Security teams already know to distrust image libraries, archive extractors, template engines, PDF renderers, and office document parsers. Far fewer teams put font build tooling in the same risk bucket. CVE-2025-66034 is a reminder that they should. The vulnerable component is fontTools.varLib, part of the widely used Python fonttools project, and the vulnerable input is a .designspace file that many engineers would not instinctively treat as hostile. The result is not a vague parsing bug. It is a filesystem write primitive with attacker influence over both path and content, and in the wrong deployment that is exactly the kind of primitive that stops being “just a local tool issue” and starts becoming an incident. (NVD)
The public record is unusually clear on the basics. NVD says versions from 4.33.0 up to but not including 4.60.2 are affected, and that the vulnerable path is the fonttools varLib script, or any code path that invokes fontTools.varLib.main(). GitHub’s advisory goes further and says the issue combines unsanitized filename handling with content injection, allowing arbitrary writes to filesystem locations via path traversal and output content injection via XML-controlled fields. That is the core of the bug, and everything else in this article flows from that. (NVD)
There is one more reason this CVE deserves a better article than the usual “upgrade and move on” summary. The public severity picture is split. GitHub, the CNA for the record, assigns a 6.3 Medium score with a local vector, high complexity, and required user interaction. NVD later enriches the same CVE to 9.8 Critical with a network vector and no user interaction. That is not trivia. It is the real story. If you understand why those two scores can coexist, you understand how modern software supply chain vulnerabilities actually behave in production. (NVD)
What CVE-2025-66034 actually is
At a factual level, CVE-2025-66034 affects fontTools.varLib, which is part of the fonttools Python package used for manipulating fonts and building variable fonts from designspace definitions. The official documentation describes varLib as the component that builds variable fonts from a designspace file and its masters. The vulnerable interface is not some obscure internal helper. It is the main() path used by the command-line flow and by programs that call that entry point directly. (PyPI)
That matters because .designspace files are not random blobs. In the font workflow, they are structured XML documents that describe axes, masters, instances, and variable-font outputs. The fontTools designspace documentation explains that the <variable-font> element can include a nome do arquivo attribute telling tools where to store the built font on disk. After the fix, the documentation now explicitly states that this value is intended to be a simple basename or stem only, not an absolute path or relative path, and that build tools will ignore directory separators for security reasons. The reason the docs say that now is simple: before the fix, the code path did not consistently enforce it. (fontTools Documentation)
So the best mental model is not “font parsing bug.” It is “attacker-controlled structured input influenced where a backend build tool wrote an output file.” Once you think in those terms, the bug stops sounding niche. It begins to look like the same class of trust-boundary failure defenders already understand in tar extraction bugs, archive unpackers, markdown renderers, PDF workflows, and CI artifact generators. The file extension changes. The control problem does not. (GitHub)
Why this is a file write bug before it is an RCE bug
A lot of public coverage compresses CVE-2025-66034 into “fontTools RCE.” That headline is understandable because it is short and attention-grabbing, and you do see that framing in visible public pages. But the better engineering description starts one step earlier: this is an arbitrary file write problem that can become RCE when the environment turns that write into execution. That distinction is not semantic hair-splitting. It is how you decide whether your environment is mildly exposed, seriously exposed, or not materially exposed at all. (SentinelOne)
GitHub’s own advisory summary is explicit here. It says the vulnerability exists because of unsanitized filename handling combined with content injection. Attackers can write files to arbitrary filesystem locations via path traversal sequences and inject malicious code into output files through XML injection in labelname elements. The advisory even explains the escalation condition in plain language: when those files are placed in web-accessible locations and executed, the result is remote code execution. In other words, the primitive is write-what-where. The outcome depends on where “where” lands and how the target environment treats the written content. (GitHub)
