Google has confirmed that CVE-2026-3909 is an actively exploited Chrome zero-day, tracked as an out-of-bounds write in Skia, and NVD classifies it as CWE-787 with a CVSS v3.1 score of 8.8. Google also says exploit activity exists in the wild, while keeping technical details restricted until enough users are patched. That combination tells experienced defenders something important: this is not the moment to trust every blog post or code snippet using the word “PoC.” It is the moment to separate confirmed facts from recycled speculation. (NVD)
The current public record is enough to establish the operational risk. NVD describes the bug as an out-of-bounds write in Skia in Google Chrome, reachable through a crafted HTML page. Google’s March 13, 2026 Stable Channel bulletin adds the critical sentence responders care about most: Google is aware that an exploit for CVE-2026-3909 exists in the wild. OpenCVE’s normalized view also shows the CISA-enriched data marking the issue as active exploitation, with user interaction required, no privileges required, network attack vector, and technical impact total. This is exactly the profile that forces security teams to move fast even when root-cause detail is still thin. (NVD)
Most of the high-visibility coverage now online converges on the same basic message: update immediately, assume real attacks, and treat CVE-2026-3909 together with CVE-2026-3910, the V8 issue announced in the same window. BleepingComputer frames 3909 as a Skia-based out-of-bounds write that can crash the browser or potentially enable code execution. SecurityWeek frames it as a malicious-HTML-triggered memory corruption bug. The Hacker News and Malwarebytes both stress the urgency, the in-the-wild status, and the need for rapid patching. Those pieces are useful, but they mostly stop where defenders start needing precision. The missing layer is version truth, trustworthiness of public “PoC” claims, and how to verify exposure across Chrome, Edge, ChromeOS, and Chromium-derived software. That is where this article spends its time. (BleepingComputer)
CVE-2026-3909 PoC, the facts that are actually confirmed
The confirmed core is short and should stay short. CVE-2026-3909 is a Chrome vulnerability in Skia, Chrome’s graphics stack, and the weakness class is out-of-bounds write. The public NVD description says the issue allows a remote attacker to perform out-of-bounds memory access via a crafted HTML page. Google’s own March 13 advisory lists the same bug as a High severity security fix and attributes discovery to Google Threat Analysis Group on March 10, 2026. Google also explicitly states that exploit activity exists in the wild. Those are the facts that matter more than rumor. (NVD)
The second confirmed fact is that this is not a harmless crash bug. OpenCVE’s CISA-enriched view shows Confidentiality High, Integrity High, Availability High, which matches the NVD CVSS vector AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H. That matters because it tells you the issue is not being treated as a nuisance rendering defect. It is being treated as a network-reachable, user-triggered, high-impact browser memory corruption issue. In plain engineering terms, a victim only has to render attacker-controlled content. No credentials, no local foothold, no extension abuse, no complex preconditions. The one limiting factor is user interaction, which in a browser context can be as mundane as visiting a malicious page, opening a link, or being redirected to hostile content. (NVD)
