The fastest proof-of-concepts are usually the least dramatic. They are not full compromise chains. They are not post-exploitation demos. They are not payload collections dumped into a scanner and fired at random. A good PoC is smaller than that. In security practice, a PoC is code or a demonstration that proves a vulnerability exists and is exploitable, while stopping short of full weaponization. Its job is to validate the issue, show impact clearly, and make the finding reproducible for the people who need to fix it. (Pentesterlab)
That distinction is the whole article. When experienced testers say they can go from finding to PoC in under a minute, they usually do not mean they can turn every bug into maximum impact in sixty seconds. They mean they can reduce a hypothesis into the smallest convincing signal. They know what input matters, what effect matters, and what point is enough. The speed comes from reduction, not recklessness. It also comes from discipline: authorization, scope, observability, and the willingness to stop as soon as the case is proven. NIST frames technical testing as a planned assessment activity rather than ad hoc experimentation, and HackerOne’s guidance on report quality centers on reproducibility, clear impact, and supporting material. (NIST CSRC)
A one-minute PoC is therefore not a trick. It is a very specific kind of engineering move. You take a noisy finding, isolate the attacker-controlled input, choose the smallest security-relevant effect, create a minimal control-versus-test comparison, and stop at confirmation. That approach is what separates good validation from noisy testing and what keeps a PoC useful to pentesters, bug bounty hunters, product engineers, blue teams, and security buyers at the same time.
How to Build a PoC in One Minute Starts With the Right Definition
A PoC and a full exploit are related, but they are not the same deliverable. PentesterLab’s glossary describes a PoC as code or a demonstration that proves a vulnerability exists and is exploitable, without necessarily delivering a fully weaponized exploit. TechTarget makes the same distinction in more enterprise-friendly language: a PoC exploit is meant to show the weakness in a controlled way, not to cause damage. (Pentesterlab)
That difference sounds obvious until a real engagement starts moving fast. Once a tester sees a promising sink, there is a strong temptation to keep pushing. If a reflected input triggers JavaScript execution, maybe the next step is cookie theft. If an asynchronous command injection issue produces a callback, maybe the next step is command output exfiltration. If a gateway bug leaks sensitive memory, maybe the next step is session harvesting. Technically, those next steps may be possible. Operationally, they are often the wrong next steps. A PoC is not weak because it stops early. It is strong because it proves exactly what it must prove, then preserves that proof in a way others can reproduce. HackerOne’s own quality checks lean on that standard by asking whether the vulnerability can be reproduced easily, whether the impact is clearly explained, and whether supporting materials are included in proper format. (HackerOne Help Center)
The easiest way to keep the distinction clean is to define success before you send a single request. If you are testing a reflected XSS hypothesis, is the smallest convincing signal a harmless script execution in a lab page. If you are testing blind SSRF, is the smallest convincing signal an out-of-band interaction from the target to your callback endpoint. If you are testing CSRF, is the smallest convincing signal a state-changing action triggered through a browser session that should not have been accepted. When you know the smallest convincing signal, the PoC gets easier to design and safer to run.
A practical way to think about the boundary looks like this:
| ゴール | PoC standard | Full exploit standard | Why the difference matters |
|---|---|---|---|
| Validate reality | Show the vulnerability can be triggered | Chain the vulnerability into larger impact | Validation is enough for prioritization and triage |
| Demonstrate impact | Use the minimum observable effect | Maximize access, exfiltration, or persistence | Bigger demos often increase risk without improving the argument |
| Enable remediation | Produce exact steps engineers can replay | Produce attacker-grade workflow | Fixing teams need reproducibility more than spectacle |
| Preserve safety | Stop once the issue is proven | Continue after proof to extend control | Good scope discipline depends on a clear stop condition |
The table is simple on purpose. It reflects a principle that turns up in both official testing guidance and mature tool documentation: the best proof is the one that makes the case with the least ambiguity and the least unnecessary blast radius. OWASP’s testing materials repeatedly frame security work around identifying injection points, testing exploitability, and assessing severity, not around escalating every issue to its theoretical maximum. PortSwigger’s documentation on Collaborator, CSRF PoCs, and AI-assisted issue exploration follows the same pattern: validate, review, reproduce, then decide whether more testing is justified. (OWASP財団)
How to Build a PoC in One Minute Requires Scope, Logging, and a Stop Condition
No serious team should optimize for speed before it optimizes for authorization. NIST SP 800-115 says its purpose is to help organizations plan and conduct technical tests and examinations, analyze findings, and develop mitigation strategies. FedRAMP’s penetration test guidance goes further and explicitly requires a rules-of-engagement document developed in accordance with NIST SP 800-115 Appendix B and approved before testing. Those are not bureaucratic side notes. They are the difference between security work and impulsive probing. (NIST CSRC)
In practice, a one-minute PoC requires five preconditions.
