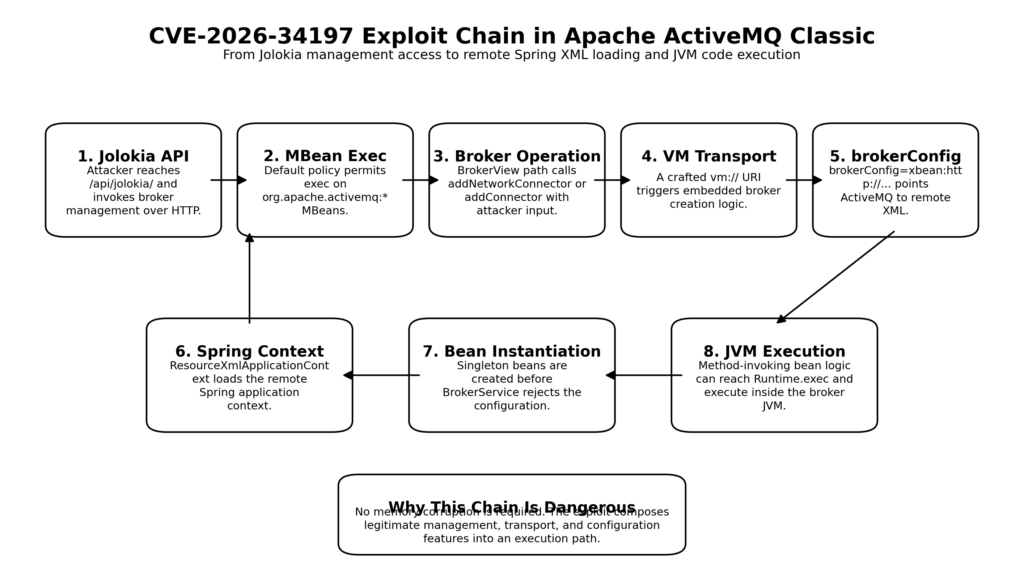
Apache ActiveMQ has had serious security problems before, but CVE-2026-34197 stands out for a different reason. It is not a simple command injection hidden behind one careless call site. It is a composed exploit chain that starts at a management endpoint, crosses a permissive JMX policy boundary, abuses a runtime broker operation, pivots into an embedded transport feature, and ends inside Spring’s XML application context semantics. Apache’s advisory describes the path plainly: ActiveMQ Classic exposes Jolokia at /api/jolokia/, permits エグゼック operations on ActiveMQ MBeans by default, and can be driven through addNetworkConnector(String) または addConnector(String) into loading a remote Spring XML configuration via brokerConfig, which then executes code in the broker JVM before the broker validates the configuration. (ActiveMQ)
That makes this a useful case study for two different audiences at once. For ActiveMQ operators, it is an immediate patching and detection problem. For security researchers, it is a clean example of how dangerous behavior often appears not in one feature but in the seam between several features that were designed in isolation. And for anyone trying to understand the current state of AI-assisted vulnerability research, it is one of the clearest public examples so far of where models are already strong and where they still need human verification, boundary-setting, and judgment. Horizon3’s disclosure is explicit on that point: the researcher says this bug was “80% Claude with 20% gift-wrapping by a human,” and says the model stitched together a path that likely would have taken much longer to find manually. (Horizon3.ai)
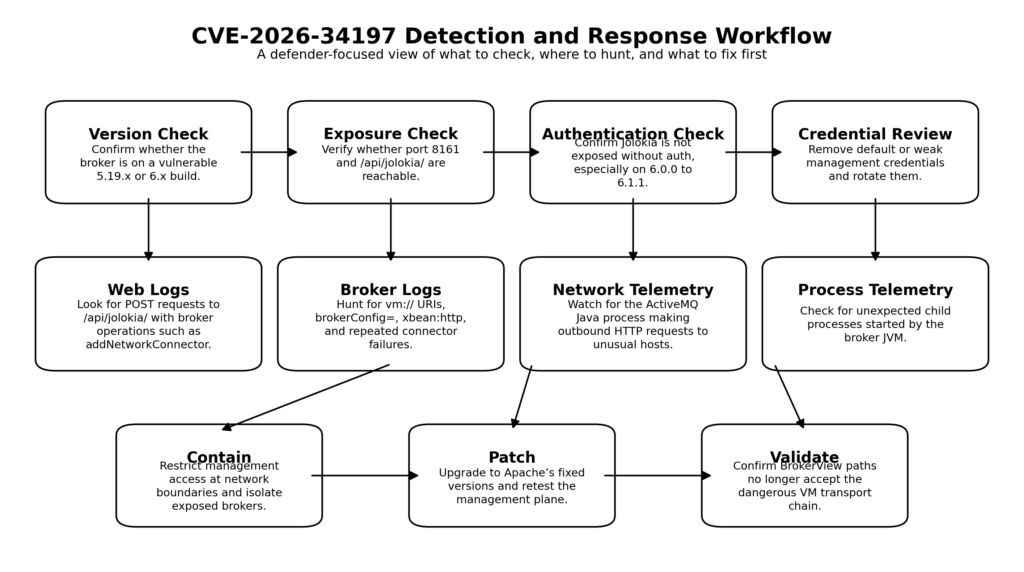
The practical urgency is not hypothetical. Apache’s official advisory says the affected ranges are ActiveMQ Broker and activemq-all before 5.19.4, and 6.0.0 before 6.2.3, with upgrades recommended to 5.19.4 or 6.2.3. ActiveMQ’s release pages show 6.2.3 was released on March 30, 2026 and 5.19.4 on March 31, 2026, and both release pages explicitly mention preventing VM transport from being used with BrokerView and validating nested composite URIs used with BrokerView. NVD, however, is still “Awaiting Analysis” and currently repeats a recommendation to upgrade to 5.19.5 or 6.2.3, even though Apache’s own advisory and release pages point to 5.19.4 and 6.2.3. For defenders, that discrepancy matters, because version guidance is exactly the kind of detail that gets copied into change tickets, scanner checks, and emergency patching notes. (ActiveMQ)
CVE-2026-34197 in plain English
The shortest accurate description is this: an attacker who can reach ActiveMQ Classic’s Jolokia management API can call broker management operations that accept a URI, supply a crafted URI that invokes the VM transport, cause the broker to load a remote Spring XML configuration through xbean:, and turn that XML load into arbitrary code execution inside the Java process. Apache’s advisory names the exact MBean operations, the exact transport parameter, the exact Spring class involved, and the exact execution consequence. This is not speculation or a third-party interpretation. It is how the Apache Software Foundation described the flaw when it published the advisory. (ActiveMQ)
There are three details worth holding in your head from the start. First, this is an ActiveMQ Classic issue, not a generic “all message brokers” problem. Second, the primary path described publicly is an authenticated path, but authentication is a weak comfort if the product ships with well-known defaults and if some deployments accidentally expose the management plane more broadly than intended. Third, on ActiveMQ 6.0.0 through 6.1.1, CVE-2024-32114 can remove the authentication barrier on /api/* entirely, which means the same chain becomes, in operational terms, a no-auth remote code execution path on those builds. Apache’s own 2024 advisory says the default configuration in affected 6.x versions did not secure the API web context, including Jolokia, and that anyone could interact with those layers without authentication. (ActiveMQ)
NVD currently shows the record as awaiting enrichment by NIST, while listing a CISA-ADP CVSS 3.1 score of 8.8 with the vector AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H. That score tracks the official description fairly well for the authenticated case, but if you are triaging 6.0.0 through 6.1.1 systems that are also exposed through CVE-2024-32114, the real-world priority should be higher than the privileges-required field suggests. In practice, those versions collapse a “low privileges” management flaw into an internet-reachable management-plane compromise if the API surface is exposed. (NVD)
How the ActiveMQ Jolokia RCE chain actually works
The management surface is the opening move
ActiveMQ Classic’s documentation has long described the web console as the way to monitor the broker on port 8161. The getting-started guide points administrators to http://localhost:8161/admin, says the web apps are secured out of the box from 5.8 onward, and states that the default username and password are admin/admin unless changed in conf/jetty-real.properties. That is not itself the vulnerability, but it is the first reason the bug matters operationally: it tells you there is a built-in management plane, a built-in Jetty-backed web surface, and a documented default credential pair that many environments may never have rotated. Horizon3’s write-up makes the same practical point more bluntly, noting that the vulnerability formally requires credentials but that default credentials are common in real deployments. (ActiveMQ)
The specific surface at issue is not the /admin HTML console itself but the Jolokia API beneath the web console. Apache’s 2026 advisory says ActiveMQ Classic exposes the Jolokia JMX-HTTP bridge at /api/jolokia/. Jolokia’s own documentation explains the broader model: it is a way to expose JMX operations over HTTP and to restrict them through an XML policy file. That makes Jolokia powerful by design. It exists to let HTTP clients read attributes and invoke management operations on MBeans. The security lesson is that this is not “just another endpoint.” It is a generic administrative bridge. When a product puts that bridge on a web server, every permissive policy choice becomes part of the product’s remote attack surface. (ActiveMQ)
