Backup infrastructure used to be treated as a safety net. In 2026, that is no longer a safe mental model. In real environments, backup servers sit close to hypervisors, identity systems, storage, repositories, service accounts, restore workflows, and disaster recovery operations. If an attacker reaches that layer, they do not just gain a server. They gain leverage over recovery itself. Veeam’s own security guidance is unusually direct on this point: backup infrastructure can become a backdoor into systems and data if it is not hardened, segmented, and administered with care. (Veeam Software)
That is why the search term veeam cve matters far beyond patch management. It is really a search for something larger: how exposed is the recovery plane, how much trust has accumulated around it, and how many organizations still treat “backup” as an operational function instead of a privileged security boundary. The strongest current Veeam stories all point in the same direction. Official advisories from Veeam, CISA’s known exploited vulnerability tracking, and recent reporting from BleepingComputer and SecurityWeek all reinforce the same operational truth: backup infrastructure is now part of the primary ransomware attack path, not merely part of the post-incident response path. (CISA)
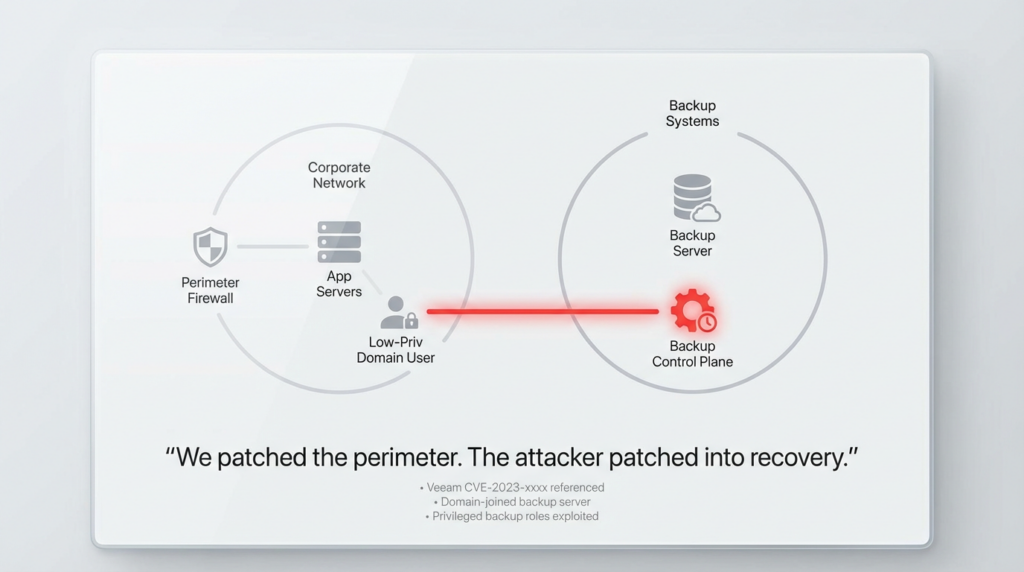
One of the most visible current English-language summaries for this topic is BleepingComputer’s March 12, 2026 coverage of Veeam’s newest patch cycle. That article does something useful that many vendor summaries do not: it frames the latest release not as a single headline flaw, but as a cluster of critical remote code execution issues that let low-privileged domain users, and in one case even a Backup Viewer, reach highly sensitive execution contexts on vulnerable backup servers. That framing is the right one, because defenders who focus on one CVE at a time often miss the architectural lesson. The real problem is not one bug. The real problem is accumulated trust around the backup plane. (컴퓨터)
The Veeam vulnerability story is not one bug — it is a pattern
If you trace the major Veeam vulnerabilities from 2023 through March 2026, a pattern becomes obvious. The specific bug classes vary — missing authentication, deserialization, arbitrary file manipulation, local privilege escalation, abuse of low-privileged product roles, credential extraction, and unsafe restore or service behaviors. But the operational outcome repeats itself: attackers move closer to the accounts, hosts, repositories, and workflows that determine whether an organization can recover from a destructive event. (Veeam Software)
That pattern also explains why Veeam’s own best-practice guidance has kept emphasizing workgroup deployment or a separate management domain, plus stronger protection for administrative accounts. In plain terms, Veeam is telling customers not to let the platform that protects the production domain fully depend on the same trust boundary it is supposed to save. The best-practice guide says the most secure option is to place Veeam components in a management workgroup or in a separate Active Directory forest, with protected administrative accounts. The help center repeats the same philosophy by warning that backup infrastructure can be used as a backdoor. (Veeam Backup)
That advice looks even more justified when you read the actual vulnerability notes. Multiple critical Veeam RCE issues in 2025 and 2026 explicitly affected domain-joined backup servers, or required only low-privileged domain access to move toward code execution on the backup server. When the product vendor’s exploit conditions and the product vendor’s own hardening guidance line up that neatly, defenders should pay attention. (Veeam Software)
The Veeam CVE timeline that actually matters
The table below is not a complete list of every Veeam vulnerability. It is the shortest practical timeline that still captures the attack-surface evolution security engineers need to understand.
