When the weakness sits in the directory itself, the blast radius is different. A browser bug may give an attacker code execution on one endpoint. A server bug may give them a foothold on one host. But an identity-layer bug changes how trust is resolved across the environment. That is why CVE-2026-25177 matters more than its short public advisory might suggest. The official public record says this is an improper restriction of names for files and other resources in Active Directory Domain Services that allows an authorized attacker to elevate privileges over a network. Microsoft assigned a CVSS v3.1 score of 8.8 with a vector of AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H, meaning the attack is network-reachable, requires only low privileges, needs no user interaction, and carries high impact across confidentiality, integrity, and availability. (NVD)
That alone is enough to get a Windows and identity team’s attention. This is not a local-only edge case and not a “user clicks something weird” vulnerability. It sits in AD DS, the service that many enterprises still rely on as the trust spine for authentication, Kerberos, service identity, policy application, and authorization inheritance. Microsoft disclosed the CVE on March 10, 2026, and NVD later enriched the record with affected CPEs on March 13, 2026. Zero Day Initiative classified it as an Important 8.8-rated elevation-of-privilege flaw in the March 2026 release, while Rapid7’s Patch Tuesday table listed it as not publicly disclosed and assessed exploitation as “Less Likely” at release time. Those two things can both be true: a vulnerability can be less likely to see immediate mass exploitation and still be one of the most important patches in a real enterprise if it touches identity. (NVD)
That distinction matters because the current public source landscape is uneven. Microsoft’s own advisory text is concise. It confirms the product area, the weakness class, and the severity. It does not, at least in the accessible public text reviewed here, provide a full implementation-level explanation of the exploitation mechanics. In that gap, several third-party writeups have filled in the likely story, most commonly framing the bug around how Active Directory handles security-significant names such as service principal names and user principal names, including possible uniqueness bypass through crafted Unicode or visually confusable values. Those writeups are plausible, and they align with Microsoft’s own long-standing documentation that SPNs and UPNs are security-sensitive attributes with strict uniqueness behavior. But responsible engineering writing should keep the line visible: confirmed public facts on one side, informed operational inference on the other. This article follows that line throughout. (NVD)
What the public record actually confirms
At the highest-confidence level, the record is straightforward. CVE-2026-25177 affects Active Directory Domain Services. The weakness maps to CWE-641, improper restriction of names for files and other resources. The attacker must already be authorized, but only at a low privilege level. The attack is remote over the network. No user interaction is required. All three impact dimensions are high. That is the baseline every defender can rely on without stretching beyond the vendor-backed record. (NVD)
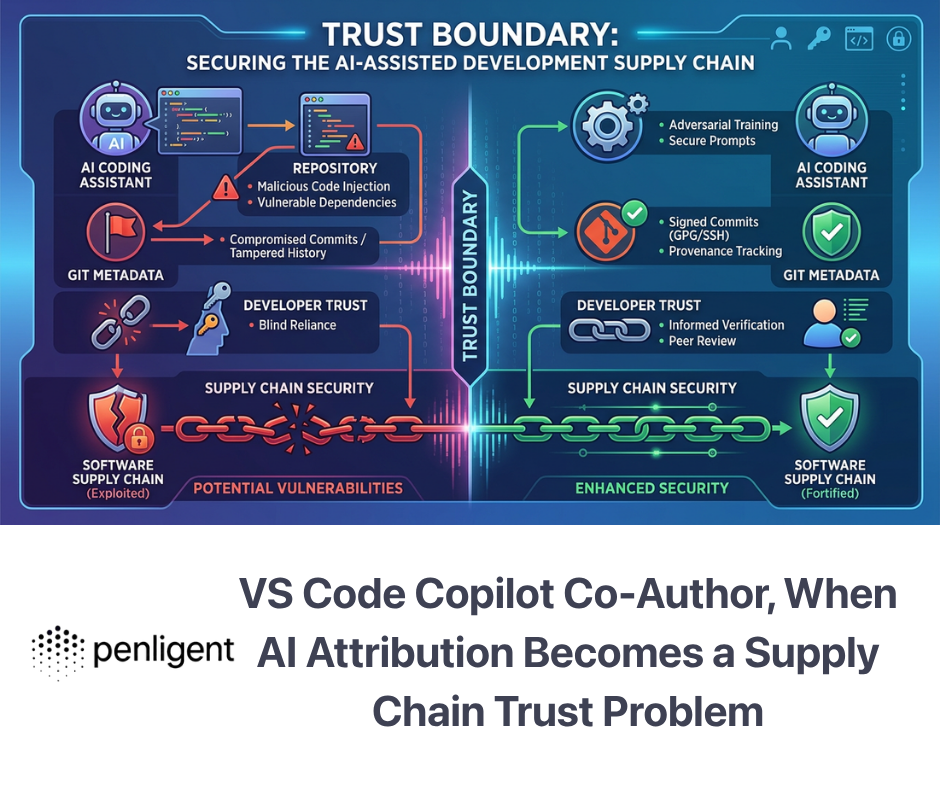
One of the easiest mistakes defenders make with terse Patch Tuesday advisories is to confuse “short description” with “small risk.” In practice, the opposite is often true. The shorter the public description, the more important it becomes to understand the trust boundary around the affected component. In the case of AD DS, the component is not just another Windows subsystem. It is the directory that resolves who users are, what services are named, where tickets are supposed to bind, which principals are allowed to delegate, and which account owns a given identity-like attribute. A weakness here does not need flashy remote code execution to be dangerous. If it lets a low-privileged authenticated identity alter how the directory interprets a name, the environment’s trust model can start bending in ways that are operationally severe even before an attacker “owns” a machine. (NVD)
Rapid7’s March 2026 Patch Tuesday table adds an important piece of context. The issue was not marked publicly disclosed at release and was assessed as exploitation less likely, which is useful for prioritization but should not be overread. It does not mean safe to defer. It means Microsoft’s exploitability model did not place it in the most urgent “likely to be hit immediately at scale” bucket on release day. In a mature identity environment, that is not enough to relax. A low-privilege, network-reachable AD privilege escalation flaw deserves fast patching because identity bugs are often exploited after initial access, not as an internet-wide worm. They become high-value second-stage abuse paths once an attacker lands a normal domain account through phishing, password reuse, token theft, or a web application compromise. (ラピッド7)
Tenable’s March 2026 Patch Tuesday commentary reinforces the broader release context. Their count placed Microsoft’s March 2026 release at 83 CVEs, with eight rated critical and 75 rated important. In other words, CVE-2026-25177 did not stand out because it was the only serious issue that month. It stood out because it belonged to the family of vulnerabilities that touch the core trust fabric of Windows estates. In environments where patch teams must choose what gets emergency attention, identity and authentication-path defects deserve a different weighting than generic workstation issues. (Tenable®)
The table below summarizes the confirmed public baseline without adding speculation.