First, the target must be authorized and in scope. That sounds basic, but it matters more when the issue is easy to validate. The shorter the distance from finding to proof, the easier it is to act before thinking through blast radius. Fast does not excuse sloppy boundary control.
Second, the hypothesis must be narrow. “This application feels unsafe” is not a PoC hypothesis. “This reflected parameter may execute script in the browser” is. “This image-fetching endpoint may fetch attacker-controlled URLs” is. “This session cookie may be client-side serialized state” is. A vague suspicion burns time because it expands the search space.
Third, the effect must be observable. You need a response difference, a browser effect, a state change, a callback, a timing change, or some other signal you can capture. If you cannot name the signal, you cannot design the proof.
Fourth, the environment must preserve evidence. That means HTTP history, raw requests, timestamps, any relevant screenshots, and enough context to replay the same action later. HackerOne’s reporting guidance is not unique here; it simply states plainly what engineering teams already know. If a bug cannot be reproduced from the write-up, the report slows everyone down. (HackerOne Help Center)
Fifth, the stop condition must be explicit. This is the part many testers skip when they are excited. A stop condition answers a single question: what exact observation means I have already proved the vulnerability. For reflected XSS, it may be script execution in a lab browser. For blind SSRF, it may be a DNS or HTTP interaction at a unique callback host. For CSRF, it may be a state-changing action executed through a victim session. For client-side prototype pollution, it may be a controlled sink hit that confirms exploitability. Without that stop condition, a fast PoC turns into unbounded exploration. OWASP’s testing guide and PortSwigger’s workflow documentation both reward the opposite habit: focused validation tied to a concrete test objective. (OWASP財団)
How to Build a PoC in One Minute, The Fast Reduction Workflow
Most people waste time at the same place: they start building payloads before they finish reducing the hypothesis. The better sequence is almost always the reverse.
Reduce the attacker-controlled input
The first reduction step is to isolate exactly what the attacker controls. Not “the page,” not “the API,” not “the login flow.” One parameter. One header. One cookie. One file field. One JSON property. The more precise the attacker-controlled input, the more precise the PoC can be.
This is where many one-minute PoCs are won. A reflected parameter that lands in HTML is already most of the problem statement for reflected XSS. A URL parameter that gets fetched by server-side code is already most of the problem statement for SSRF. A state-changing POST without anti-CSRF protection is already most of the problem statement for CSRF. OWASP’s reflected XSS material defines the condition clearly: attacker-controlled input is improperly processed and returned in the victim-facing response. OWASP’s SSRF material defines the other side of the pattern just as clearly: the application fetches a remote resource based on user-supplied input and can be coerced into sending a request to an unexpected destination. (OWASP財団)
Reduce the sink
The second reduction step is to identify the smallest security-relevant sink. For browser issues, that sink might be a script context, a DOM sink, or a state-changing endpoint. For server-side issues, it might be a fetch primitive, a shell boundary, or a template engine. For auth issues, it may be a resource boundary that should reject access.
This is why a one-minute PoC is often impossible for complex business logic problems. If the sink is spread across four roles, three background jobs, and a delayed consistency model, the proof probably will not fit into sixty seconds. But if the sink is obvious and close to the input, the route to proof can be very short. PortSwigger’s documentation on DOM Invader is a good example of tool support matching this logic: detect a prototype pollution source, scan for gadgets, then test the sink with a PoC exploit. The whole workflow is built around a narrow source-to-sink path. (ポートスウィガー)

Choose the smallest effect that still proves the issue
This is the part that most directly affects safety. The smallest convincing effect is often not the biggest effect. A harmless alert is enough for reflected XSS in a lab. A single callback is enough for blind SSRF. A controlled form submission is enough for CSRF. The point is not to minimize seriousness. The point is to isolate the proof variable.
A simple control-versus-test model helps. In the control case, the input is benign and the expected security effect does not happen. In the test case, the input is altered and the effect does happen. That gap is your proof. Without the control, many PoCs are just stories. With it, they become engineering evidence.
