Enterprise defenders see critical CVEs every week. Most of them matter. A smaller subset changes how you think about trust inside the network.
CVE-2026-22769 belongs in that second category.
This vulnerability affects Dell RecoverPoint for Virtual Machines (RP4VMs), and Dell/NVD describe it as a hardcoded credential issue that can allow an unauthenticated remote attacker (with knowledge of the credential) to gain unauthorized access to the underlying operating system and potentially achieve root-level persistence. Dell’s advisory and the NVD entry both frame it as a critical issue and urge immediate remediation. (NVD)
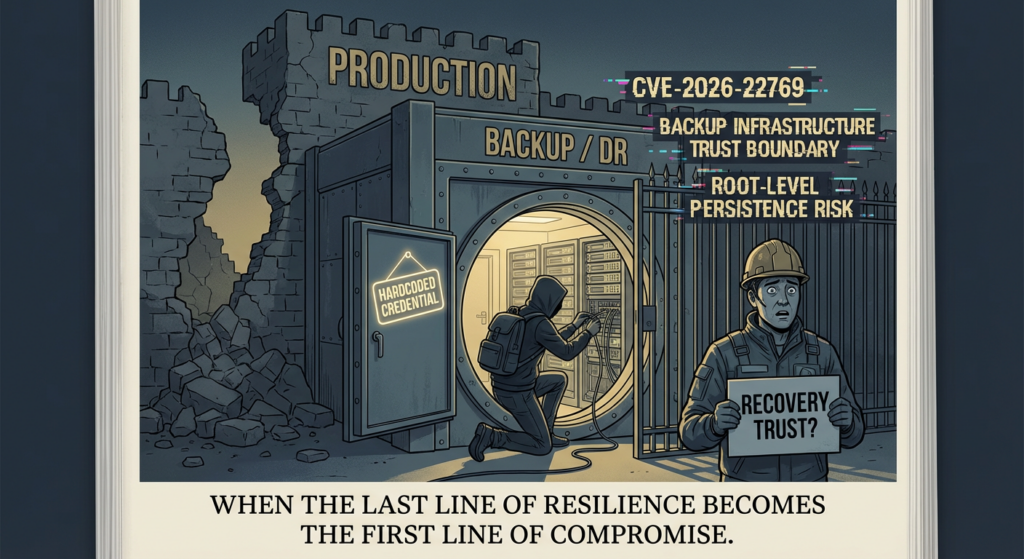
What makes this incident more than “another CVSS 10” is where it lives: backup and disaster recovery infrastructure. These systems are often deployed in trusted internal zones, connected to highly privileged management paths, and expected to be the last line of resilience when everything else goes wrong. When that layer becomes the intrusion beachhead, the technical impact and the operational impact collide.
This article is written for security engineers, incident responders, infrastructure owners, and technical leaders who need a practical, evidence-driven response. It covers what the CVE is, why the public reporting matters, how to triage exposure, what to hunt for, how to validate remediation, and how to think about this class of bug as a recurring design failure rather than a one-off patch cycle event. It also includes detection-oriented code snippets and a validation checklist you can adapt in production.
What CVE-2026-22769 Is
Dell’s advisory (DSA-2026-079) and the NVD entry are the authoritative starting points.
Dell states that RecoverPoint for Virtual Machines versions prior to 6.0.3.1 HF1 contain a hardcoded credential vulnerability, and describes the risk as potentially enabling unauthorized access to the underlying operating system and root-level persistence. Dell assigns a CVSS v3.1 base score of 10.0, with vector AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H. (Dell)
NVD mirrors the core description, lists the weakness as CWE-798 (Use of Hard-coded Credentials), and records the same CVSS vector. NVD also reflects KEV-related updates from CISA in its change history and summary fields. (NVD)
Why the CVSS vector matters here
The vector is not just a severity label. It maps directly to why defenders should treat this as a top-tier response item:
- AV:N (Network): reachable over a network path, not a local-only issue. (NVD)
- AC:L (Low complexity): exploitation conditions are not unusually fragile. (NVD)
- PR:N (No privileges) 그리고 UI:N (No user interaction): no existing account and no user click are required. (NVD)
- S:C (Scope changed): compromise can cross the vulnerable component’s trust boundary. (NVD)
- C/I/A:H: full-spectrum business risk, not just information disclosure. (NVD)
The weakness class: CWE-798
MITRE CWE-798 describes hard-coded credentials as a class of weakness where the product contains fixed credentials (passwords, keys, or equivalent secrets) used for authentication or other security-sensitive functions. The core security problem is that once the credential becomes known or extractable, authentication assurance collapses. (CWE)
In practical terms, hardcoded credentials are not “just another secret leak.” They are often more dangerous than accidentally exposed environment variables because they can be built into product logic, replicated across deployments, and difficult for customers to rotate independently.
