Lo que ocurrió, en términos sencillos
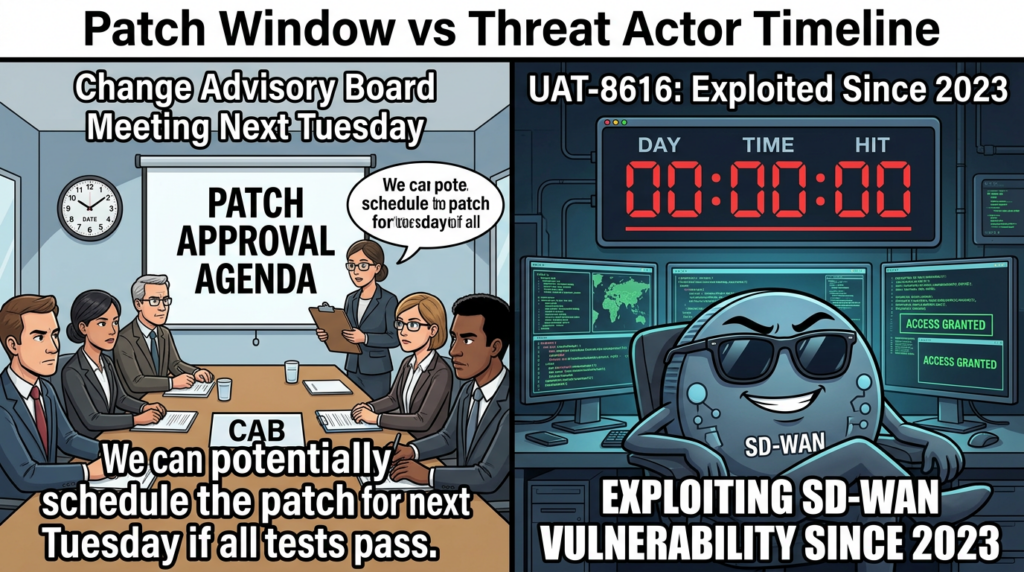
Un día cero de máxima gravedad, CVE-2026-20127, afecta Controlador Cisco Catalyst SD-WAN anteriormente vSmart y Cisco Catalyst SD-WAN Manager anteriormente vManage. Se ha publicado un PoC público, y se ha observado explotación en la naturaleza que se remonta al menos a 2023. (Noticias sobre ciberseguridad)
A alto nivel, la cuestión permite atacante remoto no autenticado a evitar la autenticación enviando solicitudes falsas, luego inicie sesión como un usuario interno no root con privilegios elevadosque es suficiente para manipular la configuración del tejido SD-WAN a través de NETCONF. (NVD)
Cisco Talos rastrea el clúster de explotación como UAT-8616describiéndola como sofisticada y centrada en componentes SD-WAN. (Blog Cisco Talos)
Por qué este día cero es especialmente peligroso para las redes reales
SD-WAN no es "un servidor de aplicaciones más". Cuando los atacantes obtienen acceso privilegiado a la plano de gestión y controlno están tratando de robar una sola base de datos. Están tratando de reescribir la realidad de la red:
- Introducir cambios de política en todos los sitios
- Redirigir el tráfico o crear desvíos de inspección
- Añadir o suplantar componentes SD-WAN de confianza
- Cree una persistencia duradera y difícil de ver dentro del tejido superpuesto (Noticias Hacker)
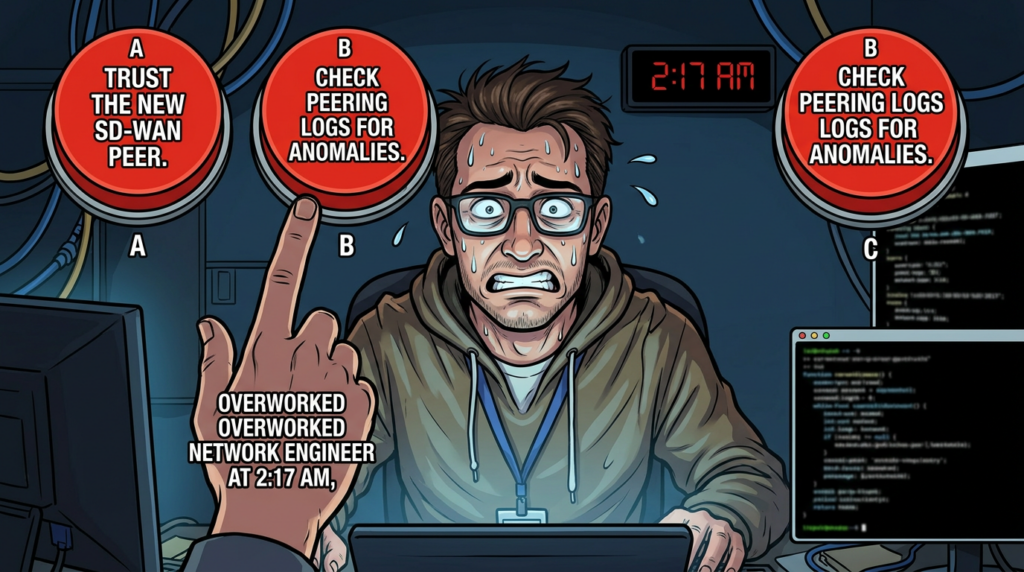
La guía de caza de amenazas multiagencia describe un concepto clave que importa desde el punto de vista operativo: el actor puede crear un compañero rebelde que aparece brevemente como componente SD-WAN de confianza y puede realizar "acciones de confianza" en el plano de gestión/control. (Cyber.gov.au)
Por eso los defensores siguen repitiendo una regla contundente: no exponga las interfaces de gestión de SD-WAN a Internet-el parcheo es obligatorio, pero la reducción de la exposición es lo que te hace ganar tiempo. (Noticias Hacker)
