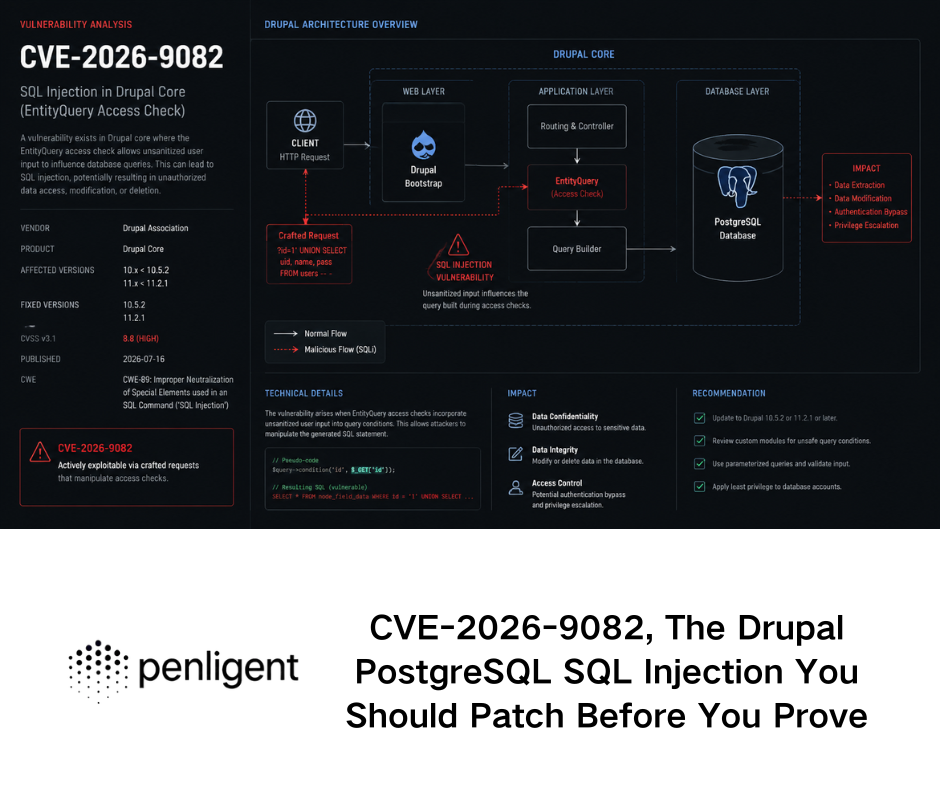
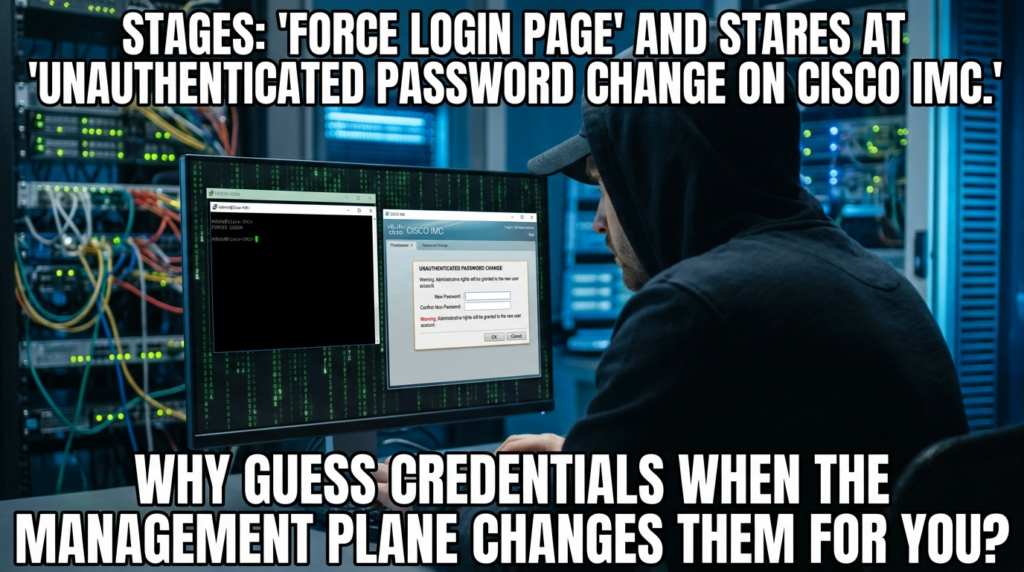
As of April 9, 2026, the publicly confirmed picture around CVE-2026-20093 is already serious enough to justify emergency treatment. Cisco disclosed the issue on April 1, 2026. NVD still marks the entry as Awaiting Analysis, but the Cisco CNA vector is already set to CVSS 3.1 9.8. Cisco’s description is direct: a flaw in the change-password functionality of Cisco Integrated Management Controller can let an unauthenticated remote attacker send a crafted HTTP request, alter the password of any user including an Admin account, and then access the system as that user. Cisco PSIRT says it is not aware of public announcements or malicious use, and GitHub’s advisory page shows no known public source code as of the current advisory state. None of that lowers the operational urgency, because this is not a routine application bug on a low-trust edge service. It is a management-plane failure on an out-of-band controller. (nvd.nist.gov)
That distinction matters more than the score alone. Cisco IMC is not just another web console bolted onto a server. Cisco describes it as the integrated management controller for UCS C-Series rack servers and S-Series storage servers, with lifecycle support, health monitoring, alerting, vKVM access, HTML5 WebUI, SSH CLI, XML API support, and Redfish REST support. In other words, IMC is a control surface for the server itself, not merely for an application running on top of the server. Cisco’s own out-of-band management guidance says management networks should be physically and logically separated, should not be accessed through public networks, and should be restricted to known internal or VPN address pools. A flaw that breaks authentication in that layer collapses assumptions that many security teams still treat as “architecture” rather than “active attack surface.” (Cisco)
A lot of the internet coverage on CVE-2026-20093 stops at the headline: critical, unauthenticated, password reset, admin access, patch now. That is all true, but it misses what makes this vulnerability materially different from the average critical CVE. The real story is about trust boundaries. The real story is about how a flaw in a password-change path on a hardware management controller can turn exposure, even partial exposure, into full administrative control over a system that often sits below or beside the host operating system’s own controls. Help Net Security’s summary makes the same point in plainer operational language: IMC is powered by a baseboard management controller and remains usable even when the operating system is not running. That is why conventional OS-level assumptions become less important once the management plane is compromised. (Ajuda à segurança da rede)
The official description is narrow, and that narrowness is useful. Cisco and NVD do not say that attackers get arbitrary code execution directly from CVE-2026-20093. They say the flaw is in the change-password functionality, that the root problem is incorrect handling of password-change requests, and that a crafted HTTP request can let an unauthenticated attacker alter the password of any account and then log in as that user. That wording is important because it tells defenders where to focus first: account control, management reachability, and post-login privilege consequences. This is not the kind of disclosure that invites guesswork about exotic exploit chains. It already tells you enough. If the management interface is reachable and the target is on a vulnerable build, a single unauthenticated interaction may be enough to cross from “outside the trust boundary” to “inside the admin plane.” (nvd.nist.gov)
CVE-2026-20093, What Is Publicly Confirmed Right Now
The first thing defenders need is a clean separation between what is public fact and what remains inference. The facts are straightforward. Cisco published the advisory on April 1, 2026. NVD mirrors the vendor description and shows the CNA vector as CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H. The weakness is mapped to CWE-20, improper input validation. Cisco’s publication metadata indicates that no workaround is published in the advisory. Cisco also credits the researcher “jyh” for reporting the issue. GitHub’s advisory page shows no known public source code and lists an EPSS of 0.028 percent at the time of retrieval, which places the vulnerability in a low percentile for short-term exploitation prediction despite its critical technical severity. (nvd.nist.gov)
