When a vulnerability lands on a management plane instead of an edge service, the conversation needs to change immediately. CVE-2026-20079 is not just another web bug with a scary score. It is a pre-authentication flaw in Cisco Secure Firewall Management Center, FMC, that can let a remote attacker bypass authentication and execute script files on the appliance, ending with root access to the underlying operating system. Cisco rates it a 10.0 on CVSS 3.1, classifies it under CWE-288, and describes the root cause as an improper system process created at boot time. (Cisco)
That description matters because FMC is not an isolated administrative nicety. It is the coordination layer many organizations rely on to manage policy, software lifecycle, telemetry, and security administration across Cisco firewall estates. Publicly available technical summaries emphasize the same point: once the management plane is compromised, the impact extends beyond the single box you patch on a Thursday night. The CVSS vector for CVE-2026-20079 includes Scope Changed, which is a strong hint that the blast radius is architectural, not local. (runZero)
Cisco disclosed CVE-2026-20079 on March 4, 2026 as part of a larger March 2026 bundled publication covering dozens of vulnerabilities across Cisco Secure Firewall ASA, Secure FMC, and Secure FTD software. In that same release, Cisco also disclosed CVE-2026-20131, another maximum-severity issue in the FMC management plane, this time a remote code execution bug caused by insecure deserialization. Treating CVE-2026-20079 in isolation misses the operational reality. Defenders are looking at two separate unauthenticated routes to root against a core administrative system, disclosed at the same time, in the same product family, with no workarounds for the auth bypass path. (Cisco)
The right way to read this vulnerability is not “Cisco has another critical CVE.” The right way to read it is this: if your organization exposes or loosely protects its firewall management plane, then a single internet-reachable administrative surface can become the shortest path to full trust collapse inside a security control stack. That is why CVE-2026-20079 deserves more than a patch note. It deserves a serious look at architecture, exposure, telemetry, validation, and recovery assumptions. (CyCognito)
What CVE-2026-20079 Actually Is
Cisco’s own description is direct. A vulnerability in the web interface of Cisco Secure Firewall Management Center Software could allow an unauthenticated remote attacker to bypass authentication and execute script files on an affected device to obtain root access to the underlying operating system. The flaw exists because of an improper system process created at boot time, and exploitation is performed by sending crafted HTTP requests to an affected device. (Cisco)
There are a few phrases in that description that should immediately raise eyebrows for any security engineer.
The first is unauthenticated. No stolen password, no reused admin credential, no SSO weakness, no phishing foothold. A pre-auth management-plane flaw removes the usual friction that buys defenders time. That is why bugs like this age badly. Once enough defenders and attackers understand what part of the request path is special, the cost of initial access tends to fall quickly. Public monitoring sources already note proof-of-concept activity in the ecosystem and are tracking the CVE as a vulnerability worth watching, even though, as of this writing, I have not found a Cisco or CISA statement confirming active exploitation of CVE-2026-20079 in the wild. That distinction matters, and it is worth being precise about it. (GitHub)
