Authentication libraries rarely get treated with the same urgency as exposed admin panels, deserialization sinks, or remote code execution bugs. That is a mistake. In a modern Java environment, the authentication layer is often the shortest path to full compromise. If the code that validates identity can be tricked into trusting an attacker-controlled token, every authorization check downstream becomes decoration. That is why pac4j deserves more attention than it usually gets. It is not just another framework dependency. It is a security engine that sits directly on the trust boundary between a user, an identity provider, and the application that will decide what that user may do. (جيثب)
pac4j describes itself as a Java security framework for authenticating users, retrieving profiles, and managing authorization across web applications and web services. Its current documentation shows support for OpenID Connect, OAuth, SAML, CAS, HTTP, Kerberos, LDAP, SQL, JWT, MongoDB, CouchDB, IP-based authenticators, REST APIs, authorizers, and request matchers. The implementation matrix also shows that pac4j is not tied to one narrow runtime: it spans Spring MVC, Spring WebFlux, Spring Security, JEE, Play, Vert.x, Spark Java, Javalin, Ratpack, JAX-RS, CAS, and more. In other words, pac4j is often the layer that standardizes identity handling across very different Java stacks. That convenience is exactly what makes it strategically important in security reviews. (pac4j.org)
The project is also active rather than dormant. The GitHub organization shows the main pac4j repository updated on March 8, 2026, with roughly 2.5k stars and hundreds of forks, alongside maintained companion repositories for Play, Spring Security, Vert.x, Javalin, and others. The Maven ecosystem also reflects meaningful usage: pac4j-jwt alone shows more than a hundred versions on MvnRepository, is listed among JWT libraries there, and continues to publish fresh releases, including 6.3.3 on March 2, 2026. This is not evidence of universal adoption, but it is enough to make pac4j an ecosystem component that defenders and red teamers should know how to inspect. (جيثب)
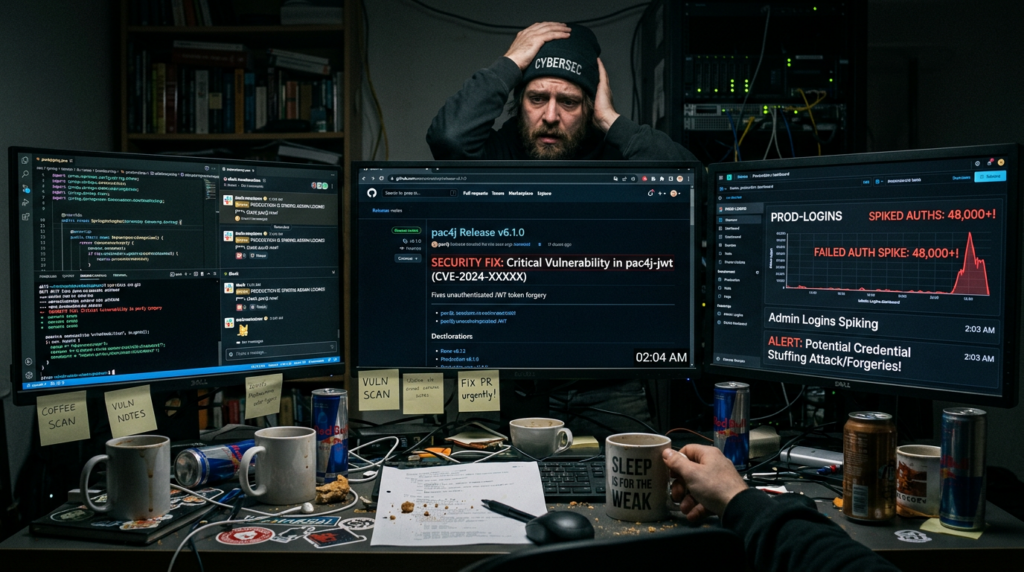
What changed the urgency around pac4j in March 2026 was not a theoretical paper or a low-impact edge case. It was a maximum-severity authentication bypass in pac4j-jwtيتم تتبعها على النحو التالي CVE-2026-29000. The NVD describes the issue plainly: versions prior to 4.5.9, 5.7.9و 6.3.3 contain an authentication bypass in JwtAuthenticator when processing encrypted JWTs. According to the NVD, an attacker who possesses the server’s RSA public key can create a JWE-wrapped PlainJWT with arbitrary subject and role claims, bypass signature verification, and authenticate as any user, including administrators. pac4j’s own security advisory does not argue with the risk; it tells users to upgrade immediately to 4.5.9+, 5.7.9+أو 6.3.3+. (NVD)
That description deserves to be translated into operational English because the security meaning is bigger than the CVE title. The core failure is not simply “JWT bug.” It is a trust-boundary collapse inside the identity envelope. Many teams mentally bucket encrypted JWTs as safer than signed-only tokens because “they’re encrypted.” CVE-2026-29000 is a reminder that confidentiality and authenticity are not interchangeable properties. If the validation path can be manipulated so that decryption happens without a proper signature-verification guarantee, the application may still extract claims and treat them as real identity. Once that happens, the system does not need a memory corruption or command execution bug to be compromised. It hands over its own authorization model voluntarily. (NVD)
This is exactly why authentication bypasses in libraries like pac4j tend to have a broader blast radius than many teams initially assume. pac4j is often not the final business application; it is the identity-processing layer in front of business applications. That means one vulnerable pac4j-based filter, callback, or gateway can become a privilege-injection point for everything behind it. A backend service that trusts an already-validated JWT, an admin console that consumes pac4j profiles, an internal edge service that mints downstream identity, or an SSO integration node that centralizes authentication can all inherit the compromise. The Penligent write-up on CVE-2026-29000 captures this well by emphasizing pac4j-jwt’s typical position in API gateways, backend services, SSO components, and edge services. That is consistent with how these libraries are deployed in real Java estates. (بنليجنت)