That combination can confuse teams that overfit to a single metric. A 9.8 on a management-plane flaw with no authentication required should trigger immediate attention. A low EPSS does not cancel that. EPSS is useful, but it answers a different question: how likely the vulnerability is to be exploited in the next 30 days across the broader ecosystem, not how catastrophic it would be in your environment if the management path is already reachable. The vulnerability is still remotely reachable, requires no credentials, and lands on a plane that directly governs server configuration, console access, and recovery operations. On a public-facing CMS plugin, a low EPSS might justify a small delay. On a BMC-class management surface, it is a weak argument for waiting. (GitHub)
Another useful boundary: Cisco PSIRT says it is not aware of public announcements or malicious use. That is worth knowing, but it should be read carefully. It is a statement about current public visibility, not a guarantee that opportunistic scanning or private exploitation is absent. Teams often misread this kind of vendor language as “safe to schedule later.” The more accurate reading is “patch before someone else turns this into a reliable management-plane playbook.” On vulnerabilities that involve password control on an out-of-band controller, exploit maturity often matters less than basic exposure and protocol understanding. (Cisco)
Why Cisco IMC Is a Different Kind of Exposure
Cisco’s own product documentation is enough to explain why this vulnerability deserves a different mental model. IMC is designed to manage server components through multiple interfaces, including HTML5 WebUI, SSH-based CLI, XML API, and Redfish REST and XML API support. It is intentionally programmable. It is intentionally remote. It is intentionally capable of lifecycle and operational control. Those are valuable features for administrators. They are also the reason a bug in this surface should be treated as a control-plane event, not a mere account issue. If your ordinary application admin panel gets compromised, the blast radius is defined mostly by the application and its host. If your server’s dedicated management controller gets compromised, the blast radius can include console access, media workflows, reboot control, monitoring visibility, and a privileged vantage point that sits outside many host-level detection assumptions. (Cisco)
Cisco’s out-of-band best-practices document reinforces the intended security posture in unusually explicit terms. It says management traffic should not traverse the management network alongside user traffic. It says management networks should not be accessed through public networks. It recommends restricting managed devices to known internal IP or VPN address pools. It recommends strong VPN controls, MFA, auditing, a no-split-tunnel posture, and jumpservers that act as hardened intermediary hops between less-trusted networks and sensitive internal zones. Cisco even frames jumpservers as a way to prevent direct access to sensitive infrastructure while centralizing auditing and access control. That guidance is not abstract architecture advice when a flaw like CVE-2026-20093 appears. It is the shortlist of compensating controls for everyone who cannot patch immediately. (Cisco)
This also explains why “it is not internet-facing” is often an incomplete answer. Management-plane exposure rarely exists in just two states, public or private. Real environments add VPN concentrators, jump hosts, remote support links, third-party maintenance paths, internal route leaks, flat management VLANs, inherited firewall rules, forgotten NAT entries, and virtualized appliance sprawl. A Cisco IMC interface can be invisible from the open internet and still be dangerously reachable from a compromised workstation, a vendor-connected bastion, or an overbroad admin VPN pool. Cisco’s own best-practice wording around VPN groups, group-specific IP pools, route filtering, and jumpservers is valuable here precisely because it recognizes that the management network is often reachable in controlled ways that still become dangerous when trust assumptions fail. (Cisco)

What the Password-Change Flaw Appears to Break
Public documentation on Cisco IMC’s account model makes the disclosure more interesting. Cisco’s XML API documentation states that obtaining authentication tokens requires user or admin privileges, and read-only users cannot obtain those tokens. The GUI documentation describes separate roles such as read-only, user, admin, and SNMP-only. It also states something subtle but highly relevant: users with the admin role do not have the “Change Password” option in the same self-service location, while non-admin users can use a change-password flow if configured appropriately. The guide walks through the creation of a non-admin account and shows that password-change capability is meant to be a constrained action inside a pre-existing authenticated relationship. (Cisco)
