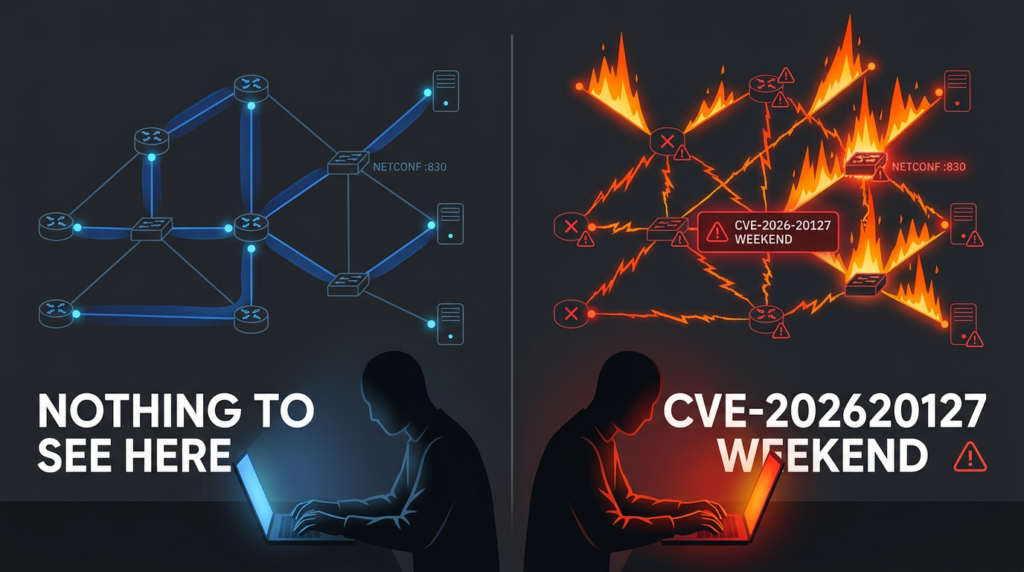
If you run Cisco Catalyst SD-WAN, CVE-2026-20127 is not “just another critical.” It’s a control-plane trust failure that can let an unauthenticated remote attacker cross the boundary that normally separates “an internet noise source” from “a trusted SD-WAN peer that can make fabric-level changes.”
Cisco describes the issue as a peering authentication weakness in Catalyst SD-WAN Controller, formerly vSmart, and Catalyst SD-WAN Manager, formerly vManage. In practical terms, a crafted request can bypass authentication and yield administrative privileges, landing the attacker in a high-privileged internal, non-root context that can access NETCONF and manipulate SD-WAN fabric configuration. (एनवीडी)
Multiple independent responders and government partners also treat it as an in-the-wild threat, not a theoretical one. Cisco Talos publicly tracks exploitation and related post-compromise activity as UAT-8616. (Cisco Talos Blog) The U.S. government placed the vulnerability into CISA’s Known Exploited Vulnerabilities catalog, which is reserved for vulnerabilities with evidence of active exploitation. (सीआईएसए)
This article does three things for practitioners:
- Builds a realistic mental model of what CVE-2026-20127 enables and why SD-WAN makes it uniquely dangerous
- Maps the publicly described intrusion chain to concrete artifacts defenders can validate in their own environment
- Gives copy-pastable checks, hunt ideas, and an engineering plan that doesn’t end at “patch it and pray”
What CVE-2026-20127 is, in operational terms
Vulnerability class: improper authentication, authentication bypass, remote, unauthenticated (CWE-287) (एनवीडी)
Affected products: Cisco Catalyst SD-WAN Controller and Cisco Catalyst SD-WAN Manager (एनवीडी)
Worst-case impact: administrative privileges, then NETCONF-backed configuration manipulation across the SD-WAN fabric (एनवीडी)
Exploit status: publicly acknowledged active exploitation, tracked by Cisco Talos (Cisco Talos Blog)
Priority signal: listed in CISA KEV (सीआईएसए)
From the defender’s perspective, the most important word in that list is not “critical.” It’s fabric.
When an attacker can manipulate SD-WAN configuration, the blast radius is no longer limited to a single device. SD-WAN controllers and managers sit at the point where policy, segmentation, routes, tunnels, and trust are orchestrated. That makes a compromise qualitatively different from “one edge box got popped.” The control plane can be used to rewrite how the network behaves.
Why this CVE is different from typical edge-device bugs
Security teams are used to urgent patch cycles for VPN gateways, firewalls, and web appliances. Those incidents are painful, but they often share a pattern: exploit → local foothold → lateral movement. With SD-WAN control components, the path can invert:
Exploit → control-plane authority → policy and connectivity changes → downstream compromise or disruption.