| Year | CVE | Product area | What made it matter | 다음에서 수정되었습니다. |
|---|---|---|---|---|
| 2023 | CVE-2023-27532 | Backup & Replication, Cloud Connect | Unauthenticated actor within the backup infrastructure perimeter could obtain encrypted credentials from the configuration database; Veeam specifically called out TCP 9401 and suggested blocking external access as a temporary mitigation | V12 build 12.0.0.1420 P20230223, V11a build 11.0.1.1261 P20230227 (Veeam Software) |
| 2024 | CVE-2024-40711 | Backup & Replication | Unauthenticated RCE, CVSS 9.8; later surfaced in CISA KEV and in ransomware reporting | VBR 12.2 build 12.2.0.334 (Veeam Software) |
| 2024 | CVE-2024-39714 | Veeam Service Provider Console | Low-privileged file upload leading to RCE on VSPC server | VSPC 8.1 build 8.1.0.21377 (Veeam Software) |
| 2025 | CVE-2025-23120 | Backup & Replication v12 | Authenticated domain user to backup-server RCE, CVSS 9.9; domain-joined backup servers only | VBR 12.3.1 build 12.3.1.1139 (Veeam Software) |
| 2025 | CVE-2025-48983, CVE-2025-48984 | Backup & Replication v12 | Critical RCE flaws, both 9.9, again tied to domain-joined infrastructure | VBR 12.3.2.4165 patch (Veeam Software) |
| 2026 | CVE-2025-59470, CVE-2025-55125, CVE-2025-59469, CVE-2025-59468 | Backup & Replication v13 | High-privileged operator roles could be abused for RCE as postgres or root, or for file-write abuse | VBR 13.0.1.1071 (Veeam Software) |
| 2026 | CVE-2026-21666, CVE-2026-21667, CVE-2026-21668, CVE-2026-21672, CVE-2026-21708 | Backup & Replication v12 | Fresh March 2026 cluster: low-privileged domain users to RCE, arbitrary file manipulation on repositories, LPE, and Backup Viewer to postgres RCE | VBR 12.3.2.4465 (Veeam Software) |
| 2026 | CVE-2026-21669, CVE-2026-21670, CVE-2026-21671, CVE-2026-21672, CVE-2026-21708 | Backup & Replication v13 | Fresh March 2026 cluster for v13: authenticated domain user RCE, SSH credential extraction, HA deployment RCE, LPE, Backup Viewer to postgres RCE | VBR 13.0.1.2067 (Veeam Software) |
The reason this timeline matters is that it shows three distinct eras of concern. The first era was credential exposure and unsafe trust around exposed services. The second era was critical pre-auth or near-pre-auth compromise potential on the backup plane. The third era, where we are now, is a sustained stream of flaws that expose the danger of role misdesign, domain trust, and over-connected backup infrastructure. (Veeam Software)

CVE-2023-27532 — the credential exposure bug that changed how defenders looked at Veeam
CVE-2023-27532 remains one of the most important Veeam vulnerabilities to understand, not because it is the newest, but because it clarified how dangerous the backup service boundary really was. Veeam’s advisory said an unauthenticated user operating within the backup infrastructure network perimeter could obtain encrypted credentials stored in the configuration database. The vulnerable service was Veeam.Backup.Service.exe, listening on TCP 9401 by default. Veeam also documented a very practical temporary remediation: block external connections to TCP 9401 on the backup server firewall until the patch can be installed. (Veeam Software)
Researchers at Horizon3.ai pushed the operational understanding further. Their deep dive described how an unauthenticated user with access to the Veeam backup service could request cleartext credentials, reverse engineer the service, and extract credential data through Veeam’s exposed methods. That is exactly the kind of progression defenders should fear in backup infrastructure: not just “some data leak,” but credential material that becomes the bridge to backup hosts, repositories, and eventually broader infrastructure. (Horizon3.ai)
This bug also helped establish a mental model that still holds. The most important question is not “is the service internet-facing.” The question is “who can reach the service from where, and what trust sits behind it.” Many Veeam environments are not exposed directly to the internet, but they are reachable after one internal foothold, one VPN compromise, one management segment mistake, or one lateral move. For attackers, that is good enough. For defenders, it means backup segmentation must be treated as real segmentation, not just a documentation diagram. (Veeam Software)
CVE-2024-40711 — the moment Veeam backup servers moved fully into the ransomware spotlight
If CVE-2023-27532 taught defenders that the backup plane held dangerous credentials, CVE-2024-40711 made the risk impossible to downplay. Veeam’s September 2024 security bulletin described it as an unauthenticated remote code execution vulnerability in Backup & Replication, with a CVSS 9.8 score. That by itself is severe enough. But what turned this bug into a lasting reference point was what happened next: CISA added it to the Known Exploited Vulnerabilities catalog, and later reporting connected it to real ransomware activity. (Veeam Software)
