The short version you can read in a war room
CVE-2026-20127 is a vulnerability in Cisco Catalyst SD-WAN Controller and Cisco Catalyst SD-WAN Manager that lets an unauthenticated remote attacker bypass authentication and obtain administrative privileges. The underlying issue is an authentication mechanism for peering that “is not working properly.” (NVD)
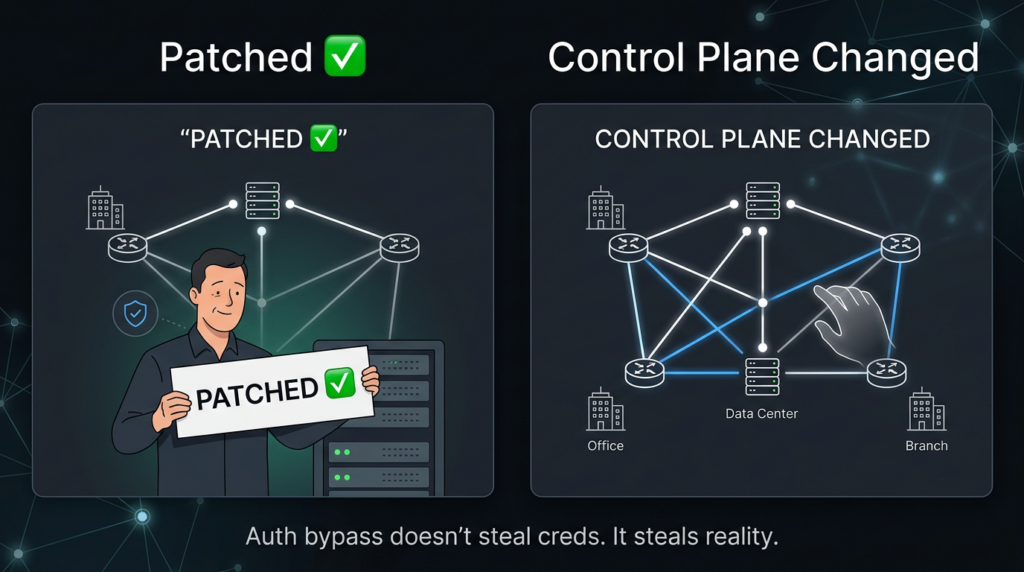
That sentence is already bad. The next sentence is worse: once the attacker gets in as a high-privileged internal, non-root account, they can access NETCONF and manipulate network configuration for the entire SD-WAN fabric. (NVD)
This is why defenders keep calling it a “control plane” problem instead of a single-box compromise. SD-WAN is designed to turn policy and routing intent into distributed reality. A control plane foothold doesn’t just see things; it can cambiar what everything believes is true.
Cisco Talos reports active exploitation and clusters the activity as UAT-8616, with evidence going back to at least 2023. (Blog Cisco Talos) Rapid7 summarizes public reporting that the actors used CVE-2026-20127 for initial access, then downgraded firmware for post-exploitation and chained CVE-2022-20775 to escalate to root, then restored the original version to reduce suspicion. (Rápido7)
If you operate Cisco SD-WAN, treat this as: patch fast, restrict exposure now, and hunt for trust-plane tampering, not just “webshells.”
What people are actually searching when they type “cve 2026 20127”
The highest-intent queries around this incident aren’t academic. They cluster around four phrases that show up repeatedly in top, widely-referenced writeups and headlines:
- “Cisco Catalyst SD-WAN authentication bypass” (vendor + product + vuln class) (NVD)
- “CVE-2026-20127 exploited in the wild / active exploitation” (risk confirmation + urgency) (Blog Cisco Talos)
- “vManage / vSmart” (legacy naming used in many environments and runbooks) (NVD)
- “SD-WAN control plane / rogue peer / peering events” (what to hunt, not just what to patch) (Blog Cisco Talos)
That set maps cleanly to the searcher’s real question:
Am I exposed, have I been touched, and what evidence proves it either way?
In the rest of this piece, we’ll answer those questions in operational terms, using only what’s publicly substantiated in primary sources: NVD, Cisco Talos, and mature incident-response style writeups (Rapid7). (NVD)
CVE-2026-20127 enables in the real world
At a technical level, the vulnerability is categorized as improper authentication (CWE-287). (NVD) That classification matters because the most dangerous auth bugs share a property: they often sit antes de the normal telemetry you rely on.
