If you’ve worked in security for more than a week, you’ve seen it: a vulnerability is announced, a patch drops, scanners light up, and suddenly every conversation becomes a string of IDs—CVE-2024-3094, CVE-2021-44228, CVE-2025-53770. Those IDs show up in vendor advisories, bug trackers, SIEM alerts, vulnerability scanners, and executive dashboards.
That’s not an accident. The entire industry needed a shared vocabulary long before it had shared tooling.
CVE—Common Vulnerabilities and Exposures—exists to give the world one common name for one publicly known vulnerability so different databases and tools can “speak the same language,” improving interoperability and reducing gaps created by inconsistent naming.
But here’s the part that trips people up (and causes bad prioritization): a CVE is not a severity score, not proof of exploitation, and not a fix. It’s an identifier and a record anchor that lets you reliably connect the rest of the ecosystem—NVD enrichment, CVSS scoring, exploit intelligence, vendor patches, detections, and your own asset reality.
This article answers the search intent behind “cve meaning in cyber security” from the perspective of someone who has to operationalize it: not just define CVE, but make it usable in triage, remediation, and verification.
What CVE means in cyber security
CVE stands for Common Vulnerabilities and Exposures. In practice, when people say “a CVE,” they usually mean a specific publicly disclosed security flaw that has been assigned a CVE ID. (Kırmızı Şapka)
A useful mental model:
- CVE is a standardized label for a vulnerability record—an industry-wide reference handle.
- It allows correlation across vendor advisories, patch notes, scanners, threat intel, and vulnerability management systems.
- The CVE record itself typically contains a brief description and references; deeper structured metadata often lives in NVD. (NVD)
MITRE’s CVE materials describe CVE as “a dictionary of common names” and emphasize that CVE identifiers enable data exchange and tool interoperability.
What a CVE is not
Security teams waste time when they treat CVE as more (or less) than it is. Three common misconceptions:
A CVE is not a severity score
Severity scoring is typically communicated using CVSS (Common Vulnerability Scoring System), which is an open framework managed by FIRST for describing vulnerability severity using defined metric groups. (first.org)
CVE = identifier/record.
CVSS = scoring methodology.
A CVE is not proof of exploitation
A CVE may be theoretical, hard to exploit, or unexploited in the wild. If you need a more authoritative signal for active exploitation, organizations often look to sources like CISA'nın Bilinen Açıklar (KEV) Kataloğu, which is explicitly about vulnerabilities exploited in the wild. (CISA)
A CVE is not a patch
A CVE can exist with no patch (yet), or with multiple remediation paths (patch, configuration change, feature disablement, compensating control). NVD’s definition of a vulnerability emphasizes weakness and negative impact, and mitigation can involve code changes but may also involve changes to specs or functionality. (NVD)
What a CVE ID looks like, and what the year really means
Most CVE IDs look like:
CVE-YYYY-NNNN...
CVE.org documents the identifier format and notes the sequence portion can be four or more digits. (CVE)
The most misunderstood part is the year. The year in a CVE ID is not the discovery date. Archived CVE FAQs explain the YYYY portion is the year the ID was assigned veya the year the vulnerability was made public (if public before assignment). (CVE)
That matters because:
- You can discover a bug in 2022, embargo it, and the CVE may be assigned/published in 2024.
- The year won’t reliably tell you how long attackers have known—only when it entered the public CVE ecosystem.
RESERVED and REJECTED—why some CVEs look “empty” or disappear
In real programs, you’ll see CVE records marked as RESERVED. That usually means the ID exists, but details are not yet populated—often because the requester or CNA hasn’t provided publication details. (CVE)
You’ll also see REJECTED CVEs. NVD explains that CVE IDs may be denied and tagged REJECTED for reasons like lack of qualifying factors or irregularities in reporting. (NVD)
Operasyonel olarak:
- RESERVED → treat as “pending record”; track it if it’s relevant to your assets, but expect details to change.
- REJECTED → treat as invalid; remove from tickets/dashboards once confirmed REJECTED.

Who assigns CVEs—CNA, MITRE, and the program’s workflow
CVE assignment is not “the internet.” It’s a structured program with CVE Numbering Authorities (CNAs) that can allocate IDs for products within their scope, governed by operational rules. (CVE)
MITRE’s CVE materials describe a flow where a potential vulnerability is discovered and reported, then a CNA assigns a CVE Identifier, and the record is posted as part of CVE’s management process.
