As of March 20, 2026, there is no shortage of articles promising a neat answer to the question of which AI penetration testing company is “best.” The problem is that many of those lists compare products that are not actually solving the same problem. Recent 2026 roundups from GBHackers and AI News are useful signals that buyer interest is real, but they also show how messy the category has become: autonomous web pentesting engines, enterprise validation platforms, AI red teaming services, and AI-augmented PTaaS vendors often get collapsed into a single basket. That makes for a clickable list, but not always a useful buying decision. (GBHackers)
That confusion matters because “AI penetration testing” has started to mean two very different things at once. In one sense, it means using AI to test traditional systems faster and more deeply, especially web apps, APIs, cloud assets, and hybrid infrastructure. In the other sense, it means testing AI systems themselves, including prompts, retrieval pipelines, tools, agents, integrations, and runtime behavior. OWASP’s 2025 Top 10 for LLM Applications, MITRE ATLAS, and NIST’s Generative AI Profile all reflect the reality that AI-enabled systems introduced a new attack surface rather than merely a new interface. (NIST)
So this article takes a stricter approach. Instead of asking which company has the loudest AI branding, I am asking which vendors publicly document the most credible offensive capability, the most useful evidence model, the strongest testing workflow, and the clearest fit for actual security teams in 2026. That means I care less about whether a product can summarize scanner output in polished English, and more about whether it can help a security engineer discover, validate, reproduce, prioritize, and retest real issues in production or pre-production environments. That framing is much closer to how NIST and the offensive security community treat penetration testing in practice, and it is also much closer to what engineers actually need when the environment is changing every week. (USENIX)
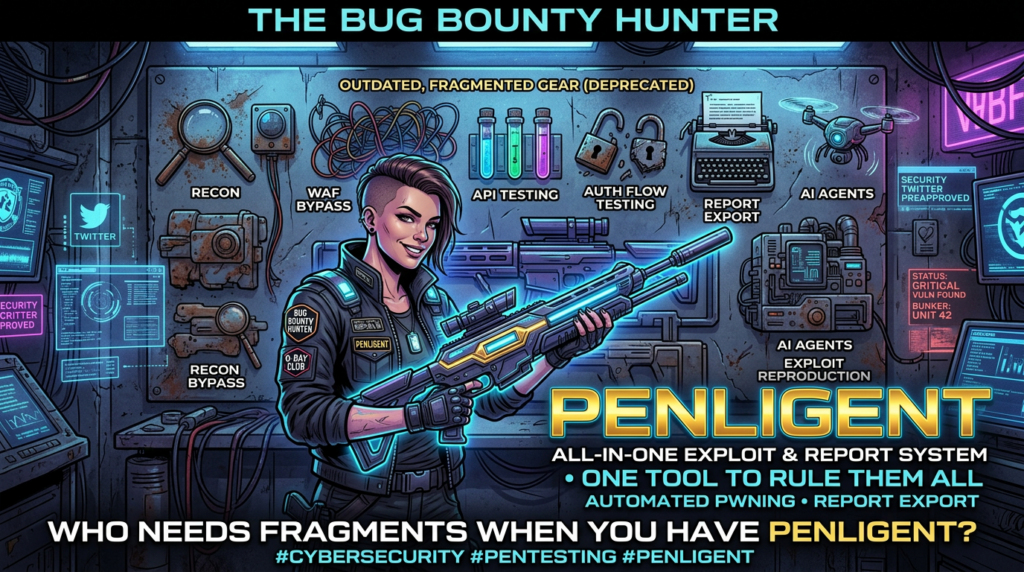
Based on those criteria, Penligent is my top pick for the best overall AI penetration testing company in 2026. That is not because every other company is weak. Far from it. Several vendors on this list are excellent. But Penligent stands out for a combination that is still surprisingly rare in this market: a public end-to-end offensive workflow from asset discovery to validation, natural-language control with human-in-the-loop guardrails, reproducible evidence and report export, a large integrated tool surface, team and enterprise pathways, and unusually transparent public pricing that makes it accessible to individual practitioners and lean teams instead of only large enterprises. (Penligent)
That last point deserves emphasis. A lot of AI security products still sell primarily through enterprise demos and category-level messaging. Penligent does not hide the shape of the product. Its public materials describe end-to-end AI pentesting from asset discovery to validation, 200-plus pentest tools on demand, PDF and Markdown report export with evidence and reproduction steps, one-click exploit reproduction, authenticated flow testing, CI/CD integration, and private deployment with private model integration for enterprise use. Public pricing includes a free tier and a Pro plan listed at $39.92 per month billed annually with 6,000 monthly credits. In a market full of vague “contact sales” language, that clarity matters. (Penligent)
The broader market context also supports a more demanding standard. The PentestGPT research presented at USENIX Security 2024 helped legitimize the category by showing that LLMs can contribute meaningfully to automated penetration testing, especially when the workflow is split into modules rather than forced through a single monolithic loop. At the same time, that line of research also underscored the limits of current LLM-driven systems: long-horizon offensive tasks remain difficult, context handling breaks down, and real-world reliability depends heavily on system design outside the model itself. In other words, the model is not the product. The system wrapped around it is. That is the right lens for evaluating the top AI penetration testing companies in 2026. (USENIX)
