The real reason CVE-2024-6387 is “back”
When CVE-2024-6387 first broke into the mainstream in July 2024, it carried the kind of headline that triggers instant muscle memory in every SOC and SRE team: OpenSSH, pre-auth, الجذر, تنفيذ التعليمات البرمجية عن بُعد. Researchers described a regression bug (hence the name regreSSHion) in OpenSSH’s server (sshd) that could, under timing-dependent conditions, be triggered before authentication and potentially lead to code execution with high privileges. Early technical write-ups were serious—but also cautious: race conditions are notoriously hard to win consistently, and proof-of-concepts often don’t translate into reliable real-world exploitation at scale. Qualys’ original disclosure framed it as a signal-handler race condition in OpenSSH on glibc-based Linux, potentially enabling unauthenticated RCE as root. (كواليس)
So why is it trending again now?
لأن CISA added CVE-2024-6387 to the Known Exploited Vulnerabilities (KEV) Catalog with a “Date Added” of 2026-02-25. That is the difference between “a scary vulnerability” and “a vulnerability with evidence of exploitation in the wild,” which immediately changes how many organizations prioritize patching, exception handling, and executive attention. (CISA)
If you run a security program inside a regulated environment, you already know what KEV tends to do:
- It compresses patch timelines.
- It triggers re-triage across huge asset inventories.
- It turns “we’ll patch in the next window” into “prove you’ve remediated.”
That KEV inflection point is the cleanest explanation for the second wave of attention.
What CVE-2024-6387 actually is
CVE-2024-6387 is a race condition tied to unsafe signal handling behavior in OpenSSH’s server (sshd) on glibc-based Linux systems, triggered around the authentication grace period timeout. NVD describes it as a regression of an older issue (CVE-2006-5051): a condition in which sshd can handle signals in an unsafe manner, and an unauthenticated remote attacker may be able to trigger it by failing to authenticate within a set time period. (NVD)
Several credible technical analyses converge on the same core mechanism:
sshdsets an alarm to enforce a timeout (commonly discussed in relation toLoginGraceTime).- When the timeout fires,
sshdreceives SIGALRM asynchronously. - The SIGALRM handler can call functions (directly or indirectly) that are not async-signal-safe (often highlighted around
syslog()and memory allocation paths likemalloc()/free()), which can lead to memory corruption under precisely timed conditions. - Under the right circumstances, that corruption can be steered toward control-flow manipulation—hence the “potential RCE” framing. (Unit 42)
What it is لا:
- It is not a simple “send one packet, get shell” bug.
- It is not a vulnerability where “a PoC exists” automatically means widespread, commodity exploitation.
- It is not universally identical across distributions because OpenSSH is frequently patched and backported by Linux vendors, and version strings can be misleading.
Why OpenSSH bugs don’t need to be easy to become urgent
Two facts can be simultaneously true:
- Race conditions can be difficult to exploit reliably. Multiple defenders’ write-ups emphasized the complexity and the need for repeated attempts or precise timing. Some public commentary noted that early PoCs were not reliably achieving RCE in testing environments. (Dynatrace)
- Organizations still need to treat the risk as urgent once exploitation signals appear. CISA’s KEV inclusion is a strong operational signal: it is based on evidence of active exploitation, not theoretical severity. (CISA)
For defenders, the practical decision is not “do I personally believe the exploit is easy.” The decision is:
Is my environment exposed in ways that allow an attacker to try enough times, from enough vantage points, on enough targets, to eventually win?
The answer is often “yes” for:
- Internet-facing SSH on high-value servers,
- jump boxes and bastions,
- legacy fleets where patch consistency is weak,
- environments with permissive network access and long authentication grace windows.
The keywords people actually search when this resurges
You asked specifically to “search the web for the highest-click keywords” around CVE-2024-6387 and integrate the dominant viewpoints. There is no universally public, verifiable dataset that says “this exact keyword has the highest CTR across all search engines” without paid SEO tooling or proprietary clickstream data. What we يمكن do rigorously is identify the high-intent query clusters that repeatedly appear across major vendor write-ups, advisories, and community discussions—because those topics correlate with what engineers search when they need to act.
