ZoneMinder has been around long enough that many teams treat it like infrastructure furniture. It is open source, well known in self-hosted CCTV circles, and often deployed by people who know Linux well enough to make it run. That familiarity can become a security problem. Products that feel operationally ordinary are easy to under-classify. A camera management stack gets treated like a convenience service when it should be treated like a privileged operational application with persistent access to sensitive images, event history, user accounts, and an administrative web plane. That framing matters for ZoneMinder v1.37.63, because the security story around this version is not a vague concern or a theoretical footnote. It sits inside a patch window that security teams can misread very easily. (NVD)
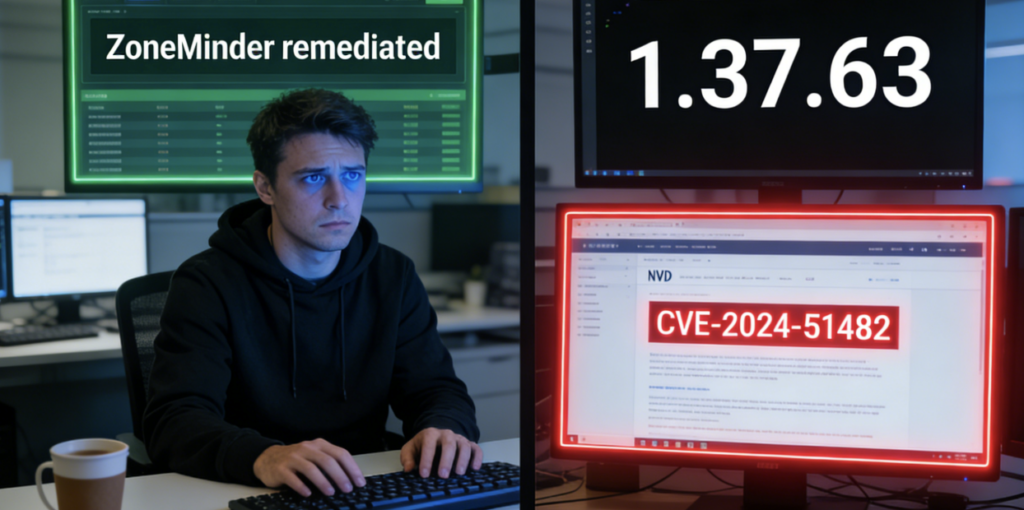
The most important answer up front is simple. ZoneMinder v1.37.63 should not be treated as a safe endpoint simply because it is “in the 1.37 line.” NVD states that CVE-2024-51482 affects ZoneMinder v1.37.* <= 1.37.64 and that the correct fixed version is 1.37.65. The same public record preserves an earlier wording mistake that briefly claimed the flaw was fixed in 1.37.64 before being corrected to 1.37.65. That change history is more than a paperwork detail. It is exactly the sort of record inconsistency that leads defenders to believe they crossed the patch boundary when they did not. ZoneMinder 1.37.63 remains on the vulnerable side of that line. (NVD)
That is why the keyword zoneminder v1.37.63 cve deserves a precise answer instead of a generic one. The correct answer is not that 1.37.63 introduced a unique headline CVE. The correct answer is that 1.37.63 sits in a dangerous interval within the 1.37 development branch, and the most operationally important issue for that version is CVE-2024-51482, a boolean-based SQL injection in web/ajax/event.php, later fixed only in 1.37.65. If your inventory says only “ZoneMinder 1.37” without patch-level detail, you do not yet know whether you are safe. (NVD)

ZoneMinder, why patch-level precision matters here
ZoneMinder describes itself as a free, open source closed-circuit television software application. That product description is accurate and incomplete. In practice, it is a web application, a media broker, an event store, a privileged admin surface, and in many deployments a bridge into physical security workflows. NVD’s older records make that very clear. CVE-2023-26035, for example, was described as an unauthenticated remote code execution issue caused by missing authorization in the snapshot action, where attacker-controlled input could reach shell_exec through TriggerOn. That is not the profile of a harmless “camera dashboard.” It is the profile of a system that sits close to operational trust and should be defended like one. (NVD)
GitHub’s current ZoneMinder security policy also reinforces an important branch-level reality: the project says it supports the latest stable release and development releases, and it explicitly lists both 1.36.x y 1.37.x as supported. At the same time, GitHub shows that the latest release is now 1.38.1, published in February 2026. That means a defender evaluating 1.37.63 today is not looking at a current end state. They are looking at an older development-line point release that must be interpreted in the context of later security fixes and branch evolution. (GitHub)
This is one reason why the phrase “we are on 1.37” can be operationally useless. A team might have upgraded after the August 2024 issues were disclosed and still remain exposed to a later critical issue if they stopped at 1.37.61, 1.37.63, or 1.37.64. In other words, the difference between 1.37.61 and 1.37.65 is not cosmetic. It is the difference between having closed one cluster of web-plane bugs and still carrying another critical one. (NVD)
The clean answer first
Before getting into the branch history, here is the shortest defensible summary.