Prefer non-destructive proofs and out-of-band confirmation
The safest fast PoCs often use non-destructive signals. OWASP’s CSRF material emphasizes that the attack targets state-changing requests, not arbitrary response viewing. PortSwigger’s CSRF PoC generator automates exactly that kind of minimal demonstration by generating HTML based on the selected request. For blind vulnerabilities, Collaborator-style workflows are even cleaner. PortSwigger’s documentation on Burp Collaborator explains the general pattern: generate a unique payload, insert it into the request, then poll for out-of-band interactions to confirm that the target made a request to your controlled domain. That turns invisible server-side behavior into visible proof without requiring a destructive follow-up. (OWASP財団)
Stop as soon as the issue is confirmed
This step sounds moralistic until you see how much time it actually saves. PortSwigger’s January 2026 write-up on functional PoCs in less than a minute is useful here because it shows what “good stopping” looks like in a real tool-driven workflow. In the SSTI example, Burp AI was given a narrow task, tested the highlighted parameter, confirmed the vulnerability, and then stopped. It ran 18 requests in 44 seconds and produced a working PoC, not an endless exploratory burst. The stopping behavior is part of what made the result good. (ポートスウィガー)
Record the proof in a replayable form
A PoC is not finished when you see the effect. It is finished when another person can replay it from your evidence. That means preserving the exact request, the context, the expected signal, the observed signal, and the assumptions. Burp’s Explore Issue documentation makes this explicit. It logs the steps taken, allows AI-generated requests to be sent into Repeater or Intruder for manual verification, and emphasizes transparency and reproducibility rather than hidden magic. That is the right model even if you are working manually. (ポートスウィガー)
A clean template looks like this:
Finding hypothesis:
Attacker controls [input] and may influence [sink].
Control:
Send the benign request and record the normal result.
Test:
Send the minimal altered request that should trigger the security-relevant effect.
Expected proof:
State exactly what signal confirms the issue.
Stop condition:
State what observation is enough and what you will not do after confirmation.
Evidence saved:
Raw request, raw response or callback record, timestamp, affected asset, role or session used.
This is not glamorous. It is effective. Most fast PoCs are just this template executed well.
One-Minute PoC Patterns for XSS, CSRF, SSRF, and Prototype Pollution
Some vulnerability classes fit the one-minute model naturally because the signal path is short and the proof variable is obvious. Others do not. The sections below focus on the classes that most often compress well.
A one-minute PoC for reflected XSS
OWASP describes reflected XSS as non-persistent input that is delivered through a single request and response and executed when the victim opens the crafted link or page. That is why reflected XSS is one of the best candidates for a fast PoC. You often have a clear input, a direct response surface, and immediate browser feedback. (OWASP財団)
In a controlled lab, the smallest convincing proof is usually a harmless script execution that shows the input crossed the trust boundary into executable context. You do not need cookie theft. You do not need a data exfiltration endpoint. You need proof that the browser executed attacker-controlled code.
A minimal local-lab example might look like this:
curl 'http://lab.local/search?q=%3Csvg/onload=alert(1)%3E'
If the vulnerable application reflects the q parameter into executable HTML or JavaScript context, the browser-rendered version of that request is enough to prove the bug. The actual value you use in a training environment can be as simple as an alert, because the point is browser code execution, not downstream abuse. The one-minute win comes from targeting the exact reflected parameter and stopping after the first clean proof.
Where testers waste time is context confusion. They try five payload families before checking whether the input is inside HTML text, an attribute, a script block, or a JavaScript string. If you spend ten seconds classifying the context first, the PoC often becomes trivial. That is reduction at work.
A one-minute PoC for CSRF
CSRF is another class that compresses well because the vulnerability is about unauthorized state change, not about stealthy deep exploitation. OWASP summarizes CSRF as forcing an authenticated user to execute unintended actions on a web application. The community page also notes that CSRF attacks target state-changing requests, such as changing an email address or password, because reading a response through the victim browser does not by itself benefit the attacker. PortSwigger’s documentation adds an operational detail that matters a lot here: Burp Suite Professional can automatically generate HTML for a CSRF PoC, which is faster and easier than writing it by hand, especially when the request has many parameters. (OWASP財団)
That means the fastest CSRF PoC is usually not a novel exploit. It is a clean replay of a state-changing request in a form the victim browser will submit. In a local training environment, the skeleton can be very small:
<html>
<body>
<form action="http://lab.local/account/email" method="POST">
<input type="hidden" name="email" value="poc@example.test">
<input type="submit" value="Submit">
</form>
<script>
document.forms[0].submit();
</script>
</body>
</html>
If the browser, while authenticated, submits that request successfully and the state changes without a valid anti-CSRF mechanism, the issue is proven. That is enough. You do not need to build a phishing scenario. You do not need to chain it into account takeover if the application’s risk model already makes the impact clear.
The fastest CSRF testers do two things right. They first confirm that the target request is state-changing and interesting. Then they reproduce it with the smallest possible HTML. Everything else is noise.
A one-minute PoC for blind SSRF
Blind SSRF looks harder until you realize that it often gives you a cleaner stop condition than reflected issues do. OWASP’s SSRF material describes the core pattern as a server-side application fetching a remote resource based on user-supplied input, allowing an attacker to coerce requests to unexpected destinations. PortSwigger’s documentation on blind SSRF says the easiest and most effective way to test this is out-of-band: inject a unique Collaborator domain, then monitor for any incoming interaction. If the application reaches out, the server-side fetch happened. That is your proof. (OWASP財団)
A harmless placeholder request in a lab can be conceptualized like this:
GET /fetch?url=https://callback.example/poc-123 HTTP/1.1
Host: lab.local
The application may never reflect the fetched content back to you. It does not need to. If the callback service sees an interaction from the target, the vulnerability is established. That is why blind SSRF can be a great one-minute PoC candidate: input point, callback token, confirmation, done.