The Jolokia policy was permissive enough to matter
Apache’s advisory says the default Jolokia access policy permits エグゼック operations on all ActiveMQ MBeans under org.apache.activemq:*. Horizon3 shows why that matters. Their write-up explains that after the earlier Jolokia-linked CVE-2022-41678, the project tightened access to dangerous JDK-side MBeans, but preserved a broad allow for ActiveMQ’s own MBeans so that the web console would continue to function. In other words, the earlier hardening did not remove danger from the system. It moved the danger away from one set of objects and left a large trusted island around another set. (ActiveMQ)
This is a common pattern in security engineering. Teams fix the thing that was publicly exploited, preserve the internal functionality they still need, and then inherit risk from the newly trusted path. Jolokia itself supports restrictive policy files. Its documentation says access to MBeans and the Jolokia agent can be restricted through XML policy and split across general command rules and more granular allow and deny rules. The lesson from CVE-2026-34197 is that broad “allow all operations on product-owned MBeans” rules are safer on paper than in reality. Product-owned MBeans are not automatically benign just because they belong to the product rather than to the JDK. (Jolokia)
The dangerous operation was a legitimate runtime feature
The specific MBean operations Apache names are BrokerService.addNetworkConnector(String) そして BrokerService.addConnector(String). ActiveMQ’s API documentation for BrokerService describes addNetworkConnector(String discoveryAddress) as adding a new network connector using a discovery address, and the BrokerViewMBean documentation exposes corresponding addNetworkConnector(String) そして addConnector(String) operations at the JMX layer. None of that is a bug on its own. Runtime broker management is a valid feature. Operators do need ways to create connectors, bridges, and destinations in long-running broker processes. (ActiveMQ)
The problem is that a feature designed as an internal management capability becomes a remote code path when it is reachable through an HTTP-to-JMX bridge. A string parameter that would be harmless in a local operator workflow becomes attacker input. A connector-creation action that would be reasonable inside a trusted control plane becomes an execution primitive when an attacker can choose the URI syntax and the nested parameters inside that URI. Public cloud incidents are full of examples where a “management” feature only became dangerous after it escaped the trust boundary it was written for. CVE-2026-34197 belongs squarely in that family. (ActiveMQ)
The Horizon3 write-up focuses on addNetworkConnector(String) because it provides the cleanest public demonstration. Apache’s advisory lists both addNetworkConnector(String) そして addConnector(String), which matters because defenders should not build detections only around one operation name if they are inspecting management traffic or broker-side JMX audit traces. Still, the public exploit narrative centers on addNetworkConnector, and so should most defensive hunting content, because that is where the publicly documented mechanism is clearest. (ActiveMQ)
VM transport is where a URI stops being just a URI
The next pivot in the chain is the VM transport. ActiveMQ’s documentation describes VM transport as an in-process transport for connecting within the same JVM, without the overhead of network communication. Its embedding documentation shows vm:// as the local transport used by clients inside the same JVM to connect to an embedded broker, and says that an embedded broker can be created through an ActiveMQConnectionFactory using a vm://localhost broker URL. The same document says the broker will be created when the first connection is created, unless create=false is explicitly set. That is the behavior the exploit path relies on: a URI string is not merely parsed. It can lead the broker to create a new embedded broker instance. (ActiveMQ)
That behavior makes sense in its intended use case. Developers embedding ActiveMQ inside an application do want local, lightweight bootstrap behavior. They do want vm:// to be able to bring up a broker. What they do not want is for an internet-facing management API to accept an attacker-chosen string that enters exactly that code path. Once you understand that distinction, the exploit becomes less mysterious. The vulnerability is not that VM transport exists. It is that the semantics of VM transport became reachable from the wrong trust zone. (ActiveMQ)
BrokerFactory and xbean turn configuration into a loader
ActiveMQ’s embedding documentation goes further. It says BrokerFactory.createBroker(new URI(...)) can be used to create a broker via URI, and it lists xbean: as a supported URI scheme for loading an XML document that then becomes ActiveMQ configuration. In the same documentation, the Spring section says a broker factory bean can refer to an external ActiveMQ XML configuration file and explicitly notes that Spring resource loading can use file: または http: prefixes. ActiveMQ’s XML configuration documentation separately states that ActiveMQ uses XBean for XML configuration. Those are legitimate, documented features. They are also precisely what make the attack chain possible. (ActiveMQ)
The chain here is elegant in a bad way. The attacker does not need a memory corruption bug. The attacker does not need template injection. The attacker only needs the product to honor a URI, let that URI reach broker creation logic, and allow broker creation logic to interpret xbean: plus a remote Spring XML resource as configuration input. At that point the “configuration” channel has become a code-loading channel in everything but name. This is exactly the kind of bug that disappears if you review components in isolation and becomes obvious only when you reason across the full path from HTTP request to management operation to transport selection to broker creation to resource loading. (ActiveMQ)
