要旨
CVE-2026-24858 is not just another management-plane bug with a scary score. It is a live example of what happens when cloud-assisted identity becomes deeply embedded in security appliances and the trust boundary around that identity flow fails. Fortinet’s own advisory and the NVD describe the issue as an authentication bypass using an alternate path or channel, tracked under CWE-288. The published impact is unusually serious: an attacker with a FortiCloud account and a registered device could log into devices registered to other accounts, provided FortiCloud SSO was enabled on those devices. NVD also records the Fortinet CNA severity as 9.8 and notes that the CVE was added to CISA’s Known Exploited Vulnerabilities catalog on January 27, 2026. (NVD)
That last detail matters more than the score. KEV inclusion means this was not treated as a theoretical edge case. Public reporting from Fortinet, CISA-linked references, Arctic Wolf, SecurityWeek, Rapid7, and Help Net Security all converge on the same conclusion: the flaw was exploited in the wild, attackers used it to obtain administrative access, and the observed post-authentication activity included creating local admin accounts and exfiltrating device configuration data. (NVD)
What makes CVE-2026-24858 especially important for security engineers is that it was disclosed in the aftermath of two earlier FortiCloud SSO issues, CVE-2025-59718 and CVE-2025-59719. Those earlier vulnerabilities already showed that the FortiCloud SSO path was under attack. Then customers started reporting suspicious admin logins on devices that were already patched against the December issues, forcing Fortinet to investigate and disclose a new attack path. That sequence changes how defenders should think about the incident. This is not just about one firmware build. It is about a fragile identity trust chain spanning cloud, device registration, management UI, and tenant separation. (フォーティネット)
Across current coverage, the most discoverable phrase associated with this incident is not the raw CVE identifier by itself, but the cluster of terms around FortiCloud SSO authentication bypass そして FortiCloud SSO zero-day. That pattern is visible in how the major results frame the issue, including Fortinet’s own advisory, Arctic Wolf’s bulletin, SecurityWeek’s reporting, Help Net Security’s incident coverage, and The Hacker News. For a technical article meant to match how practitioners actually look for the issue, those phrases deserve to sit alongside the CVE in headings and body copy. (FortiGuard Labs)
This article breaks the incident down in practical terms. It explains what is confirmed, what changed over time, which products and versions were affected, how observed attacks behaved, how CVE-2026-24858 relates to the December FortiCloud SSO flaws, what to hunt for in logs, what to patch first, and why this vulnerability should reshape how teams validate cloud-linked admin authentication on perimeter devices. Where it is genuinely useful, it also connects the case to modern AI-assisted exposure validation, because this is the sort of issue that simple version matching can miss or flatten into false confidence. (寡黙)
What CVE-2026-24858 is
The formal description published through NVD is clear. CVE-2026-24858 is an authentication bypass vulnerability affecting multiple Fortinet products. The condition allows an attacker with a FortiCloud account and a registered device to log into other devices registered to other accounts when FortiCloud SSO authentication is enabled on those devices. NVD lists the issue under CWE-288 and records a critical CNA-provided CVSS v3.1 score of 9.8 with vector AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H. (NVD)
The initial NVD description covered FortiAnalyzer, FortiManager, and FortiOS. NVD change records and later public reporting broadened the picture, and Tenable’s CVE page reflects an expanded affected set that includes FortiProxy and FortiWeb as well. By late January and early February 2026, Fortinet ecosystem documents and third-party summaries consistently treated the issue as a multi-product FortiCloud SSO problem rather than a FortiOS-only event. (NVD)
The most important operational qualifier is that this was not universally reachable on every deployment. Public guidance repeatedly notes that exploitation required FortiCloud SSO to be enabled on the target device. Fortinet, Arctic Wolf, SecurityWeek, and Rapid7 all point out another subtle but consequential detail: although the feature is disabled in factory defaults, it can become enabled when a device is registered through the GUI unless the administrator explicitly opts out. In practice, that means many organizations may have had more exposure than they realized because the enabling condition was tied to ordinary onboarding workflow rather than an obviously risky change. (Arctic Wolf)
This distinction is worth slowing down for. Security teams often read “disabled by default” as “probably not relevant.” In modern appliance ecosystems, that is not always how exposure works. A feature can be disabled at first boot and still become common in the field because the recommended cloud registration path turns it on. CVE-2026-24858 is a case study in how that gap between product default and operational reality creates dangerous blind spots. (Arctic Wolf)
Why this flaw matters more than a typical login bypass
Many authentication bypasses are severe because they grant access to one application or one device. CVE-2026-24858 is worse in a different way. It touches the trust relationship between a device’s administrative plane and a cloud-backed single sign-on system that is expected to represent identity correctly across accounts and tenants. When that trust breaks, the result is not merely “someone bypassed a login page.” The result is that an external identity and registration context may be accepted as authoritative for the wrong customer environment. That is a deeper architectural failure. The Fortinet description itself highlights cross-account access as the core impact. (NVD)
That matters because the affected products sit near the center of network control and visibility. FortiOS powers FortiGate firewalls. FortiManager handles centralized administration. FortiAnalyzer aggregates and analyzes logs. FortiProxy and FortiWeb sit on important traffic paths in many deployments. Administrative access to any of these systems can expose configuration state, policy, topology, credentials, monitoring context, and control surfaces that matter far beyond the individual appliance. SecurityWeek, Arctic Wolf, and Fortinet’s own incident notes all point to configuration theft and local admin creation as observed consequences. (フォーティネット)
