Pack2TheRoot is the name Deutsche Telekom’s Red Team gave to CVE-2026-41651, a high-severity local privilege escalation vulnerability in PackageKit. The important part is simple: on vulnerable systems, a low-privileged local user can cause PackageKit to install or remove system packages without proper authorization, and that can lead to root access or other forms of host compromise. The vulnerability affects multiple Linux distributions in default installations, carries a CVSS 3.1 score of 8.8, and is fixed in PackageKit 1.3.5 and distribution backports. (Telekom Security)
This is not a remote unauthenticated RCE. That distinction matters. An attacker already needs local access, a user shell, a compromised account, an exposed session, or another foothold on the host. But in real intrusions, local privilege escalation is often the step that decides whether the attacker remains boxed inside a user account or becomes the system owner. Developer workstations, shared Linux desktops, CI runners, lab machines, jump hosts, VDI systems, and servers with management tooling can all turn a “local only” bug into a serious post-compromise accelerator.
The uncomfortable part of Pack2TheRoot is not that Linux package managers are dangerous by nature. Package managers must perform privileged operations by design. The problem is that PackageKit sits at the boundary between unprivileged user-facing clients and root-level package operations. A race condition at that boundary can turn an ordinary package transaction into a privilege boundary failure. NVD describes the bug as a time-of-check time-of-use race condition on PackageKit transaction flags that lets unprivileged users install packages as root, with PackageKit versions from 1.0.2 through 1.3.4 affected and 1.3.5 patched. (NVD)
Pack2TheRoot at a glance
| Öğe | What security teams need to know |
|---|---|
| CVE | CVE-2026-41651 |
| İsim | Pack2TheRoot |
| Bileşen | PackageKit daemon |
| Güvenlik açığı sınıfı | Time-of-check time-of-use race condition, CWE-367 |
| Security impact | Local privilege escalation to root through unauthorized package installation or removal |
| Attacker position | Local low-privileged user |
| Network exposure | Not directly remote by itself |
| User interaction | None after the attacker has local access |
| CVSS | 8.8 High, CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H |
| Confirmed affected range | PackageKit 1.0.2 through 1.3.4 |
| Yukarı akış sürümü düzeltildi | PackageKit 1.3.5 |
| Patch model | Upstream release plus distribution backports |
| Key detection idea | Check installed PackageKit versions and inspect PackageKit journal logs for crash indicators |
| Main response | Patch through the distribution vendor, verify installation state, then investigate high-value hosts for possible abuse |
GitHub’s PackageKit security advisory lists the package as PackageKit, rates the issue high, marks versions through 1.3.4 as affected, and lists 1.3.5 or later as patched. The same advisory records the CVSS vector as local, low-complexity, low-privilege, no user interaction, changed scope, and high impact across confidentiality, integrity, and availability. (GitHub)
Why PackageKit is a serious local security boundary
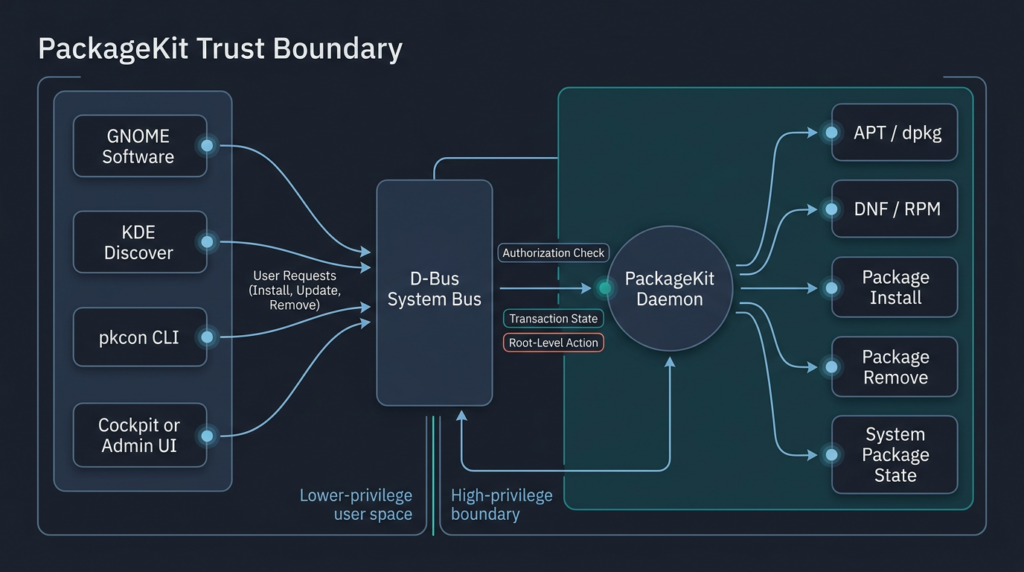
PackageKit is easy to underestimate because many users never call it directly. They use GNOME Software, KDE Discover, desktop update dialogs, Cockpit, or distribution management tools. Under the hood, PackageKit provides a common interface between those clients and the actual package management backend. Its official specification describes it as a D-Bus abstraction layer that lets a session user manage packages through a secure, cross-distro, cross-architecture API, using a lightweight backend architecture. (PackageKit)
That design makes sense. Linux distributions do not all use the same package manager. Debian and Ubuntu use APT and dpkg. Fedora, Rocky Linux, and RHEL-family systems use dnf or rpm-backed workflows. Desktop environments and management tools do not want to reimplement every package manager’s behavior. PackageKit gives them a common API, while backends perform distro-specific work.
