The most important technical detail in the LiteLLM incident was not simply that two PyPI versions were malicious. It was that one of them used a Python startup hook. LiteLLM’s own incident materials say 1.82.7 carried a malicious payload in litellm/proxy/proxy_server.py, while 1.82.8 added litellm_init.pth, making the package capable of executing code at Python startup without an explicit import litellm. Python’s site documentation is clear about why that matters: lines beginning with import inside a .pth file are executed at every Python startup. (LiteLLM)
That changed the security meaning of the event. A poisoned dependency that triggers only when a specific module is imported is one class of problem. A poisoned dependency that turns ordinary interpreter startup into an execution path is another. MITRE now documents Python Startup Hooks as ATT&CK sub-technique T1546.018, describing abuse of Python startup mechanisms on Linux, Windows, and macOS for persistence and execution. The LiteLLM incident was therefore not just “another malicious package on PyPI.” It was a live example of a now-recognized adversary technique delivered through a trusted registry path. (MITRE ATT&CK)
The second reason this incident matters beyond LiteLLM itself is architectural. LiteLLM is not a cosmetic wrapper. Its own PyPI page and docs position it as both a Python SDK and a centralized LLM gateway, with authentication and authorization, multi-tenant spend tracking, per-project logging and guardrails, virtual keys, and MCP gateway capabilities with permission controls by key, team, or organization. In many real deployments, that means the package sits close to provider API keys, routing policy, usage logs, tenant isolation, and tool-access boundaries. Compromise a component in that position and the attacker may not just steal “a key.” They may steal a control surface. (PyPI)
This is why the LiteLLM event deserves to be read as a release-security case study, not only as an incident-response story. The immediate response work is obvious and urgent: rotate secrets, hunt for litellm_init.pth, check for contact with models.litellm.cloud, and audit where 1.82.7 or 1.82.8 landed. LiteLLM’s official guidance says exactly that. But once those steps are done, the harder question remains: what should Python release and install practices look like when a single package can bridge model access, team budgets, MCP tools, and cloud credentials? (LiteLLM)
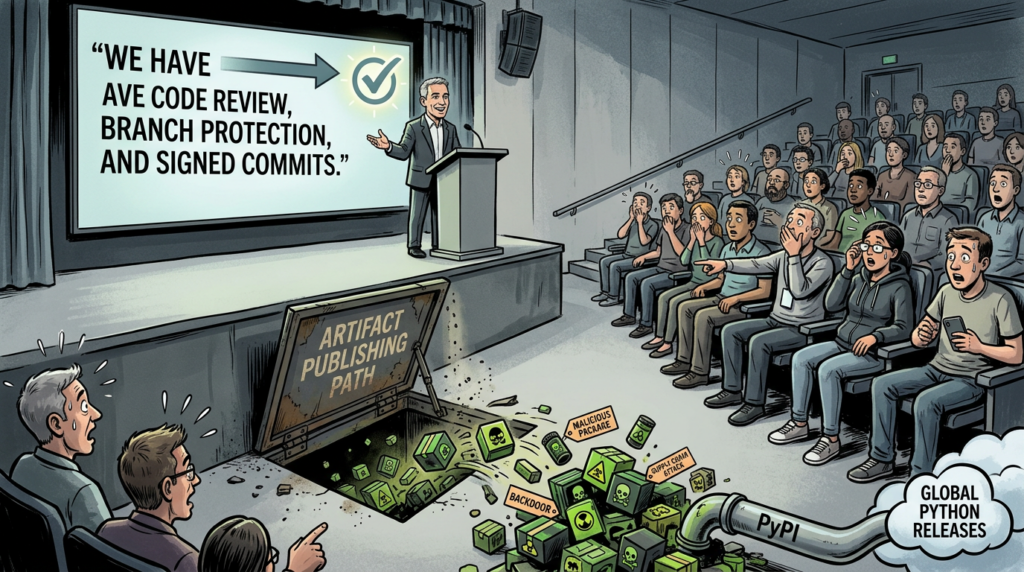
The LiteLLM incident was about artifacts, not just source code
LiteLLM’s incident thread says the malicious versions were published to PyPI but were never released through the project’s official GitHub CI/CD flow, and that GitHub releases only went up to v1.82.6.dev1 while 1.82.7 and 1.82.8 appeared directly on PyPI. That matters because it breaks a habit many engineering teams still have: they look first at repository history and assume artifact integrity follows from repository integrity. In this case, the repository view and the published-artifact view diverged. The artifact was the attack surface. (GitHub)
That divergence should permanently change how Python teams think about trust. A clean Git tree does not prove a clean wheel. A signed commit does not prove a clean upload. A tagged release process does not protect you if packages can be published outside that path. In the LiteLLM case, the project’s official update says the malicious packages were 1.82.7 and 1.82.8, both removed from PyPI after discovery, while the currently visible latest version on PyPI is 1.82.6. PyPI’s project page and file details also show that 1.82.6 was uploaded with twine and that Trusted Publishing was not used for that file. That does not prove causation by itself, but it does show how much publish-path trust still depends on credential handling in many Python projects. (LiteLLM)
The broader lesson is simple: source provenance and artifact provenance are related, but they are not the same control. Security review that stops at code review is incomplete for any project distributing release artifacts through a public index. The artifact itself, the upload path, and the identity that produced it all need to be part of the trust model.