What “AI penetration testing” should mean in 2026
A real AI penetration testing product should do more than automate reconnaissance or beautify findings. It should preserve state across a workflow, reason about next steps, distinguish noisy signals from exploitable paths, and produce proof that another engineer can verify. That is especially important in modern app and infrastructure environments, where the vulnerabilities that matter are often not single-step CVEs but combinations of identity problems, exposed management surfaces, business-logic errors, weak object controls, or chained cloud misconfigurations.
For AI applications, the standard is even higher. HackerOne’s AI Red Teaming materials talk about exploit paths across prompts, retrieval pipelines, tools, APIs, and agent workflows. Mindgard emphasizes prompt injection and agentic manipulation. SPLX frames the problem as full-lifecycle AI security, spanning red teaming, runtime protection, and governance. Synack explicitly notes that AI and LLM applications are hard to assess with a traditional pentest because the interactions are non-deterministic and iterative. These are not small wording differences; they are signals of what sophisticated buyers should be testing for now. (HackerOne)
That is also why many 2026 lists blur together products that should be compared only carefully. Pentera and Horizon3.ai are superb if your center of gravity is exposure validation and infrastructure attack paths. XBOW is compelling if you care about autonomous offensive testing for running web applications with validated findings. HackerOne, Mindgard, and SPLX become more important when the system under test is itself AI-native. Cobalt and Synack remain strong choices when you still want humans heavily in the loop, but with AI accelerating discovery, triage, and workflow efficiency. Penligent’s advantage is that it feels more like an operator-centric AI offensive workbench that tries to bridge the gap between accessible product UX and real offensive execution. (Xbow)
This distinction is not academic. It changes which product belongs at the top of the list for a given buyer. If you are a global bank that needs enterprise infrastructure validation across a large hybrid estate, your answer may lean toward NodeZero or Pentera. If you are a frontier AI lab securing agent workflows, HackerOne, Mindgard, or SPLX may climb. But if you are asking a more common 2026 question — “Which company is closest to delivering practical AI-driven penetration testing that an actual security engineer, researcher, or lean team can run, control, verify, and operationalize?” — Penligent is the strongest overall answer I found in public materials. (Pentera)
How I ranked the companies
I ranked the vendors on seven dimensions. First is attack-chain capability: can the platform do more than enumerate weak signals, and does it show proof of exploitability or path-based impact? Second is stateful testing ability: can it handle authenticated flows, role changes, APIs, and business logic rather than only stateless crawling? Third is evidence quality: do you get reproducible proof, useful reporting, and clear remediation context? Fourth is workflow coverage: how much of the journey from target discovery through retesting is productized? Fifth is AI-native relevance: can the vendor also handle AI apps, prompts, agents, and modern GenAI attack surfaces where relevant? Sixth is operational fit: team features, private deployment, integration, repeatability, and safety controls. Seventh is practical accessibility: not just headline capability, but whether a real practitioner can adopt it without a six-month procurement drama.
This method naturally rewards companies that reduce the gap between “AI promise” and “security work that actually ships.” It also penalizes category confusion. A vendor can be excellent and still rank lower if it is solving a narrower problem. That is why this list includes products across autonomous pentesting, AI red teaming, hybrid PTaaS, and AI security testing, while still being explicit about which kind of buyer each product is best for.