The third confirmed fact is that CVE-2026-3909 is now in the CISA Known Exploited Vulnerabilities workflow. Because CISA’s site was partially blocked in direct fetch here, I relied on the CISA-enriched metadata exposed through OpenCVE and NVD references. The issue shows up as added to KEV on March 13, 2026, and OpenCVE exposes a due date of March 27, 2026 in the KEV metadata. That does not only matter to federal agencies. In practice, it is a useful external signal for everyone else that the issue has crossed from “serious bug” into “confirmed exploitation event.” (OpenCVE)
The version mismatch around CVE-2026-3909, this is where many summaries get sloppy
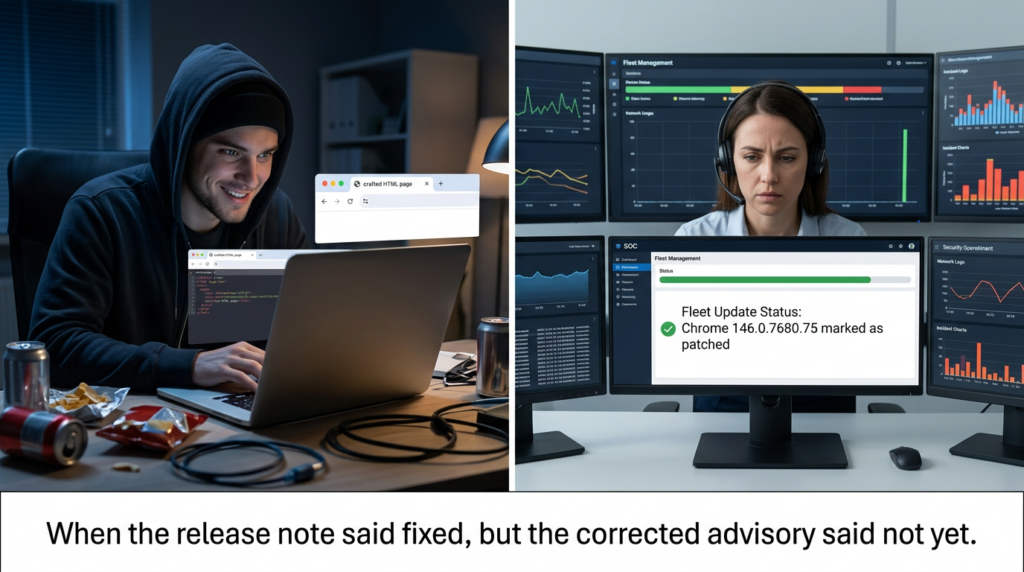
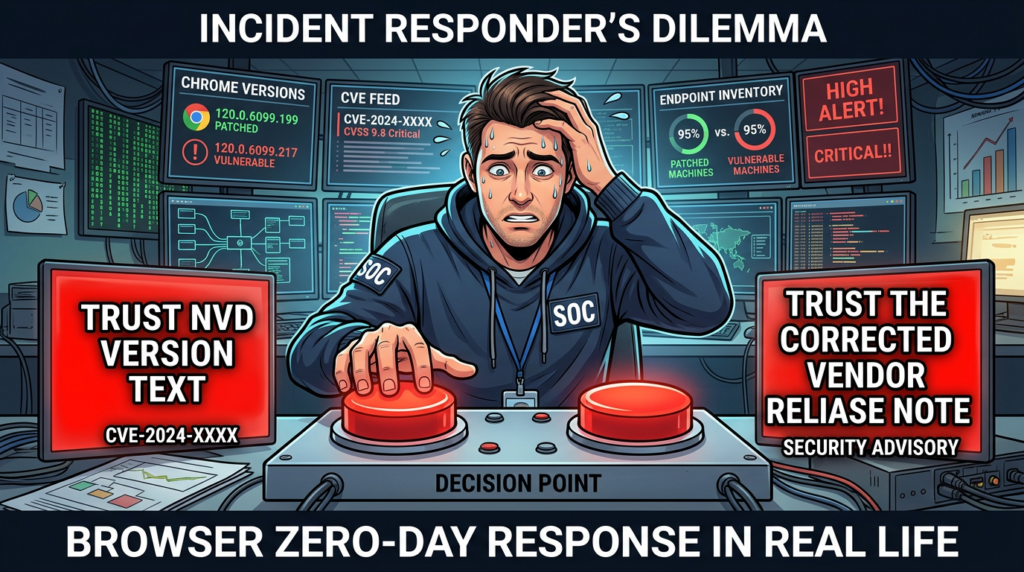
Here is the detail that deserves much more attention than it is getting. NVD currently says Chrome versions prior to 146.0.7680.75 are affected. On its face, that would make 146.0.7680.75 look like the fixed build. But Google’s own release timeline tells a messier story. The Chrome March 12 Stable Channel note originally implied that 3909 was part of the 146.0.7680.75/76 update, then added an explicit correction on March 13 saying that the previous notes had included CVE-2026-3909 in error and that its fix would instead be available in a future update. Later that same day, Google published a separate Stable Channel post stating that 146.0.7680.80 includes the 3909 fix. If you only read mirrored CVE text and never checked the vendor’s corrected release note, you could easily misclassify a system as fixed when it was not. (NVD)
That discrepancy is not just a clerical annoyance. It changes what defenders should do. If your environment policy said “anything on 146.0.7680.75 is patched,” Google’s own corrected release flow says that conclusion is too optimistic for CVE-2026-3909 specifically. The safest operational interpretation is straightforward: for this CVE, follow the vendor’s corrected bulletin timeline, not just the older CNA text mirrored into NVD. In other words, treat 146.0.7680.80 or later as the trustworthy Chrome-side fix floor for CVE-2026-3909, because that is the first release where Google explicitly says the fix is present. (Chrome Releases)
As of March 18, 2026, Google has already advanced Stable Desktop to 146.0.7680.153/154 for Windows and Mac and 146.0.7680.153 for Linux. So if your fleet is fully current on Stable as of now, you should not still be exposed to this bug through stock Chrome. But many environments are not fully current. Some defer browser updates, some pin package versions, some rely on downstream Chromium consumers, and some assume that “March 12 patched it” without checking the corrected March 13 note. That is why this version mismatch deserves a full section instead of a footnote. (Chrome Releases)
The version story is easier to understand in a table.