Spring bean initialization is where configuration becomes execution
Apache’s advisory makes the final step explicit. The crafted discovery URI causes the VM transport’s brokerConfig parameter to load a remote Spring XML application context through ResourceXmlApplicationContext, and because ResourceXmlApplicationContext instantiates singleton beans before BrokerService validates the configuration, arbitrary code execution occurs on the broker JVM through bean factory methods such as Runtime.exec(). That sentence from the advisory is the heart of the bug. The danger is not only that Spring loads XML. The danger is that Spring treats that XML as executable object construction logic, and that object construction happens before ActiveMQ gets a chance to reject the configuration as invalid for broker purposes. (ActiveMQ)
Spring’s own documentation on MethodInvokingFactoryBean explains why this works conceptually. It describes the class as a FactoryBean that returns the result of a static or instance method invocation, and notes that it is still useful when the point is to invoke a method that does not return a value. In other words, Spring supports a configuration object whose purpose can be “call this method.” When that capability is exposed through a remotely loaded XML resource in the wrong context, configuration has crossed the line into execution. That is why CVE-2026-34197 is best understood as an execution-by-configuration-chain bug, not merely as a malformed URI issue. (ホーム)
Public exploit write-ups include working request and payload examples. They are not necessary to understand the security engineering lesson, and defenders do not need them to patch or detect the issue. What matters operationally is the mechanism: remote management call, attacker-controlled URI, VM bootstrap path, remote XML load, bean instantiation before validation, and execution inside the broker process. If you understand those five transitions, you understand the bug. (Horizon3.ai)
Why this ActiveMQ RCE matters beyond one patch cycle
This flaw is dangerous even before you get to the no-auth edge cases. ActiveMQ’s own documentation says the web console is how operators monitor a broker, that it lives on port 8161, and that the historical default credential pair is admin/admin. That alone means many environments are likely to have a management endpoint that exists, is routable somewhere it should not be, and may be protected by credentials that were never changed. Horizon3’s write-up treats default credentials as a realistic assumption, not a contrived lab detail, and that matches how management-plane incidents usually play out in practice. (ActiveMQ)
The second reason it matters is history. ActiveMQ Classic has a track record of remotely reachable flaws that later turned into real intrusion paths. NVD’s record for CVE-2023-46604 describes an unauthenticated OpenWire remote code execution issue that allowed a remote attacker to cause either the broker or the client to instantiate arbitrary classes on the classpath. A 2026 DFIR Report case study shows that threat actors exploited that flaw on an exposed ActiveMQ server, used a malicious Spring XML file as part of the execution path, returned after initial eviction, and eventually deployed LockBit-built ransomware. The same report explicitly says that in the second round of compromise, defenders would have had less than 90 minutes before ransomware execution if the first half of the intrusion had not been detected. ActiveMQ is not hypothetical prey. It has already been in real incident chains. (NVD)
The third reason is architectural. CVE-2026-34197 lives in a part of enterprise software that often remains under-governed because teams treat it as “admin functionality.” Admin functionality is exactly where the most dangerous primitives often reside: runtime configuration changes, debug endpoints, object inspection, connector creation, class loading, plugin systems, importers, backup restoration paths, and policy exceptions made for operational convenience. If AI is now better at finding cross-component chains, these are the places that will keep producing findings. The bug is important not only because ActiveMQ users must patch it, but because many other products have similar seams between management, configuration, and execution. (Horizon3.ai)
The version question, why Apache and NVD do not fully match
The most trustworthy source for affected ranges and upgrade targets here is Apache’s own advisory plus Apache’s own release pages. The advisory says the issue affects ActiveMQ Broker before 5.19.4 and from 6.0.0 before 6.2.3, and recommends upgrading to 5.19.4 or 6.2.3. The 6.2.3 release page says that release was published on March 30, 2026 and includes the changes “prevent a VM transport from being used with BrokerView” and “validate nested composite URIs used with BrokerView.” The 5.19.4 release page says the same thing for the 5.19.x line and shows a release date of March 31, 2026. (ActiveMQ)
NVD’s page, at least in its current state, still says the record is awaiting analysis. It reproduces the advisory description but then says users are recommended to upgrade to 5.19.5 or 6.2.3. That does not line up cleanly with Apache’s own advisory text or Apache’s public release pages. The prudent reading is straightforward: use the project’s advisory and release pages as the source of truth for patch selection unless Apache later republishes new guidance. In emergency response work, this kind of mismatch is not a trivial editorial mistake. It can create false negatives in asset searches and wasted time in change windows. (NVD)
The risk picture by version is also uneven. For the main affected branches, the public description is “authenticated RCE through Jolokia.” For ActiveMQ 6.0.0 through 6.1.1, Apache’s 2024 advisory says the default configuration did not secure the /api/* web context, including Jolokia, and Horizon3 states that CVE-2026-34197 is effectively unauthenticated on those versions. That is the population defenders should move to the top of the queue first, especially if port 8161 is externally reachable or exposed to broad internal segments. (ActiveMQ)
The table below is the practical version summary.