Kısacası:
- A vulnerability is found and validated.
- A CNA (often the vendor or a delegated authority) reserves/assigns a CVE ID.
- The vulnerability is disclosed publicly; details and references become available.
- Downstream systems (especially NVD) enrich the record with structured data.
CVE vs NVD—why you often look up CVEs on NVD
A common workflow is: “Find the CVE on NVD.” That’s because NVD is the U.S. government repository for standards-based vulnerability management data, represented using SCAP, and it provides automation-friendly data. (NVD)
NVD also exposes APIs and data feeds used by many tools to pull CVE details at scale. Its developer documentation describes the CVE API and pagination model for retrieving records. (NVD)
Think of it like this:
- CVE program: ensures a unique ID and a baseline record that the ecosystem can reference.
- NVD: enriches vulnerabilities with structured metadata used for automation—product matching, metrics, and machine-readable feeds.
This distinction matters when someone asks, “Why does NVD show more than the CVE page?” Because they’re not the same thing; they’re linked systems with different purposes. (NVD)
CVE vs CVSS—how severity is calculated, and why it still isn’t your priority order
CVSS is designed to communicate vulnerability severity using standardized metrics. FIRST describes CVSS as an open framework with metric groups (including Base, Threat, Environmental, and Supplemental). (first.org)
NVD hosts CVSS-related guidance and points to FIRST as the owner/manager of CVSS specifications. (NVD)
The key operational point: CVSS is a severity model, not a business priority model. A “9.8 Critical” on an unreachable internal service may be less urgent than a “7.5 High” on an internet-facing system with known exploitation.
A realistic priority decision usually needs at least:
- Asset criticality (what breaks if compromised)
- Maruz kalma (internet-facing, partner-facing, internal-only)
- Reachability (is the vulnerable code path actually callable in your config)
- Exploitability and active exploitation signals (KEV, vendor notes, threat intel)
- Compensating controls (WAF rules, segmentation, EDR protections)
- Fix complexity (downtime, regression risk, dependency constraints)
CVE vs CWE—instance vs weakness category
Engineers often ask: “Is CWE the same as CVE?” No.
- CVE: a specific vulnerability instance in a specific product/version.
- CWE: a category of weakness (a pattern), useful for secure development and systemic remediation.
They complement each other: CVEs tell you what to patch today; CWEs tell you what to stop shipping forever.
CISA KEV—when “public” becomes “actively exploited”
CISA’s Bilinen Açıklar (KEV) Kataloğu is widely used as an authoritative indicator that a vulnerability is exploited in the wild, and CISA recommends organizations use it as input to vulnerability management prioritization. (CISA)
NVD added labeling on CVE detail pages to identify vulnerabilities appearing in CISA’s KEV catalog, making it easier to integrate that signal into automated workflows. (NVD)
Practical impact:
- If a CVE is in KEV, your default posture should shift from “schedule” to “expedite,” unless you can prove non-applicability (not installed, not reachable, mitigated).
- KEV is not perfect coverage of all exploitation, but it’s a high-confidence “this is real” signal.
High-impact CVE examples, and what they teach
You asked for influential and recent CVEs. The point here isn’t to relitigate every technical detail, but to show why CVE tracking became operationally necessary.
Heartbleed, CVE-2014-0160 — when ubiquitous crypto libraries leak secrets
Heartbleed became a household security term because it affected OpenSSL’s heartbeat extension and allowed memory disclosure, potentially exposing keys and sensitive data at scale. The lesson: vulnerability impact can be catastrophic even without a complicated exploit chain when the component is ubiquitous.
Shellshock, CVE-2014-6271 — when “environment variables” become code execution
Shellshock highlighted how seemingly mundane parsing behavior can yield remote code execution in real deployments (CGI, embedded systems). Lesson: legacy behavior + widespread deployment equals internet-scale incident.
EternalBlue, CVE-2017-0144 — exploitation at worm speed
EternalBlue’s SMB exploitation helped enable outbreaks like WannaCry and NotPetya. Lesson: when exploit reliability is high and scanning is cheap, patch windows collapse.
Log4Shell, CVE-2021-44228 — dependency graphs as blast radius multipliers
Log4Shell taught every organization that your risk is not just your code; it’s your transitive dependencies. Identifying nerede a vulnerable library exists in your fleet becomes as critical as patching.
MOVEit Transfer, CVE-2023-34362 — supply-chain style impact through managed file transfer
MOVEit exploitation reminded teams that “secure niche enterprise software” is still software, and attackers love centralized data-transfer points.