Cisco’s own description explicitly calls out NETCONF access as the bridge from “privileged user” to “fabric manipulation.” (एनवीडी) Reporting around the incident repeatedly highlights NETCONF usage on port 830 as part of observed activity. (द हैकर न्यूज़)
That matters because NETCONF is not “a random service.” It’s a configuration protocol, and in orchestrated environments it often acts like a privileged automation channel.
So, CVE-2026-20127 should be treated as a control-plane integrity incident first and a device compromise second.
What security teams are calling it, and why those keywords rank
Across high-traffic reporting and incident-response notes, the highest-click phrasing tends to converge on a few terms because they compactly describe risk in a way buyers and operators immediately understand:
- Cisco SD-WAN zero-day
- Authentication bypass
- Actively exploited since 2023
- Control plane compromise
- सीआईएसए केईवी
For example, The Hacker News frames it as a “Cisco SD-WAN Zero-Day… exploited since 2023 for admin access,” and summarizes the bypass, the privilege level, and the use of NETCONF to manipulate configuration. (द हैकर न्यूज़) While you should never outsource truth to headlines, these terms do reflect the core risk pattern described by primary and semi-primary sources: Cisco’s vulnerability description in NVD, Cisco Talos reporting, and government guidance artifacts. (एनवीडी)
Use these terms when you build internal incident tickets and stakeholder summaries. They are not marketing keywords; they’re the shortest path to shared urgency.
Affected components and exposure patterns that actually matter
Components in scope
At minimum, you should assume exposure risk if you operate:
- Catalyst SD-WAN Controller, formerly vSmart
- Catalyst SD-WAN Manager, formerly vManage
NVD’s CVE record explicitly names both. (एनवीडी)
Exposure is not “is it on the internet” — it’s “can an attacker talk to the management plane”
Many organizations think “it’s behind a firewall” equals “not internet-facing.” In practice, SD-WAN management planes often become reachable through:
- Direct public IP exposure for remote operations
- Mis-scoped security groups in cloud-hosted deployments
- Partner and vendor access pathways
- Forgotten NAT rules created during migrations
- Split-brain environments where lab connectivity leaks into production
Public reporting notes risk when systems are exposed to the internet and ports are reachable. (द हैकर न्यूज़) That’s true, but it’s incomplete as a checklist item. What you want is an attack-path audit: can an unauthenticated actor originate traffic that reaches the peering/authentication surface?
The publicly described intrusion chain, translated into defender language
Cisco Talos describes exploitation and post-compromise activity under UAT-8616. (Cisco Talos Blog) The widely circulated summary chain looks like this:
- Initial access via CVE-2026-20127 to bypass authentication and obtain admin-level access (एनवीडी)
- Creation of a rogue peer that appears as a legitimate SD-WAN component in management/control plane context (द हैकर न्यूज़)
- Use of NETCONF to manipulate SD-WAN configuration (एनवीडी)
- Version downgrade to enable additional exploitation paths (post-compromise enabling step) (द हैकर न्यूज़)
- Privilege escalation via CVE-2022-20775 after downgrade, reaching root-level capability (द हैकर न्यूज़)
- Persistence and cleanup behaviors including accounts, SSH keys, script modifications, and log tampering (द हैकर न्यूज़)
Rapid7’s analysis aligns with the downgrade → CVE-2022-20775 escalation sequence as part of observed exploitation narratives. (रैपिड7)
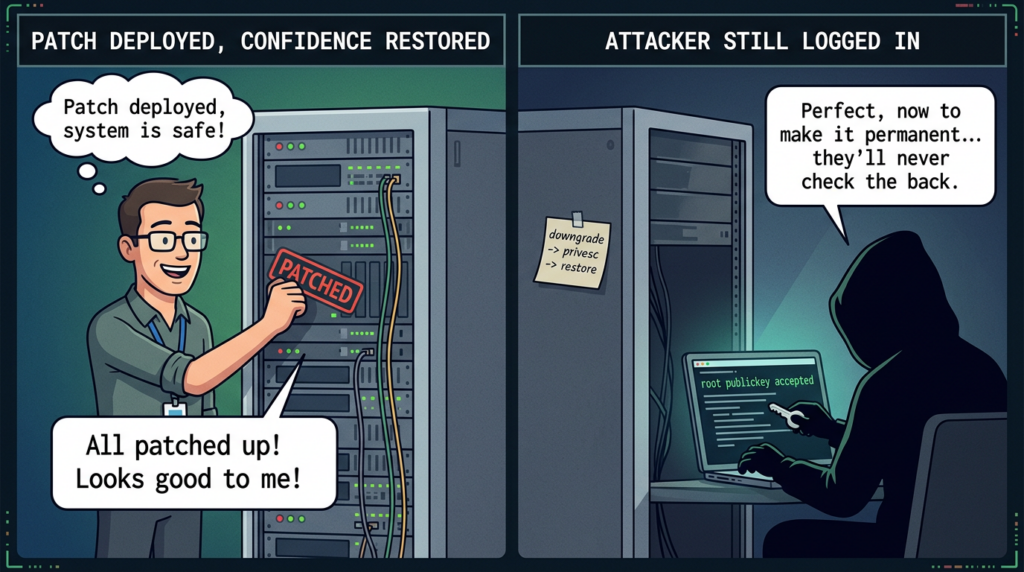
The key insight for defenders: CVE-2026-20127 is the door, but the intrusion is a chain. If you only patch the door and don’t look for signs of someone already inside, you will miss the real risk window.