This is also why CISA’s KEV decision is so significant. KEV is not a popularity contest and not every severe CVE lands there. NVD explicitly marks CVE-2026-24858 as included in KEV, and the listed required action was to apply vendor mitigations or discontinue use if mitigations were unavailable, with a federal due date of January 30, 2026. That is a short fuse, and short fuses are typically reserved for bugs that materially change intrusion risk in the real world. (NVD)
The broader lesson is uncomfortable but useful. A cloud convenience feature on a security appliance can quietly become one of the most sensitive identity surfaces in the environment. Once administrative login depends on remote service trust, tenant isolation, registration state, and assertion handling, the security problem is no longer “does the password screen work.” It becomes “is every link in this trust chain still honest, isolated, and bound to the right device and the right tenant.” CVE-2026-24858 shows what happens when the answer is no. (フォーティネット)

Timeline, how the incident unfolded
To understand CVE-2026-24858 correctly, you have to start in December 2025. Fortinet had already disclosed CVE-2025-59718 and CVE-2025-59719, both critical FortiCloud SSO login authentication bypass vulnerabilities. Fortinet described those earlier bugs as improper verification of cryptographic signature issues that allowed unauthenticated attackers to bypass FortiCloud SSO authentication via crafted SAML messages when the feature was enabled. Fortinet’s January 2026 blog later referenced those December findings as the backdrop for the new incident. (FortiGuard Labs)
In January 2026, customers began reporting suspicious logins and post-login activity on devices that appeared fully updated against the December flaws. Fortinet’s January 22 blog post states that a small number of customers reported unexpected login activity that looked similar to the earlier SSO abuse, but investigation found cases where exploitation occurred on devices already upgraded to the latest release at the time of attack. That observation strongly suggested a new path rather than a straightforward replay of the previous vulnerabilities. (フォーティネット)
Fortinet’s published incident update sequence is one of the most useful public timelines for defenders. On January 23, the company disabled the FortiCloud accounts being abused. On January 26, it disabled FortiCloud SSO to prevent further abuse. On January 27, it issued the public advisory for the new flaw and restored FortiCloud SSO access with a restriction: vulnerable devices would no longer be supported for FortiCloud SSO logins. By January 30, the advisory had been updated with the last of the release information. (フォーティネット)
The same day the public advisory appeared, CISA added CVE-2026-24858 to KEV, and SecurityWeek reported the federal patching deadline of January 30. Rapid7’s updated write-up also emphasized that Fortinet had deployed a cloud-side fix on January 26, 2026, while still publishing fixed software because the server-side change introduced breaking changes to the FortiCloud SSO login protocol. That combination is unusual and important. It means the cloud service was part of the mitigation story, but it did not eliminate the need for customer-side upgrades. (NVD)
This timeline is why defenders should resist oversimplified summaries such as “Fortinet fixed it in the cloud” or “this was just a patch bypass of the December bug.” Public sources support neither simplification cleanly. What they support is more nuanced: there were earlier FortiCloud SSO issues, a new attack path emerged against systems already updated for those issues, Fortinet intervened at the cloud side to reduce exploitation, and patched client versions remained necessary to restore secure FortiCloud SSO functionality. (フォーティネット)
The search language that best matches the incident
When practitioners search for a vulnerability, they rarely use only the CVE number. They use the language that the incident ecosystem has converged on. For CVE-2026-24858, that language is consistently centered on FortiCloud SSO authentication bypass, FortiCloud SSO zero-dayそして Fortinet FortiCloud SSO. You can see that in the naming used by Fortinet’s PSIRT page, Arctic Wolf’s bulletin title, SecurityWeek’s article title, Help Net Security’s coverage, and The Hacker News reporting. (FortiGuard Labs)
That is not a marketing observation. It is a technical one. Those phrases capture the operational essence of the bug better than the CVE number alone. “FortiCloud SSO authentication bypass” tells engineers where the trust failure lives. “FortiCloud SSO zero-day” tells incident responders why the initial signal was alarming even on updated devices. “Fortinet multiple products” tells infrastructure owners the blast radius may include more than just firewalls. If you are writing runbooks, internal advisories, or SIEM content, those phrases are the practical handles that map best to the public record. (FortiGuard Labs)
Affected products, exposed conditions, and fixed versions
The affected-product story evolved during disclosure, which is common in real incidents and one reason relying on a single early article can leave defenders under-informed. The NVD description initially covered FortiAnalyzer, FortiManager, and FortiOS, while later change records and third-party CVE aggregators reflected broader scope. Tenable’s current CVE page includes FortiProxy and FortiWeb in addition to the original products. Help Net Security also reported that later Fortinet document changes showed FortiWeb and FortiProxy in scope, and that FortiManager Cloud, FortiAnalyzer Cloud, and FortiGate Cloud were not impacted. Fortinet’s January 28 blog update added another important clarification: third-party SAML identity providers and FortiAuthenticator used as custom IdP were not impacted by this specific issue. (NVD)
The table below consolidates what is consistently supported in the public record. Where Fortinet release-note pages are available, they are the best confirmation that a given train is no longer vulnerable.