| Artículo | Valor |
|---|---|
| Producto | ZoneMinder |
| Version in question | 1.37.63 |
| Most important CVE for that version | CVE-2024-51482 |
| Tipo de vulnerabilidad | Boolean-based SQL injection |
| Vulnerable component | web/ajax/event.php |
| Official affected range | v1.37.* <= 1.37.64 |
| Correct fixed version | 1.37.65 |
| Weakness class | CWE-89 |
| Operational takeaway | 1.37.63 is still on the vulnerable side of the fix boundary |
Every row in that table matters, but the one that causes the most confusion is the fix boundary. The NVD entry explicitly shows a correction from “fixed in 1.37.64” to “fixed in 1.37.65.” Teams that captured the first phrasing and never revisited it can carry a wrong remediation assumption into asset tracking, patch verification, or customer reporting. (NVD)
The CVE that matters most for ZoneMinder v1.37.63
CVE-2024-51482 is the vulnerability that defenders should anchor on when they search for zoneminder v1.37.63 cve. NVD describes it as a boolean-based SQL injection in web/ajax/event.php affecting ZoneMinder v1.37.* <= 1.37.64, with the corrected fix at 1.37.65. The record associates the issue with CWE-89, and the GitHub-contributed CVSS vector is AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H, which is about as clear a signal as a defender gets that the issue is not a low-grade nuisance. It is network reachable, low complexity, needs no user interaction, and has high impact across confidentiality, integrity, and availability. (NVD)
A detail worth slowing down on is the privileges requirement. The CNA vector indicates low privileges, not none. That does not make the issue unimportant. In real environments, it often makes it more realistic. Surveillance platforms frequently have multiple users, delegated views, legacy service accounts, or shared operational credentials. A vulnerability that starts from a low-privilege foothold can still be dangerous if the application exposes sensitive data and sits in a trusted network position. For a blue team, “requires low privileges” should not be translated into “unlikely to matter.” In many internal and partner-connected environments, low privileges are the normal starting point of a real incident. (NVD)
The other reason CVE-2024-51482 stands out is timing. By the time it was published on October 31, 2024, defenders had already seen a round of ZoneMinder web-plane issues earlier that year. Some teams likely upgraded once, saw a clean bill of health for those earlier advisories, and assumed the 1.37 branch was effectively under control. CVE-2024-51482 breaks that assumption. It lands after the August 2024 fixes and extends through 1.37.64, which means deployments on 1.37.63 can look “recent enough” and still be wrong. (NVD)
Why 1.37.63 still matters even after earlier 2024 fixes
This is where version history becomes more important than headline severity. In August 2024, GitHub and NVD recorded several ZoneMinder issues that were fixed in 1.36.34 y 1.37.61. NVD says CVE-2024-43358 was an XSS flaw in the filter view via filter[Id], fixed in those versions. NVD also says CVE-2024-43359 was an XSS issue in montagereview through the displayinterval, speedy scale parameters, again fixed in 1.36.34 y 1.37.61. In the same time frame, GitHub advisory GHSA-9cmr-7437-v9fj described a critical SQL injection issue involving the sort y mid parameters in /zm/index.php, with affected versions listed as <1.36.33, <1.37.43; the ZoneMinder 1.36.34 release notes then explicitly noted mitigations such as restricting mid to a cardinal value and limiting sort to event columns. (NVD)
The trap is obvious in hindsight. A team that patched to 1.37.61 after those disclosures could truthfully say it had addressed several public 2024 issues. But that same team would still be exposed to CVE-2024-51482 if it never moved to 1.37.65. That is exactly why 1.37.63 deserves its own analysis. It sits after the August 2024 fix wave and before the October 2024 SQL injection boundary was actually closed. From a vulnerability-management perspective, it is the classic “looks patched, is not fully patched” state. (NVD)
The practical version map looks like this:
| Version | CVE-2024-43358 | CVE-2024-43359 | CVE-2024-51482 | Practical reading |
|---|---|---|---|---|
| 1.37.42 and earlier | Vulnerable | Vulnerable | Not yet the relevant boundary | Clearly exposed |
| 1.37.43 to 1.37.60 | Not necessarily exposed to the August SQLi boundary, but still pre-1.37.61 for other 2024 web fixes | Vulnerable until 1.37.61 | Vulnerable if within <=1.37.64 | Still weak |
| 1.37.61 | Fixed for the August 2024 XSS set | Fixed | Still vulnerable | Partially remediated |
| 1.37.63 | Fixed for those earlier XSS issues | Fixed | Vulnerable | False sense of safety |
| 1.37.64 | Fixed for those earlier XSS issues | Fixed | Vulnerable | Still exposed |
| 1.37.65 | Fixed | Fixed | Fixed | Minimum safe point in 1.37 for this issue |