What to hunt for, using artifacts defenders can validate
A useful hunt plan has three properties:
- It uses data sources you plausibly have
- It focuses on high-signal anomalies
- It produces evidence you can act on
Fortunately, a government-published Cisco SD-WAN threat hunt guide provides concrete detection ideas and example log patterns, including clustering “rogue peer” events, remote-color anomalies, debug packet artifacts, and indicators of CVE-2022-20775 exploitation and root SSH key usage. (संयुक्त राज्य युद्ध विभाग)
High-signal areas
1) Unexpected control-connection state changes and peer outliers
The hunt guide suggests grouping by peer-type and peer-system-ip and investigating low-frequency pairs, especially with “new-state: up” and short uptimes — a pattern consistent with ephemeral rogue peers being introduced. (संयुक्त राज्य युद्ध विभाग)
2) Remote-color anomalies
It also highlights cases where “remote-color” is null or malformed during control-connection events, presented as a high-signal indicator when temporally aligned with other anomalies. (संयुक्त राज्य युद्ध विभाग)
3) NETCONF activity and port 830
Public reporting ties post-compromise manipulation to NETCONF on port 830. (द हैकर न्यूज़) Even if your environment legitimately uses NETCONF, what matters is: who is using it, from where, and when.
4) Root SSH public key acceptance and vmanage-admin key changes
The hunt guide flags “Accepted publickey for root” as an essentially-no-false-positive event, because root SSH should not be used on these systems. (संयुक्त राज्य युद्ध विभाग) It also calls out suspicious authorized_keys changes for vmanage-admin as relevant to observed activity. (संयुक्त राज्य युद्ध विभाग)
5) Version downgrade and reboot events that don’t match maintenance windows
The narrative around exploitation includes downgrading and restoring versions as an anti-forensic and capability-enabling step. (द हैकर न्यूज़) Your job is to treat unexplained downgrade patterns as “possible attacker enabling action,” not “weird upgrade glitch.”
Copy-pastable checks for exposure and early triage
These are defensive validation checks, not exploitation guidance.
1) Identify internet exposure and management-plane reachable services
# Replace CIDR with your management plane ranges, public egress IPs, or known SD-WAN endpoints
# Focus on confirming whether management/control services are reachable where they shouldn't be.
nmap -sS -Pn -p 22,443,830,8443,2080,3181,9999 --open <TARGET_IP_OR_RANGE> -oN sdwan_surface_scan.txt
# If you have a list of SD-WAN public IPs, scan those first
nmap -sS -Pn -p 443,830 --open -iL sdwan_public_ips.txt -oN sdwan_public_surface.txt
Why port 830? Because NETCONF is repeatedly referenced in the post-compromise chain for configuration manipulation. (द हैकर न्यूज़)
2) Hunt for root SSH key usage and suspicious auth events
# On systems where auth logs are available/centralized
sudo grep -R --line-number -E "Accepted publickey for root|Accepted publickey for vmanage-admin" /var/log/auth.log*
# If you forward logs to SIEM, translate this into a search:
# message contains "Accepted publickey for root"
Root SSH public key acceptance is explicitly called out as high-signal in the hunt guide. (संयुक्त राज्य युद्ध विभाग)
3) Detect likely rogue peer outliers by clustering
If you can access controller/manager logs referenced in the hunt guide, implement a simple aggregation:
# Minimal example: count peer-type + peer-system-ip pairs to surface outliers
# Input: parsed fields from control-connection state-change logs
from collections import Counter
events = [
# {"peer_type": "vmanage", "peer_system_ip": "1.2.3.4", "new_state": "up", "uptime": "0:00:00:00"},
]
c = Counter((e["peer_type"], e["peer_system_ip"]) for e in events if e.get("new_state") == "up")
outliers = sorted(c.items(), key=lambda x: x[1])[:20]
for (peer_type, peer_ip), count in outliers:
print(peer_type, peer_ip, count)
This mirrors the hunt guide’s approach: identify small clusters of rogue peers and then validate against inventory. (संयुक्त राज्य युद्ध विभाग)
Quick-reference table: what to look at first
| Signal | यह क्यों मायने रखती है | Where to look | What to do next |
|---|---|---|---|
| CVE-2026-20127 in-scope components reachable | Remote unauth bypass risk | Edge ACLs, cloud SGs, external scan results | Restrict access immediately, then patch to fixed releases (द हैकर न्यूज़) |