Why This Is More Dangerous in Backup and DR Infrastructure
If this were a hardcoded credential in a low-value edge tool, it would still be urgent. In backup and disaster recovery infrastructure, the blast radius is structurally larger.
Dell RecoverPoint for Virtual Machines is a replication and recovery platform used in VMware environments. That deployment context matters because backup/DR systems typically have:
- Broad visibility into protected workloads
- Trusted positioning inside internal networks
- Operational exceptions (legacy connectivity, service accounts, management ports)
- Lower day-to-day scrutiny than internet-facing applications
- High business criticality during incident response and recovery
Google GTIG/Mandiant’s reporting reinforces this concern by showing how compromise around this ecosystem was used in larger intrusion activity, including movement into VMware virtual infrastructure and follow-on operations. (Google 클라우드)
This is the strategic reason CVE-2026-22769 deserves attention beyond the CVE score. A compromise in backup infrastructure can create three simultaneous failures:
- Intrusion foothold
- Persistence pathway
- Recovery trust degradation
That third failure is the one many organizations underestimate. If defenders are unsure whether recovery systems or management planes are clean, recovery operations slow down at exactly the worst time.
What Public Reporting Added Beyond the CVE Summary
A lot of CVE writeups stop at “affected versions + patch now.” That is not enough for CVE-2026-22769, because the public reporting provides concrete defender value.
Google Cloud’s GTIG/Mandiant post describes how investigators identified exploitation while investigating compromised Dell RecoverPoint for Virtual Machines appliances associated with BRICKSTORM and GRIMBOLT activity. The writeup notes requests using the username 관리자 to the installed Apache Tomcat Manager, deployment of a malicious WAR containing a SLAYSTYLE web shell, and identification of hardcoded credentials for the 관리자 user in Tomcat configuration (/home/kos/tomcat9/tomcat-users.xml). The report also notes that an attacker with those credentials could authenticate to Tomcat Manager, upload a malicious WAR via /manager/text/deploy, and execute commands as root on the appliance. (Google 클라우드)
The report further states the earliest identified exploitation activity was in mid-2024, which materially changes prioritization discussions for defenders who might otherwise treat the issue as “new but not yet weaponized.” (Google 클라우드)
TTPs that matter for defenders
The same Google GTIG/Mandiant report highlights additional observed activity beyond the initial appliance exploitation, including:
- “Ghost NICs” for stealthy pivoting inside VMware environments
iptablesbased Single Packet Authorization (SPA)-style behavior on compromised vCenter appliances- Malware families including BRICKSTORM, SLAYSTYLE, and GRIMBOLT
- Investigative artifacts and log paths defenders can check immediately (Google 클라우드)
Even if your environment shows no evidence of these specific families, the operational lesson stands: this CVE should be handled as a compromise possibility, not only a patch management ticket.
CISA KEV Status and Why It Changes Triage Conversations
NVD reflects that CVE-2026-22769 was added to CISA’s Known Exploited Vulnerabilities (KEV) catalog, including the date added and due date information, and the required action language tied to vendor guidance. (NVD)
This matters for two reasons.
First, KEV status is one of the strongest public prioritization signals because it indicates evidence of exploitation in the wild, not just theoretical severity. Second, even for organizations outside U.S. federal mandates, KEV inclusion is widely used as an internal risk-ranking accelerator by SOCs, vuln management teams, and security leadership.
If you are building a remediation queue and CVE-2026-22769 is sitting beside non-exploited CVSS 9.x issues, the KEV signal is a defensible reason to move it to the top.
