CVE-2026-20131 is a critical flaw in the web-based management interface of Cisco Secure Firewall Management Center, or FMC. Cisco and NVD describe it as an insecure deserialization issue in a user-supplied Java byte stream that lets an unauthenticated remote attacker execute arbitrary Java code as root on an affected device. The same public record also makes one other point easy to miss: this is not just a serious bug in a web interface. It lands on the system many teams use to define firewall policy, manage upgrades, and aggregate security telemetry across their estate. That changes the operational meaning of the vulnerability immediately. (NVD)
By March 2026, the public picture had already moved beyond hypothetical risk. AWS said its threat intelligence teams found activity tied to exploitation beginning on January 26, 2026, which put live use of the flaw 36 days ahead of Cisco’s March 4 disclosure. On March 19, the issue was added to CISA’s Known Exploited Vulnerabilities catalog. That is the difference between a high-severity patch bulletin and a management-plane incident that deserves urgent inventory, containment, patching, validation, and compromise assessment in the same workflow. (Amazon Web Services, Inc.)
A lot of quick coverage stops there. It says “CVSS 10,” “unauthenticated RCE,” and “patch now,” then moves on. That is not enough for engineers who actually have to decide whether an FMC appliance is internet-reachable, whether a patch window is sufficient, whether an exposure path still exists after the upgrade, or whether pre-patch access may already have been used to establish persistence. CVE-2026-20131 is one of those cases where the public record is already rich enough to support much better analysis than the average summary provides. (NVD)
What the public record confirms
The basic facts are unusually clear. Cisco’s advisory stream and NVD both describe a pre-authentication remote code execution path in FMC’s web management layer. Cisco scores it 10.0 on CVSS 3.1 with the vector AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H. NVD maps the weakness to CWE-502, Deserialization of Untrusted Data. Cisco also states that no workaround exists, and that if the FMC management interface is not exposed to the public internet, the attack surface is reduced. Reduced does not mean eliminated. It means one obvious external path narrows, not that the system becomes low-risk. (NVD)
The product scope matters almost as much as the bug class. Cisco’s own advisory snippets state that CVE-2026-20131 affects Cisco Secure FMC Software and Cisco Security Cloud Control Firewall Management regardless of device configuration. Public summaries from Arctic Wolf add an important cloud nuance: SCC Firewall Management, as a SaaS-delivered service, was upgraded by Cisco during maintenance, so customers did not need to take a separate patch action there. That distinction matters because many hybrid Cisco environments use both cloud-managed and on-premises administration surfaces, and confusing them wastes response time. (Cisco)
The table below consolidates the most important confirmed facts before we get into mechanism, exploitation, and response. It is intentionally narrow and only includes points backed by primary or high-confidence sources. (NVD)
| Item | Confirmed public detail |
|---|---|
| CVE | CVE-2026-20131 |
| Produto | Cisco Secure Firewall Management Center, plus Cisco Security Cloud Control Firewall Management |
| Classe de vulnerabilidade | Insecure deserialization of a user-supplied Java byte stream |
| Authentication required | Nenhum |
| Remote exploitability | Sim |
| User interaction required | Não |
| Result of successful exploitation | Arbitrary Java code execution as root |
| CVSS 3.1 | 10.0 Critical |
| Weakness mapping | CWE-502 |
| Workaround | None published by Cisco |
| Exposure note | Public internet access to the management interface increases the attack surface |
| Exploitation status | AWS reported exploitation activity beginning January 26, 2026 |
| KEV status | Added to CISA KEV on March 19, 2026 |
That compact summary already tells you why this is not a “wait for the next maintenance cycle” issue. A remotely reachable, unauthenticated, root-level code execution bug on a platform that governs security policy is a concentration-of-trust problem as much as a software flaw. The KEV addition reinforces that point. NVD’s KEV section shows CISA added the vulnerability on March 19 and assigned a March 22 due date with instructions to apply vendor mitigations, follow cloud guidance where appropriate, or discontinue use if mitigations were unavailable. (NVD)
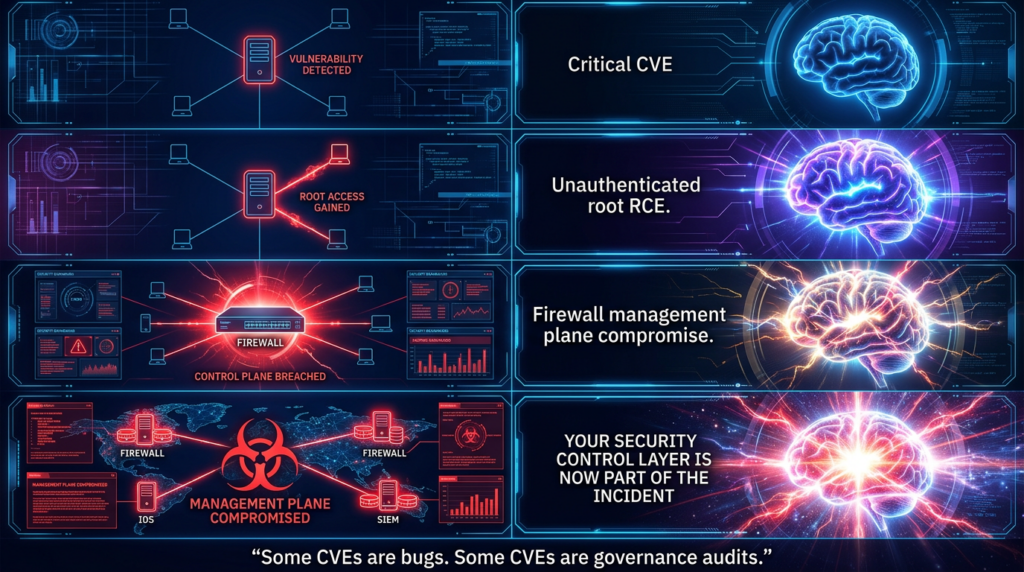
Why the FMC management plane changes the severity conversation
Cisco FMC is not just another web application with admin pages. runZero describes it as a centralized administrative platform used to configure security policies, manage firmware updates, and aggregate threat telemetry across physical and virtual Cisco security appliances from a single interface. That is the sentence that should drive prioritization. If a routine line-of-business server gets compromised, the response is serious but localized. If the system that defines firewall policy and visibility gets compromised, the trust model of the defensive stack itself is in question. (runZero)