The security problem is that PackageKit is not just a passive library. It mediates actions that can change the system. The Debian pkcon manual describes pkcon as the command-line client for PackageKit and lists actions such as installing packages from repositories, installing local package files, removing packages, updating the system, refreshing metadata, enabling and disabling repositories, and triggering offline updates. Those operations are not cosmetic. They affect what code exists on the machine and what code runs with privilege. (manpages.debian.org)
Package installation is one of the most sensitive operations on a Linux host. A package can place files under privileged paths, create services, install scripts, modify system state, and influence future execution. On RPM-based systems, the NVD entry explicitly notes that a local unprivileged user can install arbitrary RPM packages as root, including executing RPM scriptlets, without authentication. That is why Pack2TheRoot should be treated as a root-compromise path, not merely an odd package manager bug. (NVD)
PackageKit also has an operational detail that makes naive exposure checks unreliable: it does not always sit in the process list. Telekom’s advisory warns that it is not enough to grep running processes because PackageKit and Cockpit may be activated on demand through D-Bus. A host can look quiet until a client invokes the service. (Telekom Security)
The bug, without turning this into an exploit recipe
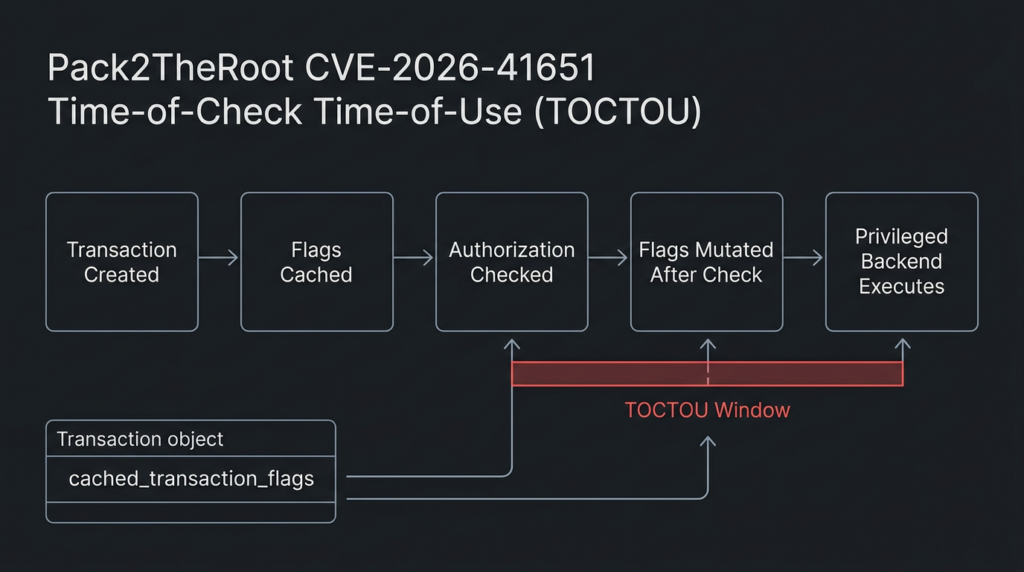
Pack2TheRoot is a TOCTOU bug. TOCTOU stands for time-of-check time-of-use. The vulnerable program checks a state, permission, object, or parameter at one moment, then uses something later after the relevant state has changed. The check may have been correct when it happened. The use may be unsafe because the world is no longer the same.
In PackageKit’s case, the race concerns transaction flags. A safe package operation needs the operation, state, flags, and authorization decision to stay bound together. If a client can influence transaction flags after authorization has been evaluated, the daemon can end up executing a transaction under assumptions that no longer match what was approved.
NVD’s enriched description gives the clearest public technical shape. It says the race involves transaction->cached_transaction_flags and a silent state-machine guard. Three issues are called out: InstallFiles() writes caller-supplied flags without checking whether the transaction has already been authorized or started; pk_transaction_set_state() silently discards backward state transitions while leaving the overwritten flags in place; and the scheduler’s idle callback reads the cached transaction flags at dispatch time rather than binding them at authorization time. (NVD)
A simplified defensive model looks like this.
| Sahne | Safe assumption | What Pack2TheRoot breaks |
|---|---|---|
| Client requests a package operation | The request parameters and flags are stable | |
| Authorization is evaluated | The authorization decision applies to the same operation that will execute | |
| Transaction state changes | Illegal state changes should not leave security-relevant side effects behind | |
| Backend executes work | The backend should consume the same flags that were checked earlier | |
| System package state changes | Only authorized package operations should run as root |
The patch tells the same story from the maintainer side. The PackageKit fix is titled “Do not allow re-invoking methods on non-new transactions.” Its commit message says the change ensures cached parameters, such as transaction flags, cannot be changed on a transaction that is already running or waiting for authorization, and that it prevents backward state transitions when a client misbehaves. (GitHub)
That is the core security lesson. A transaction object that crosses a privilege boundary must not let later calls rewrite the security-relevant parameters of an earlier authorization decision. Once an operation has moved out of the “new” state, callers should not be able to mutate the data that determines what root will eventually do.
This is also why exploit details do not need to be reproduced for defenders to act. The public record already establishes the essential impact: unprivileged local users can cause root-level package operations without authorization on vulnerable systems. Telekom states that it developed a working proof of concept but did not publish it at the time of disclosure for security reasons. (Telekom Security)
Why a local bug still deserves urgent treatment
Security teams sometimes underrate local privilege escalation because it does not start from the internet. That is a dangerous habit. Attack chains rarely consist of one vulnerability. They usually start with phishing, a stolen credential, a browser session, a vulnerable internal service, a compromised developer dependency, a weak SSH key, an exposed notebook, a CI misconfiguration, or a normal user account abused from inside the network.
