The ground-truth facts, without the hype
Here are the key statements you can safely put in a security write-up and defend with primary sources:
- CVE ID: CVE-2026-25046 (NVD)
- Bileşen: Kimi Agent SDK (MoonshotAI/kimi-agent-sdk) (GitHub)
- Vulnerable behavior:
vsix-publish.jsveovsx-publish.jspass filenames toexecSync()as shell command strings; filenames containing shell metacharacters (example:$(cmd)) could lead to arbitrary command execution (NVD) - Fixed in: version 0.1.6 (NVD)
- End-user exposure: NVD and GitHub Advisory explicitly note the vulnerable scripts exist only in the repository’s development scripts, and the published VS Code extension does not include these files; end users are not affected (NVD)
Quick reference table
| Öğe | What it means for defenders | Kaynak |
|---|---|---|
| Affected scripts | vsix-publish.js, ovsx-publish.js | NVD, GitHub Advisory (NVD) |
| Root cause pattern | Filename concatenated into shell command string → execSync() | NVD, SentinelOne summary (NVD) |
| Fixed version | 0.1.6 | NVD, Red Hat (NVD) |
| End-user impact | Published VS Code extension does not include the dev scripts; end users not affected | NVD, GitHub Advisory (NVD) |
How this vulnerability actually works, in plain technical terms
Yüksek seviyede, the bug isn’t “Kimi Agent SDK executes attacker input.” The bug is more specific and more classic:
- A script builds a shell command as a string
- It inserts a dosya adı into that string
- It calls Node.js
execSync()to run the string through a shell - If the filename contains shell metacharacters, the shell interprets them
The NVD entry highlights the exact class of problem: filenames are passed to execSync() as shell command strings, and filenames containing shell metacharacters could execute arbitrary commands. (NVD)
Why filenames are a real input channel in CI
Security teams often underestimate filenames because “we don’t accept filenames from users.” But in CI/CD and release workflows, filenames come from many places:
- artifacts created by build steps (sometimes via templating)
- downloads/unzips into the workspace
- cache directories restored from previous runs
- dependency outputs (including third-party packaging tools)
- files introduced by a compromised contributor, compromised mirror, or poisoned artifact bucket
Başka bir deyişle: even if your application has no “upload a file” feature, your build pipeline often does.
That’s the operational story behind moonshot cve: it’s a publishing boundary issue, not a runtime extension issue. (NVD)
“Low severity” doesn’t mean “ignore it”
Some public databases mark CVE-2026-25046 as low severity. That is consistent with the common CVSS logic: it usually assumes constraints like local conditions and a narrower initial vector. (Feedly)
But for teams shipping code, the question is different:
What happens if the vulnerable script runs inside a high-privilege CI job?
Typical CI environments have access to things attackers actually want:
- publishing tokens (VS Code marketplace, Open VSX, npm, PyPI, etc.)
- signing keys and release credentials
- private repository access tokens
- secrets for cloud storage buckets that store artifacts
So while the vulnerability is in a dev script, the blast radius can still be disproportionate—because CI is where trust and privilege concentrate.
This is also why the broader VS Code extension ecosystem has been tightening controls. In early 2026, multiple reports and announcements describe pre-publish security checks for extension registries like Open VSX—an explicit shift from “clean up after publication” to blocking risky uploads earlier. (The Hacker News)
Safe verification: how to check whether you’re exposed
This section avoids weaponization. The goal is to help maintainers and defenders detect the vulnerable pattern ve confirm remediation.
1) Confirm the version boundary
If you’re using the repository scripts directly (or vendoring them), ensure you’re not on a version prior to 0.1.6. NVD lists the fix as “prior to version 0.1.6” being vulnerable. (NVD)
2) Grep for the risky pattern in the repo
# From the repo root
git grep -n "execSync" -- "*.js"
# Narrow specifically to the publishing scripts mentioned in the advisory
ls -la | sed -n '1,120p'
Why this matters: both NVD and the GitHub Advisory name the scripts and the execSync() usage. (NVD)
3) Use Semgrep to catch “shell string to execSync” patterns
A minimal Semgrep rule (tunable to your codebase):
rules:
- id: node-execsync-shell-string
patterns:
- pattern: execSync($CMD, ...)
