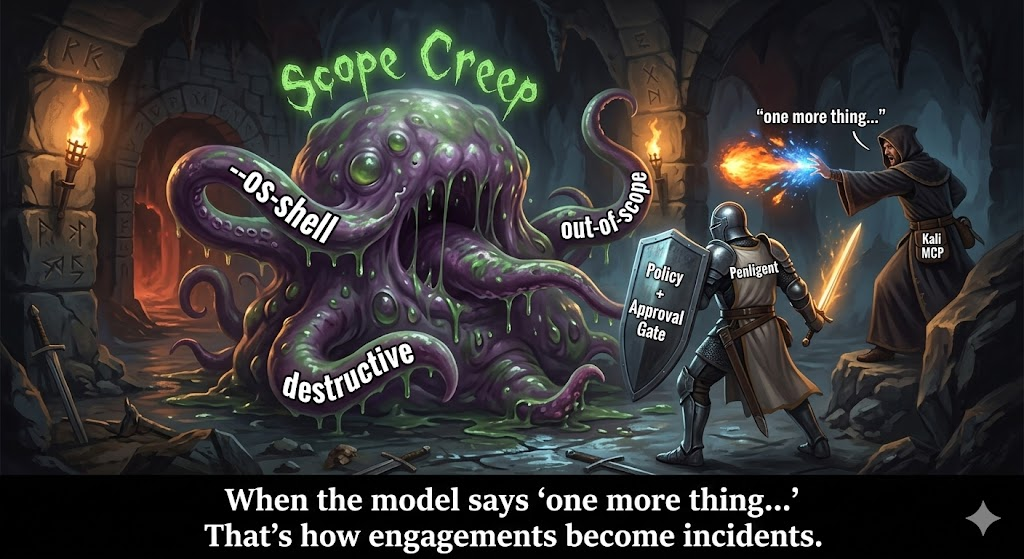
Kali MCP is not a feature, it is a boundary shift
If you’ve been around offensive security long enough, you’ve seen “AI for pentesting” cycle through a predictable pattern. First it’s a smarter search engine. Then it’s a note-taking assistant. Then it’s a “planning copilot” that writes a beautiful methodology doc but never touches a packet.
Kali MCP is different because it moves AI from “talking about the work” to “touching the work.”
Kali’s own mcp-kali-server listing doesn’t try to be subtle: it’s a server that “allows the MCP to run terminal commands like nmap… interact with web applications using tools like curl, wget, gobuster… and perform AI-assisted penetration testing,” with explicit examples like solving CTF web challenges in real time or helping with HTB/THM machines. (Kali Linux)
That’s a major change in kind. When a model can execute tools, the primary question stops being “How good is the model’s advice?” and becomes:
- What did it actually run?
- Under which identity?
- Against which scope?
- With which artifacts and evidence?
- With what guardrails?
- With what audit trail?
This is where teams start to split into two camps.
One camp treats Kali MCP as a productivity trick: “I can drive Kali from a native AI client, faster recon, faster enumeration, faster iteration.” That camp will ship cool demos.
The other camp treats Kali MCP as a new control plane. That camp asks what every mature security team asks when a control plane appears: “Where is the boundary, and how do we govern it?”
That second camp is the only one that can safely deploy Kali MCP as a default in real pentesting operations.
Model Context Protocol, what it is in operational terms
Anthropic introduced the Model Context Protocol, MCP, as an open standard for connecting AI assistants to the systems where data and tools live, so you don’t have to build custom integrations for every tool and every client. (Anthropic)
MCP matters for pentesting not because it makes the model “more intelligent,” but because it standardizes the interface between the model and capability.
MCP uses JSON-RPC, which is exactly why it scales and why it can fail like classic AppSec
The MCP specification explicitly states that messages between clients and servers follow JSON-RPC 2.0, and it defines roles such as hosts, clients, and servers. (Model Context Protocol)
JSON-RPC is a simple RPC protocol that defines request/response structures and is transport agnostic. (jsonrpc.org)
That combination is powerful because it’s predictable. Predictability is how you get an ecosystem: servers can be written once and used by many clients; clients can support many servers. This is one reason you see MCP adoption patterns beyond pentesting, such as AWS publishing MCP servers and documentation for secure, authenticated access to services. (Amazon Web Services, Inc.)
But predictability is also why MCP can fail in boring, dangerous ways: argument validation, path scoping, and unsafe defaults become central. MCP doesn’t eliminate classic vulnerability classes; it routes them into a new plane where a model can trigger them.
The simplest MCP mental model for pentesters
If you’re a pentester, treat MCP as three pieces:
- A host app: the user-facing AI application, often a native desktop client.
- An MCP client component: the connector inside the host app that speaks MCP.
- One or more MCP servers: services that expose tools and resources.
If an MCP server exposes a “tool,” the model can call it. If it exposes a “resource,” the model can read from it. The moment your MCP server can run terminal commands, your model can cause real operational impact.