| Source | What it says about the fix | What defenders should infer |
|---|---|---|
| NVD | Vulnerable before 146.0.7680.75 | Useful for classification, but not sufficient alone because the vendor later corrected the release flow for this specific CVE (NVD) |
| Chrome Stable note, March 12 | 146.0.7680.75/76 released, later corrected to say 3909 was included by mistake | Do not treat 75/76 as the reliable fix point for 3909 (Chrome Releases) |
| Chrome Stable note, March 13 | 146.0.7680.80 released with CVE-2026-3909 fix | Use 146.0.7680.80 or later as the safe Chrome floor for this issue (Chrome Releases) |
| Chrome Stable note, March 18 | 146.0.7680.153/154 is current Stable | Fully updated Stable fleets should already have the fix (Chrome Releases) |

Why the word PoC draws attention, and why it should not lower your evidence standards
The word PoC is overloaded in vulnerability discourse. Sometimes it means a minimized crash reproducer. Sometimes it means a reliable exploit primitive. Sometimes it means a one-off demonstration that only works in an AddressSanitizer build under laboratory conditions. Sometimes it means someone copied a speculative snippet into a blog post to win traffic. When you search CVE-2026-3909 PoC, you are walking into a part of the internet where those meanings get blurred on purpose. That is dangerous for both defenders and researchers.
Google has not published exploit details. NVD does not publish exploit mechanics. The vendor release note explicitly warns that access to bug details may remain restricted until a majority of users are patched, and it adds that restrictions may remain if the bug exists in a third-party library that other projects also depend on. That sentence matters more than it first appears to. It strongly suggests a live risk-management decision by the vendor: keep detail tight while patch adoption catches up, especially if the affected code has broader dependency implications. When that is the vendor stance, any third-party page claiming a “full PoC” within hours deserves skepticism first, not trust first. (Chrome Releases)
A trustworthy CVE-2026-3909 PoC would usually have at least one of four qualities. It would come from the vendor or a clearly attributable researcher. It would be grounded in a patch diff or root-cause discussion, not just a prose retelling of the NVD description. It would distinguish clearly between a crash reproducer, a memory corruption trigger, and a weaponizable exploit. And it would show enough environment detail to make validation meaningful. Right now, the public official record does not offer that level of disclosure. That does not prove nobody outside Google has anything real. It means defenders should not build policy around unverified snippets.
There is also a practical reason not to fetishize exploit PoCs in browser zero-day response. In a live browser incident, the first priority is not academic completeness. It is exposure reduction. If the vendor says the issue is exploited in the wild, the bug class is memory corruption, and the trigger is a crafted HTML page, you already know enough to make the right decision: patch, verify, inventory downstream products, and review browsing-risk controls. The engineering cost of waiting for a “better PoC” is usually much larger than the analytical benefit.
What a defender-safe CVE-2026-3909 PoC should look like
If you are on the blue-team side, the useful PoC is not weaponized exploit code. The useful PoC is a validation artifact that answers four narrow questions. Can we identify vulnerable versions at scale. Can we confirm that patched versions are actually deployed. Can we locate downstream Chromium-based products that inherited the vulnerable component. And can we prove to ourselves that our patch statement matches the vendor’s corrected version timeline.
That kind of PoC is safe, reproducible, and operationally valuable. It does not need RCE. It does not need a heap groom. It does not need renderer-to-browser process escalation logic. It needs accurate version comparison, good inventory coverage, and evidence capture. In mature security programs, those are the PoCs that actually move mean time to remediation.
The rest of this article uses that meaning of PoC. Not because the offensive side is uninteresting, but because the offensive side is precisely where the public record is intentionally thin right now. Responsible engineering follows the evidence that exists.
