For a lot of teams, the first reaction to any new Log4j CVE is emotional memory. People still remember December 2021, emergency patches, broken maintenance windows, WAF rules thrown into production at 2 a.m., and the long tail of buried Java services nobody thought they owned until scanners lit them up. CVE-2025-68161 lands in that shadow, but it is a different class of problem. It is not a general-purpose remote code execution event like Log4Shell. It is a trust failure in Apache Log4j Core’s Socket Appender, where TLS hostname verification is not actually enforced even when configuration says it should be. Apache lists the issue as affecting Log4j Core from 2.0-beta9 through 2.25.2, with a fix in 2.25.3. NVD records the same affected range, and the current scoring puts it in the medium band, with the Apache CNA assigning CVSS 4.0 6.3 and NVD listing CVSS 3.1 4.8. (Apache Logging Services)
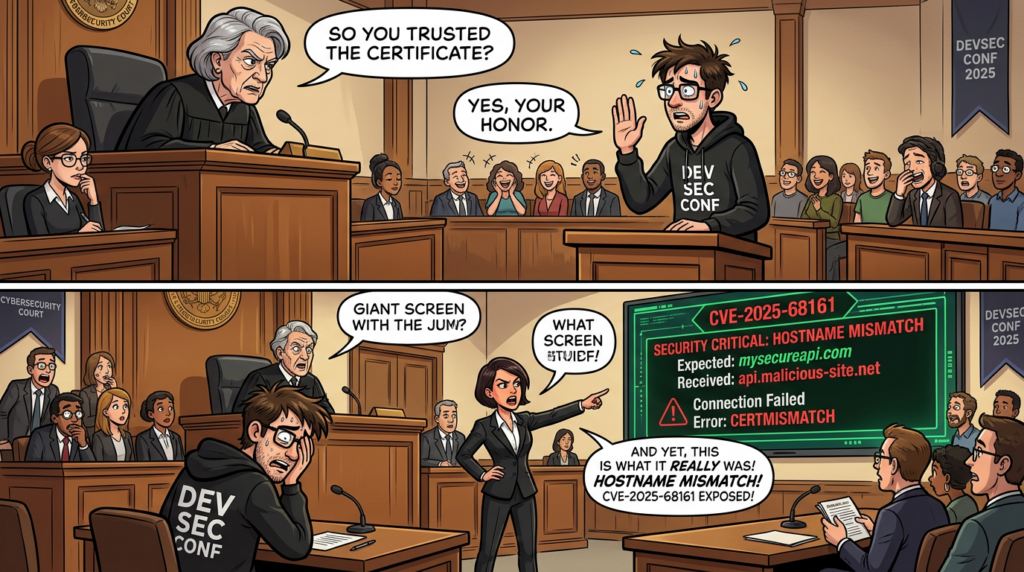
That sounds modest until you think about what remote logging is supposed to give you. Logs are not just text exhaust. They are evidence, control-plane telemetry, alert input, compliance material, and post-incident memory. Once you forward them over the network, you have created a trust relationship between the application and a remote receiver. CVE-2025-68161 weakens that relationship precisely where many engineers assume it is strongest: inside TLS identity validation. Apache’s own documentation describes verifyHostName as the setting that should compare the hostname in the X.509 certificate to the requested host and fail the connection on mismatch. The advisory for CVE-2025-68161 says that promise was not being honored in the affected Socket Appender path. In other words, the control existed on paper and in configuration, but it did not reliably exist where it mattered. (Apache Logging Services)
Apache’s release notes for Log4j 2.25.3 make the scope of the fix unusually clear. The 2.25.3 release, dated December 15, 2025, explicitly calls out “an important fix” for hostname verification in SSL/TLS configuration used by Socket Appender, and references the underlying fix in issue 4002. That matters because it tells you this is not a vague “security hardening” release note. The maintainers tied the release directly to the broken trust behavior. The Apache security page adds that the issue was discovered by Samuli Leinonen and reported through the Log4j Bug Bounty Program on YesWeHack, funded by the Sovereign Tech Agency. That kind of provenance does not make the bug more dangerous by itself, but it does tell you this was handled as a real vulnerability, not as a documentation misunderstanding or a vendor-scanner disagreement. (Apache Logging Services)
What CVE-2025-68161 actually is
At the center of this CVE is one sentence that every security engineer working in Java environments should internalize. Apache and NVD both describe the flaw this way: the Socket Appender in Apache Log4j Core does not perform TLS hostname verification of the peer certificate, even when verifyHostName or the log4j2.sslVerifyHostName system property is set to נכון. The advisory then spells out the consequence. Under the right conditions, a man-in-the-middle attacker can intercept or redirect log traffic if they can sit on or reroute the path between the logging client and the log receiver and present a certificate issued by a CA trusted by the configured trust store, or by the default Java trust store if no custom trust store is in place. (Apache Logging Services)
That description is a lot more precise than the way many vulnerability tickets get written internally. The common bad summary is “Log4j TLS vuln.” The better summary is “remote TLS log forwarding may trust the wrong endpoint.” The distinction matters because the vulnerable behavior is not activated by simply loading log4j-core at runtime. It appears when an environment uses the affected component, over the affected transport, with the affected trust assumptions, across a network path that can actually be interfered with. Broadcom’s Applications Manager advisory is valuable here because it translates Apache’s advisory into operational prerequisites. It says exploitation requires the Log4j Socket Appender to be configured for TLS to a remote logging server, requires man-in-the-middle control of traffic, and requires the attacker to present a certificate the client trusts. In their product context, Broadcom says the issue is not exploitable because the product uses local logging and does not expose the necessary Log4j configuration surface. That is a model example of how defenders should think about this CVE: not as a binary “present or absent,” but as a chain that may or may not be reachable in a real product. (Support Portal)