A local root bug changes what the attacker can do after that first foothold. Without root, a user-level process may be limited by file permissions, endpoint controls, audit policies, network restrictions, or container boundaries. With root, the attacker can tamper with logs, install persistence, read secrets, alter build artifacts, disable controls, dump credentials, modify package repositories, implant services, pivot to other systems, and conceal activity.
Pack2TheRoot is especially relevant in environments where Linux hosts are shared or automation-heavy. A university lab workstation, a research cluster login node, a build server, a shared developer desktop, a contractor VDI image, or a server with local application users can all have many low-privilege paths into the machine. A bug that turns any of those users into root raises the stakes.
The threat model is even more important when PackageKit is installed near management tooling. Telekom notes that PackageKit is an optional dependency of Cockpit, and that servers with Cockpit installed might be vulnerable, including Red Hat Enterprise Linux environments, if PackageKit is present and enabled. That does not mean every RHEL server is automatically exploitable. It means teams should check actual package state and activation behavior rather than assume a server is safe because no desktop is visible. (Telekom Security)
Affected versions and tested distributions
The clean upstream rule is: PackageKit versions from 1.0.2 through 1.3.4 are vulnerable, and PackageKit 1.3.5 contains the upstream fix. Telekom’s disclosure says all versions between >= 1.0.2 ve <= 1.3.4 are vulnerable, and GitHub’s advisory lists patched versions as >= 1.3.5. (Telekom Security)
There is one nuance: GitHub’s advisory says affected versions are >= 0.8.1 and <= 1.3.4, while also stating that all versions between 1.0.2 and 1.3.4 are confirmed vulnerable and that the issue likely exists since 0.8.1. That difference matters for accurate writing. The confirmed tested range and the likely historical range are not identical. Treat 1.0.2 through 1.3.4 as confirmed affected in the public advisory language, and treat 0.8.1 as a likely earlier introduction unless your vendor has confirmed your package. (GitHub)
Telekom explicitly tested exploitability on these default installations with apt and dnf backends: Ubuntu Desktop 18.04, 24.04.4, and 26.04 LTS beta; Ubuntu Server 22.04 through 24.04 LTS; Debian Desktop Trixie 13.4; RockyLinux Desktop 10.1; Fedora 43 Desktop; and Fedora 43 Server. The advisory also says it is reasonable to assume distributions shipping PackageKit enabled are vulnerable. (Telekom Security)
| Environment | Public status signal | Practical interpretation |
|---|---|---|
| PackageKit 1.0.2 through 1.3.4 | Confirmed vulnerable in Telekom disclosure | Patch or verify vendor backport immediately |
| PackageKit 1.3.5 or later | Upstream fixed | Still verify distro package changelog and deployment |
| Fedora 42 through 44 | Telekom links Fedora fixed package as PackageKit 1.3.4-3 | Do not rely only on upstream version numbers when distros backport patches |
| Ubuntu 22.04 LTS, 24.04 LTS, 25.10, 26.04 LTS | Ubuntu page lists fixed package versions for these releases | Use Ubuntu package status, not generic version comparison alone |
| Ubuntu 20.04 LTS, 18.04 LTS, 16.04 LTS | Ubuntu page showed these as vulnerable at the checked update state | Verify support status and vendor remediation path |
| Debian, Rocky Linux, other distros with PackageKit | Tested or reasonably suspected depending on package state | Check installed packages and vendor advisories |
Ubuntu’s CVE page listed CVE-2026-41651 as High with CVSS 8.8 and described the priority reason as local privilege escalation to the root user. Its status table showed fixed package versions for 26.04 LTS, 25.10, 24.04 LTS, and 22.04 LTS, while 20.04 LTS, 18.04 LTS, and 16.04 LTS were shown as vulnerable at the time reflected in the page. (Ubuntu)
The Fedora case is a useful reminder for asset owners. Telekom links Fedora 42 through 44 as fixed in PackageKit-1.3.4-3. That looks older than upstream 1.3.5, but it may contain a distribution backport. Security teams should not blindly compare only the upstream semantic version. They should check distribution security trackers, changelogs, and package release notes. (Telekom Security)
How to check Linux hosts safely
The first question is whether PackageKit is installed. Do not start with exploit attempts. Start with inventory.
On Debian and Ubuntu systems:
dpkg-query -W -f='${Package} ${Version}\n' 'packagekit*' 2>/dev/null
apt-cache policy packagekit packagekit-tools 2>/dev/null
On Fedora, Rocky Linux, RHEL-family, AlmaLinux, and similar RPM-based systems:
rpm -qa | grep -i '^PackageKit\|^packagekit'
dnf info PackageKit packagekit 2>/dev/null
On hosts where package naming may vary, use a broader case-insensitive query:
dpkg -l | grep -i packagekit
rpm -qa | grep -i packagekit
Those two commands match Telekom’s own initial package detection guidance. The advisory explicitly notes the -i flag because the package may appear with camel-case naming such as PackageKit. (Telekom Security)
The second question is whether PackageKit can be activated. Do not assume “not running right now” means “not reachable.” PackageKit can be D-Bus activated. A systemd process check can miss an on-demand service.
systemctl status packagekit --no-pager
systemctl cat packagekit 2>/dev/null
busctl list | grep -i packagekit || true
You can also look for D-Bus service files:
grep -R "PackageKit" /usr/share/dbus-1/system-services /etc/dbus-1/system.d 2>/dev/null
Telekom recommends systemctl status packagekit or PackageKit monitor tools as availability checks. It notes that if systemctl shows the service as loaded or running, or monitoring tools show transaction output, the daemon is active and the system is potentially exploitable if unpatched. For PackageKit before 1.3.3, Telekom recommends pkmon; for 1.3.3 and later, it recommends pkgcli monitor. (Telekom Security)
A safe monitoring check looks like this:
command -v pkmon >/dev/null && timeout 5s pkmon
command -v pkgcli >/dev/null && timeout 5s pkgcli monitor
This does not exploit the vulnerability. It only helps determine whether PackageKit transaction activity is observable.