Python .pth files moved from obscure packaging detail to frontline security concern
Python’s official site documentation says .pth files can extend sys.path, but it also says something more important: lines beginning with import are executed, and an executable line in a .pth file runs at every Python startup whether or not the associated module is otherwise used. The docs even note that this behavior is intentionally constrained to discourage complex logic there. That warning looks academic until an attacker decides to live inside exactly that mechanism. (Python documentation)
LiteLLM 1.82.8 turned that mechanism into the story. The original GitHub issue states that the wheel contained litellm_init.pth, 34,628 bytes long, and that the file was listed in the package’s own RECORD. The follow-up issue summarized the trigger difference in one line: 1.82.7 fired on import litellm.proxy, while 1.82.8 could run on any Python startup, no import needed. That is a technical shift with operational consequences. It means package review cannot stop at “what code does our app import.” It has to ask “what code can this environment execute before our app even starts.” (GitHub)
Once that clicks, several blue-team implications follow. site-packages is no longer just a dependency directory; it is part of the execution surface. .pth, sitecustomize.py, and usercustomize.py become first-class hunt targets. Python interpreter startup becomes an event worth correlating with unexpected network activity. Build agents, developer laptops, and ephemeral runners all become more interesting because Python is everywhere in modern automation, not just in long-lived application services. MITRE’s classification of Python Startup Hooks as a persistence and privilege-escalation sub-technique is a useful reminder that this is not a one-off trick. It is a reusable technique with broad platform coverage. (MITRE ATT&CK)
That alone is enough to justify a process change inside many organizations. If your endpoint or server monitoring does not already watch for new .pth files under site-packages and dist-packages, that gap is now material. If your release review cannot answer which wheels were installed, from which index, on which hosts, during which build window, that gap is material too.
AI gateways make supply-chain compromise more dangerous than package counts suggest
A supply-chain incident is not only about how many environments resolved a bad package. It is about what that package is positioned to see. LiteLLM’s own docs describe a centralized API gateway with auth, spend management, virtual keys, logging, guardrails, and an MCP gateway that can restrict tool access by key, team, or organization. The PyPI project page likewise describes it as a unified interface for 100-plus LLMs, available as either a gateway or a Python SDK. That combination makes LiteLLM a much more consequential target than a typical utility dependency. (LiteLLM)
LiteLLM’s official advisory says the malicious versions harvested environment variables, SSH keys, cloud-provider credentials for AWS, GCP, and Azure, Kubernetes tokens, and database passwords, then exfiltrated data to models.litellm.cloud, which the project says is not an official LiteLLM or BerriAI domain. That target list makes sense precisely because LiteLLM often lives where gateway secrets, provider credentials, cluster credentials, and admin material coexist. The malware did not need a perfect understanding of each victim’s architecture. It only needed to search where gateway-class software naturally lives. (LiteLLM)
This changes how engineering teams should rank dependency risk. The right ranking is not “most popular package first.” It is “most privileged package first.” A package that arbitrates access to OpenAI, Anthropic, Azure OpenAI, Bedrock, Vertex, or MCP tools deserves a higher trust bar than a package with the same download count that only formats strings or parses dates. The consequence is concrete: gateway-class dependencies should be treated more like identity infrastructure than like ordinary application libraries.