The weakness taxonomy also reinforces the point. Apache classifies the bug as CWE-297, Improper Validation of Certificate with Host Mismatch. NVD additionally maps it to CWE-295, Improper Certificate Validation. Those are trust-establishment failures, not memory safety bugs or parser overflows. The security problem is not that a packet crashes a process. The problem is that the client can be persuaded to accept a valid-looking but wrong identity for the server it thinks it is talking to. For a logging channel, that can expose event data, distort downstream analytics, or make a security team trust telemetry that never came from the sink it thought it was using. (NVD)
The scoring reflects that narrower path. NVD shows the Apache CNA’s CVSS 4.0 vector as network-based, no privileges required, no user interaction, but high attack complexity, with low confidentiality impact and low subsequent-system integrity impact. NVD’s own CVSS 3.1 score is 4.8 medium. None of that says “ignore this.” It says “this is not a one-packet internet-wide catastrophe.” When engineers read only the word “medium,” they often underreact. When they read only the word “Log4j,” they overreact. CVE-2025-68161 punishes both habits. (NVD)
Why hostname verification matters more than many teams realize
TLS is often explained too casually inside engineering organizations. Teams talk about “encrypting the connection” as if confidentiality automatically proves identity. It does not. Encryption without correct peer identity verification can still protect a session that terminates at the wrong server. Hostname verification is the step that checks whether the certificate the other side presents actually matches the destination you intended to reach. Apache’s Log4j documentation for network appenders describes the intended behavior directly: if hostname verification is enabled, the hostname in the X.509 certificate should be compared to the requested host, and the connection should fail on mismatch. Apache’s own remediation guidance for CVE-2025-68161 then acknowledges that this guarantee was not being enforced in the affected Socket Appender implementation. (Apache Logging Services)
This is especially important for remote logging because application developers often treat the logging path as secondary infrastructure. A payment service may have strict mTLS policies for user-facing traffic and database traffic, while log shipping quietly relies on inherited Java defaults, a general-purpose trust store, and a remote sink host that has not been revisited in years. Apache’s network appender documentation says the trust store determines whether the remote authentication credentials should be trusted, and notes that the default Java trust store is often not appropriate for Log4j Core communications. The same documentation, echoed in the security advisory, recommends using only the CA certificates required for the intended communication scope, such as a private or enterprise CA. That recommendation is not decorative. It directly narrows the set of certificates an attacker could use in a man-in-the-middle position. (Apache Logging Services)
This is where CVE-2025-68161 becomes more than a dependency-management footnote. Remote log channels routinely carry authentication events, internal IPs, request identifiers, stack traces, customer references, cloud resource names, and sometimes sensitive application context that never appears in frontend traffic. Even where the confidentiality impact seems low at first glance, the integrity implications can spread downstream. If logs can be redirected to the wrong receiver, delayed, selectively dropped, or observed on the way, the security team’s detection pipeline loses some of its reliability at the moment it needs it most. The advisory itself speaks in terms of intercepting or redirecting log traffic. The defensive inference is straightforward: once the wrong endpoint is trusted as the log sink, the logging stream is no longer a dependable source of truth. (NVD)
A lot of teams have learned this lesson the hard way in other parts of the stack. Certificates are “valid,” but the host is wrong. The CA is trusted, but the service is not the one you meant to reach. The channel is encrypted, but the wrong party is at the other end. CVE-2025-68161 is the logging-specific version of that failure mode. It matters because logging pipelines are often granted more trust than they earn.