Most IR playbooks assume “successful login” implies a credential story. Auth bypass flips that. You can see sessions, config changes, and netconf operations without seeing the “why” you’re used to seeing.
From NVD’s description, the exploit path is:
- Send crafted requests to an affected system. (NVD)
- Bypass authentication and log in as an internal, high-privileged non-root user. (NVD)
- Use that access to reach NETCONF. (NVD)
- Manipulate SD-WAN fabric configuration. (NVD)
That last step is the threat model: a policy orchestration layer is only as safe as its strongest trust boundary.
CVSS 10.0 is not the story, the vector tells you why responders panicked
NVD lists a CVSS v3.1 vector string for CVE-2026-20127:
AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H (NVD)
Even if you don’t live in CVSS math, the semantics are straightforward:
- Network reachable, low complexity → reachable from afar, not a puzzle box. (NVD)
- No privileges required, no user interaction → you don’t need creds and you don’t need to trick anyone. (NVD)
- Scope changed → compromise crosses a boundary (fitting for “control plane can change fabric”). (NVD)
- High CIA impact → confidentiality, integrity, availability all at high impact. (NVD)
You don’t need to debate whether you “agree” with CVSS. What matters is that this vector matches what defenders fear most in edge / management products: remote reachability + auth bypass + system-wide integrity risk.

Why SD-WAN makes this kind of bug uniquely dangerous
SD-WAN is designed to centralize trust
In classic networking, misconfigurations and compromises often propagate slowly because control is distributed: CLI sessions, per-device configs, manual change windows.
SD-WAN changes the physics:
- The controller is the declarative truth.
- The manager is the operational orchestrator.
- The fabric is the execution environment.
That is precisely why NVD calling out NETCONF-backed manipulation of SD-WAN configuration is a red siren. (NVD)
NETCONF isn’t “just another interface.” In many deployments it’s a programmatic path to push, pull, and reconcile configuration state across domains. When attackers reach it from a privileged foothold, the compromise shifts from “device access” to “state control.”
Attackers don’t need data theft to win, they can win by changing reality
A sophisticated actor targeting SD-WAN may prioritize:
- altering routing intent to enable interception,
- adding “peers” to insert themselves into control relationships,
- modifying segmentation and security policy to open paths,
- degrading availability as a decoy while persistence is established elsewhere.
That’s why the best response posture is not only “patch the box,” but “prove the fabric’s intended state equals its actual state.”
What the public intrusion chain tells us, and why the downgrade move matters
Cisco Talos describes active exploitation and notes evidence of malicious activity going back at least three years (2023). (Blog Cisco Talos)
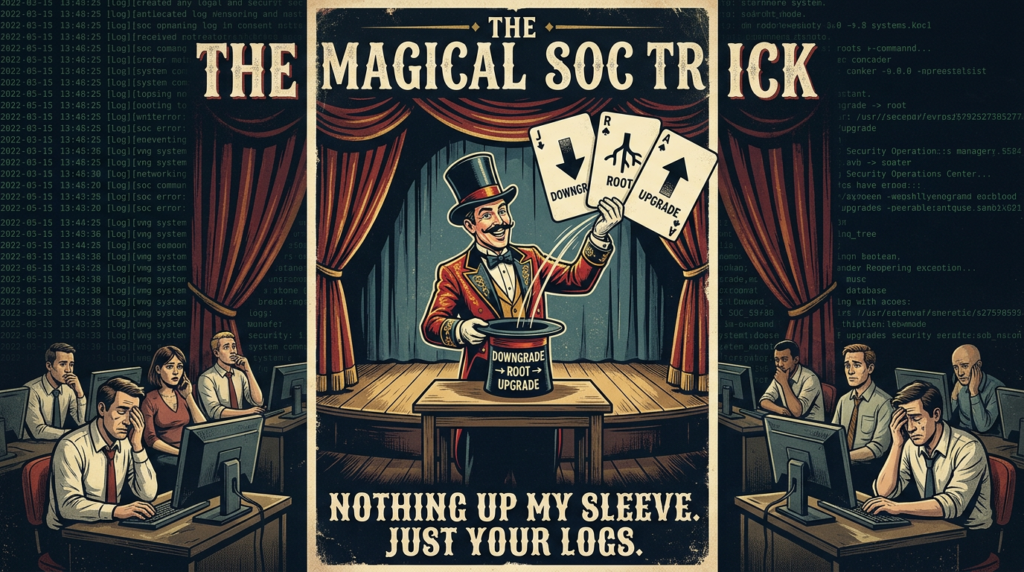
Rapid7 adds a concrete detail defenders should internalize: at disclosure time, Talos outlined that actors used CVE-2026-20127 for initial access, then downgraded the software version for post-exploitation. After downgrade, they exploited CVE-2022-20775 to escalate privileges and gain root access, then restored the original firmware to avoid detection. (Rápido7)
This pattern is not random. It’s a response to modern patching reality:
- Many orgs patch eventually.