| Version line | Status in Apache docs | CVE-2026-34197 relevance | What to do |
|---|---|---|---|
| 5.19.x before 5.19.4 | Supported line before security fix | Vulnerable to the Jolokia to VM to Spring XML chain | Upgrade to 5.19.4 based on Apache advisory and release page |
| 5.19.4 and later in 5.19.x | Current supported patched line | Release notes say VM transport use through BrokerView was prevented | Verify upgrade and regression-check management plane |
| 6.0.0 through 6.1.1 | Deprecated lines, and also affected by CVE-2024-32114 | Highest operational priority because /api/* may be unauthenticated, making this chain effectively no-auth | Upgrade off the line immediately and verify API auth exposure |
| 6.1.2 through 6.2.2 | Affected by CVE-2026-34197, but not by the default API auth bug fixed in 6.1.2 | Authenticated RCE path still applies | Upgrade to 6.2.3 |
| 6.2.3 | Current patched release | Release page says VM transport use via BrokerView was prevented | Use as patch target on 6.x |
The affected ranges, release dates, and fix notes above come from Apache’s advisory, Apache’s download and release pages, and the 2024 API-auth advisory for the 6.x line. (ActiveMQ)
ActiveMQ has seen this movie before
One reason this bug should not be dismissed as a one-off is that it fits a recognizable pattern in the product’s history. Older ActiveMQ Classic flaws have repeatedly involved dangerous management surfaces, unsafe assumptions about trusted inputs, or configuration and class-loading behaviors that can be turned into execution.
The first useful anchor is CVE-2016-3088. Apache’s advisory for that flaw says the Fileserver web application in ActiveMQ 5.0.0 through 5.13.x allowed attackers to replace web application files with malicious code and perform remote code execution. NVD’s summary is even more direct: remote attackers could upload and execute arbitrary files via an HTTP プット followed by an HTTP MOVE. That was a classic web-management-surface RCE. It did not look like CVE-2026-34197 mechanically, but it came from the same part of the security map: functionality that belonged near administrative and web-facing tooling rather than core message delivery. CISA’s KEV catalog also includes CVE-2016-3088 as an Apache ActiveMQ vulnerability that is known to be used in the wild. (ActiveMQ)
The second anchor is CVE-2022-41678. Apache’s advisory calls it a deserialization vulnerability on Jolokia that allowed authenticated users to perform remote code execution. Even without going deep into that exploit path, the significance is obvious: Jolokia had already been part of a publicly assigned RCE story in ActiveMQ. The product had already learned, at least once, that exposing powerful JMX-side behavior over HTTP is risky. CVE-2026-34197 is not the first time a management bridge turned into an execution path. It is a later chapter in the same family of risk. (ActiveMQ)
The third anchor is CVE-2023-46604, which is especially important because it shows that ActiveMQ has already been a serious operational target for real attackers. Apache’s advisory says the OpenWire protocol marshaller was vulnerable to remote code execution. NVD’s description says a remote attacker could manipulate serialized class types so that the client or broker instantiated arbitrary classes on the classpath. The DFIR Report’s 2026 case study shows how that mattered in practice: the attacker exploited an internet-facing ActiveMQ server, used a malicious Spring XML file to run commands, escalated privileges, dumped credentials, moved laterally, returned after initial eviction, and finally deployed ransomware. CISA’s KEV ecosystem also reflects that exploitation history. (ActiveMQ)
The fourth anchor is CVE-2024-32114. Apache’s advisory says the default configuration in affected ActiveMQ 6.x releases did not secure the API web context, including the Jolokia JMX REST API and the Message REST API. That means the product had a documented management-plane exposure bug only two years before this new Jolokia-to-RCE chain. When you put 2022, 2024, and 2026 together, the pattern is hard to ignore. Jolokia, web API exposure, runtime broker control, and remotely loaded configuration are recurring pressure points. (ActiveMQ)
The pattern becomes clearer in one view.