The second phrase is execute script files. That wording implies more than a narrow authorization bypass. In practical terms, this is not “you can see a page you should not see.” It is a path to code-bearing behavior on the appliance. Cisco’s published CVSS vector is CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H, which places it at the top of the severity scale. Network reachable, low complexity, no privileges required, no user interaction, scope changed, and high impact across confidentiality, integrity, and availability. That is the scoring profile defenders associate with emergency handling, not routine maintenance. (Cisco)
The third phrase is root access to the underlying operating system. Once an attacker reaches root on a management appliance, incident response can no longer assume that local logs, local integrity, or local trust are intact. A root-capable adversary can tamper with scripts, persistence, configurations, and potentially the administrative workflows that connect FMC to downstream managed devices. This is why third-party analysis from runZero, CyCognito, and Abstract all emphasizes that the business risk is not limited to the FMC host itself. (runZero)
Why This Vulnerability Matters More Than the Average CVE
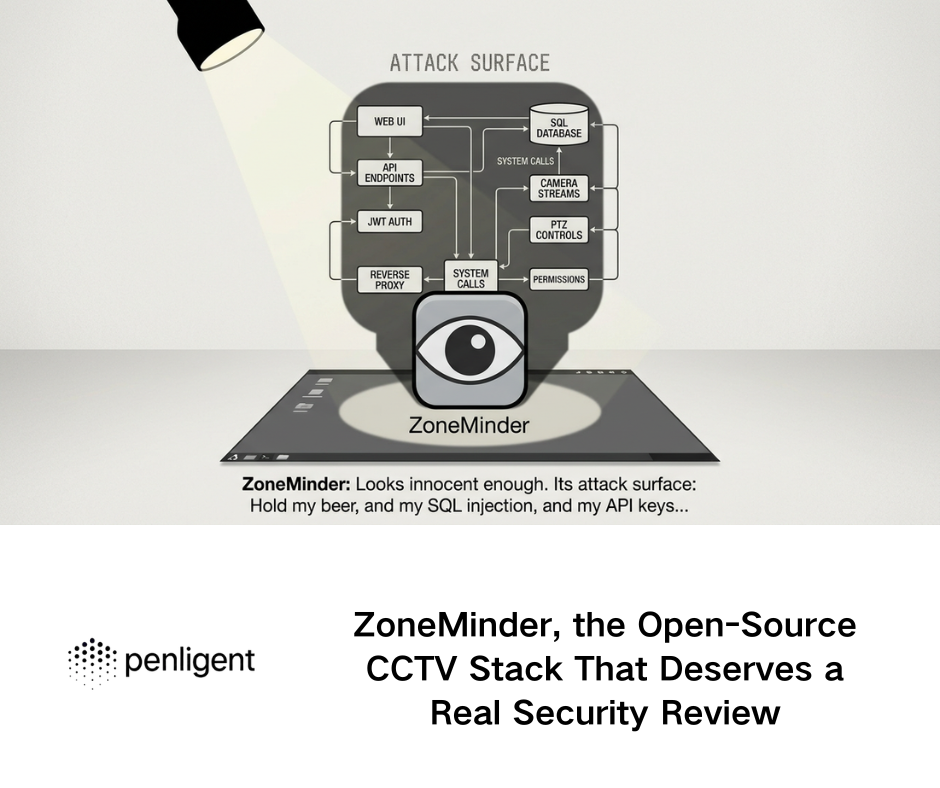
There is a large difference between exploiting a line-of-business application and exploiting a centralized security management plane. The former gives an attacker access to one application boundary. The latter can give the attacker leverage over the very systems defenders trust to define, distribute, and audit policy.
FMC is used as a centralized administrative platform for Cisco security environments. Public summaries describe it as the place where organizations configure policies, manage updates, and aggregate security telemetry across firewall deployments. That means the value of the target is not just the data on the appliance. The value is the control relationship between the appliance and the rest of the security estate. (runZero)
This is where the CVSS “Scope Changed” attribute deserves real attention. In vulnerability scoring, scope changed often gets treated as a checkbox buried in a vector string. In operational terms, here it means compromise is not neatly contained within the vulnerable software component. Abstract’s write-up makes this explicit by noting that successful exploitation of FMC can affect the security of other components such as managed Firewall Threat Defense devices. Even if you prefer to stay anchored to vendor language and avoid extending claims beyond Cisco’s own text, that interpretation tracks with the architecture. Centralized firewall management is a trust hub. Trust hubs are not ordinary nodes. (abstract.security)
It is also important to understand what makes management-plane vulnerabilities historically dangerous in enterprise environments.
First, they are often reachable from places they should not be reachable from. An organization may not intentionally expose the FMC UI to the public internet, but security teams regularly inherit realities such as temporary admin exceptions, permissive VPN access, split-tunnel mistakes, shadow jump boxes, flat management networks, or reverse proxy patterns that widen exposure. When a product sits in the “trusted infrastructure” category, people become overly comfortable with weak segmentation.
Second, they are often under-monitored. SOC teams may spend enormous effort on endpoint, email, identity, and east-west traffic, while relatively little high-fidelity detection engineering exists for firewall management appliances themselves. That gap is especially painful when the vulnerability is pre-auth and leads to root.
Third, management appliances carry decision authority. Even when a compromise begins on the management server, the attacker’s strategic objective is usually the downstream trust chain: policy modification, rule weakening, configuration export, credential harvesting, software distribution abuse, or simply persistence inside a tier-0 administrative zone.
