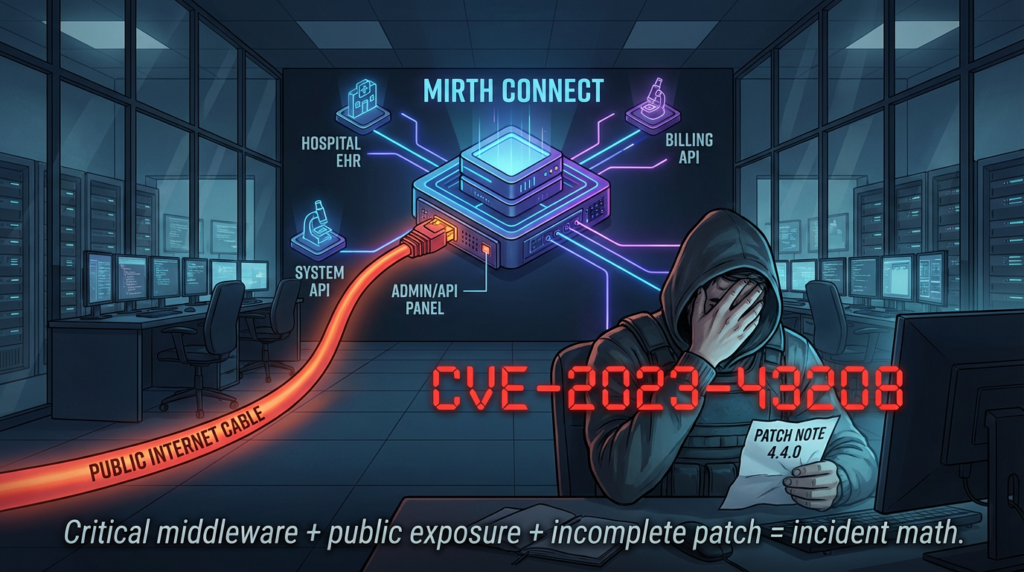
CVE-2023-43208 is one of those vulnerabilities that keeps showing up in security operations conversations long after initial disclosure, not because the headline is unclear, but because the real work begins after the headline. It is a critical, unauthenticated remote code execution vulnerability in NextGen Healthcare Mirth Connect, and it became especially important because it was not just a standalone issue—it was the result of an incomplete patch for an earlier critical bug, CVE-2023-37679. (NVD)
NVD describes CVE-2023-43208 as affecting NextGen Healthcare Mirth Connect before version 4.4.1, and notes that the vulnerability is caused by the incomplete patch of CVE-2023-37679. NVD also records a CVSS v3.1 score of 9.8 (Critical) with the vector AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H, which matches the risk profile defenders expect for a pre-authentication RCE exposed over the network. (NVD)
What moves this CVE from “serious” to “urgent” is the combination of technical severity and operational context. Mirth Connect is widely used in healthcare environments as an integration layer for data exchange and interoperability workflows. Horizon3’s advisory and writeup both highlight that Mirth Connect is widely used by healthcare organizations, which raises the practical impact of internet-facing exposure and makes patch verification more important than simple version labeling. (Horizon3.ai)
This article focuses on what security engineers and platform teams actually need: what happened, why the earlier patch was bypassed, what changed in 4.4.1, how to safely validate exposure without reproducing the exploit, what to monitor, and how to close the ticket with evidence rather than assumptions.