What Kali MCP shipped, and what “mcp-kali-server” actually is
Kali’s mcp-kali-server package is small and direct: install with sudo apt install mcp-kali-server, and you get an MCP-facing service that can execute terminal commands and interact with web apps via standard CLI tooling. (Kali Linux)
Kali also published a walkthrough focused on using Claude Desktop as the GUI on macOS, with a Kali machine as the attacking box and an Anthropic LLM providing the intelligence layer. The post frames the approach as “moving beyond direct terminal command execution” by leveraging an LLM to translate natural-language descriptions into technical commands, and it emphasizes the integration of multiple systems to make this work. (Kali Linux)
Kali MCP is not a vague concept. It’s a shipped package plus a reference workflow.
That matters because when something is packaged in Kali, engineers will use it. Not because it’s perfect, but because Kali has trained the entire industry to assume “if it’s in Kali, it’s usable.”
So the maturity question is not “Can Kali MCP be used?” It’s “Can Kali MCP be used as a default without turning your environment into an agent-driven incident factory?”
Why Kali MCP feels like magic in a demo
You can understand the appeal of Kali MCP in one sentence: it collapses the loop between reading output and deciding the next command.
In a normal workflow, even skilled operators burn time on:
- reformatting outputs
- copying host lists between tools
- extracting only the relevant findings from noisy output
- remembering what they already tried
- writing down evidence before they forget it
Kali MCP turns that into a feedback loop where the model can:
- run a tool
- parse the results
- decide what matters
- run the next tool
- keep state
This is also why Anthropic’s engineering write-up about code execution with MCP focuses on efficiency: load tools on demand, filter data before it reaches the model, and run complex logic as a single step, with security and state management benefits when done correctly. (Anthropic)
The demo version of Kali MCP is: “Tell the AI what you want, it runs nmap and ffuf and summarizes.”
The production version of Kali MCP must answer: “What are the guardrails, and what happens when an attacker tries to steer the loop?”
The uncomfortable truth, Kali MCP creates a new supply chain boundary
When you adopt Kali MCP, you aren’t just adopting a protocol. You are adopting:
- MCP server implementations
- their dependency trees
- their argument validation logic
- their filesystem boundaries
- their release cadence and patch discipline
That is a supply chain boundary.
In agentic systems, the supply chain is not only the tools you install. It is also the connectors that define what the model can do.
Penligent’s own analysis of agent ecosystems treats “skills and integrations” as a supply chain boundary, not a convenience feature, and that framing maps cleanly onto MCP servers. (펜리전트)
If you want a mental model that will keep you out of trouble, it’s this:
MCP servers are like plugins that can execute. Treat them like you treat production dependencies.
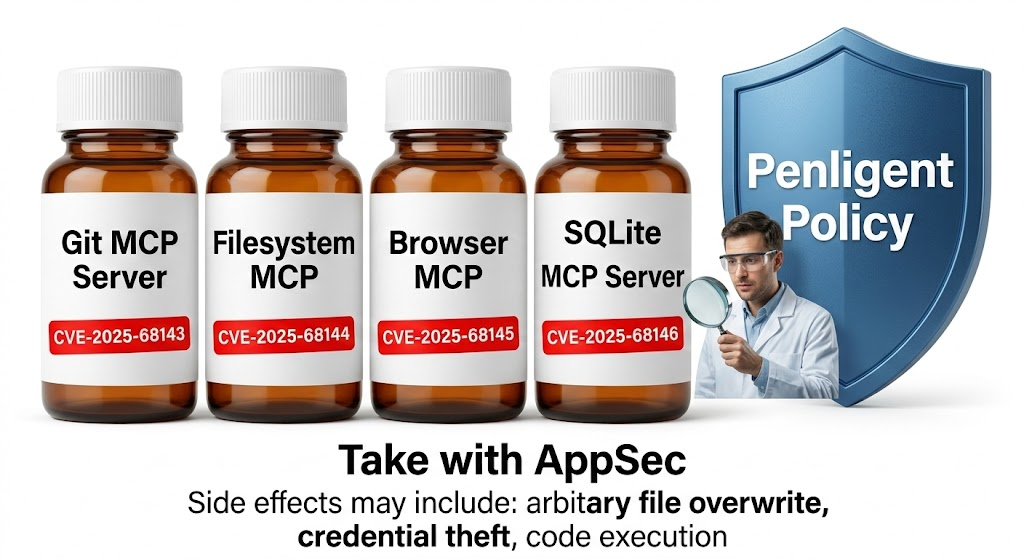
The Git MCP server CVEs that proved MCP needs AppSec
If you want one case study that instantly upgrades your Kali MCP threat model, it’s the vulnerabilities disclosed in Anthropic’s official Git MCP server.
The Hacker News summarized the incident bluntly: three flaws in mcp-server-git could be exploited for arbitrary file access and, in some conditions, code execution. (해커 뉴스)
The NVD entries are even more useful because they describe the root cause patterns in plain terms.
CVE-2025-68143, path scope failure at initialization
영향을 받는 버전에서는 git_init tool accepted arbitrary filesystem paths and created Git repositories without validating the target location. Unlike other tools that required an existing repo, git_init could operate on any directory accessible to the server process, making those directories eligible for subsequent git operations. (NVD)
This is not “AI security.” This is classic boundary validation failure, routed through an MCP tool.