- Attackers want persistence across patch cycles.
- Downgrade + exploit a known local privesc can produce durable root-level control, then you “return” the system to a “healthy-looking” version to survive casual checks.
The CVE they chained is not hypothetical. NVD describes CVE-2022-20775 as a vulnerability in the CLI of Cisco SD-WAN Software where an authenticated local attacker can run a maliciously crafted command and execute arbitrary commands as root; Cisco released updates and no workaround exists. (NVD)
So the combined mental model becomes:
- CVE-2026-20127 gives you an admin foothold remotely without creds. (NVD)
- CVE-2022-20775 can help convert that foothold into root-level execution after the downgrade maneuver. (NVD)
Affected components and why naming confusion can hide exposure
NVD is explicit: affected products include Controlador Cisco Catalyst SD-WAN (formerly vSmart) and Cisco Catalyst SD-WAN Manager (formerly vManage). (NVD)
That “formerly” clause is a common failure mode during incident response. Asset inventories, firewall rules, monitoring dashboards, and runbooks might still say “vManage” and “vSmart,” while executives and threat intel say “Catalyst SD-WAN.”
If your internal search for “Catalyst SD-WAN” returns nothing, that does not mean you’re safe. It may mean your environment is labeled with the older names.
Patch guidance that matters, the minimum you should communicate upstream
Rapid7’s writeup includes specific upgrade targets by major version families, and it emphasizes urgency and lack of workaround recommendations at publication time. (Rápido7)
Quick reference table, what to upgrade to
| SD-WAN major line (as referenced publicly) | Minimum fixed target (public guidance) | Why this matters |
|---|---|---|
| 20.11 | 20.12.6.1+ | closes auth bypass path (Rápido7) |
| 20.12.5 | 20.12.5.3+ | closes auth bypass path (Rápido7) |
| 20.12.6 | 20.12.6.1+ | closes auth bypass path (Rápido7) |
| 20.13 / 20.14 / 20.15 | 20.15.4.2+ | closes auth bypass path (Rápido7) |
| 20.16 / 20.18 | 20.18.2.1+ | closes auth bypass path (Rápido7) |
Two practical takeaways:
- If you cannot patch within hours, shrink exposure immediately. This is an auth bypass with network reachability and no required user interaction. (NVD)
- Your “done” state is not “box upgraded,” but “box upgraded + no evidence of rogue peers / tampered config state.”
What to hunt for, evidence that actually correlates to this campaign
Cisco Talos is unusually direct about what to look for. The first and most critical indicator is control de eventos de peering de conexión in SD-WAN logs, which may indicate an attempt at initial access via CVE-2026-20127. Talos says peering events require manual validation to confirm legitimacy, and it provides a validation checklist. (Blog Cisco Talos)
The peering-event validation checklist you can operationalize today
Talos’ checklist items include validating:
- timestamps vs normal change windows,
- public IP ownership vs authorized ranges,
- peer system IP vs documented topology,
- peer type (vmanage, vsmart, vedge, vbond) vs expected roles,
- correlation of repeated events from same IP,
- correlation with authentication logs and change records. (Blog Cisco Talos)
That’s the backbone of your detection logic: not “signature for exploit,” but “signature for control-plane trust violations."