The official pac4j release notes reinforce the timeline. The main release notes for the current documentation branch state that v6.3.3 included a security fix on the pac4j-jwt module, while the v4.5 release notes show v4.5.9 as the corresponding security fix in the older JDK 8 line. This matters because pac4j uses different major branches for different JDK baselines. The v6 blog states that pac4j v6 is for JDK 17, v5 is for JDK 11, and v4 is for JDK 8. In practice, that means patching guidance has to follow runtime reality. Telling a JDK 8 team to “just move to latest” is often not actionable; telling them to move to 4.5.9+ is. (pac4j.org)
That version split is one reason pac4j security work can be deceptively hard in enterprise estates. A single organization may have one legacy JDK 8 monolith on pac4j 4.x, one JDK 11 service cluster on 5.x, and one newer JDK 17 gateway on 6.x. All three may implement “the same login” at a business level while running materially different pac4j internals and defaults. The implementation matrix published by pac4j makes that complexity visible: newer bridges such as Spring MVC, Spring Security, Javalin, Ratpack, and JAX-RS align to 6.x on JDK 17+, while some other integrations still map to older branches. A serious assessment therefore has to begin with dependency inventory, not assumptions. (pac4j.org)
CVE-2026-29000 is the most urgent pac4j story right now, but it is not the only security lesson in the project’s history. A few years earlier, CVE-2021-44878 raised concerns about pac4j accepting OpenID Connect ID tokens using the "لا شيء" algorithm. The NVD states that pac4j v5.1 and earlier allowed clients, by default, to accept and validate unsigned ID tokens in some scenarios, which could enable token-validation bypass with malformed tokens using "alg":"none". The pac4j maintainer publicly argued that the original description overstated pac4j’s isolated responsibility because pac4j instantiates validators based on the OIDC server’s advertised metadata, but the release notes still show a concrete security response: in v5.2.0, the project reinforced OIDC security so the لا شيء algorithm must be explicitly accepted through allowUnsignedIdTokensو v5.3.1 fully fixed the issue by checking the OIDC response type when creating the token validator. (NVD)
The right takeaway from CVE-2021-44878 is not to argue over who deserves the bigger share of blame. The real lesson is architectural. Identity stacks are made of at least three moving parts: the application library, the identity provider, and the configuration contract that binds them. If any part allows weak token validation or ambiguous algorithm acceptance, the whole trust boundary becomes negotiable. pac4j’s response improved the client side, but the episode also highlights a recurring problem in SSO engineering: teams often assume protocol correctness because they are using a standard like OIDC. In practice, standards only help if implementations reject unsafe edge cases by default. (pac4j.org)
An even older and more dangerous category appeared in CVE-2023-25581. The NVD says pac4j-core prior to version 4.0.0 was affected by a Java deserialization vulnerability when externally controlled values were stored in attributes of the UserProfile class. The exploit path involved a serialized Java object with the {#sb64} prefix and Base64 encoding, and NVD notes that this could lead to remote code execution in the worst case. This is a very different class of issue from the 2026 JWT bypass, but it reaches the same conclusion: identity objects are not just passive data bags. In Java systems especially, profile attributes, session serialization, and object hydration paths can become dangerous if the system confuses “user metadata” with “trusted internal object state.” (NVD)