That difference is why CVSS alone is not enough to explain CVE-2026-20131. The vulnerability earns a perfect 10.0 because it is network-reachable, low complexity, requires no privileges, requires no user interaction, and impacts confidentiality, integrity, and availability at a high level. But the architectural significance is even bigger than the score implies. The affected system is positioned at the point where configuration authority, operational visibility, and administrative access converge. An attacker who lands there is not starting from an arbitrary Linux host. They are landing at a control point. (NVD)
That is also why the CVSS vector’s S:C, or changed scope, deserves attention. In practical terms, defenders should read that not as a scoring curiosity but as a reminder that the consequences extend beyond a single vulnerable component. When a management plane can be pushed from an unauthenticated web request to root-level code execution, the impact spills into policy control, credentials, downstream visibility, and the credibility of the management surface itself. Even before any post-exploitation action is observed, the compromise has crossed a trust boundary that most environments cannot afford to treat casually. (NVD)
The management-plane angle also explains why “not exposed to the public internet” is only a partial relief. Cisco’s note, repeated in NVD, says the attack surface is reduced when the management interface does not have public internet access. That is true and important. But reduced attack surface is not the same as acceptable risk. If an attacker already has internal foothold, VPN access, a pivot through another management zone, or a partner network path, the value of FMC as a target remains high. In mature environments, the management plane should be isolated precisely because external attackers are not the only attackers that matter. (NVD)
This is where many patch summaries become too shallow. They frame the question as “Is the interface internet-facing?” The better question is “Which trust domains can reach this interface, and how confidently can we prove that list has been tightened?” The first question is about exposure at one moment. The second is about administrative design. CVE-2026-20131 is best understood as a forced audit of that design. (runZero)
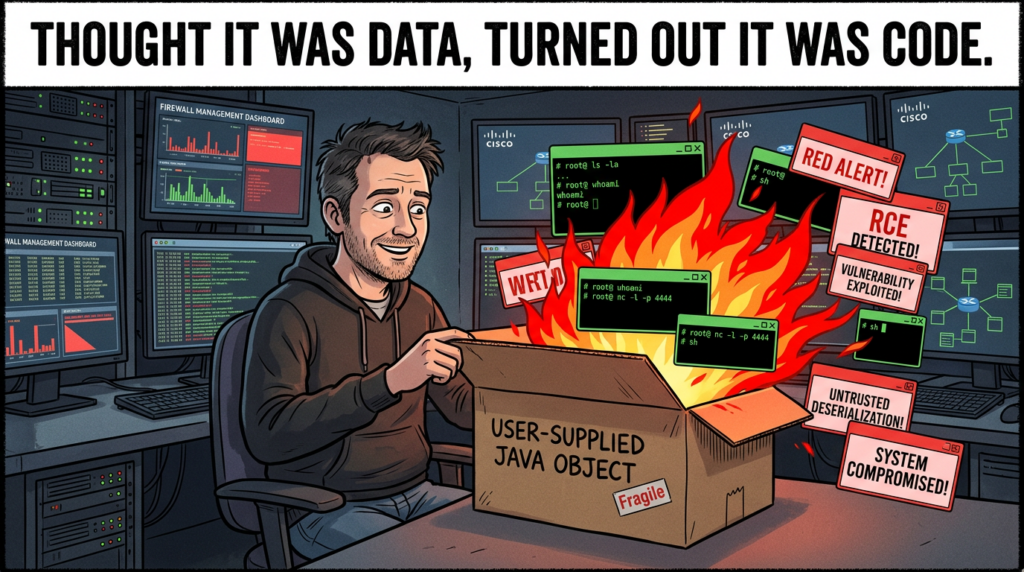
How the bug works without mystifying it
The public record is specific enough to explain the vulnerability class without inventing Cisco-internal details that have not been published. Cisco and NVD say the flaw is due to insecure deserialization of a user-supplied Java byte stream. The important engineering point is that deserialization is not merely “parsing text.” It is reconstructing object state from attacker-controlled input. If the application trusts that input too broadly, allows risky object graphs, or permits execution paths during object reconstruction that should never be reachable from untrusted data, the deserialization step becomes a code execution primitive rather than a data handling routine. (NVD)
In plain terms, the danger of insecure deserialization is that the application is not just reading values from a request. It is rehydrating behavior-bearing structures. In many Java ecosystems, that has historically created space for gadget chains, class-loading abuse, or side effects that occur during object construction or method invocation. The public sources for CVE-2026-20131 do not publish a vendor-confirmed gadget chain, endpoint walkthrough, or exploit recipe, and a responsible analysis should not pretend otherwise. What is confirmed is enough: a crafted serialized Java object sent to the FMC management interface can lead to arbitrary code execution with root privileges. (NVD)
That last clause matters. This is not described as arbitrary code execution in an unprivileged web worker that must then be chained with a separate privilege escalation. Cisco’s description and NVD’s copy both state that successful exploitation can execute arbitrary code on the device and elevate privileges to root. For defenders, that means the exploit path itself already collapses several usual response assumptions. You do not get to comfort yourself with “they still need local escalation.” The public record says the exploit path can end at root. (NVD)
Because the issue is pre-authentication, any control strategy that begins with “make sure all admins have MFA” is incomplete. MFA is still necessary for the platform. It just is not the first thing that stands between this bug and root. That is another reason the management-plane context is so important. Many organizations are accustomed to thinking of admin interface protection in identity-first terms. CVE-2026-20131 reminds them that identity controls do not help when the attacker is not entering through the login flow at all. (NVD)
The difference between a dangerous deserialization flaw and a headline that engineers can act on is operational specificity. Here, the specificity is not in a public exploit. It is in the combination of confirmed facts: the vulnerability class, the pre-auth remote reachability, the root outcome, the lack of workarounds, the affected management platform, the later exploitation evidence, and the fixed branch data. That combination is more than enough to justify an aggressive response even if you never see a weaponized proof of concept. (NVD)
