Oracle did not leave CVE-2026-21992 for the next routine quarterly patch cycle. It published a standalone Security Alert for a vulnerability affecting Oracle Identity Manager and Oracle Web Services Manager, and both Oracle and NVD describe it as remotely exploitable without authentication and capable of leading to remote code execution. The affected supported versions are 12.2.1.4.0 and 14.1.2.1.0, and NVD’s wording goes further by saying successful attacks can result in takeover of the affected products. (Oracle)
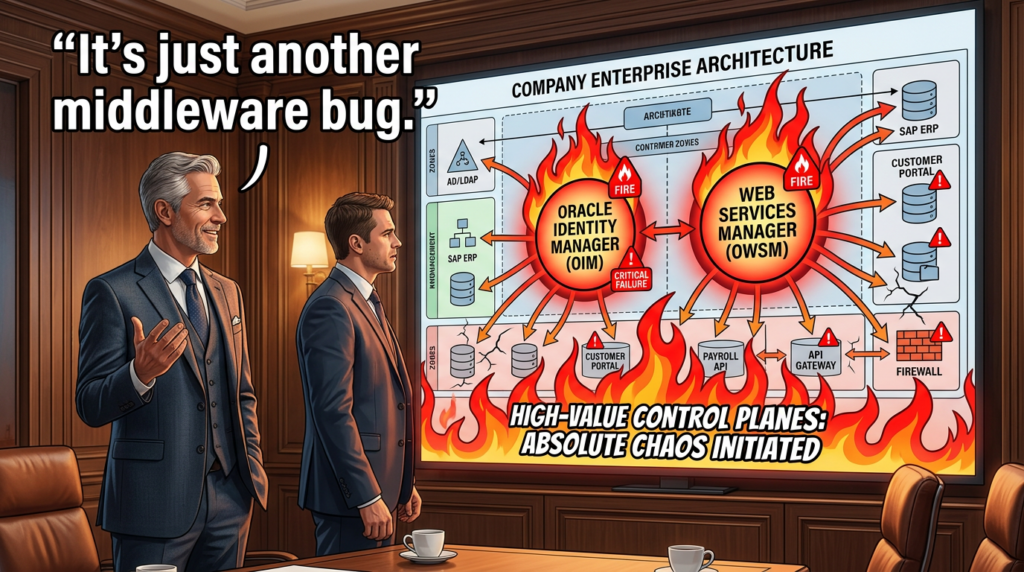
That already puts the issue in the highest-response tier for most enterprises. But the more important point is where the bug lands. Oracle Identity Manager sits in the identity lifecycle and governance layer. Oracle Web Services Manager sits in the security policy and trust-management layer for web services. A critical unauthenticated flaw in either product is bad. A single CVE that reaches both products at once is the kind of event defenders should treat as a control-plane problem, not merely a middleware patch ticket. (Oracle Docs)
The public record is still incomplete. Oracle has not published a root-cause write-up. Oracle has not publicly confirmed exploitation in the wild. Public reporting has also noted that, at least at the time Tenable published its analysis, there was no public proof of concept. That uncertainty does not lower the urgency. It changes the right response: patch fast, reduce reachability, verify trust boundaries safely, and do not invent details that are not yet public. (Oracle)
What Oracle and NVD currently confirm
The public facts are straightforward and unusually serious. Oracle’s advisory says CVE-2026-21992 affects Oracle Identity Manager and Oracle Web Services Manager, is remotely exploitable without authentication, and may result in remote code execution. NVD names the affected components more precisely: REST WebServices in Oracle Identity Manager and Web Services Security in Oracle Web Services Manager. NVD also records the CVSS 3.1 vector as AV:N, AC:L, PR:N, UI:N, S:U, C:H, I:H, A:H, which is the standard signature of a low-complexity network bug with complete confidentiality, integrity, and availability impact if exploited successfully. (Oracle)
Oracle’s advisory lists supported affected versions as 12.2.1.4.0 and 14.1.2.1.0 for both products. It also makes an important support-policy statement that many organizations gloss over during crisis triage: patches released through Oracle’s Security Alert program are only provided for versions still under Premier Support or Extended Support, and Oracle explicitly says earlier releases are likely affected even if they were not tested in the alert process. That means version inventory has to include unsupported legacy estates as a risk question, not just supported production clusters as a patch question. (Oracle)
Oracle also notes that Oracle Web Services Manager is installed with an Oracle Fusion Middleware Infrastructure. That matters operationally because some teams will not think of themselves as “running OWSM” even though it is present as part of a broader Oracle middleware footprint. During triage, the question is not whether a business unit remembers deploying the product name. The question is whether the relevant software and components are present, reachable, and still on affected versions. (Oracle)
