On March 11, 2026, Stryker disclosed that it had suffered a cybersecurity attack that caused a global disruption to its Microsoft environment. The company said it activated its incident response plan, launched an investigation with external advisors, and believed the incident was contained to its internal Microsoft environment. Stryker also said it had detected no ransomware or malware. Within a day, the company confirmed that the disruption was affecting order processing, manufacturing, and shipping, while stating that connected products were not impacted and remained safe to use. (Stryker)
That combination of facts is what makes the Stryker cyber attack worth studying far beyond the headline cycle. This was not presented as a classic ransomware case with an encryption note and a negotiation channel. It was an operationally disruptive incident centered on a large enterprise’s internal Microsoft estate, with downstream effects on core business functions. Reuters reported that an Iran-linked group calling itself Handala claimed responsibility, while security experts interviewed in public coverage described the incident as consistent with destructive retaliation rather than ordinary cyber extortion. Stryker’s official statements, however, remain more restrained: the company has confirmed disruption, containment efforts, and operational impact, but has not publicly validated many of the attackers’ claims. (Reuters)
That distinction matters. Security teams often lose precision when a story is still unfolding. In this case, there are at least three different layers that should not be blended together. First, there are the facts Stryker itself has confirmed: date, scope, affected environment, operational disruption, and the absence of identified ransomware or malware. Second, there are the threat actor claims, including assertions about stolen data volume and the scale of wiping activity. Third, there are industry inferences, including the increasingly common view that the attackers may have abused legitimate management tooling or privileged control paths rather than deploying conventional malware. A serious technical analysis needs to keep those layers separate. (Stryker)
The easiest way to misunderstand the incident is to reduce it to “a cyberattack on a healthcare company.” Stryker is not just another corporate network. It sits in the medical technology ecosystem, with products, workflows, service relationships, and logistics that connect into real care delivery environments. Even when patient-facing connected products remain safe, disruption to ordering, manufacturing, and shipping is not a minor back-office inconvenience. In healthcare and medtech, a business systems outage can become a supply chain event quickly. Dark Reading framed the incident as a disaster recovery wake-up call for exactly this reason: continuity planning is often less mature for destructive disruption than for classic ransomware response. (Cybersecurity Dive)

What the public record actually shows
The public record now supports a concise but important timeline. On March 11, Stryker disclosed a cyberattack affecting its Microsoft environment and said the issue appeared contained. By March 12 and March 13, the company was publishing rolling customer updates and media statements acknowledging disruption to order processing, manufacturing, and shipping. Reuters reported that Stryker had 56,000 employees and operations in 61 countries, which helps explain why even a disruption limited to an internal environment could create global business friction. (Stryker)