That is why a maximum-severity Cisco FMC auth bypass should be read as an infrastructure trust event, not just a product update event. (Arctic Wolf)
The Affected Versions, the Safe Branches, and What Is Not Affected
One of the most useful public summaries comes from runZero, which distilled the affected Cisco FMC versions in a practical format. According to that write-up, the affected version lines are:
| Product branch | CVE-2026-20079 status | Practical fixed point |
|---|---|---|
| Cisco FMC 7.0.x | Affected before 7.0.9 | 7.0.9 or later |
| Cisco FMC 7.2.x | Affected before 7.2.11 | 7.2.11 or later |
| Cisco FMC 7.4.x | Affected before 7.4.4 | 7.4.4 or later |
| Cisco FMC 7.6.x | Affected before 7.6.4 | 7.6.4 or later |
| Cisco FMC 7.7.x | Affected before 7.7.12 | 7.7.12 or later |
| Cisco FMC 10.0.x | Not listed for CVE-2026-20079 | 10.0.1 is relevant to CVE-2026-20131 only |
This same runZero summary also notes the adjacent fix line for CVE-2026-20131, where 7.4.6, 7.6.5, and 10.0.1 become relevant. That distinction matters because defenders patching “the Cisco FMC issue” need to make sure they are solving both problems, not just one. A team that upgrades only to a branch point sufficient for CVE-2026-20079 but still vulnerable to CVE-2026-20131 may believe the emergency is over while leaving another pre-auth root path intact. (runZero)
Cisco’s public advisories and follow-on coverage also make an important boundary clear. CVE-2026-20079 affects on-premises Cisco Secure Firewall Management Center. Cisco has confirmed that Cloud-Delivered FMC is not affected by CVE-2026-20079. Public summaries further note that Cisco ASA और Cisco FTD themselves are not directly affected by this specific CVE. That does not reduce urgency for organizations using FMC to manage those platforms; it simply means the vulnerable administrative surface sits in FMC, not in the managed products named above. (Cisco)
There is also a subtle but important difference between CVE-2026-20079 and CVE-2026-20131 regarding Cisco Security Cloud Control. Public advisory summaries indicate that Security Cloud Control is not affected by CVE-2026-20079, while CVE-2026-20131 does affect Security Cloud Control Firewall Management. Because that service is SaaS-delivered, Cisco says the cloud-delivered component has already been upgraded and no customer action is required there. That means an organization with a hybrid mental model of “Cisco firewall management” cannot treat all administrative surfaces as equivalent. The exposure story is product-specific and deployment-specific. (Arctic Wolf)
CVE-2026-20079 and CVE-2026-20131 Should Be Triaged as One Operational Problem
A common failure mode in vulnerability response is to follow the numbering rather than the architecture. That is understandable. Ticketing, scanners, and patch programs are all CVE-centric. But operationally, CVE-2026-20079 and CVE-2026-20131 are best treated as one administrative surface emergency.
CVE-2026-20079 is the authentication bypass route. CVE-2026-20131 is the insecure deserialization route. Both land on Cisco Secure Firewall Management Center. Both are unauthenticated and remote. Both can yield root-level control. Both were disclosed together on March 4, 2026. Both have CVSS 10.0. Both are the kind of defects that turn management interfaces into adversary entry points. (Cisco)
The technical classes differ, and that affects how one thinks about exploit development. A CWE-288 auth bypass usually forces defenders to think about alternate paths, alternate channels, request routing, trust misbinding, or hidden system behavior that accidentally sidesteps the intended control flow. A CWE-502 deserialization bug pushes defenders toward gadget chains, object graphs, and parser trust boundaries. But from a security operations standpoint, the difference matters less than the shared outcome: the management plane cannot be assumed trustworthy until patched and validated. (Cisco)
This is also where third-party threat summaries have added useful framing. CyCognito and Arctic Wolf both emphasize that FMC is the management center of gravity for firewall administration. That means defenders should not frame the decision as “do we patch a server.” The decision is “how long are we willing to leave a remote pre-auth root path open on the system that controls policy, telemetry, and trust relationships in our firewall estate.” That is a much clearer executive question. (CyCognito)

The Most Valuable Public Takeaways From Current Coverage
You asked for the current high-interest web coverage to be read and synthesized into the article. There is an important limitation worth stating plainly: public search results do not provide reliable click-through data, so it would be dishonest to claim I know the true highest-CTR article for this keyword. What I can say, based on current search prominence and practical utility, is that several pieces stand out for different reasons.