That is why Cisco’s advisory wording should catch an experienced reader’s eye. When a vendor says that a flaw in “change password functionality” can let an unauthenticated attacker alter any user’s password, including an Admin user, it suggests a failure much more specific than generic login bypass. Public documents indicate that the legitimate model is role-sensitive and authenticated. The vulnerability appears to let crafted requests cross that intended boundary and act on accounts the caller should not control. That is an inference from the public material, not a statement of the full private root-cause analysis, but it is a strong and operationally useful inference. It tells defenders that the vulnerable seam is likely in a request-validation or authorization boundary around password modification, not merely in cosmetic login logic. In practice, that means a team should pay close attention to password-related request paths, account service exposure, sessionless POST activity, and any unexpected credential changes in the IMC plane. (nvd.nist.gov)
There is another practical implication. Because the effect of successful exploitation is password control rather than an immediate shell in the vendor wording, defenders have a better chance of building containment and review around identity events than they would against a pure memory-corruption RCE with no intermediate state change. Account password changes, administrative logins from new origins, and management-plane session creation are often observable somewhere, even if the environment lacks great BMC telemetry. That means the response plan for CVE-2026-20093 should not stop at “version check and upgrade.” It should also include account review, credential reset strategy, log preservation, and verification that no unauthorized changes occurred before remediation. (nvd.nist.gov)
Which Systems Are Actually Affected by CVE-2026-20093
This is where most short writeups leave defenders stranded. Cisco’s own advisory content is difficult to quote directly through every public parser, but runZero’s April 2026 operational writeup usefully summarizes the affected product families and fixed release guidance extracted from Cisco’s disclosures. For CVE-2026-20093 specifically, the affected families include 5000 Series Enterprise Network Compute Systems running affected NFVIS releases, Catalyst 8300 Series Edge uCPE on specified NFVIS branches, UCS C-Series M5 and M6 Rack Servers in standalone mode on vulnerable IMC branches, UCS E-Series M3 and M6 on affected IMC branches, and a long list of Cisco appliances built on those UCS platforms when the IMC interface is exposed. That last condition matters. The application or appliance layer is not necessarily the primary defect location. The management controller underneath is. (runZero)
The appliance list is where many teams will find their real exposure. According to runZero’s summary of Cisco’s advisory scope, platforms that can inherit this risk when their IMC user interface is exposed include APIC servers, Catalyst Center appliances, Expressway appliances, HyperFlex nodes, Nexus Dashboard appliances, Secure Endpoint Private Cloud appliances, Secure Firewall Management Center appliances, Secure Malware Analytics appliances, Secure Network Analytics appliances, Secure Workload servers, and more. That is exactly the kind of cross-product blast radius that gets missed when defenders search their fleet only for “Cisco IMC” by name. Some of the most important targets are not standalone servers in a lab. They are security or infrastructure platforms that happen to run on affected UCS hardware with exposed management controllers. (runZero)
The disclosure also makes clear that not every Cisco server-adjacent product is affected in the same way, and not every product line shares identical fixed-version logic. Some platforms require IMC firmware changes. Some NFVIS platforms require NFVIS upgrades that automatically bring along the IMC update. Some appliance families can be upgraded through Cisco Host Upgrade Utility workflows with platform-specific exceptions. The operational takeaway is simple: you cannot responsibly close this issue with a single blanket statement such as “all Cisco servers patched.” The right closure statement is per product family, per IMC branch, and per exposure condition. (runZero)
Affected Products and Fixed Releases for CVE-2026-20093
The table below consolidates the public operational guidance that is most useful during triage and patch planning. Fixed releases vary by product line, and Cisco’s publication metadata indicates that no workaround has been published, so upgrade planning should not be treated as optional. (runZero)
| Product family | Publicly summarized affected versions | Publicly summarized fixed direction |
|---|---|---|
| 5000 Series ENCS | NFVIS 4.15 and earlier | Upgrade to 4.15.5 or later |
| Catalyst 8300 Series Edge uCPE | NFVIS 4.16 and earlier, plus 4.18 | Migrate from older branches, or upgrade 4.18 to 4.18.3 or later |
| UCS C-Series M5 Rack Server | IMC 4.2 and earlier, IMC 4.3 | Migrate from old 4.2 branches, or upgrade 4.3 to 4.3(2.260007) or later |