| フィールド | Publicly confirmed signal |
|---|---|
| CVE | CVE-2026-25177 |
| Product area | Active Directory Domain Services |
| 脆弱性タイプ | 特権の昇格 |
| 弱さ | CWE-641 |
| Disclosure date | March 10, 2026 |
| CVSS v3.1 | 8.8 High |
| 攻撃ベクトル | ネットワーク |
| Privileges required | 低い |
| User interaction | なし |
| Public disclosure at release in Rapid7 summary | いいえ |
| Exploitation status in Rapid7 summary | Less Likely |
| Patch family | Microsoft March 2026 security updates |
This summary is compiled directly from NVD, ZDI, and Rapid7’s March 2026 coverage. (NVD)

Why a naming bug in AD is not an ordinary bug
The key to understanding CVE-2026-25177 is to stop reading the phrase “improper restriction of names for files and other resources” like it came from a desktop application. In a traditional line-of-business app, a naming bug might affect uploads, path parsing, object creation, or authorization checks around user-controlled resource identifiers. In Active Directory, names are part of the identity model itself. They are not decorative labels. A userPrincipalName is a login identity. A servicePrincipalName is how Kerberos associates a service instance with an account. A computer account name or related identity attribute can shape how the directory resolves trust and how the KDC decides what a ticket is for. When a directory service fails to restrict or normalize such names correctly, the problem is not mere inconsistency. The problem is misbinding of identity. (マイクロソフト学習)
Microsoft’s documentation on UPNs is explicit: a UPN must be unique among all security principal objects within a directory forest. Their documentation on SPNs is equally clear: an SPN must be unique in the forest in which it is registered, and if it is not unique, authentication will fail. Microsoft’s deeper support content on SPN and UPN uniqueness also explains that Windows Server 2012 R2 domain controllers block creation of duplicate SPNs and UPNs, and that Event ID 2974 records blocked attempts and shows which objects already contain the duplicate value. Those are not academic details. They are direct evidence that uniqueness and validation around these attributes are fundamental to correct identity resolution in AD. (マイクロソフト学習)
That is why the current public reporting around CVE-2026-25177 keeps circling SPNs, UPNs, and Kerberos. eSecurity Planet’s coverage frames the flaw as tied to how AD DS processes SPNs and UPNs during Kerberos authentication and describes a scenario in which crafted Unicode characters could produce visually similar but logically distinct values that bypass duplicate-prevention logic. Feedly’s CVE summary says something similar, specifically mentioning Unicode character injection that bypasses duplicate-prevention checks in SPNs and UPNs. Microsoft has not publicly confirmed that exact root cause in the sources reviewed here, so those specifics should not be repeated as settled vendor truth. But they are technically coherent with the documented importance of SPN and UPN uniqueness, and they are useful for defenders because they point attention toward the right telemetry and governance surface. (イーセキュリティ・プラネット)
In practical terms, the risk is not that one odd string appears in LDAP. The risk is that AD accepts or misinterprets a security-significant name in a way it should have refused. If that happens, several outcomes become possible even without a public exploit whitepaper: a service identity might resolve to the wrong principal, a ticket request might be associated with the wrong object, a duplicate-like value might introduce authentication confusion, or a low-privileged user might be able to move from ordinary membership in the domain to a materially more trusted position. When defenders say identity vulnerabilities are “different,” this is what they mean. The trust error is not downstream from authentication. It is embedded in the naming and resolution layer that authentication depends on. (NVD)
Another reason this class of bug matters is that naming errors in AD often create ambiguous blast radius. A broken web route usually affects one application. A broken SPN, UPN, or security principal mapping can affect service tickets, logon behavior, synchronization, service account trust, and even incident response visibility. Microsoft’s support article notes that duplicate SPNs commonly result in authentication failures and may lead to excessive LSASS CPU utilization, while duplicate UPNs can break synchronization with Microsoft cloud identity services. That means even failed or partial exploitation attempts can create noisy operational symptoms that look like “authentication weirdness” rather than obvious attack activity. For defenders, that is a warning sign: a bug of this class can degrade identity correctness before it produces a clean privilege escalation artifact. (マイクロソフト学習)
What current public reporting suggests, and what remains uncertain
The most defensible way to discuss exploitation right now is to separate confirmed mechanics from likely mechanics. Confirmed mechanics are simple: the attacker is already authenticated, needs only low privileges, reaches the target over the network, and exploits an AD DS name-restriction weakness to gain elevated privileges. That is enough to justify urgent patching. The likely mechanics, based on current public reporting and Microsoft documentation about directory uniqueness constraints, are that the attacker abuses a security-significant naming edge case involving SPN or UPN handling to create confusion or bypass around uniqueness enforcement. (NVD)
eSecurity Planet’s article adds one plausible attack narrative: if a malicious duplicate SPN can be created, the attacker may be able to trigger Kerberos authentication requests that cause the directory to associate a service ticket with the wrong key or wrong service binding, producing failed decryption by the legitimate service and potentially pushing authentication down undesirable paths, including NTLM fallback where it still exists. Again, that is third-party reporting, not official root-cause documentation. But it is operationally useful because it tells blue teams what symptoms to watch for after patching windows open or suspicious directory writes occur: odd Kerberos failures, unexpected authentication fallbacks, service disruptions around previously stable SPN-bound workloads, and attribute modifications touching servicePrincipalName or userPrincipalName. (イーセキュリティ・プラネット)
