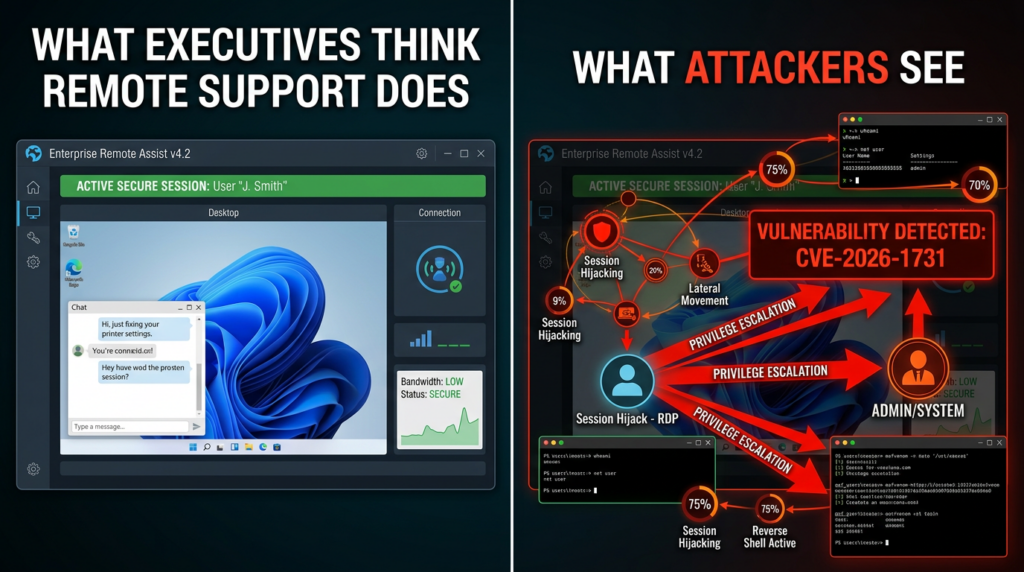
Security teams do not need another reminder that remote access infrastructure sits too close to the center of enterprise trust. CVE-2026-1731 is a fresh example of why. Public records from BeyondTrust, NVD, and multiple threat intelligence teams describe it as a critical pre-authentication remote code execution flaw in BeyondTrust Remote Support and certain older versions of Privileged Remote Access. In plain English, an unauthenticated attacker can send crafted requests and potentially execute operating system commands in the context of the site user, without credentials and without any victim interaction. NVD lists a CVSS v3.1 score of 9.8, while the vendor-supplied CVSS v4 score is 9.9. CISA has also placed the flaw in the Known Exploited Vulnerabilities catalog. (NVD)
That alone would make it urgent. What makes it more important is where it lives. BeyondTrust Remote Support and Privileged Remote Access are not commodity edge appliances in the abstract. They often sit near help desk workflows, privileged sessions, endpoint support paths, and administrative access patterns. When a flaw lands in that layer, compromise is not just about code execution on one service. It is about what that service can reach, broker, launch, and inherit across an enterprise. GreyNoise summarized the pattern well: these products occupy a uniquely sensitive position because attackers who compromise them do not merely gain a foothold, they often gain privileged operational leverage. (GreyNoise)
The basic facts are now stable enough to state confidently. According to BeyondTrust and NVD, Remote Support 25.3.1 and earlier are affected, as are Privileged Remote Access 24.3.4 and earlier. BeyondTrust says its SaaS customers were remediated as of February 2, 2026. Self-hosted customers were told to apply patches manually if automatic updates were not enabled, and customers on sufficiently old builds may need to upgrade before they can apply the relevant fix. BeyondTrust lists Remote Support 25.3.2 and later, and Privileged Remote Access 25.1 or later, as fixed lines, with specific BT26-02 patches also available for supported ranges. (BeyondTrust)
The exploitability picture escalated fast. BeyondTrust’s own advisory timeline says initial exploitation attempts were observed on February 10, 2026. GreyNoise reported that a public proof of concept appeared on February 10 and that reconnaissance against likely targets showed up in its sensor network by February 11, less than twenty-four hours later. Unit 42 later reported in-the-wild exploitation activity associated with malware families including SparkRAT and VShell, and said its Cortex Xpanse telemetry identified more than 16,400 exposed instances potentially vulnerable to the flaw at the time of publication. That sequence matters more than any individual headline, because it is the now-familiar real-world cadence: disclosure, PoC, internet-wide enumeration, opportunistic exploitation, then post-exploitation tooling. (BeyondTrust)
The short answer, before the deep dive
For readers triaging this under time pressure, the operational conclusion is straightforward. CVE-2026-1731 is a critical, pre-authentication, network-reachable RCE affecting BeyondTrust RS and PRA. It requires no login and no user interaction. It is mapped to CWE-78, improper neutralization of special elements used in an OS command. CISA added it to KEV on February 13, 2026, with a due date of February 16 for federal civilian agencies. Public reporting and threat intelligence show exploitation activity and active scanning shortly after disclosure. If you run self-hosted BeyondTrust infrastructure and you have not positively verified remediation, you should treat that as an incident-handling problem, not a routine patching task. (NVD)
A concise version of the technical picture looks like this:
| Campo | Valor |
|---|---|
| CVE | CVE-2026-1731 |
| Product family | BeyondTrust Remote Support, Privileged Remote Access |
| Classe de vulnerabilidade | OS command injection, leading to pre-auth RCE |
| Authentication required | Nenhum |
| User interaction | Nenhum |
| Vendor CVSS v4 | 9.9 Critical |
| NVD CVSS v3.1 | 9.8 Critical |
| Affected RS versions | 25.3.1 and earlier |
| Affected PRA versions | 24.3.4 and earlier |
| Fixed RS version line | 25.3.2 and later, or BT26-02-RS on supported lines |
| Fixed PRA version line | 25.1 and later, or BT26-02-PRA on supported lines |
| KEV status | Sim |
| Public exploitation context | Active exploitation attempts, rapid recon, public PoC, post-exploitation malware observations |