| CVE | Surface | Core mistake | Real lesson |
|---|---|---|---|
| CVE-2016-3088 | Fileserver web application | Web management file handling could be turned into remote file upload and execution | Administrative web features deserve the same paranoia as public app surfaces (ActiveMQ) |
| CVE-2022-41678 | Jolokia | Authenticated users could reach dangerous execution behavior through the Jolokia path | JMX-over-HTTP bridges need strict least-privilege controls, not broad product-owned exceptions (ActiveMQ) |
| CVE-2023-46604 | OpenWire protocol | Broker or client could be tricked into instantiating arbitrary classes from attacker-controlled protocol content | “Instantiate anything on the classpath” is an execution sink even before shell-level payloads appear (ActiveMQ) |
| CVE-2024-32114 | /api/* web context | Default configuration left Jolokia and Message REST API unsecured in 6.x | Management API exposure bugs can turn a medium-looking issue into immediate remote compromise (ActiveMQ) |
| CVE-2026-34197 | Jolokia to BrokerView to VM transport to Spring XML | A runtime management action accepted a URI that crossed into broker creation and executable XML configuration | When management, configuration, and execution semantics overlap, attackers only need one reachable edge to join them (ActiveMQ) |
This historical context also helps explain why Horizon3 urges defenders to treat CVE-2026-34197 as a high-priority issue. Their write-up notes that ActiveMQ has been a repeated target, and points specifically to CVE-2016-3088 and CVE-2023-46604 being in CISA’s KEV orbit. That is not mere rhetorical emphasis. It is a reminder that attackers already know how to recognize ActiveMQ exposures and operationalize them. (Horizon3.ai)
Detection for defenders, what to log and hunt now
The good news about CVE-2026-34197 is that exploitation should not be invisible if you collect the right signals. Horizon3’s disclosure is unusually helpful here. It says exploitation leaves recognizable traces in broker logs, especially network connector activity involving vm:// URIs and brokerConfig=xbean:http. The sample log flow in the disclosure shows the broker establishing a network connection from vm://localhost to a URI containing brokerConfig=xbean:http://.../payload.xml, then logging a configuration failure after the payload has already run. That timing detail matters. The failure message does not mean the attempt was harmless. It can mean the malicious XML was already loaded and executed before the broker rejected it as an invalid broker configuration source. (Horizon3.ai)
Horizon3 also lists three other practical indicators: POST requests to /api/jolokia/ containing addNetworkConnector in the body, outbound HTTP requests from the ActiveMQ broker process to unexpected hosts, and unexpected child processes spawned by the Java process that runs ActiveMQ. Those signals line up with the mechanics of the chain. The attacker must call the management API. The broker must fetch remote XML. And a successful payload must lead to process execution or some equivalent code path inside the JVM. Even if the actual command or post-exploitation tooling varies, the structure of the chain gives defenders multiple observation points. (Horizon3.ai)
A safe first triage check is not to “test the exploit,” but to answer four simpler questions. Is the broker on an affected version? Is port 8161 reachable from places it should not be? Does /api/jolokia/ answer at all, and if so, under what authentication state? And do recent broker logs contain connector attempts involving vm:// そして brokerConfig=? Those are inventory and exposure questions, not exploit questions, and they are enough to prioritize emergency work. Apache’s documentation and advisories give you the version and surface facts you need for that initial pass. (ActiveMQ)
A minimal exposure check can stay entirely on the defensive side.
# Check whether the management surface is reachable
curl -i http://ACTIVEMQ_HOST:8161/admin/
# Check whether Jolokia responds and whether it requires auth
curl -i http://ACTIVEMQ_HOST:8161/api/jolokia/version
# If auth is expected, verify only with authorized credentials
curl -i -u "$ACTIVEMQ_USER:$ACTIVEMQ_PASS" \
http://ACTIVEMQ_HOST:8161/api/jolokia/version
Those checks are useful because Apache’s documentation confirms the management port and default admin surface, while the 2024 advisory tells you that some 6.x versions did not protect /api/* correctly. A system that answers the Jolokia version endpoint without authentication on 6.0.0 through 6.1.1 deserves immediate attention. (ActiveMQ)
Broker log hunting is equally straightforward.
grep -R -E 'brokerConfig=|xbean:http|addNetworkConnector|vm://' \
/opt/activemq/data/activemq.log \
/var/log/activemq/* 2>/dev/null
That search is not a signature for the full exploit. It is a practical way to find the suspicious syntax that Horizon3 says should appear in exploitation attempts. In mature environments, this grep should be supplemented with central logging and correlation against source IP, user identity, and outbound connection records. But even on a single host, it is a fast way to surface whether the broker has recently tried to build connectors using unusual local transport URIs or remote XBean resources. (Horizon3.ai)
For teams with SIEM or log pipelines, the highest-value HTTP-layer detection is narrow and specific.
title: Suspicious ActiveMQ Jolokia Connector Creation
logsource:
product: webserver
detection:
selection_uri:
cs-uri-stem|contains: "/api/jolokia/"
selection_method:
cs-method: "POST"
selection_body:
request_body|contains:
- "addNetworkConnector"
- "org.apache.activemq:type=Broker"
condition: selection_uri and selection_method and selection_body
level: high
That kind of rule works because the publicly documented chain depends on a management POST that names a broker MBean operation. It is much more actionable than broad “watch for Jolokia” heuristics, especially in environments where Jolokia is legitimately used. The important point is to combine URI, method, and operation name rather than trigger on any single one alone. (Horizon3.ai)
Process and network telemetry should be treated as equal citizens here. The DFIR Report on CVE-2023-46604 is a useful reminder. In that case, defenders observed the ActiveMQ Java process downloading malicious XML, then executing follow-on payloads, and later saw the compromise turn into credential theft, lateral movement, and ransomware. CVE-2026-34197 is a different entry point, but it lands in the same runtime: the broker JVM. If you only look at HTTP access logs and ignore Java child processes, outbound requests, and post-exploitation activity, you are blind to the stage that actually matters. (The DFIR Report)
The detection sequence below is a good operational baseline.