Feedly’s summary is more explicit still, describing Unicode character injection in SPNs and UPNs that bypasses duplicate-prevention checks. That should be treated carefully. Feedly is a useful aggregation lens, not the primary vendor source. Still, defenders do not need Microsoft to publish every branch of the code path to use the defensive implications. If current reporting repeatedly points to Unicode-like manipulation, then it becomes rational to hunt for mixed-script values, suspiciously confusable names, or recent principal values containing unexpected non-ASCII characters. If the exact primitive later turns out to be narrower, the hunting effort was still low-regret because it focused on the identity attributes most likely to matter. (フィードリー)
This is also where many current articles become too absolute. Some headlines talk about SYSTEM privilege escalation or imply straightforward domain takeover. That may prove directionally true in some environments, especially if write permissions, service account hygiene, delegation settings, and fallback protocols create favorable conditions. But the cleanest reading of the official record is still “privilege escalation over a network,” not a vendor-confirmed promise of universal domain takeover. Good engineering writing should resist the urge to oversell. The operational truth is strong enough already: if an ordinary authenticated principal can distort AD’s interpretation of a security-significant name, the downstream consequence can be serious enough to justify immediate response even before the public has a weaponized exploit chain. (NVD)
A realistic attack model, stated carefully, looks like this. An attacker lands ordinary domain credentials. They enumerate where they have direct or indirect write access to directory objects or identity-relevant attributes. They try to introduce a new value or modify an existing value in a naming-sensitive field that shapes identity or service resolution. AD DS accepts the change or fails to interpret it as conflicting with a protected or existing value. Subsequent authentication or resolution behavior binds to the wrong object or fails open in a way the attacker can steer. The attacker then leverages the new trust position to gain materially higher rights than their original account should have had. That is not a PoC. It is the most defensible abstraction of what the confirmed facts imply. (NVD)
There is also an important permissions nuance here. Microsoft’s setspn documentation notes that not every user can modify servicePrincipalName on arbitrary objects; rights depend on access control and can be delegated through the “Validated write to service principal name” permission. That means exploitation feasibility is likely shaped by the directory’s existing delegated administration model. In a tightly governed environment with narrow write rights and disciplined service account provisioning, the attacker’s path may be harder. In a large, old, or hybrid environment where app teams, scripts, installers, service owners, or automation principals have broad write scope, the path may be much easier. This is one reason identity flaws often behave differently in the field than in vendor scoring models. The score sees PR:L. Real environments decide how much power “low privilege” quietly accumulated over a decade of delegation. (マイクロソフト学習)

Affected versions and patch boundary
The NVD change record shows that this is not limited to one obscure Windows branch. The affected configuration list includes Windows Server 2012 and Windows Server 2012 R2, Windows Server 2016, Windows Server 2019, Windows Server 2022, Windows Server version 23H2, Windows Server 2025, and multiple Windows 10 and Windows 11 client families. For several branches, the change record also exposes the patched build boundary. Windows Server 2016 is listed as vulnerable up to but excluding 10.0.14393.8957. Windows Server 2019 and Windows 10 1809 are listed up to but excluding 10.0.17763.8511. Windows Server 2022 is listed up to but excluding 10.0.20348.4830. Windows Server 2022 23H2 is listed up to but excluding 10.0.25398.2207. Windows Server 2025 is listed up to but excluding 10.0.26100.32463. On the client side, Windows 10 21H2 is listed up to but excluding 10.0.19044.7058, Windows 10 22H2 up to but excluding 10.0.19045.7058, Windows 11 23H2 up to but excluding 10.0.22631.6783, Windows 11 24H2 up to but excluding 10.0.26100.7979, Windows 11 25H2 up to but excluding 10.0.26200.7979, and Windows 11 26H1 up to but excluding 10.0.28000.1719. (NVD)
That list tells a larger story. This is not a legacy-only defect. It spans both old and current Windows branches and hits the administrative reality most enterprises actually live in: mixed fleets, staggered patching, long-lived domain controllers, management workstations, and identity-adjacent hosts that do not all move in sync. Even if AD DS itself is primarily a server concern, the broader CPE coverage underscores a familiar truth about identity security: governance, tooling, and delegated directory writes often live far beyond the domain controller itself. It is unwise to treat this as “just patch the DCs someday.” The DCs are first. They are not the only systems whose patch and governance state matters. (NVD)
The March 2026 update ecosystem gives additional anchor points for verification. Microsoft’s support pages identify KB5078775 for Windows Server 2012 and KB5078774 for Windows Server 2012 R2 in the March 10, 2026 release. Microsoft’s KB5078752 page maps Windows Server 2019 and Windows 10 version 1809 to OS Build 17763.8511, which aligns with the NVD patched build boundary. Microsoft’s KB5078883 page maps Windows 11 23H2 to OS Build 22631.6783, again lining up with NVD’s version ceiling. Tenable’s plugins page also maps the March 2026 security updates to platform-specific KBs, including Windows Server 2012, Windows Server 2012 R2, Windows Server 2019, Windows 10 21H2 and 22H2, Windows 11 23H2, Windows 11 24H2 and 25H2, Windows 11 26H1, Windows Server version 23H2, and Windows Server 2025. (Microsoft Support)
There is one practical wrinkle worth calling out for older server lines. Microsoft’s Windows Server 2012 R2 March 2026 KB page reiterates that the platform reached end of support in 2023 and continues to receive updates through Extended Security Updates until October 13, 2026. That matters because some organizations still run AD roles on older branches and assume “patched enough” when the estate is actually outside mainstream support. For those environments, the vulnerability conversation becomes both a patching issue and a lifecycle issue. If an identity platform is still hanging on a near-end ESU track, the right conversation is not only “install this month’s rollup.” It is also “how much longer are we willing to run the trust spine of the organization on software in extended support?” (Microsoft Support)
A concise patch-boundary planning view looks like this.