The common mistake is to chase internal metadata endpoints or internal service abuse too early. Those may be valid follow-on questions, but they are not required for the PoC. The callback proves that untrusted input controls a server-side fetch. That alone can be severe depending on network layout and egress policy. Proof first, chain later.
A one-minute PoC for asynchronous command injection
Asynchronous command injection is similar in structure to blind SSRF. PortSwigger describes it as command injection where the command is executed asynchronously and has no noticeable impact on the application response. The same documentation explains why Collaborator-style out-of-band confirmation works: inject a benign command that triggers a network interaction, then poll the callback service. If the interaction appears, the command ran. (ポートスウィガー)
The important lesson is that the proof should be about execution, not about harvesting arbitrary command output on the first pass. PortSwigger’s follow-up documentation does show how a tester can exfiltrate data through the out-of-band channel after confirmation, but that is exactly the boundary to treat carefully. In many authorized engagements, command execution confirmation is enough for the vulnerability to be triaged at the highest level. The one-minute model favors that narrow proof because it reduces risk and reduces debate. (ポートスウィガー)

A one-minute PoC for client-side prototype pollution
Client-side prototype pollution used to feel slower because the source-to-sink path was not always obvious. PortSwigger’s DOM Invader tooling changes that by turning a lot of the discovery and sink-scanning work into a guided workflow. The official documentation says DOM Invader can automatically detect prototype pollution sources, scan for gadgets, and use discovered sources to pollute Object.prototype as a proof of concept. Once a sink is identified, clicking Exploit tests it with a PoC exploit and confirms whether the issue is exploitable. (ポートスウィガー)
That is a good example of why some “one-minute PoCs” are really “one-minute confirmations after good preparation.” The environment, the instrumented browser, and the source detection do a lot of the hard work up front. But once the input path is known, the actual proof can be very fast.
Which classes usually fit the model best
| 脆弱性クラス | Best minimal proof | Why it is fast | Where testers overdo it |
|---|---|---|---|
| 反射型XSS | Harmless script execution in a lab browser | One request, one response, direct effect | Jumping to theft or persistence |
| CSRF | State-changing request replayed through victim session | Simple request replay with visible state change | Building social engineering instead of validating the control failure |
| ブラインドSSRF | Unique callback interaction | Proof does not require reflected content | Targeting sensitive internal resources before confirmation |
| Async command injection | Benign execution callback | No need for visible response change | Exfiltrating command output before the issue is already proven |
| Prototype pollution | Controlled sink hit through discovered gadget | Tooling can shorten source-to-sink confirmation | Turning a browser proof into a bigger client-side chain too early |
The pattern running through all five cases is the same. The fastest PoC is the one with the shortest path between controllable input and unambiguous signal.
Why Some Findings Resist the One-Minute PoC Model
If all security bugs fit the patterns above, public PoCs would be easier to write and easier to reproduce than they actually are. The data says otherwise. A 2025 arXiv preprint on the real-world usability of vulnerability PoCs collected 470,921 PoCs and associated reports from 13 platforms and found that 78.9 percent of CVE vulnerabilities lacked available PoCs. It also found that existing PoC reports typically missed about 30 percent of the essential components needed for effective understanding and reproduction. (arXiv)
That result lines up with older empirical work as well. A USENIX Security 2018 paper on the reproducibility of crowd-reported vulnerabilities evaluated 368 real-world cases, spent 3,600 analyst-hours on reproduction experiments, and found both missing information and low reproducibility. The paper explicitly says relying on a single public vulnerability report from a popular forum is generally difficult because the report is incomplete. (USENIX)
The implication is straightforward: many findings do not compress into a one-minute PoC because the missing pieces are the whole problem. A stored XSS issue may require another user, another page view, or a specific moderation workflow. OWASP’s stored XSS material calls it the most dangerous type of XSS precisely because the application stores the input and a later viewing action triggers the effect. That delayed model is more realistic and often more severe, but it is less friendly to the single-request proof pattern. (OWASP財団)
The same is true for business logic abuse, multi-step authorization flaws, race conditions, and deserialization problems with environment-specific gadget chains. Even PortSwigger’s own “functional PoCs in less than a minute” article, which is genuinely impressive, uses carefully scoped lab contexts and narrow prompts. The SSTI example was fast because the parameter reflection had already been noticed and the prompt told the AI to stop on confirmation. The deserialization example was fast for similar reasons: the cookie format and likely behavior were already narrowed down. The article is useful not because it proves every PoC can be instant, but because it demonstrates how much speed comes from pre-reduction and context. (ポートスウィガー)
So the honest answer to “How do you build a PoC in one minute” is sometimes “You do not.” You can only do it when the vulnerability class, target context, observability, and pre-analysis make that reduction possible. Pretending otherwise leads to bad validation, broken scope discipline, and lower trust in the final report.