Resumen técnico de CVE-2026-20127
Clase de vulnerabilidad e impacto
CVE-2026-20127 es un anulación de la autenticación en el mecanismo de autenticación de peering de Cisco Catalyst SD-WAN Controller y Manager. Una explotación exitosa permite a un atacante obtener privilegios administrativos e iniciar sesión como una cuenta interna no root con privilegios altos, y luego utilizar ese acceso para interactuar con NETCONF y manipular la configuración del tejido SD-WAN. (NVD)
Explotación observada y calendario
- La explotación se ha observado "in the wild", con pruebas que se remontan al menos a 2023. (Noticias sobre ciberseguridad)
- Cisco Talos agrupa la actividad como UAT-8616. (Blog Cisco Talos)
Una cadena común en el mundo real: auth bypass to root
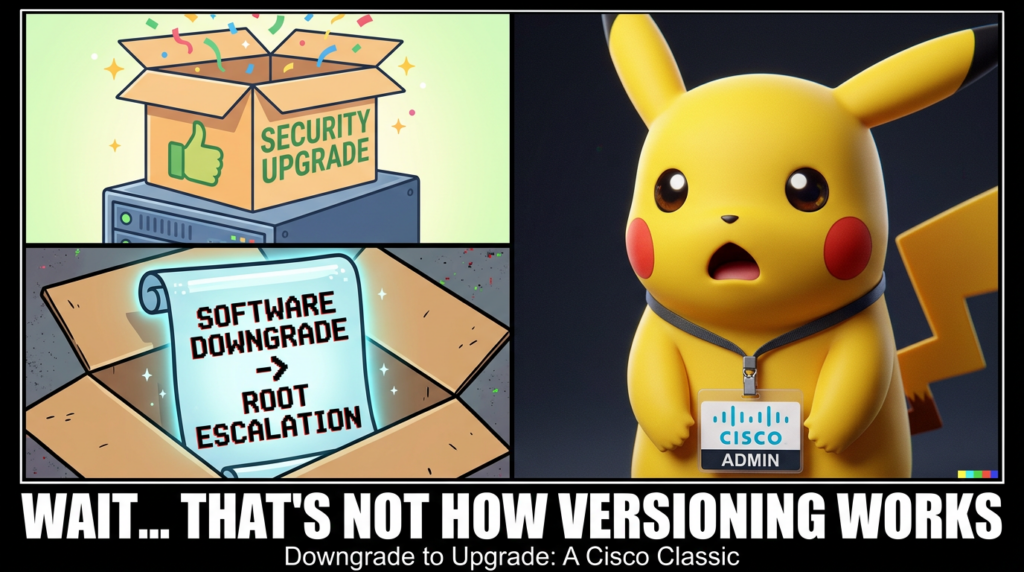
Múltiples fuentes describen un patrón práctico: tras el acceso inicial a través de CVE-2026-20127, el actor escala privilegios a través de actualización del software y luego aprovecha CVE-2022-20775 para llegar a la raíz, antes de restaurar las versiones para reducir los indicadores obvios. (Blog Cisco Talos)
CVE-2022-20775 es una vulnerabilidad de escalada de privilegios en la CLI del software Cisco SD-WAN que puede permitir comandos elevados como root bajo ciertas condiciones. (NVD)
CVEs SD-WAN de Cisco relacionadas a las que debería dar prioridad junto con CVE-2026-20127
Los atacantes rara vez se detienen en la primera puerta. Múltiples escritos y referencias de proveedores destacan dos vulnerabilidades adicionales de SD-WAN Manager confirmadas como explotadas in the wild:
- CVE-2026-20122 Cisco Catalyst SD-WAN Manager sobreescritura arbitraria de archivos
- CVE-2026-20128 Divulgación de información sobre Cisco Catalyst SD-WAN Manager (Tenable)
Trátelos como parte de la misma clase de incidente operativo: focalización en el borde/plano de control con maduración rápida de las hazañas.
