If you only look at the CVSS score, CVE-2026-20131 reads like a familiar headline. It is critical. It is remote. It is unauthenticated. It ends at root. But that summary still undersells the real issue. This vulnerability lands in Cisco Secure Firewall Management Center, the system many teams trust to define policy, aggregate telemetry, and coordinate administration across their firewall estate. That makes the blast radius different from a routine web bug. This is not just compromise of a service. It is compromise of the management plane that tells other security controls what to do. Cisco’s CNA-scored CVSS v3.1 vector is AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H, and NVD classifies the weakness as CWE-502, deserialization of untrusted data. In practical terms, a remote attacker who can reach the vulnerable interface can send a crafted serialized Java object and execute arbitrary Java code as root on the appliance. (NVD)
That alone would justify emergency attention. What makes CVE-2026-20131 more serious is that the public record no longer describes a purely hypothetical path to impact. AWS says its threat intelligence teams observed activity linked to exploitation beginning on January 26, 2026, more than a month before Cisco publicly disclosed the flaw on March 4, 2026. AWS then tied the operation to the Interlock ransomware family after recovering later-stage tooling from attacker infrastructure exposed by a misconfigured server. By March 19, 2026, the vulnerability had been added to CISA’s Known Exploited Vulnerabilities catalog, with a March 22, 2026 due date for Federal Civilian Executive Branch agencies. As of today, March 23, 2026, that due date has already passed. (Amazon Web Services, Inc.)
The right way to read this is not as one more “patch now” bulletin. The right way to read it is as a management-plane trust failure with active, documented exploitation. Once an attacker reaches root on FMC, the problem is no longer limited to that single box. You have to think about what that appliance can see, what it can change, what credentials and trust relationships it holds, and how much downstream administrative authority it concentrates. runZero’s framing is useful here because it turns the issue into the question defenders actually need to answer under pressure: do you know where every FMC instance is, do you know which branch it is running, and do you know which of those interfaces are reachable from untrusted paths. That is a better starting question than simply asking whether the advisory has been read. (runZero)
What CVE-2026-20131 is, in plain technical terms
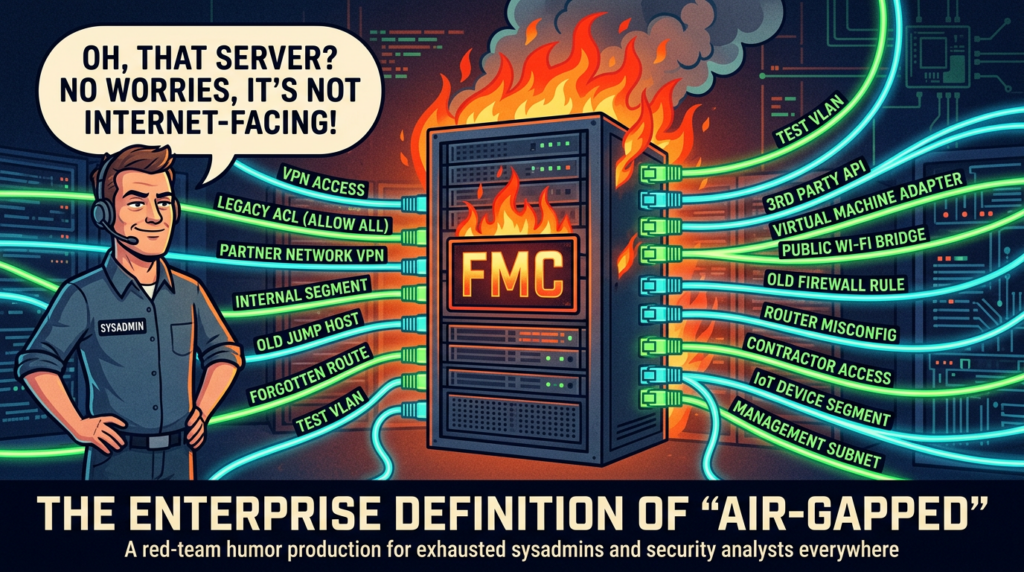
Cisco and NVD describe CVE-2026-20131 as a vulnerability in the web-based management interface of Cisco Secure Firewall Management Center software. The flaw exists because the product performs insecure deserialization of a user-supplied Java byte stream. A remote, unauthenticated attacker can send a crafted serialized Java object to the management interface and, if the target is vulnerable, execute arbitrary Java code and elevate privileges to root. NVD also preserves one important nuance that many rushed summaries miss: if the FMC management interface is not exposed to the public internet, the attack surface associated with this vulnerability is reduced. Reduced is the key word there. It does not say removed. It does not say safe. It only says smaller. (NVD)