CVEs That Show When a Fast PoC Works and When It Becomes Dangerous
The most useful way to understand one-minute PoCs is to look at famous CVEs and ask a narrower question than most blog posts ask. Not “How bad was it.” Not “Was there public exploit code.” Ask instead: what was the smallest convincing proof, and how much risk did even that small proof carry.
Log4Shell, the classic case of a fast conceptual PoC
CVE-2021-44228 is still the clearest example of why a tiny proof can be enough. Apache’s official security page says the vulnerable condition was in Log4j’s JNDI features, where configurations, log messages, and parameters did not protect against attacker-controlled LDAP and related endpoints. The page identifies affected log4j-core versions as 2.0-beta9 through 2.15.0 in the relevant branches and lists fixes in 2.3.1, 2.12.2そして 2.15.0 depending on Java version. NVD describes the vulnerability in similar terms, stating that an attacker who can control log messages or parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. (Apache Logging Services)
What made Log4Shell such a fast PoC case was not just the severity. It was the simplicity of the proof condition. If attacker-controlled input reached a logged lookup sink and the environment performed the external JNDI resolution, the vulnerability could often be established with a single carefully crafted request and an out-of-band observation. The right lesson from that history is not “go for RCE first.” The right lesson is that a callback was usually a better proof than a larger exploit path, especially in production-like environments.
Apache’s later notes also show why even famous “one-shot” bugs need careful reading. The same security page documents that the 2.15.0 fix for CVE-2021-44228 was incomplete in certain non-default configurations, leading to CVE-2021-45046 and fixes in 2.16.0, 2.12.3そして 2.3.1. In other words, fast proof never removed the need for precise version and configuration analysis. It only accelerated the confirmation step once the path was understood. (Apache Logging Services)
The operational lesson still matters in 2026. A good Log4Shell-style PoC proves input-to-sink reachability and environment behavior. It does not need to become a shell session to be persuasive.
Citrix Bleed, when even a minimal PoC can be too risky to treat casually
CVE-2023-4966, better known as Citrix Bleed, is the opposite kind of lesson. NVD describes it as sensitive information disclosure in NetScaler ADC and NetScaler Gateway when configured as a Gateway or AAA virtual server. That sounds narrower than a remote code execution bug, but the operational reality was severe. In NetScaler’s October 2023 public update, the vendor said it had reports of incidents consistent with session hijacking and credible reports of targeted attacks exploiting the vulnerability. The same post urged affected customers to update immediately, stated that no workarounds were available, recommended killing active and persistent sessions after patching, and explicitly said technical details were being limited to protect customers from further exploitation. (NVD)
This is exactly the kind of CVE that exposes the limit of the “just prove it quickly” mindset. NVD later recorded third-party PoC references for the issue, which tells you public proof material existed. But when the bug class involves leaking sensitive memory and potentially live session material, even a “minimal” external proof can cross into real user impact very quickly. (NVD)
That does not make PoC thinking irrelevant. It makes it more precise. The right question for defenders was not “Can I personally see leaked bytes from the internet-facing appliance right now.” The right question was “Am I on an affected build and role, are targeted attacks already happening, and have I patched and invalidated sessions.” NetScaler’s own guidance answers that operationally. If you are using an affected build in the gateway or AAA roles, update immediately and clear sessions. There was no vendor-supported workaround to rely on instead. (NetScaler)
For practitioners, Citrix Bleed is a reminder that “fast proof” is a testing pattern, not a moral blank check. If the smallest proof itself risks touching live secrets, the safer move may be version verification, vendor remediation, and internal validation in a lab clone rather than casual internet testing.
PHP-CGI CVE-2024-4577, a fast PoC that depends completely on environment facts
CVE-2024-4577 is a very different kind of fast-validation case. NVD says the issue affects PHP 8.1 before 8.1.29, 8.2 before 8.2.20, and 8.3 before 8.3.8 when using Apache and PHP-CGI on Windows in certain code-page conditions. The root problem is Windows “Best-Fit” character replacement leading PHP-CGI to misinterpret arguments, potentially allowing source disclosure and arbitrary code execution. The PHP CNA score is 9.8. (NVD)
DEVCORE’s disclosure adds the environmental nuance that matters for any PoC discussion. Their write-up says the issue bypasses the earlier protection for CVE-2012-1823, affects all supported PHP versions on Windows, and was verified as directly exploitable on Traditional Chinese, Simplified Chinese, and Japanese code pages. It also notes that common Apache-to-PHP-CGI configurations are affected and that the default XAMPP for Windows exposure pattern is vulnerable. DEVCORE explicitly recommends asset assessment, usage verification, and upgrades rather than assuming all Windows deployments behave identically. (DEVCORE 戴夫寇爾)
This is the perfect case study for a central point about one-minute PoCs. A proof may be fast only because the environment has already satisfied a long list of preconditions. If the server is Windows, if PHP is reachable in CGI mode, if the code page is one of the vulnerable ones, and if the front-end mapping exposes the right path, then validation can become very short. If those conditions are not confirmed, public exploit snippets are not evidence. They are hypotheses.