| Platform family | Public patch indicator |
|---|---|
| Windows Server 2012 | March 2026 monthly rollup KB5078775 |
| Windows Server 2012 R2 | March 2026 monthly rollup KB5078774, ESU track |
| Windows Server 2016 | Patched at 10.0.14393.8957 or later |
| Windows Server 2019 and Windows 10 1809 | Patched at 10.0.17763.8511 or later, KB5078752 |
| Windows 10 21H2 | Patched at 10.0.19044.7058 or later |
| Windows 10 22H2 | Patched at 10.0.19045.7058 or later |
| Windows 11 23H2 | Patched at 10.0.22631.6783 or later, KB5078883 |
| Windows 11 24H2 | Patched at 10.0.26100.7979 or later |
| Windows 11 25H2 | Patched at 10.0.26200.7979 or later |
| Windows 11 26H1 | Patched at 10.0.28000.1719 or later |
| ウィンドウズ・サーバー2022 | Patched at 10.0.20348.4830 or later |
| Windows Server version 23H2 | Patched at 10.0.25398.2207 or later |
| Windows Server 2025 | Patched at 10.0.26100.32463 or later |
This table is condensed from the NVD change record and Microsoft and Tenable update references. (NVD)
What the impact looks like in a real Windows estate
The cleanest way to think about impact is in three layers. The first layer is direct privilege escalation. That is the part the official advisory confirms. An authenticated user with low privileges can escalate to something more powerful over the network. In an identity system, that alone is severe because the starting point is so common. Attackers do not need domain admin to begin abuse. They need one valid identity. Phishing, password spraying against neglected MFA gaps, session theft, credential reuse from a web bug, or compromise of a low-tier internal host can all supply that starting position. If the next step is an AD DS flaw that helps convert “any domain user” into a more trusted security principal, the delta in attacker capability is much larger than the CVSS string alone conveys. (NVD)
The second layer is authentication confusion and service instability. Microsoft’s documentation on SPN uniqueness is explicit that duplicate SPNs can result in authentication failures. Their support content on SPN and UPN uniqueness says the same and ties duplicate values to operational breakage and even LSASS load issues. If current reporting around CVE-2026-25177 is directionally correct about uniqueness bypass or name confusion, then organizations should think not only about malicious privilege gain but also about symptoms that will present as Kerberos noise, intermittent service failures, or hard-to-explain access problems. Defenders sometimes miss identity exploitation because the first thing the service owner sees is “the app is failing to authenticate,” not “we are under attack.” (マイクロソフト学習)
The third layer is what happens when identity confusion intersects with broader environmental weaknesses. If NTLM fallback still exists for important services, if service accounts have overly broad rights, if constrained delegation boundaries are poorly understood, if app installers or automation can write SPNs more broadly than intended, or if hybrid synchronization obscures recent attribute changes, then the privilege-escalation path becomes easier to operationalize. None of those conditions are required by the CVE text itself. They are risk amplifiers. And real breaches are built out of amplifiers more often than out of one perfect vulnerability. That is why a vulnerability like CVE-2026-25177 is best treated as an identity multiplier. It turns already-existing administrative looseness into a much more dangerous problem. (マイクロソフト学習)
This is also why identity flaws have a habit of surviving prioritization meetings. Security teams see “no public exploit,” “less likely,” and “not a critical 9.8 RCE,” then slide the patch behind something noisier. But identity defects are not competing in the same category as consumer-facing browser bugs. They sit closer to the heart of the enterprise. A one-host bug hurts one host. A naming-boundary error in AD can alter how the environment decides who a service is, which account a ticket belongs to, or whether a user identity resolves uniquely. That is the sort of problem attackers love after initial access because it lets them move from local success to trust-level advantage. (ラピッド7)
Detection and hunting, what to look for before and after patching
The best detection strategy for CVE-2026-25177 is not to hunt for the CVE string. It is to instrument the directory surfaces the vulnerability is most likely to touch. Microsoft’s documentation gives defenders a solid starting point. Event ID 5136 is generated every time an Active Directory object is modified, assuming the appropriate SACL is present. Event ID 4738 is generated every time a user object is changed. Event ID 4742 is generated every time a computer object is changed, and only on domain controllers. Microsoft’s SPN and UPN uniqueness guidance also highlights Event ID 2974 as the event that records blocked duplicate UPN or SPN attempts and shows the value and one or more objects that already contain it. Together, those events describe the most important hunting surface for this vulnerability class: directory changes to security-significant attributes. (マイクロソフト学習)
That matters even if the exact exploit primitive turns out not to be Unicode-based. The attack still has to manifest somewhere useful to the attacker. In a directory service, that usually means object creation, modification, rename behavior, or attribute writes on accounts and services that influence authentication. If your monitoring does not have visibility into directory changes, you are blind at the layer the vulnerability most likely touches. That is true whether the attacker abuses SPNs, UPNs, computer accounts, or another identity-like resource name inside AD DS. (NVD)
A practical detection program should do four things immediately. First, inventory all domain controllers and confirm patch state rather than assuming it from ticket closures. Second, identify the objects and accounts in your estate where SPN or UPN changes are normal, because those will need tighter review during the patch window. Third, enable or confirm directory change auditing where it is missing, especially on tier-zero systems. Fourth, run targeted hunts for recent changes to servicePrincipalName, userPrincipalName, and related identity attributes around the disclosure and patch period. Those steps are valuable even if you have no evidence of compromise, because they shrink the time between suspicious identity activity and human review. (NVD)