CVE-2025-68144, argument injection through CLI option parsing
In affected versions, git_diff 그리고 git_checkout passed user-controlled arguments directly to Git CLI commands without sanitization. Flag-like values could be interpreted as command-line options rather than refs, enabling arbitrary file overwrites. The fix rejects args starting with - and verifies the argument resolves to a valid git ref. (NVD)
Again: this is classic argument injection, not mystical prompt injection.
CVE-2025-68145, repo scoping bypass when using -repository
In affected versions, even when the server was started with --repository to restrict operations, it did not validate that subsequent repo_path arguments were within the configured path, allowing tool calls to operate on other repositories accessible to the server process. (NVD)
This is classic path traversal / scoping bypass.
Why these CVEs matter for Kali MCP specifically
Even if you never run the Git MCP server, these CVEs teach three transferable lessons:
- Initialization functions are dangerous. Anything that can create or open a new scope tends to bypass guardrails that protect “normal operations.”
- CLI tools are injection surfaces. If you pass user-controlled strings to a CLI, you must treat every argument as hostile and parse it yourself.
- Scope flags are not security unless enforced. “We started the server with
-repository” is not a control unless the server validates every subsequent path against it.
Endor Labs’ analysis makes the broader point: MCP is infrastructure, and it needs classic AppSec disciplines because classic vulnerabilities show up in MCP servers. (IBM)
If you adopt Kali MCP without adopting AppSec discipline around MCP servers, you are betting your environment on optimistic defaults.
Prompt injection is worse when the model can execute
Prompt injection is often discussed like an LLM problem, but operationally it’s a control-plane integrity problem.
In a chat-only system, a successful prompt injection might cause a model to say something wrong.
In an MCP-enabled system, a successful prompt injection can cause a model to run something wrong.
The difference is impact.
The Git MCP server reporting explicitly discusses prompt injection in the context of tool chaining and file access outcomes. (해커 뉴스)
This becomes relevant to Kali MCP because pentesting is full of adversary-controlled text:
- HTML content from targets
- API responses
- error pages that reflect input
- logs that contain attacker-controlled values
- wordlist hits that include attacker-crafted paths
If your model reads these and treats them as instructions, the model is now executing attacker influence, not just describing it.
This is why “human in the loop” alone is not enough. You need policy layers that separate:
- data to observe
- instructions to follow
- actions that require explicit approval

A practical threat model for Kali MCP deployments
Below is a threat model table that matches how Kali MCP systems actually fail.
| 레이어 | Failure mode | What triggers it | What prevents it |
|---|---|---|---|
| AI host and client | model steered into unsafe tool use | prompt injection via target content | explicit approval gates, structured tool policies |
| MCP server | path and argument validation bugs | user-controlled args, weak scoping | allowlists, canonicalization, strict parsing |
| Toolchain | dangerous flags or modules | “helpful escalation” to exploit modes | blocked flags, per-tool policies, rate limits |
| Execution host | privilege, secrets, and persistence risk | running as root, ambient tokens | least privilege, secrets isolation, sandboxing |
| Artifacts and logs | evidence gaps, tampering, leaks | ad hoc outputs, mutable logs | append-only logs, immutable evidence bundles |
The point is not paranoia. The point is operational maturity: Kali MCP is a control plane, and control planes must be governed.
Setting up Kali MCP, make it work first, then make it safe
Most teams fail because they either over-engineer before they confirm basic functionality, or they ship a working demo and never add valves.
Do it in two phases.
Phase 1, minimal working Kali MCP
Kali’s package install is simple. (Kali Linux)
sudo apt update
sudo apt install -y mcp-kali-server
# Start the server on a local port
kali-server-mcp --port 5000
At this point, your goal is not to run a full engagement. Your goal is to verify:
- the server starts
- the host app can connect
- a safe command can execute
- output returns cleanly
Use harmless checks first.
whoami
id
uname -a
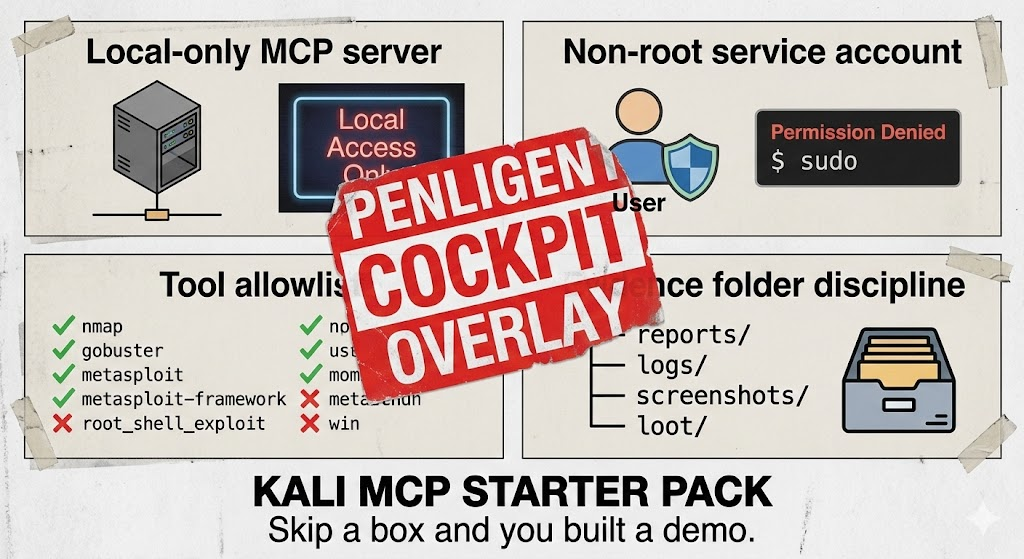
Phase 2, production hardening that actually maps to real pentests
The hardening that matters for Kali MCP tends to cluster into four domains:
- identity and privilege
- network exposure
- tool policies
- evidence and audit
Identity and privilege, non-root is a baseline, not an option
If your MCP server runs as root, your model has root-adjacent power. That is a non-starter for any serious team.