This is also why the record looks slightly awkward if you try to force it into only one weakness label. NVD carries CWE-91, XML Injection, and MITRE defines that CWE as improper neutralization of special elements used in XML, allowing attackers to modify XML syntax, content, or commands before the XML is processed by an end system. That is part of what is happening here. But operationally, defenders should think about a compound issue: XML-controlled input, path traversal, arbitrary file write, and deployment-specific execution potential. The patch itself makes that obvious. The docs update makes it even more obvious. (NVD)
The exact trust boundary that failed
The upstream patch is one of those rare fixes that tells the whole story in a few lines. Before the fix, the vulnerable code path effectively took vf.filename when present and joined it with an output directory. After the fix, if vf.filename is present, the code first reduces it to os.path.basename(vf.filename) and only then joins it to the output directory. That is not a generic cleanup. It is a direct answer to path traversal. The commit message says it plainly: “only use the basename” to prevent path traversal attacks. (GitHub)
A simplified version of the trust failure looks like this:
# Simplified pre-fix logic
if vf.filename is not None:
filename = vf.filename
else:
filename = vf.name + ".{ext}"
output_path = os.path.join(output_dir, filename)
vf.save(output_path)
And the security hardening looks like this:
# Simplified post-fix logic
if vf.filename is not None:
filename = os.path.basename(vf.filename)
else:
filename = vf.name + ".{ext}"
output_path = os.path.join(output_dir, filename)
vf.save(output_path)
That change is directly reflected in the upstream commit, where the code now strips directory components from vf.filename and the documentation notes that only a basename should be honored. (GitHub)
What failed, then, was not os.path.join() itself. The failed assumption was that a structured input file describing font output metadata could be trusted to carry path-bearing values safely. That assumption is common in build tooling. Engineers treat configuration-like files as if they were authored by friendly tools and reviewed by friendly humans. Attackers treat them as an input surface. CVE-2025-66034 exists in the gap between those two mindsets. (GitHub)
How a designspace file becomes a write primitive
The official designspace documentation says the <variable-font> element’s nome do arquivo attribute tells build tools where to store the built font on disk, and that the filename may include an extension such as .ttf while the build tool may replace that extension as needed. In a benign workflow, that is exactly what you want. In a hostile workflow, that means a malicious input file is influencing output placement. The moment directory separators are honored instead of stripped, the attacker is no longer just naming a font. The attacker is steering a write target. (fontTools Documentation)
GitHub’s advisory PoC text makes the control path concrete without needing to reproduce the full exploit here. The public advisory says attackers can specify a path-traversal sequence in the variable-font nome do arquivo, causing output to land outside the intended directory, and can also inject malicious code into output content through XML-controlled labelname elements. The advisory’s example uses that second channel to show controlled content being written into an output file. That is enough to explain the escalation model without turning this article into an exploitation tutorial. (GitHub)
The important defensive insight is that this was not merely “malformed input crashes parser.” It was “malicious input changes output semantics.” Those are radically different risk classes. Parser crashes are often availability issues. Output-semantic manipulation is what lets attackers influence future system behavior. If the written file lands under a web root, plugin directory, build artifact directory, interpreter search path, or later deployment bundle, then the arbitrary write stops being an isolated corruption event and starts becoming a stepping stone to execution or persistence. That consequence is not speculative; it is the exact condition GitHub describes when it explains how the arbitrary write can turn into RCE. (GitHub)

Why the public score disagreement is real
The split score is the part of this CVE that most shallow writeups get wrong. They either parrot GitHub’s 6.3 Medium or parrot NVD’s 9.8 Critical and act as if the other score is obviously mistaken. The truth is more useful than that. GitHub scored the vulnerability as AV:L/AC:H/PR:N/UI:R/S:C/C:N/I:H/A:L, which assumes a model where a victim processes a malicious file locally, user interaction exists, and the immediate effect is mostly integrity damage with some availability effect. That model fits local tool usage, desktop build workflows, or other contexts where a human or a controlled job explicitly feeds a file to varLib. (NVD)
NVD’s enriched score is AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H, which is a completely different world. The CVMAP notes show how NVD adjusted the assumptions: it treated the vector as network, lowered complexity, removed user interaction, and raised confidentiality and availability impact. NVD’s notes are not saying every installation is directly reachable from the internet by default. They show that the NVD analyst believed the public record was consistent with a network-delivered, automatically processed scenario with no meaningful limiting factors called out. (NVD)