The affected releases and the safe upgrade targets
One of the easiest ways to waste time during response is to treat Cisco release families as interchangeable. They are not. runZero’s March 18 asset guidance gives the clearest public branch map and is consistent with the published advisory flow around FMC. The safe target depends on the branch you are on. That sounds obvious, but it is exactly where rushed enterprise responses go wrong, especially when two critical FMC CVEs are being handled at once. (runZero)
The branch guidance that is most useful for defenders is summarized below. For 7.4 and 7.6, pay attention to the distinction between the version that fixes CVE-2026-20079 and the one that fixes CVE-2026-20131. If you are responding to the overall March FMC emergency, the higher floor is the only one that matters. (runZero)
| Current release family | Publicly affected floor | Safe target for CVE-2026-20131 | Important note |
|---|---|---|---|
| 6.4.0.13 through 6.4.0.18 | Affected | Upgrade to 7.0.9 or later | Legacy branch requires jump |
| 7.0.x | Prior to 7.0.9 | 7.0.9 or later | Applies to FMC on this branch |
| 7.1.x through 7.2.x | Prior to 7.2.11 | 7.2.11 or later | Includes 7.1.x and 7.2.x |
| 7.3.x through 7.4.x | Prior to 7.4.6 | 7.4.6 or later | 7.4.4 covers CVE-2026-20079, but not enough for 20131 |
| 7.6.x | Prior to 7.6.5 | 7.6.5 or later | 7.6.4 covers CVE-2026-20079, but not enough for 20131 |
| 7.7.x | Prior to 7.7.12 | 7.7.12 or later | Treat as full-floor target |
| 10.0.0 | Affected | 10.0.1 or later | Listed for CVE-2026-20131 only |
The 7.4 and 7.6 nuance is exactly the sort of detail that gets lost in “patch now” reporting. If your environment is on 7.4.x and someone upgrades to 7.4.4 because they were tracking the companion auth-bypass advisory first, the FMC estate is still not at the public safe floor for CVE-2026-20131. The same logic applies to 7.6.4 versus 7.6.5. In real environments, partial correctness is often operationally indistinguishable from failure because the system still remains exposed. (runZero)
Cisco’s advisory snippets also make two other points that matter during change management. First, Cisco says there are no workarounds. Second, the advisory text indicates that the issue affects FMC and SCC regardless of device configuration. That combination means you should not spend hours looking for a clever configuration toggle that magically removes the bug. The useful questions are version, exposure path, and whether the system was reachable long enough to justify compromise assessment. (Cisco)
For cloud-managed teams, the SCC detail narrows the problem. Public reporting that cites Cisco’s guidance says Cisco had already upgraded the SaaS service as part of routine maintenance, and no customer action was required there. For on-premises FMC, the burden stays with the customer: identify the branch, move to the right target, and validate the result. That split is important because it prevents two opposite mistakes at once: unnecessary panic for SCC, and false comfort for on-prem FMC. (Arctic Wolf)
Why CVE-2026-20079 belongs in the same incident
CVE-2026-20131 is serious enough on its own, but a response that handles it in isolation is missing the operational shape of the event. On the same day Cisco disclosed CVE-2026-20131, it also disclosed CVE-2026-20079, another critical Cisco FMC vulnerability. NVD describes CVE-2026-20079 as an unauthenticated remote authentication bypass in the FMC web interface that stems from an improperly created system process at boot time. Successful exploitation lets an attacker execute script files on the affected device and obtain root access to the underlying operating system. (NVD)
The technical classes are different. CVE-2026-20079 is about authentication bypass and script execution. CVE-2026-20131 is about insecure deserialization and Java code execution. The operational meaning is nearly identical. Both are pre-authentication. Both are remote. Both can end at root. Both land on the same management plane. Both were disclosed together as part of Cisco’s March 2026 firewall security publication. If you assign them to different owners and never reunify them in one management-plane response, the ticketing system has become smarter than the organization. (runZero)
Arctic Wolf’s public bulletin is useful precisely because it presents the two bugs together as maximum-severity Cisco FMC issues. That framing is more useful than catalog-driven thinking. Engineers do need the separate CVE numbers, separate branch notes, and separate root causes. Leadership and operations teams also need the higher-order truth: there were two separate unauthenticated root paths into the same firewall administration surface at the same time. That is a management-plane emergency, not a pair of unrelated bug classes. (Arctic Wolf)
A compact comparison makes the relationship clearer. (NVD)
| CVE | Causa raiz | Entry condition | Confirmed outcome | Most important operational lesson |
|---|---|---|---|---|
| CVE-2026-20079 | Improper system process created at boot, leading to auth bypass | Unauthenticated crafted HTTP requests | Script execution and root access | Identity controls do not save you if the login barrier is bypassed |
