a family of adjacent weaknesses.
Who is affected, a production-minded checklist
React2Shell risk is not evenly distributed across “all React apps.” Your exposure depends on whether your application accepts and processes RSC/Server Function requests on the server.
Use this checklist:
- Do you run React Server Components in production If you’re using Next.js App Router with Server Components and Server Actions, or any framework implementing RSC server-side handling, you’re in the higher-risk group. React2Shell is explicitly described as impacting React Server Components and frameworks like Next.js. (מיקרוסופט)
- Are vulnerable RSC packages present at runtime NVD lists affected React Server Components packages such as
react-server-dom-*packages in specific version ranges. (NVD) - Is the service reachable from the internet The most common exploitation path described across advisories is an attacker sending a crafted HTTP request to a Server Function endpoint. If your app is internet-facing, assume it’s being scanned.
- Are you running Node.js server runtime Some research notes exploitation targeting server-side runtime behavior; if you deploy on Node, treat this as urgent. (Don’t assume edge runtime saves you without verifying your exact architecture and vendor guidance.) (www.trendmicro.com)
If you’re unsure whether your application exposes Server Function endpoints, assume a motivated attacker can find them faster than your team can “reason about routes.”
Exploitation in the wild, what defenders can safely learn without weaponizing it
A lot of content online about React2Shell drifted into either panic or irresponsible “copy-paste exploitation.” You don’t need either to defend.
Trend Micro’s technical analysis summarizes the exploit as a multi-stage attack chain that ultimately reaches arbitrary code execution, and also emphasizes the chaotic PoC landscape—many “tools” being shared are low quality, fake, or backdoored. (www.trendmicro.com)
Cloudflare and Censys advisories also describe the vulnerability mechanism at a high level: insecure deserialization within the Flight protocol / Server Function handling, exploited via crafted HTTP requests. (The Cloudflare Blog)
The defender takeaway:
- You are dealing with a network-to-execution boundary failure.
- Attackers can vary payload formatting.
- A naive signature like “block
__proto__” is not a strategy; it’s a bet. Trend Micro explicitly calls out common misconceptions that lead to ineffective defenses. (www.trendmicro.com)
Why this became a crisis, “one request RCE” changes the math
In the real world, “critical” isn’t a CVSS number; it’s the combination of blast radius and attacker economics.
Multiple major threat intelligence and security vendor reports describe React2Shell as:
- pre-auth, low-friction, single-request RCE (economical to scan) (מיקרוסופט)
- widely relevant due to adoption of RSC in modern stacks (ענן גוגל)
- rapidly exploited after disclosure, including by multiple actor types, from financially motivated groups to nation-state aligned clusters (ענן גוגל)
Once scanning tooling hits underground channels, the time between “public advisory” and “mass probing” compresses to hours or days—not weeks.
Immediate remediation, patching is non-negotiable and there is no safe workaround
Step 1 — Patch to officially listed versions
React’s official guidance provides concrete version upgrade instructions for Next.js release lines (multiple next@... versions depending on your track). (להגיב)
Next.js’ advisory states bluntly: there is no workaround—upgrading to a patched version is required, and it recommends running an interactive tool to bump dependencies deterministically. (Next.js)
Step 2 — Use the official “fix” tooling where it fits your workflow
Vercel maintains תיקון-react2shell-next, designed to bump your Next.js / RSC dependency set to align with official advisories via a single command (תיקון npx-react2shell-next). (GitHub)
That tool is not magic; it’s a guardrail against teams accidentally landing on an “almost patched” state where Next is upgraded but a vulnerable transitive dependency remains.
Step 3 — Rotate secrets after redeploying
Next.js’ advisory also recommends rotating application secrets after patching and redeploying. (Next.js)
If an attacker got code execution, assume environment variables and service tokens were within reach.
A practical patch workflow you can run today
Below is an intentionally defensive workflow that avoids exploit content and focuses on what teams actually do under pressure.