| 製品 | Publicly affected versions | Publicly documented fixed version examples | 備考 |
|---|---|---|---|
| FortiOS | 7.6.0 through 7.6.5, 7.4.0 through 7.4.10, 7.2.0 through 7.2.12, 7.0.0 through 7.0.18 | 7.6.6, 7.4.11, 7.2.13, 7.0.19 | NVD, Arctic Wolf, SecurityWeek, Fortinet release notes confirm patched trains. (NVD) |
| FortiManager | 7.6.0 through 7.6.5, 7.4.0 through 7.4.9, 7.2.0 through 7.2.11, 7.0.0 through 7.0.15 | 7.6.6, 7.4.10, 7.2.13, 7.0.16 | Arctic Wolf and SecurityWeek list fixed trains; release notes confirm 7.6.6. (Arctic Wolf) |
| FortiAnalyzer | 7.6.0 through 7.6.5, 7.4.0 through 7.4.9, 7.2.0 through 7.2.11, 7.0.0 through 7.0.15 | 7.6.6, 7.4.10, 7.2.12, 7.0.16 | Arctic Wolf and SecurityWeek list fixed trains; release notes confirm 7.6.6. (Arctic Wolf) |
| FortiProxy | Public CVE pages later included 7.6.0 through 7.6.4, 7.4.0 through 7.4.12, older 7.2 and 7.0 trains | 7.6.5 or 7.6.6 depending on train, 7.4.13 | Tenable and Fortinet docs confirm FortiProxy was in scope; release notes confirm 7.4.13 and 7.6.5 are no longer vulnerable. (Tenable®) |
| FortiWeb | Later public sources include 8.0.0 through 8.0.3, 7.6.0 through 7.6.6, 7.4.0 through 7.4.11 | Later fixed versions were reflected in ecosystem reporting, but public release-note evidence is harder to pull from the open web snapshot here | The issue appears in later affected lists, but the open-source confirmation trail is less tidy than for FortiOS and FortiManager. (Tenable®) |
The condition for exposure is just as important as the version. Public guidance repeatedly states that the device must have FortiCloud SSO enabled for exploitation to apply. If your appliance version was in range but FortiCloud SSO was not enabled, the public record does not suggest the same attack path. Conversely, if the feature was enabled, version alone was not enough information during the most active phase of the incident. Defenders had to check for exploitation indicators as well. (フォーティネット)
One more nuance matters here. Fortinet’s temporary cloud-side changes reduced the immediate exploitation path by preventing vulnerable versions from using FortiCloud SSO, but those changes did not magically sanitize a device that had already been compromised. That is why the remediation advice from Fortinet-aligned reporting still included log review, suspicious-admin review, credential rotation, and restoration from clean configurations where compromise indicators were present. (フォーティネット)

How the attack path should be understood
Public reporting does not provide a full exploit walkthrough, and that is a good thing. But the confirmed impact is enough to reason about the attack path at a defensive level.