| UCS C-Series M6 Rack Server | IMC 4.2 and earlier, IMC 4.3, IMC 6.0 | Migrate from old branches, or upgrade to 4.3(6.260017) or 6.0(2.260044) and later |
| UCS E-Series M3 | IMC 3.2 and earlier | Upgrade to 3.2.17 or later |
| UCS E-Series M6 | IMC 4.15 and earlier | Upgrade to 4.15.3 or later |
| Cisco appliances built on affected UCS platforms | Exposure depends on whether the IMC UI is exposed | Validate the underlying UCS/IMC guidance and appliance-specific upgrade path |
If a team needs one sentence to remember during incident response, it is this: the patch path is product-specific, but the risk question is not. The first question is whether the IMC surface is reachable from any path an adversary could use. The second question is whether the platform is running a vulnerable branch. The third question is whether sibling IMC vulnerabilities were closed at the same time. Those questions matter more than whether the asset is labeled as a “server” or an “appliance” in your inventory. (runZero)
Why the CVSS 9.8 Score Is Justified
Some critical scores are mostly a theoretical outcome of generous worst-case assumptions. This one is not. Cisco’s CNA vector assigns network reachability, low complexity, no privileges required, no user interaction, unchanged scope, and high impact across confidentiality, integrity, and availability. That is a classic pre-auth management-plane profile. Even if an attacker gains “only” account-level control in the first documented step, the system they control is the out-of-band interface for the server. That translates quickly into operational dominance, not just account misuse. Help Net Security captured the logic well when it highlighted that IMC sits below the operating system layer and maintains persistent out-of-band access, which can render many traditional OS-side controls less meaningful after compromise. (GitHub)
The bigger lesson is that management-plane bugs distort normal vulnerability prioritization logic. Engineers are used to mapping flaws onto business apps, internal admin pages, or internet edge services. A BMC or management controller falls into a different category because it governs recovery, provisioning, hardware state, virtual media, and remote console functions. If an attacker can control passwords in that plane, they are not merely impersonating an operator inside a narrow web workflow. They are taking over the interface designed to supervise the machine itself. That is why BMC-style vulnerabilities remain disproportionately dangerous even when the public exploit ecosystem has not yet caught up. (Cisco)
What Changes If the IMC Interface Is Internet Reachable
If the vulnerable IMC interface is directly internet accessible, the response should be immediate and blunt. Exposure is the hardest part of exploitation for many real attackers. Cisco has already told you that no authentication is required and that a crafted HTTP request is enough. In a directly reachable scenario, there is no defensible argument for leaving the service exposed while waiting for a normal patch window. The right move is to remove public reachability first and then finish patching. That can mean ACL changes, VPN-only access, management network isolation, route removal, firewall blocks, or jumpserver-only access depending on your architecture. Cisco’s out-of-band guidance explicitly says management networks should not be accessed through public networks and should be restricted to known internal or VPN pools. (nvd.nist.gov)
If the interface is not directly internet accessible but is reachable through broad admin VPNs, vendor support paths, or flat internal routing, the urgency is still high but the work looks different. In those cases, the security team should assume that the real risk is not anonymous scanning from the public internet but authenticated or semi-trusted path abuse after an initial foothold. That is why Cisco’s jumpserver guidance matters. A hardened jumpserver with MFA, logging, limited access groups, and route segmentation does more than satisfy a best-practice checklist. It reduces the number of places from which a flaw like CVE-2026-20093 can be exercised at all. In practical terms, every overbroad route, every shared VPN pool, and every unmanaged third-party maintenance path increases the number of attackers who can turn an internal compromise into an IMC compromise. (Cisco)
Safe Ways to Find Potentially Affected Systems
The safest first step is asset discovery, not vulnerability reproduction. runZero’s April 2026 response note provides a concise query for locating Cisco Integrated Management Controller assets in its software inventory: vendor:=Cisco AND product:="Integrated Management Controller". That is a practical starting point because it focuses the hunt on management-plane assets without requiring active exploit attempts. In organizations with good CMDB hygiene, the same logic should be replicated in asset tags, rack inventory, virtualization catalogs, and appliance ownership records. The goal is to build the denominator before you try to prove exploitability. (runZero)