The exact conditions required for exploitation
The easiest way to misjudge this CVE is to collapse all environments into one bucket. A much better approach is to ask whether your environment satisfies the full set of conditions Apache and downstream vendors describe. Those conditions are more restrictive than many scanner dashboards imply.
| Condition | מדוע זה חשוב | What often gets missed |
|---|---|---|
| You are running Log4j Core in an affected version range | Without the affected library, the issue does not exist | Some products bundle multiple versions or shaded jars |
| The application actually uses Socket Appender or an equivalent remote socket logging path | The vulnerable code path is not triggered otherwise | Many apps log locally only |
| TLS is enabled for that remote logging path | The bug concerns hostname verification in TLS | Plain TCP logging has different problems, but not this one |
| An attacker can intercept or redirect the path between client and receiver | The attack is a man-in-the-middle problem | Internal traffic is often assumed “safe” without proof |
| The attacker can present a certificate trusted by the appender’s trust store or default Java trust store | Trust root scope determines whether the fake endpoint is accepted | Teams often forget they are trusting far more CAs than intended |
The underlying sources for this table are consistent across Apache, NVD, GitHub Advisory, and vendor write-ups. Apache’s advisory provides the core conditions. NVD repeats them. Broadcom’s product advisory restates them in practical terms and uses them to explain why one of its products is not exploitable in context. That alignment is important because it means you do not need to choose between the “vendor says patch everything” school and the “scanner is probably wrong” school. The correct answer is conditional: patch broadly, but prioritize based on whether the vulnerable path is reachable. (Apache Logging Services)
Notice what is not on that list. You do not need an authenticated user inside the app. You do not need code execution on the host. You do not need someone to click anything. But you do need a real network position and a trust chain the client accepts. That is why the attack complexity is high in the CVSS vector while privileges required and user interaction are both none. CVE-2025-68161 is not hard because it is obscure. It is hard because it depends on architecture, trust stores, and path control. That kind of bug often gets mishandled operationally because it sits awkwardly between AppSec, platform engineering, and network security. (NVD)

Why many scanner findings are not automatically exploitable
By early 2026, a clear operational pattern had already emerged around this CVE. Security tools were flagging the affected log4j-core versions in vendor products and internal estates, while product teams kept answering a more nuanced question: does the vulnerable library exist, and is the vulnerable runtime path actually used? The difference between those two questions is the entire story.
Broadcom’s Applications Manager advisory is one of the clearest examples. It states that the product ships a vulnerable Log4j version, but the issue is not exploitable in that product because it does not allow Log4j configuration and uses local logging, which means the Socket Appender over TLS is not in play. IBM’s VM Manager Tool advisory makes a similar point from a different angle: IBM says the CVE cannot be exploited on any instance of the tool as shipped, yet still provides a jar-replacement workaround to stop security scans from reporting the issue. That is exactly what mature product security looks like in the face of dependency-driven scanner findings. The library version matters. The product context matters more. (Support Portal)
Veritas makes the same operational distinction in its Enterprise Vault support article covering CVE-2025-68161 in Elasticsearch. The article says affected Log4j versions may be present, but the vulnerable code cannot be executed within Elasticsearch because the relevant Socket Appender component is neither configured nor used there. That is a useful reminder that software composition analysis and runtime exploitability are related but not identical. A build can be noncompliant from a policy standpoint and still non-exploitable from a product-behavior standpoint. Security engineers need to be able to hold both truths at once. (Veritas)
The danger is that organizations often choose the wrong simplification. One camp says, “It is only a scanner issue.” That can be false in products that really do forward logs remotely over TLS with broad trust roots. Another camp says, “The library is present, therefore the product is vulnerable.” That is also false in products that never instantiate the vulnerable path. The right response is not philosophical. It is evidentiary. Can you show the affected dependency, the appender configuration, the transport, the trust store, the network path, and the vendor’s product statement? If you can, you can prioritize accurately. If you cannot, you are still guessing.