The earlier December issues, CVE-2025-59718 and CVE-2025-59719, were explicitly tied to crafted SAML messages and improper verification of cryptographic signatures in the FortiCloud SSO login flow. Those descriptions tell us that the trust boundary under stress was already the SSO assertion path. CVE-2026-24858 appears after customers observed similar abuse against patched systems, and Fortinet’s new description changed the framing from signature-verification weakness to authentication bypass using an alternate path or channel. That strongly suggests the security problem was not just one invalid signature check but a larger logic issue around how administrative FortiCloud SSO access was bound to accounts and devices. (FortiGuard Labs)
NVD’s wording is especially revealing. The attacker is described not as an anonymous outsider with no foothold at all, but as someone with a FortiCloud account and a registered device who can log into devices associated with other accounts. That is not the language of a simple credential bypass. It is the language of a control-plane isolation failure, where some identity or registration state that should be scoped to one tenant can be abused to satisfy trust checks for another. (NVD)
From a systems perspective, this is why CVE-2026-24858 belongs in the same mental bucket as other cross-boundary identity failures. The scary part is not only that login succeeds. The scary part is that a platform accepted the wrong source of trust for an administrative action. Once that happens on perimeter and control products, everything behind those products becomes harder to trust as well. Firewall policy, VPN settings, address objects, log forwarding, admin accounts, and configuration archives all become suspect. Fortinet’s own attack notes and Arctic Wolf’s observations point directly at local admin creation and configuration exfiltration as follow-on steps. (フォーティネット)
What attackers were observed doing
Fortinet’s January 22 incident analysis provides the most concrete public observations. The company published indicators of compromise that included the SSO login user accounts cloud-noc@mail.io そして cloud-init@mail.io, observed source IP addresses including 104.28.244.115 そして 104.28.212.114, and additional third-party observed IPs 37.1.209.19 そして 217.119.139.50. It also reported that after successful authentication via SSO, the actor created local admin accounts such as audit, backup, itadmin, secadminそして support. Fortinet included a representative log entry showing a successful admin login with method="sso" そして ui="sso(...)". (フォーティネット)
Arctic Wolf’s bulletin adds useful post-authentication context. It states that threat actors authenticated against Fortinet devices with FortiCloud SSO enabled, created local administrative accounts for persistence, and exfiltrated configuration data. SecurityWeek reported the same broad pattern, citing automated attacks targeting FortiGate devices to create new administrators and exfiltrate configuration files. Rapid7 also noted observations of attackers authenticating as admin and downloading the system configuration, warning that organizations with indicators of compromise should assume credential exposure because configuration files often contain hashed credentials. (Arctic Wolf)
That sequence is important because it tells defenders where to look after the login event. If your response stopped at “we patched” or even “we disabled SSO,” you may have missed the persistence stage. A local admin created after malicious SSO login can survive after the original cloud path is blocked. A stolen configuration can extend the compromise window by exposing secrets, certificates, topology details, and VPN settings long after the visible event has passed. Public reporting does not support complacency here. It supports the opposite. (フォーティネット)
One more caution is necessary. Public IoCs are useful, but they are not sufficient for clean bill-of-health decisions. Fortinet itself notes that attacker email addresses may change in the future, and the company observed shifts in behavior over time. Treat IoCs as high-confidence positives, not as exhaustive negatives. A clean sweep for the published usernames does not prove the environment was untouched. (フォーティネット)

How CVE-2026-24858 relates to CVE-2025-59718 and CVE-2025-59719
This is one of the first questions engineers ask, and for good reason. The names, timing, and affected surface are similar enough to cause confusion.
CVE-2025-59718 and CVE-2025-59719 were FortiCloud SSO login bypass vulnerabilities disclosed by Fortinet in December 2025. Fortinet described them as improper verification of cryptographic signature issues allowing unauthenticated attackers to bypass authentication using crafted SAML messages if the feature was enabled. Fortinet’s January 2026 incident blog explicitly references these flaws as the initial context for the later suspicious activity. (FortiGuard Labs)
CVE-2026-24858 emerged when customers and defenders saw suspicious admin logins on systems that had already applied the December fixes. Fortinet’s January 22 analysis says this directly: some attacked devices had been fully upgraded to the latest release at the time, implying a new attack path. Rapid7 later emphasized that CVE-2026-24858 was confirmed as a net-new vulnerability rather than a simple patch bypass. (フォーティネット)
The cleanest way to explain the relationship is this. The December bugs and CVE-2026-24858 all sit on the same operational attack surface, FortiCloud SSO administrative login. The December flaws were tied publicly to crafted SAML and signature verification failures. CVE-2026-24858 was publicly framed as a distinct authentication bypass using an alternate path or channel. So the family resemblance is real, but the public record does not support reducing them to one identical bug. They are better understood as closely related trust-boundary failures on the same identity plane. (FortiGuard Labs)
For defenders, this distinction changes response priorities. If you treat CVE-2026-24858 as nothing more than “the old SAML bug again,” you may underweight the importance of reviewing cloud-side trust assumptions, registration workflows, and tenant isolation. If you treat it as completely unrelated, you miss the obvious lesson that repeated incidents on the same authentication surface often signal broader design fragility. The safer conclusion is that FortiCloud SSO became a concentrated risk domain, and organizations using it should validate that domain much more aggressively than they would a routine appliance feature. (フォーティネット)
Business and operational impact
A vulnerability like CVE-2026-24858 does not need remote code execution to become a major incident. Administrative access to firewalls, managers, analyzers, proxies, or web firewalls can be enough to produce consequences that are operationally equivalent to a major breach.