That same logic also explains why LiteLLM’s official unaffected guidance is so revealing. The project says LiteLLM Cloud users were not affected, source installs from GitHub were not affected, and users of the official ghcr.io/berriai/litellm Docker image were not affected because that deployment path pins dependencies in requirements.txt and does not rely on the compromised PyPI packages. That is not only a helpful scoping note. It is a real-world demonstration that distribution path and dependency determinism can sharply change exposure, even when the application code is nominally the same. (LiteLLM)

Exact pins, compatible specifiers, and the false comfort of “we pinned it”
Many Python teams overestimate how much safety they get from version constraints. PyPA’s version-specifier documentation says the compatible-release operator ~= is intended to allow later releases that are expected to remain compatible. The Python Packaging User Guide gives the rough equivalence name ~= X.Y ≈ name >= X.Y, == X.*. That means a requirement that looks narrow to a human may still accept newly published patch releases. (Python Packaging)
Applied to the LiteLLM case, the difference is not theoretical:
litellm
litellm>=1.82.6
litellm~=1.82.6
litellm==1.82.*
All four patterns can drift into 1.82.7 or 1.82.8. Only an exact pin such as the following excludes those releases:
litellm==1.82.6
The important part is not memorizing one incident’s numbers. It is recognizing the category error. Many teams say “pinned” when they actually mean “bounded loosely enough to keep receiving new patch releases.” In routine operations that may feel efficient. During a malicious release event, it is the difference between deterministic deployment and accidental ingestion. PyPA’s specifier rules are explicit enough that teams should encode this distinction in policy rather than leaving it to convention. (Python Packaging)
Even exact pins are only a partial answer. They prevent resolver drift, but they do not verify the artifact itself. If a build system resolves from a public index and trusts whatever archive corresponds to the pinned version name, the security guarantee still depends on the integrity of the registry path, archive metadata, and your own download process. That is why the next control matters more than many teams realize.
Hash-checked installs are the minimum artifact-trust baseline most teams still skip
Pip’s secure-install documentation says --require-hashes forces hash checking mode and is useful in deploy scripts to ensure the requirements file author provided hashes. The pip install reference says --require-hashes requires a hash for each requirement for repeatable installs, and pip hash exists specifically to compute digests for use in hash-checking mode. pip-tools adds a practical workflow on top of that with pip-compile --generate-hashes. None of this is exotic. It is mainstream tooling that many teams still leave off the table. (pip)
A safer install path looks more like this:
pip-compile --generate-hashes requirements.in
pip install --require-hashes -r requirements.txt
And the resulting requirement line looks more like this:
litellm==1.82.6 \
--hash=sha256:164a3ef3e19f309e3cabc199bef3d2045212712fefdfa25fc7f75884a5b5b205
PyPI’s current file metadata for litellm-1.82.6-py3-none-any.whl publishes that SHA256, which makes the example concrete rather than abstract. The value of hash checking is not that it solves every supply-chain problem. It does not. Its value is that it collapses silent artifact drift. An unexpected wheel, a replaced archive, or a mismatched source-versus-wheel fetch stops being invisible. The installation fails loudly. (PyPI)
That kind of failure is exactly what you want in production and CI. Attackers win when dependency resolution is quiet, normal-looking, and easy to rationalize after the fact. Hash-checked installs turn one large class of ambiguity into an error condition. For teams operating AI gateways, agent runtimes, or MCP infrastructure, that is not packaging perfectionism. It is control-plane hygiene.