A sample log line you should recognize
Talos includes a sample log entry with fields like control-connection-state-change, peer-type:vmanage, peer-system-ipy public-ip. (Blog Cisco Talos)
You don’t need to memorize the exact string. You need your monitoring to extract those fields and your analysts to know what “weird” looks like.
Copy-pastable log triage, fast checks before you build perfect detections
The goal here is speed and coverage, not elegant tooling.
1) Grep for control connection peering events
# Adjust paths for your platform; the intent is to find control-connection and peering state changes.
sudo grep -RInE "control-connection|peering|peer-type|VDAEMON_0" /var/log 2>/dev/null | head -n 200
If you find events, pivot on:
- public IP not owned by you,
- peering outside normal windows,
- new peer types appearing unexpectedly,
- repetitive events that look like probing.
This maps directly to Talos’ recommended initial analysis. (Blog Cisco Talos)
2) Detect suspicious downgrade / revert behaviors
Talos calls out “unexpected and unauthorized version downgrades and upgrades accompanied by a system reboot” and even gives example log language such as “Software upgrade not confirmed. Reverting…” (Blog Cisco Talos)
sudo grep -RInE "revert|downgrade|upgrade not confirmed|Waiting for upgrade confirmation" /var/log 2>/dev/null | head -n 200
Any downgrade pattern should be treated as high priority because the publicly described intrusion chain uses downgrade as a stepping stone to root. (Rápido7)
3) Hunt for evidence of log wiping and “too-clean” systems
Talos lists high-fidelity indicators such as abnormally small logs, missing history, log truncation (syslog, wtmp, lastlog, cli-history, bash_history), and mismatched histories (cli-history present, bash history absent). (Blog Cisco Talos)
# Look for suspiciously tiny log files (tune threshold to your environment).
sudo find /var/log -type f -size -2k -print -exec ls -lh {} \\; 2>/dev/null | head -n 200
A “clean” system is not necessarily a healthy system.
SIEM-friendly detection ideas, build once, keep forever
Below are examples you can adapt. They are intentionally defensive and avoid exploit-enabling detail.
Splunk, anomalous peering events by unknown public IP
index=sdwan sourcetype=*
("control-connection-state-change" OR "peering" OR "peer-type")
| rex field=_raw "peer-type:(?<peer_type>\\w+)"
| rex field=_raw "public-ip:(?<public_ip>[0-9\\.]+)"
| rex field=_raw "peer-system-ip:(?<peer_system_ip>[0-9\\.]+)"
| stats count min(_time) as first_seen max(_time) as last_seen values(peer_type) as peer_types values(peer_system_ip) as peer_system_ips by public_ip
| where count > 3
Then enrich public_ip against your authorized IP ranges. That’s straight from the Talos “manual validation” worldview. (Blog Cisco Talos)
KQL concept, peering outside change windows
SdwanLogs
| where Message has_any ("control-connection", "peering", "peer-type")
| extend PeerType = extract(@"peer-type:(\\w+)", 1, Message)
| extend PublicIP = extract(@"public-ip:([0-9\\.]+)", 1, Message)
| summarize Events=count(), FirstSeen=min(TimeGenerated), LastSeen=max(TimeGenerated) by PublicIP, PeerType
| where Events > 5
The key is not the query syntax; it’s the model: treat “unexpected peers” as potential initial access. (Blog Cisco Talos)
Incident response priorities that match the attacker’s advantages
Priority 1: remove internet reachability to management/control surfaces
Auth bypass means credentials aren’t the chokepoint. Your chokepoint is exposure.
Do the blunt thing first:
- remove internet routing to management interfaces,
- enforce allowlists from jump hosts,
- segment controller/manager management networks,
- monitor for any newly added inbound paths.
This aligns with the risk framing that exploitation is remote and unauthenticated. (NVD)
Priority 2: patch, but also prevent downgrade games
The public reporting and Talos discussion of downgrade as part of the chain suggests you should operationalize “no silent downgrade” controls. (Rápido7)
Concrete ideas:
- alert on any version change events,
- require explicit approval workflows for upgrades/downgrades,
- store hashes / manifests of deployed images,
- maintain immutable logs off-box.