# 1) Inventory the deployed versions
node -v
npm ls react react-dom next react-server-dom-webpack react-server-dom-turbopack react-server-dom-parcel
# 2) Apply official upgrades (example only — use React/Next official matrix for your release line)
npm install next@latest
npm install react@latest react-dom@latest
# 3) If you use Next.js App Router / RSC, run the official helper
npx fix-react2shell-next
# 4) Rebuild and redeploy
npm run build
# 5) After deploy, rotate secrets (platform-specific)
# - rotate CI/CD secrets
# - rotate cloud keys
# - rotate DB passwords if any chance of exposure
Notes:
- Follow the exact version matrix from React’s advisory for your Next.js track, not “latest” blindly, if you are pinned to a release line. (להגיב)
- If you depend on canary releases or specialized features, the Next.js advisory describes specific canary guidance and downgrade options. (Next.js)
Version and CVE reference table you can hand to your on-call
| פריט | מה זה | מדוע זה חשוב | What to do |
|---|---|---|---|
| CVE-2025-55182 | React Server Components pre-auth RCE | Unsafe deserialization of attacker input to Server Function endpoints | Patch per React advisory and verify transitive deps (NVD) |
| CVE-2025-66478 | Next.js-tracked identifier often used for React2Shell | Treated as duplicate/merged into CVE-2025-55182 in some reports | Treat alerts as same incident, follow Next.js guidance (יחידה 42) |
| תיקון-react2shell-next | Official helper tool from Vercel | Prevents “partial patch” and bumps deterministically | לרוץ תיקון npx-react2shell-next in affected repos (GitHub) |
| CVE-2025-55183 | Source code exposure, medium severity | RSC handling edge-cases can leak server function code | Patch and reduce exposure surface (להגיב) |
| CVE-2025-55184, CVE-2025-67779 | DoS, high severity | Attackers can degrade availability without full RCE | Patch and add rate limiting/WAF controls (להגיב) |
| CVE-2026-23864 | DoS added in later update | Shows ongoing scrutiny around the boundary | Keep dependencies current, watch advisories (להגיב) |
Detection and monitoring, what to look for without chasing brittle signatures
1) WAF and edge-layer controls
Cloudflare published a threat brief that includes protections and references to related vulnerabilities and detection approaches. (The Cloudflare Blog)
The key idea: you’re not trying to “regex your way out” of a parsing boundary flaw. You’re buying time while patching, and you’re improving signal to spot probing and exploitation attempts.
Practical controls:
- Rate-limit requests to Server Function endpoints and any routes that handle action payloads
- Enforce allowlists for content types and request sizes where feasible
- Alert on anomalous POST bursts to action endpoints from new IP ranges
2) Log-driven suspicious pattern hunting
Trend Micro includes a section on “payload structure” and traffic patterns at a high level, plus IOC guidance and warns about misinformation and fake tools. (www.trendmicro.com)
You can implement safe, generalized hunting queries around:
- bursts of POSTs to action/function endpoints
- unusual headers that appear in Server Action workflows
- unexpected multipart uploads to internal action endpoints
Example pseudo-detections (adapt to your stack). These are not exploit rules; they are anomaly-based filters:
-- Example: suspicious POST bursts to server-action endpoints (generic)
SELECT
ip,
COUNT(*) AS hits,
MIN(ts) AS first_seen,
MAX(ts) AS last_seen
FROM access_logs
WHERE method = 'POST'
AND (
path LIKE '/api/%action%' OR
path LIKE '/_next/%' OR
path LIKE '%server%function%'
)
AND ts > NOW() - INTERVAL '24 HOURS'
GROUP BY ip
HAVING COUNT(*) > 200
ORDER BY hits DESC;
# Example: high-level SIEM filter idea (pseudo Sigma-like)
title: Suspicious POST Activity to RSC or Server Action Routes
logsource:
category: webserver
detection:
selection:
method: "POST"
path|contains:
- "/_next/"
- "/api/"
condition: selection
level: medium
Once you find suspicious clusters, pivot to:
- processes spawned by the web runtime
- outbound connections from the server
- newly written binaries/scripts in tmp/work directories
- unexpected cron/systemd entries
3) Incident response checklist
| שלב | מטרה | Actions |
|---|---|---|
| Triage | Determine exposure and urgency | Confirm whether RSC/Server Functions are used, check versions, check internet exposure (NVD) |
| Containment | Stop further compromise | Patch immediately, add temporary WAF/rate limiting, isolate suspicious hosts (Next.js) |
| Eradication | Remove attacker persistence | Hunt for miners/remote tools/tunnels, rotate secrets, redeploy clean images (Next.js) |
| Recovery | Restore service safely | Validate dependencies, monitor for repeat probes, tighten endpoint exposure |
| Postmortem | Prevent repeat | Add SBOM checks, pin dependencies, improve route inventory, tabletop RSC parsing incidents |
Don’t get owned by the “PoC economy,” fake scanners are part of the attack surface
One of the most useful and under-discussed points in the best technical writeups is not about payload mechanics—it’s about defender operational risk.