Cadena de ataque, asignada a lo que los defensores pueden ver realmente
Esta sección comprime el oficio en una secuencia que puedes cazar.
Etapa 1 Acceso inicial mediante abuso de peering en el plano de control
Cisco Talos destaca que una de las "actividades más críticas que hay que buscar" en una fase temprana es control de eventos de peering de conexión en los registros de SD-WAN, porque pueden indicar intentos de acceso inicial a través de CVE-2026-20127. Talos pide un escrutinio extra en vGestionar los tipos de peering. (Blog Cisco Talos)
La guía de caza también se centra en gran medida en los comportamientos de peering anómalos y la telemetría relacionada en el registro de vSmart. (Cyber.gov.au)
Etapa 2 Acceso privilegiado a través de una cuenta no root con privilegios elevados
Una vez que el atacante puede iniciar sesión como usuario interno con privilegios elevados, el plano de control de la SD-WAN se convierte en el objetivo. Uno de los pivotes clave de los que se habla en los informes públicos es el uso de NETCONF. (Noticias Hacker)
Fase 3 Escalada de raíz mediante downgrade y CVE-2022-20775
La guía de caza multiinstitucional señala explícitamente una secuencia de descenso seguida inmediatamente por la explotación de CVE-2022-20775. (Cyber.gov.au)
Esto es importante porque proporciona a los defensores un asidero de correlación temporal: artefactos de downgrade + marcadores de reinicio + señales de escalada de privilegios.
Fase 4 Persistencia y evasión de la defensa
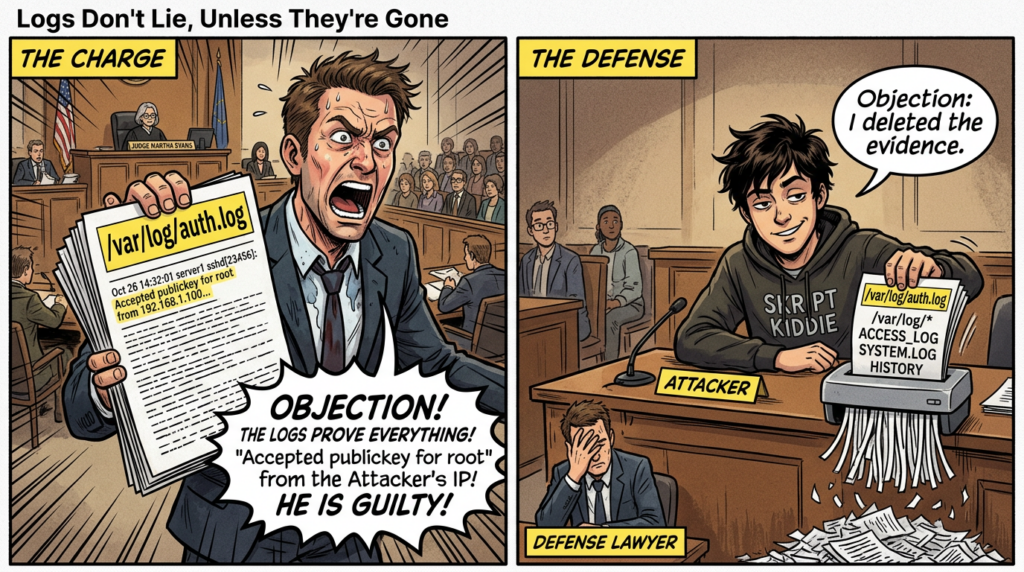
Dos señales repetidamente enfatizadas:
- Claves autorizadas SSH añadidas para acceso privilegiado
- Los esfuerzos para eliminar los troncos bajo /var/log y el historial de comandos (Noticias Hacker)
La guía de caza también hace hincapié en centralizar los registros fuera del dispositivo específicamente para reducir la eficacia de este estilo de limpieza.