What Security Engineers Are Actually Searching For Right Now
There is no public dashboard that exposes exact Google click-through rate (CTR) per query for this CVE across the open web. So the right way to talk about “highest-click” intent is to be explicit: this section is based on current SERP patterns and repeated phrasing in authoritative and high-visibility coverage (Dell, NVD, Google GTIG/Mandiant, and major cybersecurity outlets), not private CTR telemetry. (NVD)
Based on the current results landscape, the dominant search-intent clusters around CVE-2026-22769 appear to be:
1) Immediate risk framing
Searches like:
- “CVE-2026-22769”
- “Dell RecoverPoint zero-day”
- “Dell RecoverPoint hardcoded credential”
- “CVE-2026-22769 actively exploited”
These map to the “What is it / am I affected / how urgent is this” intent. The repeated emphasis on “critical,” “actively exploited,” and “zero-day” in coverage is a strong signal. (Cybersecurity Dive)
2) Patching and remediation
Searches like:
- “Dell DSA-2026-079”
- “RecoverPoint 6.0.3.1 HF1”
- “CVE-2026-22769 remediation script”
This is the operational owner’s intent. Dell’s advisory is the source of truth for affected versions and remediation paths (upgrade vs remediation script, depending on branch). (Dell)
3) Threat intelligence and intrusion context
Searches like:
- “UNC6201 Dell RecoverPoint”
- “BRICKSTORM GRIMBOLT RecoverPoint”
- “SLAYSTYLE Tomcat Manager WAR”
This is where security engineers move after initial patch awareness. They want evidence, not just advisories. Google’s GTIG/Mandiant report is the anchor here. (Google 클라우드)
4) Detection and hunting
Searches like:
- “Tomcat manager deploy log CVE-2026-22769”
- “RecoverPoint forensic artifacts”
- “IOCs GRIMBOLT BRICKSTORM”
The Google writeup directly supports this intent with log paths, file locations, and detection opportunities. (Google 클라우드)
The practical SEO/GEO takeaway for your article (without turning the article into an SEO memo) is simple: if you cover these four intent clusters well, you cover what serious readers actually need.
Affected Versions and Remediation Paths
Dell’s DSA-2026-079 advisory should be treated as authoritative for version-specific remediation. The advisory lists affected branches and provides upgrade and/or remediation script options for different lines, including explicit guidance for 5.3 SP4 P1 and multiple 6.0 service pack variants. It also notes that older 5.3 versions and potentially earlier versions may be impacted and should be upgraded into a supported path before applying the remediation steps. (Dell)
Dell also notes an important deployment assumption: RecoverPoint for Virtual Machines is intended to be deployed in a trusted, access-controlled internal network and is not intended for use on untrusted/public networks. That statement is useful context, but it should not be misunderstood as a mitigation substitute. If a system is exposed through internal pathways, VPN, jump hosts, flat segments, or compromised adjacent systems, the risk remains operationally real. (Dell)
Quick triage table for engineering teams
| 질문 | 중요한 이유 | What to check first |
|---|---|---|
| Do we run Dell RecoverPoint for Virtual Machines? | Scope confirmation | CMDB, virtualization platform owners, backup/DR team inventory |
| Which version/branch? | Dell remediation path depends on branch | Appliance UI / package version evidence / vendor docs |
| Is it internet-exposed or broadly reachable internally? | Determines immediate containment urgency | Firewall rules, mgmt VLANs, VPN reachability, reverse proxies |
Do logs show Tomcat Manager /관리자 access? | Direct clue from public exploitation reporting | Tomcat/RP4VM logs, web logs, audit logs |
| Any WAR deployment traces or anomalous files? | Possible post-exploitation evidence | Tomcat deploy/cache dirs, catalina logs |
| Has the remediation been applied and validated? | Patch status ≠ closure | Version verification + forensic checks + traffic monitoring |
Exposure Triage Playbook You Can Run This Week
This section is intentionally operational. The goal is to reduce both false reassurance and unnecessary panic.
Phase 1: Confirm asset existence and ownership
Before security teams start scanning at scale, identify the system owners and operational windows. Backup and DR platforms are often change-sensitive and tied to recovery SLAs. A rushed, unsynchronized change can create avoidable business risk.
Actions:
- Identify all RP4VM instances and environments (prod, DR site, test, legacy).
- Map business owners and on-call contacts.
- Record version evidence, not just verbal statements.
- Confirm maintenance windows and recovery obligations.
Phase 2: Prioritize by reachability and criticality
Treat “public exposure” as urgent, but do not treat “internal only” as safe. Internal management-plane compromise is a common path in real-world intrusions.
Prioritization factors:
- Externally reachable management interfaces
- Broad east-west reachability
- Co-location with vCenter / hypervisor management paths
- Presence in highly regulated or mission-critical environments
- Evidence of suspicious traffic or prior intrusions
Phase 3: Apply vendor remediation path
Use Dell DSA-2026-079 as the source of truth for:
- Affected version branch
- Upgrade target (
6.0.3.1 HF1) - Whether remediation script is applicable
- Upgrade staging requirements for older branches (e.g., 5.3 → 6.x pathing) (Dell)
Phase 4: Validate, don’t just patch
A patched appliance can still be compromised if exploitation occurred before remediation. This is the point many organizations miss.