Everything in that table is grounded in BeyondTrust’s advisory, NVD, and associated public reporting. (BeyondTrust)
Why this flaw matters more than a generic RCE headline
There are many critical RCEs every year. Not all of them deserve equal attention. CVE-2026-1731 does, because remote support systems are part of the enterprise control plane, whether organizations admit it explicitly or not. These products exist to bridge operators and endpoints, support staff and systems, privileged users and administrative tasks. A vulnerability at that layer can serve as a force multiplier. The attacker is not breaking into an isolated line-of-business app. The attacker is stepping into a system whose purpose is to reach elsewhere. (GreyNoise)
That is also why defenders should resist the instinct to treat the flaw as “just another web command injection.” The vulnerability class is indeed command injection, and the execution path is rooted in improper input handling. But the business risk comes from the role of the product. Remote support platforms often maintain trust relationships with identity systems, customer environments, privileged workflows, and endpoint fleets. In mature enterprises, even indirect compromise of that layer can create cascading opportunities: credential theft, session hijack, administrative pivoting, remote tooling abuse, or trusted-process masquerading. The line between application compromise and environment compromise is thinner here than it is for a typical web service. (NVD)
There is also a historical reason to take the issue personally. BeyondTrust’s RS and PRA ecosystem was already under intense scrutiny because of the 2024 zero-day chain centered on CVE-2024-12356 and CVE-2024-12686. BeyondTrust’s public investigation materials describe those December 2024 bugs and the subsequent security response, while BleepingComputer reported their use in attacks tied to the Treasury-related incident. GreyNoise explicitly frames CVE-2026-1731 as fitting a continuing BeyondTrust pattern: a new variant appeared in early 2026 on the same broad trust surface that had already proven attractive to serious threat actors. (BeyondTrust)

What actually happened in CVE-2026-1731
The official public description is deliberately short. NVD says that BeyondTrust Remote Support and certain older versions of Privileged Remote Access contain a critical pre-authentication RCE vulnerability, and that specially crafted requests can let an unauthenticated attacker execute operating system commands in the context of the site user. That description is enough to establish severity, but not enough to understand why the bug exists or how defenders should reason about adjacent risk. (NVD)
The most useful public technical write-up came from Unit 42. Their analysis says the flaw affects the thin-scc-wrapper component in unpatched BeyondTrust remote support software and that this component is reachable via the network and handles incoming WebSocket connections. According to Unit 42, the vulnerable path processes a client-supplied remoteVersion value during the WebSocket handshake. The key problem is that the backend script compares version values using bash arithmetic contexts such as (( ... )) ou let. In bash, those contexts can evaluate expressions rather than safely treating all input as inert numeric data. If the input is not rigorously constrained, command substitutions like $(command) may be evaluated before the comparison logic does what the developer intended. (Unidade 42)
That subtlety is worth dwelling on because it explains why these bugs keep recurring in infrastructure code. Developers often think they are writing a bounded comparison routine, perhaps checking client compatibility or version gating. But shell semantics are hostile territory if untrusted data ever reaches an evaluative context. Even when teams add sanity checks after an earlier incident, those checks can be incomplete if they focus on “does this look numeric enough” rather than “can this input ever reach a shell evaluator.” Unit 42 explicitly notes that previous measures reportedly introduced numeric coherence checks, but those checks were not comprehensive enough to prevent bash from evaluating embedded expressions. (Unidade 42)
The result is classic command injection, but wrapped in a path that is easy to underestimate. It is not a giant obvious admin console textbox that screams danger. It is a handshake parameter in a remote support workflow. That is exactly the kind of place where defensive review often weakens. Teams assume protocol metadata is less dangerous than application content. Attackers do not make that distinction. They care only whether the input crosses an execution boundary. In CVE-2026-1731, it did. (Unidade 42)