Create a dedicated service account and a constrained workspace.
sudo useradd --system --home /opt/kali-mcp --shell /usr/sbin/nologin kali-mcp
sudo mkdir -p /workspace/{targets,recon,web,evidence,reports,logs,tmp}
sudo chown -R kali-mcp:kali-mcp /workspace
sudo chmod 750 /workspace
Systemd unit with hardening flags
A good habit is to encode constraints in your service definition rather than relying on operator memory.
# /etc/systemd/system/kali-mcp.service
[Unit]
Description=Kali MCP Server
After=network.target
[Service]
Type=simple
User=kali-mcp
Group=kali-mcp
WorkingDirectory=/workspace
ExecStart=/usr/bin/kali-server-mcp --port 5000
Restart=on-failure
# Hardening
NoNewPrivileges=true
PrivateTmp=true
ProtectSystem=strict
ProtectHome=true
ReadWritePaths=/workspace
RestrictAddressFamilies=AF_INET AF_INET6 AF_UNIX
LockPersonality=true
MemoryDenyWriteExecute=true
RestrictSUIDSGID=true
[Install]
WantedBy=multi-user.target
This is not perfect sandboxing, but it meaningfully reduces blast radius for common failure modes.
Network exposure, local-first unless you can justify otherwise
Most Kali MCP deployments should be local-only:
- local socket
- localhost port
- SSH port forwarding if remote access is needed
If you expose your MCP server to a network segment, you’ve turned “AI tool control” into a remotely reachable surface. That is rarely necessary.
If you must expose it, terminate TLS properly and put it behind authentication. Treat it like any other internal control-plane service.
The cockpit requirement, execution is not the product
This is the heart of why teams keep getting disappointed by “AI pentesting.”
They confuse 실행 와 함께 outcome.
A real pentest outcome includes:
- scope correctness
- reproducibility
- evidence that survives review
- clean reporting artifacts
- explicit non-findings where appropriate
- constraints and approvals for destructive actions
A pentesting cockpit is the system that makes those outcomes default. Kali MCP makes execution easy; it does not make outcomes inevitable.
This is the natural place where 펜리전트 를 입력합니다.
Penligent’s positioning is explicit: it is an AI-powered penetration testing platform designed to ship outcomes, not just ideas. The platform emphasizes verification and reportable results, and its product pages and resources frame it as a workflow system rather than a prompt interface. (펜리전트)
Penligent’s own Kali MCP analysis is also explicit: Kali + Claude via MCP is powerful because it’s direct, and that directness is exactly why it’s a poor default for real teams operating on real assets. (펜리전트)
In operational terms, a cockpit layer earns its keep in two places.
첫째, configuration is the hidden cost center. In the field, teams waste time and budget on wordlists, callbacks, proxies, auth contexts, tool versions, and environment drift. A cockpit that treats configuration as a first-class object reduces waste and prevents repeated “token burn” cycles.
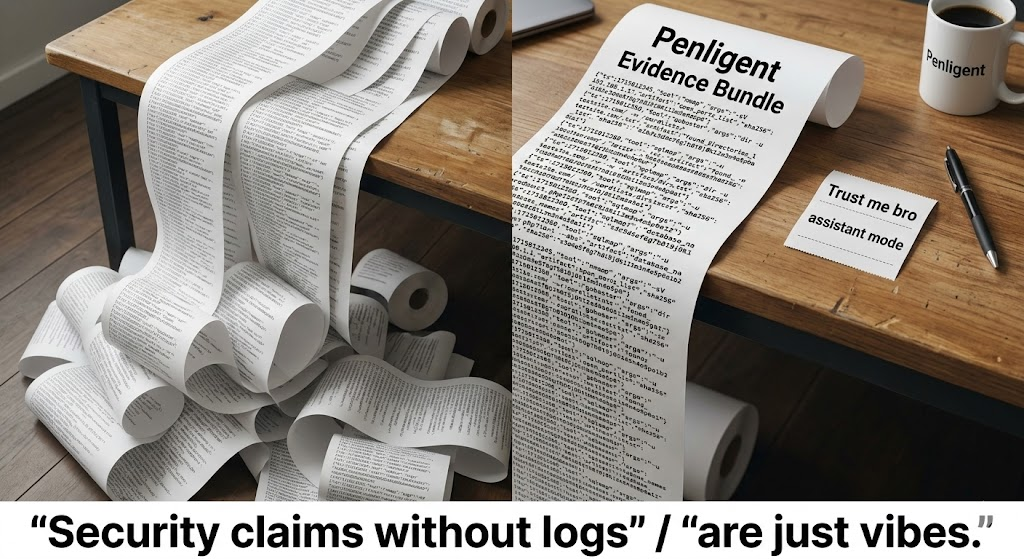
둘째, proof beats persuasion. A cockpit enforces evidence capture and audit logs. You shouldn’t have to remember to save screenshots or export JSON; the system should do it.