A straightforward PowerShell inventory pass can start with the systems that matter most:
Get-ADDomainController -Filter * |
Select-Object HostName, Site, OperatingSystem, OperatingSystemVersion
Get-HotFix |
Where-Object {$_.InstalledOn -ge (Get-Date).AddDays(-45)} |
Sort-Object InstalledOn -Descending |
Select-Object HotFixID, InstalledOn, Description
This does not prove exposure or remediation by itself, but it gives you two things you need before hunting can mean anything: which hosts are domain controllers, and whether they actually received relevant March 2026 updates recently. The logic is simple because good incident-response triage usually is. Start with the trust spine, not the whole forest. The exact KBs you expect will vary by OS branch, but the inventory process should be identical. (NVD)
Next, pull visibility on the identity-bearing objects most likely to matter:
Get-ADUser -LDAPFilter "(servicePrincipalName=*)" `
-Properties servicePrincipalName,userPrincipalName,whenChanged |
Select-Object SamAccountName, UserPrincipalName, whenChanged, ServicePrincipalName
Get-ADComputer -LDAPFilter "(servicePrincipalName=*)" `
-Properties servicePrincipalName,whenChanged |
Select-Object Name, whenChanged, ServicePrincipalName
Get-ADObject -LDAPFilter "(|(servicePrincipalName=*)(userPrincipalName=*))" `
-Properties servicePrincipalName,userPrincipalName,whenChanged,whenCreated |
Sort-Object whenChanged -Descending |
Select-Object Name, ObjectClass, whenCreated, whenChanged, userPrincipalName, servicePrincipalName -First 200
These commands are not exploit detectors. They are triage accelerators. They tell you where SPN-bearing and UPN-bearing objects live, which ones changed recently, and where security teams should concentrate review first. In large estates, the key is not perfect coverage in one pass. It is getting from “we have thousands of principals” to “here are the hundred identity objects we most want to examine this week.” The vulnerability is identity-centric, so your hunting should be too. (マイクロソフト学習)
Because current reporting suggests possible confusable or mixed-script naming tricks, it is reasonable to run a heuristic search for values that look unusual rather than waiting for a known signature:
Get-ADObject -LDAPFilter "(|(servicePrincipalName=*)(userPrincipalName=*))" `
-Properties servicePrincipalName,userPrincipalName |
ForEach-Object {
$spns = @($_.servicePrincipalName)
$upn = $_.userPrincipalName
foreach ($spn in $spns) {
if ($spn -match '[^\\u0000-\\u007F]') {
[PSCustomObject]@{
Name = $_.Name
Type = $_.ObjectClass
Field = 'servicePrincipalName'
Value = $spn
}
}
}
if ($upn -and $upn -match '[^\\u0000-\\u007F]') {
[PSCustomObject]@{
Name = $_.Name
Type = $_.ObjectClass
Field = 'userPrincipalName'
Value = $upn
}
}
}
That query is intentionally conservative and will produce false positives in multilingual environments. But false positives are acceptable at this stage. The goal is not to accuse every non-ASCII value of being malicious. The goal is to surface a review set containing the exact class of data that current public reporting says might be relevant. In many environments, the mere discovery of unexpected non-ASCII or visually confusable values in highly privileged service identities is enough to justify closer scrutiny. (フィードリー)
For SIEM hunting, Event ID 5136 is the most directly useful because it records directory object modifications at the attribute level when properly audited. A KQL starting point might look like this:
SecurityEvent
| where EventID == 5136
| where AttributeLDAPDisplayName in ("servicePrincipalName", "userPrincipalName", "sAMAccountName")
| project TimeGenerated, Computer, SubjectUserName, ObjectClass, ObjectDN,
AttributeLDAPDisplayName, OperationType, OldValue, NewValue
| order by TimeGenerated desc
This query deliberately stays close to the identity problem instead of expanding into generic anomaly hunting. If current public reporting is directionally right, the attacker needs to alter how AD interprets some security-relevant name. That means attribute-level changes to the naming layer are higher value than a dashboard full of unrelated authentication noise. (マイクロソフト学習)
A broader KQL version that correlates user, computer, and directory-object changes can give better context:
SecurityEvent
| where EventID in (5136, 4738, 4742)
| summarize FirstSeen=min(TimeGenerated), LastSeen=max(TimeGenerated), Count=count()
by EventID, Computer, SubjectUserName, TargetUserName, AttributeLDAPDisplayName, tostring(NewValue), tostring(OldValue)
| order by Count desc
Event 4738 and 4742 matter because not every relevant change will surface in the same way across tools, pipelines, or auditing configurations. Microsoft’s own event documentation makes clear that 4738 is generated when a user object changes and 4742 when a computer account changes. In an identity-focused investigation, defenders should want both the object-level change view and the attribute-level change view, because attackers do not always choose the path your telemetry pipeline prefers. (マイクロソフト学習)
A simple Splunk equivalent can stay narrow:
index=wineventlog (EventCode=5136 OR EventCode=4738 OR EventCode=4742)
("servicePrincipalName" OR "userPrincipalName" OR "sAMAccountName")
| stats count min(_time) as firstTime max(_time) as lastTime
by host, EventCode, SubjectUserName, TargetUserName, AttributeLDAPDisplayName, NewValue, OldValue
| sort - count
When teams write Splunk or KQL queries for identity vulnerabilities, they often overcomplicate the first pass. That is usually a mistake. Start with the names that matter, the events that record them, and the users or hosts making the changes. Once you have the suspicious cluster, enrich from there with ticketing logs, Kerberos failures, service outages, or identity governance context. (マイクロソフト学習)
A Sigma-style rule can help security teams standardize a first layer of alerting:
title: Suspicious AD Naming Attribute Change
id: 0d4c2915-c74e-4d4e-9d92-cve202625177-ad-name-change
status: experimental
logsource:
product: windows
service: security
detection:
selection:
EventID:
- 5136
- 4738
- 4742
attrs:
AttributeLDAPDisplayName|contains:
- servicePrincipalName
- userPrincipalName
- sAMAccountName
condition: selection and attrs
level: high
description: Detects changes to identity-sensitive AD naming attributes that may warrant review in the context of CVE-2026-25177 or related identity abuse.