| CVE-2026-20131 | Insecure deserialization of attacker-controlled Java byte stream | Unauthenticated crafted serialized object to the web interface | Arbitrary Java code execution and root access | Unsafe object handling on a management plane is enough to become full compromise |
For response teams, the practical conclusion is simple. If you are checking FMC versions, isolating admin reachability, reviewing logs, or planning post-patch compromise assessment, both CVEs belong in the same room. Even when the exact exploit evidence later centered on CVE-2026-20131, the broader lesson did not change: the administrative surface itself was under maximum-severity stress. (Amazon Web Services, Inc.)

The timeline is the story
The public timeline around CVE-2026-20131 is one of the strongest reasons this issue deserves more than generic patch advice. Cisco first published the advisory on March 4, 2026. By March 6, Arctic Wolf’s bulletin said it had not observed threat actors exploiting the vulnerabilities and was not aware of public proof-of-concept exploits, while still warning that reverse engineering of the patched releases was likely because of the level of access the flaws could provide. That was a reasonable statement at the time. It was also incomplete in the way early vulnerability intelligence often is. (Cisco)
On March 18, AWS published a much more consequential update. Its threat intelligence teams said they had identified active Interlock ransomware activity exploiting CVE-2026-20131 and that their research found exploitation beginning on January 26, 2026, 36 days before Cisco’s public disclosure. That changed the interpretation of the vulnerability from “highly dangerous and likely to be weaponized” to “already used as a zero-day against real targets.” (Amazon Web Services, Inc.)
One day later, NVD reflected the CISA KEV change record: on March 19, the vulnerability was added to CISA’s Known Exploited Vulnerabilities catalog with a due date of March 22 and a required action that told agencies to apply vendor mitigations, follow the relevant cloud guidance, or discontinue use of the product if mitigations were unavailable. Whether you are in a U.S. federal context or not, that is a strong public signal about how seriously government defenders were expected to treat the issue. (NVD)
This sequence matters because it shows how fragile static vulnerability summaries can be. A March 6 post saying “no exploitation observed” can be perfectly honest and still become insufficient days later. Engineers should not read that as a failure of one analyst. They should read it as a reminder that management-plane bugs can move from disclosure to confirmed threat activity, or from uncertain visibility to retrospective zero-day confirmation, faster than routine patch governance expects. (Arctic Wolf)
There is also a quieter lesson in the dates. The gap between January 26 and March 4 is not just a statistic. It is the period in which any organization with a reachable FMC surface could have been exposed without knowing the CVE existed. That is why the right question after patching is not only “Are we safe now?” but also “What should we verify about the period before the fix?” If the system was externally reachable or reachable from an untrusted network segment during that window, it deserves more than a version check. (Amazon Web Services, Inc.)
What AWS observed in the Interlock campaign
AWS’s March 18 write-up is the most valuable public source on what post-disclosure defenders should actually hunt. The article says Amazon threat intelligence identified activity related to CVE-2026-20131 beginning January 26. The observed activity involved HTTP requests to a specific path in the affected software. AWS does not reduce the story to “attacker sent exploit, got shell.” It describes a fuller chain: request bodies containing Java execution attempts, embedded URLs that supported the exploit, a verification mechanism that relied on an HTTP PUT upload from the victim, and follow-on delivery of an ELF binary from a remote server once exploitation appeared successful. (Amazon Web Services, Inc.)
That detail is valuable because it shifts response from abstract severity to concrete investigative hypotheses. If your logs show only generic web requests and you never look for callback behavior, staged configuration delivery, or outbound fetches from the FMC host, you may miss the part of the intrusion that matters most. The exploit is not the only event. It is the opening move in a larger chain. Public reporting that stops at “root RCE is possible” does not help defenders decide where to search next. AWS’s write-up does. (Amazon Web Services, Inc.)
One of the most important observations in the AWS material is the alternative payload path involving a Java class file that becomes a memory-resident webshell. According to AWS, when the class is loaded by the JVM, its static initializer registers a ServletRequestListener with the server’s StandardContext, creating a persistent in-memory backdoor that intercepts HTTP requests without writing a file to disk. That is not a trivial detail. It means defenders who only look for dropped binaries or changed files can miss a post-compromise foothold that lives in runtime state instead. (Amazon Web Services, Inc.)