| レイヤー | What to look for | なぜそれが重要なのか |
|---|---|---|
| Web logs | POST to /api/jolokia/ with broker operation names such as addNetworkConnector | Publicly documented trigger path uses a broker MBean exec call (Horizon3.ai) |
| Broker logs | vm:// connector activity, brokerConfig=, xbean:http, repeated connector retries | Horizon3 says these are strong indicators and notes that failure logs can come after payload execution (Horizon3.ai) |
| Network telemetry | Outbound HTTP from the ActiveMQ Java process to unusual hosts | The chain requires the broker to fetch remote XML or equivalent remote content (Horizon3.ai) |
| Process telemetry | Java spawning unexpected child processes | A successful payload often becomes process execution inside the broker context (Horizon3.ai) |
| 資産目録 | ActiveMQ Classic version and 6.0.0 through 6.1.1 API exposure | Determines whether the issue is authenticated or effectively unauthenticated in practice (ActiveMQ) |
Remediation for ActiveMQ Classic, patching, isolation, policy, credentials
The first remediation step is simple and non-negotiable: patch to Apache’s fixed lines. The 6.2.3 release page says that release prevents VM transport from being used with BrokerView and validates nested composite URIs used with BrokerView. The 5.19.4 release page says the same for the 5.19.x line. Apache’s advisory names those two versions as the fix targets. That is the cleanest primary action. (ActiveMQ)
The second step is to treat management exposure as a design problem, not only a version problem. Apache’s own docs say the web console lives on 8161 and document default credentials. Apache’s 2024 advisory says some 6.x defaults left /api/* exposed without authentication. Jolokia’s documentation says policy can be restricted with XML. Those three facts together mean remediation is not complete when the package version changes. A broker that is fully patched but still broadly exposes management surfaces, still uses weak credentials, or still trusts a wide management network is more fragile than it needs to be. (ActiveMQ)
The third step is to stop thinking about “authenticated RCE” as a comfortable category. In enterprise environments, admin credentials are often reused, vaulted but over-shared, copied into deployment automation, left at defaults, or delegated through reverse proxies and monitoring systems. An RCE that requires only management credentials is still an infrastructure emergency. If you want to rank the work rationally, prioritize systems in this order: externally reachable 6.0.0 through 6.1.1, then externally reachable affected versions on either line, then broadly reachable internal management planes, then narrow internal management planes. That ordering is an inference from the official version guidance and the /api/* exposure bug in 6.x. (ActiveMQ)
A practical hardening checklist looks like this.
| Time horizon | アクション | Why it belongs here |
|---|---|---|
| Immediate | Upgrade to 5.19.4 or 6.2.3 | Apache identifies these as fixed targets (ActiveMQ) |
| Immediate | Remove or rotate admin/admin and any weak management credentials | ActiveMQ docs document the historical default pair; Horizon3 notes default credentials are common in practice (ActiveMQ) |
| Immediate | Restrict access to 8161 and /api/* at network boundaries | Limits reachability of the management plane that the bug depends on (ActiveMQ) |
| Short term | Verify Jolokia requires authentication on all 6.x systems, especially 6.0.0 through 6.1.1 | Apache’s 2024 advisory says those versions did not secure /api/* by default (ActiveMQ) |
| Short term | Review Jolokia policy for least privilege rather than broad product-wide allow rules | Jolokia supports granular policy restrictions and the default ActiveMQ exception proved too broad (Jolokia) |
| Short term | Hunt historical logs for vm://, brokerConfig=, and suspicious broker-initiated outbound HTTP | Public disclosure lists these as meaningful indicators of exploitation (Horizon3.ai) |
| Long term | Treat management planes as separate trust zones with dedicated ACLs, auth, and monitoring | ActiveMQ’s recurring security history shows management features repeatedly becoming execution surfaces (ActiveMQ) |
A modest regression test is worth institutionalizing after the patch. The release notes say the fix prevents VM transport from being used with BrokerView and validates nested composite URIs. That tells defenders what they should confirm in staging or authorized validation environments: management actions that used to accept transport and nested URI tricks should now reject them safely, and those rejections should happen before any network fetch or bean instantiation side effects occur. The specific test harness will vary by environment, but the principle is stable: verify the security property the release notes claim, not only the package version. (ActiveMQ)
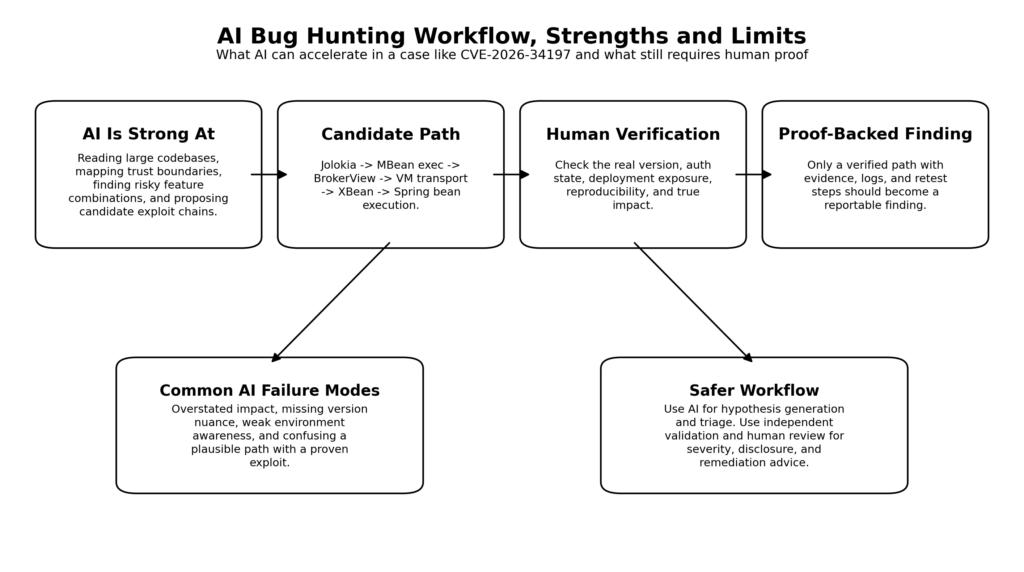
What CVE-2026-34197 says about AI vulnerability research
The public conversation around this bug will probably center on the phrase “Claude found an ActiveMQ RCE in ten minutes.” That is a catchy headline, but it misses the more important lesson. The real significance is not that an LLM found “a bug.” The significance is that an LLM was strong at assembling a multi-component path where each component looked reasonable in isolation. Horizon3 says exactly that: the bug involved Jolokia, JMX, network connectors, and VM transports, each developed independently over time, and the model was good at stitching the path together end to end. That is the kind of codebase reasoning frontier models are increasingly good at. (Horizon3.ai)