If an attacker can authenticate into FortiGate or FortiOS-backed devices, they may gain visibility into interface layouts, security policies, VPN tunnels, address groups, routing constructs, objects, and administrative settings. If they can export configuration files, they can collect a compact blueprint of the environment. Rapid7 warns that configuration downloads often imply credential exposure risk because hashed credentials may be included. That makes downstream password cracking, credential stuffing into related systems, or long-tail lateral movement more plausible even if the original appliance is later patched. (ラピッド7)
If the compromised product is FortiManager, the risk becomes more centralized. Administrative control of a management plane can affect fleets of devices, change policy at scale, or create misleading confidence in central source-of-truth. If the product is FortiAnalyzer, the concern shifts toward visibility integrity and the sensitivity of log data. If the product is FortiProxy or FortiWeb, the risk includes high-value traffic mediation surfaces that can influence what is inspected, blocked, bypassed, or logged. The public record around CVE-2026-24858 does not need to document every theoretical abuse path for those implications to be obvious. The role of these products in enterprise architecture already tells the story. (Tenable®)
There is also a response-cost impact. Cloud-side mitigations can stop active abuse, but they create operational friction of their own. Fortinet’s mitigation path effectively made FortiCloud SSO unsupported for vulnerable firmware, which means teams had to accelerate upgrades to preserve normal SSO function. In the middle of an incident, that can mean out-of-cycle maintenance, emergency CAB approvals, rushed testing, and overlapping investigative work. The cost is not just attacker access. It is also forced defensive urgency. (フォーティネット)
Detection and hunting guidance
The strongest public hunting guidance starts with Fortinet’s own logs. The company published a representative log pattern for malicious login activity with logdesc="Admin login successful", a user field containing one of the known malicious account names, ui="sso(...)"そして method="sso". It also provided example usernames and source IP addresses, plus examples of local admin names created after login. That gives defenders a practical first-pass hunting model: suspicious FortiCloud SSO admin login, followed by new local admin creation, followed by configuration access or export. (フォーティネット)
A reasonable first step in log analysis is to search for successful admin logins where the authentication method is SSO and the UI context explicitly indicates SSO, then pivot on the source IP and account. Even if the published IoCs do not match, the pattern itself is still useful. Administrative SSO logins from unusual geography, infrastructure providers, or cloud-fronted IP space deserve investigation, especially if they are followed closely by configuration downloads or admin-account changes. Fortinet’s own notes mention that attackers appeared to switch to Cloudflare-protected IPs, which is a reminder not to anchor too hard on a short IP list. (フォーティネット)
Here is a practical Splunk-style search based on Fortinet’s published log structure:
index=fortinet sourcetype=fortigate
(logdesc="Admin login successful" OR msg="Administrator*logged in successfully*")
(method="sso" OR ui="sso*")
| eval suspicious_user=if(match(user,"cloud-init@mail.io|cloud-noc@mail.io"),"known_ioc","unknown")
| stats count min(_time) as first_seen max(_time) as last_seen values(srcip) values(user) values(profile) by host suspicious_user
| sort - last_seen
That query is intentionally conservative. It is designed to surface the authentication pattern first. Once you have hits, add a second pivot for suspicious admin creation:
index=fortinet sourcetype=fortigate
("audit" OR "backup" OR "itadmin" OR "secadmin" OR "support")
("admin" OR "administrator")
| stats count values(srcip) values(user) by host _time
| sort - _time
If your SOC prefers Sigma-style content, the logic can be expressed like this:
title: Fortinet Suspicious Administrative SSO Login Related to CVE-2026-24858
id: 4f9f7f9e-2485-4260-a111-forticloud-sso
status: experimental
logsource:
product: fortinet
service: fortigate
detection:
selection_login:
logdesc: "Admin login successful"
method: "sso"
selection_known_users:
user|contains:
- "cloud-init@mail.io"
- "cloud-noc@mail.io"
condition: selection_login and selection_known_users
level: high
falsepositives:
- Legitimate FortiCloud SSO admin use with reused test identities
tags:
- attack.initial_access
- attack.valid_accounts
- cve.2026.24858
If you need quick shell-side triage on exported logs:
grep -E 'Admin login successful|method="sso"|ui="sso|cloud-init@mail.io|cloud-noc@mail.io|audit|backup|itadmin|secadmin|support' forti-logs.txt