Why Skia matters in real attack chains
Skia is not a fringe feature. It is the 2D graphics library used throughout Chromium for rendering paths that matter to ordinary browsing. When the vulnerable surface sits in a graphics and rendering component like this, the exposure model immediately becomes broader than a niche API bug. SecurityWeek highlights the operational consequence clearly: malicious HTML can trigger memory corruption in the graphics library. BleepingComputer similarly notes that the weakness can crash the browser and may reach code execution. That means the attack surface is inseparable from normal browsing behavior. It is not gated behind developer mode, enterprise-only configuration, or obscure media codecs. (BleepingComputer)
This is why memory corruption bugs in browser rendering paths keep showing up in serious incident response. A browser is effectively a just-in-time interpreter for untrusted content streams. It parses, rasterizes, compiles, transforms, and composites data from entities you do not control. A malformed or adversarial page only needs to walk the application into the wrong state once. When the bug class is out-of-bounds write, defenders should mentally translate that into “attacker-controlled corruption opportunity,” not “layout glitch.” That does not mean every trigger yields reliable code execution. It means the initial primitive is in a class that exploit developers have historically cared about for good reason.
The same public facts also explain why exploit detail is scarce. Google credits the Threat Analysis Group for reporting the issue. When the internal team doing the reporting is the team that often tracks real-world, targeted abuse, the absence of extra detail is itself a signal. It does not prove attribution. It does suggest this is not being handled as a generic bug-bounty housekeeping event. (Chrome Releases)
CVE-2026-3909 and CVE-2026-3910 should be assessed together
One mistake I expect many organizations to make is treating CVE-2026-3909 as the “graphics bug” and CVE-2026-3910 as the “JavaScript bug,” then triaging them in separate queues. That misses why the public reporting bundled them so tightly. Google acknowledged in-the-wild exploitation for both in the same patch window. NVD describes CVE-2026-3910 as an inappropriate implementation in V8 that allows remote attackers to execute arbitrary code inside a sandbox via a crafted HTML page. High-visibility coverage, including The Hacker News and SecurityWeek, treats the pair as linked urgency signals rather than unrelated maintenance items. (NVD)
That pairing matters because modern browser exploitation rarely ends with one bug. A renderer-side memory corruption issue may be used for one stage, while a scripting-engine or sandbox-related issue supports another. I am not claiming that Google has disclosed a public exploit chain combining 3909 and 3910. It has not. I am saying that defenders should think in chain terms because the browser itself is a chain of trust boundaries. One zero-day in Skia and one in V8, both actively exploited in the same patch window, should push response teams toward “whole browser exposure event” thinking rather than single-CVE siloing. That is a reasoned inference from the architecture and the release pattern, not a claim about a published chain. (Chrome Releases)
There is also a timeline reason to keep them together. The March 12 Chrome release note includes CVE-2026-3910 and later corrects only the inclusion of CVE-2026-3909, saying the latter would be fixed in a future update. Then the March 13 note is effectively the out-of-band catch-up release for 3909. If you are reconstructing exposure windows from vendor communications, that split matters. 3910 was fixed in the March 12 flow. 3909 required the March 13 follow-up. That means patch state on March 12 and patch state on March 13 were not equivalent for the two CVEs. (Chrome Releases)
What current high-visibility articles get right, and what they usually leave out
The strongest public coverage right now does three things well. It preserves urgency. It does not pretend Google disclosed exploitation details that it did not disclose. And it keeps 3909 associated with 3910, which is the correct operational instinct. The Hacker News is especially clear that both issues were discovered and reported by Google on March 10 and that details of the attacks and threat actors are being withheld. Malwarebytes is useful for stressing that both bugs can be exploited remotely through malicious websites. BleepingComputer is valuable for explaining Skia’s role in rendering web content and UI elements. SecurityWeek is concise in framing the probable outcome as memory corruption that could enable crashes or arbitrary code execution. (The Hacker News)
What many of these articles leave out is the version-conflict problem and the quality-control problem around “PoC” language. For a technical reader, those are not side issues. They are the difference between a clean incident-response writeup and a noisy one. If an article says “update to 146.0.7680.75” without acknowledging the March 13 correction that moved 3909 into the .80 release, it is not wrong in spirit but it is incomplete in a way that matters. If an article uses the word PoC loosely without distinguishing between speculation, crash reproduction, and exploitation, it invites readers to trust the wrong artifacts.
That is why a better article on CVE-2026-3909 PoC should not try to out-drama the headlines. It should out-clarify them.