This rule is intentionally generic. It is not a silver bullet for CVE-2026-25177. It is a normalization step for an attack surface. The real value comes from adding environment-specific suppression and enrichment after the first week of review. In a disciplined enterprise, changes to servicePrincipalName and userPrincipalName should already be rare enough that a simple rule has a good signal-to-noise starting point. (マイクロソフト学習)
Event ID 2974 deserves special attention. Microsoft’s SPN and UPN uniqueness guidance says the event lists the value that was blocked and one or more objects that already contain the duplicate value. That makes it unusually useful during remediation because it can reveal both attempted duplication and preexisting hygiene issues. If your domain controllers generate 2974 events during the weeks around this patch cycle, do not treat them as harmless administrative friction. They are evidence that the exact class of identity-sensitive naming conflict Microsoft designed the platform to block is active in your environment. Even if none of those events are malicious, they tell you where your directory is already fragile. (マイクロソフト学習)
Remediation and hardening, what mature teams should actually do
The first remediation step is still patching, and there is no reason to pretend otherwise. Domain controllers and other systems carrying directory-adjacent administrative roles should be first-wave targets for the March 2026 update cycle. Verify the resulting build or KB state. Do not treat deployment tickets, maintenance completion, or SCCM compliance dashboards as proof that the relevant branch has crossed the version boundary. Identity vulnerabilities are exactly where false confidence accumulates because everyone assumes the DCs must already be well managed. The right question is not “was the patch approved?” It is “which exact build is the domain controller on right now?” (NVD)
The second step is to review delegated write permissions around identity-sensitive attributes. Microsoft’s setspn documentation reminds defenders that rights to access or modify SPN properties depend on access control and can be delegated via “Validated write to service principal name.” In mature environments, that right is more widely distributed than many teams think. Application teams, deployment services, migration tooling, installers, join scripts, and service provisioning workflows may all have direct or indirect ability to manipulate SPNs or related objects. CVE-2026-25177 is a reminder that the definition of “low privilege” in AD is not just group membership. It is the total capability footprint hidden inside delegated write paths. (マイクロソフト学習)
That review should include service accounts, computer object delegation, self-service provisioning workflows, and any automation principal that writes to AD as part of application deployment or hybrid synchronization. In many environments, a security team will discover that the patch is easy but the real long-term risk sits in old delegation decisions nobody has revisited in years. If your environment allows broad attribute changes because “the app team needed it once,” then the patch addresses the immediate defect while leaving a weak trust boundary intact for the next identity bug. (マイクロソフト学習)
The third step is to make uniqueness and naming hygiene part of regular directory operations instead of treating them as emergency-only concerns. Microsoft’s own SPN and UPN uniqueness guidance already gives two strong operational clues: duplicate SPNs lead to authentication failures and duplicate UPNs break synchronization. In other words, even without active abuse, poor identity hygiene costs reliability. Teams that regularly review duplicate-like values, recent SPN additions, new alternate UPN suffixes, and unusual cross-domain naming patterns will be much better positioned when the next naming or identity resolution vulnerability lands. The security win and the operations win are aligned here. Cleaner identity data is not just safer. It is easier to keep running. (マイクロソフト学習)
The fourth step is to reduce fallback and adjacent-path risk. Current public reporting suggests that broken or confused Kerberos flows may push attention toward fallback behavior, especially where NTLM remains available. This is not a claim that CVE-2026-25177 automatically produces NTLM abuse. It is a reminder that authentication failures in mixed environments rarely stay isolated. If your environment still tolerates legacy fallback, has inconsistent SMB signing posture, or lets service authentication drift into whatever still works, then every identity defect becomes more dangerous. Good remediation therefore includes asking where Kerberos failure becomes authentication downgrade, and whether those downgrade paths are still acceptable. (イーセキュリティ・プラネット)
The fifth step is to harden monitoring permanently, not only for the patch week. Teams often crank up auditing during a scare and then turn it down once the change window closes. That is understandable but short-sighted. Identity abuse rarely announces itself during the same 24 hours the CVE goes public. Attackers exploit the lag between disclosure, patch rollout, and governance follow-through. Microsoft’s documentation on Event 5136, 4738, 4742, and 2974 makes clear that the telemetry surface already exists. The harder part is operational discipline: keeping the logs, forwarding them centrally, preserving enough history to investigate slow-burn abuse, and ensuring someone actually reviews the attribute changes that matter. (マイクロソフト学習)