A fleet inventory script for defenders
The following script is designed for authorized internal inventory. It does not attempt exploitation. It prints installed PackageKit package names, versions, service state, D-Bus service hints, and the most relevant journal indicators.
#!/usr/bin/env bash
set -euo pipefail
echo "== Host =="
hostnamectl 2>/dev/null || hostname
echo
echo "== PackageKit packages =="
if command -v dpkg-query >/dev/null 2>&1; then
dpkg-query -W -f='${Package} ${Version}\n' 'packagekit*' 2>/dev/null || true
fi
if command -v rpm >/dev/null 2>&1; then
rpm -qa | grep -i '^PackageKit\|^packagekit' || true
fi
echo
echo "== systemd service state =="
if command -v systemctl >/dev/null 2>&1; then
systemctl status packagekit --no-pager 2>/dev/null || true
systemctl is-enabled packagekit 2>/dev/null || true
fi
echo
echo "== D-Bus service references =="
grep -R "PackageKit" /usr/share/dbus-1/system-services /etc/dbus-1/system.d 2>/dev/null || true
echo
echo "== PackageKit monitor tools =="
command -v pkmon || true
command -v pkgcli || true
echo
echo "== Recent PackageKit journal indicators =="
if command -v journalctl >/dev/null 2>&1; then
journalctl --no-pager -u packagekit --since "14 days ago" 2>/dev/null \
| grep -Ei 'emitted_finished|pk-transaction|assertion failed|PackageKit:ERROR' || true
fi
For a large environment, run this through your normal endpoint management, configuration management, or EDR live response mechanism. Do not SSH manually into hundreds of machines unless you enjoy turning vulnerability response into a spreadsheet marathon. The goal is to quickly answer four questions: where PackageKit exists, which version or vendor build is installed, whether it can be activated, and whether there are suspicious journal signals.
Log indicators and their limits
Telekom published a useful indicator of compromise. It says successful exploitation leaves traces because the PackageKit daemon hits an assertion failure and crashes. Systemd can recover the daemon on the next D-Bus invocation, so the crash does not necessarily create a lasting denial of service, but it can be visible in system logs. The advisory gives a journal query for emitted_finished and shows a PackageKit assertion failure in pk_transaction_finished_emit. (Telekom Security)
Use this query as a starting point:
journalctl --no-pager -u packagekit | grep -i emitted_finished
A broader defensive query is often better:
journalctl --no-pager -u packagekit --since "30 days ago" \
| grep -Ei 'emitted_finished|pk_transaction_finished_emit|assertion failed|PackageKit:ERROR|pk-transaction'
For SIEM-style environments, translate the logic into your platform’s search syntax. The event source will typically be systemd journal, syslog, or an endpoint telemetry stream that captures service crashes. You are looking for abnormal PackageKit daemon assertions, especially around transaction completion.
A useful detection table:
| Sinyal | Neden önemli | Sınırlama |
|---|---|---|
| PackageKit installed with vulnerable build | Confirms potential exposure | Does not prove exploit occurred |
| PackageKit D-Bus activation available | Shows service may be reachable on demand | D-Bus state varies by distro and install profile |
emitted_finished assertion in PackageKit logs | Published IOC associated with successful exploitation | Logs may rotate, be cleared, or be unavailable |
| Unexpected package install or removal near crash time | Can indicate abuse of package transaction flow | Admin actions and updates can be noisy |
| New services, scripts, cron jobs, or package scriptlet artifacts after PackageKit crash | Indicates possible post-escalation persistence | Requires host forensics |
| PackageKit crash followed by suspicious root process activity | Stronger chain evidence | Needs EDR, auditd, or process accounting |
Do not reverse the logic. A log hit is concerning. No log hit is not proof of safety. A vulnerable system still needs patching even if there is no IOC.
Patching guidance that avoids version traps
The safest response is to install the vendor security update for your distribution. Upstream PackageKit 1.3.5 fixes the issue, but distributions may backport the patch into packages that do not show 1.3.5 as the visible version. Telekom’s updated packages section explicitly points to distribution package overviews for Debian, Ubuntu, and Fedora, and notes Fedora 42 through 44 fixed in PackageKit-1.3.4-3. (Telekom Security)
On Debian and Ubuntu:
sudo apt update
sudo apt install --only-upgrade packagekit packagekit-tools
apt-cache policy packagekit packagekit-tools
On Fedora:
sudo dnf upgrade --refresh PackageKit packagekit
rpm -qa | grep -i '^PackageKit\|^packagekit'
On Rocky Linux, RHEL-family, AlmaLinux, and compatible systems:
sudo dnf update --refresh PackageKit packagekit
rpm -qa | grep -i '^PackageKit\|^packagekit'
After patching, validate service state:
systemctl status packagekit --no-pager
journalctl --no-pager -u packagekit --since "1 hour ago"
A reboot is not always strictly required for a user-space daemon fix, but it is often the cleanest way to ensure a high-value workstation or server has no stale process state and that all package-triggered services have restarted. At minimum, restart the PackageKit service after patching if your change process allows it:
sudo systemctl restart packagekit
For high-value assets, patching should be followed by a short post-incident check if the host was exposed to untrusted local users or had a recent user-level compromise. Look for unusual packages, new repositories, new services, new users, suspicious files under /etc/systemd/system, unexpected cron entries, modified SSH authorized keys, and anomalous root process history.