Comprobación rápida de la exposición, qué confirmar en la primera hora
1 Confirme si su plano de gestión es accesible por Internet
Si vManage o las interfaces de gestión del controlador están expuestas a Internet, trátelo como una emergencia. Los informes públicos enfatizan que la exposición es un factor de riesgo importante para el compromiso. (Noticias Hacker)
Como mínimo, quieres:
- ACL estricta allowlists de admin saltar hosts
- Acceso sólo VPN para la gestión
- ninguna entrada pública directa a la interfaz de usuario de gestión, SSH o NETCONF (a menos que su arquitectura lo requiera explícitamente y esté estrictamente controlada)
2 Identificar versiones y postura ante los parches
Los informes de los proveedores y de los estudios de seguridad indican que hay parches disponibles y que se recomienda aplicarlos de inmediato. (Tenable)
Dado que las páginas de avisos de Cisco pueden tener el acceso restringido en algunos entornos, confíe en su inventario interno de software de Cisco y compárelo con el aviso oficial en su proceso de cambio. (No "adivine" versiones a partir de blogs: utilice la salida de versiones de su propio dispositivo y la lista de versiones fijas de Cisco).
3 Asume el compromiso si encuentras artefactos de degradación
La guía de caza proporciona una idea concreta de detección: una actualización de software en vSmart a menudo precede a la escalada, normalmente desencadena un reinicio y produce artefactos distintivos de cambio de versión (con marcadores de ejemplo como cdb_set y la inicialización de la instalación maestra).
Caza de amenazas, registros que extraer y qué consultar
Lugares de registro a los que se hace referencia repetidamente en las orientaciones
Múltiples fuentes públicas señalan a los defensores archivos de registro específicos para identificar patrones de acceso sospechosos y comportamientos de degradación.
A partir de la información pública y las referencias de las orientaciones de caza:
/var/log/auth.logpara la aceptación de claves SSH sospechosas (incluidos los patrones root o vmanage-admin) (Noticias Hacker)- Registros relacionados con vdebug utilizados para la correlación de downgrades y reinicios (rutas de ejemplo mostradas en los informes) (Noticias Hacker)
Cómo es la "buena" caza
Deja de buscar un único COI. Esta clase de incidente se caza mejor como correlación de comportamiento:
- suceso inusual en el plano de control
- seguido de anomalías en la bajada de versión o en el reinicio
- seguido de artefactos de autenticación privilegiados
- seguido de actividad NETCONF o cambios de configuración
- seguido de señales de manipulación del registro
Precisamente por eso, la guía de caza publica detecciones estructuradas y hace hincapié en el registro fuera del dispositivo. (Cyber.gov.au)
Consultas y comprobaciones listas para adaptar
Son los siguientes ejemplos del lado del defensor que puedes adaptar a tu entorno. No son códigos de explotación.
Bash triage en el dispositivo, validar rápidamente
# 1) Comprobar la aceptación de claves SSH sospechosas
sudo grep -E "Clave pública aceptada para (root|vmanage-admin)" /var/log/auth.log | tail -n 200
# 2) Búsqueda rápida de cambios repentinos de versión / downgrade en los logs tipo vdebug
sudo grep -RInE "cdb_set|master install|older_version|system-reboot-issued" /var/log /var/volatile/log 2>/dev/null | head -n 200
# 3) Identificar las authorized_keys SSH recientemente modificadas para cuentas privilegiadas
sudo find /home -maxdepth 3 -type f -name "authorized_keys" -printf "%TY-%Tm-%Td %TT %p\\n" 2>/dev/null | sort
Por qué estas comprobaciones: la guía de caza señala explícitamente "clave pública SSH de root aceptada" como de alta gravedad y describe los artefactos de downgrade y los marcadores de reinicio como una secuencia útil.