Government and CERT-style sources also underscore the urgency side. CISA’s Known Exploited Vulnerabilities catalog includes CVE-2024-4577, and Singapore’s CSA said publicly available PoC code had been reported and that successful exploitation could allow unauthenticated remote code execution. That does not change the logic of safe testing, but it does reinforce the prioritization message. When the environment matches, this is not a theoretical edge case. (CISA)
The broader lesson is simple. A one-minute PoC is not just about vulnerability class. It is also about how much environment truth you already have.
AI and the One-Minute PoC, Faster Validation With Human Control
The most meaningful change in the last two years is not that AI suddenly made PoCs magical. It is that AI shortened the path from a narrow hypothesis to a narrow proof when the context is already structured.
PortSwigger’s current Burp AI documentation is a good example of how mature vendors are framing this. The Burp AI overview says AI-powered features are designed to enhance the testing workflow, help uncover vulnerabilities more efficiently, and keep the user in control. Burp AI in Repeater can analyze a suspicious request, test for a specific vulnerability, or suggest next steps. Explore Issue is described more specifically as an AI-powered pentesting assistant that performs automated follow-up investigations on findings identified by Burp Scanner, helping validate issues, generate PoC exploits, and uncover additional attack vectors. The same Explore Issue documentation emphasizes transparency and reproducibility: every step is logged, requests can be sent into Repeater or Intruder for manual investigation, and the user can pause or stop the task. (ポートスウィガー)
That framing matters. It treats AI as a compression layer over analyst work, not a replacement for analyst judgment. PortSwigger’s January 2026 write-up on functional PoCs in less than a minute makes the point concrete. In one lab example, Burp AI tested a highlighted message parameter for XSS or SSTI, ran 18 requests in 44 seconds, spent about €0.43 in credits, and produced a working SSTI PoC. The author’s prompt explicitly told the system to focus on a specific parameter, use specific confirmation criteria, and stop immediately on proof. That is why the run was both fast and clean. (ポートスウィガー)
The most important word in that story is not “AI.” It is “focused.” Narrow context is what enables fast proof. A human who knows where to point the assistant changes the economics of confirmation. Instead of spending several minutes generating attack ideas, enumerating payload families, and reviewing diffs manually, the tester delegates that local search to a system that can iterate quickly and keep notes.
Still, there are hard limits. A 2025 arXiv preprint on generating web vulnerability PoCs with LLMs evaluated GPT-4o and DeepSeek-R1 across 100 real-world reproducible CVEs. The authors report that with only public data, the models generated working PoCs in 8 percent to 34 percent of cases. Supplying contextual code improved results by 17 percent to 20 percent, and adaptive reasoning strategies raised success rates to 68 percent to 72 percent. Those numbers are interesting, but they also tell a humbling story. Public descriptions alone are often not enough. Context matters. Refinement matters. Human direction still matters. And because this is a preprint rather than a standards document, it should be read as strong research signal rather than settled operational doctrine. (arXiv)
A second 2025 preprint reinforces the same conclusion from another angle. The large-scale PoC usability study found that most CVEs do not even have available PoCs and that existing reports are often missing essential components. If the raw material is incomplete, AI does not remove the uncertainty. It just helps search through it faster. The older USENIX reproduction study arrives at a similar conclusion from practitioner labor rather than LLM evaluation: public reports are frequently incomplete and hard to reproduce without extra manual debugging and inference. (arXiv)
The right takeaway is that AI changes the slope of the work, not the nature of the work. It gets you to a likely proof path faster. It can reduce repetitive reasoning, generate candidate requests, and preserve step logs. It does not erase scope boundaries, legal boundaries, missing environment facts, or the need to define a stop condition. In that sense, the best AI-assisted PoC work still looks like classic good testing. The inputs are tighter. The loops are faster. The evidence is cleaner. The human remains accountable.
Turning a Fast PoC Into Evidence Engineers Can Actually Use
Security teams do not fix PoCs. They fix reproducible evidence attached to a real system, version, trust boundary, and observed behavior. That is why the last twenty percent of a fast PoC often matters more than the first eighty percent.