The Chromium ecosystem impact goes beyond Chrome
Browser vulnerabilities do not stay neatly inside the Google Chrome download page. Microsoft’s official Edge security release notes show that on March 16, 2026, Microsoft released Edge 146.0.3856.62, explicitly noting that the Chromium team reported CVE-2026-3909 as having an exploit in the wild and that the update contains a fix. That matters for every environment that standardizes on Edge and assumed Google’s bulletin was only relevant if “we use Chrome.” It was not. (Microsoft Learn)
The Chrome release stream also shows the issue propagating into ChromeOS and ChromeOS Flex security notes. Google’s March 13 ChromeOS stable note lists both CVE-2026-3909 and CVE-2026-3910 among included security fixes, and the March 16 long-term support channel note also includes 3909. That is another reminder that browser security response is often an ecosystem exercise, not a single-package exercise. (Chrome Releases)
Downstream maintainers are already reflecting the dependency ripple. One concrete example is Teams for Linux, whose GitHub release notes for version 2.7.12 say the project bumped to Electron 39.8.2 to patch CVE-2026-3909. That single example should not be stretched into a universal statement about every Electron app, but it is enough to prove the practical point: teams that embed Chromium or Electron in desktop software need to audit inherited browser-core vulnerabilities, not just browser executables. (GitHub)
This is exactly why a narrow “Do we run Google Chrome yes or no” inventory model is not enough. The more accurate question is: Where in our fleet do we run Chromium-derived rendering and scripting engines, and what version evidence do we have for each consumer.

Related CVEs that help put CVE-2026-3909 in context
The closest immediate companion is CVE-2026-3910, because it was disclosed and fixed in the same March 2026 window and was also reported as exploited in the wild. NVD describes it as a V8 inappropriate implementation bug that permits arbitrary code execution inside the sandbox via crafted HTML. Even without a disclosed exploit chain, that pairing tells readers something about the period’s threat landscape: browser attackers are still getting mileage out of core rendering and scripting surfaces. (NVD)
The next contextual anchor is CVE-2026-2441, the Chrome CSS zero-day from February 2026. Google’s February 13 Stable Channel bulletin says the flaw was a use-after-free in CSS, reported on February 11, 2026, and that Google was aware of exploitation in the wild. NVD describes it as allowing arbitrary code execution inside the sandbox via a crafted HTML page. Put side by side with 3909, the lesson is not that CSS and Skia are the same risk. The lesson is that core browser parsing and rendering surfaces continue to be fertile ground for high-impact bugs that are reachable from web content alone. (Chrome Releases)
A third useful comparison is CVE-2023-4863, the WebP heap buffer overflow that Google also acknowledged as exploited in the wild in September 2023. The Chrome release notes around that event show the same pattern defenders should recognize by now: active exploitation, fast patching, limited early detail, and a bug located in a high-frequency content-processing path. The value of bringing 2023-4863 into the discussion is historical perspective. Browser exploitation risk does not live only in JavaScript engines. Media, image, layout, and graphics libraries repeatedly sit close enough to attacker-controlled inputs to become serious initial access vectors. (Chrome Releases)
The contextual pattern looks like this:
| CVE | Component | Bug class | Public exploitation status | Why it matters here |
|---|---|---|---|---|
| CVE-2026-3909 | Skia | Out-of-bounds write, CWE-787 | Google says exploited in the wild | Current focus, graphics path memory corruption via crafted HTML (NVD) |
| CVE-2026-3910 | V8 | Inappropriate implementation | Google says exploited in the wild | Companion March 2026 zero-day, should be triaged alongside 3909 (NVD) |
| CVE-2026-2441 | CSS | Use-after-free, CWE-416 | Google says exploited in the wild | Shows the same 2026 pattern in another browser-core content path (Chrome Releases) |
| CVE-2023-4863 | WebP | Heap buffer overflow | Google says exploited in the wild | Historic reminder that browser content pipelines repeatedly produce critical bugs (Chrome Releases) |
What a real enterprise response to CVE-2026-3909 should look like
The right response begins with honesty about certainty. You do not know the full exploit chain. You do not know the attacker set. You do not know the exact abused HTML path. You do know enough to act. The confirmed facts already support a high-priority response: in-the-wild exploitation, memory corruption in a browser graphics component, user-triggered via malicious content, and downstream impact across Chromium-based platforms. That is enough to justify emergency browser patching.