That’s the difference between “AI helped me run tools” and “AI helped me deliver a defensible engagement.”
A deliverable Kali MCP workflow, playbooks, policies, and audit artifacts
If you want Kali MCP to be something more than a demo, you need a structure that turns tool execution into deliverables.
The simplest pattern that scales is:
- define a playbook
- enforce tool policies
- capture audit logs
- store evidence in a predictable workspace
- produce a report bundle
Workspace structure, boring is good
/workspace
/targets
/recon
/web
/evidence
/reports
/logs
/tmp
A playbook format, “intent” becomes bounded execution
This is not an MCP standard; it’s a practical wrapper that forces determinism.
target: example.com
scope:
in:
- example.com
- "*.example.com"
out:
- "admin.example.com"
controls:
max_runtime_minutes: 90
require_confirmation_for:
- metasploit
- password_spraying
artifacts:
root: /workspace
logs: /workspace/logs/audit.jsonl
evidence: /workspace/evidence
steps:
- name: passive_subdomains
tool: subfinder
args: ["-d", "example.com", "-silent"]
output: /workspace/recon/subdomains.txt
- name: http_probe
tool: httpx
args: ["-l", "/workspace/recon/subdomains.txt", "-o", "/workspace/recon/httpx.txt"]
- name: port_scan
tool: nmap
args: ["-sV", "-Pn", "-iL", "/workspace/recon/subdomains.txt", "-oN", "/workspace/recon/nmap.txt"]
- name: web_fuzz
tool: ffuf
args: ["-u", "<https://example.com/FUZZ>",
"-w", "/usr/share/wordlists/dirb/common.txt",
"-of", "json",
"-o", "/workspace/web/ffuf.json"]
This playbook is your “truth.” The model can still reason creatively about what to do next, but execution stays inside the defined rails.
Tool policies, the minimum guardrails that prevent easy disasters
A cockpit-grade system does not let the model freely choose tools and flags in production. It constrains choices and escalates to a human only when justified.
Here is a minimal allowlist validation pattern, blocking the most common injection tokens and the most common high-risk flags.
from dataclasses import dataclass
from typing import List
ALLOWED_TOOLS = {"nmap", "ffuf", "nuclei", "sqlmap", "httpx", "subfinder"}
DISALLOWED_TOKENS = [";", "&&", "|", "`", "$(", ">", "<"]
DISALLOWED_FLAGS = {
"sqlmap": {"--os-shell", "--os-pwn"},
"nmap": {"--interactive"},
}
@dataclass
class ToolCall:
tool: str
args: List[str]
def validate(call: ToolCall) -> None:
if call.tool not in ALLOWED_TOOLS:
raise ValueError(f"Tool not allowed: {call.tool}")
for a in call.args:
if any(t in a for t in DISALLOWED_TOKENS):
raise ValueError(f"Suspicious token in arg: {a}")
if call.tool in DISALLOWED_FLAGS and a in DISALLOWED_FLAGS[call.tool]:
raise ValueError(f"Flag blocked for {call.tool}: {a}")
validate(ToolCall("nmap", ["-sV", "-Pn", "example.com"]))
print("validated")
This is not security theater. It is directly motivated by the kinds of failures we saw in MCP server CVEs: untrusted strings reaching a CLI without adequate validation. (NVD)
Evidence and audit, the difference between “it worked” and “it happened”
Engineers trust systems that can be replayed.
A minimal audit log schema should capture:
- timestamp
- project identifier
- step name
- tool and args
- working directory
- execution identity
- exit code
- artifact path
- artifact hash
A JSONL record might look like this:
{"ts":"2026-03-03T18:12:01Z","project":"acme-q1","step":"port_scan","tool":"nmap","args":["-sV","-Pn","example.com"],"cwd":"/workspace","user":"kali-mcp","exit":0,"artifact":"/workspace/recon/nmap.txt","sha256":"<hash>"}
If your Kali MCP workflow can’t produce something like this automatically, it is not suitable for high-stakes environments.
Mapping Kali MCP workflows to real pentest phases
Pentesting is not a single tool call. It is a chain where every step constrains the next.