The CISA and partner advisory update on Akira ransomware made the problem even more concrete. In the updated advisory path summarized in late 2025 reporting, Akira operators were observed leveraging Veeam vulnerabilities including CVE-2023-27532 and CVE-2024-40711 after initial access, alongside remote administration tools and other infrastructure abuse, to expand control and delete or impact backups. That matters because it moves the conversation from hypothetical risk to validated attacker behavior. Backup compromise is not a theoretical “worst case.” It is part of the working playbook of real ransomware operators. (CISA)
Veeam’s 2024 bulletin also included additional high-severity issues around MFA bypass by low-privileged roles, remote execution as the service account, file removal, TLS validation weakness during restore operations, and local path traversal to LPE. Read together, those issues show that the attack surface was not limited to one isolated code path. It included identity, transport security, restore trust, and role boundaries. That is why teams who patched 40711 but did not revisit architecture were still missing the larger lesson. (Veeam Software)
The 2025 domain-joined RCE wave — why “inside the domain” became the wrong place for backup servers
In March 2025, Veeam disclosed CVE-2025-23120, a critical RCE on the backup server by an authenticated domain user. The advisory gave it a 9.9 CVSS score and made a deployment detail explicit: the vulnerability only impacts domain-joined backup servers. Veeam recommended upgrading to version 12.3.1 build 12.3.1.1139, while also offering a hotfix path for customers who could not immediately upgrade. (Veeam Software)
That should have been a wake-up call on its own. Instead, the October 2025 patch cycle reinforced it. Veeam’s advisory for build 12.3.2.4165 patched CVE-2025-48983 and CVE-2025-48984, both critical 9.9 RCE vulnerabilities, and again the advisory explained that they affect domain-joined v12 backup infrastructure servers or backup servers. It also noted that non-domain-joined infrastructure was not impacted by that specific class of vulnerability, and that the Veeam Software Appliance plus the upcoming Windows-based v13 architecture were not architecturally impacted in the same way. (Veeam Software)
This is where Veeam’s workgroup-versus-domain guidance stops sounding like generic hardening advice and starts reading like a security boundary model. The best-practice guide says the most secure deployment is a management workgroup or a management domain in a separate Active Directory forest, specifically so that the backup infrastructure does not rely on the environment it is meant to protect. In a world where several of the highest-impact Veeam RCEs have targeted domain-joined deployments, that recommendation should be read as a design control, not an optimization. (Veeam Backup)
The January 2026 Veeam 13 flaws — when privileged product roles become the attack surface
The January 2026 Veeam 13 advisory is important because it shifts the discussion from domain trust to role trust inside the product. According to Veeam’s KB, all disclosed vulnerabilities affected Backup & Replication 13.0.1.180 and earlier v13 builds. The group included CVE-2025-55125, which allowed a Backup or Tape Operator to perform RCE as root by creating a malicious backup configuration file; CVE-2025-59469, which allowed a Backup or Tape Operator to write files as root; CVE-2025-59468, which allowed a Backup Administrator to perform RCE as the postgres user; and CVE-2025-59470, which allowed a Backup or Tape Operator to perform RCE as postgres by sending malicious interval or order parameters. These were fixed in 13.0.1.1071. (Veeam Software)
The most interesting detail in that advisory is not just the impact. It is Veeam’s own severity adjustment note on CVE-2025-59470. While the CVSS severity was critical at 9.0, Veeam explicitly adjusted its response severity because Backup and Tape Operator roles are highly privileged roles that should be protected as such. That line is valuable because it is the vendor spelling out a reality defenders often ignore: when backup products expose granular operator roles, those roles are not “safe convenience accounts.” They are part of the privileged control plane and must be governed like privileged identities. (Veeam Software)
In practice, that means any internal argument like “this account is not a domain admin, it is only a Veeam operator” should be treated as a risk statement, not a reassurance. Backup operator roles can sit close enough to scheduling, repositories, restore paths, configuration files, and service contexts that they become excellent stepping stones in a larger compromise. The January 2026 advisory made that visible in black and white. (Veeam Software)

The March 2026 patch cluster — the most important current Veeam CVE story