That distinction matters because administrative exposure today is rarely a simple public-versus-private binary. A management interface may not be open to the full internet and still be reachable from broad VPN populations, contractor segments, inherited trust zones, partner networks, cloud-connected administrative enclaves, or internal routes that have grown too permissive over time. For this class of issue, “not internet-facing” is not a defense strategy. It is just one exposure-reduction factor. Teams that stop their analysis there are treating topology as a control substitute, and topology is not a substitute for patch state, segmentation, and verified access restrictions. The official record supports the narrower claim that attack surface is smaller without public exposure; the operational implication is broader and more uncomfortable: every reachable management path has to be treated as part of the risk picture. (NVD)
The CVSS vector also tells a story that should change response behavior. AV:N 그리고 PR:N mean the attacker does not need local foothold or prior credentials. UI:N means there is no dependency on tricking a user into clicking anything. S:C means the impact crosses a security boundary. And the C:H/I:H/A:H trio is exactly what defenders do not want to see on a centralized administrative appliance: high impact to confidentiality, integrity, and availability, all at once. This is why writing the issue off as “just a deserialization bug” misses the point. The vulnerability class explains the implementation failure. The deployment target explains the operational danger. (NVD)
The timeline that changes how you should prioritize this
Cisco published the advisory on March 4, 2026 and rated the issue critical. The advisory metadata surfaced in search results also states that there were no workarounds available, which means this was not a case where defenders could toggle off a feature, drop a mitigative configuration, and buy time. Software updates were the real fix path. That detail matters because teams often build short-term response plans around interim mitigations. Here, the window for “we’ll wait until a later maintenance cycle” was weak to begin with. (Cisco)
AWS added the missing piece on March 18, 2026. According to AWS, Amazon threat intelligence began research into the vulnerability after Cisco’s disclosure and then found evidence that Interlock had been exploiting it 36 days before public disclosure, starting on January 26, 2026. AWS observed exploit requests that contained Java code execution attempts and two embedded URLs, one to deliver configuration data for the exploit and another meant to confirm successful compromise by having the victim upload a generated file via HTTP PUT. AWS then emulated the expected callback behavior, which caused the attackers to proceed to the next stage and fetch a malicious ELF binary from attacker-controlled infrastructure. That operational mistake by the threat actor exposed a broader toolkit tied to Interlock. (Amazon Web Services, Inc.)