Minimum validation includes:
- Version verification
- Historical log review
- Current file integrity/path review around Tomcat deployment areas
- Outbound traffic review for unexpected destinations
- Persistence checks
- Adjacent VMware management infrastructure review (if exposure likely)
Detection and Forensic Leads From Public Reporting
This is where the Google GTIG/Mandiant writeup is especially useful. It gives defenders concrete artifacts to investigate.
The report highlights:
- Requests to Tomcat Manager
/관리자 - Potentially malicious deployment patterns such as
PUT /manager/text/deploy?... - Tomcat and application log locations
- WAR upload and compiled artifact directories
- Related malware families and IOC availability via a GTI collection for registered users (Google 클라우드)
High-value artifact paths and patterns
Google’s writeup specifically calls out:
/home/kos/auditlog/fapi_cl_audit_log.log(check for/관리자access; suspicious if present)/var/lib/tomcat9(uploaded WAR files)/var/cache/tomcat9/Catalina(compiled artifacts)/var/log/tomcat9/(Catalina / Localhost logs around WAR deployment events) (Google 클라우드)
Practical hunting questions
- Do you see any
Tomcat Manageraccess in periods where no legitimate maintenance occurred? - Were there deploy events tied to unusual source IPs?
- Are there WAR files or compiled artifacts that do not map to approved software updates?
- Did file writes cluster around suspicious authentication or web requests?
- Did the appliance initiate unusual outbound connections after Tomcat deployment activity?
Detection Engineering Examples
The snippets below are defensive detection and validation examples, not exploitation guidance. They are intended as starting points for SOC and IR teams.
Example 1: Log grep for suspicious Tomcat Manager deploy access on Linux appliances
# Defensive triage only: look for Tomcat Manager access and deploy endpoints
# Adapt paths based on your environment and retention model.
LOGS=(
"/home/kos/auditlog/fapi_cl_audit_log.log"
"/var/log/tomcat9/catalina.out"
"/var/log/tomcat9/localhost_access_log.*"
)
for f in "${LOGS[@]}"; do
if ls $f >/dev/null 2>&1; then
echo "==== Checking $f ===="
grep -E -i "/manager|/manager/text/deploy|HostConfig\\.deployWAR|PUT .*manager/text/deploy" $f | tail -n 200
fi
done
This aligns with the public reporting’s focus on Tomcat Manager requests and WAR deployment indicators. (Google 클라우드)
Example 2: Sigma-style rule idea for suspicious Tomcat WAR deployment (web/app logs)
title: Suspicious Tomcat Manager WAR Deployment on Backup Appliance
id: 9f6e8b3d-2d1c-4f1d-a8de-cve-2026-22769-hunt
status: experimental
description: Detects suspicious Tomcat Manager deploy requests and deployment events consistent with public reporting around CVE-2026-22769 investigations.
references:
- Dell DSA-2026-079
- NVD CVE-2026-22769
- Google GTIG/Mandiant report on UNC6201 exploitation
logsource:
product: linux
category: webserver
detection:
selection_uri:
message|contains:
- "/manager/text/deploy"
- "/manager"
selection_method:
message|contains:
- "PUT "
- "POST "
selection_hostconfig:
message|contains:
- "HostConfig.deployWAR"
condition: (selection_uri and selection_method) or selection_hostconfig
falsepositives:
- Legitimate administrative deployment activity
level: high
tags:
- attack.persistence
- attack.t1505
- cve.cve-2026-22769
Example 3: Splunk search pattern (adapt fields to your schema)