If someone searches veeam cve today, the most current story they need to understand is the March 2026 patch cluster. On the v12 line, Veeam’s KB4830 says all vulnerabilities documented there were resolved in 12.3.2.4465 and affected 12.3.2.4165 and earlier v12 builds. The advisory includes CVE-2026-21666 and CVE-2026-21667, both critical 9.9 flaws allowing an authenticated domain user to perform remote code execution on the backup server; CVE-2026-21668, a high-severity arbitrary-file manipulation issue on a Backup Repository; CVE-2026-21672, a high-severity local privilege escalation issue on Windows-based servers; and CVE-2026-21708, a critical 9.9 flaw allowing a Backup Viewer to perform RCE as the postgres user. (Veeam Software)
On the v13 line, Veeam’s KB4831 says the disclosed vulnerabilities affect 13.0.1.1071 and earlier v13 builds and were fixed starting with 13.0.1.2067. The advisory documents CVE-2026-21669, a critical 9.9 RCE for an authenticated domain user on the backup server; CVE-2026-21670, which allows a low-privileged user to extract saved SSH credentials; CVE-2026-21671, a critical RCE affecting HA deployments for a user with the Backup Administrator role; CVE-2026-21672, local privilege escalation on Windows-based servers; and again CVE-2026-21708, Backup Viewer to postgres RCE. (Veeam Software)
That is a serious collection even before you start modeling attack paths. Once you do, the picture gets worse. The recurring theme is that attackers do not necessarily need to start with high privilege or public exposure. In multiple cases they need only a low-privileged domain account, a low-privileged product role, or proximity to the backup environment. That is precisely why these flaws deserve attention from security engineering teams, not only backup administrators. The question is no longer “is Veeam patched.” The question is whether Veeam is reachable from identities or segments that should never have had a path to the recovery plane in the first place. (Veeam Software)
What the highest-visibility current coverage gets right
The current official KBs are the authoritative source for affected versions and fixes, but the most visible reporting adds useful defender context. BleepingComputer’s March 12 article highlighted three newly patched RCE flaws that allow low-privileged domain users to execute code on vulnerable backup servers, plus a fourth that allows a Backup Viewer to gain code execution as postgres. It also noted that Veeam fixed the issues in versions 12.3.2.4465 and 13.0.1.2067. That summary is valuable because it foregrounds exploit preconditions defenders might miss in raw advisories: low complexity 그리고 low privilege in trusted environments can be enough. (컴퓨터)
SecurityWeek’s January 2026 reporting added a second useful lens by connecting Veeam’s long-running exposure to CISA’s KEV catalog. It noted that KEV already included multiple weaknesses in the product, including CVE-2024-40711 and CVE-2023-27532, both tied to ransomware activity. That matters because it turns patch prioritization into a historical pattern problem. When a vendor’s product line repeatedly lands in exploited-vulnerability tracking and ransomware reporting, the right response is not to fix one issue and move on. The right response is to revisit architecture, segmentation, identity design, and monitoring assumptions around the entire platform. (보안 주간)
Why backup infrastructure keeps showing up in ransomware operations
Attackers like Veeam environments for the same reason defenders depend on them. They are central. They often know where the crown-jewel workloads live. They talk to hypervisors, storage, repositories, credentials, and service accounts. They frequently hold enough trust to restore, mount, inspect, or move sensitive data. And if an attacker can disable or manipulate backups before encryption, the victim’s negotiating position changes dramatically. Veeam’s own documentation warns that backup infrastructure can become a backdoor. CISA’s Akira materials and later reporting show how unpatched Veeam systems have fit into real-world attack chains. (Veeam Software)
There is also a structural reason. Backup systems are usually administered by infrastructure teams, not product security teams. That often means they inherit broad trust and deep network reach, but not the same code-review scrutiny, application isolation, or attack-surface management that internet-facing applications receive. The result is an environment that feels “internal,” yet holds many of the privileges and pathways attackers want most. That mismatch between perceived risk and actual privilege is exactly what turns a backup server into an intrusion amplifier. (Veeam Software)
The architecture lesson — Veeam hardening is really trust-boundary design
The single most important lesson from the Veeam CVE history is architectural. Patch management is necessary, but it is downstream. The upstream control is trust reduction.