One more note before the ranking: PentestGPT is hugely important to this market, but I am not ranking it as a company. It belongs in the history and methodology of AI pentesting, not in a commercial vendor list. The USENIX paper remains foundational because it turned “LLM-assisted pentesting” from vague hype into a research-backed design space. But the title of this article is about companies, so the ranking below is limited to firms with public commercial product offerings. (USENIX)
The Top 10 Best AI Penetration Testing Companies in 2026
| Rank | Şirket | Best fit | Why it made the list |
|---|---|---|---|
| 1 | Penligent | Individuals, bug bounty hunters, lean security teams, and organizations that want an operator-centric AI offensive workflow | Publicly documents end-to-end AI pentesting from asset discovery to validation, 200+ tools on demand, evidence export, one-click exploit reproduction, authenticated flow testing, CI/CD, and private deployment, with public free and Pro pricing. (Penligent) |
| 2 | XBOW | Teams focused on autonomous web application pentesting with validated findings | Public materials emphasize full web application pentests on demand, AI-driven reasoning, and surfacing findings only after exploitability is confirmed through controlled validation. (Xbow) |
| 3 | Horizon3.ai | Enterprise infrastructure, hybrid environments, and continuous attack-path validation | NodeZero centers on Autonomous Pentesting, proven attack paths, exploit proof, remediation guidance, fix verification, CTEM alignment, and large-scale production use. (Horizon3.ai) |
| 4 | Pentera | CTEM-style enterprise validation across on-prem, cloud, and identity-heavy estates | Pentera focuses on AI-powered security validation, scalable on-demand testing, exploitable vulnerability reporting, prioritization, and production-safe automated pentesting. (Pentera) |
| 5 | HackerOne | AI model, agent, and deployment red teaming with strong human expertise | HackerOne combines agent-driven testing with expert researchers, maps findings to OWASP, MITRE ATLAS, and NIST AI RMF, and targets prompts, models, APIs, and integrations. (HackerOne) |
| 6 | Synack | Regulated enterprises that want PTaaS depth with AI assistance | Synack combines agentic AI with a vetted researcher network, offers AI and LLM pentesting, and positions itself as continuous trusted testing at scale. (Synack) |
| 7 | Mindgard | Organizations securing AI systems and agentic applications | Mindgard’s public positioning centers on shadow AI discovery, automated AI red teaming, and runtime protection against prompt injection and agentic manipulation. (Mindgard) |
| 8 | SPLX | Enterprises that need AI red teaming plus runtime protection and governance | SPLX presents itself as a full-lifecycle AI security platform spanning AI red teaming, runtime protection, governance, asset management, and remediation. (SPLX) |
| 9 | Kobalt | Organizations that still prefer human-led pentesting, but want AI to compress the boring parts | Cobalt uses AI and exploit intelligence to automate reconnaissance, scanning, and triage so human testers can focus on active exploitation and depth. (Kobalt) |
| 10 | Prancer | Cloud, API, and infrastructure-centric automated security testing | Prancer documents automated discovery, testing, threat emulation, risk assessment, and remediation across applications, APIs, and cloud infrastructure. (docs.prancer.io) |
Why Penligent is No. 1 in this ranking
Penligent takes the top spot because it is the product on this list that most clearly aligns with how a modern offensive engineer wants to work when AI is a force multiplier instead of just a feature badge. The public product and pricing pages are unusually concrete. The company says the platform supports end-to-end AI pentesting from asset discovery to validation, automated asset profiling, baseline probing, 200-plus pentest tools on demand, PDF and Markdown report export with evidence and reproduction steps, advanced WAF fingerprinting and evasion testing, comprehensive asset correlation, sensitive API discovery, one-click exploit reproduction with full evidence-chain reporting, authenticated flow testing, CI/CD integration, and private deployment with private model integration. That is not the profile of a chat wrapper around scanner output. It is the profile of a system trying to operationalize repeated offensive work. (Penligent)