By March 19, 2026, NVD reflected that the CVE was in CISA’s Known Exploited Vulnerabilities catalog, and the NVD page records the corresponding due date of March 22, 2026 for federal civilian agencies. That due date is not a general patch-SLA law for private companies, but it is still an excellent signal of urgency. When CISA moves a vulnerability into KEV this quickly after disclosure and NVD records a three-day action window for covered agencies, the message to every other defender is obvious: treat this as an active exposure event, not as backlog. (NVD)
One subtle point is worth keeping clear because public reporting sometimes blurs it. The KEV addition is official. . ransomware attribution comes from threat intelligence analysis, most prominently AWS’s Interlock write-up. Those two facts reinforce each other, but they are not the same kind of source. CISA’s catalog proves exploitation mattered enough for formal federal action. AWS’s analysis explains who was doing it, when they started, and what the post-compromise activity looked like. That separation is helpful because it keeps the article grounded in what is directly documented versus what is analytically attributed. (NVD)
Why this management-plane compromise matters more than a typical edge bug
Security teams sometimes make an understandable mistake when triaging edge vulnerabilities. They compare two issues with similar scores and treat them as interchangeable because both are remote and severe. In reality, where the bug lands matters almost as much as how the bug works. A flaw in a single externally exposed application server is dangerous. A flaw in the system that centrally defines firewall policy, aggregates alerts, distributes administrative actions, and sits close to security workflows is different. The first may produce a host compromise. The second may produce administrative leverage, operational blind spots, or a path to broader policy manipulation. Cisco FMC is the coordination layer for a lot of security decision-making. That is why the victim system type changes the story. (runZero)
runZero captures this operationally by describing FMC as a centralized platform used to configure security policies, manage updates, and aggregate telemetry across Cisco security appliances. Arctic Wolf says much the same thing from a different angle by emphasizing that these March 2026 vulnerabilities affect the product used to centrally manage Cisco Secure Firewall devices. When multiple independent sources converge on that architectural role, defenders should read the vulnerability through that lens. The management plane is not just another administrative convenience. It is a trust concentration point. Trust concentration points deserve tier-zero handling, tighter segmentation, faster validation, and deeper post-patch review than a normal application server would receive. (runZero)
That is also why CVE-2026-20131 should not be summarized only as “an unauthenticated RCE.” That phrase is technically correct and strategically incomplete. A remote unauthenticated RCE on a commodity line-of-business app is bad. A remote unauthenticated RCE on the platform that manages firewall policy and visibility is the kind of defect that makes every downstream assumption feel shakier. If the management center itself cannot be trusted, how much confidence should you place in the alerts, policy states, access restrictions, or historic administrative records it has been presenting to your team. That question is larger than a patch bulletin, and that is exactly why this CVE deserves more than a thin rewrite of the advisory. (NVD)
Affected versions and the practical fixed targets
The most useful public summaries for operational response are the ones that translate vendor language into practical branch decisions. runZero’s March 2026 write-up is especially good here because it lays out practical fixed points by branch, while Qualys and Arctic Wolf reinforce the broader affected scope and the need to upgrade rather than rely on non-existent workarounds. The important thing for defenders is not to memorize every exact vulnerable build in the advisory. The important thing is to know the safe target for the branch you are actually running. (runZero)
Here is the cleanest publication-ready matrix for defenders responding to CVE-2026-20131:
| FMC branch | Practical vulnerable condition | Practical fixed target |
|---|---|---|
| 6.4.0.13 through 6.4.0.18 | 취약한 | 7.0.9 or later |
| 7.0.x | Earlier than 7.0.9 | 7.0.9 or later |
| 7.1.x through 7.2.x | Earlier than 7.2.11 | 7.2.11 or later |
| 7.3.x through 7.4.x | Earlier than 7.4.6 | 7.4.6 or later |
| 7.6.x | Earlier than 7.6.5 | 7.6.5 or later |
| 7.7.x | Earlier than 7.7.12 | 7.7.12 or later |
| 10.0.0 | 취약한 | 10.0.1 or later |
This table is compiled from runZero’s practical fixed-version guidance and Qualys’s version summary of affected branches. (runZero)