The Reuters reporting also captured one of the most consequential details in the early discussion: some staff and contractors described Windows-based devices and remote-connected systems being wiped. Reuters could not independently verify those social posts, but the report added broader expert concern that Iran-linked proxies may be using destructive cyberattacks, including data deletion, as retaliation. That interpretation was echoed in multiple industry writeups that emphasized the difference between extortion-driven encryption and destruction-driven disruption. (Reuters)
Stryker’s own customer updates are equally important because they narrow the blast radius in one dimension while widening it in another. The company repeatedly stated that connected products were not impacted and were safe to use. That is reassuring from a medical device safety standpoint. At the same time, the company acknowledged the business impact on ordering, manufacturing, and shipping. This is a useful reminder for defenders: in a medtech incident, the most consequential outcome may not be direct compromise of device firmware or bedside functionality. It may be the interruption of the operational machinery required to get the right products, services, accessories, and support where they need to be. (Stryker)
This is also why the story resonated so strongly in the security press. The phrase that appears most consistently across high-visibility coverage is not “medical device exploit” but “Stryker cyberattack” or “Stryker cyber attack,” often paired with “Iran-linked.” That language tracks what readers are actually trying to understand: not a single bug, but a major enterprise disruption involving a critical healthcare supplier. (Reuters)
Why the absence of ransomware is one of the biggest clues
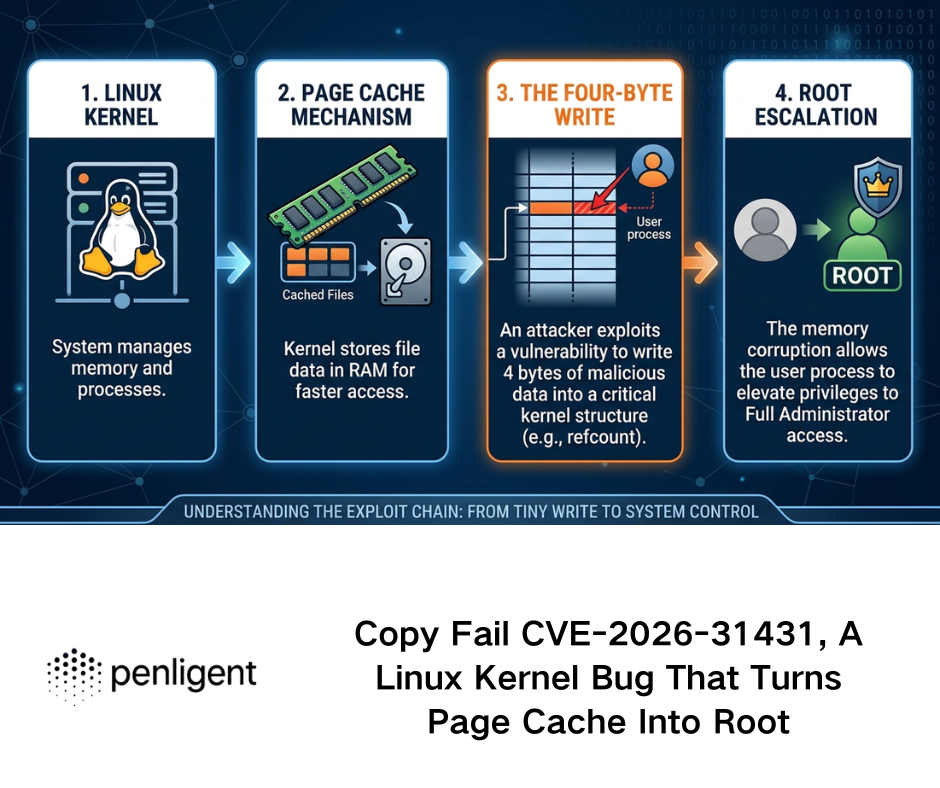
One of the most revealing official statements in this case is Stryker’s repeated assertion that it had no indication of ransomware or malware. In many incidents, that line would be treated as a footnote. Here, it should be treated as a design clue. If the affected environment was the organization’s internal Microsoft estate, and if widespread business disruption occurred without confirmed ransomware or malware, then defenders should immediately expand their threat model beyond “malicious binary landed on endpoints.” (Stryker)
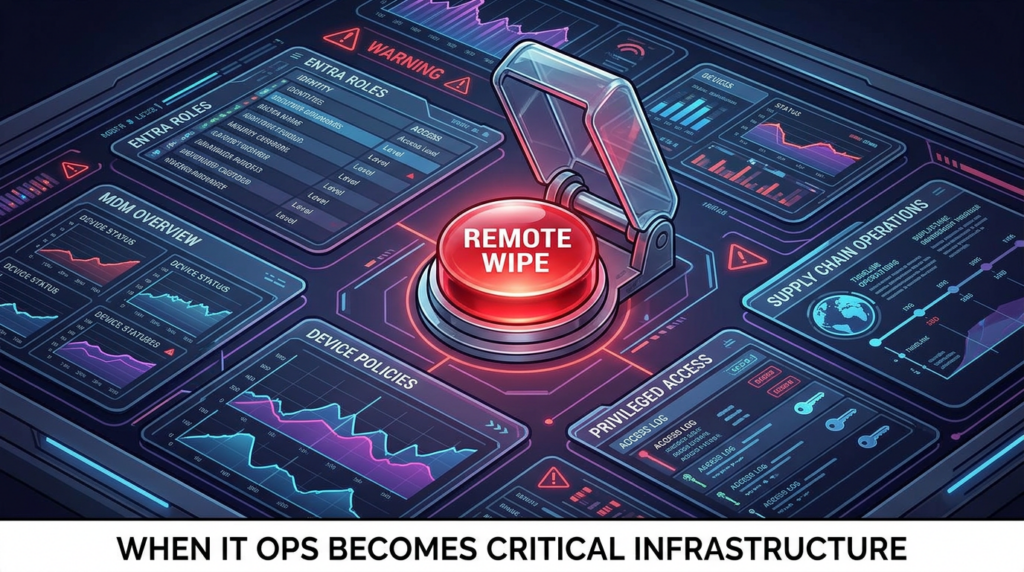
Public reporting and vendor commentary increasingly point toward a different class of failure: the misuse of legitimate administrative capability. SecurityWeek reported that evidence indicated attackers may have leveraged existing endpoint management software rather than malware to wipe devices, and cited unverified reports that Intune was involved. Microsoft’s own documentation makes clear that Intune supports remote wipe actions that can factory reset managed devices and remove data, apps, and configurations. In other words, the same control plane that makes large-scale fleet administration efficient can become a kill switch if the wrong identity or privilege chain is compromised. (SecurityWeek)
That does not prove Intune abuse in the Stryker case. It does something more useful: it shows why the hypothesis is technically plausible and why many defenders reacted so strongly to it. A modern enterprise can suffer catastrophic business interruption without a custom wiper if an attacker can authenticate into the right management plane and issue destructive actions through built-in features. The defenders who still design detections primarily around malware signatures or ransomware notes are preparing for yesterday’s intrusions. (SecurityWeek)