(index=linux OR index=appliance OR index=tomcat)
(
"/manager/text/deploy" OR "/manager" OR "HostConfig.deployWAR"
)
| eval suspicion=case(match(_raw,"/manager/text/deploy"),"deploy_endpoint",
match(_raw,"HostConfig\\\\.deployWAR"),"war_deploy_event",
match(_raw,"/manager"),"manager_access",
true(),"other")
| stats count min(_time) as first_seen max(_time) as last_seen values(src_ip) values(host) by suspicion user uri_path
| convert ctime(first_seen) ctime(last_seen)
| sort - count
Example 4: KQL-style detection concept for command execution and firewall proxy behavior (vCenter/Linux telemetry)
DeviceProcessEvents
| where Timestamp > ago(30d)
| where ProcessCommandLine has "iptables"
| where ProcessCommandLine has_any ("--dport 443", "--dport 10443", "REDIRECT", "--hex-string")
| project Timestamp, DeviceName, InitiatingProcessAccountName, FileName, ProcessCommandLine
| order by Timestamp desc
This is inspired by the public description of iptables commands used for SPA-like access control and redirection behavior. Tune aggressively to your environment to avoid noise. (Google 클라우드)
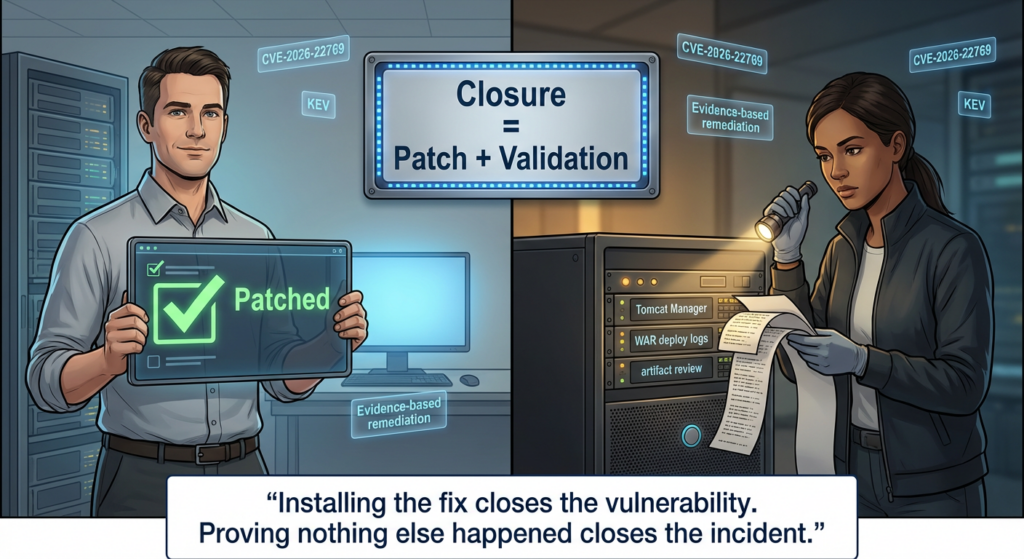
Why “Patched” Is Not the Same as “Closed”
Security programs repeatedly lose time by treating patch deployment as the finish line. For CVE-2026-22769, public reporting gives enough evidence to justify a stronger standard: remediate + investigate + validate.
A defensible closure decision should include at least three layers:
1) Remediation evidence
- Confirm appliance version and/or remediation script execution records
- Capture timestamps, operator identity, and change control references
- Store evidence in ticket/IR system
2) Compromise assessment evidence
- Historical log review for Tomcat Manager requests and deployment events
- File/path review for suspicious WARs and compiled artifacts
- Outbound network review for anomalous destinations
- Persistence review on appliance and adjacent management systems
3) Post-remediation control validation
- Network segmentation still enforced
- Management interfaces not unnecessarily exposed
- Monitoring rules deployed and tested
- IR runbook updated for backup/DR appliance scenarios
This is not overkill. It is what “evidence-based remediation” looks like when the target system is part of your resilience layer.
Recovery Trust Is the Real Theme
The most important lesson from CVE-2026-22769 is not “hardcoded credentials are bad.” Everyone already knows that.
The real lesson is that trust assumptions around recovery infrastructure are often too generous.
Many organizations have mature controls for internet-facing apps and endpoint telemetry, but their backup/DR management stack often sits in a gray zone:
- important enough to avoid touching,
- trusted enough to under-monitor,
- old enough to lag upgrades,
- connected enough to become a pivot point.
That combination is exactly why this class of vulnerability becomes strategically dangerous.
Dell’s advisory itself reminds customers that RP4VM is intended for trusted, access-controlled internal networks and not public/untrusted networks. That is good deployment guidance. But modern intrusions frequently operate 내부 “trusted” networks. Internal trust is not a security boundary unless it is backed by segmentation, access control, monitoring, and verification. (Dell)
Related CVEs and Pattern-Level Context
It is useful to place CVE-2026-22769 in a broader pattern without forcing weak comparisons.