Veeam’s best-practice material says the most secure deployment is either a management workgroup or a management domain in a separate Active Directory forest. The same guidance explains the logic clearly: the backup infrastructure should not depend on the environment it is meant to protect. The help center expands that into broader security guidelines and hardening recommendations. Running the backup server in a separate workgroup reduces the attack surface and limits lateral movement if domain credentials are compromised; Veeam’s own security best-practices PDF makes that point explicitly. (Veeam Backup)
That means secure Veeam design should start with a few non-negotiable questions. Is the backup server joined to the same production domain it protects? Are operator roles over-granted? Is the backup network truly segmented? Can a normal domain foothold reach backup services? Are restore workflows treated as sensitive trust transitions? Are service accounts monitored as privileged identities? If the answer to several of those questions is uncomfortable, patching one advisory will not be enough. (Veeam Backup)
A practical defender checklist for Veeam right now
The immediate priority is versioning. If you are on the v12 line, the March 2026 fixes landed in 12.3.2.4465. If you are on the v13 line, the March 2026 fixes landed in 13.0.1.2067. Earlier 2026 v13 fixes landed in 13.0.1.1071, and earlier critical v12 fixes landed in 12.3.1.1139 and 12.3.2.4165 depending on the advisory. The official Veeam current-version post also reflects these build milestones. (Veeam Software)
The next priority is deployment model. If the Veeam backup server is still domain-joined to the production domain, the historic vulnerability pattern says you should consider that a design risk, not a neutral default. Several critical 2025 issues explicitly impacted domain-joined backup servers, and Veeam’s own best-practice guidance favors a separate workgroup or management domain. (Veeam Software)
The third priority is role minimization. Backup Administrator, Backup Operator, Tape Operator, and even Backup Viewer have now appeared in advisories as meaningful exploit preconditions. Review who holds those roles, how they authenticate, what MFA protection exists, and whether those accounts are monitored as privileged identities. Treat them the way you would treat a control-plane admin in any other high-value platform. (Veeam Software)
The fourth priority is network control. If your environment still exposes legacy management access more broadly than necessary, narrow it. The lesson from CVE-2023-27532 is still relevant: a service reachable from the wrong place can turn into a credential and control problem. Segment repository access, restrict admin paths, and validate that the backup plane is not reachable from ordinary workstation or general server zones. (Veeam Software)
Sample validation and detection content
Below is a simple PowerShell example that inventories common Veeam services and installed product version information on a Windows backup server. It does not prove vulnerability status by itself, but it gives defenders a fast starting point for host-side validation.