That table is not a substitute for vendor documentation. It is a way to stop teams from thinking in branch labels rather than precise builds. The phrase “patched 1.37” is not evidence. A package string, a release artifact, or a verified runtime version is evidence. (NVD)

The broader ZoneMinder vulnerability pattern is the real lesson
A single CVE can be dismissed as bad luck. A pattern is harder to dismiss. ZoneMinder’s public security history shows repeated issues across authorization, SQL handling, and web UI input processing. The 2023 NVD entry for CVE-2023-26035 describes unauthenticated remote code execution prior to 1.36.33 and 1.37.33 because the snapshot action lacked permission checks and ultimately passed attacker-controlled input into a shell execution path. That is a severe design-level failure in access control. (NVD)
Then, in August 2024, public advisories described multiple flaws in the web plane. NVD recorded CVE-2024-43358 and CVE-2024-43359 as XSS issues in the filter and montage review flows, both fixed in 1.36.34 and 1.37.61. GitHub advisory GHSA-9cmr-7437-v9fj described a critical SQL injection path affecting the sort y mid parameters and rated it 9.8. The 1.36.34 release notes showed concrete hardening work, including type restrictions and limiting sortable columns. That is not the profile of a product that had one unlucky bug in one forgotten endpoint. It is the profile of a codebase where the trust boundary between web input and privileged application behavior has repeatedly needed tightening. (NVD)
GitHub’s security overview adds one more important current signal. As of March 2026, the project’s advisory list still includes newer high- and critical-severity issues, including a command injection advisory and a second-order SQL injection advisory published in February 2026. Those later advisories are not about 1.37.63 specifically, so they should not be used to overstate the exact risk of that point release. But they do matter as context. They show that ZoneMinder should be treated as an application that needs ongoing validation, not a one-time patch event followed by years of trust. (GitHub)
That is the deeper answer to why zoneminder v1.37.63 cve keeps drawing attention. Defenders are not just asking whether one package build was vulnerable. They are asking whether this product family has shown enough repeated security friction that older development-line deployments should be reviewed with extra skepticism. The public record says yes. (NVD)
Why “it is just SQL injection” is the wrong mental model
Security teams often underreact to SQL injection findings when the product is not obviously business-critical in the way that identity, payment, or customer portals are. That is a mistake with ZoneMinder. Even if a vulnerability starts as a database integrity or disclosure issue, the surrounding application context amplifies the consequence. ZoneMinder is not a generic CRUD app. It handles event history, camera metadata, monitor configuration, and potentially operationally sensitive timelines about what happened, where, and when. In some environments, it is directly adjacent to physical security workflows. In others, it is an internal web application trusted enough to live near infrastructure that defenders would rather not expose. (NVD)
A flaw in an event-related endpoint can therefore matter beyond “database exposure.” It can affect visibility, operational trust, administrative behavior, and downstream investigation. Event data is often valuable even when video itself is not immediately accessible. Timestamps, monitor names, tags, archive flags, alarm states, user behavior, and linkage between cameras and zones can be enough to build a picture of facility habits, staffing patterns, or high-value periods. Where an application already has a history of authorization failures and input-handling bugs, a data-layer defect should be read as part of a broader trust problem, not a single bug class in isolation. (NVD)
There is also a very practical ops angle. Systems like ZoneMinder are often deployed by administrators who prioritize camera uptime and recording continuity over application hardening. That is understandable. Video systems are noisy, operational, and time-sensitive. But it creates a recurring failure mode: a package gets upgraded once, nobody wants to touch the running system again, and security assumptions begin to drift away from reality. ZoneMinder’s public advisory history is a reminder that surveillance management systems age like web applications, not like dumb appliances. (GitHub)
What defenders should verify on a live environment
The first question is not “can we reproduce the bug.” The first question is “what exact build is running, where is it exposed, and what compensating controls exist if patching is delayed.” That is how mature blue teams reduce risk without creating avoidable operational disruption.