Below is a mapping that stays realistic and keeps deliverables in view.
| 단계 | 목표 | Typical outputs | Safe default tools |
|---|---|---|---|
| Scope intake | prevent accidental out-of-scope execution | scope file, exclusions, auth notes | text templates, config |
| Passive recon | build target surface without touching too much | subdomain list, DNS notes | subfinder, amass |
| Active recon | validate reachability and services | http probe list, ports, versions | httpx, nmap |
| Discovery | enumerate paths and parameters safely | fuzz JSON, endpoint lists | ffuf, nuclei |
| Hypothesis | pick likely vulnerability classes | candidate list, rationale | model reasoning, knowledge |
| 인증 | collect evidence without destructive impact | request/response captures, logs | curl, browser, burp |
| Reporting | produce defensible artifacts | evidence bundle, report draft | templates + exports |
Kali MCP can help drive many of these steps, but the policy and evidence layers determine whether the chain is safe and defensible.
CVE-driven reality checks, why “execution boundary” is the new center
If you want to explain the difference between an assistant and a cockpit to a hard-core security audience, use real incidents and real CVEs.
Log4Shell, CVE-2021-44228, proof beats explanation
The NVD entry for CVE-2021-44228 describes how attacker-controlled JNDI endpoints could lead to remote code execution via Log4j2 in affected versions, and it notes behavior changes in 2.15.0. (NVD)
CISA’s guidance calls it a critical RCE vulnerability affecting Log4j versions 2.0-beta9 to 2.14.1, known as Log4Shell. (CISA)
The cockpit lesson from Log4Shell is simple: when the world is on fire, you don’t need a model to explain “what is JNDI.” You need a workflow that can:
- identify likely exposure quickly
- verify safely within scope
- capture evidence
- track remediation status
- avoid destructive actions
Kali MCP can accelerate the loop, but only if your system forces evidence capture and scoping discipline. A pure assistant can produce plausible text that looks right and still fails the engagement because it can’t prove what happened.
XZ supply chain compromise, CVE-2024-3094, toolchains are the target
The NVD entry for CVE-2024-3094 documents malicious code discovered in upstream xz tarballs starting with 5.6.0, involving obfuscated build behavior and a modified liblzma that can affect software linked against it. (NVD)
CISA’s alert describes a reported supply chain compromise affecting XZ Utils versions 5.6.0 and 5.6.1. (CISA)
This incident matters in a Kali MCP article because MCP servers are part of your toolchain supply chain. If your execution plane depends on connectors and servers, you must track them like you track packages. A cockpit layer helps by centralizing version pinning, dependency inventory, and patch discipline.
Cisco Catalyst SD-WAN authentication bypass, CVE-2026-20127, exploited control planes are the new big game
The NVD entry for CVE-2026-20127 describes an authentication bypass in Cisco Catalyst SD-WAN Controller and Manager that could allow an unauthenticated remote attacker to bypass authentication and obtain administrative privileges. (NVD)
Cisco’s own security advisory provides the vendor framing and remediation context. (sec.cloudapps.cisco.com)
CISA added CVE-2026-20127 to the Known Exploited Vulnerabilities Catalog and published alerts about ongoing exploitation. (CISA)
Cisco Talos reported active exploitation tracking for CVE-2026-20127. (Cisco Talos 블로그)
This matters for Kali MCP because it demonstrates what attackers increasingly target: control planes. Once you run “AI that can execute” against high-impact infrastructure, you must ensure you can prove, constrain, and audit what your tooling did. It is dangerously easy for an AI-driven workflow to overstep boundaries in environments where a single misstep has enormous consequences.
If you’re doing authorized testing or internal validation for a vulnerability like CVE-2026-20127, a safe cockpit workflow focuses on version identification, exposure assessment, and evidence capture aligned with vendor guidance, not on “try random exploitation attempts.” A cockpit makes the safe approach the default.
Apache bRPC command injection, CVE-2025-60021, classic injection still wins
NVD describes CVE-2025-60021 as a remote command injection vulnerability in a heap profiler built-in service in Apache bRPC versions prior to 1.15.0. (NVD)
CyberArk published technical analysis discussing command injection in the heap profiler endpoint and coordinated disclosure context. (CyberArk)
Red Hat’s CVE page highlights that upgrading to 1.15.0 is a remediation path. (Red Hat Customer Portal)
The cockpit lesson is again not “the model should explain command injection.” The lesson is: if your workflow includes tools or services with diagnostic surfaces, you must treat those surfaces as hostile and enforce strict scope, logging, and verification guardrails.
osTicket arbitrary file read, CVE-2026-22200, untrusted content becomes an execution path
NVD describes CVE-2026-22200 as an arbitrary file read vulnerability in osTicket’s ticket PDF export functionality where crafted rich-text HTML can be insufficiently sanitized before PDF export processing. (NVD)
Horizon3’s research explains the attack mechanics at a high level and why it’s severe, including the role of PDF export processing. (Horizon3.ai)
This is especially relevant to Kali MCP because it’s a reminder: untrusted content is a trigger surface. In MCP-enabled workflows, the model will ingest untrusted content constantly. You must constrain what that content can cause in the execution layer.