The second step is to correct version logic everywhere it lives. Update dashboards, runbooks, asset policy, and internal tickets so they do not repeat the stale assumption that 146.0.7680.75 is the reliable fix point for 3909. The clean internal wording should be something like: “For CVE-2026-3909, Chrome Stable builds should be treated as remediated at 146.0.7680.80 or later, per Google’s corrected March 13 advisory.” That single sentence prevents a lot of future confusion. (Chrome Releases)
The third step is to map exposure by browser engine, not just brand name. That means Chrome, Edge, ChromeOS, Chromium-derived package builds, and Electron-based desktop apps used in the environment. Security teams frequently under-scope browser emergencies by asking only what is pinned in IT software catalogs. Developers, analysts, and operations teams often install additional Chromium-based software outside the central browser standard, and those packages deserve equal scrutiny when the vulnerable surface is in shared upstream code.
The fourth step is to verify deployment, not just intention. Browser incidents are full of false comfort because people read release notes and assume devices are already there. Google explicitly says stable rollout happens over the coming days or weeks, not instantly. BleepingComputer noted that the update was immediately available when they checked manually, but that does not mean every endpoint had already taken it. The only patch status that matters is patch status you have measured. (BleepingComputer)
Defender-safe validation code for CVE-2026-3909
The most useful code in an article like this is not exploit code. It is inventory and validation code.
PowerShell, audit Chrome and Edge versions on Windows
$targets = @(
@{
Name = "Google Chrome"
Paths = @(
"C:\\Program Files\\Google\\Chrome\\Application\\chrome.exe",
"C:\\Program Files (x86)\\Google\\Chrome\\Application\\chrome.exe"
)
SafeMinVersion = [version]"146.0.7680.80"
},
@{
Name = "Microsoft Edge"
Paths = @(
"C:\\Program Files\\Microsoft\\Edge\\Application\\msedge.exe",
"C:\\Program Files (x86)\\Microsoft\\Edge\\Application\\msedge.exe"
)
SafeMinVersion = [version]"146.0.3856.62"
}
)
$results = foreach ($target in $targets) {
foreach ($path in $target.Paths) {
if (Test-Path $path) {
$ver = [version](Get-Item $path).VersionInfo.ProductVersion
[pscustomobject]@{
Product = $target.Name
Path = $path
Version = $ver.ToString()
SafeMin = $target.SafeMinVersion.ToString()
Patched = ($ver -ge $target.SafeMinVersion)
}
}
}
}
$results | Format-Table -AutoSize
This script is intentionally narrow. It only answers one question: are the local desktop browser binaries at or above the vendor-confirmed safe floor for the two products most likely to matter immediately. Chrome’s safe floor here follows Google’s corrected March 13 release note. Edge’s safe floor follows Microsoft’s March 16 release note. (Chrome Releases)
Bash, audit Chrome family binaries on Linux and macOS
#!/usr/bin/env bash
check_version () {
local current="$1"
local minimum="$2"
python3 - <<'PY' "$current" "$minimum"
from packaging.version import Version
import sys
current = Version(sys.argv[1])
minimum = Version(sys.argv[2])
print("true" if current >= minimum else "false")
PY
}
report_binary () {
local label="$1"
local cmd="$2"
local min="$3"
if command -v "$cmd" >/dev/null 2>&1; then
local raw
raw=$("$cmd" --version 2>/dev/null | grep -Eo '[0-9]+(\\.[0-9]+)+')
if [ -n "$raw" ]; then
local patched
patched=$(check_version "$raw" "$min")
echo "$label | $raw | minimum $min | patched=$patched"
fi
fi
}
report_binary "Google Chrome" "google-chrome" "146.0.7680.80"
report_binary "Google Chrome Stable" "google-chrome-stable" "146.0.7680.80"
report_binary "Chromium" "chromium" "146.0.7680.80"
report_binary "Microsoft Edge" "microsoft-edge" "146.0.3856.62"
This script is deliberately conservative. A Chromium package can lag or backport patches in ways that make version mapping less direct than stock Google Chrome, so in distro-managed environments you should combine this with package metadata and vendor-specific advisories. Still, it is a useful first pass for unmanaged developer workstations and lab environments.
osquery, fleet inventory snapshot
SELECT
name,
version,
path
FROM apps
WHERE
name LIKE '%Chrome%'
OR name LIKE '%Edge%'
OR name LIKE '%Chromium%'
OR name LIKE '%Electron%';
The value of an osquery-style view is that it broadens your response beyond the obvious browser packages. In incidents like this, the blind spot is usually not Chrome itself. It is the long tail of Chromium consumers nobody remembered to check.