The strongest pattern match is not “all CVSS 10s” or “all VMware-related issues.” It is this narrower class:
- Management-plane vulnerabilities
- Appliance or infrastructure software
- Hardcoded/default credentials or embedded trust assumptions
- Post-compromise leverage into high-value internal environments
CWE-798 is a useful anchor because it reminds teams that hardcoded credentials are a design-time failure mode, not just an operational misconfiguration. MITRE’s CWE guidance and OWASP security guidance on secrets management both reinforce the same principle: secrets must be centrally managed, rotatable, and auditable; fixed credentials embedded in product logic create systemic risk. (CWE)
If you want to improve long-term resilience, don’t stop at this one patch. Use this incident to review:
- appliance onboarding standards,
- management interface exposure policy,
- secret rotation assumptions,
- vendor security review criteria,
- “patch + compromise assessment” requirements for KEV items.
A Practical Response Plan for Security Leaders and Infra Owners
When you brief leadership, avoid technical overload and avoid false certainty. The message should be direct:
- This is a critical vulnerability in backup/DR infrastructure.
- Public reporting indicates active exploitation in the wild.
- Vendor remediation is available and should be applied per supported path.
- We are also validating for signs of prior exploitation because patching alone does not prove safety.
- We will document closure with evidence (version, logs, detections, and post-change validation).
That framing helps leadership understand why the response may involve both emergency change work and forensic review.
If you want to connect this topic to Penligent in a way that feels natural and technically honest, the best angle is evidence-based validation.
Penligent (as an AI-assisted penetration testing and verification platform) is not a replacement for Dell’s remediation guidance, and it is not a substitute for incident response on a potentially compromised backup appliance. The vendor advisory and the forensic evidence collection process still come first. (Dell)
Where a platform like Penligent can help is after the organization has triaged scope and applied the vendor path: it can support structured validation workflows, attack-surface checks, and repeatable evidence collection to verify whether management interfaces, related paths, or exposed services still present reachable risk after remediation. In practice, that makes the post-patch phase less subjective and easier to document across teams.
자주 묻는 질문
Is CVE-2026-22769 “just a patching issue”?
No. It is a patching issue 그리고 a potential compromise-assessment issue because public reporting describes real-world exploitation and provides concrete forensic leads. (Google 클라우드)
If our RecoverPoint system is only on an internal network, are we safe?
Not automatically. Dell’s deployment guidance assumes a trusted internal network, but internal reachability is still exploitable in many real intrusion scenarios. Treat internal-only placement as a risk-reduction factor, not a guarantee. (Dell)
What should we check first if we suspect compromise?
Start with the Google GTIG/Mandiant forensic leads: Tomcat Manager access (/관리자), deploy events, WAR artifacts, Tomcat log directories, and suspicious follow-on activity. (Google 클라우드)
Why did this get so much attention compared with other appliance bugs?
Because it combines critical severity, a high-value infrastructure target (backup/DR), and public evidence of active exploitation in the wild. KEV inclusion also amplifies prioritization pressure. (NVD)
결론
CVE-2026-22769 is a useful test of how mature a security program really is.
If the response ends at “we scheduled the patch,” the organization learned very little. If the response includes asset confirmation, vendor-aligned remediation, compromise assessment, and evidence-based validation of the recovery stack, then the organization improves not only this week’s risk posture, but its long-term resilience.
The deeper lesson is straightforward: backup infrastructure is not merely a recovery tool. It is a trust boundary. CVE-2026-22769 shows what happens when that boundary is implemented with assumptions an attacker can reuse.
참조
- NVD: CVE-2026-22769 (description, CVSS, CWE, change history, KEV-related details reflected in NVD) (NVD)
- Dell DSA-2026-079 Security Advisory (affected versions and remediation matrix) (Dell)
- Google Cloud GTIG / Mandiant: UNC6201 exploitation analysis and defender guidance (Tomcat, SLAYSTYLE, BRICKSTORM, GRIMBOLT, Ghost NICs, iptables SPA, forensic artifacts) (Google 클라우드)
- CVE.org record for CVE-2026-22769 (canonical CVE record) (CVE)
- MITRE CWE-798: Use of Hard-coded Credentials (weakness classification context) (CWE)
- OWASP Secrets Management Cheat Sheet (secret-handling design best practices) (OWASP 치트 시트 시리즈)
- Penligent: CVE-2026-22769 and the Backup Infrastructure Trust Problem (펜리전트)
- Penligent: CVE-2026-22769 백업 인프라를 침입의 거점으로 만드는 하드코딩된 크리덴셜 (펜리전트)