Detection should not stop at the login. Hunt for configuration export events, unexpected admin profile assignments, changes to trusted hosts, new API administrators, and unusual activity on the management interface. Arctic Wolf and Rapid7 both point defenders toward the practical sequence of admin login, persistence creation, and configuration exfiltration. That sequence should guide your timeline reconstruction. (Arctic Wolf)

Immediate mitigation and response steps
The first action is straightforward: upgrade affected products to fixed versions appropriate for your train. For FortiOS, public reporting and Fortinet release notes support 7.4.11, 7.6.6, 7.2.13, and 7.0.19 as fixed examples. For FortiManager and FortiAnalyzer, fixed trains include 7.6.6 with additional branch-specific versions listed by Arctic Wolf and SecurityWeek. For FortiProxy, Fortinet documentation confirms at least 7.4.13 and 7.6.5 as no longer vulnerable on those trains. (Arctic Wolf)
The second action is to treat patching and compromise assessment as separate workstreams. Fortinet’s own guidance and aligned reporting recommend checking logs for published IoCs and suspicious admin activity, reviewing all administrative accounts for unexpected entries, rotating credentials if indicators are present, and restoring device configuration from a known clean version where compromise is suspected. That is the right model. A patched but backdoored management plane is still compromised. (フォーティネット)
The third action is to narrow administrative exposure. Help Net Security summarizes Fortinet’s continuing advice to restrict administrative access to edge devices over the internet and, where possible, limit via local-in policies the IP addresses allowed to reach the admin interface. That advice predates this single CVE as a general best practice, but incidents like CVE-2026-24858 are why the practice exists. Even when SSO is the initial weakness, limiting who can reach the management plane reduces the value of that weakness. (ヘルプ・ネット・セキュリティ)
The fourth action is to verify whether FortiCloud SSO is enabled and whether you actually need it. Fortinet’s January 22 blog provided a temporary workaround to disable administrative login using FortiCloud SSO through the GUI or CLI. For organizations that do not strictly need administrative cloud SSO, removing the feature from the attack surface is often cleaner than keeping it enabled out of habit. Fortinet later re-enabled the service in a safer way, but that does not make the feature mandatory for every environment. (フォーティネット)
A FortiOS CLI example for temporary disablement, consistent with Fortinet’s own blog guidance, is:
config system global
set admin-forticloud-sso-login disable
end
If you are operating in a regulated or high-assurance environment, add one more step: document whether FortiCloud SSO became enabled through normal device registration workflow. That matters for root-cause analysis and future control design. Many organizations may discover that no one intentionally “turned on a risky feature” at all. The exposure may have entered through standard onboarding frictionlessly. Public reporting repeatedly notes that the feature can be enabled during GUI registration unless explicitly disabled. (Arctic Wolf)
What defenders should learn from the cloud-side mitigation
Fortinet’s response included a notable cloud-side intervention. The company disabled FortiCloud SSO on January 26 to prevent abuse and then restored it on January 27 in a state that no longer supported vulnerable device versions. Rapid7 noted that this was not simply a marketing statement about “platform hardening”; Fortinet’s cloud-side fix also introduced breaking changes to the FortiCloud SSO login protocol, which is why updated client software remained necessary. (フォーティネット)
There are two big defensive lessons here.
The first is that modern appliance risk is often split across customer-managed firmware and vendor-managed cloud control planes. If your incident model assumes all meaningful fixes arrive as local firmware patches, you can miss half the story. Conversely, if your model assumes the vendor can fix everything in the cloud, you can miss residual risk on already-accessed devices or client compatibility and trust-state problems. CVE-2026-24858 needed both sides of the response. (フォーティネット)
The second is that “service restored” is not the same as “incident over.” When a vendor restores cloud functionality in a safer mode, customers still need to answer harder questions. Was the device previously accessed? Was a local admin planted? Was a configuration exported? Were there follow-on changes to policy, VPN, API, or logging? Public reporting on this case strongly supports that post-authentication abuse happened, so the burden remains on defenders to reconstruct state, not just re-enable convenience. (フォーティネット)
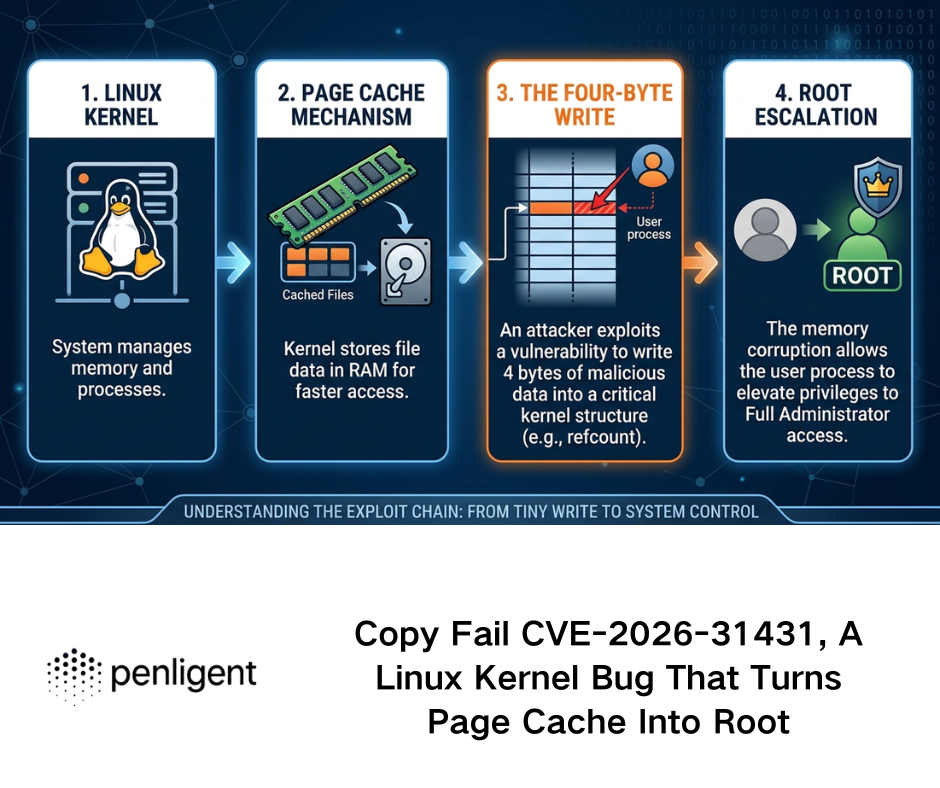
Why version-based scanning alone is not enough here