AWS also says that this memory-resident backdoor inspects requests for specially crafted parameters containing encrypted command payloads, decrypts them with AES-128 using a hardcoded seed-derived key, treats the result as compiled Java bytecode, and executes it dynamically in memory. Again, the right takeaway is not how to recreate the mechanism. The right takeaway is that the attack path includes a fileless option designed to evade simple file-based antivirus logic. Post-patch review has to account for that. (Amazon Web Services, Inc.)
A separate AWS-recovered component listened on TCP port 45588 for connectivity verification. The technical role of that tool is less important than the investigative implication. If an FMC appliance that should be tightly managed and quietly operated shows evidence of unusual listening behavior on unexpected high ports, that is the kind of anomaly that should be correlated with other signs rather than dismissed as a one-off misconfiguration. (Amazon Web Services, Inc.)
The campaign visibility AWS obtained also extended beyond the initial Linux-side foothold. The article describes follow-on tooling attributed to Interlock, including reconnaissance and data collection activity on Windows environments, staging to network shares, custom remote access trojans, and infrastructure relationships that supported the broader ransomware workflow. For defenders, that widens the scope of compromise assessment. If FMC was exposed and suspicious activity exists, the question is not only whether the appliance itself was hit. The question is whether it became the opening door into a larger enterprise intrusion chain. (Amazon Web Services, Inc.)
Detection and hunting, the signals that actually matter
The best public hunting clues are in the AWS indicators section. AWS explicitly warns that many file hashes are unreliable as standalone indicators because the threat actor varied scripts and binaries across targets. That is a critical warning for defenders who still think IOC matching begins and ends with SHA-256 values. In this campaign, the more durable signals include infrastructure, protocol fingerprints, specific user-agent patterns, runtime behavior, and post-compromise operational patterns. (Amazon Web Services, Inc.)
At the network layer, AWS published exploit source IP addresses, exploit support domains, C2 domains, JA3 and JA4 fingerprints, and an exploit HTTP user-agent string. Those are useful for retrospective review of web logs, proxy logs, Zeek, Suricata telemetry, and TLS metadata. They are not a guarantee of detection, because actors can shift infrastructure and fingerprints. But they are very good starting points for scoping whether your environment saw traffic that resembles the campaign AWS documented. (Amazon Web Services, Inc.)
At the application and runtime layer, the most valuable clue is the ServletRequestListener behavior described in the memory-resident webshell section. Most production Java web applications do not dynamically register such listeners during ordinary FMC administration workflows. If you have JVM telemetry, web container instrumentation, or forensic memory capture capability, this behavior is much higher signal than generic “Java process did something interesting.” It points directly at a persistence technique AWS observed in connection with the campaign. (Amazon Web Services, Inc.)
At the host and lateral-movement layer, AWS’s observations about PowerShell-based reconnaissance, data staging to network shares using per-host directories, HAProxy with aggressive log deletion, and unusual connections to high-numbered ports create strong hunting opportunities even outside the original FMC system. Those signals matter because they help teams avoid a common failure mode: patching the entry point but not hunting the follow-on tradecraft that already passed through it. (Amazon Web Services, Inc.)
The hunt matrix below is not exhaustive, but it organizes the public clues by the kind of question each one helps answer. It is built from AWS’s published observations and should be treated as a scoping aid, not a complete detection package. (Amazon Web Services, Inc.)
| Signal type | Example public clue | What it can help answer |
|---|---|---|
| Web and proxy logs | Specific exploit source IPs and the published Firefox 136 user-agent | Did the environment see traffic that overlaps with AWS-observed exploit activity |
| TLS metadata | Published JA3 and JA4 values | Did TLS sessions to FMC resemble the observed campaign fingerprints |
| Java runtime behavior | Unexpected ServletRequestListener registration | Was a memory-resident Java backdoor potentially installed |
| Network services | Unusual listener or traffic on TCP 45588 | Did post-compromise tooling create nonstandard service behavior |
| DNS and outbound traffic | Support domains and C2 domains from AWS’s IOC list | Did the appliance or adjacent hosts resolve or connect to campaign infrastructure |
| Windows post-compromise activity | PowerShell reconnaissance and staging to host-named network share paths | Did activity pivot beyond the FMC appliance into the internal environment |
| Proxy tampering | HAProxy installations with rapid log deletion | Was infrastructure used to relay or hide malicious traffic |
One further detail is worth noting for teams that already use Cisco network detection content. Cisco’s public advisory publication metadata associates Snort rule IDs 66082 and 66083 with CVE-2026-20131. That does not replace independent validation and hunting, but it gives defenders a concrete vendor-linked starting point if they are reviewing network-based detection coverage inside a Cisco-heavy environment. (Cisco)
A practical first-pass hunt
The following examples are deliberately defensive. They are meant to help teams search logs and assess exposure, not reproduce exploitation.