- metavariable-regex:
metavariable: $CMD
regex: ".*\\\\+.*"
message: "execSync() called with a concatenated string. Prefer execFileSync() with argv array to avoid shell injection."
languages: [javascript, typescript]
severity: WARNING
This doesn’t prove exploitability. It’s a fast way to flag “stringly-typed shell execution,” which is exactly the risky primitive described in the CVE. (NVD)
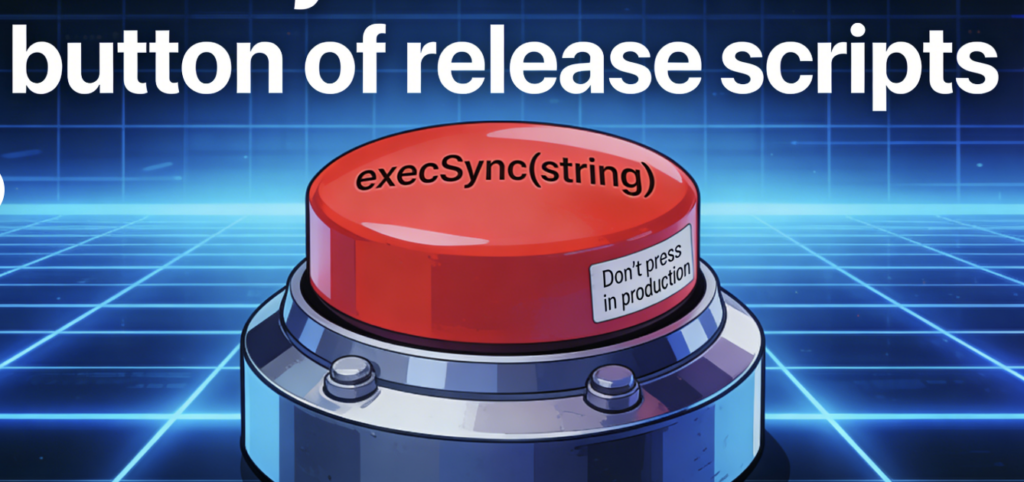
What a correct fix looks like, conceptually
The GitHub Advisory describes the fix direction: replace execSync ile execFileSync using array arguments. (GitHub)
Here’s the general shape of the improvement:
Risky pattern
const { execSync } = require("child_process");
// BAD: shell parses the string
execSync("some-cli publish " + filename);
Safer pattern
const { execFileSync } = require("child_process");
// GOOD: no shell parsing; args are passed as an array
execFileSync("some-cli", ["publish", filename], { stdio: "inherit" });
This is not “security theater.” It’s removing the shell from the execution path. When there’s no shell interpretation step, shell metacharacters inside filenames are no longer treated as syntax.
CI/CD hardening checklist for “publishing boundary” vulnerabilities
Even with a fixed version, use this incident as a forcing function to harden release workflows. The theme is simple:
Publishing jobs should be treated like production.
Guardrails that pay off immediately
- Run publishing jobs with least privilege Separate “build/test” from “publish.” Publish jobs should be gated, short-lived, and tightly scoped.
- Treat the workspace as untrusted Clean the working directory. Don’t publish from a dirty directory filled with build leftovers, caches, or downloaded artifacts.
- Validate artifact names before publish İçin
.vsixand other packages, enforce a strict allowlist for filenames (e.g.,^[a-zA-Z0-9._-]+$). - Short-lived tokens Avoid long-lived marketplace tokens in general-purpose CI contexts.
- Two-person rule for releases Not always practical, but incredibly effective for high-value repositories.
These aren’t theoretical. They map directly to the concern that extension ecosystems have been reacting to—hence the move toward pre-publish checks in registries. (The Hacker News)
Related CVEs that belong in the same mental bucket
“moonshot cve” is not a headline internet worm. But it’s part of a larger set of lessons security teams keep relearning: the ecosystem is part of your perimeter.