CVE-2026-24858 is exactly the kind of vulnerability that exposes the limits of simplistic scanner logic. A pure version check can tell you whether a device is in a potentially affected range. It cannot tell you whether FortiCloud SSO is enabled, whether it became enabled through GUI registration, whether the management interface is exposed to a dangerous source population, whether the cloud-side trust relationship has changed, or whether the device has already been used to create a rogue local admin. Public reporting around this incident makes all of those questions relevant. (Arctic Wolf)
That is why this case maps naturally to a more verification-oriented security workflow. Penligent’s own writing on 2026 vulnerability handling explicitly uses CVE-2026-24858 as an example of a class of flaw where a useful platform does more than match version numbers. It emphasizes interaction with the exposed identity and management path to validate whether the risky condition is actually present. That framing is technically sensible for this incident because the real-world question is not only “is the firmware old,” but “is the risky SSO path live, reachable, and bound in a way that could matter.” (寡黙)
Used carefully, AI-assisted validation can also help reduce noise after disclosure. Security teams often spend the first 48 hours after a high-profile KEV entry drowning in asset lists and version tables. A better workflow is to combine patch intelligence with runtime validation of exposed management paths, SSO configuration state, and post-compromise evidence. That is the space where an AI-driven penetration testing platform can be genuinely helpful without replacing the need for disciplined incident response. (寡黙)
Related CVEs that belong in the same conversation
The two most relevant related CVEs are the FortiCloud SSO vulnerabilities Fortinet disclosed in December 2025.
CVE-2025-59718
Fortinet described CVE-2025-59718 as an improper verification of cryptographic signature vulnerability in FortiOS, FortiWeb, FortiProxy, and FortiSwitchManager that could allow an unauthenticated attacker to bypass FortiCloud SSO login authentication via a crafted SAML message if the feature was enabled. Public reporting in early 2026 consistently treated it as part of the immediate lead-up to CVE-2026-24858. (FortiGuard Labs)
CVE-2025-59719
Rapid7 and related reporting describe CVE-2025-59719 as the sibling flaw affecting FortiWeb, while CVE-2025-59718 covered FortiOS, FortiProxy, and FortiSwitchManager. The two flaws were treated as having the same root cause family with different product scope. Their existence matters because they showed that the FortiCloud SSO path was already being stress-tested adversarially before the January 2026 incident. (ラピッド7)
The reason to keep these CVEs in the same article is not historical completeness for its own sake. It is because defenders need a full picture of the attack surface. Looking only at CVE-2026-24858 can make the incident look like a bolt from the blue. Looking at the December pair makes a different pattern visible: a concentrated zone of identity-related weakness around FortiCloud SSO administrative access. That pattern should influence future control reviews, especially around device registration, trust assertions, and management-plane exposure. (FortiGuard Labs)
The engineering lesson, identity trust at the edge is now part of attack surface management
For years, teams thought of firewall hardening as firmware, ACLs, VPN settings, certificates, and management-port exposure. Those controls still matter. But CVE-2026-24858 shows that identity architecture has become inseparable from perimeter hardening. A management plane that accepts cloud SSO assertions is no longer just a box on the network. It is part of a distributed authentication system whose security depends on tenant separation, registration workflows, assertion handling, and control-plane policy. (NVD)
That should change review habits. When a security appliance offers cloud registration and administrative SSO, ask hard questions before enabling it at scale. What exactly turns the feature on. Is it opt-in or operationally auto-enabled during onboarding. Which identity providers are in play. Is the trust scoped to the tenant correctly. Can admin login be constrained by IP, device certificate, or local policy even when cloud SSO is enabled. What telemetry proves the assertion path is behaving normally. CVE-2026-24858 is what happens when those questions are asked too late. (Arctic Wolf)
The incident also reinforces an old truth in a new form: convenience features on security products deserve the same threat modeling rigor as the products’ packet-processing engines. A cloud-linked admin login workflow may look like a usability enhancement. In practice it is a privileged identity bridge. If that bridge fails, the device is no longer a boundary. It becomes a pivot. (NVD)

What a mature response looks like after patching
A mature response to CVE-2026-24858 goes beyond compliance checkboxes.