A concise way to frame the public record is this: Oracle has confirmed a critical unauthenticated remote code execution issue affecting identity and policy-control products; NVD has confirmed takeover impact; Oracle has published the affected supported versions; Oracle has not published the full technical root cause; and public reporting remains cautious about exploitation status. That is enough to act on immediately. (Oracle)
Why these products are not ordinary middleware
Oracle’s own product documentation describes Oracle Identity Management as a unified security platform for managing user lifecycle and secure access across enterprise resources. In practice, the naming across Oracle’s docs and APIs can be confusing: the CVE record uses Oracle Identity Manager, while many Oracle documentation pages and REST interfaces use Oracle Identity Governance, or OIG, and the URI space frequently begins with /iam/governance/. Defenders should assume all of those names belong in the same investigation vocabulary when they are tracing affected services, API surfaces, deployment paths, and patch status. (Oracle Docs)
Oracle’s Identity Governance documentation makes the risk profile plain. Its SCIM and REST services cover self-service, users, roles and groups, organizations, and password policy management. Oracle says the SCIM service is deployed by default when Oracle Identity Governance is deployed, and the documentation explicitly states that SCIM is configured by default to run on both HTTP and HTTPS ports unless administrators change that behavior. This is not a theoretical back-end component that only exists in an internal SDK. It is a documented web-facing control surface for identity operations. (Oracle Docs)
Oracle Web Services Manager is equally important for a different reason. Oracle describes OWSM as a policy framework to manage and secure web services consistently across an organization. Its documentation says it supports authentication, authorization, message protection, identity propagation, trust configuration, policy management, auditing, rollback, monitoring, and policy attachment across REST and SOAP services. Oracle’s REST API documentation further says the OWSM APIs can manage domain-level configuration properties, token issuer trust documents, policies, and policy sets. If a bug reaches that layer, the risk is not just “a server ran a bad request.” The risk is that the system that enforces or configures security policy itself may become untrusted. (Oracle Docs)
This is why CVE-2026-21992 deserves a different kind of conversation than a generic “critical RCE.” The vulnerable products sit upstream of many other business and technical trust decisions. Identity governance tells systems who a user is, what the user can access, and what lifecycle actions can be performed. Web services policy management tells services what authentication, authorization, trust, token, and message-protection rules to enforce. When those layers are exposed, the blast radius tends to outgrow the server where the initial compromise happened. (Oracle Docs)

What is known, what is not, and why that distinction matters
Defenders often make two opposite mistakes during fast-moving disclosure cycles. One group assumes that every critical unauthenticated RCE already has mature exploit tooling and widespread opportunistic scanning. The other group dismisses urgency because the vendor has not published a full technical breakdown. Both are bad habits.