This is one reason the article cluster around CVE-2025-68161 has converged on the same practical framing. The authoritative pages that dominate public search visibility are not breathless exploit stories. They are advisories, release notes, issue trackers, and vendor product-impact statements. The recurring message is patch to 2.25.3, restrict trust roots, and do not confuse a version hit with a demonstrated exploit path. (Apache Logging Services)
Where the impact becomes real
If you want to understand the practical risk of CVE-2025-68161, stop asking only whether an attacker can “read logs.” Start asking which decisions depend on the assumption that those logs came from the right place and arrived intact. Once you frame the issue that way, the impact expands.
In many environments, remote logs feed SIEM pipelines, incident enrichment, fraud models, anomaly detection, retention workflows, and compliance evidence stores. If an attacker can redirect or observe that stream in transit, the damage is not limited to the individual log entry. A security team may lose confidence in the chronology of an incident. A compliance team may lose confidence in the custody chain for audit records. A platform team may make remediation decisions based on missing or misrouted telemetry. Apache’s advisory does not claim a universal catastrophic outcome, but its statement that log traffic may be intercepted or redirected is enough to justify treating this as a telemetry-trust issue, not as a cosmetic scanner nuisance. (Apache Logging Services)
In some sectors, the stakes are even higher. Consider environments where logs contain token identifiers, upstream endpoint names, internal tenant routing metadata, or exception traces with customer references. Even “low” confidentiality impact in a CVSS sense may still translate into meaningful disclosure in a regulated environment. NVD’s 4.8 and Apache’s 6.3 are technical severity assessments, not universal business-risk outcomes. Oracle’s January 2026 CPU makes this visible in practice. Oracle lists CVE-2025-68161 as affecting multiple Oracle GoldenGate and Oracle Communications products, and in those product contexts assigns downstream risk language that includes unauthorized read access to a subset of accessible data and unauthorized update, insert, or delete access to some accessible data, depending on product and scope. That is not a contradiction of the upstream advisory. It is what happens when a dependency flaw is embedded inside a real system with real trust and data flows. (אורקל)
There is also a second-order operational cost. Teams that have already lived through Log4Shell often default to two bad reactions: panic patching or cynical dismissal. Panic patching can break stable logging paths, especially in legacy middleware and commercial products where Log4j upgrades are coupled to vendor support matrices. Cynical dismissal leaves broad trust stores, remote log sinks, and dependency blind spots untouched. CVE-2025-68161 is a good test of organizational maturity precisely because it punishes both extremes. The teams that handle it best are the teams that can distinguish dependency exposure from reachable exposure without using that distinction as an excuse to do nothing. (Support Portal)
Real product impact is uneven, and the vendor record already proves it
A strong article on CVE-2025-68161 should not stay at the library level. It should show what downstream product impact looks like in practice. The official record already gives us both sides of that story.