Start with version certainty. If this is an apt-based installation, do not rely only on memory or documentation. Check the package manager, the web UI about page if available, container image tags if containerized, and deployment manifests if it sits behind orchestration. Version ambiguity is how teams remain exposed long after they believe they remediated. NVD’s correction history for CVE-2024-51482 makes that especially important. (NVD)
Here is a safe version-checking sequence you can use on Linux hosts:
# Debian or Ubuntu package check
dpkg -l | grep -i zoneminder
# apt metadata
apt-cache policy zoneminder
# If installed from source or custom packaging
zm --version 2>/dev/null || zoneminder --version 2>/dev/null
# Container image inspection
docker ps --format "table {{.Names}}\\t{{.Image}}"
docker inspect <container_name> | grep -i -E 'image|version'
# Basic filesystem clues
find / -maxdepth 3 -type f 2>/dev/null | grep -i zoneminder | head
These commands do not prove safety by themselves, but they close the most common remediation gap: believing you know the version without verifying it from the runtime system. Once you have the actual build number, compare it against the relevant advisory boundaries, not just the branch name. For this topic, that means paying particular attention to whether the system is at or below 1.37.64, or at 1.37.65 and beyond. (NVD)
Next, verify exposure. Even a vulnerable internal-only deployment is different from a public internet-facing one. The following checks are defensive and non-invasive:
# Confirm listening services and local bindings
ss -tulpn | grep -E '80|443|8080|8443'
# Review reverse proxy rules
grep -R "server_name\\|location /zm\\|proxy_pass" /etc/nginx /etc/apache2 2>/dev/null
# Look for external exposure in firewall policy
iptables -S 2>/dev/null | sed -n '1,120p'
ufw status verbose 2>/dev/null
# Check whether auth gates are present upstream
grep -R "allow\\|deny\\|auth_basic\\|satisfy" /etc/nginx /etc/apache2 2>/dev/null
What you are looking for is not only whether ZoneMinder is reachable, but whether it is casually reachable. A web UI that was intended for internal staff often ends up exposed through a convenience reverse proxy, a leftover NAT rule, or a temporary partner access exception that became permanent. Exposure discipline matters at least as much as patching for a product with ZoneMinder’s history. (NVD)
You should also review logs after any version transition. A clean upgrade is not the same as a clean security state. The project’s own older advisories around log-related issues are a reminder that logging surfaces themselves have mattered historically. That does not mean defenders should distrust all logs. It means they should review them with intent. Check for repeated requests to event-related endpoints, anomalous query strings, odd error bursts in the web layer, and authentication behaviors that do not fit normal operator patterns. (GitHub)
A simple triage pattern can help:
# Web access logs, adjust paths for your distro
grep -R "event.php\\|index.php\\|watch\\|montagereview\\|filter" /var/log/nginx /var/log/apache2 2>/dev/null | tail -n 200
# PHP and app logs
grep -R "ZoneMinder\\|SQL\\|warning\\|error\\|exception" /var/log 2>/dev/null | tail -n 200
# Package update history
grep -R "zoneminder" /var/log/apt/history.log* /var/log/dpkg.log* 2>/dev/null
Again, this is not exploit validation. It is operational validation. It helps answer the questions that matter during patch verification and incident triage: when was the package updated, what endpoints were touched, and did unusual behavior cluster around the window in which the system was vulnerable. (NVD)
A version-check script defenders can adapt
Teams with more than one deployment should not do this by hand forever. A simple inventory script is usually enough to find the problem systems quickly.