HackerOne’s guidance is blunt in the right way. Before submitting, the reporter should ask whether the vulnerability can be reproduced easily, whether the impact is clearly explained, whether supporting materials are included, and whether logs and code are formatted properly. Those are not platform-specific habits. They are the baseline for any bug that needs to survive triage and move into engineering. (HackerOne Help Center)
A good evidence bundle usually includes these elements:
| Evidence element | なぜそれが重要なのか | Common failure mode |
|---|---|---|
| Asset and endpoint | Tells engineering where to look | Vague target descriptions |
| 前提条件 | Explains session, role, feature flag, or config assumptions | Hidden setup steps |
| Control request | Shows normal behavior | No baseline for comparison |
| Test request | Shows the altered input that triggers the issue | Missing exact request |
| Observable effect | Defines the proof signal | Hand-wavy “it looked vulnerable” claims |
| Impact statement | Ties the proof to a security consequence | Severity without explanation |
| Remediation direction | Helps engineering move faster | Report stops at demonstration |
| Regression check | Prevents reintroduction after the fix | No post-fix validation plan |
A lightweight Markdown bundle works well because it is portable across bug bounty platforms, engineering tickets, internal wikis, and audit artifacts:
## Finding
Reflected XSS in the `q` parameter on `/search`
## Asset
https://target.example/search
## Preconditions
No authentication required
## Control
Request:
GET /search?q=test
Observed result:
Input is reflected as plain text, no script execution
## Test
Request:
GET /search?q=<payload>
Observed result:
Payload executes in browser context in controlled lab replay
## Why this proves the bug
Attacker-controlled input crosses into executable client-side context
## Security impact
An attacker can execute arbitrary browser-side script in the victim context
## Safe stop condition
Proof ends at controlled script execution in a lab browser
## Suggested fix
Apply contextual output encoding and remove unsafe rendering in the sink
## Regression check
Replay the same request after the fix and confirm the payload is no longer executable
That kind of bundle is more useful than a flashy screen recording with no raw request attached. It also makes retesting much easier. NIST SP 800-115 centers testing around planning, execution, analysis, and mitigation strategy development. A PoC that cannot flow into those phases is incomplete no matter how quickly it was produced. (NIST CSRC)
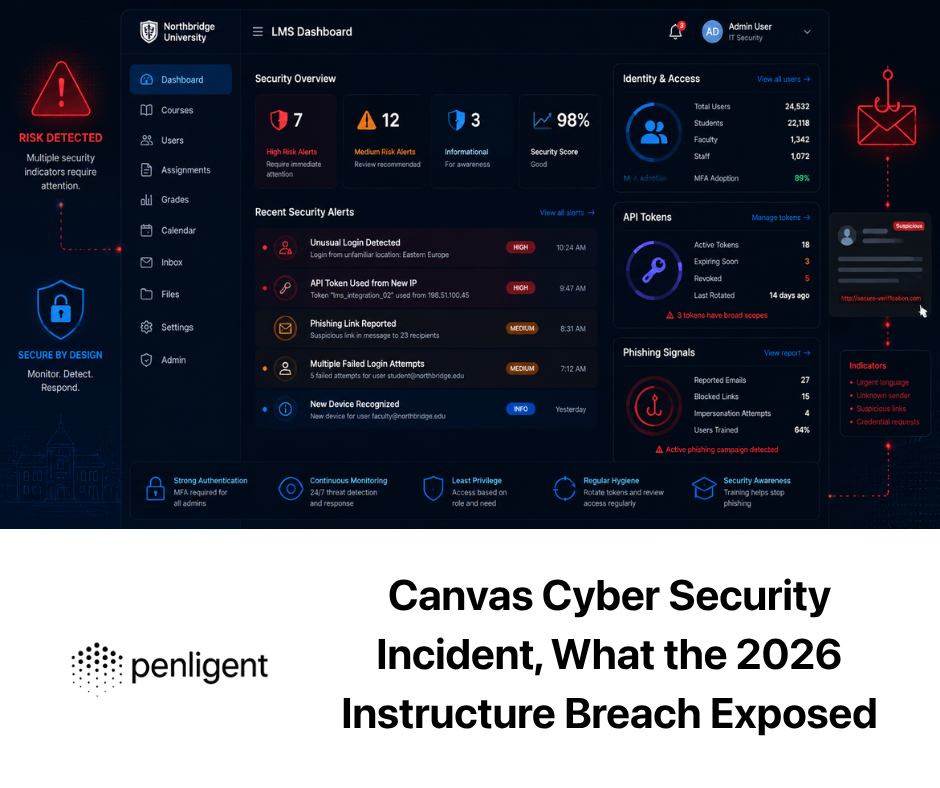
There is a practical tooling angle here too. Penligent’s public overview page describes the platform as an AI-powered penetration testing workflow that merges tools such as nmap, Metasploit, Burp Suite, and SQLmap into a unified process from asset discovery through validation and report generation. Its current pricing page says the platform supports 200-plus pentest tools on demand and can export PDF and Markdown reports with evidence and reproduction steps; the Pro plan also advertises one-click exploit reproduction with evidence-chain reporting. Read carefully, that is not most useful as a “do hacking for me” promise. It is most useful when your bottleneck is preserving evidence quality and repeatability across multiple findings and repeated retests. (寡黙)
A related Penligent workflow article makes a second point worth borrowing even if you never use the product. It recommends separating suspected findings from confirmed ones and requiring regression proof for confirmed findings. That is exactly the discipline a fast PoC should feed into. A quick proof is not the end state. It is the moment a finding stops being a suspicion and becomes a tracked engineering fact that can be revalidated after the fix. (寡黙)
A Practical Pipeline for Building Fast, Minimal, Reproducible PoCs
The best PoC builders tend to follow the same operational rhythm even when they use different tools.