| Product context | Vendor position | מדוע זה חשוב |
|---|---|---|
| Oracle GoldenGate Big Data and Application Adapters | Oracle lists CVE-2025-68161 as affecting supported versions and describes network access via TLS as the attack path | Shows a real enterprise product where the dependency issue has meaningful product impact |
| Oracle Communications IP Service Activator | Oracle lists the CVE as affecting version 7.5.0 | Confirms the issue propagates into supported commercial products |
| Oracle Communications Network Integrity | Oracle lists supported affected versions 7.3.6, 7.4.0, 7.5.0, and 8.0.0 | Demonstrates that exposure is not theoretical in the commercial ecosystem |
| Broadcom Applications Manager | Broadcom says the product ships the vulnerable library but is not exploitable because it uses local logging and does not allow the necessary configuration | Illustrates why library presence is not enough |
| IBM VM Manager Tool | IBM says the issue cannot be exploited in the product context, but offers a workaround to quiet scanners | Shows compliance pressure versus exploitability reality |
| Enterprise Vault with Elasticsearch | Veritas says affected Log4j may be present, but the vulnerable code path is not used in the product | Another example of a non-reachable path despite dependency presence |
The Oracle entries are particularly useful because they show something many teams forget: downstream vendors may score and describe the practical impact differently from the upstream library maintainer. Oracle’s January 2026 CPU includes multiple CVE-2025-68161 entries across product lines, with supported version ranges and product-specific descriptions. That does not change the underlying bug in Log4j Core. It changes the surrounding blast radius. The more valuable the data moving through the logging channel and the more privileged the consuming system, the more costly a trust-boundary failure can become. (אורקל)
By contrast, Broadcom, IBM, and Veritas show the opposite pattern: the dependency is there, but the exploit path is blocked by design or by product behavior. Those statements are not excuses to skip patching. They are evidence that reachability analysis matters. Good vulnerability management needs both dimensions. You want the dependency upgraded where possible, but you also want your incident priority to reflect whether the vulnerable behavior is actually exposed in your environment. (Support Portal)

Why this is not another Log4Shell, and why that comparison still matters
Every serious piece of writing about CVE-2025-68161 should answer the question readers are already asking in their heads: how does this compare to the 2021 Log4j wave? The short answer is that CVE-2025-68161 is materially narrower. The longer answer is more interesting, because it tells you how to triage it correctly.
Apache’s security page still provides one of the cleanest comparative views of the Log4j vulnerability family. CVE-2021-44228, the original Log4Shell issue, was the JNDI lookup flaw that could allow arbitrary code execution from attacker-controlled LDAP endpoints, with Apache listing it at CVSS 10.0 critical. CVE-2021-45046 showed that the initial fix was incomplete in some non-default configurations and could still lead to information leak and remote code execution in some environments. CVE-2021-45105 was the self-referential lookup recursion issue leading to denial of service. CVE-2021-44832 involved the JDBC Appender and could lead to remote code execution in certain configurations, but required a much stronger precondition: write access to the logging configuration or equivalent administrative control. (Apache Logging Services)
CVE-2025-68161 belongs much closer to that “configuration- and context-dependent” end of the spectrum than to Log4Shell. It is not a universal unauthenticated RCE primitive hiding in a ubiquitous code path. It is a trust-validation failure in a specific remote logging component. But the comparison is still useful because it exposes a familiar blind spot. The 2021 wave taught defenders to fear Log4j because of code execution. CVE-2025-68161 teaches a different lesson: logging components are security-sensitive even when they are not leading directly to RCE. Remote logging is infrastructure, and infrastructure trust failures can damage confidentiality, integrity, detection, and investigations even when no shell ever lands on a box. (Apache Logging Services)
The table below captures the practical difference.
| CVE | Core issue | Impact pattern | Operational lesson |
|—|—|—|
| CVE-2021-44228 | JNDI lookup leading to attacker-controlled remote code execution | Internet-scale emergency, broad blast radius | Never assume “logging” code is low-risk |
| CVE-2021-45046 | Incomplete fix under non-default layouts and MDC conditions | Still severe in some environments | Partial mitigations need careful validation |
| CVE-2021-45105 | Self-referential lookup recursion causing DoS | Availability-focused | Logging inputs can still be attack surfaces |
| CVE-2021-44832 | JDBC Appender configuration leading to RCE in certain configurations | Configuration-dependent, but still dangerous | Admin or config control can convert “medium” into serious impact |
| CVE-2025-68161 | Socket Appender does not enforce TLS hostname verification | MitM log interception or redirection under specific conditions | Trust validation in telemetry paths is a real security boundary |
Apache’s own historical advisories support this comparison directly. CVE-2021-44228 is described as JNDI-based arbitrary code execution. CVE-2021-44832 is described as JDBC Appender RCE in certain configurations. CVE-2025-68161 is described as missing TLS hostname verification in Socket Appender. They are all “Log4j CVEs,” but they are not the same kind of problem. Treating them as interchangeable creates bad incident response. (Apache Logging Services)
How to find out whether you are actually exposed
The defensive workflow for CVE-2025-68161 should begin with inventory, move to configuration, then end in reachability. Teams that reverse that order waste time. Teams that stop after dependency inventory create noise without knowing their real risk.