That matters because this is where many human reviews fail. Humans get anchored on the intended purpose of components. A reviewer sees “JMX management,” “network connector creation,” “embedded broker transport,” and “XML configuration” as separate administrative features. A model can be less constrained by those conceptual silos and more willing to ask what happens when one feature’s output becomes another feature’s input. In practical appsec terms, it is good at candidate path enumeration across trust boundaries. That does not mean it understands the target system better than an experienced researcher. It means it can search a much larger hypothesis space much faster. (Horizon3.ai)
Horizon3’s post also says something even more important for defenders and buyers of AI security tools: “A lot of the time, Claude finds interesting stuff but it doesn’t quite rise to the level of a CVE I’d bother reporting.” That sentence is the cleanest public statement of the current frontier. Models are increasingly good at surfacing suspicious behavior, weird compositions, and plausible attack paths. They are not automatically good at converting those paths into findings that deserve disclosure, survive retest, and hold up under adversarial review. There is still a large gap between “interesting” and “reportable.” (Horizon3.ai)
Anthropic’s own public work points in the same direction. In its March 2026 write-up on collaboration with Mozilla, Anthropic says Claude Opus 4.6 discovered 22 Firefox vulnerabilities over two weeks, 14 of which Mozilla classified as high severity. That is an extraordinary finding rate. But the same write-up also says that when Anthropic spent about $4,000 in API credits trying to turn discovered Firefox bugs into actual exploits, the model succeeded in only two cases. Anthropic’s stated takeaway is explicit: Claude was much better at finding bugs than exploiting them, and the cost of identifying vulnerabilities was an order of magnitude lower than creating an exploit for them. (Anthropic)
That pattern helps explain why a case like CVE-2026-34197 is such a strong AI success story. The chain is clever, but its exploitation logic is not exploit-development-heavy in the browser-engine sense. It is not a modern heap shaping problem. It is not a subtle race. It is not a multi-stage memory corruption chain requiring precise reliability work. It is a codebase reasoning problem: find the reachable route from a trusted management action to a configuration loader that behaves like an execution engine. AI is currently very well suited to exactly that class of work. (Horizon3.ai)
Where AI bug hunting is still weak
The first weakness is proof. A model can propose that a path is dangerous. It can even explain that path convincingly. But exploitability is still an empirical question. Does the endpoint actually answer in the deployed version? Does the environment use the vulnerable module? Is there a compensating control in front of the broker? Does the authentication state differ in production? Does the target support the required resource-loading behavior? In the ActiveMQ case, those questions include exact version boundaries, exact management exposure, and exact credential state. The model can narrow the search. It cannot quietly replace environment validation. (ActiveMQ)
The second weakness is overclaiming. Anthropic’s public report on an AI-orchestrated cyber espionage campaign says that during autonomous operations, Claude frequently overstated findings and occasionally fabricated data, including claiming to have obtained credentials that did not work or identifying public information as critical discoveries. Anthropic describes this as a real limitation in offensive contexts and says it required careful validation of all claimed results. That problem matters just as much in defensive research. A model that sounds certain can still be wrong about reachability, privileges, impact, or even the existence of a vulnerability. (Anthropic Brand Portal)
The third weakness is framing dependence. Horizon3 shares the kind of prompt they use to start many reviews: enumerate unauthenticated endpoints, research prior commits and vulnerabilities, and focus on RCE, auth bypass, broken access control, file read, SSRF, XXE, SQLi, and important misconfigurations while ignoring XSS, CSRF, open redirects, and DoS. That is a smart operator prompt, but it tells you something fundamental about current AI use in security. The model is not independently choosing a research program from first principles. It is being pointed at the problem by a human with a threat model. The quality of the result depends heavily on the operator’s ability to bound the search space and decide what counts as worth investigating. (Horizon3.ai)
The fourth weakness is deployment context. CVE-2026-34197 is a perfect demonstration. The same source set gives you a genuine discrepancy between NVD and Apache on recommended 5.19.x upgrade targets. The same code path means different operational risk depending on whether the host is on 6.0.0 through 6.1.1 and whether /api/* is unintentionally unauthenticated. The same “authenticated RCE” label means something different if the environment still uses admin/admin. None of those distinctions live purely in one function body. They live at the boundary between source code, product defaults, version history, docs, and deployment reality. Models still do not handle that boundary robustly enough to be trusted without external verification. (NVD)
The fifth weakness is that narrative quality is not evidence. A polished explanation from a model can make a fragile claim sound mature. Security teams should be actively suspicious of that. If a finding does not include narrow preconditions, a reproducible path, independently observable evidence, and a plausible remediation story, it is still a research note. It is not yet a vulnerability claim you should act on. That is not anti-AI advice. It is the standard of proof that has always separated useful research from interesting chatter. Horizon3’s own description of the process, and Anthropic’s own public reporting, both reinforce that point from different angles. (Horizon3.ai)
The table below summarizes the current state more honestly than either hype or dismissal.