Priority 3: verify fabric integrity, not just device integrity
Because NVD explicitly calls out NETCONF access enabling manipulation of SD-WAN fabric configuration, you need a configuration truth process: exports, diffs, baselines. (NVD)
A practical baseline comparison pattern:
# Pseudocode style: export intended config from your source of truth and compare to live.
# Replace with your tooling for config exports.
git show HEAD:sdwan/intended_config.json > intended.json
curl -s -k -H "Authorization: Bearer $TOKEN" <https://sdwan-manager/api/config/export> > live.json
jq -S . intended.json > intended.sorted.json
jq -S . live.json > live.sorted.json
diff -u intended.sorted.json live.sorted.json | head -n 200
You’re not trying to be perfect on day one. You’re trying to catch “someone changed the network.”
How this maps to a broader pattern, edge devices as persistence infrastructure
Talos explicitly frames UAT-8616 as part of a continuing trend: threat actors targeting network edge devices to establish persistent footholds into high-value orgs, including critical infrastructure. (Blog Cisco Talos)
The operational pattern looks like this:
- Exploit boundary device to avoid endpoint telemetry.
- Pivot into control/management layers.
- Convert access into durable trust manipulation.
- Hide by restoring “expected” versions and cleaning logs.
The downgrade-then-restore detail is the punchline: modern defenders check “are we patched?” Attackers ask “can we make you think you’re patched?” (Rápido7)
Related CVEs that matter for defenders investigating CVE-2026-20127
CVE-2022-20775, the privesc companion in the publicly described chain
NVD describes CVE-2022-20775 as a Cisco SD-WAN CLI vulnerability that allows an authenticated local attacker to execute arbitrary commands as root due to improper access controls; Cisco shipped updates and no workaround exists. (NVD)
In the context of CVE-2026-20127, it matters because public reporting and Talos indicate attackers used downgrade tactics and then exploited CVE-2022-20775 to reach root. (Rápido7)
So if you’re investigating an environment, don’t treat CVE-2026-20127 as “the only thing.” Look for evidence of root-level activity that would be consistent with a privesc stage.
CVE-2026-20127 is the kind of incident where teams lose time not because they lack patches, but because they lack a tight loop from exposure discovery → evidence collection → risk verification → response documentation. The painful part is that your “ground truth” is distributed: edge appliances, controller logs, config state, change records, and sometimes incomplete telemetry because attackers actively clear history. (Blog Cisco Talos)
If you’re already using Penligent as an AI-assisted penetration testing and verification platform, the most natural fit here is not “exploit generation.” It’s repeatable verification: enumerating externally reachable management surfaces, validating whether risky paths are exposed, and producing artifacts you can attach to a ticket or an executive update. When the question is “are we exposed and are we clean,” speed and evidence quality beat perfect prose.
Referencias
- CVE-2026-20127 PoC, What We Know, What We Don’t, and What You Should Do Today — https://www.penligent.ai/hackinglabs/cve-2026-20127-poc-what-we-know-what-we-dont-and-what-you-should-do-today/ (Penligente)
- CVE-2026-20127 and the SD-WAN Control Plane Trust Problem — https://www.penligent.ai/hackinglabs/cve-2026-20127-and-the-sd-wan-control-plane-trust-problem/ (Penligente)
- What Is Zero Trust Security, the Model Behind Modern Breach Containment — https://www.penligent.ai/hackinglabs/what-is-zero-trust-security-the-model-behind-modern-breach-containment/ (Penligente)
- CVE-2025-53770 ToolShell and the SharePoint Trust Problem — https://www.penligent.ai/hackinglabs/es/cve-2025-53770-toolshell-and-the-sharepoint-trust-problem-that-patching-alone-doesnt-solve/ (Penligente)
- NVD entry for CVE-2026-20127 — https://nvd.nist.gov/vuln/detail/CVE-2026-20127 (NVD)
- Cisco Talos threat advisory on UAT-8616 exploitation — https://blog.talosintelligence.com/uat-8616-sd-wan/ (Blog Cisco Talos)
- Rapid7 ETR summary and mitigation guidance — https://www.rapid7.com/blog/post/etr-critical-cisco-catalyst-vulnerability-exploited-in-the-wild-cve-2026-20127/ (Rápido7)
- NVD entry for CVE-2022-20775 — https://nvd.nist.gov/vuln/detail/CVE-2022-20775 (NVD)
- IT Pro
- TechRadar