The Cisco advisory and bundled publication are the authoritative baseline. They define the vulnerability class, impact, severity, and official remediation direction. Everything else should be measured against them. (Cisco)
The runZero write-up is one of the most operationally useful because it turns the advisory into an asset-discovery and version-triage problem. It does not stop at “patch now.” It asks the question many defenders still struggle with in practice: do you actually know where your FMC instances are, and do you know which branch they are running. That is a better question than “have you read the advisory.” (runZero)
Arctic Wolf’s bulletin is useful because it puts CVE-2026-20079 next to CVE-2026-20131 and highlights the patch branches together. It also clearly notes that Cisco Security Cloud Control was automatically upgraded for the SaaS-affected side of CVE-2026-20131, which helps reduce confusion in hybrid environments. (Arctic Wolf)
CyCognito’s summary is useful for risk framing because it reinforces that the affected scope is on-prem FMC and that central management compromise carries downstream risk. For practitioners, that is a reminder not to treat the CVE as a single-host emergency only. (CyCognito)
The most valuable common lesson across these sources is straightforward: patching is necessary, but exposure awareness is equally urgent. A patched appliance you can identify is manageable. An unpatched appliance you forgot exists is the one that becomes the incident. (runZero)
How an Attacker Would Think About This Without Getting Into Exploit Instructions
Because CVE-2026-20079 is a pre-authentication HTTP-driven flaw, an attacker’s first question is not “what credential can I steal.” It is “where is the management interface reachable, and what unusual request path gives me behavior before normal authentication enforcement.”
That kind of thinking is why management-plane hardening is often weaker in reality than on architecture diagrams. Organizations frequently assume one of the following is enough:
They put the interface “behind VPN,” but the VPN is broad and reachable by many user classes.
They restricted internet exposure, but not partner exposure or contractor networks.
They rely on an internal address range but do not segment internal administrative traffic well.
They trust that the appliance itself is a security product and therefore somehow safer by default.
None of those assumptions survive a pre-auth root flaw very well.
There is another uncomfortable reality. Once a management appliance has been rooted, the question “was this exploited” becomes harder to answer with confidence using the appliance’s own records. Root access changes the reliability of local evidence. That means defenders should think in terms of corroboration: upstream network telemetry, reverse-proxy logs, firewall logs, VPN logs, identity telemetry, change windows, config backups, and any external monitoring that can establish whether unusual access occurred around the disclosure window or earlier.
At the time of writing, I have not found a Cisco or CISA statement saying CVE-2026-20079 is actively exploited in the wild. OpenCVE indicates the CVE is not in the KEV list, and public monitoring sources describe it as worth tracking rather than confirmed exploited. That should not be read as comfort. A public PoC trail exists in the ecosystem, and Cisco’s March 2026 security cycle has already shown how quickly other Cisco management-plane vulnerabilities moved from disclosure to confirmed exploitation discussions in adjacent product lines. The right posture is urgency without embellishment. (OpenCVE)

What Defenders Should Do in the First Hour
The first hour should not be spent reading social media takes about how bad the bug is. The first hour should be spent answering a short list of questions that determine whether you are dealing with theoretical exposure or immediate risk.
- Do we have any on-prem FMC instances at all This sounds obvious, but it is exactly the kind of question that reveals incomplete asset intelligence. Large organizations often have lab FMCs, inherited branch deployments, discontinued DR instances, or shadow admin systems that are absent from CMDB quality reports. The public runZero guidance is valuable here because it reframes the vulnerability as an asset discovery problem first. (runZero)
- Which versions are running If you do not know the version branch, you do not know the remediation target. A team on 7.4.x needs a different fixed point than a team on 7.6.x. A team concerned about both CVE-2026-20079 and CVE-2026-20131 needs to validate both branch thresholds. (runZero)
- Is the management interface reachable from any untrusted network path “Not on the public internet” is not enough. The practical question is whether any semi-trusted or overly broad path exists from user, contractor, VPN, vendor, partner, or cloud-connected networks into the FMC web interface.
- Can we reduce exposure immediately while preparing the upgrade Cisco states there are no workarounds for CVE-2026-20079. That means you cannot feature-toggle your way out of the bug. But you can still reduce attack surface by limiting reachability, enforcing jump-host-only access, tightening ACLs, reducing VPN scope, and monitoring inbound traffic to the management interface while patch planning happens. (Cyber Security Agency of Singapore)
- Do we have reason to suspect prior exposure If the management plane was broadly reachable, the response should include compromise assessment, not just patching.