Temporary mitigation when patching is blocked
Patching is the fix. Temporary mitigation is only a bridge for systems where package updates cannot be applied immediately.
The most direct mitigation is to remove or disable PackageKit where it is not needed. That decision must be tested because PackageKit can support desktop software management, update tools, and Cockpit-related workflows. Removing it from a developer workstation may break expected GUI update behavior. Disabling it on a server may affect management tooling.
Inventory first:
systemctl status packagekit --no-pager
systemctl list-dependencies --reverse packagekit 2>/dev/null || true
rpm -q --whatrequires PackageKit packagekit 2>/dev/null || true
apt-cache rdepends packagekit 2>/dev/null || true
If your environment confirms PackageKit is unnecessary on a specific host class, a temporary service-level control may look like this:
sudo systemctl stop packagekit
sudo systemctl disable packagekit
sudo systemctl mask packagekit
Masking should be treated as a change-management action, not a casual hardening trick. It may block expected software management flows and can be undone by administrators who need normal PackageKit behavior later:
sudo systemctl unmask packagekit
sudo systemctl enable packagekit
sudo systemctl start packagekit
On hosts where D-Bus activation exists, service masking may still need to be validated. Do not assume a one-line control is sufficient. Test whether PackageKit can still be invoked through the normal frontends in your distro image.
A more conservative temporary control is to restrict local shell access, disable unneeded shared accounts, pause nonessential multi-user access, or isolate high-value hosts until the package update is complete. That does not fix the vulnerability. It reduces the number of people and processes that can reach the local starting point.
What to prioritize first
Patch prioritization should be based on attacker access, host value, and package state. CVSS is useful, but it does not know your environment.
| Öncelik | Host type | Neden önce gelir |
|---|---|---|
| En yüksek | Shared Linux workstations, student labs, research workstations | Many low-privilege users can reach the local attack condition |
| En yüksek | Developer machines with production credentials | Root can expose tokens, SSH keys, source, secrets, and signing material |
| En yüksek | CI runners and build agents | Root compromise can poison build outputs and credentials |
| Yüksek | Jump hosts, admin desktops, bastions with local users | Local root can become lateral movement infrastructure |
| Yüksek | Servers with Cockpit and PackageKit installed | PackageKit may exist outside classic desktop assumptions |
| Orta | Single-user desktops with strong endpoint controls | Still patch, but prioritize after multi-user and high-value assets |
| Orta | Ephemeral lab images | Patch base images to prevent redeploying vulnerable state |
| Daha düşük | Systems without PackageKit installed | Record as not affected, but verify golden images |
The most common mistake is treating “server” and “desktop” as clean categories. Many servers include management packages. Many desktops hold production secrets. Many CI agents are technically servers but behave like developer workstations with far more privilege. Pack2TheRoot response should follow actual attack path value, not asset labels.
Why PackageKit version alone may mislead you
Version comparison is easy when every system tracks upstream exactly. Enterprise Linux does not work that way. Distributions often backport security fixes while keeping the visible upstream version number stable. That means a scanner that only says “PackageKit version is below 1.3.5” can overstate risk on a patched backport. A scanner that only says “the package name is installed” can also overstate risk if the distro has already shipped a fixed build.
The inverse mistake is worse: assuming a package is safe because your distro did not jump to 1.3.5. Fedora’s referenced fix is exactly why that logic breaks. Telekom’s advisory points to Fedora 42 through 44 fixed in a 1.3.4-3 package. (Telekom Security)
Use a layered check:
# Debian and Ubuntu
apt-cache policy packagekit packagekit-tools
apt changelog packagekit 2>/dev/null | head -80
# RPM-family systems
rpm -qi PackageKit 2>/dev/null || rpm -qi packagekit 2>/dev/null
rpm -q --changelog PackageKit 2>/dev/null | head -80
dnf updateinfo list --cve CVE-2026-41651 2>/dev/null
A good vulnerability management record for this issue should store the distribution, release, installed package name, installed package version, vendor advisory status, patch date, reboot or service restart state, and any IOC checks performed. That is more useful than a single “vulnerable yes or no” field.
Attack scenarios that matter
A Pack2TheRoot risk assessment should not start with “can someone run a local exploit.” It should start with “who can already reach a low-privilege context on this host.”
A stolen developer SSH key is one example. A normal user shell on a development workstation might not immediately expose root-only files. If PackageKit is vulnerable, that same shell can become root, and root can read local credentials, modify tools, inspect build caches, and implant persistence.
A compromised browser session is another. Browser compromise often starts in user context. If the host is a Linux desktop with vulnerable PackageKit available, the browser foothold may become a route to root if the attacker can run local code.
A CI runner is a third. Many CI jobs run as non-root users by design. That boundary matters because CI hosts often hold deployment tokens, registry credentials, signing keys, and network access. A local privilege escalation on such a host can turn a malicious build step into full host compromise.