Both models are defensible depending on deployment. If your only use of fontTools is a local designer workstation compiling trusted in-house assets, GitHub’s score may be closer to reality for you. If you run a service or automated job that ingests external designspace content over HTTP, from pull requests, from vendor handoffs, or from customer uploads, the NVD model becomes much easier to justify. In that environment, “local tool invocation” is no longer the operative boundary. The malicious input arrived over the network, the processing was automatic, and the resulting file write may affect data or code that matters. That is why a single CVE can honestly look Medium in one organization and Critical in another. (NVD)
The downstream vendor picture reinforces that point. Ubuntu’s public notice repeats the lower-severity style reasoning and describes the issue as a case where a user or automated system is tricked into processing a specially crafted .designspace file, leading to arbitrary file writes outside the target directory and potentially RCE. IBM, in a product bulletin that includes CVE-2025-66034 among bundled vulnerabilities, adopts the NVD 9.8 score. Those documents do not contradict each other so much as reveal different product assumptions. (Ubuntu)
A practical way to read the score split
The safest way to use the score disagreement is this: treat GitHub’s 6.3 as the minimum credible baseline for any vulnerable environment, and treat NVD’s 9.8 as the upper bound for reachable automated deployments where hostile input crosses a network boundary and the output path can influence meaningful files. If you do not know which side you are on, that uncertainty is itself a reason to investigate reachability and output-path risk before you downgrade the issue mentally. (NVD)
Where this becomes a real incident
The obvious high-risk pattern is a backend service that accepts user-supplied designspace projects and runs fonttools varLib or equivalent code as part of an API workflow. In that architecture, the delivery vector is effectively remote even if the vulnerable function itself is a local Python call. The service receives the malicious designspace file over the network, parses it automatically, and writes outputs to disk without meaningful human review. If the output directory is web-served, synchronized into an asset pipeline, scanned by another service, or otherwise consumed later, the jump from arbitrary file write to RCE or persistence becomes much more realistic. That is the scenario NVD seems to be scoring for. (fontTools Documentation)
The second major pattern is CI and build automation. Security teams often underweight CI exposure because the pipeline is “internal.” But pipelines routinely ingest outside content: pull requests, issue attachments, vendor files, design handoffs, mirrored repositories, and generated assets. If a font build stage processes a malicious .designspace file, the resulting write may target workspace files, cached dependencies, artifact directories, or adjacent paths used in later stages. In a modern chain of build, package, deploy, and publish, poisoning an artifact can be more operationally meaningful than getting a shell on the build worker itself. The advisory does not enumerate every CI abuse case, but the write primitive it describes makes this a straightforward engineering inference. (GitHub)
The third pattern is transitive product exposure. IBM’s bulletin is useful because it proves the vulnerable package was present deeply enough inside a shipped product stack that customers needed notice and remediation. Debian and Ubuntu package trackers tell a similar story from the distribution side. This was not a one-off issue isolated to people manually running font tooling from a terminal. It propagated through packaging ecosystems and product dependencies, which means some organizations may be exposed without ever recognizing that fonttools sits inside their software path. (IBM)
The table below is the most practical risk model for most teams. It consolidates the exploit primitive from the GitHub advisory with distro and product context from Ubuntu, Debian, and IBM. (GitHub)
| Deployment pattern | Likely exposure | Por que é importante |
|---|---|---|
| Local designer workstation, trusted inputs only | Inferior | Trigger usually requires handling a malicious .designspace file in an otherwise controlled workflow |
| CI job processing external design assets | Medium to high | Arbitrary file write can poison workspace files, artifacts, or later deployment outputs |
| Backend API or SaaS font generation service | Alta | Malicious designspace arrives over the network and may be processed automatically |
| Output path under web root or executable path | Critical in practice | Arbitrary file write can become code execution when the written file is later interpreted or executed |
| Transitive dependency inside larger product | Variable but meaningful | Exposure depends on whether the vulnerable path is reachable, not just whether the package is present |