Ejemplo Splunk, autentificación de privilegios y patrones de pares sospechosos
index=sdwan sourcetype=linux_secure ("Clave pública aceptada para root" O "Clave pública aceptada para vmanage-admin")
| stats count min(_time) as firstSeen max(_time) as lastSeen values(src) as srcIP values(host) as host by user
| sort -lastSeen
Ejemplo elástico, aceptación de la clave auth.log
GET logs-*/_search
{
"consulta": {
"bool": {
"must": [
{ "match_phrase": { "mensaje": "Accepted publickey" } }
],
"should": [
{ "match_phrase": { "mensaje": "for root" } },
{ "match_phrase": { "message": "for vmanage-admin" } }
],
"minimum_should_match": 1
}
},
"size": 200,
"sort": [{ "@timestamp": "desc" }]
}
Lógica de estilo Sigma inspirada en la estructura de la guía de caza publicada
La guía de caza proporciona una entrada de detección estructurada para "Descenso de aplicaciones" y describe condiciones como artefactos de cambio de versión, inicialización de instalación maestra y marcadores de reinicio.
Se puede traducir conceptualmente en una regla similar a Sigma:
título: Cisco SD-WAN vSmart sospechoso secuencia de downgrade
logsource:
producto: cisco_sdwan
detección:
downgrade_markers:
- 'cdb_set'
- 'Establecer software'
- versión_antigua
install_markers:
- 'instalación maestra'
reboot_markers:
- 'system-reboot-issued'
condición: (1 de downgrade_markers) y (1 de install_markers) y (1 de reboot_markers)
nivel: alto
falsos positivos:
- rollback autorizado
- actualización fallida fallida
Esto refleja la lógica de secuencia mostrada en la guía y mantiene el mismo encuadre de falsos positivos.
Mitigación y endurecimiento que reducen realmente el riesgo
La estrategia de los parches, única solución duradera
Para CVE-2026-20127, múltiples fuentes de buena reputación enfatizan la aplicación inmediata de parches porque se ha observado la explotación y un PoC es público. (Noticias sobre ciberseguridad)
Al mismo tiempo, la aplicación de parches por sí sola no es suficiente si su plano de gestión está expuesto a Internet o si su registro es sólo local.
Reducción de la exposición e higiene del plano de control
La sección de mitigación de la guía de caza es contundente:
- utilice el concepto de versión "golden star" recomendado por el vendedor
- parche tan pronto como sea posible
- filtrar la red para que sólo las IP de administración legítimas y los dispositivos periféricos puedan acceder a las interfaces sensibles
- centralizar el registro fuera del dispositivo
Este último punto es fundamental porque la actividad posterior a la vulneración incluye la limpieza de registros. Si los registros sólo permanecen en el dispositivo, se está dejando que el atacante decida lo que se puede probar más tarde. (Cyber.gov.au)
Tratar NETCONF como una API privilegiada del plano de control
NETCONF aparece en los informes públicos como un mecanismo al que un atacante puede acceder tras eludir la autenticación, lo que permite manipular la configuración del tejido SD-WAN. (NVD)
Barandillas prácticas:
- restringir quién puede acceder a TCP 830 en el plano de gestión
- alertar sobre sesiones NETCONF inusuales, especialmente poco después de anomalías de peering o reinicios
- línea de base de la automatización "normal" de la gestión para que destaquen las anomalías
Manual de respuesta a incidentes, si sospecha que se ha producido un ataque
1 Contener primero, investigar después
Si ve eventos de peering sospechosos, artefactos de downgrade o aceptación de clave raíz:
- aislar el acceso al plano de gestión a un pequeño conjunto de hosts de salto
- hacer instantáneas y conservar los registros fuera del dispositivo inmediatamente
- contratar procesos de apoyo de proveedores si es necesario
2 Caza de la persistencia
Dado que los pasos posteriores a la infracción incluyen la adición de claves autorizadas SSH y la creación de usuarios locales que imitan a los usuarios existentes, priorice:
- comparar las listas de usuarios actuales con las últimas conocidas
- revisión de authorized_keys para cuentas privilegiadas
- validación de la configuración de inicio de sesión root y modificaciones inesperadas (Noticias Hacker)
3 Validar la integridad de la configuración
Incluso si no encuentra malware, el compromiso de SD-WAN puede ser "primero la configuración". Confirme que la política, las rutas y las relaciones de confianza coinciden con su estado previsto.