A sensible hardening sequence for large estates looks like this. Patch all DCs and verify builds. Review who can write SPNs, UPNs, or adjacent account attributes. Enable or confirm directory-object change auditing on tier-zero systems. Hunt recent changes to servicePrincipalName, userPrincipalName, and sAMAccountName. Review Event 2974 on all writable DCs. Search for nonstandard or mixed-script values in identity-critical attributes. Confirm service owners know how to report authentication anomalies that may actually be security signals. Then fold the whole workflow into monthly identity hygiene reviews instead of treating it as one-off emergency work. That is the difference between patching a CVE and learning from it. (マイクロソフト学習)
Related CVEs that explain why this pattern keeps coming back
The most useful way to understand CVE-2026-25177 is not to compare it with generic Windows privilege-escalation bugs. Compare it with earlier identity flaws that turned small trust assumptions into much larger consequences. CVE-2021-42278 is the obvious starting point. Microsoft’s support guidance describes it as an Active Directory Security Accounts Manager hardening issue that allowed attackers to impersonate a domain controller using computer account sAMAccountName spoofing. That alone should sound familiar. The structural lesson is the same: identity metadata that looks like a naming or validation detail can sit directly on the path to privilege escalation. (Microsoft Support)
CVE-2021-42287 makes the point even more sharply. Microsoft says it affected the Kerberos Privilege Attribute Certificate and allowed attackers to impersonate domain controllers by causing the KDC to create a service ticket with a higher privilege level than that of the compromised account. The official mitigation path required patching all domain controllers and moving into enforcement mode over time. In other words, Microsoft treated it not as an optional oddity but as a trust-boundary correction that needed staged, whole-domain rollout. That history matters because it shows how Microsoft itself responds when identity resolution and ticketing assumptions are wrong. (Microsoft Support)
The famous combination of CVE-2021-42278 and CVE-2021-42287 became well known because it showed how a low-privileged domain user could, under default conditions, leverage naming and ticketing behavior to impersonate highly trusted identities. Fortinet summarized the pair with the striking phrase “from user to domain admin in less than 60 seconds.” The specific exploit path is not the point here. The point is the family resemblance. These were not remote buffer overflows on internet-facing appliances. They were identity logic defects where the system could be persuaded to believe the wrong thing about who an account was or what it should be treated as. That is the same broad neighborhood in which CVE-2026-25177 lives. (フォーティネット)
CVE-2022-26923 offers another strong comparison. NVD marks it as an Active Directory Domain Services privilege-escalation issue and explicitly notes that it is in CISA’s Known Exploited Vulnerabilities Catalog. IBM’s X-Force later documented incident response work in which attackers exploited CVE-2022-26923 to elevate privileges to domain administrator through Active Directory Certificate Services and then attempted DCSync. What makes that relevant here is not that AD CS and AD DS are identical. It is that another “small” identity control point became the route to domain-level trust. Certificate issuance logic, like name validation and service identity binding, is just another part of the enterprise’s trust plane. When it fails, the result is far bigger than the bug title suggests. (NVD)
March 2026 itself also contains neighboring signals. CVE-2026-24297 is a Windows Kerberos security feature bypass caused by a race condition, according to the public CVE record. CVE-2026-25171 is a Windows Authentication elevation-of-privilege vulnerability caused by use-after-free, according to the public CVE and CVE Details records. These are not the same weakness class as CVE-2026-25177, and they should not be conflated. But they reinforce the same operational truth: identity, Kerberos, and authentication code paths remain one of the most dangerous places to be wrong in Windows environments. When multiple vulnerabilities in a single month land in or near the authentication plane, defenders should read that as a signal about priority, not coincidence. (CVE)
The comparison table below is useful because it shows the pattern more clearly than prose can.
| CVE | Identity surface | Publicly relevant lesson |
|---|---|---|
| CVE-2021-42278 | AD SAM account naming and validation | Naming semantics can let attackers impersonate highly trusted identities |
| CVE-2021-42287 | Kerberos PAC and KDC ticket handling | Ticketing logic can magnify a low-privilege foothold into domain-level trust |
| CVE-2022-26923 | AD DS and AD CS certificate trust | Identity enrollment controls can turn ordinary access into domain admin |
| CVE-2026-24297 | Windows Kerberos | Authentication race conditions still matter in the core trust plane |
| CVE-2026-25171 | Windows Authentication Methods | Authentication-path memory safety flaws remain a privilege boundary risk |
| CVE-2026-25177 | AD DS naming and resource restriction | Security-significant name handling inside AD can create network-reachable privilege escalation |
This comparison is synthesized from Microsoft support, NVD, IBM X-Force, CVE.org, and March 2026 Patch Tuesday coverage. (Microsoft Support)