They begin with structure, not payloads. They map the input, the sink, and the expected signal. They preserve a control case before touching the test case. They choose the least destructive effect that still proves the issue. They stop as soon as the issue is established. They package the proof so someone else can replay it. That pattern works whether the tooling is entirely manual, partly AI-assisted through something like Burp AI, or orchestrated across a larger validation workflow.
A minimal pipeline for a team looks like this:
- Triage the finding into a narrow hypothesis.
Strip away everything vague. Name the input, sink, and expected signal. - Decide whether the class fits the one-minute model.
Reflected XSS, CSRF, blind SSRF, async command injection, and instrumented client-side issues often do. Multi-step auth logic and environment-heavy RCE often do not. - Choose the smallest acceptable proof.
Browser execution, callback, state change, or sink confirmation. - Capture the control first.
Baselines reduce debate. - Run the test once, then stop on confirmation.
Do not “keep exploring” unless the scope and objective justify it. - Package evidence immediately.
Requests, responses, callbacks, timestamps, role assumptions, and next actions. - Tie the PoC to remediation and retest.
A security proof that cannot become a regression check is less valuable than it looks.
That sequence sounds ordinary because it is. The point of a one-minute PoC is not that it invents a new methodology. The point is that it rewards disciplined execution of an old one.
The Real Skill Behind a One-Minute PoC
The most underrated security skill is not payload memorization. It is knowing when you already have enough proof.
That is what lets one tester spend ten minutes chasing a finding while another tester proves it in forty seconds. The second tester is not necessarily smarter, braver, or using a more exotic toolkit. Often they are just asking a better question: what is the smallest observation that would make a reasonable engineer, triager, or customer agree that this is real.
Once you adopt that mindset, a lot of security work gets cleaner. Reflected XSS becomes a context classification problem instead of a payload contest. Blind SSRF becomes a callback confirmation problem instead of an internal network adventure. CSRF becomes a state-change replay problem instead of an overproduced demo page. Even AI fits the picture better. The best AI-assisted workflows are the ones that reduce local search and documentation cost while preserving human control, step visibility, and manual verification. PortSwigger’s Burp AI documentation explicitly leans into that philosophy, and the current research literature supports the same conclusion from the other direction: context-rich, well-structured problems are the ones machines help with most. (ポートスウィガー)
A one-minute PoC is therefore not really about time. It is about precision. If you can explain the exact input, the exact sink, the exact observable effect, and the exact stop condition in a few sentences, the proof itself often becomes easy. If you cannot, no tool is going to rescue the process completely.
Further Reading on Fast PoC Validation and Reproducible Proof
For authoritative external reading on testing method and minimal proof design, the strongest public material is still the combination of OWASP’s Web Security Testing Guide sections on reflected XSS, stored XSS, CSRF, and SSRF, plus PortSwigger’s official documentation on generating CSRF PoCs, using Burp Collaborator for blind vulnerabilities, testing asynchronous command injection, using DOM Invader for prototype pollution, and reviewing step-by-step AI issue exploration logs. (OWASP財団)
For testing discipline and evidence expectations, NIST SP 800-115 remains a foundational public reference, and HackerOne’s quality report guidance is a useful shorter operational checklist. For real CVE grounding, Apache’s Log4j security page, NVD’s entries for CVE-2021-44228, CVE-2023-4966, and CVE-2024-4577, NetScaler’s advisory update on Citrix Bleed, and DEVCORE’s disclosure on PHP-CGI are all worth keeping close when you think about the difference between a fast proof and a dangerous overreach. (NIST CSRC)
For related Penligent reading that naturally extends this topic, the most relevant public pages are Penligent.aiの自動ペネトレーションテストツールの概要, Penligent Pricing, Exploit DB in 2026そして Claude Code Security and Penligent: From White-Box Findings to Black-Box Proof. Those pages are useful here because they focus on workflow shape, evidence handling, validation, and the difference between suspected and confirmed issues rather than treating vulnerability testing as a black box. (寡黙)