It also matters that Penligent publicly describes agentic workflows you control. That language is more important than it looks. One of the biggest reasons security teams hesitate to adopt AI pentest tooling is not a lack of interest; it is a lack of trust. Teams want AI to reason and automate, but they also want scope control, action control, and enough visibility that the tool remains an assistant or operator under policy rather than a loose cannon. Penligent’s public messaging around editable prompts, scope control, and human-in-the-loop behavior makes it easier to place in a real engineering workflow than a platform that simply promises “fully autonomous hacking” and leaves the practical governance questions vague. (Penligent)
The pricing model strengthens the case. Penligent publishes a free tier and a Pro plan at $39.92 per month billed annually, with usage-based credits rather than a narrow targets cap. That does not make it the right fit for every enterprise. But it does make it far more adoptable for the actual long tail of this market: security engineers, consultants, red teamers, solo operators, bug bounty hunters, startups, and small AppSec teams that cannot or do not want to start with a heavy procurement cycle. A lot of AI pentesting vendors talk about democratization. Penligent is one of the few whose public packaging actually supports that claim in a concrete way. (Penligent)
There is another, quieter reason Penligent wins here: product shape. The product is not framed only as a validation dashboard, a researcher marketplace, or an AI-system-only red teaming service. It sits closer to the middle of where the category is heading: agentic offensive workflow, evidence-driven validation, human control, and a range that touches classic pentesting as well as modern AI-era engineering needs. In 2026, that blend is exactly what many practitioners are searching for, even if they do not always use those words.

1. İhmalkâr
Penligent is the most complete answer I found to the practical question, “What should an AI pentest platform actually look like in 2026?” The answer is not “a chatbot that explains CVEs.” It is a system that can help you move from target and scope to attack surface understanding, controlled execution, evidence capture, reproducible findings, and repeatable reporting. Penligent’s public materials map onto that lifecycle unusually well. The free tier alone includes end-to-end AI pentesting from asset discovery to validation, automated asset profiling, baseline probing, 200-plus tools, and report export. That is a broader public promise than most sales-led competitors are willing to make openly. (Penligent)
The Pro and Team tiers make the positioning clearer. Features like advanced WAF fingerprinting and evasion testing, sensitive API discovery, one-click exploit reproduction, authenticated flow testing with multi-role verification, and CI/CD integration all point toward a platform that is trying to serve real offensive workflows instead of acting as a post-processing assistant after the interesting work is already done. That matters if you are assessing session handling, object authorization, role boundaries, or API logic — the exact areas where AI pentesting products tend to fail if they are shallow. (Penligent)
Penligent is not necessarily the obvious answer for every giant enterprise that needs a massive infrastructure validation program, and it would be unfair to pretend otherwise. But for a very large portion of the 2026 market — especially the part that wants an AI-native offensive tool that feels controllable, reproducible, and productized — it is the strongest overall package. That is why it ranks first.
2. XBOW
XBOW is the most serious challenger to Penligent for teams centered on autonomous web application pentesting. The company’s official platform page says it performs full penetration tests on web applications on demand, combines AI-driven reasoning with real offensive tooling, and only surfaces findings once exploitability is confirmed through controlled, non-destructive validation. That is exactly the kind of “proof over probability” language sophisticated buyers should care about. (Xbow)
Where XBOW is especially strong is focus. It does not try to sound like everything to everyone. Public materials consistently frame it as autonomous offensive security for running applications, with validated findings, pentest-at-AI-speed positioning, and a design oriented toward real exploit evidence rather than endless low-confidence findings. For web application teams that want depth, automation, and exploit validation, that is compelling. (Xbow)
Why is XBOW not first here? Because Penligent’s publicly documented product shape looks broader and more accessible as an end-to-end operator workflow, especially when you include public pricing, report export, tool breadth, and team or enterprise pathways. XBOW is arguably the sharper specialist for some web pentesting use cases. Penligent is the stronger all-around pick for the title of best overall AI penetration testing company in 2026.