A Practical Triage Table for CVE-2026-20079
| Question | यह क्यों मायने रखती है | Good answer | Bad answer |
|---|---|---|---|
| Do we run on-prem FMC | Determines applicability | Yes, inventoried | “Probably not” |
| Which branch is installed | Determines exact fixed version | Known branch and patch window | Unknown version |
| Is the web UI exposed beyond a hardened admin zone | Determines pre-auth attack surface | Only through tightly controlled admin path | Reachable from broad VPN or public internet |
| Are both CVE-2026-20079 and CVE-2026-20131 being remediated | Prevents partial closure | Single change plan covers both | Team only patches for one CVE |
| Can we validate after patching | Avoids false closure | Version, access path, and logging verified | “Upgrade completed” with no validation |
| Is compromise assessment in scope | Root-level pre-auth risk justifies it | Yes for exposed instances | No, because “we patched fast” |
Detection and Verification, Without Turning This Into an Exploit Tutorial
For many teams, the challenge is not understanding the advisory. The challenge is turning the advisory into safe internal validation work. Below are examples of what that looks like.
1. Inventory likely FMC systems
Use your existing asset intelligence stack first. If you maintain internal DNS, CMDB, EASM, NAC, or scanner inventories, search for FMC naming, admin subnets, certificate subjects, and legacy Firepower naming. Do not rely on one data source.
A minimal internal inventory pattern could look like this:
#!/usr/bin/env bash
# Safe internal inventory helper
# Purpose: find likely Cisco FMC hosts from an internal admin network inventory export
grep -Ei 'fmc|firepower management center|secure firewall management center' assets.csv
That is intentionally simple. The point is not tooling elegance. The point is to avoid the all-too-common situation where a critical patch exists but the inventory is incomplete.
2. Verify version on known FMC instances
If you have legitimate administrative access and an approved maintenance process, version verification can be handled through the console, the administrative UI, or internal documentation exports. A safe internal checklist is often more valuable than a fancy script.
#!/usr/bin/env bash
# Record version evidence for known FMC hosts
while read -r host; do
echo "=== $host ==="
echo "Collect version from approved admin channel, screenshot or export retained"
done < fmc_hosts.txt
If your organization has a standardized method for collecting version banners through management APIs, use that. The important point is to record evidence, not just a verbal confirmation from an operator.
3. Confirm reachability assumptions
The goal here is not aggressive probing. The goal is to verify who can reach the management plane.
#!/usr/bin/env bash
# Safe reachability check from approved internal vantage points
while read -r host; do
echo "Testing TCP/443 to $host"
nc -vz "$host" 443
done < fmc_hosts.txt
Run this from approved segments only. A result that says “reachable from user VPN” or “reachable from a contractor enclave” is an architectural finding, even before you patch.
4. Inspect reverse-proxy, VPN, or edge logs for unusual access patterns
Because the vulnerability is HTTP-driven and pre-auth, look for management-interface requests from unusual sources, unexpected geographies, broad scanning behavior, or paths inconsistent with normal admin patterns. If your FMC sits behind a reverse proxy, WAF, or network control point, those upstream logs may be more trustworthy than the local appliance in a suspected compromise scenario.
5. Hunt for suspicious post-exploitation signs
Cisco’s description says the attacker can execute script files and achieve root access. Post-exploitation triage should therefore include:
- unusual script execution activity on or around the appliance
- unexpected new scheduled behavior or persistence indicators
- abnormal admin access times
- unexplained policy changes
- unusual outbound connections from the appliance
- divergence between expected configuration state and current state
Even if you find nothing, the act of checking is part of responsible closure.

Why “No Workaround” Changes the Response
Cisco says no workarounds are available for CVE-2026-20079. That has a practical consequence many organizations underestimate. It removes the comforting middle ground. There is no neat feature toggle, no benign configuration flag, no safe temporary fix that neutralizes the flaw while you wait for next month’s patch cycle. The only durable answer is software remediation combined with access reduction and validation. (Cisco)
When there is no workaround, patch deferral becomes much harder to justify. Teams sometimes delay emergency upgrades because the maintenance blast radius of a central management appliance feels risky. That concern is real. But the decision must be compared against the risk of unauthenticated root on the same system. In most environments, especially any environment where administrative reachability is broader than intended, that comparison is not close.