NVD’s weakness mapping reinforces that interpretation. The flaw is associated with CWE-78, OS command injection. That matters because CWE mappings are sometimes broad, but this one is unusually aligned with the public technical explanation. This is not a vague memory corruption category where the public record leaves room for many plausible exploit shapes. Here, the weakness category, the vendor description, and the third-party technical analysis all point in the same direction: unsafe processing of attacker-controlled input in an operating-system command context. (NVD)

Why WebSocket paths and protocol metadata keep becoming attack surfaces
Security teams have spent years getting good at reviewing classic HTTP forms, REST handlers, file uploads, and template rendering. Many are still weaker at reasoning about “supporting” protocol flows: WebSocket handshakes, device-registration metadata, version negotiation values, agent callback fields, or status beacons. Yet those surfaces often sit in privileged systems where the software authors assume a trusted or semi-trusted client. CVE-2026-1731 is a case study in why that assumption does not hold on internet-reachable systems. (Unidade 42)
The problem is not WebSocket as a protocol. The problem is what teams build around it. When a component exposed to the network accepts client-supplied metadata and passes it into convenience logic written in shell scripts, every tiny parser shortcut becomes security-significant. A version string is no longer just a version string. A capability flag is no longer just a flag. Every field is attacker-controlled until proven otherwise. This is the same lesson defenders have learned repeatedly in VPN appliances, remote management tooling, update agents, mail gateways, and identity edges: the code that “just helps the real workflow happen” is often exactly where pre-auth exploit chains start. (Unidade 42)
The older BeyondTrust history makes this harder to dismiss as bad luck. GreyNoise describes CVE-2026-1731 as a variant of CVE-2024-12356 and says it hit the same WebSocket endpoint class, even if through a different code path. Whether or not every organization accepts that exact framing, the practical lesson is the same: after one serious incident on a high-value remote support surface, defenders should assume similar paths deserve exhaustive review. Variant analysis is not optional after a pre-auth RCE in a remote administration platform. The vendor acknowledgement that Hacktron AI identified this flaw through AI-enabled variant analysis is, in that sense, one of the most important lines in the advisory. (GreyNoise)
The exploitation timeline tells the real story
On paper, many organizations still behave as though critical vulnerabilities unfold over weeks. The public record on CVE-2026-1731 says otherwise. BeyondTrust’s advisory timeline shows patches issued and automatically deployed to SaaS and auto-update-enabled instances on February 2, 2026, customer portal guidance on February 3, public advisory publication on February 6, and initial exploitation attempts observed by February 10. GreyNoise says a public GitHub proof of concept was posted on February 10 and reconnaissance followed by February 11. That is not a leisurely remediation window. It is a few days from vendor action to public awareness, and roughly a day from PoC publication to broad target mapping. (BeyondTrust)
This is the timeline that security engineering teams should build around now. The old model of “read the advisory, schedule the maintenance window, patch next week” breaks down for internet-facing privileged infrastructure. If an appliance, support platform, or access broker is public-facing and pre-auth exploitable, the relevant clock is not your change process. It is the interval between PoC availability and mass reconnaissance. GreyNoise’s observation that one scanner accounted for 86 percent of early reconnaissance sessions also illustrates a point that incident responders know well: the first wave is often driven by a small number of efficient actors or toolkits, not a chaotic crowd. Once they map the landscape, the wider opportunistic ecosystem follows. (GreyNoise)