That deserialization theme does not stop at pac4j core. In 2025, CVE-2025-31129 affected Jooby’s pac4j integration. NVD’s description says the io.jooby.internal.pac4j.SessionStoreImpl#get module deserializes untrusted data, with fixes in Jooby 2.17.0 و 3.7.0. In 2024, CVE-2024-45384 hit Apache Druid’s optional druid-pac4j extension, where NVD describes a padding oracle that could allow manipulation of a pac4j session cookie; Apache recommends upgrading to 30.0.1+ and using a strong druid.auth.pac4j.cookiePassphrase. These issues are not proof that pac4j itself is uniquely unsafe. They are proof of a more general point: when a security engine gets bridged into frameworks, gateways, session stores, or extension modules, the effective attack surface becomes the library plus every adapter around it. (NVD)
For security engineers, that broader view is more useful than a raw CVE list. The practical risk of pac4j comes from the fact that it centralizes protocol parsing, callback handling, profile creation, session interaction, and authorization handoff. Any design flaw, weak default, or unsafe adapter code in that chain can turn a “login bug” into a system-wide trust failure. The pac4j documentation itself reflects how central this chain is: authentication mechanisms feed profiles, profiles feed authorizers, and matchers determine whether security is applied at all. The older security filter documentation makes the flow explicit: if requests satisfy the matcher configuration, pac4j attempts authentication, checks authorization, and either grants access, redirects to an IdP, or returns an error. That means a mistake in matcher scope, authorizer scope, or credential validation logic can alter the application’s behavior before business code even runs. (pac4j.org)
This is why pac4j reviews should never stop at “What version are we on?” Version is the first question, not the only one. The second question is what protocol paths are actually enabled. pac4j supports OIDC, OAuth, SAML, CAS, LDAP, JWT, HTTP auth, and more. Every one of those brings a different trust model. JWT validation risks center on algorithm handling, signing versus encryption semantics, issuer and audience checks, and claims trust. OIDC adds provider metadata, discovery, token response-type nuances, and logout behavior. SAML adds XML signature semantics, certificate rollover, metadata freshness, ACS configuration, and attribute mapping complexity. The library gives you many capabilities, but it also inherits the full complexity of the protocols it implements. (pac4j.org)
JWT is the easiest place to start because the failure modes are easy to misunderstand. The pac4j JWT documentation says the library validates JSON Web Tokens and is built on Nimbus JOSE+JWT. That is a solid foundation, but it does not remove the need to reason carefully about algorithm choices and token classes. CVE-2026-29000 shows why. When engineering teams say “we use encrypted JWTs,” that often sounds strong. Yet a JWE is not proof that the embedded claims were authenticated in the way your application expects. A safe validation path must make it impossible for a token to arrive in an accepted state without the signature, issuer, audience, key, and claims structure checks your threat model requires. If you cannot explain that path from first principles, you are not done. (pac4j.org)
OIDC is safer than rolling your own auth, but it is not safe enough to run on autopilot. The history of CVE-2021-44878 makes that clear. OIDC is often treated as the “sane default” compared with older SAML deployments, and in many cases that is operationally true. But teams still underestimate the dangers around algorithm acceptance, discovery metadata trust, front-channel versus back-channel logout semantics, and claim normalization. pac4j’s release notes show ongoing OIDC hardening work, including the explicit handling of unsigned ID tokens and response-type checks. That is encouraging, but it is also evidence that token-validation correctness is a moving target, not a solved problem. (pac4j.org)
SAML deserves special attention because pac4j is frequently chosen precisely to simplify SAML integration. The docs say pac4j supports SAML 2.0 and has been tested with providers such as Okta, CAS SAML2 IdP, and Shibboleth. The release notes also show a long history of SAML-specific work: fixes for metadata signatures, better signing options, URL comparison controls during endpoint verification, re-enforcement of requested authentication context checks, support for subject handling in AuthnRequest objects, and more. That history is not a red flag by itself; mature SAML support inevitably involves years of fixes and edge cases. The red flag is when engineering teams assume pac4j has “handled SAML” for them after the login screen works once in staging. It has not. SAML remains configuration-heavy, certificate-heavy, and operationally brittle. pac4j reduces boilerplate, not complexity. (pac4j.org)