A shared lab machine is a fourth. Universities, training labs, research clusters, and internal security sandboxes often have legitimate low-privilege users. A local bug that allows any such user to become root can collapse the trust model of the entire shared machine.
A server with Cockpit or desktop packages installed is a fifth. Administrators may assume PackageKit is absent because the machine is “a server,” but PackageKit may arrive as a dependency or optional management component. Telekom explicitly calls out Cockpit as relevant because PackageKit is an optional dependency. (Telekom Security)
How Pack2TheRoot compares to other Linux local root bugs
Pack2TheRoot fits a long pattern: a local low-privilege foothold crosses a privileged helper or kernel boundary and becomes root. The implementation details differ, but the operational lesson is consistent. Local privilege escalation is not minor when the affected component is common, default, privileged, and easy to reach.
| CVE | Bileşen | Why it is relevant to Pack2TheRoot |
|---|---|---|
| CVE-2021-4034 | polkit pkexec | A widely deployed privileged helper allowed local privilege escalation through unsafe handling of parameters and environment behavior |
| CVE-2022-0847 | Linux kernel Dirty Pipe | Local attackers could exploit a kernel flaw to alter protected file state and escalate impact |
| CVE-2023-4911 | glibc dynamic loader | A local attacker could use crafted GLIBC_TUNABLES environment variables with SUID binaries to execute code with elevated privileges |
| CVE-2024-1086 | Linux kernel nf_tables | A netfilter use-after-free could be exploited for local privilege escalation |
NVD describes CVE-2021-4034 as a local privilege escalation in polkit’s pkexec, a setuid tool intended to let unprivileged users run commands as privileged users according to policy. The bug involved mishandling calling parameters and environment variables, allowing arbitrary code execution through crafted environment state. That is relevant because Pack2TheRoot also lives at a policy-mediated privilege boundary, though the affected component and mechanics are different. (NVD)
CVE-2023-4911, known as Looney Tunables, is another useful comparison. NVD describes it as a buffer overflow in glibc’s dynamic loader ld.so while processing GLIBC_TUNABLES, allowing local attackers to use crafted environment variables when launching SUID binaries to execute code with elevated privileges. The link to Pack2TheRoot is not the code path. The link is the defensive lesson: ordinary local inputs can become dangerous when privileged components consume them at the wrong time or under the wrong assumptions. (NVD)
CVE-2024-1086 shows the same post-compromise value from a kernel angle. NVD describes it as a use-after-free vulnerability in Linux kernel netfilter nf_tables that can be exploited for local privilege escalation. Kernel bugs often get more attention than package management bugs, but the attacker’s business logic is identical: obtain a low-privilege foothold, cross the host boundary, become root, and then persist or pivot. (NVD)
Dirty Pipe, CVE-2022-0847, belongs in the same mental bucket. It became famous because it was a Linux local privilege escalation with practical file-tampering consequences. The details are not the same as Pack2TheRoot, but both remind defenders that local Linux flaws are often the difference between containment and full host control. (NVD)
AI-assisted vulnerability research, what this event actually shows
Pack2TheRoot is also notable because Telekom says the vulnerability was discovered with AI-assisted research. Their disclosure states that the initial investigation started after unusual pkcon install behavior on Fedora Workstation, where a system package could be installed without requiring a password. They then guided research in a specific direction using Anthropic Claude Opus, discovered an exploitable vulnerability, manually reviewed and verified the finding, and responsibly reported it to the PackageKit maintainers. (Telekom Security)
That wording matters. It does not support a simplistic claim that an AI autonomously found and responsibly disclosed a Linux root bug end to end. The public disclosure says human researchers noticed a suspicious behavior, directed the investigation, used AI assistance, reviewed the result manually, validated exploitability, and coordinated with maintainers.
That is a realistic model for AI in vulnerability research. AI can help generate hypotheses, inspect code paths, propose edge cases, and connect implementation details faster than a human working alone. It can also hallucinate, overfit to irrelevant patterns, or produce misleading confidence. The Pack2TheRoot disclosure is interesting precisely because it shows AI inside a disciplined research workflow rather than replacing the workflow.
For defenders, the lesson is similar. AI can help triage logs, write safe inventory scripts, group assets, and explain whether a local bug fits a larger attack chain. It should not be trusted as the sole source of truth for exploitability, patch status, or incident conclusions. Pack2TheRoot still required vendor coordination, patch review, release timing, and careful disclosure.
Safe validation workflow for security teams
The right validation workflow is not to hunt down a public exploit. It is to prove exposure and remediation safely.
Step one is package inventory. Determine whether PackageKit is installed and which package version or vendor build exists.
Step two is activation analysis. Determine whether PackageKit can be activated through systemd or D-Bus. Remember that a missing running process does not prove absence.
Step three is vendor status mapping. Compare package state to your distribution’s advisory, not only upstream version 1.3.5.
Step four is patch deployment. Apply the vendor update or upstream fixed package where appropriate.
Step five is service restart or reboot validation. Ensure stale daemons are not still running.
Step six is IOC review. Look for PackageKit crash indicators, suspicious package transactions, unexpected repository changes, and root-level post-compromise artifacts.
Step seven is post-patch retesting. Confirm the fixed package remains installed after reboot, golden image rebuilds, and endpoint configuration enforcement.