One of the easiest mistakes to make in a rushed change window is to think “we already patched the Cisco FMC problem” when in reality the team only moved far enough to cover CVE-2026-20079 on certain branches. runZero explicitly points out this difference for 7.4.x 그리고 7.6.x. For the authentication bypass companion flaw, 7.4.4 and 7.6.4 may be enough. For CVE-2026-20131, the practical fixed points are 7.4.6 그리고 7.6.5. That distinction is exactly the kind of thing that creates false closure in vulnerability response programs. A team that upgrades to the wrong “good enough” point can leave one of the two pre-auth root paths open while believing the incident has been remediated. (runZero)
There is also an important product-scope nuance around Cisco Security Cloud Control. Arctic Wolf notes that CVE-2026-20131 also affects Cisco Security Cloud Control Firewall Management, but Cisco had already upgraded the SaaS service as part of routine maintenance, so no customer action was required there. That is useful because hybrid Cisco customers may otherwise assume the same remediation burden applies equally to on-prem and cloud-managed surfaces. It does not. The exposure story is product- and delivery-model-specific. (Arctic Wolf)
The technical shape of the flaw, without turning this into an exploit guide
The simplest correct technical description is that Cisco’s web-based FMC management interface accepted attacker-controlled serialized Java input and handled it unsafely. Insecure deserialization bugs are so dangerous because they are not “input validation issues” in the ordinary web-form sense. They are trust-boundary failures at the object-processing layer. Once a system accepts and reconstitutes attacker-controlled object data, the question becomes whether the application can be pushed into constructing an execution path the developer never intended. On a Java-based management plane, that can become catastrophic quickly when the receiving code runs with broad privileges or sits close to privileged operations. NVD’s classification under CWE-502 is exactly right, but the operational translation is this: the application trusted a kind of input that should never have been trusted at that boundary. (NVD)
That is why the danger here is not just “the parser crashes” or “the application misbehaves.” The danger is that deserialization problems often bridge the gap between network input and execution context in ways that are disproportionate to how small the triggering request may look. A team reading this article does not need exploit recipe details to understand the risk. The only facts that matter for triage are already public and sufficient: the request is remote, the attacker does not need credentials, the object data can be crafted, and success lands at root. That is enough to justify immediate administrative-surface review, accelerated patching, and compromise-minded follow-up for exposed systems. (NVD)
AWS’s observations make the practical shape of the attack clearer without requiring the reader to see weaponized payloads. The threat intelligence team observed requests to a specific path in the affected software, with request bodies containing Java execution attempts and embedded URLs used for exploit configuration and success confirmation. That is useful because it tells defenders something important about how to think, even if it does not give them a canned detection signature: the attacker workflow was not random spray-and-pray probing. It was structured exploitation with orchestration around confirmation and follow-on delivery. That should move defenders toward reviewing web access patterns, unexpected callback behavior, anomalous outbound requests from the appliance, and post-exploit activity rather than limiting their review to “was the version vulnerable.” (Amazon Web Services, Inc.)
What the Interlock campaign tells us about real-world risk
The AWS report is the part of this story that separates theoretical severity from lived adversary behavior. According to AWS, once the company emulated the expected success callback, the attacker infrastructure responded by serving an ELF binary, and subsequent investigation connected that infrastructure to a broader Interlock toolkit. AWS then described post-compromise components including a Windows reconnaissance PowerShell script, custom remote access trojans implemented in both JavaScript and Java, persistent WebSocket-based command-and-control, file transfer, and proxying capabilities. That means the issue is not best framed as “Cisco FMC gets popped and that’s the end.” The better framing is “Cisco FMC can become the breach point for a larger ransomware intrusion chain.” (Amazon Web Services, Inc.)
AWS also adds useful context about sector targeting. Interlock has historically concentrated on industries where disruption creates leverage, with education accounting for the largest share of activity, followed by engineering, architecture and construction, manufacturing and industrial organizations, healthcare providers, and government and public sector entities. That does not mean organizations outside those sectors can relax. It means defenders inside them should read the story with an even lower tolerance for delay, because the campaign history suggests attackers already understand where downtime and compliance pressure can force faster payment decisions. (Amazon Web Services, Inc.)