Start with dependency inventory
You need to know whether log4j-core is present, which version is present, and where it enters the build. This includes direct dependencies, transitive dependencies, shaded jars, fat jars, vendor bundles, cached bootstraps, and container images. In Java estates, the same vulnerable library often appears in multiple ways at once: as an explicit application dependency, inside a commercial product, in a build tool cache, or buried inside a plugin. The public issue trail around CVE-2025-68161 already shows this pattern in the wild across Apache JMeter, Ray, sbt, H2O, OpenRefine, and vendor products. The fix version is 2.25.3. Everything below that in the affected line deserves review. (GitHub)
Representative inventory commands:
# Maven
mvn -q dependency:tree | grep -i "log4j-core"
# Gradle
./gradlew dependencies --configuration runtimeClasspath | grep -i "log4j-core"
# Search unpacked application trees
find . -type f | grep -E 'log4j-core-.*\.jar'
# Inspect a fat jar or application package
jar tf app.jar | grep -i 'log4j-core'
# Search container images after export or unpack
grep -R -n "log4j-core" ./image-rootfs 2>/dev/null
These commands tell you whether the library exists. They do not tell you whether the vulnerable path is live. That comes next.
Inspect the logging configuration, not just the library list
For CVE-2025-68161, the most important configuration questions are brutally simple. Are you using a Socket Appender or equivalent remote socket logging path? Is it using TLS? Is a hostname involved rather than a raw IP literal? Are you relying on verifyHostName או log4j2.sslVerifyHostName and assuming that this made the path safe before 2.25.3?
Apache’s network appender documentation is the right primary source here. It documents the Ssl element, the trust store, and the intended hostname-verification behavior. The vulnerability exists precisely because the documented security control could be enabled without being correctly enforced in the affected path. That means the presence of a “secure-looking” configuration is not a sign that you are safe on vulnerable versions. In fact, it may be the signal that you are in the exact usage pattern that matters. (Apache Logging Services)
Useful search patterns for code and configuration review:
rg -n "SocketAppender|<Socket|<TLSSyslog|verifyHostName|log4j2\.sslVerifyHostName" .
If this returns nothing and the application only logs locally, your priority likely drops, though you still need to document the dependency. If it returns live remote logging configuration, the ticket becomes real.
Review trust stores, not just certificates
Apache’s documentation makes a strong point that many teams miss: the trust store for Log4j communications should be scoped to the intended communication domain, and the default Java trust store is often not appropriate. That statement matters because a wide trust store broadens the set of certificates an attacker could use in a man-in-the-middle position. Even when you patch to 2.25.3, a poorly scoped trust model remains a bad design for remote logging. The CVE fix repairs one broken security control. It does not make a broad, overly permissive trust store a good idea. (Apache Logging Services)
Questions worth asking during trust-store review include these. Are you using the default JRE trust roots? Are you trusting public CAs for an internal logging sink that should only ever terminate behind a private PKI? Are multiple unrelated sinks sharing the same trust scope? Are hostnames stable and specific, or are engineers using raw IPs and assuming TLS will “just work”? Apache’s documentation notes that hostname verification is only effective when the provided host is not an IP literal and is a valid hostname. That detail matters operationally, because teams that use IP-based sink definitions often create avoidable ambiguity around certificate identity. (Apache Logging Services)
Validate network reachability and path control
At this point, AppSec and platform engineers usually need help from the network side of the house. Apache’s advisory makes clear that exploitation depends on the attacker being able to intercept or redirect the traffic between client and receiver. That means local-only logging, loopback-only delivery, or heavily constrained internal routing can materially reduce practical risk even before patching. It also means internet-routable, cross-segment, or poorly governed remote log forwarding deserves higher priority. (Apache Logging Services)
The right question is not “can anyone on the internet exploit this?” The right question is “who can get in the path between this app and this sink, and what trust roots would the client accept if that happened?” For heavily segmented environments, that answer may be “very few.” For flat east-west networks, shared build labs, hostile wireless environments, unmanaged partner links, or legacy middleware zones, the answer may be much less comforting.
A safe verification pattern that does not require weaponizing the issue
Security teams often make one of two mistakes after the inventory phase. They either stop too early and treat the issue as purely theoretical, or they jump straight to offensive testing patterns that create more risk than value. There is a better path.