#!/usr/bin/env python3
import re
import subprocess
from packaging.version import Version
def get_pkg_version():
commands = [
["bash", "-lc", "dpkg -l | awk '/zoneminder/ {print $3}' | head -n 1"],
["bash", "-lc", "rpm -qa | grep -i zoneminder | head -n 1"],
]
for cmd in commands:
try:
out = subprocess.check_output(cmd, stderr=subprocess.DEVNULL, text=True).strip()
if out:
return out
except Exception:
pass
return None
def normalize(ver: str):
m = re.search(r"(\\d+\\.\\d+\\.\\d+)", ver or "")
return Version(m.group(1)) if m else None
def main():
raw = get_pkg_version()
if not raw:
print("ZoneMinder package not found")
return
ver = normalize(raw)
print(f"Detected package string: {raw}")
if not ver:
print("Could not parse semantic version")
return
if Version("1.37.0") <= ver <= Version("1.37.64"):
print("Status: potentially vulnerable to CVE-2024-51482 based on version range")
elif ver >= Version("1.37.65"):
print("Status: beyond the published fix boundary for CVE-2024-51482")
else:
print("Status: outside the direct 1.37.* <= 1.37.64 range, review other relevant advisories")
if __name__ == "__main__":
main()
No script should replace advisory review, but a small control like this can stop one of the most common failures in patch governance: the CMDB says “remediated,” the host says something else. For ZoneMinder, patch-level detail is the entire argument. (NVD)
Hardening steps that matter more than people think
Patch first. Hardening second. But if you cannot patch immediately, hardening buys time only when it narrows the path to the vulnerable surface. For ZoneMinder, the most valuable control is exposure reduction. The fact that a product can be made reachable from anywhere does not mean it should be. Public UI exposure for surveillance administration is a design smell unless there is a very strong reason and strong front-door controls. A VPN, zero-trust broker, IP allowlist, or private reverse proxy is better than a public web login page every time. That is a general principle, and ZoneMinder’s own security history gives it extra weight here. (NVD)
The second priority is privilege minimization. The SQL injection records, XSS records, and older authorization issue all point to the same operational truth: account scope matters. Review who has access, what roles they truly need, and whether service accounts or shared operator accounts have lingered beyond their original purpose. Even when a flaw requires low privileges, reducing low-privilege sprawl reduces the chance that the flaw becomes operationally reachable. (NVD)
The third priority is segmentation. Camera management systems should not sit on the same flat trust plane as general user devices or broad server administration surfaces. Even if the business case for internal access is legitimate, the network case for lateral openness is usually weak. Place the application in a segment that matches its sensitivity, restrict who can reach the admin UI, and restrict where the application can go. Surveillance software is often trusted more than it should be because it feels specialized. Specialization is not a security boundary. (NVD)
The fourth priority is database hygiene. SQL injection defenses are primarily a development concern, but operational teams still influence blast radius. Review database user permissions, isolate the database where possible, avoid overprivileged service credentials, and make sure backups are protected with the same seriousness as live data. If the application layer has a weakness, the difference between a narrowly scoped database account and an overpowered one can change the entire incident profile. (NVD)
WAF rules and input filtering can help reduce opportunistic noise, but they should be framed honestly. They are compensating controls, not authoritative remediations. A misread fix boundary, especially one preserved in public change history the way CVE-2024-51482 was, is not the kind of problem you want to solve with a regex. The right solution is to move beyond the vulnerable version. (NVD)
Why this kind of system benefits from automated validation
ZoneMinder is a good example of a product that is easy to half-fix. A team upgrades the package but forgets the old reverse proxy path. It removes public DNS but leaves a partner tunnel. It updates one node in a multi-site deployment and assumes the rest match. It closes a known issue from August 2024 and misses the later October boundary. These are not dramatic failures. They are ordinary operational failures, which is exactly why they happen so often. (NVD)
That is where automated validation has real value. Not as a substitute for patching, and not as a license to turn every advisory into an exploit exercise, but as a way to confirm the practical state of exposed assets after the human team believes the work is done. For a platform like ZoneMinder, useful validation means confirming exact version boundaries, checking whether the vulnerable web surface is still externally reachable, testing whether legacy paths are still present, and looking for risk signals that remain after the package update. That is a much better use of automation than merely producing another scanner report. (NVD)