It starts with confirming the version state and applying fixed builds where necessary. It then verifies whether FortiCloud SSO was enabled historically and whether that state aligned with policy. Next it reviews the full administrative account set, not just known bad names. Then it checks for suspicious SSO logins, unusual management-plane source IPs, configuration export events, new trusted hosts, API administrators, and changes to security policy. If compromise indicators exist, it rotates credentials, restores from known-good configurations, and validates downstream systems that may have been exposed through configuration leakage. Every one of those steps is implied by the public incident record. (フォーティネット)
A mature response also documents why the organization was exposed. Was FortiCloud SSO actually required. Was it enabled by deliberate decision or by onboarding workflow. Did external management access remain broader than necessary. Were there monitoring rules for admin SSO logins before the incident. Those are not academic questions. They decide whether the next identity-plane bug becomes a page in a patch report or a repeat intrusion. (Arctic Wolf)
Final assessment
CVE-2026-24858 deserves attention not merely because it is critical or because it landed in KEV. It deserves attention because it exposed a brittle seam between cloud identity and on-box administrative trust in products that many organizations rely on to secure the rest of the environment. The public record is strong on the key points: it was exploited in the wild, it affected multiple Fortinet products, it required FortiCloud SSO to be enabled, it was observed leading to rogue admin creation and configuration theft, and it required both vendor cloud-side intervention and customer-side patching to contain properly. (NVD)
The most useful way to remember this CVE is not as “that Fortinet zero-day from January.” It is as a warning about trust concentration. When a cloud identity path gains the ability to open administrative doors on perimeter devices, that path becomes one of the most sensitive parts of the environment. If it breaks, everything behind it becomes harder to trust. CVE-2026-24858 is the kind of incident that should push security teams to validate administrative identity flows with the same seriousness they already apply to exposed services and edge code. (NVD)
さらに読む
- NVD entry for CVE-2026-24858 — (NVD)
- Fortinet PSIRT advisory FG-IR-26-060 — (FortiGuard Labs)
- Fortinet incident analysis, Analysis of Single Sign-On Abuse on FortiOS — (フォーティネット)
- CISA Known Exploited Vulnerabilities coverage reflected by NVD and CISA catalog references — (NVD)
- Arctic Wolf, CVE-2026-24858 FortiCloud SSO Authentication Bypass Vulnerability Exploited — (Arctic Wolf)
- SecurityWeek, Fortinet Patches Exploited FortiCloud SSO Authentication Bypass — (セキュリティ・ウィーク)
- Rapid7, updated coverage including CVE-2026-24858 — (ラピッド7)
- Help Net Security, Fortinet starts patching exploited FortiCloud SSO zero-day — (ヘルプ・ネット・セキュリティ)
- The Hacker News coverage on active exploitation and patching — (ハッカーニュース)
- Fortinet advisory context for CVE-2025-59718 and CVE-2025-59719 — (FortiGuard Labs)
- Penligent, CVE 2026 The Vulnerability Landscape: When Identity Breaks and Legacy Code Bites Back — (寡黙)
- Penligent, The Ghost in the Shell: Dissecting CVE-2026-24061 and the Global Crisis of Exposed Telnet Assets — (寡黙)
- Penligent, CVE-2025-64446 PoC:AIセキュリティエンジニアのためのディープダイブ分析 — (寡黙)
- Penligent, What is Penetration Testing? The Engineering of Verified Risk — (寡黙)