What is known is solid. Oracle and NVD agree on the affected products, components, supported versions, unauthenticated network attack model, and remote compromise impact. The CWE added by CISA’s ADP in NVD is CWE-306, missing authentication for a critical function, which is directionally useful even though it does not reveal the specific buggy code path. Public reporting from Help Net Security and SecurityWeek also agrees that Oracle shipped an out-of-band fix, not a routine quarterly patch. (Oracle)
What is not known is just as important. Oracle has not published a public root-cause narrative. Oracle has not publicly identified a vulnerable URI, method sequence, or exploit precondition beyond unauthenticated network reachability. Oracle has not clearly stated that the flaw has been exploited in the wild. SecurityWeek explicitly says Oracle did not clearly state exploitation, and Help Net Security likewise says Oracle did not say whether the bug had been exploited as a zero-day. Tenable wrote that there was no public proof of concept at the time of its analysis. (SecurityWeek)
That uncertainty should change how defenders communicate. It is accurate to say that CVE-2026-21992 is severe, unauthenticated, remote, and high priority. It is not accurate to say that exploitation is confirmed, that the root cause is publicly known, or that the exploit chain is identical to any earlier Oracle flaw. Precision matters, especially when you are pushing emergency change approvals, asking for maintenance windows, or briefing an executive team that will later ask what you actually knew on day one. (Oracle)
The 2025 predecessor changes how this should be prioritized
CVE-2026-21992 did not emerge into a vacuum. In October 2025, Oracle patched CVE-2025-61757, another high-severity Oracle Identity Manager flaw in the REST WebServices component. Oracle’s October 2025 CPU text form describes that earlier issue as an unauthenticated HTTP attack that could compromise Identity Manager and result in takeover. In November 2025, CISA added CVE-2025-61757 to its Known Exploited Vulnerabilities catalog. (Oracle)
The public technical analysis of CVE-2025-61757 is what gives this new CVE its practical context. Searchlight Cyber’s write-up showed that the earlier OIM bug involved a centralized SecurityFilter pattern and bypass conditions around routes Oracle intended to leave accessible. Searchlight described how query-string handling and URI matching around WSDL and WADL could let attackers trick the filter into allowing access to protected REST APIs, including paths under /iam/governance/. Searchlight then demonstrated how auth bypass opened access to sensitive administrative or operational REST endpoints. (Searchlight Cyber)
None of that proves CVE-2026-21992 is the same bug, the same exploit path, or even a close code-relative. Oracle has not said that. Tenable explicitly notes the products, versions, and OIM component overlap, and points out that Oracle has not confirmed whether the two vulnerabilities are related. That is the correct posture: acknowledge the resemblance, refuse to invent equivalence. (Tenable)
Still, the resemblance is enough to affect prioritization. CVE-2025-61757 hit the same Identity Manager REST WebServices component, on the same supported OIM versions named in the new advisory, and it later entered KEV after active exploitation evidence emerged. When a fresh critical unauthenticated RCE lands in the same product family, on the same version span, and Oracle chooses to issue a standalone Security Alert, defenders should not wait for a root-cause blog post to decide whether the patch matters. It matters already. (Oracle)
The attack surface is visible in the documentation even without an exploit
One of the most useful things security engineers can do during the early hours of a disclosure is stop treating “no public exploit” as “no public context.” Oracle’s own documentation shows why these products deserve immediate boundary review.
For OIG, Oracle documents multiple REST families and example paths under /iam/governance/. The Application Management REST documentation includes a documented endpoint for searching templates at /iam/governance/applicationmanagement/api/v1/templates. Oracle’s Self Service REST documentation also lists a set of unauthenticated self-service endpoints, including password-reset and self-registration related paths such as /iam/governance/selfservice/api/v1/unauthservice/passwordreset, /iam/governance/selfservice/api/v1/unauthservice/selfregistrationy /iam/governance/selfservice/api/v1/unauthservice/forgotusername. These are important because they show the product already contains both authenticated management-style REST surfaces and intentionally unauthenticated self-service surfaces. Historically, that kind of mixed design has created fertile ground for route-matching mistakes in older enterprise applications. That last point is an architectural inference, not a statement of the current root cause. (Oracle Docs)
For OWSM, Oracle’s docs say the REST APIs can manage token issuer trust documents, policy sets, policy references, and domain configuration properties. Oracle’s endpoint listings include resources such as /v2/trust, /v2/trust/{trustname}, /v2/policyset/{name}, and related policy-reference and config-override APIs. Oracle also says OWSM is used to attach and manage policies for authentication, authorization, secure conversation, tokens, and message protection. Again, the point is not that these exact paths are known-vulnerable in CVE-2026-21992. The point is that the product’s documented control plane is high value by design. Any authentication failure or pre-auth code execution in that layer deserves severe treatment even before the vendor publishes exploit specifics. (Oracle Docs)
There is a second operational lesson in Oracle’s authentication documentation. Oracle’s OIG Access Policy REST docs and OWSM REST docs both document that these resources are meant to require authentication. Oracle’s examples show authenticated cURL access patterns using credentials and TLS material. For defenders, that creates a safe verification baseline: if an endpoint that should require authentication responds anonymously in a way it should not, you have found a problem worth escalating without needing to run a destructive test. (Oracle Docs)

What a realistic attacker gains here
Public advisories tend to flatten all critical middleware bugs into the same sentence: unauthenticated attacker, network access, remote code execution, patch now. That is necessary but not sufficient. The products involved here explain why the business impact may be much more strategic than the typical application-server compromise.