For teams using network-based confirmation under explicit authorization, the next safest layer is exposure-oriented probing. You do not need a password-reset exploit to confirm that a service is an IMC-like management interface or that it exposes Redfish. Cisco’s product documentation confirms that IMC supports HTML5 WebUI, XML API, and Redfish REST. That means basic fingerprinting can focus on passive or low-impact HTTP behavior, service banners, TLS metadata, and the presence of a Redfish root object. (Cisco)
A safe reconnaissance pattern can look like this:
# Confirm that the management HTTPS service is reachable
nmap -Pn -p 443 --script http-title,http-headers,ssl-cert <target-ip>
# Check for a Redfish root object without attempting authentication bypass
curl -sk https://<target-ip>/redfish/v1/ | jq .
# Capture headers only for a change-management record
curl -skI https://<target-ip>/
This does not prove vulnerability. It proves something more immediately useful for triage: that the service is reachable, that it looks like a management surface, and that it exposes an API family consistent with IMC behavior. The next step is version validation, ownership identification, and branch-specific patch mapping rather than exploit development. (Cisco)
If you are trying to answer the more important question, “Can an attacker reach this thing from a path that matters,” then network architecture review is usually more valuable than service fingerprinting. Pull route tables. Pull firewall rules. Pull VPN group mappings and IP pools. Pull jumpserver allowlists. Cisco’s out-of-band guidance recommends distinct VPN groups, distinct VPN IP pools, route filtering, no-split-tunnel policies, and known-source restrictions for management devices. Those recommendations can be turned into concrete validation questions: Which source networks can reach the IMC VLAN today? Which VPN groups can traverse to it? Are there any vendor-maintenance exceptions? Is there any direct NAT or hairpin path? Which logging points would see a request to the management interface from an unexpected segment? (Cisco)
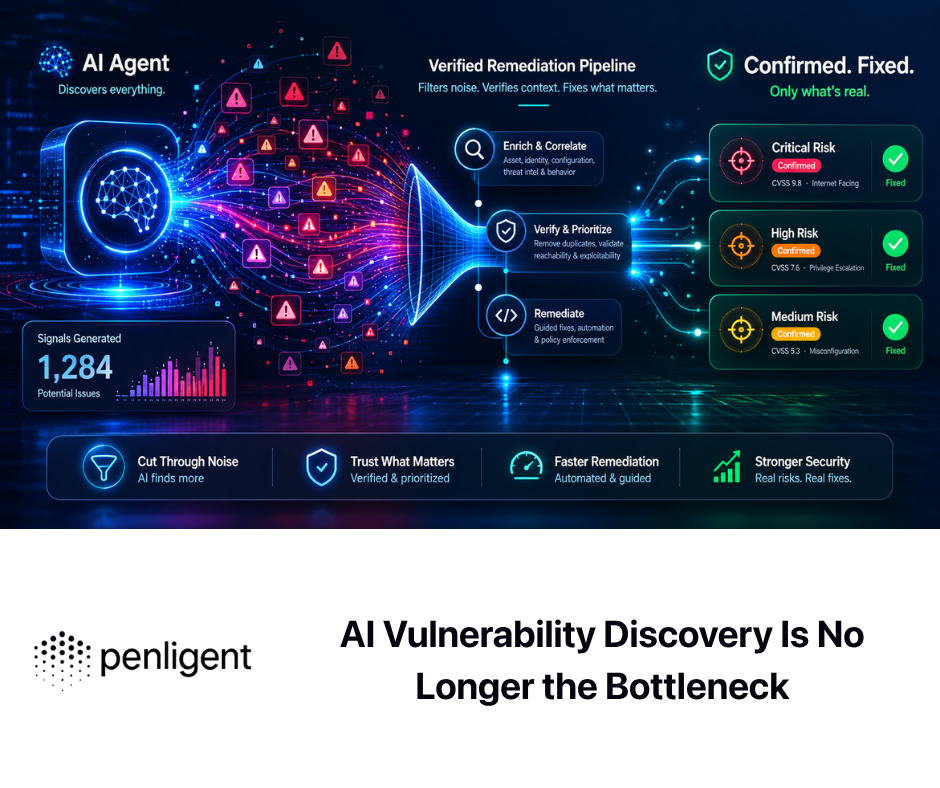
In environments where patch owners want proof before committing downtime, teams often need a workflow that turns “high-severity vendor advisory” into “evidence-backed internal action.” That is where platforms centered on scoped validation and retest workflows become useful. Penligent’s public material on continuous penetration testing and AI pentest reporting frames the problem correctly: evidence needs to include discovery context, exploit or negative-test artifacts, version and environment details, and retest proof after remediation. Used that way, a tool like Penligent is not replacing Cisco guidance or inventing exploit details. It is helping a security team turn a management-plane advisory into a repeatable validation and evidence pipeline. (penligent.ai)
What Not to Do During Validation
A common mistake in critical-CVE response is to treat every urgent advisory like a request to produce a full exploit replay in production. Public sources do not disclose the exact request structure for CVE-2026-20093, and GitHub’s advisory page currently shows no known source code. That should restrain behavior, not frustrate it. For an internal, authorized response, the most valuable work is to determine whether the vulnerable surface is reachable, whether the asset is on an affected branch, whether account events changed unexpectedly, and whether the fixed release or containment has eliminated the path. You do not need to publish or operationalize a password-reset exploit to reduce risk responsibly. (GitHub)
Another mistake is to assume that vulnerability scanning alone is enough. A scanner might tell you that a Cisco appliance is present, or that a particular IMC branch appears in a banner, or that a management interface exists. It might not tell you whether the interface is accessible from an overbroad VPN pool, whether a third-party support network can route to it, or whether an appliance team quietly enabled the IMC UI on a platform that operations thought was closed. CVE-2026-20093 is a good example of why management-plane response has to combine asset discovery, network-path validation, account review, and patch mapping. A pure version-centric response misses too much. (runZero)

Detection and Monitoring for CVE-2026-20093
Because Cisco has not publicly documented a weaponized request pattern, defenders should resist the temptation to write pretend IOCs. The highest-value detections right now are architectural and behavioral. Start with any network connection to IMC from source networks that should never reach it. Then look for management-plane HTTPS activity from unusual VPN ranges, remote-access zones, vendor subnets, or workstation segments. If your environment proxies or logs management access, pay attention to unexpected POST activity, especially around account, password, session, or user-management paths. If your Cisco logging is limited, firewall and NetFlow telemetry may still be enough to tell you that the wrong systems are talking to the management controller. (Cisco)