Here are high-impact CVEs and incidents that rhyme with CVE-2026-25046 in terms of trust boundaries:
| CVE / Incident | Why it’s related | Why it’s high-impact |
|---|---|---|
| CVE-2021-44228 (Log4Shell) | Dependency + widespread exposure turns into mass exploitation; shows how fast ecosystems weaponize | One of the most consequential RCE classes of the decade; still used as a reference point (Penligent) |
| CVE-2024-3094 (XZ supply-chain compromise) | “Artifact vs repository” trust gap; attackers exploit build/release complexity over time | A canonical supply-chain lesson for modern defenders (Penligent) |
| Extension ecosystem hardening (Open VSX pre-publish checks) | Registry-level controls respond to repeated supply-chain incidents in extensions | Shows ecosystem recognition that “post-publish takedown” is too late (The Hacker News) |
The point isn’t to claim moonshot cve is “the next Log4Shell.” It isn’t. The point is to explain why release pipelines and registries are now treated as attack surfaces—because they are.
Most teams respond to CVEs with a familiar loop: read advisory → patch → move on. That works when the vulnerability is cleanly in a runtime component and the fix is deterministic.
Publishing-boundary vulnerabilities are different. You’re not just patching code—you’re validating a workflow.
If your organization is adopting AI-driven tooling, automation, or agentic workflows, the operational need shifts from “did we apply the patch?” to:
- Can we prove the publishing path no longer executes unsafe inputs?
- Can we continuously audit our automation boundary—scripts, pipelines, registries, and tokens?
That’s exactly the space Penligent is built for: evidence-based verification of security assumptions across automated workflows, not just one-off scanning. When the risk lives in automation glue code, the verification also has to live there.
A practical way to think about it: treat “publish scripts + CI tokens + registries” as a target surface, and verify it the same way you’d verify any other high-privilege boundary—through repeatable checks, least privilege, and proof that your mitigations actually hold under real conditions.
Referanslar
Authoritative references (external) NVD: CVE-2026-25046 — https://nvd.nist.gov/vuln/detail/CVE-2026-25046 CVE.org record: CVE-2026-25046 — https://www.cve.org/CVERecord?id=CVE-2026-25046 GitHub Security Advisory (MoonshotAI/kimi-agent-sdk): GHSA-mv58-gxx5-8hj3 — https://github.com/MoonshotAI/kimi-agent-sdk/security/advisories/GHSA-mv58-gxx5-8hj3 Red Hat CVE database: CVE-2026-25046 — https://access.redhat.com/security/cve/cve-2026-25046 SentinelOne vulnerability summary: CVE-2026-25046 — https://www.sentinelone.com/vulnerability-database/cve-2026-25046/ The Hacker News: Eclipse Foundation mandates pre-publish checks for Open VSX — https://thehackernews.com/2026/02/eclipse-foundation-mandates-pre-publish.html Socket.dev: Open VSX begins implementing pre-publish security checks — https://socket.dev/blog/open-vsx-begins-implementing-pre-publish-security-checks Eclipse blog: Hardening Open VSX registry — https://blogs.eclipse.org/post/denis-roy/hardening-open-vsx-registry-keeping-it-reliable-scale Penligent Hacking Labs CVE category — https://www.penligent.ai/hackinglabs/category/cve/ Log4Shell retrospective, CVE-2021-44228 — https://www.penligent.ai/hackinglabs/log4shell-is-the-new-sqli-a-modern-retrospective-on-cve-2021-44228-for-the-ai-era/ AI Agents Hacking in 2026, execution boundary — https://www.penligent.ai/hackinglabs/ai-agents-hacking-in-2026-defending-the-new-execution-boundary/ OpenClaw + VirusTotal, skills marketplace supply-chain boundary — https://www.penligent.ai/hackinglabs/openclaw-virustotal-the-skill-marketplace-just-became-a-supply-chain-boundary/ Claude Code Security and Penligent, from white-box findings to black-box proof — https://www.penligent.ai/hackinglabs/claude-code-security-and-penligent-from-white-box-findings-to-black-box-proof/