Across the most-cited analyses and advisories, the recurring “search intent” clusters are:
- “CVE-2024-6387 affected versions / OpenSSH versions vulnerable” (people need scope) (Unit 42)
- “regreSSHion exploit / PoC / metasploit” (people want to assess exploit maturity) (Deepwatch)
- “How to check if my server is vulnerable / patched” (people need fast verification) (Ubuntu)
- “LoginGraceTime mitigation” (people want a stopgap before patch windows) (ThreatDown by Malwarebytes)
- “CISA KEV CVE-2024-6387” (people want confirmation of active exploitation) (CISA)
Those are the questions this article will answer with an evidence-first approach.
How the bug works
The best way to explain CVE-2024-6387 without turning the article into a “how-to exploit” guide is to focus on the design boundary it breaks.
Signal handlers and async-signal-safety: the fragile edge
A POSIX signal handler runs asynchronously—meaning it can interrupt code at almost any point. Only a small set of functions are considered safe to call inside a signal handler (“async-signal-safe”). If the handler calls unsafe functions, you can end up with re-entrancy problems and corrupted shared state.
Multiple analyses highlight that sshd’s alarm signal path can interact with unsafe logging/memory allocation behavior. Unit 42 describes the core risk as syslog() calling async-signal-unsafe functions such as malloc() و free(), which can lead to unsafe memory state and open the door to code execution under the right timing. (Unit 42)
Oligo’s technical write-up similarly frames the issue around async-signal-unsafe functions being called in the SIGALRM handler and the resulting heap inconsistency risk. (oligo.security)
لماذا LoginGraceTime matters
Most descriptions tie the trigger condition to failing to authenticate within a configured time window. Malwarebytes/ThreatDown summarizes this plainly: if a client fails to authenticate within the grace period, sshd may handle a signal in an unsafe way, and that grace period is typically 120 seconds by default. (ThreatDown by Malwarebytes)
NVD’s language also explicitly references “failing to authenticate within a set time period.” (NVD)
Why glibc-based Linux is repeatedly mentioned
Qualys’ disclosure emphasizes glibc-based Linux systems. (كواليس)
Unit 42 notes OpenBSD is not vulnerable in the same way, referencing differences in how logging is handled (an implementation detail that matters because it affects async-signal-safety). (Unit 42)
The operational takeaway is not “glibc is broken.” The takeaway is: platform-level implementation details change the exploitability surface, which is why defenders must evaluate risk through both version scope and vendor patches—not just the CVSS headline.
Scope: affected versions, vendor backports, and why “ssh -V” can lie
The common version range in public analyses
Many vendor and research write-ups converge on the idea that versions around OpenSSH 8.5p1 up to (but not including) 9.8p1 are in scope, with patch availability in 9.8p1. You’ll see this in Splunk’s summary (8.5p1 to 9.8p1), for example. (Splunk)
Qualys’ public materials also discuss the affected range and point to patching as the resolution. (كواليس)
OpenSSH release information shows OpenSSH 9.8/9.8p1 released on 2024-07-01, which aligns with the industry’s “patch line” discussions. (OpenSSH)
Why you must check vendor security advisories, not just upstream versions
Ubuntu’s security notice (USN-6859-1) describes the issue in terms of incorrect signal management and remote attackers potentially bypassing authentication and remotely accessing systems, and it reflects Ubuntu’s packaging reality. (Ubuntu)
Red Hat’s CVE page also mirrors the regression and race-condition description and provides distro-specific status and remediation guidance. (Red Hat Customer Portal)
This is where teams get burned:
ssh -Vshows the OpenSSH version compiled into your binary, but not necessarily the distribution backport patch level you actually have deployed.- A system may display an upstream-looking version number and still be patched (or unpatched) depending on the vendor’s packaging and backports.
The only safe answer is: use package manager metadata + vendor advisories + actual installed package revision.
Why KEV inclusion changes your playbook
CISA’s KEV Catalog is often treated as a forcing function for patch SLAs. Once a CVE is in KEV, many orgs shift from “risk-based scheduling” to “deadline-driven remediation,” because KEV is a curated set of vulnerabilities with evidence of exploitation. The KEV entry for CVE-2024-6387 shows a Date Added: 2026-02-25 and a rapid due date, which is exactly the kind of signal that triggers urgent change windows. (CISA)
So the question becomes:
- Do you have any internet-facing
sshdinstances in scope? - Can an attacker reach them repeatedly?