A quick KQL-style hunt for the AWS-published user-agent, domains, and suspicious high-port traffic can look like this:
let SuspiciousDomains = dynamic([
"cherryberry.click",
"ms-server-default.com",
"initialize-configs.com",
"ms-global.first-update-server.com",
"ms-sql-auth.com",
"kolonialeru.com",
"sclair.it.com",
"browser-updater.com",
"browser-updater.live",
"os-update-server.com",
"os-update-server.org",
"os-update-server.live",
"os-update-server.top"
]);
union isfuzzy=true
CommonSecurityLog,
DeviceNetworkEvents,
DnsEvents
| where
tostring(RequestURL) has_any (SuspiciousDomains) or
tostring(RemoteUrl) has_any (SuspiciousDomains) or
tostring(Name) has_any (SuspiciousDomains) or
tostring(UserAgent) == "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:136.0) Gecko/20100101 Firefox/136.0" or
toint(RemotePort) == 45588 or
toint(LocalPort) == 45588
| project TimeGenerated, DeviceName, SourceIP, DestinationIP, RemoteUrl, Name, UserAgent, LocalPort, RemotePort
| order by TimeGenerated desc
This query is intentionally simple. It prioritizes speed over elegance because the goal in the first pass is to answer whether any of the AWS-published infrastructure or behavioral clues appear in your environment at all. If you get hits, the next step is not to celebrate detection. The next step is to pivot into adjacent telemetry around the same FMC host or the same time window and look for evidence of follow-on behavior. AWS’s write-up makes clear that exploitation was part of a larger intrusion sequence, not an isolated HTTP event. (Amazon Web Services, Inc.)
A Splunk-style equivalent for TLS and network metadata can be kept similarly direct:
(index=proxy OR index=zeek OR index=firewall)
(
user_agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:136.0) Gecko/20100101 Firefox/136.0"
OR ja3="b885946e72ad51dca6c70abc2f773506"
OR ja3="f80d3d09f61892c5846c854dd84ac403"
OR ja4="t13i1811h1_85036bcba153_b26ce05bbdd6"
OR ja4="t13i4311h1_c7886603b240_b26ce05bbdd6"
OR dest_port=45588
OR query IN ("browser-updater.com","browser-updater.live","os-update-server.com","os-update-server.org","os-update-server.live","os-update-server.top")
)
| stats min(_time) as first_seen max(_time) as last_seen values(src_ip) values(dest_ip) values(query) values(user_agent) values(ja3) values(ja4) by host
| convert ctime(first_seen) ctime(last_seen)
Again, the value is not in magic strings alone. The value is in combining them with the system role. A generic workstation hitting one suspicious domain is interesting. An FMC management appliance doing so during the relevant time window is urgent. Context is what separates noise from signal. (Amazon Web Services, Inc.)
Version validation at scale
Large environments rarely fail because no one knew a patch existed. They fail because version reality is messy. Appliances are spread across sites, inherited from earlier projects, pinned to different release families, or tracked in inventory systems that do not encode branch-specific safe floors well enough. CVE-2026-20131 is a good candidate for a simple version-comparison script because the public branch mapping is clear and because the 7.4 and 7.6 nuances punish sloppy assumptions. (runZero)
The sample below takes a CSV export of FMC assets and flags versions that remain below the public safe floor for CVE-2026-20131. It is not vendor code. It is just a compact way to turn the public branch guidance into something teams can run against their own inventories.
import csv
from packaging.version import Version
SAFE_FLOORS = [
(Version("6.4.0.13"), Version("6.4.0.18"), Version("7.0.9")),
(Version("7.0.0"), Version("7.0.999"), Version("7.0.9")),
(Version("7.1.0"), Version("7.2.999"), Version("7.2.11")),
(Version("7.3.0"), Version("7.4.999"), Version("7.4.6")),
(Version("7.6.0"), Version("7.6.999"), Version("7.6.5")),
(Version("7.7.0"), Version("7.7.999"), Version("7.7.12")),
(Version("10.0.0"), Version("10.0.0"), Version("10.0.1")),
]
def required_floor(ver: Version):
for low, high, floor in SAFE_FLOORS:
if low <= ver <= high:
return floor
return None
with open("fmc_inventory.csv", newline="") as f:
reader = csv.DictReader(f)
for row in reader:
host = row["host"]
version_text = row["version"].strip()
try:
version = Version(version_text)
except Exception:
print(f"[WARN] {host}: cannot parse version {version_text!r}")
continue
floor = required_floor(version)
if floor is None:
print(f"[CHECK] {host}: {version} is outside the public comparison ranges, verify with Cisco Software Checker")
elif version < floor:
print(f"[VULNERABLE] {host}: {version} is below safe floor {floor}")
else:
print(f"[OK] {host}: {version} meets or exceeds safe floor {floor}")
The most important habit here is not the script itself. It is the insistence on branch-aware validation. CVE-2026-20131 is exactly the kind of issue where “we upgraded somewhere in the 7.4 family” is not a useful statement. You need the precise target. You also need to decide whether your change standard is “fix 20131 only” or “land on the minimum version that closes both 20079 and 20131 for this branch.” In most real incident-response contexts, the second standard is the sensible one. (runZero)
For teams with formal exposure management platforms, the same logic applies even if you never run a custom script. runZero published a practical query pattern to identify potentially affected FMC assets across the relevant version ranges. The value of that kind of approach is not the product-specific syntax. It is the discipline of turning public fixed-version guidance into machine-checkable state instead of relying on vague human memory. (runZero)
Patching is necessary, not sufficient
Cisco says there are no workarounds. That narrows the remediation question decisively. You need to move to a fixed version. But patching is only one of three jobs here. The other two are validating that exposure paths are actually reduced and assessing whether the system may have been touched before the patch landed. Treating patching as the entire response is the fastest way to create false closure. (Cisco)
The first post-patch question is simple and concrete: can any untrusted path still reach the management interface? NVD notes that the attack surface is reduced when the management interface lacks public internet access. That implies an action item, not just an observation. Teams should not stop at confirming the new version number. They should confirm routing, ACLs, administrative jump-path restrictions, VPN segmentation, and reverse-proxy exposure assumptions. A version change without a path review is an incomplete response to a management-plane bug. (NVD)
The second post-patch question is more uncomfortable: should this system be investigated as potentially compromised? AWS’s retrospective zero-day evidence makes that question unavoidable in some environments. If the FMC interface was internet-reachable, or reachable from a zone that should not have had management-plane access, during the window before the patch, the safe assumption is not “probably fine.” The safe assumption is that you need to look. That review should include web logs, proxy logs, outbound traffic, Java runtime anomalies, local process history where available, admin account activity, and signs of onward movement into Windows infrastructure. (Amazon Web Services, Inc.)