What CVE-2023-43208 Is and Why It Matters
At a factual level, the vulnerability is straightforward: unauthenticated remote code execution in Mirth Connect versions before 4.4.1. NVD’s description is explicit, and it also documents the tie-back to CVE-2023-37679 as an incomplete patch. (NVD)
NVD also records that this CVE was added to CISA’s Known Exploited Vulnerabilities (KEV) Catalog with a date added of 2024-05-20 and a due date of 2024-06-10 for federal remediation action. That matters because KEV inclusion is a strong prioritization signal for defenders: it means the issue is not being treated as purely theoretical or academic. (NVD)
NHS England Digital and the Cyber Security Agency of Singapore (CSA) published alerts that reinforce the same point from another angle: both describe the vulnerability as critical, both note unauthenticated RCE impact, and both reference active or probable exploitation reporting in the wild. (NHS England Digital)
When a vulnerability combines all of the following, it deserves immediate attention:
- pre-authentication remote code execution
- internet-exposed administrative/API surfaces
- healthcare-sector deployment prevalence
- public PoC and exploit ecosystem attention
- known exploitation signals
- patch-bypass lineage from an earlier critical CVE
CVE-2023-43208 checks every one of those boxes. (NVD)
The Patch-Bypass Story Behind CVE-2023-43208
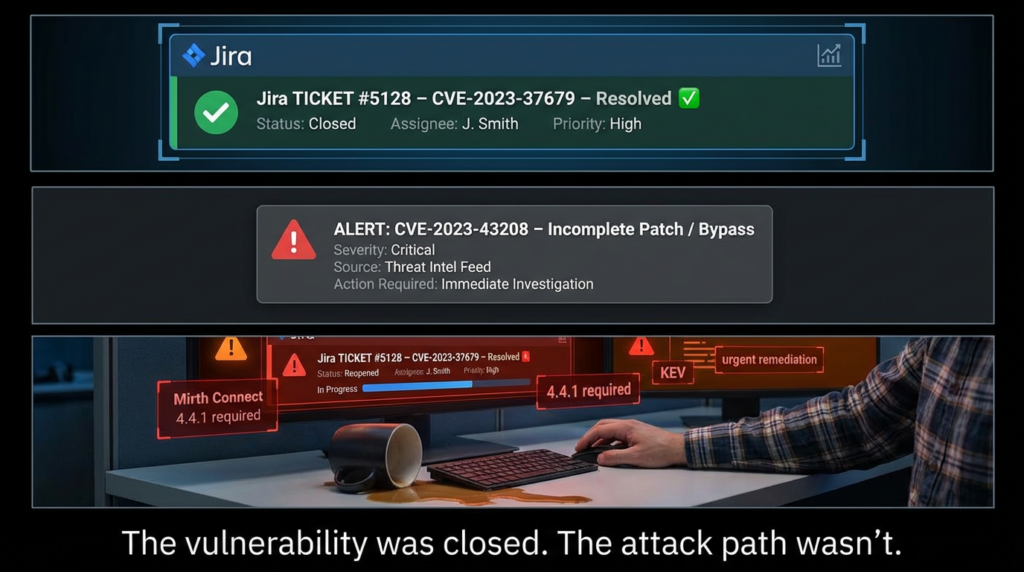
The most important part of CVE-2023-43208 is not just the exploit impact; it is the fact that it came from an incomplete patch. Horizon3’s writeup states clearly that CVE-2023-43208 arose from an incomplete patch for CVE-2023-37679, and explains that the earlier CVE had reportedly been patched in Mirth Connect 4.4.0. (Horizon3.ai)
This matters because patch-bypass vulnerabilities create a different kind of risk than a brand-new vulnerability:
- Teams may already have marked the original issue “resolved.”
- Asset inventories may show “patched” while still running a version that remains exploitable.
- Staging, DR, or secondary nodes may have stopped at 4.4.0 and never reached 4.4.1.
- Security controls and exception records may be based on outdated patch assumptions.
NHS England Digital’s alert explicitly calls CVE-2023-43208 a patch bypass of CVE-2023-37679, which is exactly the kind of language defenders should pay attention to in triage and remediation planning. (NHS England Digital)
The practical lesson is simple: when a follow-on CVE exists because of incomplete remediation, version tracking alone is not enough—you need remediation lineage awareness. In this case, “patched once” was not the same as “safe.”
Technical Root Cause in Plain Engineering Terms
Horizon3’s public writeup is the best source for understanding the technical root cause without turning a defensive article into an exploit tutorial. The writeup explains that CVE-2023-43208 is tied to insecure use of the Java XStream library for unmarshalling XML payloads and that the earlier patch approach relied on an XStream denylist in an XStreamSerializer class. Horizon3 also notes that XStream has a long history of security issues and that denylist approaches are notoriously difficult to secure in this context. (Horizon3.ai)
The writeup goes further and explains the request-processing sequence that makes this class of bug dangerous. Horizon3 describes how XML payloads are converted into objects by XmlMessageBodyReader before servlet methods process the request, and notes that while many Mirth servlets perform authentication checks in a base class path, some servlets (ConfigurationServlet, SystemServlet, UserServlet) set initLogin to false and handle authentication in the servlet itself, creating cases where XML unmarshalling can happen before the effective authentication check. (Horizon3.ai)
That sequence is the core engineering lesson:
- Untrusted XML payloads were deserialized too early
- Authentication enforcement was not consistently positioned before that processing path
- A denylist-based mitigation did not fully constrain the dangerous object surface
This is also why the 4.4.1 fix is notable: the NextGen Mirth Connect 4.4.1 “What’s New” page states that the product switched XStream to use an allowlist instead of a denylist, and explains that only strictly necessary types are allowed. That is a stronger design choice for this class of risk. (GitHub)
What Changed in Mirth Connect 4.4.1
The 4.4.1 release is not just “another patch level.” It is the version boundary that public sources consistently identify as the remediation point for CVE-2023-43208.