| AI is already strong at | AI still breaks on | Why the distinction matters |
|---|---|---|
| Reading large codebases quickly | Knowing whether a path is truly reachable in your deployment | Reachability depends on versions, auth state, routing, and config, not only code (Horizon3.ai) |
| Stitching together multi-component candidate chains | Converting a candidate into a high-confidence, disclosure-grade finding | Horizon3 explicitly says many findings are merely “interesting stuff” (Horizon3.ai) |
| Finding low-complexity vulnerability classes at scale | Reliable exploitation of difficult bugs | Anthropic says Claude was much better at finding bugs than exploiting them (Anthropic) |
| Accelerating diff reading, hot-spot analysis, and hypothesis generation | Avoiding overclaiming and fabricated success during autonomous operation | Anthropic’s public misuse report calls out overstated findings and fabricated data as a real limitation (Anthropic Brand Portal) |
| Drafting reports and reasoning through likely next steps | Replacing human judgment about impact, scope, and disclosure quality | Narrative fluency is not proof, and good reports still need external validation (Horizon3.ai) |
A safer AI-assisted workflow for vulnerability discovery
A realistic workflow starts by giving the model the jobs it is actually good at. Let it read the codebase. Let it summarize historical hotspots. Let it map candidate trust boundaries. Let it point out places where “configuration,” “management,” and “execution” overlap. Let it draft the shortest likely validation paths and the cleanest regression checks. Those are all high-leverage tasks because they reduce human search effort without pretending to remove the burden of proof. Horizon3’s example prompt, Anthropic’s Mozilla work, and Anthropic’s cyber-defender research all point toward this same pattern: AI is valuable as a force multiplier for code reasoning and candidate generation. (Horizon3.ai)
Then draw a bright line. The model does not get to decide, alone, that a bug is real, exploitable, severe, or worth disclosure. Those judgments require an external verifier. In practice that means a test environment, logs, a request recorder, a debugger, a network capture, an independent scanner, a patch diff, or a human reviewer who can say whether the path still holds after the hand-wavy parts are removed. Anthropic’s Firefox work describes exactly that kind of human verification loop for the first confirmed bug, and its public report on misuse shows why the loop matters when AI starts speaking with too much confidence. (Anthropic)
This is also where the design of AI pentesting workflows starts to matter more than raw model quality. Penligent’s public material frames AI pentesting as an operator-controlled workflow with editable actions, scope control, and reporting tied to evidence rather than to chat output. Its recent public writing on AI pentest workflows uses language that fits this case unusually well: it describes an AI pentester as a governed system for shrinking the distance between raw signal and a verified finding, and describes a trustworthy AI pentest report as something that survives retest rather than a PDF generated from a smart-looking conversation. That is exactly the standard this ActiveMQ case reinforces. The model’s hypothesis is useful. The verified finding is the thing that matters. (ペンリジェント・アイ)
A clean workflow for a bug like CVE-2026-34197 therefore looks something like this. First, let AI identify that an exposed Jolokia path, a broad MBean exec policy, runtime connector creation, VM transport, and XBean resource loading might compose into execution. Second, validate the chain in an authorized environment without trusting the model’s narrative alone. Third, confirm the exact affected versions and patch targets from project-controlled sources. Fourth, derive detections from the actual mechanism, not from generic buzzwords. Fifth, write the report around preconditions, artifacts, and regression checks. If you reverse that order and let the report come first, you end up with the weakest possible use of AI in security: a polished write-up unsupported by verifiable evidence. (ActiveMQ)
One practical way to enforce that discipline is to require four artifacts before anyone accepts an AI-assisted finding as real. The first is a narrow precondition statement. The second is a minimal reproduction path in a controlled environment. The third is independent evidence that the claimed effect actually occurred. The fourth is a regression check that would fail if the bug came back after a fix. Those requirements do not fight the model. They give the model a productive role inside a verifiable process. (Anthropic)
What security teams should do this week
If you operate ActiveMQ Classic, the fastest useful plan is simple. Inventory the version. Check whether 8161 is reachable where it should not be. Confirm whether /api/jolokia/ requires authentication. Prioritize any 6.0.0 through 6.1.1 systems because Apache’s 2024 advisory says those builds did not secure /api/* by default. Rotate management credentials if there is any chance defaults remain in use. Patch to 5.19.4 or 6.2.3. Hunt for vm://, brokerConfig=, broker-initiated outbound HTTP, and suspicious Java child processes. Then regression-test the management surface in staging and close the exposure with network policy, not just with package updates. (ActiveMQ)
If you build or buy AI-assisted offensive workflows, do not take the wrong lesson from this disclosure. The lesson is not that a model can now replace a researcher. The lesson is that frontier models are now good enough to make cross-component code review dramatically faster, especially for low-complexity but high-impact bugs that hide in the seams between features. That pushes more responsibility onto teams to build evidence-first workflows, independent verification, and disciplined reporting. Models are getting better fast. The burden of proof has not changed. (Horizon3.ai)
The real takeaway from CVE-2026-34197
CVE-2026-34197 should be read as both a product-specific warning and an industry-wide one. The product-specific warning is obvious: patch ActiveMQ Classic, lock down Jolokia, and stop treating management planes as second-class attack surfaces. The wider warning is that many enterprise products still blur the line between administration, configuration, and execution. When that happens, AI does not need a magical new exploit technique. It only needs enough reasoning power to connect the pieces faster than humans have historically done. ActiveMQ will not be the last product where that happens. (ActiveMQ)
Further reading
- Apache ActiveMQ official advisory for CVE-2026-34197 (ActiveMQ)
- NVD record for CVE-2026-34197, including current status and the present recommendation mismatch (NVD)
- Horizon3 disclosure, 10 Minutes with Claude, Remote Code Execution in Apache ActiveMQ (Horizon3.ai)
- Apache ActiveMQ 6.2.3 release page (ActiveMQ)
- Apache ActiveMQ 5.19.4 release page (ActiveMQ)
- Apache advisory for CVE-2024-32114, unsecured
/api/*in ActiveMQ 6.x (ActiveMQ) - Apache advisory for CVE-2022-41678, authenticated Jolokia RCE (ActiveMQ)
- Apache advisory and NVD record for CVE-2023-46604 (ActiveMQ)
- The DFIR Report case study on ransomware activity following ActiveMQ exploitation (The DFIR Report)
- Anthropic and Mozilla on AI-assisted vulnerability discovery in Firefox (Anthropic)
- Anthropic’s report on AI-orchestrated offensive operations and the problem of overstated findings (Anthropic Brand Portal)
- Penligent, AI Pentester in 2026, How to Test AI Systems Without Confusing the Two (ペンリジェント・アイ)
- Penligent, How to Get an AI Pentest Report (ペンリジェント・アイ)
- Penligent, How to Use AI for Bug Bounty in 2026 (ペンリジェント・アイ)
- Penligent product home page (ペンリジェント・アイ)