Unit 42’s findings push the concern further. Their report states that Cortex Xpanse saw more than 16,400 exposed instances potentially vulnerable to the flaw. They also documented post-exploitation activity involving SparkRAT and VShell. SparkRAT is described there as a cross-platform open-source RAT written in Go and used in multiple attacks since at least 2022, while VShell is characterized as a stealthy Linux backdoor and RAT with evasion features including fileless memory execution. Those details matter because they show the bug did not remain a clean theoretical exploit in lab conditions. It moved quickly into the ecology of practical intrusion tradecraft. (Unidade 42)
CISA’s KEV decision also matters as a market signal, not only a federal compliance point. NVD’s change history records the KEV addition date as February 13, 2026, with a due date of February 16 and required action to apply mitigations per vendor instructions or discontinue use if mitigations are unavailable. KEV is not a perfect oracle, but it is one of the clearest public indicators that the vulnerability crossed from “serious disclosure” into “known exploited priority.” (NVD)
Affected versions and what “fixed” actually means
One reason these incidents create avoidable damage is that teams confuse “a patch exists” with “we are remediated.” For CVE-2026-1731, the remediation picture is more specific than many headlines imply. BeyondTrust states that all Remote Support SaaS and Privileged Remote Access SaaS customers had a patch applied as of February 2, 2026. Self-hosted customers, however, were responsible for manual patching if automatic updates were not enabled in the appliance interface. For older release lines, the vendor says some customers must first upgrade to newer versions before they can apply the relevant patch. (BeyondTrust)
The remediation matrix is best expressed plainly:
| Produto | Versões afetadas | Patch path | Upgrade path |
|---|---|---|---|
| Remote Support | 25.3.1 and prior | BT26-02-RS for supported versions 21.3 through 25.3.1 | Upgrade to 25.3.2 or later |
| Privileged Remote Access | 24.3.4 and prior | BT26-02-PRA for supported versions 22.1 through 24.x | Upgrade to 25.1 or later, vendor also notes 25.1.1 or newer as remediation path |
| SaaS deployments | Vendor remediated as of Feb. 2, 2026 | Not customer-applied in normal case | Verify tenancy status and confirmation from vendor |
| Self-hosted without auto-updates | Vulnerable until customer action | Apply vendor patch manually | Upgrade where patch path is not available |
That summary is grounded in the vendor advisory and NVD configuration data. NVD’s CPE history records Remote Support versions up to but excluding 25.3.2 and Privileged Remote Access versions up to but excluding 25.1 as vulnerable. BeyondTrust’s remediation section adds the practical details about patch packages and older supported branches. (BeyondTrust)
There is also an operational nuance many teams miss. Even when a SaaS service is patched by the vendor, the incident question is not over. BeyondTrust’s advisory says exploitation activity was limited to internet-facing self-hosted environments where the patch had not been applied before February 9, 2026. That is reassuring only if you can prove your deployment model and exposure status. Hybrid environments, long-lived appliances, DR instances, lab replicas, customer-managed nodes, and externally reachable admin paths are exactly where assumptions go wrong. You need an inventory-backed answer, not an email-thread answer. (BeyondTrust)

CVE-2026-1731 in the context of the 2024 BeyondTrust failures
CVE-2026-1731 becomes easier to understand when placed next to the 2024 BeyondTrust issues. BeyondTrust’s advisory archive shows CVE-2024-12356 as a critical 9.8 RS/PRA command injection issue, and CVE-2024-12686 as a follow-on command injection issue in the same product family. The BT24-10 advisory says all PRA and RS versions contained a command injection vulnerability exploitable through a malicious client request and that successful exploitation could allow an unauthenticated remote attacker to execute operating system commands in the context of the site user. That should sound uncomfortably familiar. (BeyondTrust)
Public reporting around the 2024 incident chain raised the stakes even further. BeyondTrust’s own security investigation timeline documented discovery of CVE-2024-12356 and CVE-2024-12686 in December 2024, along with cloud patching and disclosure milestones. BleepingComputer reported that those flaws were exploited in the broader compromise context that affected Remote Support SaaS instances and that the Treasury Department was among the impacted downstream customers. Whether one focuses on the geopolitical attribution or not, the core enterprise lesson is inescapable: remote support infrastructure had already demonstrated its potential to sit at the center of a serious national-level incident before CVE-2026-1731 appeared. (BeyondTrust)