$veeamServices = Get-Service | Where-Object {
$_.DisplayName -like "*Veeam*" -or $_.Name -like "Veeam*"
}
$veeamServices | Select-Object Name, DisplayName, Status, StartType | Format-Table -AutoSize
$paths = @(
"HKLM:\\SOFTWARE\\Veeam\\Veeam Backup and Replication",
"HKLM:\\SOFTWARE\\WOW6432Node\\Veeam\\Veeam Backup and Replication"
)
foreach ($path in $paths) {
if (Test-Path $path) {
Get-ItemProperty $path | Select-Object PSPath, Version, ProductVersion
}
}
For network-focused environments, you should also identify systems that can reach historically sensitive service paths. Veeam’s 2023 advisory explicitly referenced TCP 9401 as the default port for the vulnerable backup service in CVE-2023-27532. Even if that specific bug is patched, reachability to backup services from the wrong segments is still a design smell worth eliminating. (Veeam Software)
A Sigma-style hunting rule for suspicious process creation on a Veeam backup server might look like this:
title: Suspicious Child Process From Veeam Service Context
id: 1f1f44f3-7c8d-4f2a-9d2d-veeam-service-child
status: experimental
logsource:
product: windows
category: process_creation
detection:
parent_image:
ParentImage|contains:
- '\\Veeam.Backup.Service.exe'
- '\\Veeam.Backup.MountService.exe'
suspicious_child:
Image|endswith:
- '\\cmd.exe'
- '\\powershell.exe'
- '\\pwsh.exe'
- '\\rundll32.exe'
- '\\mshta.exe'
- '\\wscript.exe'
- '\\cscript.exe'
condition: parent_image and suspicious_child
level: high
In Microsoft Sentinel or Defender XDR style KQL, you can hunt for unusual execution chains around Veeam processes like this:
DeviceProcessEvents
| where InitiatingProcessFileName in~ ("Veeam.Backup.Service.exe", "Veeam.Backup.MountService.exe")
| where FileName in~ ("cmd.exe", "powershell.exe", "pwsh.exe", "rundll32.exe", "mshta.exe", "wscript.exe", "cscript.exe")
| project Timestamp, DeviceName, InitiatingProcessFileName, FileName, ProcessCommandLine, InitiatingProcessAccountName
| order by Timestamp desc
And if you want a simple Windows logon and privilege-use lens around sensitive Veeam roles and service accounts, start with this hunting pattern:
DeviceLogonEvents
| where AccountName has_any ("veeam", "backup", "svc_veeam")
| summarize FirstSeen=min(Timestamp), LastSeen=max(Timestamp), Hosts=dcount(DeviceName) by AccountName, LogonType
| order by LastSeen desc
None of these examples replaces patching. They help answer a different question: after patching, is anything about this platform still behaving like a control plane under active pressure. That is the more mature question to ask. It aligns with Veeam’s own hardening guidance and with the history of these advisories. (Veeam Software)

What security engineers should remember when they see the phrase veeam cve
The phrase veeam cve sounds like a patching keyword. It is really a control-plane keyword.
The historical record is clear. In 2023, Veeam had a credential exposure issue that showed how dangerous backup-service reachability could be. In 2024, it had an unauthenticated RCE that later appeared in exploited-vulnerability tracking and ransomware reporting. In 2025, multiple critical RCEs hit domain-joined deployments. In January 2026, Veeam 13 showed how dangerous internal product roles could become when treated casually. And in March 2026, the newest advisories again highlighted low-privileged paths to high-impact execution on the backup plane. (Veeam Software)
The engineering conclusion is straightforward. If your backup platform is fully trusted by the same identity boundary it exists to rescue, it is too exposed. If operator roles are treated as routine accounts, they are over-trusted. If your backup network is reachable from ordinary internal footholds, it is under-segmented. And if your validation stops at “the build number looks current,” you are probably checking the easiest thing instead of the most important thing. (Veeam Backup)
The right way to think about Veeam security now is not “backup hygiene.” It is recovery-plane security engineering.
Related reading
Veeam KB4830, the March 2026 v12 advisory with CVE-2026-21666, 21667, 21668, 21672, and 21708. (Veeam Software)
Veeam KB4831, the March 2026 v13 advisory with CVE-2026-21669, 21670, 21671, 21672, and 21708. (Veeam Software)
Veeam KB4792, the January 2026 v13 advisory covering CVE-2025-59470, 55125, 59469, and 59468. (Veeam Software)
Veeam KB4771, the October 2025 v12 advisory covering CVE-2025-48983 and CVE-2025-48984. (Veeam Software)
Veeam KB4724, the March 2025 advisory for CVE-2025-23120. (Veeam Software)
Veeam KB4649, the September 2024 security bulletin covering CVE-2024-40711 and related issues across VBR, Veeam ONE, and VSPC. (Veeam Software)
Veeam KB4424, the March 2023 advisory for CVE-2023-27532. (Veeam Software)
CISA’s KEV catalog entry and alerting around CVE-2024-40711. (CISA)
CISA and partner Akira ransomware update, showing how Veeam vulnerabilities have appeared in real intrusion paths. (CISA)
BleepingComputer’s March 12, 2026 summary of the newest Veeam RCE cluster. (컴퓨터)
Horizon3.ai’s deep dive on CVE-2023-27532. (Horizon3.ai)
From White-Box Findings to Black-Box Proof. (펜리전트)
CVE 2026 — The Vulnerabilities That Matter Most Right Now. (펜리전트)
CVE 2026 The Vulnerability Landscape: When Identity Breaks and Legacy Code Bites Back. (펜리전트)