For teams already using an AI-assisted security workflow, this is also one of the rare cases where automation maps naturally to the real operational need. ZoneMinder is not hard because the CVEs are intellectually obscure. It is hard because deployment reality drifts. A validation platform such as Penligent can be useful in that gap, especially for confirming that a supposedly remediated surveillance management surface is no longer exposed through the same web paths, policy gaps, or forgotten edge routes that made it risky in the first place. The strongest role for automation here is disciplined re-testing after change, not theatrics. (Penligente)
There is also a second, more strategic reason this kind of automation matters. ZoneMinder’s public history shows more than one class of defect over more than one year. That means defenders should resist the idea that a single patched CVE closes the chapter. A better model is repeated validation over time, especially after upgrades, proxy changes, auth changes, or topology changes. In environments where surveillance infrastructure touches real operational trust, confidence should come from verification, not from branch names in documentation. (NVD)
A blue-team remediation sequence that makes sense
If you discover a deployment on 1.37.63, the first move is to classify it correctly. Do not ask only whether it is vulnerable. Ask whether it is reachable, who can authenticate, what data it manages, and what else it can touch. A public-facing 1.37.63 deployment is one kind of risk. An internal-only 1.37.63 deployment reachable by broad staff networks is another. An isolated lab instance with no sensitive retention is another. Same package, different urgency. (NVD)
The second move is to identify the shortest supported path beyond the vulnerable boundary. For teams that must stay on the 1.37 line, the public record for CVE-2024-51482 makes 1.37.65 the minimum meaningful target for this issue. More broadly, GitHub now shows 1.38.1 as the latest release, which means some teams may decide that jumping to the current stable line makes more long-term sense if compatibility testing allows it. The right destination depends on operational constraints, but the wrong destination is staying on 1.37.63 because it feels recent enough. (NVD)
The third move is to validate the fix in the live environment, not only in the ticket. Confirm version, confirm exposure controls, confirm the old surface is no longer reachable as before, and confirm that logging and package history align with the claimed maintenance event. Where possible, attach evidence to the remediation record. A patch note without runtime proof is a claim, not a closure. (NVD)
The fourth move is to review the rest of the product’s security posture while you already have hands on it. Because the ZoneMinder advisory pattern includes authorization, SQL, XSS, and log-adjacent issues, this is the right time to examine role sprawl, reverse-proxy policy, database permissions, and segmentation. A mature team uses the CVE as a forcing function to improve the whole boundary, not just to bump one package. (NVD)
Final verdict
For anyone searching zoneminder v1.37.63 cve, the most accurate answer is not “yes, there are CVEs” and not “that version itself created a unique issue.” The accurate answer is more useful than either of those. ZoneMinder v1.37.63 sits inside a security-relevant patch interval in the 1.37 branch, and the most important public issue for that version is CVE-2024-51482, a boolean-based SQL injection affecting v1.37.* <= 1.37.64, with the correct fix boundary at 1.37.65. Public records also show that the fix version was corrected after initial publication, which is exactly why defenders should verify patch level carefully instead of relying on shorthand like “we are on 1.37.” (NVD)
The broader lesson is just as important. ZoneMinder has accumulated a public history that includes unauthenticated remote code execution, SQL injection, XSS, and more recent advisories in subsequent years. That does not make every deployment compromised. It does mean the platform should be treated like a high-trust web application, not just like camera software. If you run 1.37.63, the right instinct is not debate. It is verification, upgrade planning, exposure review, and repeatable validation afterward. (NVD)
Further Reading
NVD entry for CVE-2024-51482 and its fix-boundary change history. (NVD)
GitHub advisory for GHSA-qm8h-3xvf-m7j3, the ZoneMinder boolean-based SQL injection issue tracked as CVE-2024-51482. (GitHub)
NVD entry for CVE-2023-26035, the earlier unauthenticated RCE issue in the 1.37 line prior to 1.37.33. (NVD)
NVD entries for CVE-2024-43358 y CVE-2024-43359, the August 2024 XSS issues fixed in 1.37.61. (NVD)
ZoneMinder GitHub Security Policy, including supported branches and current advisory overview. (GitHub)
ZoneMinder GitHub Releases page, showing the currently listed latest release. (GitHub)
ZoneMinder v1.37.63 CVE — The Vulnerability Security Teams Are Actually Looking For. (Penligente)
CVE-2024-51482, The ZoneMinder SQL Injection That Still Matters in 2026. (Penligente)
ZoneMinder, the Open-Source CCTV Stack That Deserves a Real Security Review. (Penligente)
ZoneMinder Security, What Security Engineers Need to Know About the Open Source CCTV Stack. (Penligente)