GreyNoise’s February 2026 analysis is therefore especially valuable because it ties the new vulnerability to a recognizable strategic pattern rather than treating it as an isolated flaw. Their article states that CVE-2026-1731 is a variant of CVE-2024-12356, calls out the same WebSocket endpoint family, and notes that even before the new CVE existed, they had observed activity replaying the old BeyondTrust exploit chain involving the prior RCE plus PostgreSQL SQL injection. Even teams that prefer to avoid strong lineage claims should pay attention to the implication: if adversaries continue revisiting the same operational surface, defenders should assume there are more variants until proven otherwise. (GreyNoise)
This is where vulnerability management often falls short. Many programs are good at counting CVEs and bad at recognizing patterns. They see one 2024 advisory, one 2025 issue, one 2026 issue, and treat them as separate tickets. Attackers do not. They see a repeated combination of internet exposure, privileged role, and parser fragility. Defenders need to start thinking that way too. (GreyNoise)
Detection, telemetry, and what to look for now
If you are assessing whether you were exposed before patching, detection should begin with the exploit path, not with broad malware hunting. Unit 42 says the vulnerable component handled incoming WebSocket connections and processed the remoteVersion value during the handshake. GreyNoise says attackers rapidly began probing for exposed BeyondTrust instances, including on non-standard ports. That suggests three immediate detection priorities: web access telemetry around BeyondTrust web and WebSocket paths, suspicious handshake or client metadata values, and exposure mapping that does not assume port 443 is the only relevant surface. (Unidade 42)
At a practical level, defenders should review:
| Telemetry source | What to examine |
|---|---|
| Reverse proxy and web logs | Requests to BeyondTrust web and WebSocket paths, especially around /nw or portal-related paths mentioned in public research |
| Appliance and application logs | Errors, anomalous client version values, shell invocation anomalies, unexpected child processes |
| EDR process trees | Bash execution from web-facing service contexts, child processes spawned by support platform components |
| Network telemetry | Unexpected outbound connections, OAST callbacks, downloads of remote tools, connections to suspicious IPs or non-standard destinations |
| Exposure inventory | All public-facing RS/PRA instances, including non-default ports, forgotten labs, DR nodes, or customer-managed deployments |
| Change records | Exact patch application time, whether automatic updates were enabled, and whether any instance remained unpatched after Feb. 9, 2026 |
Each of those review points flows from public exploit and reconnaissance reporting rather than guesswork. (GreyNoise)
The malware reporting around exploitation also gives defenders concrete post-exploitation themes. Unit 42 associated activity with SparkRAT and VShell and published multiple IOCs. Even if an environment did not show those exact artifacts, the classes of behavior remain useful: stealthy Linux backdoors, remote administration payloads, unexpected downloader activity, and post-compromise utilities fetched from public hosting or attacker-controlled infrastructure. When a support platform is exploited, defenders should assume the next step may be persistent remote control or staging for later lateral movement, not just a smash-and-grab command. (Unidade 42)
A safe, non-destructive log hunting pattern in a SIEM might look like this:
// Example KQL hunting pattern for suspicious process launch
DeviceProcessEvents
| where Timestamp > datetime(2026-02-01)
| where InitiatingProcessFileName has_any ("nginx", "httpd", "apache2", "node", "java", "php-fpm", "thin-scc-wrapper", "bt")
| where FileName in~ ("bash", "sh", "dash", "curl", "wget", "python", "perl")
| project Timestamp, DeviceName, InitiatingProcessFileName, InitiatingProcessCommandLine, FileName, ProcessCommandLine, AccountName
| order by Timestamp desc
That query is not a signature for CVE-2026-1731. It is a behavior-led starting point for spotting suspicious child process execution from web-adjacent or appliance-adjacent service contexts. The point is to hunt the consequence of exploitation, not to overfit to one proof of concept.