This is where the management-plane angle becomes even more serious. A firewall management center that controls policy and visibility is not just a good target because it is internet-reachable. It is a good target because it sits at the meeting point of trust, administration, and operational continuity. If a ransomware actor wants a clean foothold with administrative gravity, systems like this are attractive. That is why the AWS write-up, the NVD record, and the KEV addition should be read together. One source tells you what the bug is. One tells you how it was used. One tells you how the U.S. government now expects agencies to treat it. (NVD)
Why CVE-2026-20131 and CVE-2026-20079 should be triaged together
The biggest mistake I see in quick-turn vulnerability coverage is treating sibling CVEs as unrelated just because they have different numbers and different weakness classes. Arctic Wolf’s summary is useful precisely because it puts CVE-2026-20079 그리고 CVE-2026-20131 side by side. Both were disclosed on March 4, 2026. Both affect Cisco Secure Firewall Management Center. Both are remotely reachable, unauthenticated paths that can end in root-level control. The difference is how they get there. CVE-2026-20079 is an authentication bypass due to an improperly created system process at boot. CVE-2026-20131 is a deserialization-driven remote code execution bug in the web-based management interface. Operationally, they are one administrative-surface emergency. (Arctic Wolf)
The fact that the two bugs travel through different technical classes is interesting to researchers, but it should not fragment response ownership inside an enterprise. If one team owns identity controls and another owns middleware patching, someone still has to unify the response at the management-plane level. A vulnerability program that opens two tickets and never joins them architecturally is missing the point. These are not two random defects in different products. They are two separate pre-auth root roads into the same high-value administrative system. A mature response treats them as one trust incident, one exposure review, and one validation cycle. (Arctic Wolf)
That combined view also sharpens executive communication. “We have two critical CVEs to patch” is technically true and operationally thin. “We have two separate unauthenticated root paths on the platform that manages our firewall estate, and at least one was already exploited in the wild before disclosure” is a better sentence. It communicates why patching needs urgency, why exposure review matters, and why post-patch compromise assessment should not be dismissed as overreaction. (Amazon Web Services, Inc.)
What defenders should do first, second, and third
The first task is not patching. The first task is asset certainty. You need a complete list of Cisco FMC installations and their version branches before you can know how much exposure you actually have. runZero’s article is excellent on this point because it explicitly reframes the problem as an asset-discovery and version-mapping exercise. Teams that cannot answer “where are all our FMC instances” are operating on hope, not on response discipline. (runZero)
The second task is access-path certainty. NVD says public internet exposure increases the associated attack surface, but the real defensive question is broader: which networks, users, and trust domains can reach the management interface today. This is where many organizations discover that administrative surfaces are reachable through legacy VPN profiles, inherited ACLs, forgotten jump segments, partner routes, or broad internal trust that was never revisited after deployment. You do not need an exploit trace to justify tightening those paths immediately. If the appliance is not yet patched, every unnecessary path should be assumed to be risk you do not need. (NVD)
The third task is patching to the correct safe point, not just “the latest maintenance we happened to have approved.” The safe points are branch-specific, and as already noted, some branch targets sufficient for CVE-2026-20079 are still insufficient for CVE-2026-20131. Teams should verify the target version against the practical fixed matrix rather than relying on memory or generic change-ticket language. This is exactly where rushed response breaks down, especially in environments with multiple FMC branches still alive for historical reasons. (runZero)
The fourth task is post-change validation. A ticket that says “upgrade complete” is not validation. Validation means the version has been verified, the reachable paths have been reduced to only what is intentionally allowed, administrative access patterns have been reviewed, and whatever external or semi-trusted reachability existed before remediation has been rechecked. Teams that stop at install success are closing the easy part of the incident and leaving the expensive part unanswered. (runZero)
The fifth task, for any instance that was broadly reachable before the fix, is compromise-minded review. AWS’s report should make that non-negotiable for exposed systems. If exploitation was active before disclosure and later stages included tooling fetches, RATs, and reconnaissance scripts, then patching alone does not answer whether you were already visited. The question becomes whether there was suspicious inbound management traffic, unusual outbound behavior from the appliance, administrative anomalies, or policy activity that does not fit expected change history. The burden of proof should be on establishing confidence, not on assuming safety because the appliance is patched now. (Amazon Web Services, Inc.)