XZ backdoor, CVE-2024-3094 — when the build pipeline becomes the battleground
XZ highlighted the uncomfortable truth: sometimes the vulnerability story is actually an integrity story—maintainer access, release engineering, and trust boundaries.
SharePoint “ToolShell”, CVE-2025-53770 — active exploitation and hard operational guidance
In mid-2025, Microsoft published customer guidance for CVE-2025-53770, describing active attacks targeting on-prem SharePoint Server customers and recommending immediate updates and additional mitigations like enabling AMSI and rotating ASP.NET machine keys. (Microsoft)
CISA also released updates around exploitation of SharePoint vulnerabilities, describing CVE-2025-53770 as a patch bypass for an earlier issue and providing remediation guidance. (CISA)
Threat research organizations documented active exploitation and the relationship to earlier CVEs in the chain. (Birim 42)
The lesson: the “meaning” of a CVE in the real world is often a coordination primitive—it ties together vendor fixes, mitigations, detection engineering, and incident response steps.
The operational meaning of CVE—turning IDs into decisions
If you run a security program, the real question is never “What does CVE stand for?” It’s:
“What does this CVE mean for my environment, and what do we do next?”
A strong CVE workflow usually answers five questions, in this order:
- Do we have it?
- Is the product/library present anywhere (including transitive dependencies)?
- Can it be reached?
- Is the vulnerable code path reachable given configuration, network exposure, auth, and deployment topology?
- How bad is it if exploited?
- CIA impact in your context, not in abstract.
- How likely is exploitation now?
- KEV status, vendor “active exploitation” notes, public PoCs, scanning activity.
- What’s the fastest safe mitigation?
- Patch if possible; otherwise compensating controls with verification evidence.
NVD’s role here is to provide a standardized dataset that feeds automation. (NVD)
CISA KEV’s role is to provide a high-signal exploitation indicator. (CISA)
CVSS’s role is to communicate severity characteristics consistently. (first.org)
A practical CVE triage table you can actually use
Below is a compact schema that many teams implement (in ticketing systems, spreadsheets, or internal dashboards). It deliberately separates “severity” from “priority”:
| Saha | Örnek | Neden önemli |
|---|---|---|
| CVE KIMLIĞI | CVE-2025-53770 | Stable cross-tool anchor |
| Title | SharePoint RCE chain variant | Human readability |
| Source of truth | Vendor advisory, NVD, CISA KEV | Conflicting info happens |
| CVSS Base | 9.8 | Severity characteristic signal, not priority |
| Exploited in the wild | Yes, KEV or vendor states active exploitation | Determines urgency posture |
| Asset presence | 37 servers | Scope of remediation |
| Maruz kalma | Internet-facing / internal | Attack surface |
| Reachability | Proven reachable / uncertain / not reachable | Avoid wasted patching |
| Hafifletme | Patch + AMSI + rotate keys | Concrete actions |
| Verification evidence | Version check, exploit test, WAF logs, EDR detections | Close the loop |
| Deadline policy | 48 hours if KEV and internet-facing | Enforceable execution |
Pull CVE data programmatically with NVD APIs
NVD provides vulnerability APIs for retrieving CVE information at scale. (NVD)
Example 1 — retrieve one CVE from NVD (conceptual)
# Note: NVD rate limits apply and may require an API key depending on usage.
# See NVD developer docs for current requirements.
curl -s "<https://services.nvd.nist.gov/rest/json/cves/2.0?cveId=CVE-2025-53770>" | jq .
Example 2 — parse key fields in Python
import requests
def fetch_cve(cve_id: str) -> dict:
url = "<https://services.nvd.nist.gov/rest/json/cves/2.0>"
r = requests.get(url, params={"cveId": cve_id}, timeout=30)
r.raise_for_status()
return r.json()
def summarize(nvd_json: dict) -> dict:
vuln = nvd_json["vulnerabilities"][0]["cve"]
cve_id = vuln["id"]
desc = vuln["descriptions"][0]["value"]
refs = [x["url"] for x in vuln.get("references", [])][:5]
return {"cve": cve_id, "description": desc, "top_refs": refs}
data = fetch_cve("CVE-2025-53770")
print(summarize(data))
This pattern—pull, normalize, enrich, then join with your asset inventory—is the backbone of modern vulnerability management automation.