A complementary Sigma-style pattern could focus on suspicious shell creation on Linux systems hosting support infrastructure:
title: Suspicious Shell Spawned by Remote Support Web Context
id: 6b7e2d8a-7c16-4c2c-9a9f-a0e6beyond1731
status: experimental
logsource:
product: linux
category: process_creation
detection:
parent_image:
- '/usr/sbin/nginx'
- '/usr/sbin/httpd'
- '/usr/sbin/apache2'
- '/bin/thin-scc-wrapper'
child_image:
- '/bin/bash'
- '/bin/sh'
- '/usr/bin/curl'
- '/usr/bin/wget'
- '/usr/bin/python3'
condition: parent_image and child_image
level: high
falsepositives:
- vendor maintenance scripts
- approved troubleshooting actions
Again, this is not meant to be dropped in blindly. It is a starting hypothesis for environments where RS or PRA infrastructure is monitored with host telemetry.
How to validate exposure without turning validation into harm
The wrong way to respond to a headline-grabbing RCE is to copy a PoC from the internet and point it at production. The right way is to separate exposure verification from exploitation and to separate patch validation from incident response. Public sources already tell you enough to build a disciplined workflow. You know the affected products, the affected version ranges, the exposure pattern, and the timing of known scanning and exploitation activity. Use that first. (BeyondTrust)
A safe validation workflow should look like this:
- Enumerate every RS and PRA instance, including internet-facing, internal-only, test, failover, and customer-managed deployments.
- Confirm deployment model for each instance: SaaS, self-hosted with auto-updates, self-hosted without auto-updates.
- Confirm exact version and patch state, not just “latest according to the team.”
- Correlate patch time against the vendor advisory timeline, especially whether any internet-facing self-hosted node remained unpatched after February 9.
- Review web, process, and egress telemetry during the critical window from February 10 onward.
- If anything is ambiguous, isolate the instance and perform authorized testing only in a controlled environment or with the vendor’s approved validation path.
That is incident-grade hygiene, not overreaction. It follows directly from the public timeline and exploitation reports. (BeyondTrust)
Security teams should also resist a familiar trap: patching and then moving on without determining whether the system was already touched. BeyondTrust’s advisory explicitly tells self-hosted customers with internet-exposed unpatched instances as of February 9 to take immediate action and open a Severity 1 ticket. That language is significant. Vendors do not usually use that tone for a vulnerability that is merely theoretical. If you had an exposed self-hosted node in the vulnerable window, retrospective investigation is not optional. (BeyondTrust)
What this vulnerability says about remote support architecture
The most useful article about a CVE is not the one that only repeats the CVSS score. It is the one that helps defenders recognize the design lesson. CVE-2026-1731 is not just a Bash mistake. It is a reminder that remote support infrastructure remains one of the least forgiving places to be sloppy with input handling, especially around pre-auth negotiation logic. Systems in this category are asked to be internet-reachable enough to be useful, privileged enough to solve hard problems, and complex enough to broker sessions, clients, versions, and compatibility states. That combination is exactly why they make such attractive targets. (GreyNoise)
It is also why recurring vulnerability classes matter more than individual patch numbers. Once a product family has shown command injection or pre-auth parser abuse on a sensitive boundary, defenders should assume adjacent paths are risky too: version negotiation, WebSocket handlers, updater channels, support applets, file-transfer helpers, session brokers, reporting subsystems, and compatibility checks. Threat actors are good at reading vendor advisories historically, diffing fixes, and turning one public lesson into a search for the next variant. The vendor acknowledgement that AI-assisted variant analysis found CVE-2026-1731 should make defenders more realistic, not more complacent. If researchers can do that, adversaries can too. (BeyondTrust)
Where continuous validation becomes more useful than static scanning
One reason high-value infrastructure bugs keep surprising organizations is that too many environments still rely on static asset inventories, version banners, or quarterly scanning logic to judge whether they are safe. That model breaks down when the real question is not just “is this version vulnerable” but “was this exposed, reachable, and meaningfully exploitable in the way our environment is actually deployed.” Public reporting on CVE-2026-1731 underscores that difference. Reconnaissance shifted to non-standard ports. Exposure counts mattered. Deployment model mattered. Patch timing mattered. Post-exploitation behavior mattered. None of that is captured by a simplistic “software present” check. (GreyNoise)
That is the natural point where a platform like Penligent fits. For security teams dealing with high-impact CVEs, the real challenge is often not discovering the CVE record. It is validating exposure and prioritizing response in a way that reflects how attackers actually operate. Penligent’s own CVE-focused material frames this as continuous validation rather than static scanning, and that framing is appropriate here. In a case like CVE-2026-1731, defenders need to combine reachable attack surface, patch state, telemetry clues, and controlled validation logic, not just a version string in a dashboard. (Penligente)
There is also a broader strategic reason this matters. Remote support, identity edges, AI-enabled operational tooling, and internet-facing admin planes are converging into a category of systems where exploitability is dynamic. The vulnerability record is only the start. The real security question is whether the path can be exercised in your deployment, what privileges it exposes, what compensating controls exist, and whether exploitation leaves observable traces you are prepared to detect. That is exactly where reasoning-driven validation becomes more valuable than passive inventory alone. (Penligente)
What defenders should do this week
The practical response to CVE-2026-1731 should be direct.