- Are they on glibc-based Linux distributions and affected package lines?
- Can you prove remediation, not just claim it?
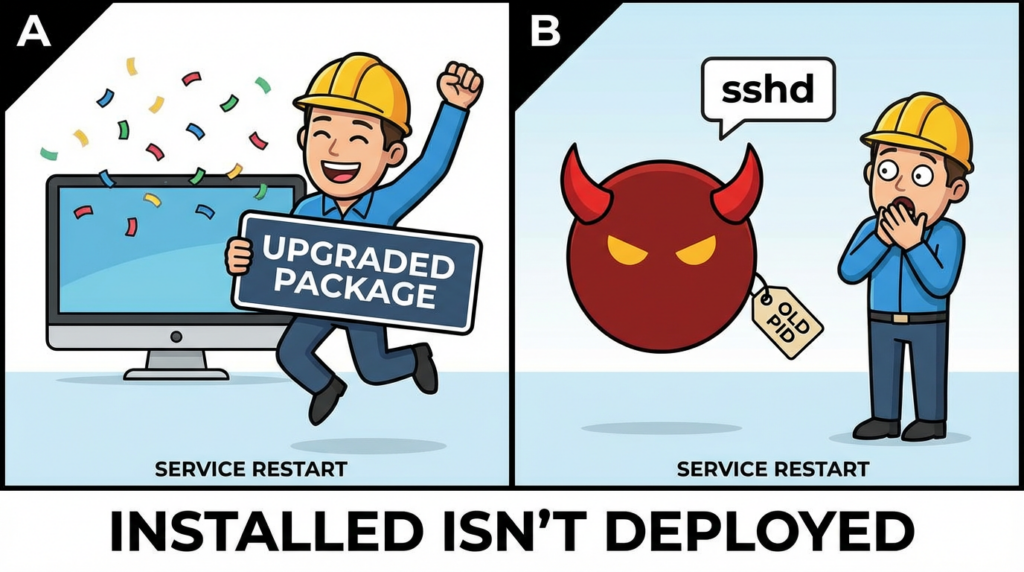
That last bullet is where most incident-driven patch sprints fail: teams patch some servers, forget others, don’t restart services, or can’t demonstrate evidence later when auditors or leadership asks.
Immediate action: a verification-first checklist
Everything below assumes authorized assets only.
1) Inventory SSH exposure quickly
On Linux (local):
sshd -V 2>&1 || /usr/sbin/sshd -V 2>&1
ssh -V 2>&1
List listening ports and processes:
sudo ss -tulpn | grep -E ':(22|2222)\\b'
ps aux | grep -E '[s]shd'
If you’re in a cloud environment:
- Enumerate security groups / firewall rules for port 22 and non-standard SSH ports.
- Identify bastions and jump hosts as highest priority.
2) Check patch status via package manager (more reliable than version banners)
Debian/Ubuntu:
dpkg -l | grep -E '^ii\\s+openssh-server\\s'
apt-cache policy openssh-server
RHEL/Rocky/Alma/CentOS Stream:
rpm -q openssh-server
dnf info openssh-server || yum info openssh-server
Then cross-reference with vendor advisories:
- Ubuntu USN notice (Ubuntu)
- Red Hat CVE page (Red Hat Customer Portal)
3) Confirm the runtime is actually running the fixed code (restart matters)
Many SSH fixes require a daemon restart to load the patched binary. Some distro advisories explicitly remind users that services must be restarted after upgrade.
تحقق من ذلك:
sudo systemctl status ssh || sudo systemctl status sshd
sudo systemctl show -p MainPID sshd
sudo ls -l /proc/$(pidof sshd)/exe
Restart (plan carefully if remote-only access):
sudo systemctl restart sshd
# or
sudo service ssh restart
Operational safety tip: before restarting SSH on a remote system, keep an existing session open and ensure you have out-of-band access (console, SSM, iLO/iDRAC) if possible.