On the identity side, Oracle’s platform documentation and REST documentation show direct control over user lifecycle, secure access, self-service flows, roles, password policies, organizations, and application-related management functions. If an attacker can fully compromise that layer, the obvious risk is code execution on a server. The more dangerous risk is that identity decisions themselves can become attacker-shaped. Account creation, role membership, connector behavior, self-service abuse, password-reset workflows, governance data, and related administrative processes all become suspect in a way that can outlast the initial intrusion. (Oracle Docs)
On the web-services security side, OWSM is the place where policies, trust documents, authentication, authorization, and security behavior are configured and enforced across services. A compromise there can mean changes to the security rules other applications rely on rather than changes to a single business application. Dark Reading captured this operationally by noting that attackers could, in theory, manipulate identities, roles, and policies through OIM and change or disable security policies in OWSM. That is not a vendor-confirmed attack chain, but it is a reasonable downstream consequence given what Oracle says these products are for. (Oracle Docs)
This is also why AI security teams, platform teams, and internal developer-platform teams should pay attention even if they do not think of themselves as “Oracle teams.” Modern model-serving platforms, internal copilots, CI and CD systems, data platforms, private APIs, and agent workflows often inherit trust from corporate IAM and middleware policy layers. If an attacker can corrupt the upstream identity or service-policy authority, later actions against AI systems may look valid because the attacker is no longer sneaking around the control plane. The attacker is standing inside it. That is a structural inference from the product roles, but it is the right mental model for impact assessment. (Oracle Docs)
The first 72 hours should focus on exposure, not theater
The worst response pattern to a vulnerability like this is exploit theater: copying random proof-of-concept snippets from social media, firing noisy scanners at fragile identity systems, and generating more uncertainty than evidence. A better response pattern is disciplined triage.
The first question is inventory. Find every environment that includes Oracle Identity Manager, Oracle Identity Governance, Oracle Web Services Manager, and Oracle Fusion Middleware Infrastructure. Check version strings, deployment records, WebLogic domains, configuration repositories, disaster-recovery sites, training environments, and any “temporary” or “legacy” installations that never made it into the main CMDB. Because Oracle says unsupported earlier versions are likely affected, do not let the inventory stop at currently supported production nodes. (Oracle)
The second question is reachability. Which of those systems can be reached from the internet, partner networks, remote-access VPN ranges, developer jump networks, or shared office subnets? Which are fronted by load balancers, reverse proxies, API gateways, or WAFs? Which expose /iam/governance/ paths or other relevant application routes directly? Which are only assumed to be internal because someone put “admin” in the host name five years ago? Those questions often produce faster risk reduction than the hunt for exploit internals. The value is not merely knowing a server exists. The value is knowing whether an unauthenticated network attacker can actually hit it. (Oracle Docs)
The third question is boundary behavior. For documented endpoints that should require authentication, what response do you get without credentials? For documented self-service endpoints that are supposed to be anonymous, what exactly is exposed and from where? Do you see consistent 401 or 403 behavior at the right places, or do you see accidental 200 responses, verbose error output, or strange redirects? You do not need a weaponized exploit to learn a lot from those answers. (Oracle Docs)
Safe verification examples that do not depend on exploit code
The following checks are designed to answer practical questions about exposure and authentication boundaries. They are not exploit steps and they do not attempt to bypass controls.
Start with documented OIG paths. Oracle documents an authenticated Application Management endpoint at /iam/governance/applicationmanagement/api/v1/templates, and it also documents several unauthenticated self-service routes. A safe baseline test is to compare how those routes behave without credentials.