How to interpret “vendor guidance” vs “community writeups” for the same CVE
A practical hierarchy many teams adopt:
- Vendor advisory / official guidance — patch availability, mitigations, detection notes Example: Microsoft guidance for CVE-2025-53770 includes specific mitigation steps (updates, AMSI, machine key rotation). (Microsoft)
- Government/authority catalogs — exploitation confirmation and mandated timelines in some contexts Example: CISA alerts around SharePoint exploitation and patch bypass relationships. (CISA)
- High-quality threat research — exploitation chains, IOCs, tradecraft, detection logic Example: Unit 42 writeup on SharePoint exploitation and CVE relationships. (Birim 42)
- General explainers — good for onboarding, not for decisions Example: definitions and high-level explanations from IBM/Red Hat. (Kırmızı Şapka)
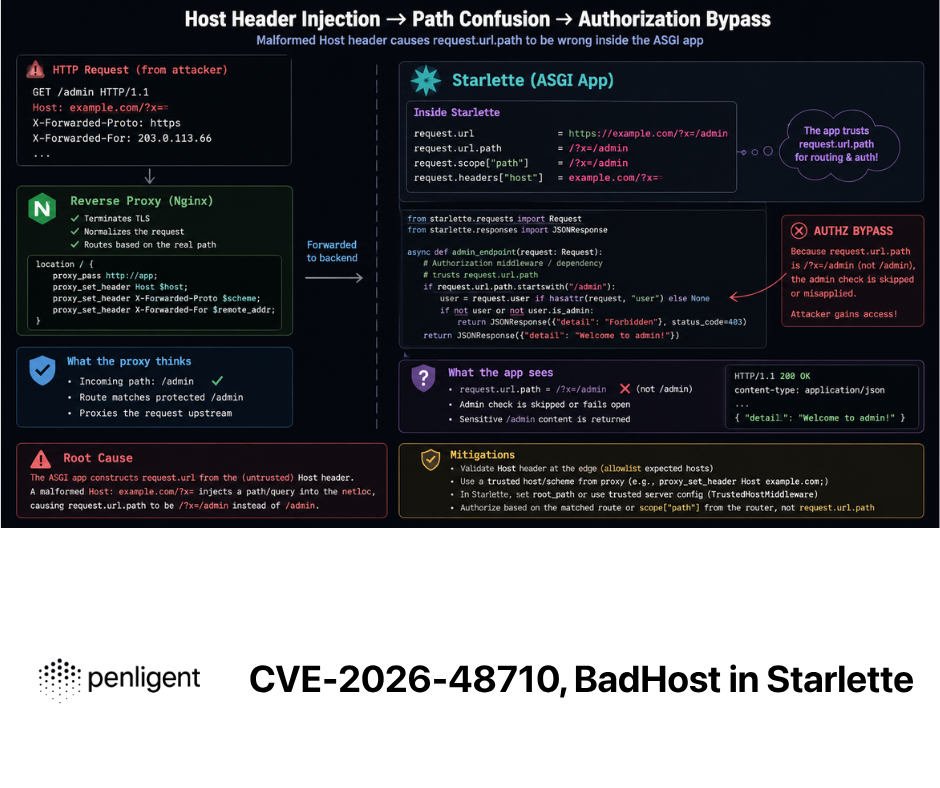
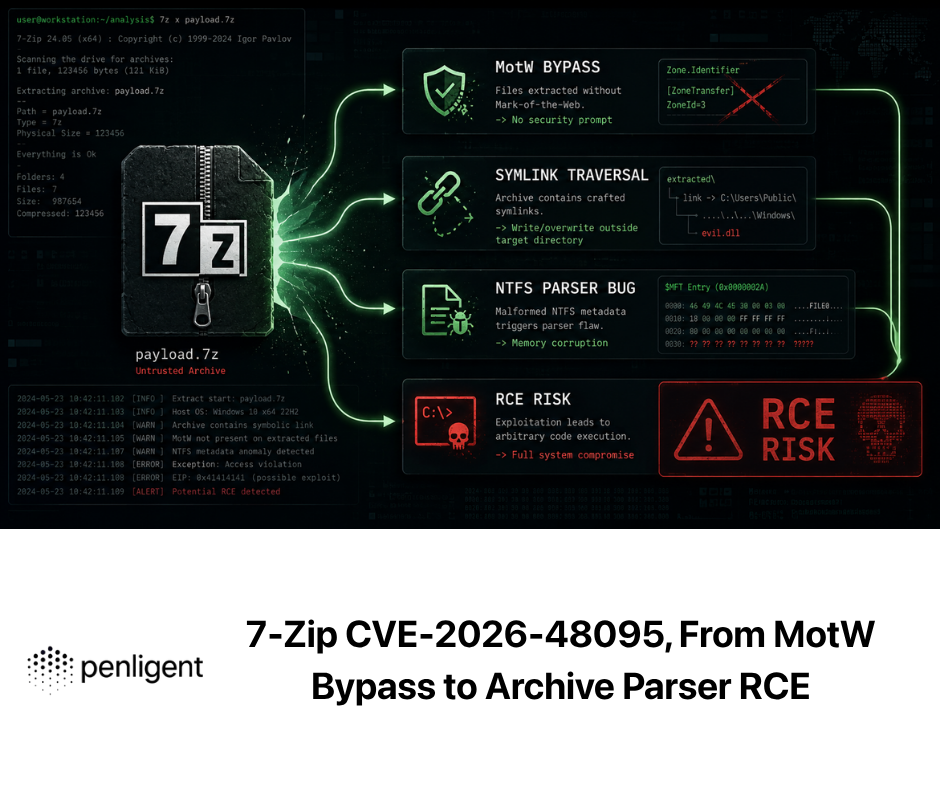
Two paragraphs where Penligent fits naturally—verification and evidence, not hype
In real remediation programs, the slowest part is often not “knowing a CVE exists,” but producing defensible answers to: Are we actually vulnerable? Did the mitigation actually work? Can we prove it? CVE identifiers help coordinate information, but they don’t generate evidence by themselves.
That’s where a workflow-oriented platform like Penligent can be useful: instead of stopping at “scanner says vulnerable,” you can drive toward tekrarlanabilir doğrulama—target profiling, controlled proof checks, headless-browser validation where relevant, and report artifacts that map remediation actions back to the CVE record. When the goal is reducing real risk (not just closing tickets), evidence-based verification is often the difference between “patched in theory” and “safe in production.”
Referanslar