What the fix tells us about the vulnerability class
One reason this bug is worth studying is that the remediation is almost embarrassingly simple. The main code fix is to use basename(vf.filename) and ignore directory separators. The documentation now says the nome do arquivo is intended to be a simple basename or stem only, and the release notes explicitly tie that change to the CVE. That combination tells you something broader than “patch applied.” It tells you the project maintainers now consider the designspace filename field a non-authoritative leaf name, not a path instruction. That is a trust-boundary decision, not just a bug fix. (GitHub)
Security engineers should learn from that design choice. If you process structured inputs that describe outputs, do not let the input specify directory structure unless you have a compelling reason and robust validation. Use generated filenames, map inputs to opaque IDs, or normalize to leaf names before any join operation. If you must preserve path semantics, force the result back under an allowlisted root and fail closed when canonicalization escapes it. CVE-2025-66034 is a textbook example of why “it’s just metadata” is not a security control. (GitHub)
How to tell whether your stack is actually exposed
The fastest way to mis-handle CVE-2025-66034 is to stop at version checking. Version checking matters, but it only answers one question: “Could the vulnerable code be present?” It does not answer the question you actually care about: “Can hostile input reach the vulnerable path in a meaningful way?” The official sources give enough information to define a four-part exposure test. You need to know whether a vulnerable fonttools version exists, whether fontTools.varLib.main() is reachable, whether untrusted .designspace content crosses that path, and whether the output directory matters. (NVD)
Start with dependency inventory. OSV lists the affected upstream version range and provides downstream references for Ubuntu and Debian. Debian’s tracker shows bullseye and bookworm still marked vulnerable at the time of the current public record, while trixie and unstable have fixes. Ubuntu’s notice shows fixes for 24.04 LTS, 25.04, and 25.10, with 24.04 delivered through Ubuntu Pro ESM for the package in question. PyPI shows 4.60.2 exists and was released on December 9, 2025 as the security backport, while 4.61.0 carried the original security fix on November 28, 2025. (OSV)
Then check code reachability. The official documentation and NVD record both say the affected path is fontTools.varLib.main(), which means you should not only search for fonttools varLib shell invocations but also direct Python imports and wrappers around that entry point. A simple source sweep like the one below is often enough to identify the first set of likely reachability points. The facts that justify these patterns come directly from NVD and the upstream docs, which identify the vulnerable path and CLI behavior. (NVD)
rg -n "fontTools\.varLib\.main|fonttools varLib|varLib\.main" .
rg -n "designspace" .
rg -n "subprocess.*fonttools" .
That search only tells you where the code is referenced. The next step is trust-boundary review. Ask whether those references can process designspace files that were uploaded by users, pulled from external repositories, handed off by design vendors, attached to tickets, or generated in partially untrusted workflows. If the answer is no, you may still need to patch, but your immediate exploitability is lower. If the answer is yes, the issue becomes much more urgent because GitHub’s advisory specifically ties exploitation to malicious .designspace processing and content injection from XML-controlled fields. (GitHub)
The final step is output-path review. A write primitive only becomes truly dangerous when the written file lands somewhere operationally meaningful. That could be a web-served asset directory, a plugin path, a package build output, a later deployment bundle, or a directory watched by another service. This is where many organizations get surprised. They correctly identify a vulnerable package and even a reachable function, then assume the risk is contained because the worker itself is “not public.” But if that worker writes artifacts that other systems trust, the downstream blast radius can be much larger than the original compute node. (GitHub)
A better checklist than “do we have the package”
The following checklist is the one I would actually use in an engineering review. It is derived directly from the public record, but it forces the conversation away from abstract CVE severity and into concrete reachability. (NVD)
| Pergunta | Por que é importante |
|---|---|
Do we run a vulnerable fonttools version | No vulnerable package, no vulnerable path |
Do we invoke fontTools.varLib.main() or the CLI | The official record says that is the affected code path |
Can untrusted .designspace content reach it | Without hostile input, practical exposure may be limited |
| Does the process have filesystem access beyond a scratch directory | Arbitrary write needs meaningful targets to matter |
| Are outputs later interpreted, deployed, or served | This is where arbitrary write turns into execution or persistence |