# Expected to require authentication in a healthy deployment
curl -sk -o /dev/null -D - \
https://oim.example.com/iam/governance/applicationmanagement/api/v1/templates
# Expected to be part of unauthenticated self-service behavior in deployments where exposed
curl -sk -o /dev/null -D - \
"https://oim.example.com/iam/governance/selfservice/api/v1/unauthservice/passwordreset?userId=testuser"
In most environments, the first request should not succeed anonymously. The second request may return application-specific content because Oracle documents it as an unauthenticated self-service route. What matters is not whether both respond. What matters is whether routes that should be gated are actually gated, whether exposed self-service routes are intentional, and whether either path is reachable from places it should not be reachable from. (Oracle Docs)
For broader triage across many hosts, a simple boundary-check loop is often more useful than a vulnerability scanner in the first few hours:
#!/usr/bin/env bash
set -euo pipefail
while read -r host; do
echo "=== $host ==="
for path in \
"/iam/governance/applicationmanagement/api/v1/templates" \
"/iam/governance/selfservice/api/v1/unauthservice/passwordreset" \
"/iam/governance/selfservice/api/v1/unauthservice/selfregistration"
do
code=$(curl -sk -o /dev/null -w "%{http_code}" "https://${host}${path}")
echo "${code} ${path}"
done
echo
done < targets.txt
This script is not trying to prove exploitability. It is trying to answer which hosts expose which documented routes and how those routes respond anonymously. That is exactly the kind of evidence you need for emergency segmentation decisions, maintenance-window requests, and patch-priority ordering. (Oracle Docs)
A basic network-level check is also useful to establish whether Oracle-related web surfaces are reachable at all:
nmap -Pn -sT -p 80,443,7001,7002 \
--script http-title,http-headers \
oim.example.com
The point here is not fingerprint fetishism. It is to establish whether the target is alive, which ports are reachable, whether a reverse proxy is involved, and whether web responses suggest Oracle middleware paths or administrative surfaces. On fragile identity infrastructure, gentle visibility beats “smart” aggression every time.
For environments where you already have legitimate credentials and a change window, Oracle’s documentation gives you authenticated REST patterns you can turn into post-patch regression checks. Oracle’s OIG Access Policy REST docs show authenticated cURL syntax, and Oracle’s OWSM docs say OWSM REST access requires WebLogic administrator credentials. That means a good post-patch test plan includes both negative and positive checks: anonymous access to authenticated endpoints should remain blocked, and authenticated access for legitimate administrators should still work after the fix. (Oracle Docs)
Detection should follow product function, not just CVE buzzwords
Because Oracle has not published the exact root cause, defenders should not narrow detection to one hypothetical exploit string. A better approach is to monitor the product functions that would be valuable before, during, and after compromise.
At the web and reverse-proxy layer, watch for unusual request bursts to /iam/governance/ paths, especially on internet-facing or partner-reachable assets. Look for sequences where repeated 401 or 403 responses are followed by a sudden 200 on a path that should require authentication. Look for new access from infrastructure that normally never talks to identity governance servers. Watch for unusual query strings, malformed path segments, and route variants that suggest authentication-boundary probing. These are generic web-hunting principles, but they become much more valuable when applied to documented OIG route families. (Oracle Docs)
At the application layer, tie detection to what OIG and OWSM actually do. Oracle’s OIG docs show surfaces for users, roles, organizations, password policy, templates, self-service flows, and SCIM operations. Oracle’s OWSM docs show trust-document, policy-set, and configuration management APIs. That means suspicious activity includes unexpected reads or writes around user and role management, odd spikes in password-reset or self-registration traffic, anomalous changes to policy sets or trust documents, and unexpected administrative actions on security-policy resources. If your logging pipeline collapses all of that into “middleware noise,” you are throwing away the context that makes incident response faster. (Oracle Docs)
At the platform layer, watch WebLogic and surrounding infrastructure for service restarts, unexpected deployment changes, administrator-auth anomalies, new listening behavior, or integrity changes in the application environment. Because OWSM sits in the policy and trust layer, even configuration changes that would normally look like routine administration deserve more scrutiny during the response window. The most dangerous post-exploitation activity may not be loud malware. It may be a subtle rule change that makes later traffic look legitimate. (Oracle Docs)
At the identity and downstream layer, ask what these systems can influence after compromise. If roles, users, registration flows, or trust relationships change unexpectedly, what secondary systems become easier to access? Which CI systems, internal APIs, model platforms, or business applications inherit trust from the Oracle identity and service-security stack? The fastest incident responders are the ones who can answer that blast-radius question while patching is still underway.