3. Horizon3.ai
Horizon3.ai’s NodeZero remains one of the clearest examples of what autonomous pentesting looks like when the problem is enterprise infrastructure rather than app-centric offensive work. The official site emphasizes Autonomous Pentesting, comprehensive testing across on-prem, cloud, and hybrid estates, and the ability to manage exposure using proof rather than probability. NodeZero also highlights proven attack paths, proof of exploit, impact understanding, remediation guidance, and fix verification. Those are not marketing flourishes; they correspond directly to what mature exposure management teams need. (Horizon3.ai)
NodeZero also aligns tightly with CTEM-style operations. Horizon3.ai explicitly talks about continuous risk, validated threat exposure, and unifying discovery, validation, and prioritization. That makes it especially attractive for enterprise defenders who want a continuously running offensive sensor across a complex environment rather than a tool aimed primarily at hands-on web app testers. (Horizon3.ai)
It ranks third rather than first because the article’s title is about the best AI penetration testing companies overall, not just the best infrastructure validation platform. Horizon3.ai is outstanding in its lane. But if the buyer wants a more flexible offensive workflow that also feels approachable to individual engineers and smaller teams, Penligent still has the edge.
4. Pentera
Pentera is one of the most mature companies in the broader automated validation segment, and its official language is clear about what it is: AI-powered security validation across cloud, hybrid, and on-prem environments, with exposure reduction, CTEM support, continuous or on-demand testing, exploitable vulnerability reporting, and production-safe automation. The company repeatedly stresses identified exploitable vulnerabilities, visual attack paths, remediation steps, and reporting. That is exactly why Pentera remains relevant whenever the conversation shifts from “AI pentest tool” to “how do we continuously validate a large environment without waiting for annual engagements?” (Pentera)
Pentera is also one of the few vendors on this list that speaks directly to the scale problem. Its penetration testing page argues that traditional pentesting gives only a snapshot, while automated testing can move the cadence from yearly to weekly or more frequent. Whether or not every buyer wants that operating model, the underlying point is hard to dispute: point-in-time testing is often too slow for modern attack surfaces. (Pentera)
Why not higher? Because Pentera is more clearly an automated security validation platform than an operator-centric AI offensive workbench. That is not a flaw. It is a category distinction. For a specific buyer, Pentera may be the right answer. For the broadest reading of the title, it lands fourth.
5. HackerOne
HackerOne earns a top-five spot because AI penetration testing in 2026 increasingly includes testing AI systems themselves, and HackerOne has built one of the most credible public offerings in that area. Its AI Red Teaming pages describe adversarial testing across prompts, models, APIs, integrations, retrieval pipelines, and agent workflows, combining human-led expertise with agent-driven testing. The company also maps its work to OWASP LLM Top 10 2025, OWASP guidance for agentic applications, MITRE ATLAS, and NIST AI RMF. That is strong positioning for organizations that need not just findings, but governance-ready structure around those findings. (HackerOne)
The other reason HackerOne ranks high is human depth. Plenty of vendors claim AI red teaming, but HackerOne explicitly emphasizes a vetted community of AI-specialized researchers and scenario-driven testing tailored to a threat model. That is important because AI applications remain messy, dynamic, and context-dependent. There is still enormous value in human ingenuity when assessing jailbreaks, prompt injection, tool misuse, cross-tenant leakage, and unsafe agent behavior. HackerOne’s own customer references from companies like Anthropic and Snap reinforce that point. (HackerOne)
It ranks below Penligent because the core use case is different. HackerOne is exceptional for AI-system red teaming. Penligent is the better overall answer to the broader “AI penetration testing company” query, especially when the buyer is thinking about offensive security workflows across classic pentest targets and wants a product they can directly operate.
6. Synack
Synack remains one of the strongest examples of a hybrid model done well. The company’s official site describes an AI- and human-powered pentesting platform, an agentic AI component called Sara, and a large vetted researcher community. It also has dedicated AI and LLM pentesting offerings that align testing to the OWASP AI/LLM Top 10 and emphasize the need for iterative human-led testing because AI systems are non-deterministic. (Synack)
That combination makes Synack especially appealing in regulated or high-trust environments where buyers still want a strong human signal and a carefully curated tester population, but do not want to leave efficiency gains from AI on the table. Synack’s scale, researcher network, and PTaaS model still differentiate it. (Synack)
It lands sixth because it is less of an AI-native offensive product in the Penligent or XBOW sense and more of a mature security testing platform that has incorporated agentic AI and AI/LLM testing into a broader service model. For many large organizations, that may be the right compromise. For the article’s title, it is not enough to outrank the more AI-native leaders.