Trusted Publishing changes who is allowed to publish, not just how convenient publishing feels
PyPI’s Trusted Publishing documentation describes the model directly: use OpenID Connect to exchange short-lived identity tokens between an external service and PyPI, eliminating the need for manually generated API tokens in automated environments. GitHub’s official OIDC guidance for PyPI says you configure a trust relationship that binds a PyPI project to a specific repository and workflow, and it warns that assigning the wrong repository or workflow is equivalent to sharing an API token. PyPI’s own usage docs say the process retrieves an OIDC token, exchanges it for a short-lived API key, and then uses that key for the upload, with id-token: write required in GitHub Actions. (PyPI Docs)
That is a meaningful change in trust structure. Long-lived publish tokens are portable secrets. They can be copied, reused outside the intended workflow, and often outlive the people or jobs that first needed them. Trusted Publishing narrows that model by binding publishing to a specific workflow identity and minting short-lived credentials on demand. That does not make release compromise impossible, but it raises the bar and makes the allowed publish path far more explicit. (PyPI Docs)
A minimal GitHub Actions release job therefore looks more like this:
name: release
on:
release:
types: [published]
jobs:
publish:
runs-on: ubuntu-latest
permissions:
id-token: write
steps:
- uses: actions/checkout@v4
- uses: actions/setup-python@v5
with:
python-version: "3.12"
- run: python -m pip install -U build
- run: python -m build
- uses: pypa/gh-action-pypi-publish@release/v1
The exact YAML depends on your workflow, but the security principle does not. A publish action should be bound to one repository, one workflow, and preferably one protected environment with explicit deployment rules. GitHub’s own guidance recommends adding environment protection rules when environments are used in workflows or OIDC policies, so branch and tag controls become part of the release trust boundary as well. (GitHub Docs)
The LiteLLM case makes the contrast easy to understand. At the time of writing, PyPI file metadata for LiteLLM 1.82.6 says “Uploaded using Trusted Publishing? No” and shows an upload via twine. Again, that does not retroactively explain the compromise by itself, but it shows that many important Python projects still live in a release model where portable publish credentials remain relevant. The lesson is not “every incident is caused by lack of OIDC.” The lesson is “publish identity should be bound as tightly as possible to the workflow that is supposed to publish.” (PyPI)
Build once, verify once, promote many is a better pattern than live resolution everywhere
A public package index is a distribution channel, not a safe-room guarantee. The more often a build pipeline resolves directly from the live public index, the more often that pipeline reopens the registry trust question. That is especially risky when the same pipeline also holds deployment credentials, registry access, or other secrets worth stealing. LiteLLM’s official guidance explicitly told users to audit local environments, CI/CD pipelines, Docker builds, and deployment logs for 1.82.7 and 1.82.8, which is an unusually direct reminder that packaging risk and pipeline risk are intertwined. (LiteLLM)
The more resilient pattern is to resolve once in a controlled path, lock exact versions and hashes, build artifacts from that resolved set, verify them, and then promote those same artifacts forward. The goal is not total immutability for its own sake. The goal is to reduce surprise. When a malicious release appears, you want to answer a binary question: “Did our promotion path ever ingest that artifact?” That is much easier when the organization has one resolution point than when every team, Dockerfile, and ephemeral runner performs fresh live resolution from the public index.