A practical triage table for engineering teams
| Question | 중요한 이유 | Strong answer | Weak answer |
|---|---|---|---|
| Do we have a complete FMC inventory | Determines scope | Every instance identified | “We think it’s just one” |
| Do we know the exact branch on each instance | Determines the right fixed target | Version recorded per asset | “Some 7.x release” |
| Is the management interface reachable from any untrusted path | Determines pre-auth exposure | Only tightly controlled admin routes | Broad VPN or legacy routes |
| Are we remediating both CVE-2026-20079 and CVE-2026-20131 | Prevents partial closure | Single plan covers both | Separate tickets with no unified review |
| Did we validate after patching | Prevents false closure | Version, access, and logs reviewed | “Change succeeded” |
| If exposure existed, did we perform compromise-minded review | Addresses zero-day reality | Yes, on every exposed instance | No, because patching felt sufficient |
The logic behind this table is drawn from the public record around the vulnerability and from the operational emphasis in runZero, Arctic Wolf, AWS, and CyCognito coverage. (runZero)
Code that helps you make a faster version decision
This Python snippet is not an exploit and does not touch the target. It is simply a small helper that lets an engineering or operations team normalize version strings and quickly sort assets into “vulnerable” versus “upgrade target” buckets for CVE-2026-20131:
from packaging.version import Version
def cve_2026_20131_status(version_str: str) -> str:
v = Version(version_str)
if Version("6.4.0.13") <= v <= Version("6.4.0.18"):
return "Vulnerable — move to 7.0.9 or later"
if Version("7.0.0") <= v < Version("7.0.9"):
return "Vulnerable — move to 7.0.9 or later"
if Version("7.1.0") <= v < Version("7.2.11"):
return "Vulnerable — move to 7.2.11 or later"
if Version("7.3.0") <= v < Version("7.4.6"):
return "Vulnerable — move to 7.4.6 or later"
if Version("7.6.0") <= v < Version("7.6.5"):
return "Vulnerable — move to 7.6.5 or later"
if Version("7.7.0") <= v < Version("7.7.12"):
return "Vulnerable — move to 7.7.12 or later"
if v == Version("10.0.0"):
return "Vulnerable — move to 10.0.1 or later"
return "Not in the practical vulnerable ranges summarized for CVE-2026-20131"
tests = ["6.4.0.18", "7.0.8.1", "7.2.10.2", "7.4.5", "7.6.4", "7.7.12", "10.0.0", "10.0.1"]
for t in tests:
print(f"{t:10} -> {cve_2026_20131_status(t)}")
The thresholds in this helper are built from the practical fixed-version matrix published by runZero and reinforced by Qualys’s March 2026 summary. (runZero)
If your team works from CMDB exports or scanner CSVs, the best use of a helper like this is not elegance. It is speed. In a real change window, security and infrastructure teams often have to reconcile inconsistent version formats from asset inventory, exposure tools, and appliance admins. The faster you can collapse those into an unambiguous “needs action” list, the less likely you are to lose time arguing about branch interpretation while an exposed management surface is still reachable. That is a small operational detail, but it is exactly the kind of detail that separates sound incident handling from noisy escalation. (runZero)
A log-review starting point that is actually useful
Because AWS described observed exploit attempts as HTTP requests to the affected software path with Java execution attempts and embedded URLs, defenders should not limit review to package state. They should also look at management-interface access logs, reverse proxy logs if one sits in front of FMC, outbound network telemetry from the appliance, and change-history context around the time of exposure. The purpose is not to chase one perfect signature. The purpose is to ask whether the management surface behaved like an attacked administrative plane rather than a quiet console. (Amazon Web Services, Inc.)