The same logic applies to Microsoft Entra and other identity governance layers. Microsoft documents that Entra audit logs are designed to record traceable tenant activities, including changes to users, groups, applications, and service-related objects. When a destructive event unfolds through identity and administration rather than through a noisy payload, the central forensic questions shift. Who activated elevated roles. Which service principal changed scope. Which policy was modified. Which remote action was issued. Which privileged session was approved. Those are not side questions. In an identity-led enterprise attack, they are the main event. (Microsoft Learn)
The real data security problem is larger than exfiltration
When readers search for stryker cyber attack, they usually expect to learn whether data was stolen. That is an understandable question, but it is too narrow. Data security in this incident should be understood across four layers.
The first layer is identity and control data. In a Microsoft-centered enterprise, the most sensitive data is not just files in SharePoint or mailboxes in Exchange. It is the administrative graph of the business: enrolled devices, role assignments, conditional access policies, service principals, device compliance states, MDM authority, authentication artifacts, and privileged workflow history. Compromise here changes what an attacker can do, not just what they can read. (Microsoft Learn)
The second layer is operational workflow data. Stryker confirmed impacts to order processing, manufacturing, and shipping. Those functions are data systems before they are business systems. Purchase orders, inventory states, manufacturing schedules, customer delivery coordination, service records, shipment status, and partner communications all live inside applications, identities, queues, and integrations. Once these become unavailable or untrustworthy, the damage is not limited to confidentiality loss. Integrity and availability failures start compounding in ways that traditional breach narratives miss. (Cybersecurity Dive)
The third layer is potential business and customer data exposure. Attackers claimed to have exfiltrated large amounts of data, but those claims remain unverified in the public record. That means defenders should be careful not to repeat the number as established fact. The right takeaway is more operational: any organization facing a potentially destructive attack should assume, until disproven, that exfiltration may have occurred before disruption became visible. Destruction often functions as cover, pressure, retaliation, or distraction. (Reuters)
The fourth layer is downstream partner and ecosystem exposure. Health-ISAC’s 2025 threat report found that health sector professionals ranked ransomware, phishing, compromised credentials, third-party credentials, and data breaches among the top current threats, while for 2025 they elevated third-party breaches and supply chain attacks even further. In parallel, the 2025 Healthcare Cybersecurity Benchmarking Study found that third-party risk management and asset management remained underperforming areas, and that vendor or supplier cybersecurity requirements lagged broader coverage. That is exactly the lens through which the Stryker incident should be read. A supplier’s outage is a customer’s security event when the supplier sits in the path of care operations.