An internal evidence record might look like this:
host: dev-linux-042
owner: platform-engineering
os: Ubuntu 24.04 LTS
packagekit_installed: true
packagekit_version_before: 1.2.8-2ubuntu1.4
vendor_status_before: vulnerable
packagekit_version_after: 1.2.8-2ubuntu1.5
vendor_status_after: fixed
service_restart: packagekit restarted
reboot_required: evaluated
ioc_check:
journal_emitted_finished: none_found
packagekit_assertion_failure: none_found
suspicious_package_changes: pending_review
notes: "Patched through vendor repository, no exploit attempt performed"
For teams running authorized security validation programs, Pack2TheRoot is the kind of issue that should be tested as part of a broader attack chain rather than isolated as a scanner finding. A useful test asks whether a low-privilege foothold on a workstation, CI host, or management server changes the blast radius. Penligent’s public materials around automated penetration testing and privilege escalation focus on evidence-backed CVE validation, attack-chain reasoning, and reporting rather than simple vulnerability labels, which is the right shape for this class of post-compromise risk. The vendor patch remains the fix; validation tooling should help teams prove exposure, prioritize remediation, and preserve evidence. (Penligent)
That distinction is important. No AI pentesting platform should be used as an excuse to delay a vendor update. The useful role is after and around patching: identify where the vulnerable condition exists, document whether a low-privileged attacker path is realistic in your environment, verify that remediation closed the path, and turn the result into an artifact another engineer can reproduce.
Defensive hardening beyond the patch
Patching PackageKit closes the known vulnerability. It does not remove the broader class of risk around privileged package workflows.
Start with local user hygiene. Remove stale local accounts. Disable unused contractor logins. Review sudoers. Confirm service accounts cannot obtain interactive shells unless absolutely necessary. Local privilege escalation requires a local starting point; reduce unnecessary starting points.
Review package repository trust. If an attacker can add repositories, alter package sources, or influence package resolution, root-level package operations become even more dangerous. Check APT source lists, dnf repo files, GPG keyrings, and unexpected local repositories.
On Debian and Ubuntu:
find /etc/apt -type f -maxdepth 3 -print -exec sed -n '1,120p' {} \;
apt-key list 2>/dev/null || true
find /etc/apt/trusted.gpg.d -type f -maxdepth 1 -print
On RPM-family systems:
find /etc/yum.repos.d -type f -print -exec sed -n '1,160p' {} \;
rpm -qa gpg-pubkey*
dnf repolist -v
Monitor package management activity. Package installs and removals are often high-signal events on servers and CI hosts. On systemd hosts, preserve journal data long enough to investigate. On high-value endpoints, collect process execution, package manager commands, service changes, and root-owned file modifications into your EDR or SIEM.
Consider auditd rules where appropriate:
sudo auditctl -w /usr/bin/pkcon -p x -k packagekit_cli
sudo auditctl -w /usr/bin/pkgcli -p x -k packagekit_cli
sudo auditctl -w /usr/libexec/packagekitd -p x -k packagekit_daemon 2>/dev/null || true
sudo auditctl -w /usr/lib/packagekit/packagekitd -p x -k packagekit_daemon 2>/dev/null || true
sudo auditctl -w /etc/yum.repos.d -p wa -k package_repos
sudo auditctl -w /etc/apt/sources.list -p wa -k package_repos
sudo auditctl -w /etc/apt/sources.list.d -p wa -k package_repos
Paths vary by distribution, so validate before deploying audit rules at scale. Poorly tested audit rules can create noise or performance issues.
Restrict GUI package management on server images. If a base image does not need desktop software centers, remove them. If a server does not need Cockpit or PackageKit, keep the image minimal. Minimalism is not a substitute for patching, but it reduces future attack surface.
Protect build systems. CI runners should be disposable, tightly scoped, and prevented from holding long-lived credentials where possible. A local root bug on a CI host is much less damaging when the host is ephemeral, secrets are short-lived, and builds run in isolated environments with strict egress.
Common mistakes during response
The first mistake is checking only ps aux. PackageKit may not be running until D-Bus activates it. Telekom explicitly warns against relying on the process list alone. (Telekom Security)
The second mistake is relying only on upstream version comparison. Distribution backports can fix the bug without changing the visible upstream version to 1.3.5. Fedora’s referenced fixed package illustrates the issue. (Telekom Security)
The third mistake is treating “local” as “low priority.” A local bug on a single-user throwaway VM may be low urgency. The same bug on a CI runner, shared workstation, admin jump host, or developer laptop with production credentials is not.
The fourth mistake is patching and skipping incident review. If a high-value host had a recent low-privilege compromise, the PackageKit patch does not answer whether the vulnerability was already used. Check logs and package state.
The fifth mistake is running untrusted PoC code. Telekom withheld its proof of concept at disclosure time, and the maintainer community intentionally kept details light to give users time to patch. Security teams should not compensate by executing random exploit code from social media or paste sites on production-like systems. (openwall.com)
The sixth mistake is assuming scanners will understand every vendor backport correctly on day one. Scanner results should be reconciled against vendor advisories, installed package changelogs, and release-specific security trackers.
What maintainers fixed
The upstream patch is small but conceptually important. The commit rejects attempts to call action methods when a transaction is no longer new. The code comment added by the patch says that action methods must only be invoked once on a new transaction and that attempts to reinvoke them after initialization are rejected to prevent a second D-Bus call from overwriting transaction flags or other cached state after authorization was already granted for previous parameters. (GitHub)
That fix reinforces a durable design principle: authorization-sensitive parameters should become immutable after the authorization boundary. If a daemon checks permissions on one set of parameters, later execution must not consume a different set. If a state machine rejects an illegal transition, it should not leave behind modified security state from the rejected operation.