Cuando un problema de dispositivos periféricos de alto impacto pasa de "explotación limitada" a "PoC pública", los equipos suelen tener dos cuellos de botella: visibilidad de los activos y verificación a escala. Aquí es donde un flujo de trabajo asistido por IA puede ser práctico sin convertirse en un "teatro de IA".
Penligent puede utilizarse como una cabina centrada en el operador para las tareas de validación defensiva que ya necesita realizar: enumerar las superficies de gestión accesibles desde el exterior, confirmar qué puntos finales SD-WAN están expuestos y ejecutar comprobaciones repetibles para demostrar que las mitigaciones son eficaces después de las ventanas de parches. La clave es mantenerlo en un ámbito autorizado y controlado y utilizarlo para automatizar las partes aburridas (confirmación de inventario, comprobaciones de exposición y recopilación de pruebas), de modo que los ingenieros puedan dedicar tiempo a las partes que requieren criterio.
Un segundo uso natural es la elaboración de informes y la repetibilidad. Los incidentes de SD-WAN están llenos de preguntas de "demuéstrelo" por parte de la dirección: qué sistemas estuvieron expuestos, cuándo se parcheó, qué pruebas demuestran que estamos limpios. La automatización de estas comprobaciones en un libro de ejecución coherente reduce tanto el tiempo de respuesta como la posibilidad de que alguien olvide una fuente de registro o pase por alto una señal de degradación.
Cuadro sinóptico, qué priorizar ahora mismo
| Artículo | Por qué es importante | Qué hacer hoy |
|---|---|---|
| CVE-2026-20127 | Evasión de autenticación, CVSS 10, explotación in-the-wild, PoC público | Parchee inmediatamente, restrinja la exposición de la dirección (Noticias sobre ciberseguridad) |
| Señales de peering no autorizadas | Indicador precoz de los primeros intentos de acceso | Revise los eventos de peering de conexión de control, especialmente los tipos de peering de vManage (Blog Cisco Talos) |
| Artefactos de degradación | A menudo precede a la escalada raíz | Alerta de descenso de categoría + marcadores de secuencia de reinicio |
| CVE-2022-20775 | Ruta de escalada de privilegios utilizada tras el acceso | Asegúrese de que las versiones son fijas y auditoría para la degradación a continuación, la escalada de privilegios (NVD) |
| Claves SSH root o vmanage-admin | Persistencia y señal de compromiso de alta confianza | Caza Clave pública aceptada y revisar authorized_keys (Cyber.gov.au) |
| CVE-2026-20122 / CVE-2026-20128 | Fallos adicionales explotados de SD-WAN Manager | Parchee y reduzca la superficie de ataque en Manager (Noticias Hacker) |
Referencias
https://cybersecuritynews.com/poc-exploit-cisco-sd-wan-0-day-vulnerability/ https://thehackernews.com/2026/02/cisco-sd-wan-zero-day-cve-2026-20127.html https://www.darkreading.com/vulnerabilities-threats/cisco-sd-wan-zero-day-exploitation-3-years https://nvd.nist.gov/vuln/detail/CVE-2026-20127 https://blog.talosintelligence.com/uat-8616-sd-wan/ https://www.tenable.com/blog/cve-2026-20127-cisco-catalyst-sd-wan-controllermanager-zero-day-authentication-bypass https://www.cyber.gov.au/sites/default/files/2026-02/ACSC-led Guía de Cisco SD-WAN Hunt.pdf https://nvd.nist.gov/vuln/detail/CVE-2022-20775 https://www.cisco.com/c/en/us/support/docs/csa/cisco-sa-sd-wan-priv-E6e8tEdF.html https://thehackernews.com/2026/03/cisco-confirms-active-exploitation-of.html https://www.securityweek.com/cisco-warns-of-more-catalyst-sd-wan-flaws-exploited-in-the-wild/ https://www.helpnetsecurity.com/2026/03/05/cisco-cve-2026-20128-cve-2026-20122-exploited/ https://penligent.ai/ https://www.penligent.ai/hackinglabs/openclaw-virustotal-the-skill-marketplace-just-became-a-supply-chain-boundary/