A practical starting point in Splunk or similar tooling is to pivot around the FMC management hostnames or IPs and ask simple questions first: did inbound request volume spike before disclosure, did unfamiliar source networks hit the interface, did response patterns change, and did the appliance make outbound connections it normally would not make. For example, the following pattern is intentionally generic and safe:
index=proxy OR index=fw OR index=web
(host="fmc.example.com" OR dest_ip="X.X.X.X")
earliest=2026-01-20 latest=2026-03-05
| stats count dc(src_ip) as unique_sources values(status) as statuses by uri_path, src_ip
| sort -count
That is not a vendor-perfect hunt. It is a first pass to identify whether the management interface looks like a stable admin portal or a suddenly interesting internet target. The key lesson from the AWS write-up is that exploitation involved structured HTTP activity and follow-on retrieval behavior. Your hunt should reflect that. (Amazon Web Services, Inc.)
You should also review any administrative or policy changes that occurred near the suspected window of exposure. The point is not to assume the attacker immediately reconfigured the firewall estate. The point is to recognize that a rooted management center sits close to policy, visibility, and trust relationships. In environments where change logging is separated across multiple systems, reconciling those records is tedious but worthwhile. A team that only checks whether the appliance is now patched may miss the harder question of whether anything around it was quietly altered during the zero-day window. That kind of review is not overkill here. It is what a management-plane incident deserves. (runZero)

Related CVEs that matter to readers of this article
The first related CVE is the one you should treat as part of the same event: CVE-2026-20079. NVD describes it as an unauthenticated authentication bypass in Cisco Secure Firewall Management Center that can let a remote attacker execute script files on an affected device and obtain root access to the underlying operating system. Arctic Wolf and runZero both treat it as the other maximum-severity FMC emergency disclosed on the same day as CVE-2026-20131. For defenders, the point is not taxonomy. The point is that both bugs hit the same management plane and both can end at root. If you are working an FMC emergency response, this CVE belongs in the same room, the same timeline, and the same validation plan. (NVD)
The second related issue is CVE-2026-20127, the Cisco Catalyst SD-WAN authentication bypass that NVD says can allow an unauthenticated remote attacker to bypass authentication and obtain administrative privileges on an affected system. This is not the same product and not the same code path, but it belongs in the conversation because it illustrates the same larger truth: exposed control and management planes remain one of the most consequential failure points in enterprise infrastructure. If your organization reads CVE-2026-20131 as an isolated curiosity instead of as part of a repeated pattern around security and network administration surfaces, you are learning too little from the current Cisco vulnerability stream. (NVD)
A third useful reference point is CVE-2022-20775, an older Cisco SD-WAN privilege-escalation issue that allowed an authenticated local attacker to execute arbitrary commands as root. I include it not because it is equivalent in urgency to CVE-2026-20131, but because it reinforces the broader theme that the control infrastructure around networking and security is often far more sensitive than defenders treat it. When a platform governs trust, routing, policy, or visibility, even “local” or “post-auth” flaws can have outsized downstream consequences. Readers who work on enterprise network defense should keep that architectural lesson front and center. (NVD)
The fourth comparison point is CVE-2025-20393, a Cisco AsyncOS vulnerability in the Spam Quarantine feature of Cisco Secure Email Gateway and Cisco Secure Email and Web Manager that NVD says could allow an unauthenticated remote attacker to execute arbitrary system commands with root privileges. This is a different product family, but it is useful because it reminds readers that Cisco-adjacent administrative or security appliances are not low-stakes systems. Once again, the important habit is not memorizing every product line. The important habit is recognizing that administrative and protective infrastructure deserves the same or greater rigor than the workloads it shields. (NVD)