Healthcare and medtech were already being warned about this
The uncomfortable truth is that this incident does not arrive in a vacuum. HHS says the Healthcare and Public Health Cybersecurity Performance Goals were developed to address common attack vectors identified in hospital resiliency analysis and grounded in established frameworks such as NIST CSF and Healthcare Industry Cybersecurity Practices. The FDA’s current cybersecurity guidance for medical devices emphasizes that devices with cybersecurity risk should be designed and documented to be resilient against cybersecurity threats. None of that language is speculative anymore. It is the baseline expectation for the sector. (HHS Cyber Gateway)
What makes the Stryker cyber attack especially useful as a case study is that it straddles the boundary between classic enterprise security and regulated healthcare resilience. Stryker’s statements that connected products were not impacted align with FDA-style thinking about device resilience and product safety boundaries. But the event also exposes how much healthcare continuity depends on non-device enterprise systems. You can have a medically safe device and still have a clinically dangerous supply chain disruption if ordering, support, provisioning, planning, or shipping is impaired. (Stryker)
That is also why third-party and supplier controls matter so much. The Health Industry Cybersecurity Supply Chain Risk Management Guide lays out a mature expectation that suppliers and third-party service partners should be identified, prioritized, contractually controlled, routinely assessed, and included in response and recovery planning. It explicitly discusses the need to verify contractual obligations, obtain audit rights or equivalent assurance mechanisms, and consider nth-party risk where a direct supplier itself depends on downstream providers. For a medtech company, this is not procurement bureaucracy. It is incident blast-radius engineering.
The related CVEs that actually matter here
A lot of breach writeups lazily bolt on unrelated CVEs for traffic. That is not useful. The better approach is to ask which vulnerabilities illuminate the class of control failure implicated by this event.
The first one worth discussing is CVE-2025-4428, an Ivanti Endpoint Manager Mobile code injection vulnerability that NVD records as a remote code execution issue in the API component, affecting Ivanti Endpoint Manager Mobile 12.5.0.0 and prior. More importantly, NVD notes that the CVE is in CISA’s Known Exploited Vulnerabilities Catalog. This does not tie the flaw to Stryker. What it does show is that endpoint and mobile management platforms are not just administrative conveniences. They are high-value attack surfaces whose compromise can translate into broad device control. In a post-Stryker world, that should be obvious to everyone. (NVD)
The second one is CVE-2025-47179, which NVD describes as an improper access control vulnerability in Microsoft Configuration Manager that allows an authorized attacker to elevate privileges locally. Again, this is not evidence of the path used against Stryker. It is a reminder that configuration and management infrastructure deserves the same intensity of testing that organizations normally reserve for internet-facing applications and identity providers. When enterprises centralize management, they also centralize blast radius. (NVD)
The bigger lesson is not “watch these two CVEs.” The lesson is that your testing program should elevate any flaw, misconfiguration, or excessive privilege in endpoint management, device administration, MDM, EMM, identity governance, and privileged access workflows to near top-tier priority. If those systems are exposed, under-segmented, or under-audited, the difference between administration and destruction can collapse quickly. (NVD)