This is also the moment when process quality matters. Patching without validation is not enough. A serious response includes:
- confirming the exact version before the change
- mapping the correct target fixed version for the running branch
- limiting reachability during the change window if possible
- completing the software update
- validating the running version after the change
- confirming that the management surface is not more exposed than before
- reviewing recent administrative activity and policy changes for anomalies
That is what separates change completion from risk reduction.
CVE-2026-20079 in the Context of Other Cisco Management-Plane Lessons
One of the easiest ways to underestimate a newly disclosed CVE is to view it as unique. Cisco’s product portfolio is broad, and vulnerabilities emerge for many different reasons. But defenders should still notice a recurring theme across some of the most operationally painful incidents: when the management plane breaks, the consequences are often outsized.
The closest immediate relative to CVE-2026-20079 is CVE-2026-20131, the other Cisco FMC maximum-severity bug disclosed in the same bundle. If CVE-2026-20079 is the auth-bypass-to-root path, CVE-2026-20131 is the deserialization-to-root path. Different bug class, same strategic target. (Cyber Security Agency of Singapore)
CVE-2026-20127 in Cisco Catalyst SD-WAN is another relevant reminder. That flaw, which affects a different Cisco product family, is a critical authentication bypass in SD-WAN control infrastructure, and public reporting indicates active exploitation. Penligent’s own recent Cisco SD-WAN coverage, based on vendor and industry sources, frames it correctly as a control-plane trust problem rather than a narrow box-level issue. That lesson translates directly to FMC: centralized administrative systems deserve stricter exposure discipline than ordinary application servers. (पेनलिजेंट)
Then there is CVE-2023-20198, the Cisco IOS XE Web UI issue that allowed unauthenticated privilege abuse through the administrative interface and became an emblematic case of why internet-exposed management services are a persistent strategic mistake. It is not the same bug, the same product, or the same exploit mechanics. But it belongs in the same mental category: management surfaces have a long history of becoming emergency priorities when they are exposed and under-defended. (पेनलिजेंट)
The point of drawing these comparisons is not to make every Cisco advisory sound apocalyptic. It is to build the right instinct. When the vulnerable component is a trust hub, defenders should move faster, validate more deeply, and assume that remediation is about the surrounding architecture as much as the software defect.
A Sensible Incident Response Flow for Exposed FMC Instances
If an affected FMC instance was reachable from a broad or semi-trusted network path before patching, a basic “upgrade and close ticket” response is too shallow. A more defensible sequence looks like this.
First, reduce exposure immediately. Limit inbound reachability to the smallest possible administrative zone while the upgrade is being staged. That does not fix the vulnerability, but it reduces the number of entities that can try to exploit it.
Second, patch to the correct fixed release for your branch, and account for CVE-2026-20131 at the same time if applicable. Mixed handling creates false confidence. (runZero)
Third, treat the appliance as a high-trust system for forensic purposes. Review available logs, but do not over-trust them if there was realistic pre-patch exposure. Pull external corroborating telemetry where available.
Fourth, review for configuration integrity. Because FMC is used to manage firewall environments centrally, any unexplained policy drift, rule relaxation, object changes, deployment anomalies, or administrative account irregularities should be reviewed.
Fifth, rotate sensitive administrative credentials and tokens associated with management workflows if your environment suggests they may have been at risk.
Sixth, document architecture changes. Many organizations patch but do not fix the surrounding control weakness. If the same management plane remains broadly reachable after patching, the next critical bug will put you in the same position again.
For teams handling CVEs like this regularly, the hard part is rarely “knowing there is a CVE.” The hard part is turning disclosures into repeatable, validated defensive action. That usually means five separate jobs: finding assets, identifying exposed paths, mapping versions to fixed branches, prioritizing what is truly reachable, and confirming the environment is clean after the change.
That is the sort of workflow where an AI-assisted penetration testing and validation platform can help without turning into theater. Used correctly, Penligent can support structured verification work around exposed management surfaces, version-aware triage, and repeatable post-patch validation. The value is not in making a dramatic claim that “AI solves patching.” The value is in standardizing the boring but essential steps that too often get skipped under time pressure.