Kimi Agent SDK publishing script command injection, CVE-2026-25046, filenames can be inputs too
NVD describes CVE-2026-25046 as a vulnerability where scripts pass filenames to execSync() as shell command strings, and filenames containing shell metacharacters could execute arbitrary commands, with the note that it exists in development scripts and end users are not affected by published extensions. (NVD)
This belongs in a Kali MCP article because it’s another “classic vulnerability meets automation” example: even build scripts and helper scripts can become execution surfaces when routed through automation.
If you want to operate Kali MCP safely, your guardrails should not only constrain “big scary tools.” They should constrain the entire path from untrusted input to command execution.
Kali MCP hardening checklist, what mature teams actually implement
You can compress maturity into a practical checklist:
Identity
- non-root service account for MCP server
- no long-lived secrets in environment variables
- separate workspace with strict permissions
Network
- local-only listener by default
- SSH forwarding rather than exposed ports
- TLS + auth if exposure is unavoidable
정책
- allowlisted tools
- blocked dangerous flags
- explicit approval gates for destructive actions
- rate limits to prevent runaway loops
증거
- deterministic artifact directories
- append-only audit logs
- evidence bundle export path
- retention and redaction rules
Operations
- version pinning for MCP servers and dependencies
- patch cadence and alerting for MCP server CVEs
- periodic review of enabled servers and scopes
This is where a cockpit like Penligent becomes attractive as a default: it centralizes policy and evidence, so it doesn’t rely on operator discipline.
You asked to be explicit: a pure assistant approach, including many PentestGPT-style workflows, is far behind a cockpit approach for real team operations.
That doesn’t mean PentestGPT is bad. It means it’s a different category.
The PentestGPT paper describes it as an LLM-empowered automated penetration testing tool designed with modules to mitigate context loss challenges. (arXiv)
A commonly referenced “Cornell” PentestGPT repository describes the system as operating in an interactive mode to guide penetration testers in overall progress and specific operations. (GitHub)
Those are valuable goals. But the category is still “assistant and guidance,” even when it automates parts of the workflow.
Kali MCP pushes the industry into a different requirement set:
- tool execution is direct
- scope errors have real consequences
- audit requirements are non-negotiable
- evidence capture is mandatory
- multi-user governance matters
A pure assistant is typically missing the core cockpit properties:
- consistent policy enforcement around tools and flags
- robust, structured audit logs as a system of record
- evidence bundling and replay support by default
- configuration surfaces that reduce setup waste
A useful way to say it without hand-waving is to map categories:
| 카테고리 | What it’s great at | What it typically lacks |
|---|---|---|
| Assistant, guidance | methodology, reasoning, planning, summarization | policy enforcement, evidence by default, audit-grade replay |
| Kali MCP execution bridge | fast tool loops, direct execution | governance layer, team workflows, defensible artifacts |
| Cockpit platform, Penligent class | outcomes, evidence, policy, repeatability | less “freeform,” more structured by design |
Kali MCP makes assistants feel obsolete because it turns “advice” into “actions.” But a cockpit still matters because “actions” are not automatically “deliverables.”
Penligent as the cockpit layer for Kali MCP plus native AI
Penligent’s Kali MCP-related pieces lean hard into one point: a direct Kali + native AI + MCP setup is impressive, but it’s not a safe default for teams. (펜리전트)
The cockpit framing is not marketing fluff; it’s an operational argument:
- Kali MCP is an execution path
- you still need governance, evidence, and repeatability
- the closer you get to “AI can execute,” the more you need a control plane that can prove what happened
Penligent’s product materials emphasize verification and reporting outcomes rather than only scanning, and its FAQ and core pages frame it as a platform, not a prompt trick. (펜리전트)
If you want to position Penligent naturally in a Kali MCP story, position it where it actually earns its keep:
- Evidence-first execution A cockpit should treat every execution as producing artifacts, not just output. That’s how you ship results and survive review.
- Policy by default A cockpit should encode what your team considers safe, and enforce it automatically, rather than trusting a model to behave.
- Team-ready workflows Most real pentests are not solo work. You need reproducibility, attribution, and shared context.
- Patch and provenance discipline MCP servers and connectors have CVEs. We’ve already seen that. (NVD) A cockpit can track versions and enforce upgrades, rather than letting connectors drift.
This is also why Penligent’s “OpenClaw + VirusTotal” analysis resonates with MCP thinking: the security boundary is not the model, it’s the integration plane. (펜리전트)
A concrete architecture, Kali MCP as substrate, Penligent as control surface
Here’s a pragmatic way to design the system without pretending MCP is a magic agent brain.
- Keep Kali MCP local on a hardened Kali execution host.
- Expose only safe tools via policies and allowlists.
- Route execution through a cockpit that:
- stores playbooks
- captures artifacts
- records audit logs
- enforces approvals
- Treat the model as a planner and summarizer with bounded execution power.
An ASCII sketch is enough to communicate the separation of concerns:
Native AI client
|
| MCP tool calls (JSON-RPC)
v
Kali MCP server -----> Kali toolchain (nmap, ffuf, nuclei, curl)
|
| audit + artifacts
v
Cockpit layer (Penligent-style)
- scope enforcement
- approvals
- evidence bundles
- reporting exports
This design acknowledges the real world: the model is not the security boundary. The boundary is the control plane.