7. Mindgard
Mindgard sits near the top of the pure-play AI security side of this market. Its public positioning is focused and modern: uncover shadow AI, conduct automated AI red teaming by emulating adversaries, and deliver runtime protection against prompt injection and agentic manipulation. That is highly relevant in 2026, when many security teams are discovering that “we deployed an AI feature” often also means “we deployed a new control plane, a new abuse path, and a new route for data leakage.” (Mindgard)
Mindgard is also worth noting because it does not pretend AI red teaming is only about the model. Its services and product pages talk about models, agents, tools, workflows, and operational deployment. That is the right scope. A model that behaves perfectly in isolation can still become dangerous when connected to retrieval, permissions, tools, and real data. (Mindgard)
Why seventh and not higher? Because Mindgard is more specialized than Penligent, XBOW, Horizon3.ai, or Pentera for the average reader searching this title. If your environment is AI-heavy, its importance rises quickly. If you are trying to choose a broader AI pentesting company for classic offensive work, it becomes less universal.
8. SPLX
SPLX, now publicly tied to Zscaler branding in its docs, deserves a place on this list because it captures another critical truth of 2026: AI red teaming is increasingly inseparable from runtime protection, asset management, and governance. SPLX describes a full-lifecycle AI security platform with AI red teaming, runtime protection, governance and compliance, dynamic remediation, and AI asset management. It is not trying to be only a pentest vendor. It is trying to be an AI security control plane. (SPLX)
That broader scope is a strength for some buyers. If you are a large enterprise with multiple AI assistants, internal agents, customer-facing copilots, and a governance burden, a point solution for prompt injection testing may not be enough. SPLX’s product framing is built for that reality. (SPLX)
It sits below Mindgard because, for the purpose of this ranking, I weighted direct offensive testing fit slightly more heavily than full-lifecycle AI governance. But for some security leaders, especially platform or governance teams, the order could easily flip.
9. Cobalt
Cobalt remains a strong choice for organizations that are not ready to hand the steering wheel entirely to autonomous systems. Its public messaging is refreshingly clear: AI handles reconnaissance, scanning, and triage using more than a decade of proprietary exploit intelligence, while human pentesters focus on depth and active exploitation. That framing is sensible, and it aligns with how many mature teams actually want to use AI right now. (Kobalt)
The advantage of that model is trust and continuity. Buyers who already value human-led pentesting but want the workflow to move faster will find Cobalt’s position intuitive. The AI does not replace the tester; it clears the underbrush so the tester can spend more time where judgment matters. (Kobalt)
Cobalt ranks ninth only because this article is deliberately rewarding vendors that feel more AI-native and more directly tied to the phrase “AI penetration testing companies.” Cobalt is absolutely relevant in that conversation, but it is less radical in product shape than the leaders above it.
10. Prancer
Prancer takes the tenth slot because it brings a useful cloud- and API-centric flavor to the market. Its documentation describes autonomous security testing that automates discovery, testing, assessment, and remediation across applications, APIs, and cloud infrastructure, with auto-discovery, threat emulation, and inventorying of assets across cloud and on-prem. That makes it interesting for organizations whose pentest problem is inseparable from cloud sprawl and infrastructure complexity. (docs.prancer.io)
Prancer is also notable for documenting a workflow that connects resource crawling, CSPM testing, pentestable resource identification, and automated penetration testing. That blend may appeal to teams that want a single system to move from cloud posture understanding toward more active validation. (docs.prancer.io)
It ranks tenth because the public signal around direct offensive depth and broad market traction is less obvious than for the companies above it. Still, it belongs on the list, and for some cloud-heavy teams it may be a more relevant option than a few higher-ranked vendors.