Patch paths and version traps
The upstream answer is straightforward: upgrade to 4.60.2 or later, or to a later mainline release such as 4.61.0 or beyond. The release notes show that 4.61.0 introduced the security fix and that 4.60.2 was the backport release created specifically so downstream projects still on Python 3.9 could receive the fix without taking the Python support change bundled into 4.61.0. PyPI confirms that 4.60.2 was released on December 9, 2025 and that newer releases now exist. (GitHub)
That last point matters because some early public discussion briefly confused people about whether 4.60.2 actually existed. As of the current public record, it does. If you are pinning directly from PyPI, pip install fonttools==4.60.2 is a valid release path, and any later fixed version is also acceptable from a vulnerability standpoint. (PyPI)
Distro packages require more care. Ubuntu’s notice shows that the issue affected Ubuntu 24.04 LTS, 25.04, and 25.10 for this CVE, with patched package versions including 4.55.3-2ubuntu0.25.10.1 e 4.55.3-2ubuntu0.25.04.1, while 24.04 LTS receives the fix through Ubuntu Pro ESM Apps as 4.46.0-1ubuntu0.1~esm1. That means version comparison against upstream alone can be misleading. A distro package with a numerically lower version may still be fixed because the patch has been backported. (Ubuntu)
Debian is even more useful for illustrating the same point. The Debian tracker shows trixie fixed at 4.57.0-1+deb13u1 and unstable fixed in 4.61.1-1, while bullseye and bookworm remain marked vulnerable with no DSA at the time of the public tracker entry. Again, the important lesson is not “only 4.60.2 is safe.” The important lesson is “know whether your exact package build contains the patch.” Upstream version strings are not the whole story in distro land. (Debian Security Tracker)
For Python application teams, the cleanest fix path usually looks like this:
python -m pip install --upgrade "fonttools>=4.60.2"
python - <<'PY'
import fontTools
print(fontTools.__version__)
PY
For distro-managed hosts, the safer path is to use your normal package update workflow and verify against the distro advisory rather than forcing a pip install into the system Python. Ubuntu and Debian both publish enough package-level detail to support that review. (Ubuntu)
Defense in depth matters more than the patch headline
Patching is necessary. It is not sufficient as a general design response. The right lesson from CVE-2025-66034 is that processors for structured design assets should be treated as untrusted-content handlers. If your service accepts external designspace files, run the worker with the narrowest practical filesystem permissions. Keep outputs in a dedicated scratch directory. Do not colocate build outputs with web roots, plugin directories, or deployment bundles. Do not grant the worker outbound network access unless it genuinely needs it. And if you can, run the conversion stage in an isolated container or sandbox that can be destroyed after one job. Those recommendations follow directly from the nature of the write primitive and from the fact that a malicious file must be processed to trigger the issue. (GitHub)
A minimal container hardening pattern for this class of workflow might look like this:
apiVersion: v1
kind: Pod
metadata:
name: font-build-worker
spec:
containers:
- name: worker
image: your-font-build-image
securityContext:
runAsNonRoot: true
readOnlyRootFilesystem: true
allowPrivilegeEscalation: false
volumeMounts:
- name: scratch
mountPath: /work/output
volumes:
- name: scratch
emptyDir: {}
That snippet is not a silver bullet, and it is not specific to fontTools. It is a reminder that when you process hostile content, the worker should not have broad write privileges anywhere that matters. CVE-2025-66034 is a clean demonstration of why. The patch removes one path traversal opportunity. Isolation limits the damage if a future parser or build-stage bug appears somewhere else in the same chain. (GitHub)
Detection and telemetry that are actually useful
A lot of defensive advice around library CVEs is too generic to help. “Monitor for suspicious behavior” is not enough. For this issue, the telemetry question is more specific: did a process handling a .designspace file write outside its expected output directory, or write content that should never appear in a generated font artifact? The advisory, patch, and docs tell you exactly where to focus. (GitHub)
The first detection layer is input review. You do not need to reproduce the public PoC to know what suspicious values look like. Review .designspace files for path traversal patterns in variable-font nome do arquivo fields, absolute paths, Windows drive prefixes, or any path semantics that go beyond a simple basename or stem. The patched documentation now says directory separators should effectively be ignored for security reasons, so any such input should already be treated as suspicious in your pipeline. (fontTools Documentation)
A simple repository or artifact scan can catch many cases before execution:
rg -n '<variable-font[^>]*filename="[^"]*(\.\./|/|\\|[A-Za-z]:\\)' .
rg -n '<labelname' .