A representative KQL-style pattern for network or proxy logs could look like this:
CommonSecurityLog
| where DeviceAction in ("allow", "Allow")
| where DestinationIP in (externaldata(ip:string)
[@"https://internal.example.com/imc_inventory.csv"] with (format="csv"))
| where RequestMethod == "POST" or DestinationPort == 443
| where SourceIP !in ("10.10.10.0/24", "10.20.30.0/24") // approved admin ranges
| summarize count(), FirstSeen=min(TimeGenerated), LastSeen=max(TimeGenerated)
by SourceIP, DestinationIP, RequestMethod, RequestURL, DeviceVendor, DeviceProduct
| order by count_ desc
This is a representative pattern, not a drop-in rule. The point is to express the core logic: identify access to known IMC assets from non-approved sources, especially state-changing web requests. Teams with richer telemetry can narrow this further around user-management URLs or correlate with identity events. Teams with poorer telemetry can still get value from source-range violations alone. (Cisco)
A Splunk-flavored example for firewall or reverse-proxy logs follows the same principle:
index=netfw OR index=proxy
dest_ip IN ([| inputlookup imc_inventory.csv | fields ip])
(dest_port=443 OR http_method=POST)
NOT src_ip IN ("10.10.10.0/24","10.20.30.0/24")
| stats earliest(_time) as first_seen latest(_time) as last_seen count by src_ip, dest_ip, http_method, uri_path, action
| convert ctime(first_seen) ctime(last_seen)
| sort - count
Again, the point is not a magic signature. The point is enforcement of the management trust boundary. Cisco’s own guidance says management devices should be restricted to known internal or VPN sources and that jumpservers should centralize access and auditing. Any access pattern that violates those assumptions deserves immediate review whether or not you have a perfect CVE-specific signature. (Cisco)
You should also treat account-state review as part of detection. Cisco’s public description explicitly states that successful exploitation can alter the passwords of any user, including Admin. That means an incident review should include recent password changes, unexpected admin logins, new login origins, and any unexplained shifts in who accessed the IMC interface around the disclosure window or before patching. In some environments, that evidence will be stronger than web-request artifacts. (nvd.nist.gov)
Patch Strategy for CVE-2026-20093
Cisco’s advisory metadata indicates there is no published workaround. That is the cleanest statement you will get from the vendor. The fix is to move to an unaffected release. The practical problem is that the path differs by platform family. Some systems need a direct IMC upgrade. Some NFVIS-based platforms need an NFVIS upgrade that automatically updates IMC. Some appliances require appliance-specific firmware or utility workflows. So the right patch plan has three tracks running in parallel: remove unnecessary reachability now, map every asset to its correct fixed release path, and verify after the upgrade that the vulnerable path is actually gone. (Cisco)
In the first 24 hours, most teams should focus less on perfection and more on blast-radius reduction. If public reachability exists, remove it. If broad internal reachability exists, constrain it to approved admin sources. If remote access exists, require it to traverse a hardened jumpserver or tightly controlled VPN group. If third parties have maintenance access, review whether their path still exists and whether it still needs to. Cisco’s out-of-band guidance strongly supports these moves: no public management access, dedicated VPN controls, MFA, role-based groups, route restrictions, and known-source limitations. These are not substitutes for upgrading, but they are the right way to buy time safely. (Cisco)
After containment, move to branch-accurate remediation. The public runZero summary of Cisco guidance is useful here because it turns advisory scope into concrete version targets. ENCS on NFVIS 4.15 and earlier should move to 4.15.5 or later. Catalyst 8300 Edge uCPE on NFVIS 4.18 should move to 4.18.3 or later. UCS C-Series M5 and M6 have distinct 4.3 and 6.0 fixed builds depending on model. UCS E-Series M3 and M6 have their own fixed IMC milestones. Teams should document these per asset rather than per program. A single spreadsheet line that says “Cisco upgraded” is not credible evidence for this vulnerability. (runZero)
What Good Remediation Evidence Looks Like