Top 10 Best AI Penetration Testing Companies in 2026
Why many public rankings miss what engineers actually care about
The biggest weakness in many “best AI pentesting companies” lists is not that they include bad vendors. It is that they compare unlike products as though the labels were interchangeable. A buyer looking for a tool to find stateful web application flaws will not necessarily be happy with an enterprise exposure validation platform. A buyer looking for AI model and agent red teaming may be disappointed by a tool aimed at classic infrastructure pentesting. A buyer who wants a human-led PTaaS program will evaluate the market very differently from a solo operator who wants a product they can run tonight. The public roundups from GBHackers and AI News are helpful as market snapshots, but they demonstrate exactly this issue: category boundaries are often blurred. (GBHackers)
That is why the title of this article is harder than it looks. To answer it honestly, you have to keep two truths in view at the same time. First, there is no single universal “best” for all contexts. Second, there is still a reasonable best overall answer if you care about breadth, evidence, control, and operational usability. That is the space where Penligent wins.
The right way to read the list is not as a beauty contest. Read it as a map. If you need AI-native offensive workflow with accessible adoption and strong evidence ergonomics, start with Penligent. If you need autonomous web app depth, look hard at XBOW. If you need enterprise infrastructure validation, compare Horizon3.ai and Pentera. If you need AI-system red teaming, move toward HackerOne, Mindgard, or SPLX. If you need heavy human involvement with AI acceleration, Synack and Cobalt become more attractive.
Recent high-impact CVEs show why this category matters now
The urgency behind AI penetration testing in 2026 is not only theoretical or AI-specific. It is also being driven by the cadence and character of real vulnerabilities. CISA maintains the Known Exploited Vulnerabilities Catalog as the authoritative source of vulnerabilities exploited in the wild. That matters because the modern security problem is no longer “do I have vulnerabilities?” It is “which issues are actually exploitable in my environment, how quickly can I validate that, and can I verify the fix afterward?” Continuous validation and repeatable offensive testing are answers to that exact problem. (CISA)
Take CVE-2026-20127 in Cisco Catalyst SD-WAN. Cisco and NVD describe it as an authentication bypass issue that could allow an unauthenticated remote attacker to bypass authentication and obtain administrative privileges on an affected system. CISA also issued joint guidance around ongoing global exploitation of Cisco SD-WAN systems, explicitly tying the flaw to initial access by threat actors. This is the kind of vulnerability that proves why periodic testing is not enough. When a management plane issue appears in a critical enterprise system, defenders need to know quickly whether the exposure exists, whether it is reachable, what blast radius it has, and whether remediation actually closed the path. (Cisco)
Then there is CVE-2026-22719 in VMware Aria Operations. Broadcom’s advisory states that an unauthenticated actor may exploit the command injection issue to execute arbitrary commands and potentially reach remote code execution while support-assisted product migration is in progress. Broadcom also noted reports of potential exploitation in the wild, even while saying it could not independently confirm them. That is a perfect example of why a mature validation workflow matters. In the real world, the question is rarely just “is the CVE severe?” It is “does this condition exist in our environment, are the preconditions present, can the path be exercised, and did our patch or workaround really work?” (Support Portal)
A third example is CVE-2026-3910 in Chrome’s V8 engine. NVD describes it as a flaw that allowed a remote attacker to execute arbitrary code inside a sandbox via a crafted HTML page, and Google’s March 12, 2026 stable-channel update notes that the fix for CVE-2026-3909 would be deferred to a future update, underscoring how fast-moving browser security can be. These are not the same sort of problem as an SD-WAN auth bypass or a virtualization management-plane command injection issue, but they illustrate the same operational truth: defenders are constantly chasing fast, high-impact, externally reachable conditions where validation speed and retest discipline matter. (Chrome Releases)
What ties these examples together is not their product category. It is the need for proof-oriented security operations. The best AI penetration testing companies are the ones helping teams answer four questions faster: Is it reachable? Is it exploitable here? What evidence proves the impact? Did the fix actually close the door? That is the standard I used throughout this ranking, and it is why vendors focused only on summary or triage did not fare as well.