Trend Micro documents a large, messy ecosystem of public “PoCs” and scanning tools, and explicitly warns that fake or backdoored tooling can cause:
- false sense of safety
- credential theft
- supply chain compromise of your scanning infrastructure
- attacker reuse of your target lists (www.trendmicro.com)
For teams under time pressure, the rule is simple:
- Prefer official vendor tooling (
תיקון-react2shell-next) and reputable providers. - If you must use third-party scanners, review code, run in isolated environments, and never feed them production credentials or proprietary target lists.
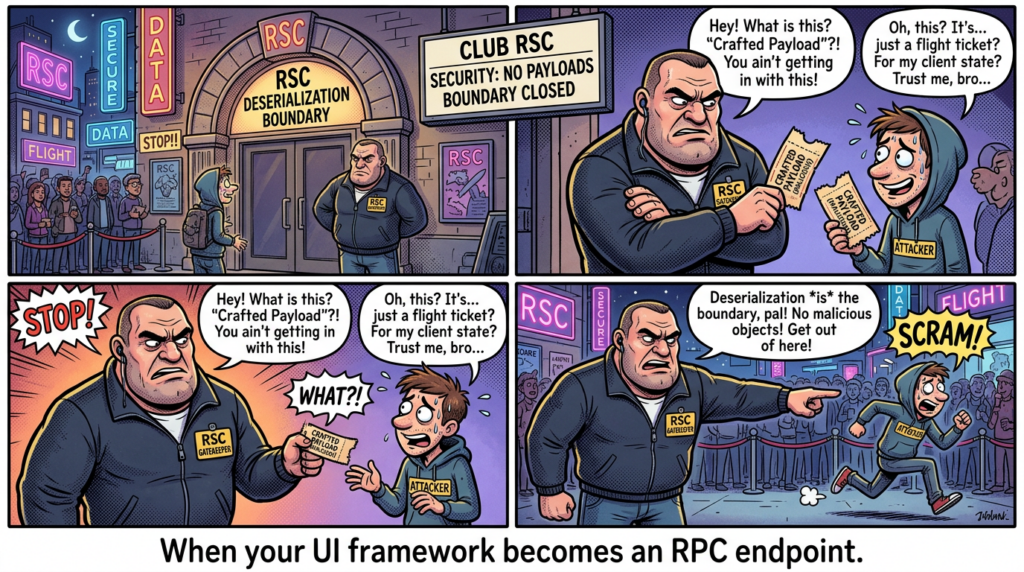
Hardening beyond patching, treat RSC like an RPC layer with real blast radius
React2Shell is a reminder that “UI framework” is no longer a client-only concern. RSC makes the UI layer a server-executed substrate, which means it inherits the same engineering discipline you’d apply to RPC endpoints.
Here are durable improvements that still matter after you patch:
- Minimize exposed Server Function endpoints Maintain an inventory of routes that accept server-action-like payloads. If you can’t name them, you can’t protect them.
- Layered controls around parsing boundaries WAF + rate limiting + request normalization buys time, but must not replace patching. (The Cloudflare Blog)
- Dependency governance that matches the new reality RSC vulnerabilities aren’t “just React.” They involve the ecosystem: framework glue code, bundlers, server runtime, and transitive dependencies. React’s own post-disclosure updates listing additional CVEs underscores ongoing surface area. (להגיב)
- Build repeatable verification into CI Add a pipeline step that fails builds on known vulnerable versions (using a reputable vulnerability database feed and lockfile checks).
Example: a lightweight lockfile gate (illustrative) that prevents deployments with known-bad package versions.