What continuous penetration testing should look like after Stryker
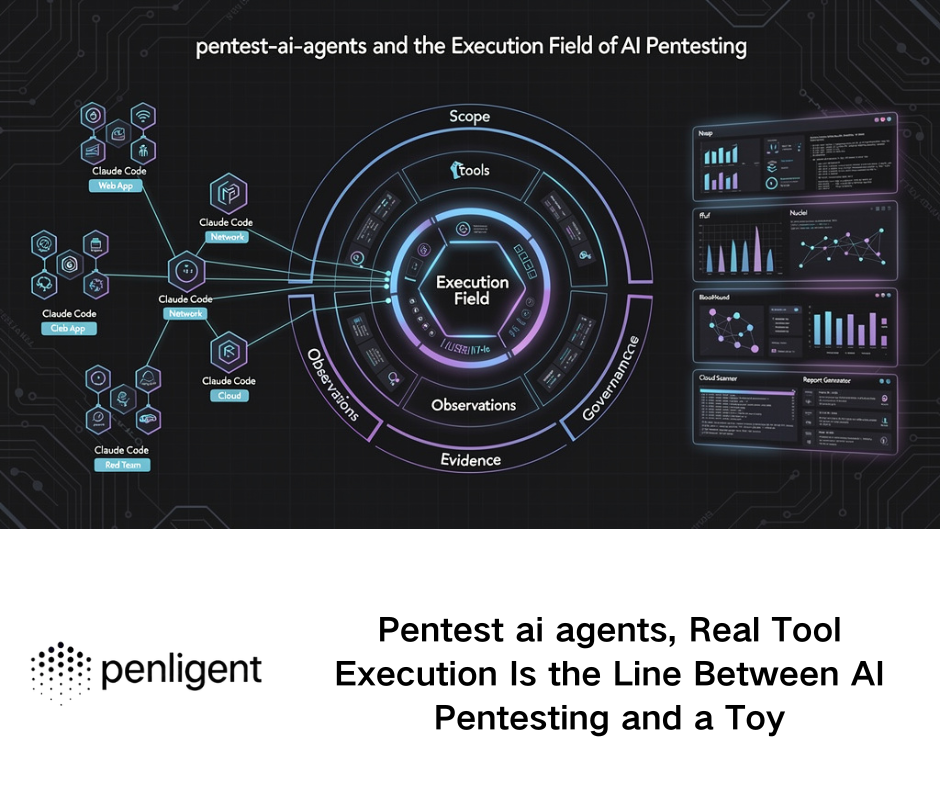
The wrong response to an incident like this is to schedule a single annual penetration test and call it maturity. The right response is to redesign validation around the control planes that actually move risk.
A modern continuous testing program for a medtech or healthcare-adjacent enterprise should include at least five recurring tracks.
| Track | What to test continuously | Why it matters after Stryker |
|---|---|---|
| External attack surface | Internet-exposed portals, VPNs, remote admin interfaces, supplier logins, forgotten subdomains | Initial access often begins outside the identity story, then pivots inward |
| Identity and privilege | Entra roles, break-glass accounts, service principals, conditional access drift, PIM workflows | A destructive attack can execute through authenticated control rather than malware |
| Management plane abuse | Intune, ConfigMgr, EMM, RMM, remote actions, bulk wipe capability, device trust boundaries | Administrative tooling can become a kill switch |
| Supplier and integration risk | Third-party access paths, support channels, API trust, B2B identities, contractual security evidence | Healthcare supply chains magnify upstream weakness |
| Recovery and continuity | Restore integrity, alternate ordering flows, shipment fallback, manufacturing rollback, comms failover | Availability damage is the defining feature of this event |
This is not theory. HHS, Health-ISAC, and the healthcare benchmarking data all point to the same pressure points: third-party risk, asset visibility, segmentation, and operational resilience are still weaker than they need to be. A continuous testing program should therefore be designed to produce evidence on those exact issues, not just generic exploit screenshots. (HHS Cyber Gateway)
A good program also distinguishes breach simulation from control validation. Red teams are useful, but most enterprises need something more repeatable between large exercises: weekly or monthly tests that re-check exposed assets, authentication flows, privilege drift, role abuse opportunities, administrative surface changes, and critical workflow availability. The question is not merely whether a pentester can get in once. It is whether your environment becomes materially more dangerous between now and next Tuesday without anyone noticing. That is what continuous validation is for. (HHS Cyber Gateway)
A practical detection mindset
If you suspect that a destructive event could be executed through identity or device management tooling, your logging and hunting assumptions need to change. Microsoft documents Intune audit logs and Entra audit logs as key administrative evidence sources. In practice, defenders should monitor for sudden spikes in remote actions, unusual bulk operations, anomalous role assignment changes, unexpected service principal activity, and policy modifications outside expected change windows. (Microsoft Learn)
An illustrative KQL-style hunt might start like this:
// Illustrative hunting logic, adapt to your tenant schema and table names
let startTime = ago(7d);
union isfuzzy=true
AuditLogs,
IntuneAuditLogs
| where TimeGenerated >= startTime
| where OperationName has_any ("wipe", "retire", "delete device", "remote action", "role assignment", "service principal", "conditional access")
| summarize Count = count(), Targets = make_set(TargetResources, 20) by bin(TimeGenerated, 1h), OperationName, InitiatedBy
| order by Count desc
This is intentionally illustrative rather than vendor-perfect. The important part is the operating model. You want detection logic that surfaces destructive administrative behavior, not only known malware telemetry.