That does not prove exploitation. It gives you a triage queue. A benign project may still contain odd-looking metadata. But a production pipeline that accepts external designspace input should not ignore path-bearing filenames casually, because the upstream fix exists precisely to stop honoring that input. (fontTools Documentation)
The second detection layer is filesystem telemetry. If you can log worker writes, alert on build jobs that write outside their designated output root. This is the most directly relevant behavioral signal because the public record says the vulnerable action is an arbitrary file write outside the target directory. Even basic EDR or auditd-style monitoring on conversion workers can be useful if scoped to “font build process wrote outside scratch path.” (Ubuntu)
The third detection layer is application-layer reachability review. Search logs for endpoints or jobs that accepted .designspace uploads or references. If the worker sits behind an HTTP service, correlate upload events with filesystem writes and with any follow-on execution or deployment stages. This is where NVD’s higher-severity model becomes operationally relevant: once the hostile file arrives over the network and triggers automated processing, the distinction between local tool bug and remote service issue starts to disappear. (NVD)

Incident response questions worth asking
If you discover that you were vulnerable, the first question is not “was there public mass exploitation.” The public record I reviewed does not establish that, and this article is not going to pretend otherwise. The first question is narrower and more actionable: did untrusted .designspace files reach the vulnerable path before you patched? If not, you likely have a patching event, not an incident. If yes, the next question is whether those jobs could write anywhere beyond a disposable scratch directory. (NVD)
Then ask what directories the worker could touch and what systems consumed those outputs. If the answer is “only an isolated temp directory cleared after each job,” your retrospective may be short. If the answer is “artifact directory later packaged and deployed,” “directory under web-served assets,” or “path read by later build steps,” you need a more serious review. That is the exact chain GitHub’s advisory is warning about when it describes the path from arbitrary write to RCE through execution of written content. (GitHub)
For organizations with centralized logging, a good retrospective query often looks like: jobs processing designspace content, correlated with filesystem writes outside the expected root, followed by file reads, deployments, or process execution involving those paths. The patch and documentation tell you what the legitimate path model should have been. Any historical deviation from that model deserves attention. (GitHub)
Related CVEs that make this bug more important, not less