The deeper lesson across all of them is simple. Identity compromise does not always arrive through stolen hashes or direct code execution on a domain controller. Sometimes it arrives because the directory, the KDC, or the certificate service can be tricked into assigning trust incorrectly. Security teams that still model Active Directory defense mainly as “protect the admin accounts and monitor DCSync” are only seeing the end of the story. The beginning is usually much quieter. It lives in account creation rules, naming semantics, service identity, certificate enrollment, and all the other places where the system decides what a principal is allowed to mean. CVE-2026-25177 belongs to that beginning. (Microsoft Support)
What continuous validation should look like after the patch
Patching closes the published vulnerability. It does not answer the more important question: what in your environment would have made this bug easy to exploit in the first place. That question is where mature security programs separate themselves. After the March 2026 updates are applied, teams should validate the surrounding assumptions. Can low-tier automation principals write servicePrincipalName on more accounts than anyone remembers. Are there service accounts with sprawling delegation. Are there hybrid workflows that rewrite UPNs or sync identity data in ways the security team does not continuously review. Are there web apps, management consoles, or enrollment endpoints that let an ordinary user pivot toward identity-sensitive control points. Those are not hypothetical governance questions. They are how low-privileged abuse becomes identity compromise. (マイクロソフト学習)
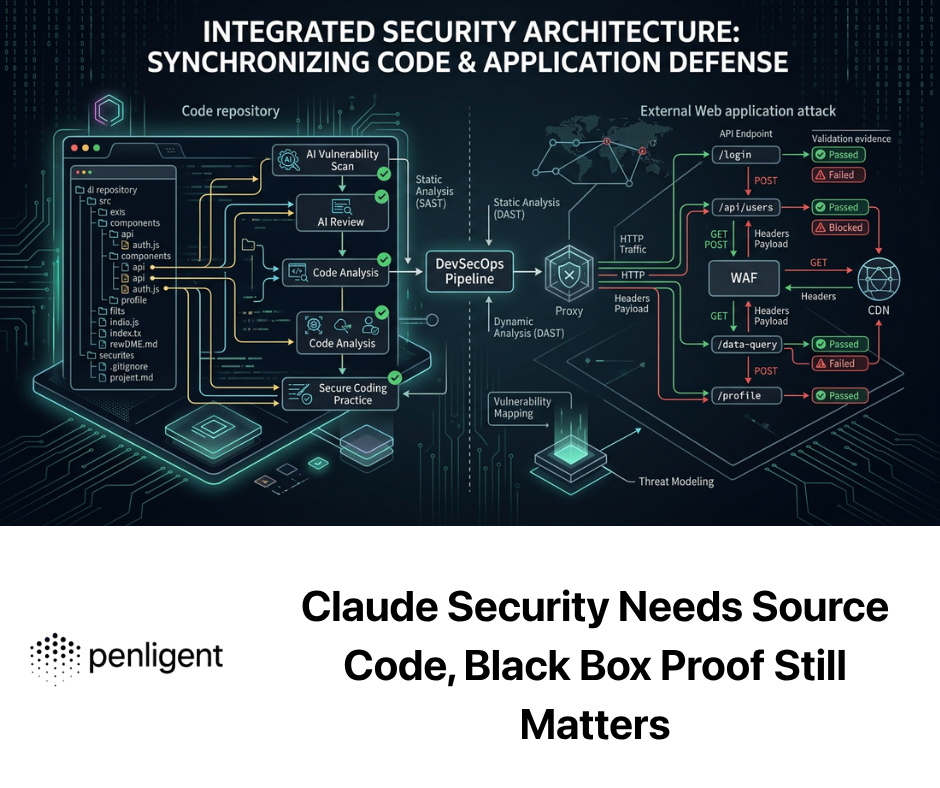
This is where automated validation becomes useful, but only if it is used honestly. A platform like Penligent is most relevant here not as a magic “exploit this AD bug for me” button, but as a way to continuously test the adjacent attack surface that supplies the authenticated foothold or the delegated pathway. Web applications, internal portals, provisioning flows, admin front ends, exposed APIs, and weak automation paths often provide the first low-privilege or mid-privilege position an attacker needs before an identity bug becomes valuable. In other words, CVE-2026-25177 is an AD problem, but the route into an exploitable state often begins outside AD. That is exactly why attack-path-oriented validation matters. (NVD)
There is also a second, more direct use case. Good security validation platforms help teams operationalize retesting. Once the March 2026 patches are deployed, defenders should not stop at “host reports compliant.” They should keep pressure on identity-adjacent services and delegated workflows, verify that dangerous low-privilege paths are not quietly reintroduced through change, and treat identity as part of the continuous exposure surface rather than as a separate administrative silo. The organizations that suffer the most from AD bugs are often not the ones that never patched. They are the ones that patched once and then resumed living with overbroad trust. (NVD)
Final assessment
CVE-2026-25177 deserves attention because it combines several risk multipliers in one place. It is in Active Directory Domain Services. It is network-reachable. It requires only low privileges. It needs no user interaction. It lands in a weakness class that is unusually dangerous inside identity infrastructure because names in AD are not cosmetic strings; they are part of how the environment resolves trust. Microsoft’s public description is short, and that leaves room for overstatement. But it does not reduce the seriousness of the problem. If anything, it should make defenders more disciplined: patch the systems that matter, verify the build boundaries, review who can write identity-sensitive attributes, watch Event ID 2974 and directory-object modifications, and treat unusual SPN or UPN changes as security-relevant until proven otherwise. (NVD)
The larger reason this CVE matters is that it fits a pattern Microsoft defenders should know by now. AD does not only break when attackers steal credentials. It also breaks when the system can be convinced to misname, misbind, misissue, or mistrust. CVE-2021-42278, CVE-2021-42287, and CVE-2022-26923 already showed what happens when small identity assumptions fail. CVE-2026-25177 is the 2026 reminder that the shortest path to major enterprise compromise still often runs through the identity layer. Security teams that patch this quickly and use it to clean up naming governance, delegated writes, and directory monitoring will get more than a closed ticket. They will get a healthier trust boundary. (Microsoft Support)
Related reading and internal links
- NVD entry for CVE-2026-25177 (NVD)
- Microsoft Learn, SPN and UPN uniqueness (マイクロソフト学習)
- Microsoft Learn, user naming attributes and UPN uniqueness (マイクロソフト学習)
- Microsoft Learn, SPN uniqueness and setspn guidance (マイクロソフト学習)
- Rapid7, Patch Tuesday March 2026 summary for CVE-2026-25177 (ラピッド7)
- Zero Day Initiative, March 2026 Security Update Review (Zero Day Initiative)
- Microsoft support guidance for CVE-2021-42278 and CVE-2021-42287 (Microsoft Support)
- NVD and IBM X-Force background for CVE-2022-26923 (NVD)
- Penligent, CVE-2026-25177 — Why This Active Directory Flaw Deserves Immediate Attention (寡黙)
- Penligent, CVE-2026-21262 — The SQL Server Privilege Escalation Flaw That Turns Small Access Into Full Database Control (寡黙)
- Penligent, CVE-2026-21262 — Why This SQL Server Privilege Escalation Flaw Deserves More Attention Than the Average Patch Tuesday Item (寡黙)
- Penligent, AI Pentest Tool — What Real Automated Offense Looks Like in 2026 (寡黙)
- Penligent, Authentication Token Manipulation Error — Technical Analysis and Security Fix Guide (寡黙)