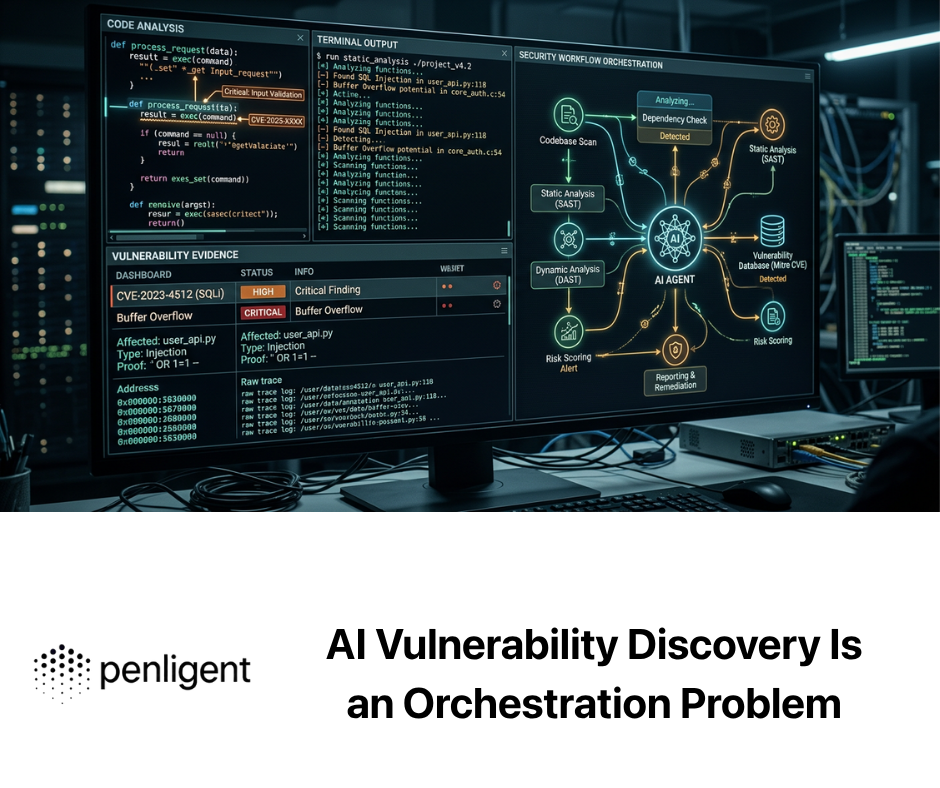
For large estates, the hardest part is usually not “understanding the CVE.” It is proving which assets are exposed, which environments still leak management surfaces, and which patches truly restore the intended authentication boundary. That is one place where an agentic validation platform can be useful without turning the response into stunt exploitation. Penligent’s public materials emphasize automated asset profiling, access to a large tool set, controlled validation, and exportable evidence-backed reports. Those are the right capabilities for fleet-wide reachability checks, post-patch retesting, and remediation evidence collection in a case like CVE-2026-21992. (Penligente)
Temporary containment is valuable, but it is not the fix
Oracle’s own advisory says customers should apply the updates or mitigations from the Security Alert as soon as possible, and Oracle reiterates its usual guidance to stay on actively supported versions and apply patches without delay. That should remain the center of the response. The patch is the fix. Containment is what buys you safer time to deploy it. (Oracle)
In practical terms, temporary containment usually means one or more of the following: remove direct internet exposure to OIM and OWSM paths; restrict access to management and administrative interfaces to trusted network ranges or jump hosts; require remote administration through VPN or privileged access infrastructure rather than from broad office or partner ranges; confirm that reverse proxies and WAFs are not unintentionally publishing Oracle administrative routes; and segment disaster-recovery, testing, and forgotten legacy estates with the same discipline as production. These measures are not a substitute for the vendor update, but they can materially reduce the pool of unauthenticated attackers who can reach the surface while change control catches up.