First, verify whether any self-hosted BeyondTrust RS or PRA instance existed in a vulnerable state after February 9, 2026. If yes, treat that as potentially exposed infrastructure and investigate accordingly. Second, confirm remediation against the vendor’s exact fixed versions or patch packages, not informal team memory. Third, review logs for WebSocket-related requests, suspicious child process creation, anomalous outbound traffic, and post-exploitation tooling indicators. Fourth, do not assume your only risk is on port 443 or on officially documented internet-facing nodes. GreyNoise’s findings on non-standard ports should end that assumption. Finally, use this incident to review remote support architecture as a class: what is exposed, what is privileged, what is internet-reachable, and what supporting scripts still touch shell contexts or legacy parsing paths. (BeyondTrust)
For security leadership, the governance lesson is just as important as the technical one. Remote support and privileged access platforms should sit in the very top tier of emergency patching and variant review. If your organization has a “patch later, investigate later” culture around those systems, CVE-2026-1731 is your evidence that the model is obsolete. The vulnerability was public on February 6. Exploitation attempts were observed by February 10. Recon was visible essentially immediately after PoC publication. In 2026, that is the operating environment. (BeyondTrust)
Tomada final
CVE-2026-1731 is important not because it is flashy, but because it is familiar in the worst possible way. It is a pre-auth command injection flaw in a high-trust remote support surface, on a product family that had already demonstrated strategic value to serious attackers. The technical mechanism is concrete, the exposure is measurable, the remediation path is known, and the exploitation timeline is short. That combination should push defenders toward a simple conclusion: remote support infrastructure belongs in the same mental category as identity edges and privileged access brokers. When it breaks, it breaks above its apparent weight. (NVD)
The right response is not panic. It is disciplined urgency. Inventory the surface. Verify the patch state. Investigate the window of exposure. Hunt for post-exploitation behavior. Then review the architecture as though attackers will keep coming back to the same class of logic, because the public record strongly suggests they will. (GreyNoise)
Further reading and related English references
NVD record for CVE-2026-1731, including severity, CWE mapping, KEV status, and change history. (NVD)
BeyondTrust advisory BT26-02, including remediation paths, affected versions, SaaS status, and timeline updates. (BeyondTrust)
Rapid7 analysis of CVE-2026-1731, with product/version impact summary and severity framing. (Rapid7)
GreyNoise analysis of rapid post-disclosure reconnaissance and the relationship to prior BeyondTrust exploitation history. (GreyNoise)
Unit 42 analysis of exploitation activity, technical mechanism, exposed-instance telemetry, and observed malware including SparkRAT and VShell. (Unidade 42)
BeyondTrust BT24-10 on CVE-2024-12356, the earlier critical command injection issue in RS/PRA. (BeyondTrust)
BeyondTrust’s SaaS security investigation timeline covering the December 2024 incident context. (BeyondTrust)
Penligente, CVE 2026 The Vulnerability Landscape, When Identity Breaks and Legacy Code Bites Back. (Penligente)
Penligent CVE category page, including related vulnerability analysis articles. (Penligente)
Penligente, Notepad CVE, When a Text Editor Becomes an Execution Path. (Penligente)