The same pattern appears in callback and filter behavior. pac4j’s security filter documentation states that matchers determine whether security is applied at all. If the HTTP request matches the configured matchers, authentication and authorization proceed; otherwise, access is granted automatically. The current security-filter docs also say that when matchers are blank, default behavior applies securityHeaders, and for web applications with at least one indirect client, the csrfToken matcher is applied as well. That is a useful default, but it also means teams must understand when they have replaced, disabled, or bypassed those defaults. A single permissive matcher configuration can quietly carve a hole in the trust boundary that the rest of the application assumes is closed. (pac4j.org)
pac4j has genuinely improved its defensive defaults over time. The v4.1 blog says CSRF protection is enabled by default since pac4j v4, with default matchers securityHeaders,csrfToken and default authorizer csrfCheck for web applications. Later release notes describe stronger CSRF token values, per-request generation, internal expiration, time-attack-resistant verification, and secure and httpOnly flags on the CSRF cookie in v5.1.5. The securityHeaders matcher is also documented as equivalent to headers such as xssprotection, noframe, hsts, nosniffو nocache. Those are meaningful controls. They are worth using. But none of them compensate for a weak identity-validation path or a mis-scoped authorization model. They harden the wrapper; they do not redeem a broken core. (pac4j.org)
That distinction matters because security reviews too often get trapped in a false binary between “the library is secure” and “the library is vulnerable.” pac4j is neither a silver bullet nor a disaster. It is a powerful, maintained, multi-protocol security engine with a visible history of protocol hardening and a visible history of security bugs, just like other serious identity libraries. The more useful question is this: what does pac4j make easier to secure, and what kinds of mistakes does it concentrate in one place? The answer is that pac4j makes it easier to centralize identity plumbing, but by centralizing it, it also makes version drift, callback trust, claim mapping, matcher scope, and adapter safety much more consequential. (جيثب)
From a penetration-testing perspective, pac4j should change how you approach a target. If you see pac4j in a dependency tree, a login callback, an SSO flow, or a JWT validation path, you should treat it as a signal that the authentication surface is richer than the UI suggests. The question is not just whether there is a public exploit. The question is whether identity validation, session storage, claims normalization, and downstream trust relationships align with the actual assumptions of the business logic. That often requires reading both code and behavior. A system can be fully patched against CVE-2026-29000 and still be vulnerable to role inflation, callback abuse, or over-trusted upstream identities. (NVD)
A useful way to think about pac4j is as a trust compiler. It takes protocol-specific identity artifacts and compiles them into application-facing profiles, roles, and authorization outcomes. If the compiler is correct, that abstraction is valuable. If it is wrong, every service downstream is now consuming a bad compile artifact. This is why pac4j-related failures often feel disproportionately dangerous: once an attacker becomes “authenticated” at the library boundary, the rest of the application frequently stops asking hard questions. That pattern appears in the public discussion around CVE-2026-29000 and in pac4j’s own design flow where successful authentication produces profiles that then drive authorization. (بنليجنت)
Where pac4j Usually Lives in Real Systems
In smaller projects, pac4j may be nothing more than the authentication layer in a single Spring or JEE application. In larger environments, it often shows up in more consequential places: SSO broker services, edge gateways, administrative consoles, internal developer platforms, and framework bridges that standardize auth across many services. The implementation matrix and GitHub organization make that breadth clear. When one library spans Spring, JEE, Play, Spark, Vert.x, Javalin, Ratpack, and JAX-RS, it becomes more than a dependency. It becomes a repeated trust primitive across the estate. (pac4j.org)