A surprising number of emergency patch projects end with weak proof. “We upgraded it” is not enough, especially for a vulnerability that affects a management controller and may also touch appliances that security teams do not own directly. High-quality closure evidence should include the pre-fix version or branch, the post-fix version or branch, confirmation that the management path is only reachable from approved sources, a negative validation from a non-approved source, and a record of any suspicious account changes reviewed during the response window. If the system was public before remediation, evidence should show exactly when and how public reachability was removed. If the system was reachable only through VPN or jump hosts, evidence should show the source restrictions and group mappings now in force. (runZero)
This is also where evidence-centric security workflows matter more than flashy automation. Penligent’s public writing on AI pentest reporting makes an important point: a trustworthy deliverable is not just a narrative, it is an evidence chain that includes environment details, artifacts, negative tests after the fix, and retest proof. For CVE-2026-20093, that philosophy is exactly right. The best closure package is one that another engineer can replay and verify later, not a ticket with a pasted advisory link and a generic comment saying “done.” (penligent.ai)
A minimum practical verification bundle for each remediated asset should include something like this:
# Capture current exposure from an approved admin segment
curl -skI https://<imc-host>/ | tee headers_after_fix.txt
curl -sk https://<imc-host>/redfish/v1/ | jq . > redfish_root_after_fix.json
# Record the host in an inventory artifact
echo "<asset-id>,<owner>,<product-family>,<fixed-version>,<date>" >> imc_remediation_log.csv
This is not meant to replace vendor-specific version validation. It is meant to preserve enough state to prove that the asset was reviewed, remained reachable only from intended paths, and was captured in an auditable remediation chain. Combined with upgrade records and access-control evidence, that is the difference between “patch theater” and usable assurance. (Cisco)
Why CVE-2026-20093 Should Be Triaged Alongside CVE-2026-20094 to CVE-2026-20097
Cisco did not disclose CVE-2026-20093 in a vacuum. Public coverage of the same IMC disclosure cluster shows that Cisco also addressed multiple vulnerabilities in the IMC web-based management interface: CVE-2026-20094 can let a remote low-privileged attacker perform command injection and execute arbitrary commands as root, CVE-2026-20095 and CVE-2026-20096 can let high-privileged attackers perform command injection as root, and CVE-2026-20097 can let a high-privileged attacker execute arbitrary code as root. Nine of the ten disclosed IMC vulnerabilities in that update cycle affected the web-based management interface. (runZero)
Operationally, that means CVE-2026-20093 is best understood as part of a management-plane emergency, not as a standalone credential bug. Even if Cisco does not publish a canonical chain, defenders should think in chain terms. If one flaw gives an attacker account control on the management plane and sibling flaws turn low or high privilege into root on the underlying operating system, then leaving the sibling set partially unpatched is a bad gamble. That is an inference about operator behavior, not a claim that Cisco published a weaponized multi-step exploit. But it is exactly the kind of inference incident responders should make. Real attackers do not care which CVE number got them through the first door as long as the next door is still open. (runZero)
This also changes ownership conversations. A lot of enterprises split responsibilities between server teams, virtualization teams, appliance teams, security operations, network operations, and product owners. If CVE-2026-20093 lands with one owner and CVE-2026-20095 lands with another, the organization can accidentally create a paper-closed environment that remains practically exposed. The right governance move is to ticket the whole IMC bundle as one response stream per affected asset family. The question is not “which CVE does this team own.” The question is “is this management surface still vulnerable in any way that matters.” (runZero)
What Older BMC Vulnerabilities Teach About This Class of Failure
Cisco is not unique in having dangerous vulnerabilities on a baseboard or out-of-band management surface. That is exactly why CVE-2026-20093 should be treated as part of a broader management-plane pattern. In March 2025, NVD published CVE-2024-54085 affecting AMI’s SPx BMC, describing a remote authentication bypass through the Redfish Host Interface that could lead to loss of confidentiality, integrity, and availability. In July 2023, the CVE record for CVE-2023-34329 described an authentication bypass in AMI MegaRAC SPx12 that could be triggered by spoofing an HTTP header. These are not Cisco IMC bugs, and they do not imply code or exploit-path equivalence. But they do underline the same architectural lesson: management controllers keep appearing as high-value remote control points, and authentication failures on them are rarely “just another web issue.” (nvd.nist.gov)