What to do if your team is already on current Chrome Stable
If your endpoints are already on 146.0.7680.153/154 for Windows or Mac, or 146.0.7680.153 for Linux, your immediate browser patch problem is largely solved for stock Chrome. But that should not be the end of the ticket. You still need to answer four aftershocks.
First, were any endpoints exposed in the gap between public exploitation and completed rollout. Second, did any systems remain on the ambiguous .75/.76 builds under the false assumption that 3909 was already fixed. Third, are there unmanaged or semi-managed Chromium consumers still behind. Fourth, do your detection and reporting pipelines preserve browser version evidence well enough that you can answer those questions after the fact.
That is the difference between “we patched” and “we understand our exposure.” The second one is what incident reviews actually need.
Why this bug class keeps producing high-stakes browser incidents
There is a deeper lesson in CVE-2026-3909 beyond the patch itself. Browser security is still dominated by a hard truth: untrusted content goes through an enormous amount of native code. Even after years of sandboxing, CFI, fuzzing, and hardening, the browser remains one of the richest attack surfaces on a normal workstation. Google’s own release notes routinely mention the internal use of AddressSanitizer, MemorySanitizer, UndefinedBehaviorSanitizer, Control Flow Integrity, libFuzzer, and AFL. The company keeps investing in those defenses because the attack surface keeps paying off for attackers. (Chrome Releases)
That is also why the public phrase “just a browser bug” should disappear from security teams’ vocabulary. Browser vulnerabilities are not soft issues at the edge of enterprise security. They are one of the most reliable bridges between external content and user endpoints. When a browser-core bug is actively exploited, it belongs in the same mental category as critical client-side zero-days in office suites, document parsers, and messaging clients. The entry mechanism may look ordinary. The exploitation consequences are not.
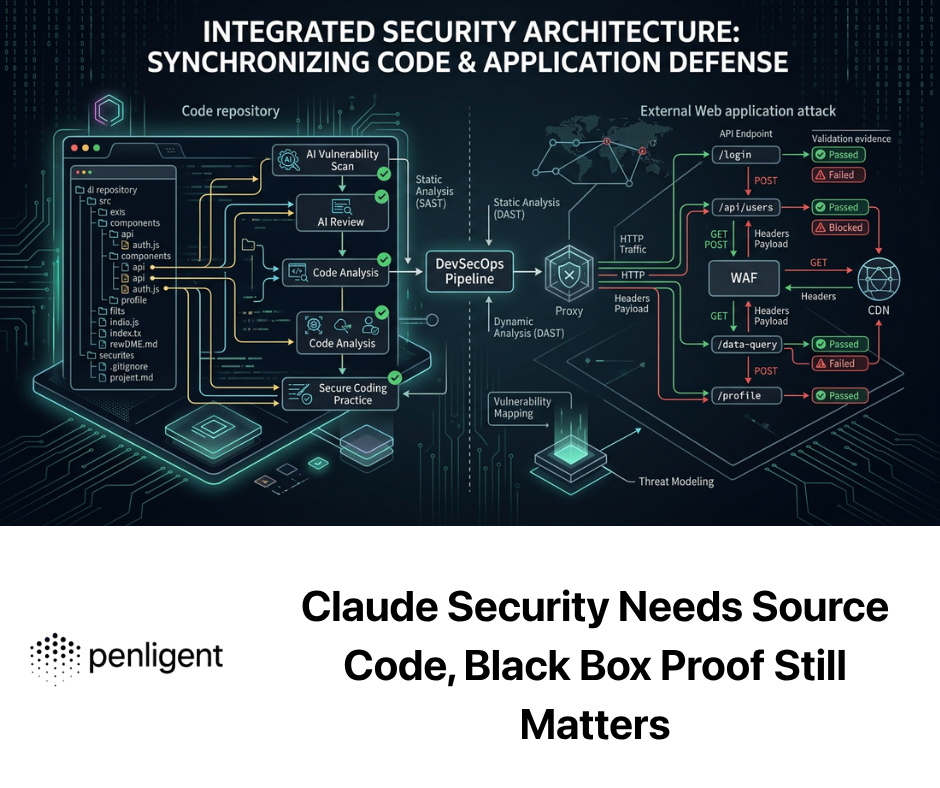
When a browser zero-day lands with restricted bug details, conflicting version language across mirrored databases, and multiple Chromium-derived downstream products, the hard part for many teams is no longer reading the advisory. It is turning fragmented evidence into a reliable exposure verdict. That is where a platform like Penligent fits naturally: not by pretending to generate a magical public exploit, but by helping teams standardize validation, asset-level evidence collection, version normalization, and response documentation across heterogeneous environments. That is especially useful when a CVE sits at the intersection of official advisories, package lag, and downstream app inheritance. (Chrome Releases)
There is also a broader product lesson here. Security teams do not need more pages that repeat the NVD description. They need systems that reduce ambiguity. For a browser event like CVE-2026-3909, the operationally valuable workflow is to discover which products in scope embed the affected engine, verify actual installed versions, compare them against the corrected vendor fix floor, attach evidence, and surface the small number of endpoints that still need action. That kind of validation-oriented workflow is far closer to the real value proposition of modern AI-assisted security tooling than flashy exploit theater. If you wanted a natural place to connect this CVE to a platform conversation, this is it.