That repeated placement matters because authentication weaknesses are rarely contained to one HTTP endpoint. A pac4j-based gateway might accept a token once and then inject user headers or session state that dozens of downstream services trust blindly. A pac4j callback endpoint might create a profile with claims that later get mapped to admin roles. An SSO service built on pac4j might front not just one app but an entire internal platform. The vulnerability is not only where the bad token enters. The vulnerability is everywhere that trusts the resulting identity object. (بنليجنت)
For blue teams, this means asset inventory must include auth middleware, not just internet-facing apps. For red teams, it means recon should treat pac4j the same way you would treat an API gateway, an IdP integration layer, or a session broker. The compromise value is often higher than the apparent surface area. (جيثب)

The Risks That Survive Even After You Patch
Patching pac4j-jwt for CVE-2026-29000 is mandatory, but patching does not end the review. There are at least six recurring categories of pac4j deployment risk that survive version upgrades.
The first is protocol overexposure. Teams often enable pac4j because it supports many auth methods, then leave more clients, flows, or callbacks wired than they actually need. Every enabled protocol path increases the chances of a validation bug, metadata issue, or misrouted callback. pac4j’s strength is breadth, but breadth without aggressive minimization is an attack-surface multiplier. (pac4j.org)
The second is claims-to-role overtrust. pac4j is designed to retrieve user profiles and hand them to authorization logic. That is useful, but if roles are derived too directly from token claims or provider attributes, the app can end up trusting externally sourced identity data with insufficient local policy checks. A token that says admin=true, a SAML attribute that maps to an elevated group, or an OIDC role claim from a provider configuration mistake can all produce business impact even when the cryptography is fine. pac4j will not invent a least-privilege model for you. (جيثب)
The third is matcher and authorizer drift. The security-filter docs show that whether security is applied depends on matchers. The defaults are helpful, but teams frequently override them for testing, reverse-proxy behavior, API quirks, or special endpoints. Years later, the same app may have a route where auth was effectively bypassed “temporarily” and never restored. Because pac4j sits before business code, such drift can be easy to miss in normal application review. (pac4j.org)
The fourth is session-store and serialization risk. CVE-2023-25581 in pac4j-core, the Jooby pac4j integration issue, and the Druid druid-pac4j issue all point in the same direction. Identity is not only about token validation. It is also about how validated identity gets stored, serialized, deserialized, and rehydrated. If profiles or session cookies move through unsafe code paths, you can end up with RCE, tampering, or other integrity failures without ever touching the login UI. (NVD)
The fifth is callback trust and redirect complexity. pac4j’s design depends heavily on callback processing. In SSO systems, callback endpoints often become choke points where provider state, request parameters, and local session state converge. pac4j has documented work over the years on understanding callback behavior, logout handling, URL comparisons, and security fixes around logout URL patterns. That history is normal for identity middleware, but it is also a sign that callback and logout handling are not “set and forget” zones. They deserve focused testing. (pac4j.org)
The sixth is downstream blind trust. This is the most common architectural failure. A pac4j-protected edge or web tier authenticates the user, then downstream services stop validating context because “auth already happened.” When that is the design, any bug in pac4j, any weak configuration, and any claim-mapping mistake immediately amplifies into broader privilege abuse. Your safest service is the one that still has a second opinion after the gateway says “trusted.” (بنليجنت)