// check-lock.js (illustrative policy gate, not a full scanner)
import fs from "fs";
const lock = fs.readFileSync("package-lock.json", "utf8");
const deny = [
"react-server-dom-webpack@19.2.0",
"react-server-dom-turbopack@19.2.0",
"react-server-dom-parcel@19.2.0"
];
const found = deny.filter(x => lock.includes(x));
if (found.length) {
console.error("Blocked deploy: vulnerable packages detected:", found);
process.exit(1);
}
console.log("OK: no denylisted packages found.");
You should replace the denylist with the exact affected ranges from official sources and your own policy system; the point is to encode “never again” into automation, not into tribal memory.
React2Shell incidents tend to expose a gap in many teams’ workflows: patching is easy to say and painful to verify across a real organization with dozens of services, CI pipelines, canary tracks, and multiple hosting platforms.
Penligent, an AI-driven penetration testing platform, is most useful here in two places:
ראשית, exposure discovery. Teams often don’t have a clean inventory of which services actually expose Server Function endpoints. That becomes especially true in microservice frontends, multi-tenant Next.js deployments, and “it’s just a marketing site” stacks that quietly evolved into complex server-rendered apps. A structured, repeatable recon workflow can quickly surface externally reachable endpoints that deserve urgent review.
שנית, remediation validation. After you patch, you still need confidence that:
- the vulnerable dependency chain is gone in the deployed artifact
- the risky endpoints are not accepting unexpected request patterns
- monitoring is catching residual probing
Used correctly, automated security workflows reduce the “we upgraded, hope it’s fine” phase and replace it with evidence.
What people are most likely clicking when they search react2shell cve, and the consensus you can trust
If you look at the most consistently referenced and widely circulated sources for React2Shell, a few titles dominate because they answer on-call questions directly:
- React’s official advisory and updated patch matrix (להגיב)
- Next.js security advisory and the “no workaround” statement, plus the fix tool (Next.js)
- Vendor threat briefs that confirm exploitation and provide defensive guidance (Microsoft, Cloudflare, Google Threat Intelligence, Trend Micro, Unit 42) (מיקרוסופט)
Across those sources, the consensus is unusually consistent:
- patch quickly to known-safe versions, 2) assume rapid scanning and exploitation, 3) rotate secrets after redeploy, 4) use layered monitoring and WAF/rate limiting to reduce risk while patching, 5) don’t trust random PoCs.
That’s the operational truth. Anything promising “one header block fixes it” is noise.
Links
React official advisory (patch matrix and updates) https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components
NVD entry for CVE-2025-55182 https://nvd.nist.gov/vuln/detail/CVE-2025-55182
Next.js security advisory for CVE-2025-66478 and fix tool guidance https://nextjs.org/blog/CVE-2025-66478
Vercel official fix tool repository https://github.com/vercel-labs/fix-react2shell-next
Cloudflare threat brief on React2Shell and related RSC vulnerabilities https://blog.cloudflare.com/react2shell-rsc-vulnerabilities-exploitation-threat-brief/
Microsoft Defender blog on React2Shell defenses https://www.microsoft.com/en-us/security/blog/2025/12/15/defending-against-the-cve-2025-55182-react2shell-vulnerability-in-react-server-components/
Google Threat Intelligence on multi-actor exploitation https://cloud.google.com/blog/topics/threat-intelligence/threat-actors-exploit-react2shell-cve-2025-55182
Palo Alto Networks Unit 42 analysis (CVE relationship and exploitation notes) https://unit42.paloaltonetworks.com/cve-2025-55182-react-and-cve-2025-66478-next/
Censys advisory for exposure and risk context https://censys.com/advisory/cve-2025-55182/
Trend Micro deep technical analysis and PoC ecosystem warning https://www.trendmicro.com/en_us/research/25/l/CVE-2025-55182-analysis-poc-itw.html
Penligent internal links (related React2Shell coverage) https://www.penligent.ai/hackinglabs/fix-react2shell-next-react2shell-rce-in-depth-guide-real-threats-and-robust-defenses/ https://www.penligent.ai/hackinglabs/unmasking-cve-2025-66478-the-silent-killer-in-next-js-server-actions/ https://www.penligent.ai/hackinglabs/beyond-the-patch-inside-fix-react2shell-next-and-the-cve-2025-66478-react2shell-exploit/ https://www.penligent.ai/hackinglabs/clawdbot-security-architectural-deep-dive-and-autonomous-defense-for-ai-engineers/