There is a second containment lesson specific to this product family. Because OIG documents intentionally unauthenticated self-service routes, security teams should resist the urge to “block everything under /iam/governance/” without understanding business impact. Emergency controls have to distinguish between routes that are supposed to be anonymous, routes that are supposed to require authentication, and routes that should not be reachable from a given network zone at all. Fast and blind are not the same thing. (Oracle Docs)
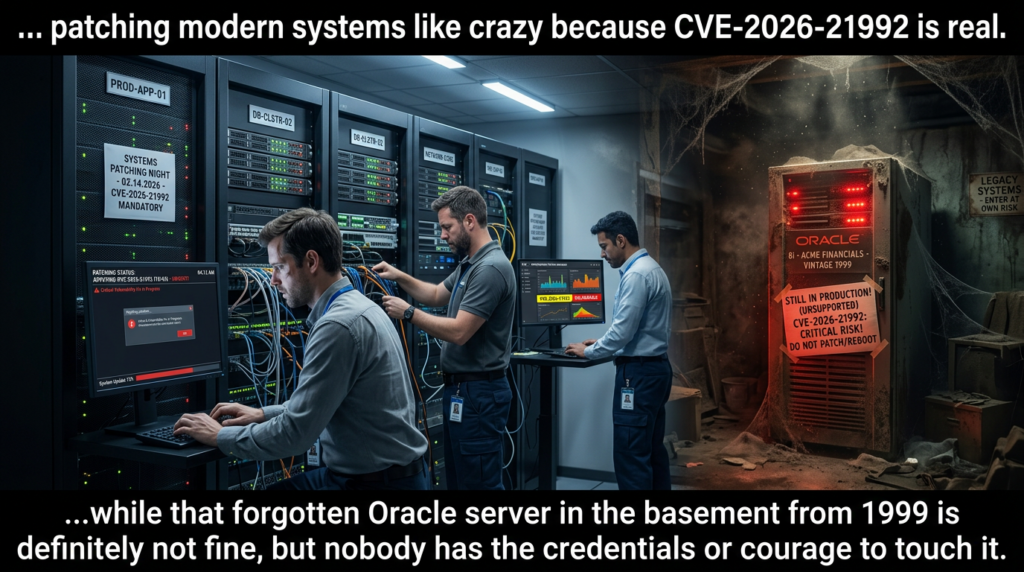
Patching reality in Oracle estates is messy, and that is part of the risk
Large Oracle environments often do not patch like clean cloud-native services. The software may sit in shared middleware clusters, mission-critical identity stacks, tightly coupled integrations, and long-lived change-management processes. Public reporting has highlighted that organizational size and implementation complexity can slow patching for Oracle customers, especially where large multinationals are involved. That does not excuse delay. It explains why attackers tend to get long tails of opportunity after disclosure. (Lectura oscura)
Oracle’s support policy language adds another complication. Security Alert patches are only provided for supported releases, but Oracle explicitly warns that older unsupported versions are likely affected. In other words, some environments cannot be “patched” in the narrow sense because they are already outside supported patch delivery. Those systems need a different decision tree: accelerated upgrade, isolation, compensating controls, migration, or retirement. Pretending they do not count because they are unsupported is how old identity infrastructure becomes a long-term intrusion path. (Oracle)
That is why version inventory, change planning, and exposure analysis have to happen together. A supported system with a fast patch window but no external reachability may rank below an unsupported disaster-recovery node that still answers requests from a broad network range. Severity scores tell you the class of problem. Reachability and operational role tell you where the real risk sits first. (Oracle)
What post-patch verification should actually prove
Many teams stop too early. They apply the vendor patch, record a maintenance ticket, and move on. For a vulnerability in the identity and policy-control tier, that is not enough.