The question nobody should answer casually, is there a public CVE-2026-3909 exploit PoC you should trust
My answer is cautious on purpose. I did not find a trustworthy, official, vendor-backed exploit PoC that should be treated as ground truth for defenders as of March 19, 2026. More importantly, the official sources do not disclose exploit mechanics, and Google explicitly says bug details may stay restricted while patch adoption proceeds. That means the correct engineering posture is not “assume no PoC exists” or “assume every PoC blog is fake.” It is “assume public exploit details are incomplete and treat unofficial material as unverified until it is tied to credible root-cause evidence.” (Chrome Releases)
That posture is stronger, not weaker. It prevents teams from importing broken assumptions into internal testing. It keeps validation focused on exposure proof. And it avoids the common trap where a low-quality public snippet becomes the basis for dashboards, signatures, or leadership reporting. In vulnerability response, bad certainty is usually more expensive than admitted uncertainty.
FAQ, the short answers security engineers actually need
Is CVE-2026-3909 real and actively exploited
Yes. Google says an exploit exists in the wild, and the issue is reflected in NVD and CISA-enriched metadata as actively exploited. (Chrome Releases)
What component is affected
Skia, the Chromium graphics library, with the bug class tracked as out-of-bounds write and CWE-787. (NVD)
What is the practical trigger
A crafted HTML page. Public sources consistently describe the attack as remotely triggerable through malicious web content, with user interaction required. (NVD)
What Chrome version should I treat as safe for this CVE
Use 146.0.7680.80 or later as the reliable Chrome floor for CVE-2026-3909 because Google corrected the March 12 note and then shipped the fix in the March 13 .80 release. (Chrome Releases)
What Edge version contains the fix
Microsoft says 146.0.3856.62 contains the fix. (Microsoft Learn)
Do I need to care if I do not use Chrome
Yes, if you use Chromium-based browsers or apps. Edge is directly affected, ChromeOS notes include the fix, and downstream Electron consumers are already shipping dependency bumps tied to CVE-2026-3909. (Microsoft Learn)
Final assessment
The most useful way to read CVE-2026-3909 PoC is not as a hunt for spectacle. It is as a test of whether your security program can stay accurate when the internet is noisy and the vendor is intentionally sparse. This CVE is confirmed, active, high-impact, and reachable through ordinary browsing. The public reporting around it is broadly correct on urgency, but often underpowered on precision. The key precision points are these.
First, this is a real Chrome zero-day in Skia, not a rumor. Second, it was exploited in the wild. Third, the release history around the fix is messy enough that you should follow Google’s corrected March 13 bulletin and treat 146.0.7680.80 as the reliable Chrome remediation floor for this bug. Fourth, you should assess CVE-2026-3909 together with CVE-2026-3910, because the two were disclosed in the same exploited-zero-day window and together describe a broader browser exposure event. Fifth, the most useful PoC for defenders is not exploit code. It is measurable evidence that your fleet is actually patched.
That is the sober conclusion this keyword deserves.
Further reading
Google’s Chrome release notes for the March 12 correction and March 13 fix remain the most important primary sources for this CVE. NVD and the CVE record are useful for classification, but the vendor timeline is what resolves the version ambiguity. For operational summaries, BleepingComputer, SecurityWeek, The Hacker News, and Malwarebytes are the strongest mainstream references I reviewed. (Chrome Releases)
For readers following the broader pattern of browser-core zero-days, Penligent already has a relevant piece on CVE-2026-2441, the earlier Chrome CSS zero-day from February 2026. (Penligent)
For readers interested in the wider browser-exploitation and AI-assisted validation angle, Penligent also has a broader retrospective on Chrome zero-day vulnerabilities exploited in 2025. (Penligent)