NVD identifies versions up to but excluding 4.4.1 as affected. (NVD)
NHS England Digital advises affected organizations to review the Mirth Connect 4.4.1 release note and apply updates. (NHS England Digital)
CSA Singapore advises users and administrators of affected versions to update immediately and notes that versions prior to 4.4.1 are affected. (Cyber Security Agency of Singapore)
The NextGen 4.4.1 release page also states, in plain language, that an unauthenticated remote command execution vulnerability existed in Mirth Connect Core 4.4.0 and lower, and that the XStream change was made to resolve the issue. It also documents the switch from a denylist to an allowlist and notes an OpenSSL upgrade for Docker images based on Eclipse Temurin. (GitHub)
That gives defenders a clean, evidence-backed rule:
For CVE-2023-43208, 4.4.1 (or later) is the minimum meaningful patch level.
This should be reflected in runbooks, CMDB compliance logic, vulnerability exceptions, and scanner validation notes.
Threat Activity and Exploitation Signals
The danger of CVE-2023-43208 is not just its theoretical exploitability. Public alerts and advisories document a progression from disclosure to proof-of-concept release to reports of exploitation.
NHS England Digital’s alert timeline notes:
- a public PoC release (January 2024),
- reported probable exploitation of web-facing Mirth Connect servers (March 2024),
- and a later update reflecting CISA KEV inclusion (May 2024). (NHS England Digital)
CSA Singapore’s advisory, published May 28, 2024, also states that there were reports of active exploitation and reiterates the critical severity (CVSS 9.8) and unauthenticated RCE impact. (Cyber Security Agency of Singapore)
NVD’s KEV metadata provides an additional hard signal for prioritization and governance workflows, especially in environments where remediation urgency is driven by regulatory, federal, or board-level risk reporting. (NVD)
For defenders, these public signals mean the response should not stop at vulnerability scanning. You need:
- version confirmation,
- exposure reduction,
- monitoring and alerting,
- and post-remediation validation.
How to Determine Whether You Are Affected
The public sources provide enough information to build a safe validation process without sharing exploit instructions.
The first check is version. Horizon3’s advisory and technical writeup describe a version-checking approach using the /api/server/version endpoint with the X-Requested-With: OpenAPI header and note that servers reporting versions below 4.4.1 are highly likely to be exploitable. (Horizon3.ai)
Quick Version Check (Non-Exploit)
curl -k -H 'X-Requested-With: OpenAPI' https://<mirth-host>:<port>/api/server/version
If the response reports a version below 4.4.1, treat the instance as high priority until it is upgraded and revalidated. This check is useful because it is simple, auditable, and safe when performed against systems you own or are authorized to assess. (Horizon3.ai)
What to Verify Beyond Version
Do not stop at a single host check. In real environments, the most common failure mode is incomplete coverage.
| Validation Area | What to Check | Why It Matters |
|---|---|---|
| Version | Mirth Connect version is 4.4.1+ | Baseline fix condition for CVE-2023-43208 |
| Asset coverage | Prod, DR, staging, lab, legacy nodes all checked | Patch gaps often persist outside primary production |
| Exposure | Administrative/API surfaces are not broadly internet-facing | Reduces attack surface even after patching |
| Runtime consistency | No stale containers / rollback images / old templates | Prevents reintroducing vulnerable versions |
| Monitoring | Alerts exist for abnormal API and host behavior | Needed for detection and validation of attempted abuse |
This kind of table belongs in the remediation ticket, not just in an article.