CVE-2025-66034 is easier to misjudge if you view it in isolation. It looks like a quirky issue in a specialized library. But fontTools already had another significant XML-related vulnerability, CVE-2023-45139. NVD describes that earlier issue as an XML External Entity problem in the subsetting module that could allow attackers to resolve arbitrary entities when parsing OT-SVG font content, potentially including arbitrary files from the filesystem or making outbound web requests. GitHub’s advisory for that issue marks the affected versions as >= 4.28.2, < 4.43.0 and assigns a High 7.5 severity. (NVD)
The point is not that the two CVEs are identical. They are not. The point is that both vulnerabilities sit in the same broader family: structured, attacker-influenced font-related data crossing into privileged backend processing paths. CVE-2023-45139 is about XXE and parser trust. CVE-2025-66034 is about path-bearing output metadata and content injection. Together they make a stronger case for treating font-processing infrastructure as part of the untrusted-content attack surface rather than as a harmless build utility. Ubuntu’s 2025 notice even fixes both issues in the same broader fontTools security context, which underscores the continuity. (NVD)
There is also a more general software engineering lesson here. Any system that takes structured input describing what to generate e where to place it is a candidate for this class of failure. Archive extractors, code generators, templating engines, report builders, static site generators, package unpackers, and font pipelines all sit in that zone. They feel different because their file formats and user communities differ. They are not different from the perspective of trust boundaries. (CWE)
The table below is a useful comparison lens. It is not saying these are the same bug. It is showing the design pattern defenders should recognize. The factual rows on fontTools come from the official records for CVE-2025-66034 and CVE-2023-45139. (NVD)
| CVE | Componente | Falha central | Immediate primitive | Why defenders should care |
|---|---|---|---|---|
| CVE-2025-66034 | fontTools.varLib | Unsanitized filename handling plus XML-controlled content injection | Arbitrary file write | Can become RCE when written output lands in an executable or trusted path |
| CVE-2023-45139 | fontTools subsetting module | XML External Entity handling in OT-SVG parsing | File inclusion and outbound requests | Proves font tooling belongs in the untrusted parser threat model |
Turning a CVE into validated evidence
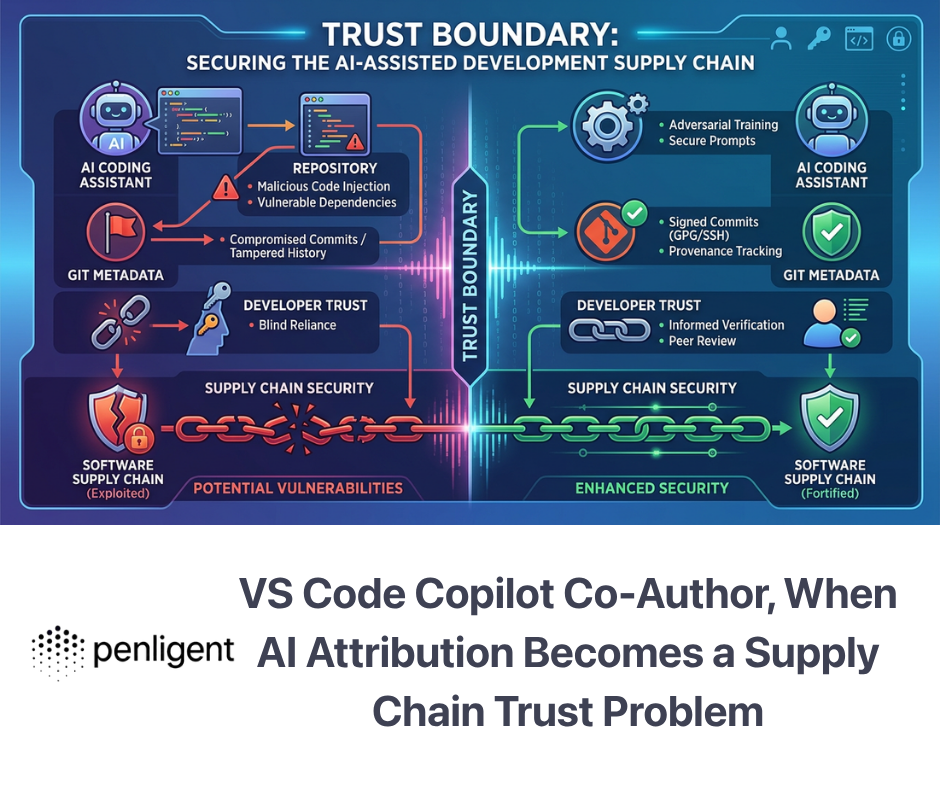
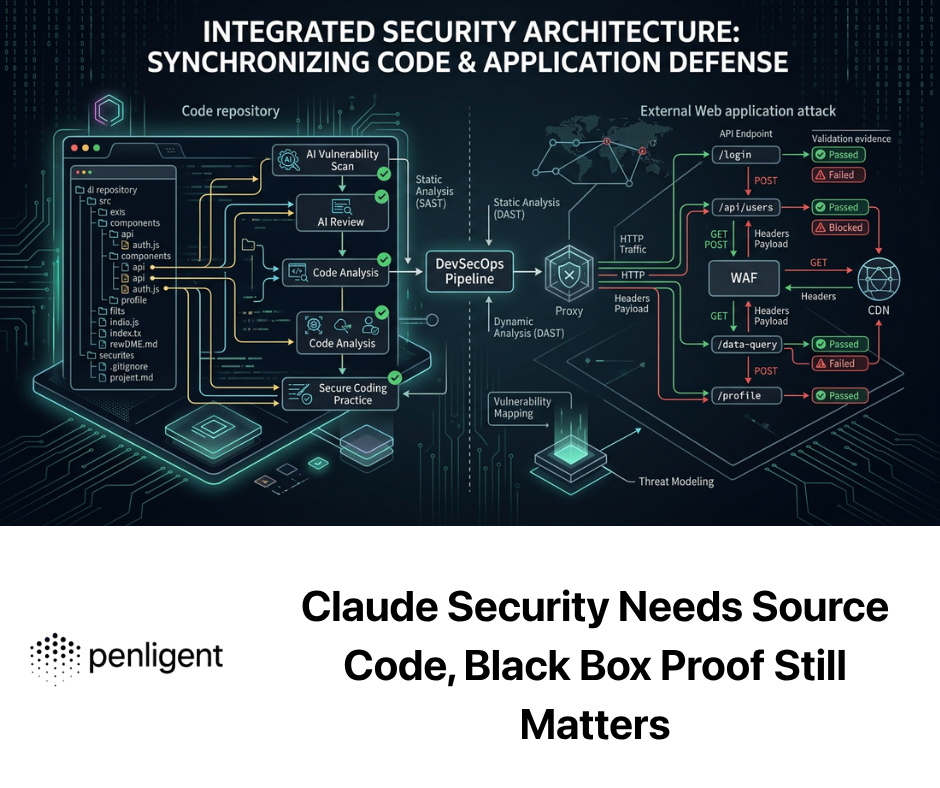
This is the natural place to talk about Penligent without forcing it. CVE-2025-66034 is exactly the kind of issue that exposes the gap between dependency awareness e exploitability awareness. A package scanner can tell you that fonttools is present. A human reviewer can tell you the advisory says arbitrary file write. What most teams still struggle to answer quickly is the operational question: does my application actually accept the relevant file type, reach the vulnerable code path, write outside the intended directory, and land somewhere meaningful? (GitHub)