For a vulnerability like CVE-2026-20131, the most defensible use of a platform such as Penligent is to reduce response friction without reducing operator judgment. A good workflow would help teams identify all relevant management-plane assets, compare branch versions against safe targets, verify that exposure paths have been reduced after patching, rerun controlled validation checks that do not cross into irresponsible exploit behavior, and produce a clear report showing what was exposed, what was upgraded, and what still needs review. On a vulnerability where the difference between “patched” and “confidently remediated” is substantial, that kind of acceleration is genuinely useful. (펜리전트)
The strategic lesson behind CVE-2026-20131
The deepest lesson here is not about Java deserialization, even though that is the implementation flaw. The deepest lesson is about where organizations still concentrate too much trust with too little scrutiny. Security teams are often very good at talking about perimeter exposure in the abstract while leaving the systems that define policy and visibility in a category of assumed safety. CVE-2026-20131 is a direct challenge to that assumption. When the firewall management plane is reachable, weakly segmented, slowly patched, or poorly inventoried, the organization is not just carrying technical debt. It is carrying administrative-plane risk that can erase the confidence of multiple downstream controls. (NVD)
AWS’s Interlock reporting sharpens that lesson. The threat group did not need a fantastical supply-chain chain reaction or a novel social-engineering trick to make this meaningful. They needed a remotely reachable management surface, a high-consequence flaw, and enough time before public disclosure to turn the foothold into a larger campaign. That is why the response to CVE-2026-20131 should not end with this month’s patch meeting. The more important follow-on questions are the ones that stay relevant after the headlines fade: which management planes in our environment are treated as tier-zero systems, which ones remain reachable from places they should not be reachable from, and how quickly can we validate their state when a high-impact issue drops. (Amazon Web Services, Inc.)
A mature organization will use this CVE to improve not just one appliance but one operating habit. Administrative surfaces should have tighter route control, clearer ownership, faster version visibility, stronger logging expectations, and less ambiguity around emergency change rights than ordinary servers. If that sounds stricter than what many environments do today, that is exactly the point. A system that governs firewall policy and visibility is not ordinary infrastructure. Defenders should stop pretending it is. (runZero)
결론
CVE-2026-20131 deserves serious attention because it combines the worst attributes defenders fear in an infrastructure vulnerability: remote reachability, no authentication requirement, no user interaction requirement, root-level execution, and a high-value victim system. Cisco and NVD define the flaw clearly. AWS proves that it was not only exploitable but actually exploited as a zero-day beginning on January 26, 2026. NVD records its addition to CISA’s KEV catalog on March 19, 2026, with a March 22 due date for covered federal agencies. The facts are already enough to justify treating this as one of the most important management-plane exposure events in the March 2026 vulnerability cycle. (NVD)
The practical response is also clear. Identify every FMC instance. Map every reachable administrative path. Upgrade to the correct safe branch, not the first branch that sounds close enough. Treat CVE-2026-20079 as part of the same incident. Validate after patching. And where pre-patch exposure existed, investigate with compromise in mind rather than letting the upgrade create a false sense of closure. The organizations that handle CVE-2026-20131 well will not be the ones that merely patched fastest. They will be the ones that treated the firewall management plane like the trust concentration point it has always been. (runZero)
Related reading
Cisco advisory for CVE-2026-20131
NVD entry for CVE-2026-20131
CISA Known Exploited Vulnerabilities catalog
AWS Security Blog, Interlock ransomware campaign targeting enterprise firewalls
runZero, How to find Cisco Secure Firewall Management Center installations on your network
Arctic Wolf, CVE-2026-20079 and CVE-2026-20131
Qualys ThreatPROTECT summary for CVE-2026-20079 and CVE-2026-2013Pentest AI, What Actually Matters in 2026
CVE-2026-20079, The Cisco FMC Auth Bypass That Turns a Management Plane into a Root-Level Exposure
AI Pentest Tool, What Real Automated Offense Looks Like in 2026
Penligent Documentation