This is especially relevant for organizations managing many administrative surfaces across inherited infrastructure, M&A sprawl, or mixed Cisco estates. In those environments, the operational question is not just “is CVE-2026-20079 bad.” The operational question is “can we consistently translate a vendor advisory into evidence-backed remediation across every real asset we own.” That is where automation earns its keep.
What a Good Post-Patch Validation Looks Like
The vulnerability is closed only when the environment proves it. A solid validation checklist for CVE-2026-20079 should include the following:
- confirmed appliance version after upgrade
- confirmation that the branch is no longer in an affected range
- confirmation that exposure paths were reviewed and narrowed where possible
- confirmation that CVE-2026-20131 was also handled if the branch required it
- review of relevant administrative and network telemetry around the disclosure and patch window
- preservation of change evidence for future audit and incident reconstruction
A simple internal checklist artifact can be more valuable than a polished dashboard if it is actually used.
#!/usr/bin/env bash
# Internal validation checklist stub for FMC patch verification
cat <<'EOF'
[ ] Asset inventoried
[ ] Pre-change version recorded
[ ] Exposure path reviewed
[ ] Correct fixed release installed
[ ] Post-change version recorded
[ ] CVE-2026-20131 also assessed
[ ] Recent admin activity reviewed
[ ] Upstream logs checked for unusual access
[ ] Findings documented
EOF
That is not glamorous. It is effective.
The Strategic Lesson Behind CVE-2026-20079
The enduring lesson here is not merely that Cisco FMC had a critical auth bypass. The lesson is that centralized management systems are some of the most dangerous places to be casually exposed, casually monitored, or casually maintained.
Enterprises often spend more energy protecting the workloads behind the firewall than protecting the systems that define the firewall’s rules, distribute its updates, and centralize its visibility. CVE-2026-20079 is a reminder that this inversion is dangerous. A management appliance is not “just another admin tool.” It is a trust concentration point.
The most mature response to this vulnerability therefore includes more than patching. It includes asking uncomfortable but necessary questions:
Why was this surface reachable from where it was reachable
Why did it take a critical advisory to map our own asset exposure
How quickly can we validate administrative-plane assumptions
What logs would we trust if the appliance itself had been rooted
Are we treating management platforms as tier-0 infrastructure or as ordinary servers
Those questions will still matter after this CVE ages out of the news cycle.
निष्कर्ष
CVE-2026-20079 deserves attention because it combines the three properties defenders fear most in an infrastructure vulnerability: it is remote, it is pre-authentication, and it ends at root on a centralized management plane. Cisco’s own advisory language is unambiguous about the impact, and public operational coverage reinforces that defenders should handle it as both a patching priority and an exposure-assessment event. (Cisco)
The immediate priorities are clear. Identify every on-prem FMC instance, determine the running branch, upgrade to the correct fixed release, make sure the companion FMC vulnerability CVE-2026-20131 is not left behind, reduce unnecessary management-plane reachability, and validate the environment after the change. If an affected appliance was broadly reachable before remediation, treat compromise assessment as part of the job, not an optional extra. (runZero)
There is no responsible way to spin CVE-2026-20079 into “probably fine if you are internal only.” Internal is not a control. Exposure is a control. Segmentation is a control. Restricted administrative paths are controls. Verified patch state is a control. Everything else is optimism wearing a badge.
References and Further Reading
- Cisco advisory for CVE-2026-20079
- Cisco March 2026 bundled firewall advisory publication
- CVE record for CVE-2026-20079
- Digital NHS cyber alert on Cisco FMC vulnerabilities
- runZero guide to finding impacted Cisco Secure FMC systems
- Arctic Wolf bulletin on CVE-2026-20079 and CVE-2026-20131
- Cisco FMC companion flaw CVE-2026-20131 coverage
- CyCognito summary of the FMC root-compromise risk
- Security Affairs coverage of the Cisco Secure FMC fixes
- CVE-2026-20127, PoC Exploit Released for Cisco SD-WAN Zero-Day Actively Exploited in the Wild
- CVE-2026-20127 and the SD-WAN Control Plane Trust Problem
- CVE-2025-20393, The Cisco AsyncOS Zero-Day That Turns Email Security Appliances into Root-Level Beachheads
- CVE-2023-20198 Incident Playbook, Exposure Triage, Compromise Checks, and Durable Remediation