This is also where release security meets offensive validation in a useful, non-marketing way. After a supply-chain event, some teams need to verify whether an exposed host or gateway actually allowed lateral movement, secret abuse, or reachable downstream compromise. In that narrower validation phase, tooling that can reproduce installation paths, simulate post-compromise flows, and preserve evidence can be useful. Penligent’s published material on automated pentesting and evidence-driven offensive workflows is relevant in that context. The point is not that attack validation replaces package trust controls. It is that once a release-path failure happens, controlled validation helps answer what the compromised environment could really reach. (Penligent)
The right comparison is not only a CVE, but CVE-2024-3094 still teaches the right lesson
The best known recent comparison is CVE-2024-3094, the xz backdoor. NVD describes that issue as malicious code in upstream xz tarballs beginning with version 5.6.0, where the build process extracted a prebuilt object file from a disguised test file and modified library behavior during build. The important commonality is not the implementation detail. It is the trust failure. In both xz and LiteLLM, the danger came from malicious content riding a trusted software-distribution path rather than from a normal bug being exploited through an exposed application endpoint. (NVD)
The difference is still worth spelling out. In xz, the compromise affected the upstream release material and then altered the build chain and linked software. In LiteLLM, the compromise affected PyPI artifacts, and in 1.82.8 it specifically abused a documented Python startup mechanism. One case rode the build path. The other rode the install and startup path. But both show the same strategic truth: once a trusted software-distribution boundary is compromised, ordinary patch-management instincts are not enough. You need artifact trust, workflow-bound publishing, and deterministic consumption. (NVD)
It is also useful to compare the March 2026 malicious-package event with an ordinary LiteLLM vulnerability. NVD’s CVE-2025-45809 describes a SQL injection issue in LiteLLM before 1.81.0 involving the /key/block and /key/unblock endpoints. That is the traditional model: a product flaw in application logic, a known affected version range, and a patch path. The malicious-package incident is fundamentally different. The package artifact itself became the attack vehicle. That is why remediation has to include credential rotation, artifact review, and release-path hardening, not just “upgrade to a safe version.” (NVD)
What should change after LiteLLM, even for teams that never used LiteLLM
The first change is cultural. Python packaging details like .pth execution, hash-checking mode, and OIDC-based publishing are not niche release-engineering trivia anymore. They are part of production security. If your organization depends on Python for CI, infrastructure automation, agent tooling, model gateways, data processing, or platform glue, then Python startup behavior and Python release trust belong in security review, not just in packaging docs.
The second change is architectural. Dependencies that sit in front of external AI providers, route requests across models, issue virtual keys, or expose MCP tools should be treated as privileged control-plane software. They deserve stricter install policy, stricter artifact trust, and tighter runtime monitoring than ordinary leaf dependencies. LiteLLM’s public feature set makes that case directly. Other gateway-style AI components should be evaluated by the same standard. (LiteLLM)
The third change is procedural. “Pinned” should mean exact version plus hash, not “probably narrow enough.” “Release automation” should mean workflow-bound identity with short-lived publish credentials, not “a token lives somewhere in CI.” “Install verification” should include artifact provenance and startup-hook visibility, not just dependency names and repository commits. None of that eliminates risk, but it closes several doors that supply-chain attackers currently walk through with too little resistance. (PyPI Docs)
The fourth change is operational. Blue teams should add Python startup hooks to their normal hunt vocabulary. If a package can arrange execution before the application even imports its own code, then .pth, sitecustomize.py, and usercustomize.py are not edge cases anymore. They are execution surfaces. MITRE’s ATT&CK entry exists because defenders need a stable way to reason about that behavior across incidents and platforms. (MITRE ATT&CK)
Related reading and references
LiteLLM’s official incident update remains the primary source for affected versions, official impact boundaries, IoCs, and immediate guidance. The two GitHub issues are still the best public references for the startup-hook detail, the proxy_server.py trigger in 1.82.7, and the direct-to-PyPI release-path explanation. (LiteLLM)
For Python-specific background, the official site documentation is the key reference for how .pth files behave. For package consumption, the Python Packaging User Guide version-specifier docs, pip’s secure-install guidance, pip install --require-hashes, and pip-tools --generate-hashes are the practical references most teams should use to turn this incident into a policy change. (Python documentation)
For release security, PyPI’s Trusted Publishing documentation and GitHub’s OIDC guidance for PyPI are the most relevant official references. For ATT&CK mapping, use T1546.018. For a comparable supply-chain case study, read CVE-2024-3094. For contrast with an ordinary LiteLLM product flaw rather than a malicious artifact, read CVE-2025-45809. (PyPI Docs)
For internal reading on Penligent that fits this topic naturally, the most relevant pages are the existing LiteLLM incident-response article, the article on why agent skills became a supply-chain boundary, the overview of Penligent’s automated penetration-testing workflow, and the article on what a real AI pentest tool should actually do in practice. (Penligent)
The lasting lesson from LiteLLM is not only that a popular package was compromised. It is that Python startup behavior, release identity, artifact verification, and AI gateway placement all belong to the same trust story now. Teams that still treat them as separate concerns are leaving attackers too much room between “we reviewed the code” and “we trusted the thing that actually ran.”