The third question is whether the response treated the FMC as ordinary infrastructure or tier-zero-like infrastructure. That distinction affects how seriously you take every other task. A compromised asset inventory portal is bad. A compromised firewall management plane is different. It can change policy, obscure visibility, influence trust decisions, and shape downstream incident detection. When a system occupies that role, compromise assessment should be deeper, retention of logs should be stronger, and emergency change rights should be clearer than they often are in ordinary server operations. (runZero)
What a disciplined response looks like
The response sequence for CVE-2026-20131 should be structured, not theatrical. A useful order is: inventory every FMC instance, identify branch and exact version, map every route that can reach the management plane, upgrade to the correct fixed release, validate that reachability is narrowed to intended admin paths, and then perform compromise assessment for the pre-patch window based on exposure history and the AWS hunt clues. That sequence matters because it prevents two common failures: patching before you understand the exposure surface, and closing the incident before you understand whether the surface was already used. (Amazon Web Services, Inc.)
If you rely on centralized logging, pay particular attention to data sources that are external to the FMC appliance itself. A memory-resident webshell and log-deleting proxy behavior are exactly the sort of things that can make local evidence less trustworthy or less complete. Secure, centralized, separately retained logs are not just “good hygiene” in this case. AWS’s recommendations specifically point toward comprehensive logging and centralized storage because zero-day windows punish overreliance on a single compromised host’s local view. (Amazon Web Services, Inc.)
If you find no sign of compromise, that is a useful outcome, but it still should not be the end of the lesson. CVE-2026-20131 is a management-plane design warning. It tells you to shrink who can reach these systems, tighten ownership, document version visibility, and rehearse emergency validation. The organizations that get real value from this event will be the ones that use it to improve how they treat administrative surfaces in general, not just the ones that closed one ticket quickly. (runZero)
Detection content you can carry into production
A short Sigma-style pattern for outbound IOC matching can be useful in SOC workflows that normalize DNS and proxy events into a common detection layer:
title: Possible Interlock Infrastructure Contact Related to Cisco FMC Campaign
id: 8d4c3f47-4ef3-4d8a-8b11-3c0a2c4b1f31
status: experimental
logsource:
category: network_connection
detection:
selection_domains:
destination.domain|contains:
- 'browser-updater.com'
- 'browser-updater.live'
- 'os-update-server.com'
- 'os-update-server.org'
- 'os-update-server.live'
- 'os-update-server.top'
- 'initialize-configs.com'
- 'ms-server-default.com'
selection_port:
destination.port: 45588
condition: selection_domains or selection_port
level: high
falsepositives:
- Internal sinkholes or controlled detonation environments
tags:
- attack.command_and_control
- attack.t1071
This should be treated as a triage aid, not a verdict engine. Campaign infrastructure rotates, false positives exist, and attackers do not politely keep using the same domains after public exposure. But rules like this are still worthwhile because they translate narrative threat intelligence into a reusable control that can run continuously while the human team works the harder parts of the incident. (Amazon Web Services, Inc.)
For Java-heavy environments, the harder but higher-signal detection work is around runtime behavior. AWS’s description of the ServletRequestListener registration provides a very specific clue. If you have EDR or application telemetry capable of seeing unusual class loading, reflective behavior, or registration of listeners in a context where they do not normally appear, that is better than generic malware hunting on a Linux appliance. A flaw that ends in arbitrary Java execution should be hunted partly as a JVM event, not only as a network event. (Amazon Web Services, Inc.)
For teams using Cisco network inspection content, Cisco’s publication metadata associating Snort rule IDs 66082 and 66083 with this advisory is worth checking against your deployment state. The key phrase here is “worth checking,” not “guaranteed coverage.” The most reliable approach combines vendor detection content, local hunt logic, exposure validation, and human review of the systems that were reachable during the window of concern. (Cisco)
A practical note on evidence-driven retesting
Post-patch validation is one of the places where security programs often underinvest. They install the fixed release, see the appliance come back, and move on. That is not enough for a pre-auth root-level issue with confirmed exploitation history. Validation should answer at least four questions: is the version correct, is the management path reduced, is suspicious behavior absent, and do the specific checks you expect to fail now actually fail. That last question is not about reproducing public exploitation irresponsibly. It is about controlled validation that the vulnerable condition is gone and the administrative surface behaves as intended. (Amazon Web Services, Inc.)