For security reviewers, this is a useful pattern to search for in other privileged daemons:
1. A client sends request parameters.
2. The daemon caches those parameters.
3. Authorization is checked.
4. The transaction enters a running or waiting state.
5. Another client call can alter cached parameters.
6. The backend later reads the modified cached parameters.
Any privileged service with that shape deserves careful review, especially when D-Bus, PolicyKit, package management, service management, or desktop-to-root transitions are involved.
Red team and bug bounty takeaways
For red teamers, Pack2TheRoot is a reminder to look beyond setuid binaries and kernel CVEs. Privileged desktop and management daemons often expose richer state machines than a single command-line helper. D-Bus services, package managers, updater daemons, software centers, and system management agents all perform privileged work on behalf of less-privileged clients.
The interesting research question is not merely “can I call this method.” It is “what state is checked, what state is cached, what state is later consumed, and can I create a mismatch.” That is how TOCTOU bugs hide in plain sight. The state machine looks reasonable under normal client behavior. It fails when a client behaves out of order.
For bug bounty hunters, the disclosure also shows the difference between AI-assisted exploration and responsible vulnerability reporting. Telekom states that the finding was manually reviewed and verified before being reported, and that maintainers confirmed the issue and exploitability. That is the standard. A vague AI-generated suspicion is not a high-quality report. A reproducible state mismatch with clear impact, version scope, safe reproduction boundaries, and responsible coordination is.
For defenders running internal adversary simulation, keep Pack2TheRoot-style checks inside authorization boundaries. Do not test local root paths on production machines with public PoC code. Use staging images, patched and unpatched lab hosts, and vendor-approved validation where possible. The goal is to prove and close risk, not to create a second incident.
Incident response checklist
If you find a vulnerable PackageKit build on a high-value host, use a short checklist.
| Adım | Eylem | Neden önemli |
|---|---|---|
| 1 | Preserve package and service state | You need before-and-after evidence |
| 2 | Patch through vendor repository | Vendor packages handle distro-specific backports |
| 3 | Restart PackageKit or reboot | Prevent stale vulnerable daemon state |
| 4 | Search PackageKit journal logs | Look for known assertion failure indicators |
| 5 | Review package install and removal history | Unauthorized package changes are central to impact |
| 6 | Inspect repository configuration | Malicious repositories amplify package installation risk |
| 7 | Check new services and persistence | Root access often becomes systemd persistence |
| 8 | Review local users and SSH keys | A local foothold may have existed before escalation |
| 9 | Compare with EDR process history | PackageKit crash plus suspicious root process is stronger evidence |
| 10 | Update base images | Prevent vulnerable state from returning |
Some useful commands:
# Debian and Ubuntu package history
grep -h " install \| remove \| upgrade " /var/log/apt/history.log /var/log/apt/history.log.* 2>/dev/null
# dpkg history
grep -h " install \| remove \| upgrade " /var/log/dpkg.log /var/log/dpkg.log.* 2>/dev/null
# RPM-family package history
dnf history 2>/dev/null || yum history 2>/dev/null
rpm -qa --last | head -80
# New or modified systemd services
find /etc/systemd/system /usr/lib/systemd/system -type f -mtime -14 -print 2>/dev/null
# Local users with shells
awk -F: '$7 !~ /(false|nologin)$/ {print $1 ":" $3 ":" $6 ":" $7}' /etc/passwd
# SSH authorized keys touched recently
find /home /root -path "*/.ssh/authorized_keys" -type f -mtime -30 -ls 2>/dev/null
None of these commands proves Pack2TheRoot exploitation by itself. They help build a timeline. If PackageKit crash indicators, unexpected package operations, new root-owned persistence, and suspicious user activity cluster together, escalate to full host investigation.
Nihai değerlendirme
Pack2TheRoot is serious because it sits at a practical privilege boundary. It affects PackageKit, a component designed to let user-facing tools manage packages safely across Linux distributions. The vulnerability is local, but low-privilege local access is common in real attack chains. It is high severity, low complexity after local access, requires no user interaction, and can cross from a normal user context into root-level package operations.
The immediate fix is straightforward: apply the vendor update or use PackageKit 1.3.5 or a distribution backport that contains the patch. The operational work is less glamorous but just as important: identify where PackageKit is installed, account for D-Bus activation, verify distro-specific fixed builds, check logs for PackageKit crash indicators, and review high-value hosts where a low-privilege foothold may have existed before patching.
The broader lesson is durable. Privileged Linux daemons do not need memory corruption to fail dangerously. Sometimes the bug is a race between what was authorized and what later runs. When the thing that later runs can install packages as root, that race deserves immediate attention.
Further reading and references
Telekom Security, Pack2TheRoot CVE-2026-41651 disclosure. (Telekom Security)
NVD entry for CVE-2026-41651. (NVD)
GitHub Security Advisory GHSA-f55j-vvr9-69xv for PackageKit. (GitHub)
PackageKit fix commit, “Do not allow re-invoking methods on non-new transactions.” (GitHub)
Ubuntu Security page for CVE-2026-41651. (Ubuntu)
Heise coverage of Pack2TheRoot and affected Linux distributions. (heise online)
PackageKit official specification. (PackageKit)
Debian pkcon manual page. (manpages.debian.org)
Penligent analysis of a related Ubuntu local privilege escalation pattern in CVE-2026-3888. (Penligent)
Penligent explanation of vertical and horizontal privilege escalation. (Penligent)
Penligent docs for running AI-assisted penetration testing workflows on Windows, macOS, and Linux. (Penligent)