For CVE-2025-68161, the safest verification workflow is evidence-driven rather than exploit-driven. You do not need a flashy proof-of-concept to answer the engineering question. You need to know whether an affected component is present, whether the application uses a remote TLS socket logging path, whether the sink hostname and trust store are configured, whether the environment is still below 2.25.3, and whether the network path is constrained enough that a man-in-the-middle scenario is realistic only in a narrow threat model. That evidence is what determines incident priority and patch urgency. The primary sources themselves emphasize configuration and path conditions, not a universal exploit recipe. (Apache Logging Services)
A representative hardened configuration pattern after upgrading looks like this:
<Appenders>
<Socket name="RemoteAudit"
host="logs.internal.example.com"
port="6514">
<JsonTemplateLayout />
<Ssl verifyHostName="true">
<TrustStore location="conf/logging-truststore.p12"
password="${env:LOG_TRUSTSTORE_PASSWORD}"
type="PKCS12"/>
</Ssl>
</Socket>
</Appenders>
The important point about this example is not the XML itself. It is the sequence behind it. Upgrade first to a fixed version. Then keep verifyHostName enabled. Then restrict trust roots to the minimum intended CA set. Then verify that the sink name is a real hostname aligned with the certificate. That sequence is exactly what Apache’s advisory and documentation imply when read together. (Apache Logging Services)
A good remediation ticket should therefore capture four artifacts: the dependency version before and after, the relevant logging configuration, the trust-store scope, and the network ownership of the sink path. That is enough for engineering, security, and audit stakeholders to agree on the real state of exposure.

Remediation is not just “upgrade the jar”
The shortest correct answer for most teams is still “move to Log4j Core 2.25.3.” Apache’s advisory says to upgrade. NVD says to upgrade. GitHub Advisory says the patched version is 2.25.3. Apache’s 2.25.3 release notes explicitly tie the release to the hostname-verification fix. That is the baseline. (Apache Logging Services)
For Maven, the remediation often looks like this:
<dependencyManagement>
<dependencies>
<dependency>
<groupId>org.apache.logging.log4j</groupId>
<artifactId>log4j-bom</artifactId>
<version>2.25.3</version>
<type>pom</type>
<scope>import</scope>
</dependency>
</dependencies>
</dependencyManagement>
For Gradle, a representative version constraint might look like this:
dependencies {
constraints {
implementation("org.apache.logging.log4j:log4j-core:2.25.3")
}
}
But stopping at the dependency bump is a mistake. Apache’s own remediation guidance includes an alternative mitigation that is conceptually broader than the patch itself: use a private or restricted trust root. Their network appender documentation reinforces the same idea by recommending trust stores that contain only the CAs required for the intended communication scope. In practice, the best remediation sequence is layered. Upgrade the library. Reduce trust scope. Verify hostname-based addressing. Remove remote socket logging where you do not need it. Limit which networks can reach the sink. And where a commercial product is involved, read the vendor’s statement instead of assuming the upstream library fix can be dropped in arbitrarily. (Apache Logging Services)
That last point matters more than it sounds. Many of the public pages around CVE-2025-68161 are product advisories precisely because commercial software often bundles Log4j inside a supported runtime. In those cases, your job is not only to eliminate the CVE. It is to eliminate it without leaving the product in an unsupported state. Oracle’s CPU, IBM’s workaround note, Broadcom’s product advisories, and product-community threads in projects like OpenRefine and JMeter all reflect that same supply-chain reality. Security teams that insist on generic “just replace the jar” guidance without checking the vendor path are often solving the wrong problem. (אורקל)
What a mature triage workflow looks like in a large Java estate
If you are responsible for a broad Java environment, the right response to CVE-2025-68161 is not a single patch command. It is a triage model.