In that part of the workflow, AI-assisted testing platforms can be useful when they reduce verification friction without replacing operator judgment. Penligent’s public documentation says the platform can invoke tools already installed in Kali, configure AI-generated script execution paths, and integrate those steps into a task-driven workflow. Its public product materials also emphasize editable reporting, reproducible evidence, and agentic workflows under operator control. Used conservatively, that kind of tooling is most valuable here not for blind exploit attempts, but for organizing inventory checks, repeatable retest steps, evidence capture, and report-ready remediation verification across multiple appliances. (Penligente)
That is the right way to think about tooling in a case like CVE-2026-20131. The hard problem is not “can a clever tool say the CVE name back to me.” The hard problem is whether your team can move from advisory to asset list, from asset list to prioritized reachability review, from patch to validation, and from validation to evidence that leadership and auditors can understand. Any tool that helps with that chain is useful. Any tool that turns the event into a noisy checklist without improving confidence is not. (runZero)
The mistakes most likely to leave risk behind
The first common mistake is reading “not exposed to the public internet” as “low priority.” Cisco’s own note is narrower than that. It says the attack surface is reduced, not removed. If your segmentation is loose, your jump-host model is weak, or your management zone can be reached from other compromised assets, the system remains a high-value target. In real enterprise intrusions, internal reachability often matters as much as external reachability. (NVD)
The second mistake is patching one FMC CVE and forgetting the other. The shared March 2026 FMC context means version decisions should be checked against both CVE-2026-20079 and CVE-2026-20131. This is especially important on 7.4.x and 7.6.x, where the minimum fixed release for the auth-bypass issue is not the same as the minimum fixed release for the deserialization issue. “We patched the Cisco bug” is not a meaningful statement unless someone can name the branch and the destination version. (runZero)
The third mistake is assuming the absence of a dropped file means the absence of compromise. AWS’s description of a memory-resident Java backdoor is a direct warning against that assumption. If defenders only look for persistent files, they can miss the kind of in-memory foothold that a Java management application is capable of hosting. That means compromise assessment has to include runtime, connection, and behavioral evidence, not only disk artifacts. (Amazon Web Services, Inc.)
The fourth mistake is using IOC matching as a substitute for thinking. AWS explicitly notes content variation across artifacts, which reduces the reliability of file hashes as universal indicators. In practice, that means defenders should combine infrastructure indicators with timeline, host role, exposure context, application behavior, and broader intrusion evidence. Good response is a synthesis problem, not a checkbox problem. (Amazon Web Services, Inc.)
The fifth mistake is letting patching close the incident automatically. If an exposed FMC appliance was reachable during the pre-disclosure window AWS documented, leadership should at least hear the case for targeted compromise assessment. The correct question is not whether you can prove exploitation happened from one dashboard. The correct question is whether the downside of not checking is acceptable for a system that controls firewall policy and visibility. In most mature programs, it is not. (Amazon Web Services, Inc.)
What leadership should hear
Leadership does not need the full Java deserialization discussion. They need the consequence model. The clearest message is that CVE-2026-20131 is a pre-authentication root-level compromise path on the platform that centrally manages firewall controls, and that public threat intelligence later linked it to zero-day exploitation before disclosure. The practical response therefore includes patching, exposure review, and compromise assessment, not patching alone. (NVD)
They also need to understand why this event is strategically important even after the immediate emergency passes. Administrative surfaces that define policy and visibility are tier-zero-like systems whether or not the organization uses that label formally. They should have tighter routing, clearer ownership, faster version visibility, and better validation discipline than ordinary servers. CVE-2026-20131 did not invent that principle. It enforced it. (runZero)
Final assessment
CVE-2026-20131 deserves serious attention for a very specific reason. It combines the set of properties defenders least want to see together: remote reachability, no authentication requirement, no user interaction requirement, root-level code execution, no published workaround, and confirmed exploitation activity tied to a real ransomware operation. Any one of those would justify urgency. On a firewall management plane, together, they justify a much more disciplined response than “install update and close ticket.” (NVD)
The right response is not hard to state, even if it is hard to execute well. Find every FMC instance. Identify the exact branch and move it to the correct safe release. Treat CVE-2026-20079 as part of the same management-plane event. Narrow who can reach the management interface. Hunt using the AWS campaign clues. Review the pre-patch window with compromise in mind where exposure existed. Retest with evidence. Then use the incident to harden how your organization treats management surfaces going forward. The teams that do that will learn much more from CVE-2026-20131 than the teams that merely patch fastest. (Amazon Web Services, Inc.)
Leitura adicional
Cisco Security Advisory, Cisco Secure Firewall Management Center Software Remote Code Execution Vulnerability. (Cisco)
NVD entry for CVE-2026-20131. (NVD)
CISA Known Exploited Vulnerabilities entry for CVE-2026-20131, including the public due date and required action reflected in NVD. (NVD)
AWS Security Blog, Amazon threat intelligence teams identify Interlock ransomware campaign targeting enterprise firewalls. (Amazon Web Services, Inc.)
runZero, How to find Cisco Secure Firewall Management Center installations on your network. (runZero)
Arctic Wolf, CVE-2026-20079 and CVE-2026-20131, maximum-severity vulnerabilities in Cisco FMC. (Arctic Wolf)
Penligent, CVE-2026-20131 — When the firewall management plane becomes the breach point. (Penligente)
Documentação negligente. (Penligente)
Penligent homepage and product overview. (Penligente)