4) Temporary mitigation levers
Vendors commonly discuss configuration-based mitigations that reduce exploit window by changing the authentication grace period. Public commentary on regreSSHion frequently references LoginGraceTime because the timeout signal is a key trigger path. (ThreatDown by Malwarebytes)
Example (choose values that balance security and operational realities):
# /etc/ssh/sshd_config
LoginGraceTime 30
MaxAuthTries 3
MaxSessions 2
# optionally limit by network / users:
AllowUsers youradmin yourops
Then:
sudo sshd -t
sudo systemctl reload sshd
This is لا a substitute for patching. It is a risk-reduction move to narrow the timing window and reduce brute attempts while you patch.
5) Detect suspicious patterns
Because exploitation attempts may require many tries, defenders often look for abnormal authentication timeout patterns and repeated failed pre-auth sequences.
Common locations:
/var/log/auth.log(Debian/Ubuntu)/var/log/secure(RHEL-family)journalctl -u sshd
مثال على ذلك:
# High-volume failures / timeouts in the last hour
sudo journalctl -u sshd --since "1 hour ago" | \\
egrep -i "timeout before authentication|Failed|Invalid user|Connection closed"
# Count by source IP (auth.log example)
sudo grep -Ei "timeout before authentication|Failed password|Invalid user" /var/log/auth.log | \\
awk '{print $(NF-3)}' | sort | uniq -c | sort -nr | head
If you are building detection content, Anomali’s example query language focuses on “timeout before authentication” style strings as a starting signal. (Anomali)
A practical table: what to verify, what evidence to keep
| الخطوة | What you’re proving | Evidence artifact you can save |
|---|---|---|
| Asset identification | Which hosts run sshd and are reachable | Inventory export, firewall rules, cloud SG snapshot |
| Package verification | Patched package revision installed | dpkg -l / rpm -q output + vendor advisory reference (Ubuntu) |
| Runtime verification | sshd is running the patched binary | systemctl status, /proc/<pid>/exe symlink evidence |
| Exposure confirmation | Port 22 reachable only where intended | nmap results from authorized scanner, SG rules |
| Detection baseline | Abnormal auth-timeout spikes investigated | Log extracts + ticket references |
| Remediation closure | Patch + restart + validation complete | Change record + pre/post evidence bundle |
This table is boring—and that’s the point. The teams that survive KEV-driven patch sprints are the teams that treat remediation as auditable proof, not a Slack message saying “patched.”
Proof-of-concept reality: what “PoC exists” should mean to defenders
In July 2024, multiple sources discussed PoCs and the difficulty of achieving reliable exploitation. Unit 42 noted that while PoC code existed, they were unable to successfully exploit to achieve RCE in their testing environment at that time. (Unit 42)
OffSec published a write-up discussing the vulnerability mechanics and exploitation concepts (without implying it is trivially exploitable in the wild). (OffSec)
Deepwatch also described the arrival of PoCs in the landscape and argued for urgent patching due to risk profile. (Deepwatch)
The important nuance:
- A PoC can be non-functional, environment-specific, or incomplete—and still be useful to attackers as a blueprint.
- A race-condition exploit can be unreliable in a lab and still succeed in production given enough attempts, enough targets, and enough time.
- KEV inclusion is a strong indicator that exploitation is not purely hypothetical anymore. (CISA)
Remediation: patch is the center of gravity
Patch guidance
The industry consensus since disclosure has been: upgrade to patched OpenSSH packages (often discussed in relation to OpenSSH 9.8p1 as the upstream patch line, with vendor backports across distributions). (OpenSSH)
Do not treat “upgrade OpenSSH” as a single instruction. Treat it as a matrix:
- Your distribution (Ubuntu / Debian / RHEL / SUSE / Alpine / container images)
- Your packaging (vendor backport or upstream build)
- Your restart posture (daemon restart required? which hosts can be restarted safely?)
- Your exposure posture (internet-facing? internal-only? behind a VPN? through a bastion?)