Safe Python Script for Version Inventory
The following script is intentionally limited to version collection and basic risk tagging. It does not attempt exploitation and should only be used with authorization.
import requests
import urllib3
from packaging.version import Version, InvalidVersion
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
HEADERS = {"X-Requested-With": "OpenAPI"}
TIMEOUT = 8
def check_mirth_version(base_url: str):
url = base_url.rstrip("/") + "/api/server/version"
try:
r = requests.get(url, headers=HEADERS, verify=False, timeout=TIMEOUT)
status = r.status_code
text = r.text.strip()
result = {
"target": base_url,
"status_code": status,
"version": None,
"cve_2023_43208_risk": "unknown",
"notes": ""
}
if status != 200:
result["notes"] = "Non-200 response. Check routing, auth requirements, proxy filtering, or endpoint access."
return result
result["version"] = text
try:
v = Version(text)
if v < Version("4.4.1"):
result["cve_2023_43208_risk"] = "likely_affected"
result["notes"] = "Upgrade to 4.4.1+ and validate exposure/monitoring."
else:
result["cve_2023_43208_risk"] = "version_not_affected_for_this_cve"
result["notes"] = "Still verify exposure controls and monitor for abnormal API activity."
except InvalidVersion:
result["notes"] = "Unexpected version format. Manual review required."
return result
except requests.RequestException as e:
return {
"target": base_url,
"status_code": None,
"version": None,
"cve_2023_43208_risk": "unknown",
"notes": f"Request failed: {e}"
}
if __name__ == "__main__":
targets = [
"<https://mirth-prod.example.org:8443>",
"<https://mirth-dr.example.org:8443>",
"<https://mirth-staging.example.org:8443>",
]
for t in targets:
print(check_mirth_version(t))
This is intentionally simple because simple scripts get used, reviewed, and attached to tickets. That is exactly what you want during a vulnerability response window.
Detection and Monitoring Priorities
For CVE-2023-43208, defenders should avoid overfitting on a single public payload shape. Horizon3’s writeup explains that the issue is tied to XML unmarshalling and discusses multiple endpoints and code paths relevant to exploitation, which means payloads and request patterns can vary. (Horizon3.ai)
A more resilient approach is to monitor behavior and exposure patterns.
What to Monitor
1) Unusual XML POST Traffic to Mirth API Paths
Look for:
- XML POSTs to management-related API endpoints
- requests from unfamiliar or untrusted IP space
- bursts of requests to multiple Mirth API endpoints
- malformed XML patterns and repeated retries
- sequences of 4xx/5xx followed by successful responses
2) Suspicious Child Process Activity from the Mirth Service Context
If you have EDR or host telemetry:
- flag uncommon child processes launched by the Mirth Java service context
- investigate outbound connections shortly after unusual API traffic
- review persistence changes or unauthorized system modifications
3) Patch Drift and Version Regression
Track:
- any Mirth Connect instance below 4.4.1
- nodes with unknown or inconsistent version responses
- deployments using old images/templates
- rollback events that may silently reintroduce vulnerable versions
Example Hunting Logic (Conceptual)
Hunt: Mirth API anomaly + host execution correlation
Data sources:
- Reverse proxy / WAF / web logs
- App gateway logs
- EDR / Sysmon / Linux audit logs
- CMDB / asset inventory
Conditions:
1) Target host is tagged as Mirth Connect
2) HTTP POST to /api/ path with XML body indicators
3) Source IP is rare or external to expected admin networks
4) Within 5 minutes, host telemetry shows unusual child process execution
5) Optional: outbound network connection spike from Mirth host
Outcome:
- Raise high-confidence alert for immediate review
- Trigger containment playbook if host activity confirms post-request execution anomalies
The goal is not to guess the exact exploit payload. The goal is to detect abuse of the vulnerable processing path and confirm whether it led to suspicious execution behavior.
Remediation That Holds Up in the Real World
Public advisories consistently say to upgrade, and they are right. NHS and CSA both emphasize updating affected versions, and NVD plus the NextGen 4.4.1 notes define the version boundary clearly. (NHS England Digital)
But strong remediation for CVE-2023-43208 should include more than patch deployment.
A Practical Remediation Sequence
Upgrade to 4.4.1 or later
This is the minimum requirement for addressing the vulnerability itself. (NVD)
Restrict internet exposure
If administrative/API access does not need to be public, move it behind VPN, private network controls, or allowlisted access paths. Even patched systems benefit from reduced exposure.
Verify every environment
Production-only patching is not enough. Check DR, staging, integration environments, and older standby systems.