Post-patch verification should prove three things. First, authenticated-only routes are still authenticated-only. A path like /iam/governance/applicationmanagement/api/v1/templates should not become anonymously reachable because of a proxy rewrite, fallback configuration, or cluster inconsistency. Second, intended business behavior still works. Legitimate administrators should still be able to access the APIs and consoles they are supposed to use, and legitimate self-service flows should still behave normally. Third, the relevant control plane has not drifted during the emergency window. Policy attachments, trust documents, registration flows, and identity-management configuration should match known-good expectations after the patch. (Oracle Docs)
A simple regression pattern is to keep paired tests for anonymous and authenticated access. If the anonymous request now gets blocked and the authenticated request still succeeds, you have stronger evidence that the trust boundary is back where it belongs. If the anonymous request is blocked but the authenticated request fails too, you may have fixed one problem while creating an outage. Identity-tier vulnerabilities punish shallow validation because they live exactly where authentication and authorization semantics are most fragile. (Oracle Docs)
For teams handling many Oracle environments at once, this is also where tooling discipline matters. A spreadsheet of version strings is not enough. You want reachability evidence, before-and-after status behavior on documented routes, authenticated smoke-test results, and archived artifacts that can survive internal audit and later incident review. The public positioning on Penligent’s pricing and product pages is relevant here because it emphasizes the same operational loop: asset profiling, controlled validation, and evidence-backed reporting. Used in that way, an automation layer supports disciplined remediation rather than replacing human judgment. (Penligente)
What not to say about CVE-2026-21992
Do not say Oracle has confirmed active exploitation. Public reporting says Oracle has not clearly stated that. (SecurityWeek)
Do not say there is already a mature public proof of concept. Tenable said there was no public PoC at the time of its analysis, and current public reporting around the bug has focused on patch urgency more than exploit publication. (Tenable)
Do not say the flaw is definitely the same root cause as CVE-2025-61757. The overlap is meaningful, but Oracle has not confirmed technical equivalence. (Tenable)
Do not reduce it to “a WebLogic bug.” The published issue is specifically in Oracle Identity Manager and Oracle Web Services Manager, in named components with identity and policy significance. Precision is part of competent response. (Oracle)
CVE-2026-21992 is urgent because it is an unauthenticated remote compromise path into Oracle’s identity-governance and web-service security layers, not because it happens to carry a 9.8. Oracle published it through a standalone Security Alert. NVD says successful attacks can result in takeover. The affected products sit upstream of user lifecycle, access decisions, trust documents, policy sets, and service-level security behavior. That combination is enough to justify immediate action. (Oracle)
The public record is still incomplete, and that is exactly why disciplined responders should separate facts from assumptions. What is confirmed is severe enough already. Patch the supported versions. Treat unsupported earlier versions as likely affected until proven otherwise. Reduce exposure while maintenance windows are being prepared. Verify boundaries using documented routes rather than rumor-driven exploit theater. Then retest after patching with the same rigor you used to justify the emergency change in the first place. (Oracle)
If the 2025 Oracle Identity Manager incident taught defenders anything, it is that identity-tier middleware flaws do not stay “just another CVE” for long. They become footholds, trust pivots, and long-tail remediation problems. CVE-2026-21992 belongs in that category now, whether or not the root-cause blog post has arrived yet. (Oracle)
Para saber más
Oracle Security Alert Advisory for CVE-2026-21992, the primary vendor advisory with affected versions, supported-version guidance, and Oracle’s risk matrix. (Oracle)
NVD entry for CVE-2026-21992, the clearest public source for the component names, CVSS vector, takeover wording, and CWE mapping. (NVD)
Oracle Identity Management 14.1.2.1.0 documentation, useful for understanding Oracle’s own naming, platform role, and where OIG REST APIs sit in the product family. (Oracle Docs)
Oracle Identity Governance SCIM and REST documentation, especially the notes that SCIM is deployed by default and can run on both HTTP and HTTPS ports by default. (Oracle Docs)
Oracle Identity Governance Self Service and Application Management REST documentation, which helps defenders verify which routes are intentionally unauthenticated and which are supposed to require authentication. (Oracle Docs)
Oracle Web Services Manager documentation and REST API references, useful for understanding OWSM’s role in policy, trust, and security configuration. (Oracle Docs)
Tenable’s analysis of CVE-2026-21992, particularly for the context around out-of-band Oracle alerts, the 2025 predecessor, and the note that no public PoC was available at the time of publication. (Tenable)
Searchlight Cyber’s technical analysis of CVE-2025-61757, which remains the most instructive public write-up for understanding how dangerous Oracle Identity Manager REST authentication failures can become in practice. (Searchlight Cyber)
Penligent’s Oracle Identity Manager write-up on CVE-2025-61757, relevant as a workflow-oriented companion read on why identity-tier compromise matters and how to think about inventory, validation, and remediation speed. (Penligente)
Penligent’s main product page and pricing page, relevant when the operational problem shifts from “What is the CVE?” to “How do we validate exposure, patching, and evidence at fleet scale?” (Penligente)