A second useful control is separation for destructive actions. If your platform allows it, require stronger approval paths or secondary authorization for bulk wipes, bulk retirements, device deletion workflows, or mass policy changes. Even vendor ecosystem guidance around Intune increasingly emphasizes stronger oversight for wipe operations because remote administrative actions have real destructive potential when misused. (Microsoft Learn)
Questions your security team should be able to answer this quarter
A Stryker-style disruption is the wrong time to discover that these questions have no clean owner.
| Pergunta | Good answer looks like |
|---|---|
| Can we list every system that can remotely wipe, retire, reset, or disable endpoints | A named inventory with owners, auth model, logging path, and approval model |
| Can a single admin identity issue destructive action at scale | No, or only under tightly controlled emergency procedures |
| Do we have recent evidence that supplier access is tiered and reviewed | Yes, with dated evidence, not just contract language |
| Can we detect abnormal spikes in management actions within minutes | Yes, with tested alerting and on-call routing |
| Do we know which business workflows fail if Microsoft tenant services degrade | Yes, mapped by process and recovery workaround |
| Have we tested alternate order, shipment, and customer support procedures | Yes, in an exercise that includes security and operations together |
The organizations that answer these well are not necessarily the ones with the biggest budgets. They are the ones that understand that management-plane security is business continuity security.
Not every control in this article is a penetration testing problem. Some are identity governance, procurement, logging, or recovery design problems. But a large portion of the risk is still best surfaced through continuous adversarial validation, especially on the external and workflow-facing side.
That is where a platform like Penligente can fit naturally. If your environment includes customer portals, partner-facing apps, exposed login surfaces, supplier integrations, public assets, forgotten subdomains, API endpoints, or recurring configuration drift, an AI-driven penetration testing platform can help you turn one-time testing into a living validation loop. Instead of treating testing as a quarterly event, you can repeatedly probe for exposure, auth weakness, route changes, exploitable regressions, and newly introduced attack paths across the assets that sit closest to real business operations.
The other advantage is speed of revalidation. After a disruptive event in your sector, you rarely need a philosophical memo. You need to know whether your own internet-facing surface has similar weaknesses today. Continuous validation helps answer that faster than a traditional point-in-time engagement. For teams that need to pressure-test web assets and automate recurring external verification without waiting for a long consulting cycle, that model is increasingly practical.
The deeper lesson of the Stryker cyber attack
The Stryker cyber attack is not important only because it hit a large medical technology company. It is important because it demonstrates how much damage can be done when attackers reach the enterprise control plane rather than just a handful of endpoints. Officially, this was an incident in Stryker’s Microsoft environment. Operationally, it disrupted order processing, manufacturing, and shipping. Strategically, it forced the security community to confront a familiar but uncomfortable reality: a modern enterprise can be crippled without a classic ransomware payload if identity, administration, and device control are compromised. (Stryker)
For data security teams, that means confidentiality is no longer the only headline metric. Integrity and availability failures inside management infrastructure can be just as consequential. For healthcare and medtech leaders, it means product cybersecurity cannot be isolated from supplier resilience, enterprise identity security, and continuity engineering. For security engineers, it means the testing frontier has moved. You still need web application testing and vulnerability management. But you also need recurring validation of administrative blast radius, third-party trust, and recovery realism. (U.S. Food and Drug Administration)
The final takeaway is straightforward. If your organization still treats MDM, EMM, identity governance, and supplier access as “IT operations” rather than first-class attack surfaces, you are under-modeling your risk. The most dangerous control in your environment may be the one your administrators use every day. That is what makes the Stryker incident more than a headline. It is a warning about where enterprise power lives now, and why that power must be tested continuously. (SecurityWeek)
Suggested internal and external links
- Stryker customer update on the March 2026 network disruption
- Reuters coverage of the Stryker cyberattack
- FDA guidance on cybersecurity in medical devices
- HHS Healthcare and Public Health Cybersecurity Performance Goals
- NVD entry for CVE-2025-4428
- NVD entry for CVE-2025-47179
- Microsoft Intune remote device wipe documentation
- Microsoft Entra audit log activity reference
- Penligent main site
- OpenClaw Security Audit, What Actually Breaks When an AI Agent Can Touch Your Files, Tools, and Accounts
- The Future of AI Agent Security, Openclaw Security Audit