| Unexpected peer-type or peer-system-ip outliers | Rogue peer pattern | vSmart/vManage logs referenced in hunt guide | Validate against inventory, correlate with other anomalies (संयुक्त राज्य युद्ध विभाग) |
| remote-color null or malformed | High-signal initial rogue peering indicator | Specific control-connection events | Treat as urgent when aligned with new peers (संयुक्त राज्य युद्ध विभाग) |
| NETCONF activity spikes, unfamiliar sources on port 830 | Config manipulation channel | Network telemetry + logs | Correlate with config diffs, peer anomalies (द हैकर न्यूज़) |
| Version downgrade and restore sequence | Enables follow-on exploitation + anti-forensics | Upgrade/downgrade logs and reboot events | Assume compromise until disproven (द हैकर न्यूज़) |
| “Accepted publickey for root” | Root SSH should not occur | /var/log/auth.log | Immediate incident response + key/script review (संयुक्त राज्य युद्ध विभाग) |
Patching guidance and why “fixed version” is not the whole answer
The public high-level guidance is straightforward: patch to versions that Cisco lists as fixed for affected trains, or migrate to a fixed release if on older versions. (द हैकर न्यूज़)
But SD-WAN compromises are often stateful: an attacker can leave behind persistent access, altered startup scripts, new keys, and configuration changes that survive patching. Public reporting of post-compromise steps includes creation of local user accounts, adding authorized keys, modifying start-up scripts, and log clearing. (द हैकर न्यूज़)
So treat patching as containment of the initial access vector, not as proof the environment is clean.
A defensible remediation plan has two parallel tracks:
- Track A — close the door: patch + restrict management-plane reachability
- Track B — validate integrity: hunt + configuration diff review + credential and key rotation + forensic preservation
The CVE-2022-20775 link: why defenders should care
Several narratives around this campaign mention attackers downgrading software to a vulnerable version and then exploiting CVE-2022-20775 to escalate privileges to root before restoring the original firmware. (द हैकर न्यूज़) NVD describes CVE-2022-20775 as a Cisco SD-WAN Software CLI privilege escalation issue that can allow execution as root. (एनवीडी)
This matters because it shows a common edge-device playbook that keeps working:
- Use a high-impact initial access flaw
- Bring the environment into a known-vulnerable state if needed
- Chain a privesc bug to reach root
- Remove obvious traces and restore “normal” version strings
Defenders should interpret this as a warning: version strings and current patch level are not reliable indicators of historical compromise. You need log evidence, inventory reconciliation, and configuration integrity checks.
When you’re handling a control-plane vulnerability like CVE-2026-20127, the failure mode is often not “we didn’t know the CVE exists.” It’s “we couldn’t turn the advisory into a repeatable, evidence-based verification workflow fast enough.” The gap between patch guidance and demonstrable safety is where incidents linger: teams patch, but can’t easily prove that exposure is gone, that configuration integrity is intact, and that no persistence remains.
Penligent is designed for that verification gap. Instead of treating remediation as a checklist that lives in tickets and tribal knowledge, you can structure a target-specific workflow that captures scope, runs controlled reconnaissance, validates reachable surfaces, and ties observed artifacts to an auditable report. For SD-WAN incidents, that means you can standardize “what we checked” across environments, reduce repeat work, and keep a durable evidence trail for security and network teams reviewing control-plane integrity.
अधिक जानकारी के लिए
- NVD entry for CVE-2026-20127 (एनवीडी)
- Cisco Talos write-up on active exploitation by UAT-8616 (Cisco Talos Blog)
- CISA Known Exploited Vulnerabilities catalog entry for CVE-2026-20127 (सीआईएसए)
- Canadian Centre for Cyber Security advisory for CVE-2026-20127 (Canadian Centre for Cyber Security)
- DoD-hosted Cisco SD-WAN Threat Hunt Guide PDF (संयुक्त राज्य युद्ध विभाग)
- Rapid7 analysis referencing the downgrade-to-privesc chain (रैपिड7)
- Penligent related article, CVE-2026-20127 PoC, what we know and what to do today (पेनलिजेंट)
- Penligent related article, CVE-2024-6387 regreSSHion (पेनलिजेंट)
- Penligent related article, XZ Utils CVE-2024-3094 reality check (पेनलिजेंट)