pac4j Security Features That Help, and Their Limits
It is important to be fair here. pac4j is not negligent about defense features. The docs and release notes show real defensive work around CSRF protection, security headers, session behavior, and protocol hardening. Since v4, CSRF protection has been enabled by default for web applications when no custom matchers are defined, and the default path uses both securityHeaders و csrfToken مع csrfCheck as the default authorizer. Later versions improved CSRF token length, expiry, generation cadence, and cookie flags. The securityHeaders matcher adds a baseline of hardening headers, and several pac4j implementation repositories explicitly advertise CSRF protection and session fixation support. (pac4j.org)
Those features matter because they reduce accidental exposure and make the secure path easier than the insecure one. That is a real engineering advantage. But security engineers should also understand the boundary of those controls. CSRF defense does not verify token integrity. Security headers do not prevent role inflation. Session fixation protection does not stop a vulnerable JWT validation path from granting an attacker a valid session in the first place. Good middleware defaults are essential, but they do not shrink the need for protocol-specific validation review. (pac4j.org)
An Audit Table for pac4j Deployments
| Audit area | What to verify | ما أهمية ذلك | الأولوية |
|---|---|---|---|
| pac4j version | Exact branch and patched version in use, especially pac4j-jwt | CVE-2026-29000 affects <4.5.9, <5.7.9, <6.3.3 | الحرجة |
| JDK alignment | Whether the app is on JDK 8, 11, or 17+ and therefore on pac4j 4.x, 5.x, or 6.x | Patch advice depends on runtime line | عالية |
| Enabled protocols | OIDC, OAuth, SAML, CAS, JWT, LDAP, HTTP, others | Unused auth paths are avoidable attack surface | عالية |
| JWT settings | Accepted algorithms, issuer, audience, JWE/JWS handling, key sources | Token-validation mistakes can become auth bypass | الحرجة |
| OIDC config | Discovery metadata trust, unsigned ID token behavior, response types | Historical pac4j OIDC weaknesses show this needs review | عالية |
| SAML config | Metadata source, certificate lifecycle, ACS/SLO endpoints, attribute mappings | SAML complexity often produces silent trust bugs | عالية |
| Matchers and authorizers | Whether defaults were overridden or disabled | Security may not apply where teams think it does | عالية |
| Callback and logout endpoints | Open redirects, bad path scoping, weak logout trust | Auth control planes often fail at edges | متوسط |
| Session store | Cookie strength, serialization behavior, adapter-specific code paths | Several pac4j-related issues involve session handling | عالية |
| Claims-to-role mapping | How external identity becomes internal privilege | Overtrust here turns valid auth into privilege abuse | الحرجة |
| Downstream trust | Whether backend services re-check context or trust edge identity blindly | One auth mistake can spread across many services | الحرجة |
The point of this table is not to turn every pac4j review into a months-long architecture project. It is to keep the assessment honest. Most real failures happen because teams patch the obvious CVE and skip the trust model around it. The table forces you to look at the trust model. (NVD)
Practical Code and Review Snippets
A first pass in code review is simply finding where pac4j is present and which modules are in play.
<!-- pom.xml -->
<dependency>
<groupId>org.pac4j</groupId>
<artifactId>pac4j-jwt</artifactId>
<version>6.3.3</version>
</dependency>
<dependency>
<groupId>org.pac4j</groupId>
<artifactId>pac4j-saml</artifactId>
<version>6.4.0</version>
</dependency>
<dependency>
<groupId>org.pac4j</groupId>
<artifactId>spring-security-pac4j</artifactId>
<version>6.0.0</version>
</dependency>
If the environment is still on JDK 11 or JDK 8, the target versions must follow the pac4j compatibility model rather than copying the latest JDK 17 examples from the docs. pac4j’s own version guidance is explicit: v4 for JDK 8, v5 for JDK 11, v6 for JDK 17. (pac4j.org)
A fast grep pass can answer surprisingly important questions before deeper review begins:
rg -n "org\\.pac4j|pac4j-jwt|OidcClient|SAML2Client|JwtAuthenticator|allowUnsignedIdTokens|authorizers|matchers|CallbackFilter|LogoutFilter" .