Ubuntu provides a USN notice path for remediation guidance. (Ubuntu)
Red Hat’s CVE entry provides distro-specific tracking and remediation context. (Red Hat Customer Portal)
Cisco’s advisory provides an ecosystem-level summary of the vulnerability and scope for Cisco products and OpenSSH contexts. (Cisco)
Hardening that actually matters while you patch
If you have any SSH exposed to the public internet, you should treat that as a deliberate design choice, not a default. You don’t need exotic controls to reduce risk meaningfully:
- Restrict source IP ranges (VPN or office egress) for port 22.
- Prefer bastions over direct SSH to every server.
- Use key-based auth only; disable passwords where feasible.
- Enforce MFA via an identity-aware proxy or SSH certificates where appropriate.
- Rate-limit and ban abusive sources (fail2ban / firewall).
None of that replaces patching. It just makes “try 10,000 times to win a race” materially harder to operationalize.

Related CVEs you should know
CVE-2006-5051: the historical anchor
NVD and multiple write-ups frame CVE-2024-6387 as a regression of CVE-2006-5051. That matters because it’s a reminder that mature infrastructure can reintroduce old classes of bugs when code changes remove critical safety properties. (NVD)
CVE-2008-4109: mentioned in some scope discussions
Unit 42 notes that versions earlier than 4.4p1 may be affected if they have not been patched against CVE-2006-5051 or patched against CVE-2008-4109 (context: historical patching paths and backports). (Unit 42)
CVE-2023-38408: a modern reminder that SSH risk isn’t only server-side
OpenSSH has seen high-impact vulnerabilities in recent years outside the exact regreSSHion class. OpenSSH release notes reference security fixes (including CVE-2023-38408 in release note context), and defenders should treat SSH as a long-lived, high-value attack surface with recurring issues across components (server, client, agent forwarding). (OpenSSH)
CVE-2024-3094 (XZ Utils incident): not “SSH,” but the same underlying lesson
Even though it is not an OpenSSH vulnerability, XZ’s widely discussed supply-chain incident in 2024 reshaped how security teams think about foundational components. The connection is conceptual: the internet runs on a small set of deeply embedded primitives, and when one of them becomes suspect, the blast radius is organizational, not just technical. (If you’re already exhausted by patching fatigue, this is why leadership still needs to care: the primitives are the battlefield.)
Making remediation real: the difference between “patched” and “proven”
If you want to handle CVE-2024-6387 like a professional program and not a social-media fire drill, your goal is not only to patch. Your goal is to produce a defensible chain of evidence:
- Which systems were in scope
- Which ones were vulnerable
- Which packages were applied
- Which daemons were restarted
- Which controls reduced exposure
- Which tests confirmed closure
KEV-driven work is where “we think we patched” becomes a liability. The right posture is: we can prove it.
If your team is already running an authorized offensive validation workflow, CVE-2024-6387 is the kind of issue that benefits from automation focused on verification, not exploit theatrics.
Penligent is designed as an AI-driven penetration testing platform that can orchestrate reconnaissance and security verification workflows across approved targets. In practice, the value for an SSH-class issue is straightforward: you can standardize an internal “exposure → patch → retest” routine, capture evidence, and reduce the gap between what the fleet يجب look like and what it في الواقع looks like in production.
Penligent has previously discussed CVE-2024-6387 (regreSSHion) in its own security research context, which you can use as an internal reference point when building a repeatable validation playbook. (بنليجنت)
Links
- CISA Known Exploited Vulnerabilities Catalog (KEV) entry context and dates (CISA)
- NVD CVE-2024-6387 record (NVD)
- OpenSSH release notes (upstream release context) (OpenSSH)
- Ubuntu USN-6859-1: OpenSSH vulnerability notice (Ubuntu)
- Red Hat CVE-2024-6387 tracking page (Red Hat Customer Portal)
- Qualys disclosure and technical summary (كواليس)
- Palo Alto Networks Unit 42 threat brief (Unit 42)
- Cisco Security Advisory overview (Cisco)
- Penligent: “The Singularity of Offensive Cyber…” (includes a section on CVE-2024-6387 regreSSHion) (بنليجنت)
- Penligent: “Anthropic Cybersecurity Tool in 2026” (references CVE-2024-6387 contextually) (بنليجنت)