Closing, the “execution era” requires proof, not vibes
Kali MCP is a milestone because it makes the most important part of pentesting faster: the loop between observation and action.
But it also makes the most dangerous part of pentesting more likely: ungoverned execution.
We already have hard evidence that MCP servers can ship with classic vulnerabilities, and that those vulnerabilities become more dangerous when chained in agentic workflows. (해커 뉴스)
We also have fresh evidence that attackers target control planes and operational surfaces, from SD-WAN authentication bypass exploitation to classic command injection in infrastructure frameworks. (NVD)
So the winning approach is not “AI everywhere.” The winning approach is:
- MCP for capability
- policies for safety
- evidence for truth
- a cockpit for outcomes
That is exactly the gap Penligent is built to fill in a Kali MCP world: turning tool-connected intelligence into controlled execution and reportable results. (펜리전트)
Copyable links, authoritative sources and Penligent internal references
Authoritative external sources Kali mcp-kali-server tool page: https://www.kali.org/tools/mcp-kali-server/ Kali blog, Claude Desktop and Kali LLM workflow: https://www.kali.org/blog/kali-llm-claude-desktop/ Anthropic, Introducing Model Context Protocol: https://www.anthropic.com/news/model-context-protocol MCP specification: https://modelcontextprotocol.io/specification/2025-11-25 Anthropic engineering, code execution with MCP: https://www.anthropic.com/engineering/code-execution-with-mcp NVD CVE-2025-68143: https://nvd.nist.gov/vuln/detail/CVE-2025-68143 NVD CVE-2025-68144: https://nvd.nist.gov/vuln/detail/CVE-2025-68144 NVD CVE-2025-68145: https://nvd.nist.gov/vuln/detail/CVE-2025-68145 The Hacker News, MCP Git server flaws: https://thehackernews.com/2026/01/three-flaws-in-anthropic-mcp-git-server.html NVD CVE-2024-3094: https://nvd.nist.gov/vuln/detail/cve-2024-3094 CISA alert on XZ compromise CVE-2024-3094: https://www.cisa.gov/news-events/alerts/2024/03/29/reported-supply-chain-compromise-affecting-xz-utils-data-compression-library-cve-2024-3094 NVD CVE-2021-44228: https://nvd.nist.gov/vuln/detail/cve-2021-44228 CISA Log4j guidance: https://www.cisa.gov/news-events/news/apache-log4j-vulnerability-guidance NVD CVE-2026-20127: https://nvd.nist.gov/vuln/detail/CVE-2026-20127 Cisco advisory CVE-2026-20127: https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-sdwan-rpa-EHchtZk CISA KEV catalog: https://www.cisa.gov/known-exploited-vulnerabilities-catalog CISA alert adding CVE-2026-20127 to KEV: https://www.cisa.gov/news-events/alerts/2026/02/25/cisa-adds-two-known-exploited-vulnerabilities-catalog CISA partners advisory on exploitation: https://www.cisa.gov/news-events/alerts/2026/02/25/cisa-and-partners-release-guidance-ongoing-global-exploitation-cisco-sd-wan-systems Cisco Talos post on exploitation: https://blog.talosintelligence.com/uat-8616-sd-wan/ NVD CVE-2025-60021: https://nvd.nist.gov/vuln/detail/CVE-2025-60021 CyberArk research on CVE-2025-60021: https://www.cyberark.com/resources/identity-security/cve-2025-60021-cvss-9-8-command-injection-in-apache-brpc-heap-profiler NVD CVE-2026-22200: https://nvd.nist.gov/vuln/detail/CVE-2026-22200 Horizon3 research CVE-2026-22200: https://horizon3.ai/attack-research/attack-blogs/ticket-to-shell-exploiting-php-filters-and-cnext-in-osticket-cve-2026-22200/ NVD CVE-2026-25046: https://nvd.nist.gov/vuln/detail/CVE-2026-25046 Kali Linux + Claude via MCP Is Cool—But It’s the Wrong Default for Real Pentesting Teams: https://www.penligent.ai/hackinglabs/kali-linux-claude-via-mcp-is-cool-but-its-the-wrong-default-for-real-pentesting-teams/ Kali + Claude via MCP Is Amazing — But It’s the Wrong Default for Real Pentesting Teams: https://www.penligent.ai/hackinglabs/kali-claude-via-mcp-is-amazing-but-its-the-wrong-default-for-real-pentesting-teams/ Kali LLM, Claude Desktop, and the New Execution Boundary in Offensive Security: https://www.penligent.ai/hackinglabs/kali-llm-claude-desktop-and-the-new-execution-boundary-in-offensive-security/ OpenClaw + VirusTotal, The Skill Marketplace Just Became a Supply-Chain Boundary: https://www.penligent.ai/hackinglabs/openclaw-virustotal-the-skill-marketplace-just-became-a-supply-chain-boundary/ Claude Code Remote Control security risks, when your local session becomes a remote interface: https://www.penligent.ai/hackinglabs/claude-code-remote-control-security-risks-when-your-local-session-becomes-a-remote-interface/