The first tier is pure dependency exposure. Which repositories, services, images, tools, vendor products, and build caches contain log4j-core below 2.25.3? This tier exists to make sure nothing disappears into the long tail of internal ownership problems. The second tier is runtime-path relevance. Which of those assets actually use Socket Appender or another remote TLS socket logging configuration? Which assets only log locally? Which assets are commercial products with a vendor impact statement already available? The third tier is trust and path risk. Among the truly relevant cases, which ones rely on default trust roots, traverse shared or weakly controlled networks, or feed logs into especially sensitive downstream systems? (Apache Logging Services)
A simple prioritization matrix often works better than trying to force everything into one severity queue.
| עדיפות | Environment profile | פעולה מומלצת |
|---|---|---|
| Critical internal priority | Affected Log4j Core, live remote TLS Socket Appender, broad trust store, weakly controlled network path, sensitive audit or security logs | Expedite upgrade to 2.25.3, restrict trust roots, validate sink path and hostname use |
| גבוה | Affected Log4j Core and remote TLS log forwarding exist, but network path is controlled | Patch in normal emergency cycle, tighten trust store and network controls |
| בינוני | Affected library present, uncertain appender usage, incomplete product knowledge | Investigate configuration and vendor statements before escalation |
| Low operational but still actionable | Affected library present only in non-reachable or vendor-confirmed non-exploitable contexts | Patch on maintenance path or follow vendor fix, document compensating evidence |
This kind of model aligns much better with the public record than blanket severity labels do. Apache and NVD give you the upstream technical truth. Vendor advisories show how product context can either amplify or suppress real risk. The job of a mature security program is to connect those layers without lying to itself in either direction. (Apache Logging Services)
היכן Penligent משתלב באופן טבעי
CVE-2025-68161 is a good example of why security teams outgrow simple version matching. A scanner can tell you that log4j-core-2.17.1.jar exists somewhere in an image or vendor bundle. That is useful, but incomplete. The harder question is whether the affected runtime path is live, whether the service is really forwarding logs over TLS, what trust roots are in use, whether the sink is reachable across a risky path, and what evidence you can attach to the remediation ticket when engineering asks whether the issue is “real.” That is exactly the gap between a vulnerability feed and a verification workflow. Penligent’s own public material on vulnerability management tools argues that modern programs need to move beyond raw CVSS and combine exploitability, exposure context, and validation. Its recent writing on AI pentest tooling makes a similar point from another direction: the hard part is not generating findings, but turning signal into defensible proof. In the context of CVE-2025-68161, that means proving whether a dependency alert is a reachable telemetry-trust problem or just a library-presence event. (Penligent)
That is why a platform like Penligent is useful here when used responsibly. Not because a logging CVE demands noisy exploit theatrics, and not because every dependency hit should become an active test. It is useful because this class of issue benefits from asset discovery, dependency enumeration, configuration inspection, and controlled verification that produces evidence engineering teams can act on. Penligent’s public overview and automated-penetration-testing material position the product around exactly that operational handoff: discovering exposed components, validating real-world security relevance, and producing reportable outputs rather than leaving teams with a pile of unactionable version alerts. For a CVE like this one, that is the right role for automation. (Penligent)
The mistake to avoid
The single biggest mistake with CVE-2025-68161 is treating it as either a nothingburger or an apocalypse. It is neither.
If you ignore it because it is “only medium,” you miss the fact that remote logging is part of your trust boundary and that weak trust-store design can turn a narrow library issue into a real telemetry problem. If you overstate it as “the next Log4Shell,” you undermine credibility, burn engineering attention, and teach teams to distrust future vulnerability guidance. Apache’s own documentation and advisory already point to the correct middle path: patch to 2.25.3, limit trust roots, and understand when the affected component is actually in use. Vendor responses from Broadcom, IBM, Veritas, and Oracle then show what that middle path looks like in real products. Some deployments are truly exposed. Some are not exploitable in context. All of them benefit from better evidence than a package-version string alone. (Apache Logging Services)
Further reading
- Apache Log4j Security Advisories
- NVD Entry for CVE-2025-68161
- Apache Log4j 2.25.3 Release Notes
- Apache Log4j Network Appenders Documentation
- GitHub Advisory Database Entry for CVE-2025-68161
- Oracle Critical Patch Update, January 2026 Risk Matrix
- Penligent — Vulnerability Management Tools: A Complete 2026 Guide
- Penligent — AI Pentest Tool, What Real Automated Offense Looks Like in 2026
- Penligent — Overview of Penligent.ai’s Automated Penetration Testing Tool
- Penligent — Automated Penetration Testing: A New Era in Cybersecurity
- Penligent — Ingress-NGINX CVEs That Actually Matter: Patch Paths, Real Blast Radius, and How to Prove You’re Safe