That historical context matters because it corrects a damaging instinct in many organizations. Teams often assume that if a surface is “for administrators,” it must already be safe enough as long as it is not on a public DNS name. The BMC vulnerability record says otherwise. These interfaces are privileged, API-capable, increasingly standardized, and sometimes poorly segmented in real deployments. A vulnerability like CVE-2026-20093 is not unusual because attackers care about Cisco specifically. It is dangerous because adversaries keep looking for the fastest path to the control plane, and BMC-like systems often are the control plane. (nvd.nist.gov)
The Immediate Action Sequence That Makes Sense
For most environments, a good response order is simple. First, identify whether you have any affected IMC assets or appliances built on affected UCS platforms. Second, determine whether the IMC interface is reachable from public space, broad internal ranges, admin VPN pools, or vendor-maintenance paths. Third, apply containment to remove unnecessary reachability. Fourth, map each asset to the correct fixed release and perform the upgrade. Fifth, review account and access evidence around the remediation window. Sixth, verify the result with negative tests and path validation. Seventh, close sibling IMC CVEs at the same time rather than treating them as separate patch trivia. (runZero)
The reason this sequence works is that it matches the architecture of the risk. CVE-2026-20093 is a reachability problem, an authentication problem, an identity-control problem, and a management-plane problem all at once. If you begin with exploit fascination, you will waste time. If you begin with reachability, asset scope, and fixed-version mapping, you will reduce real exposure fast. That is the right mindset for this class of flaw. (nvd.nist.gov)
The Real Takeaway from CVE-2026-20093
The easiest way to misunderstand CVE-2026-20093 is to file it mentally under “critical Cisco bug, patch soon.” The more accurate reading is harsher: a password-change defect on an out-of-band management controller can convert a reachable administrative surface into a full account-takeover point on the server control plane. Public exploit code is not required for that conclusion. Public confirmation is enough. Cisco says the flaw is unauthenticated and remote. Cisco says it can change any user’s password, including Admin. Cisco says there is no workaround. Cisco’s own product documentation says IMC is a programmable hardware management surface with WebUI, CLI, XML API, and Redfish support. Cisco’s own architecture guidance says that management networks should be tightly isolated and restricted. Put those statements together and the operational meaning is obvious. (nvd.nist.gov)
As of April 9, 2026, Cisco says it is not aware of public malicious use, and public advisory ecosystems do not show known public source code. That is useful context, but it should not soften the response. A management-plane flaw of this kind is an exposure emergency first and an exploit-lab curiosity second. If the interface is reachable, fix the architecture. If the asset is vulnerable, upgrade it. If the account state is uncertain, review it. If sibling IMC vulnerabilities are still open, close them too. That is the only reading of CVE-2026-20093 that matches the system it affects. (Cisco)
Further Reading
For the primary vendor and reference records, start with Cisco’s security advisory for CVE-2026-20093, the NVD entry, and GitHub’s advisory record, which currently shows the CNA vector, the “Awaiting Analysis” NVD status, and the absence of known public source code. (Cisco)
For operational scoping and fixed-release planning across affected product families and Cisco appliances built on UCS hardware, runZero’s April 2026 writeup is one of the most useful public summaries. For additional management-plane context, Help Net Security’s coverage is useful because it frames IMC correctly as a BMC-backed surface rather than a routine web admin page. Cisco’s IMC product page and out-of-band best-practices guidance are also worth reading directly. (runZero)
For readers building internal validation, remediation, and retest workflows around disclosures like this one, the most relevant Penligent pages I found are How to Get an AI Pentest Report, Project Glasswing Shows Why AI Defense Needs Continuous Penetration Testinge Vulnerability Management Tools, A Complete 2026 Guide. Those pages are useful not because they replace vendor advisories, but because they focus on evidence-backed validation, retest discipline, and continuous verification after exposure changes or patching. (penligent.ai)