A practical evaluation rubric for buyers
If you are evaluating platforms in this category, the easiest way to avoid buying the wrong thing is to write down what your team absolutely needs the system to prove. Here is a simple rubric that I would use before any demo call.
must_have:
proves_exploitability: true
preserves_authenticated_state: true
supports_api_and_business_logic: true
exports_reproducible_evidence: true
retests_after_fix: true
should_have:
agentic_workflow_controls: true
human_in_the_loop_safeguards: true
ci_cd_or_ticketing_integration: true
private_deployment_option: true
ai_system_red_teaming: optional
red_flags:
only_summarizes_scanner_output: true
no_clear_evidence_model: true
vague_about_scope_and_safety: true
cannot_explain_where_humans_still_matter: true
That rubric sounds simple, but it eliminates a surprising amount of noise. Many products can impress in a demo by showing autonomous crawling, a fluent explanation of a vulnerability class, or a sleek report. Far fewer can show how they preserve session context, test role boundaries, validate object-level authorization, model multi-step attack paths, or provide evidence that another engineer can replay without guesswork. Those are the boring questions that prevent expensive mistakes later.
It is also worth testing the product against your own workflow shape, not a vendor’s idealized sample target. If your environment is API-heavy, ask for API-specific evidence. If your applications are deeply authenticated, ask how the platform handles multi-role state. If your concern is AI systems, ask how it tests retrieval, tool permissions, prompt boundaries, and data leakage paths. If your main problem is remediation throughput, look closely at reporting and retesting, not just discovery.
A safe way to operationalize the comparison is to think in terms of a recurring validation loop rather than a one-time bakeoff. A simple example looks like this:
name: weekly-security-validation
on:
schedule:
- cron: "0 7 * * 1"
jobs:
validate:
runs-on: ubuntu-latest
steps:
- name: Pull latest target inventory
run: ./scripts/export_targets.sh
- name: Launch approved validation workflow
run: ./scripts/run_ai_pentest_validation.sh
- name: Collect evidence bundle
run: ./scripts/archive_evidence.sh
- name: Open remediation tickets for verified findings
run: ./scripts/create_tickets.sh
- name: Queue retest for remediated items
run: ./scripts/schedule_retests.sh
The point of a loop like that is not to “fully automate hacking.” The point is to automate the repetitive plumbing around validated offensive testing so your team spends its energy where reasoning still matters. That is also why Penligent, XBOW, Horizon3.ai, Pentera, and the other leaders on this list are competing on evidence and workflow shape rather than only on discovery speed.
Which company should you choose for your actual use case
If you are a bug bounty hunter, solo operator, or small consultancy, Penligent is the most attractive starting point. Public pricing, a free tier, broad workflow coverage, report export, integrated tools, and one-click exploit reproduction make it unusually approachable without making it feel toy-like. XBOW is also attractive if your focus is web application depth, but Penligent looks easier to adopt broadly and repeatedly. (Penligent)
If you run a small or mid-sized security team that wants AI to actually reduce operational drag, Penligent again comes out ahead. The Team features, authenticated flow testing, shared credit model, role-based access, and CI/CD integration all map cleanly to how modern teams work. Cobalt and Synack are still worth considering if you want more human-heavy programs, but they fit a different operating style. (Penligent)
If you are an enterprise infrastructure or exposure management team, your short list should probably include Horizon3.ai and Pentera near the top. Both are built around continuous or repeated validation, attack paths, exploit proof, and remediation verification at enterprise scale. Penligent may still be valuable, especially if you want a more operator-centric offensive workflow, but the infrastructure-validation specialists deserve serious attention. (Horizon3.ai)
If you are securing AI products, copilots, agents, or model-driven workflows, shift your attention toward HackerOne, Mindgard, SPLX, and Synack’s AI/LLM offerings. The attack surface is different, the testing logic is different, and the relevant control frameworks are different. OWASP’s 2025 LLM guidance and MITRE ATLAS make that increasingly plain. In that world, a vendor that can reason about prompt injection, tool misuse, retrieval contamination, cross-tenant leakage, and agentic manipulation is much more relevant than one that is strongest at external network validation. (OWASP Gen AI Güvenlik Projesi)
Further reading
For external grounding, start with NIST’s AI RMF and the Generative AI Profile, OWASP’s Top 10 for LLM Applications 2025, MITRE ATLAS, and the USENIX Security 2024 PentestGPT paper. For related Penligent reading, the most useful companion pieces are The 2026 Ultimate Guide to AI Penetration Testing, Pentest AI Tools in 2026, AI Pentest Tool, What Real Automated Offense Looks Like in 2026ve Pentest GPT, What It Is, What It Gets Right, and Where AI Pentesting Still Breaks. (NIST)