CVE program overview (CVE.org): https://www.cve.org/ CVE identifier process and format: https://www.cve.org/about/Process CVE year meaning (archived FAQ): https://www.cve.org/Resources/Media/Archives/OldWebsite/about/faqs.html RESERVED explanation (CVE blog archive): https://www.cve.org/Resources/Media/Archives/OldWebsite/blog/May102017_Why_is_a_CVE_entry_marked_as_RESERVED_when_a_CVE_ID_is_being_publicly_used.html NIST NVD home: https://nvd.nist.gov/ NVD vulnerability APIs: https://nvd.nist.gov/developers/vulnerabilities NVD and CVSS metrics: https://nvd.nist.gov/vuln-metrics/cvss FIRST CVSS specification (v4): https://www.first.org/cvss/specification-document CISA Known Exploited Vulnerabilities Catalog: https://www.cisa.gov/known-exploited-vulnerabilities-catalog NVD note on KEV labeling: https://nvd.nist.gov/general/news/cisa-exploit-catalog Microsoft guidance for SharePoint CVE-2025-53770: https://www.microsoft.com/en-us/msrc/blog/2025/07/customer-guidance-for-sharepoint-vulnerability-cve-2025-53770 CISA alert update on SharePoint exploitation: https://www.cisa.gov/news-events/alerts/2025/07/20/update-microsoft-releases-guidance-exploitation-sharepoint-vulnerabilities Unit 42 research on SharePoint exploitation and CVE-2025-53770: https://unit42.paloaltonetworks.com/microsoft-sharepoint-cve-2025-49704-cve-2025-49706-cve-2025-53770/ MITRE “CVE intro” handout PDF: https://makingsecuritymeasurable.mitre.org/docs/cve-intro-handout.pdf CVE-2026-2441 Chrome CSS zero-day guide: https://www.penligent.ai/hackinglabs/cve-2026-2441-the-chrome-css-zero-day-you-must-patch-and-prove-across-the-fleet/ CVE-2026-20805 Windows DWM info disclosure guide: https://www.penligent.ai/hackinglabs/cve-2026-20805-the-dwm-memory-leak-that-makes-other-exploits-suddenly-reliable/ CVE 2026 vulnerability landscape roundup: https://www.penligent.ai/hackinglabs/cve-2026-the-vulnerability-landscape-when-identity-breaks-and-legacy-code-bites-back/