Review containers and templates
The 4.4.1 notes also mention Docker image OpenSSL upgrades. That is a reminder to validate not just app version, but image lineage and template hygiene in CI/CD and infrastructure pipelines. (GitHub)
Add monitoring before closing the ticket
A patched system with no visibility still leaves you blind to scanning, exploitation attempts, or reintroduced drift.
Why This CVE Is a Good Test of Vulnerability Management Maturity
CVE-2023-43208 is a strong case study because it exposes a common weakness in many security programs: treating vulnerability management as a checklist instead of an engineering process.
A weak response looks like this:
- scanner finds CVE
- patch deployed on one system
- ticket closed
A mature response looks like this:
- all Mirth assets identified
- versions verified with evidence
- exposure reduced
- detections deployed
- drift controls reviewed
- closure documented with artifacts
This distinction matters because patch-bypass CVEs punish shallow workflows. If your process cannot track “original CVE patched, follow-on bypass CVE disclosed, patch threshold changed,” you are going to repeat the same class of failure elsewhere.
Where Penligent Can Fit in a Response Workflow
CVE-2023-43208 is exactly the type of vulnerability where teams often struggle less with understanding the advisory and more with executing a reliable, repeatable validation process across multiple environments.
For organizations that use an AI-assisted penetration testing and verification platform such as Penligent, the practical value is in operationalizing the workflow around the vulnerability: inventory-based validation tasks, version checks, exposure checks, regression testing after upgrades, and evidence collection for reporting. This is especially helpful when the same product exists in production, staging, and disaster-recovery environments and each needs consistent verification outputs.
The right way to use a platform here is not as a replacement for patching or vendor guidance. It is as a way to improve execution quality and documentation quality—turning “we upgraded” into “we can show what was checked, where it was checked, and what remains under monitoring.”
Related CVEs You Should Mention in Any Serious CVE-2023-43208 Analysis
CVE-2023-37679
This is the most important related CVE because CVE-2023-43208 is publicly documented as a follow-on issue caused by the incomplete patch of CVE-2023-37679. NVD, NHS, and Horizon3 all connect the two. (NVD)
Why the pairing matters
If you only track CVE IDs independently, you miss the engineering and operational reality:
- original issue patched,
- patch design was incomplete,
- exploit class remained reachable,
- follow-on CVE raised the patch floor again.
Security teams that track fix lineage (not just CVE counts) respond faster and close risk more reliably.
Closing the Ticket With Evidence, Not Assumptions
The final step in a CVE-2023-43208 response should not be “status: patched.” It should be a documented closure package that another engineer—or an auditor—can review independently.
Recommended Closure Artifacts
| Artifact | Example |
|---|---|
| Version evidence | Timestamped outputs showing all Mirth instances on 4.4.1+ |
| Asset coverage proof | Inventory list including prod, DR, staging, and legacy nodes |
| Exposure controls | Firewall / security group / reverse proxy rule snapshots |
| Detection coverage | SIEM alert rules and EDR policy IDs |
| Change records | Patch windows, deployment IDs, image digests |
| Runbook update | Notes on CVE-2023-43208 and CVE-2023-37679 remediation lineage |
This is how you turn emergency patching into durable institutional knowledge.
Final Takeaway
CVE-2023-43208 is not just another critical RCE entry in a vulnerability database. It is a high-value example of how real incidents happen at the boundary between software flaws and operational assumptions.
The public record is clear: this vulnerability affected Mirth Connect versions before 4.4.1, enabled unauthenticated remote code execution, was tied to an incomplete patch for CVE-2023-37679, and later became important enough to be added to CISA’s KEV catalog while national agencies warned about exploitation. (NVD)
For security engineers, the long-term lesson is bigger than this single product:
- treat parsing and deserialization paths as trust boundaries
- treat patch-bypass disclosures as priority resets
- treat “patched” as a hypothesis
- prove closure with evidence
That mindset will help on the next critical CVE just as much as it helps on CVE-2023-43208.
Links
- NVD: CVE-2023-43208
- Horizon3.ai advisory on CVE-2023-43208
- Horizon3.ai technical writeup for CVE-2023-43208
- NextGen Mirth Connect 4.4.1 “What’s New”
- NHS England Digital cyber alert (CVE-2023-43208)
- CSA Singapore alert on active exploitation of CVE-2023-43208
- Penligent Hacking Labs CVE category
- Penligent article on verification / proof-based validation workflows
- Penligent article on Exploit DB (if discussing exploit ecosystem and defender validation context)