That is where an AI-driven validation workflow is genuinely useful. Penligent’s public product and documentation pages position it as an AI-powered penetration testing platform that can run testing workflows from a task-oriented interface, and its broader published material repeatedly emphasizes moving from raw findings to validated attack paths and reproducible evidence. For a CVE like this, the value is not in shouting “Critical” louder. The value is in proving or disproving the reachability chain in your own environment. (Penligente)
Used well, a platform like that helps answer four defensible questions: where the vulnerable component exists, whether the dangerous path is actually invoked, whether untrusted input can cross that boundary, and whether the resulting write can touch anything that matters. That is the right operational standard for CVE-2025-66034. The public score disagreement already tells you that environment is everything. Validation is how you figure out which environment you are actually living in. (NVD)
The most important engineering takeaway
CVE-2025-66034 matters because it compresses several modern security lessons into one small-looking bug. First, specialized build tooling is still part of your attack surface. Second, structured design files are not inherently safer than “executable” file types when a backend service interprets them and writes outputs on their behalf. Third, CVSS arguments are often really deployment arguments in disguise. The GitHub 6.3 and NVD 9.8 split is not noise. It is a warning that you should stop asking “what is the score” and start asking “what assumptions does this score depend on.” (NVD)
The official record gives you a complete enough response plan. The affected path is known. The upstream fix is known. The release backport is known. The documentation now states the correct security boundary. The distro guidance exists. The downstream product evidence exists. What remains is the work only you can do: map reachability, isolate workers, verify where outputs land, and decide whether this was a patching event or an incident in your environment. (GitHub)
If you reduce CVE-2025-66034 to a single sentence, make it this one: a malicious designspace file should never have been able to tell your backend where to write a generated file, and once it could, everything else became a question of environment. That is why this bug is worth understanding in detail, and why teams that only patch version strings without checking reachability are still leaving the hard part undone. (GitHub)
Leitura adicional
- NVD entry for CVE-2025-66034
- GitHub advisory, GHSA-768j-98cg-p3fv
- Upstream patch commit
- fontTools designspace documentation
- fonttools 4.60.2 on PyPI
- Ubuntu notice USN-7917-1
- Debian tracker for CVE-2025-66034
- OSV record for CVE-2025-66034
- IBM bulletin showing downstream product impact
- NVD entry for related CVE-2023-45139
- GitHub advisory for CVE-2023-45139
- CVE-2025-66034, When fontTools varLib Turns a Designspace File Into a Write Primitive
- CVE-2025-66034, Why a Font Build Tool Turned Into a Real Code Execution Risk
- CVE-2025-4517, The Python Tar Extraction Bug That Breaks Trust Boundaries in Real Automation
- Pentest AI Tools in 2026, What Actually Works, What Breaks
- Ferramenta AI Pentest, como será a verdadeira ofensa automatizada em 2026