That search often reveals whether the project is using JWT directly, bridging through Spring Security, relying on SAML, or overriding matcher/authorizer behavior. You are looking for evidence of protocol sprawl, local overrides, and places where profiles or claims are consumed after pac4j completes authentication. Those are often the routes to business impact. (pac4j.org)
For dependency visibility in CI, a simple Maven dependency tree check is worth automating:
mvn -q dependency:tree | rg "org\\.pac4j"
In larger estates, this catches pac4j modules pulled transitively through framework bridges rather than declared directly. That matters because the dangerous package may not be in the top-level pom.xml. The Jooby and Druid examples are reminders that pac4j exposure can arrive through integrations, not only through pac4j-core أو pac4j-jwt entries you intentionally added. (NVD)
For JWT-specific reviews, the core question is whether the application enforces the validation properties it assumes. A simplified checklist-oriented pseudo-pattern looks like this:
// illustrative review pattern, not a copy-paste fix
boolean valid =
token.isSigned() &&
token.signatureVerified() &&
expectedIssuer.equals(token.getIssuer()) &&
expectedAudience.equals(token.getAudience()) &&
!token.isExpired() &&
allowedAlgorithms.contains(token.getAlgorithm()) &&
claimsSchemaIsExpected(token.getClaims());
The important part is not the exact syntax. It is the review mindset. Can a token enter the trusted path without signature verification? Can encryption be mistaken for authenticity? Can claims be accepted without issuer, audience, and schema enforcement? CVE-2026-29000 exists because one of those answers became “yes” in a meaningful path. (NVD)
For OIDC, reviewers should look closely for explicit acceptance of weak behavior:
// example of a setting that deserves scrutiny in code review
oidcConfig.setAllowUnsignedIdTokens(false);
pac4j’s release notes say that after CVE-2021-44878, the "لا شيء" algorithm must be explicitly accepted on the client side. That means any codebase that deliberately enables unsigned ID tokens is choosing to widen the trust boundary. If a team has done that, there should be a very strong, documented reason. In most cases, there is not. (pac4j.org)
For route protection, reviewers should locate where matchers and authorizers are defined and verify that the defaults have not been quietly neutralized:
// illustrative conceptual configuration
config.addAuthorizer("adminOnly", requireRole("ROLE_ADMIN"));
// verify whether "none" or overly broad exclusions were introduced
securityFilter.setMatchers("securityHeaders,csrfToken");
securityFilter.setAuthorizers("csrfCheck,adminOnly");
The pac4j documentation is clear that matchers determine whether security is applied and that defaults exist only when you do not replace them. The moment a project introduces custom matcher logic, a human should read it line by line. (pac4j.org)
A lightweight shell check for vulnerable pac4j-jwt lines can also help in CI or asset triage:
#!/usr/bin/env bash
set -euo pipefail
tree="$(mvn -q dependency:tree 2>/dev/null || true)"
if echo "$tree" | rg -q "org\\.pac4j:pac4j-jwt:(4\\.[0-5]\\.[0-8]|5\\.[0-7]\\.[0-8]|6\\.[0-3]\\.[0-2])"; then
echo "[!] Potentially vulnerable pac4j-jwt detected"
exit 1
else
echo "[+] No obviously vulnerable pac4j-jwt version found in dependency tree"
fi
This script is intentionally rough, but it captures the practical point: auth-library patch gates belong in CI just as much as web framework and logging-library gates do. pac4j’s official advisory gives exact minimum safe versions, so there is no excuse to leave the check manual. (pac4j.org)

How to Test pac4j in a Real Engagement
When pac4j shows up during an assessment, treat it as a structured exercise rather than a random exploit hunt.
First, identify the protocol path. Is the target using JWT, OIDC, SAML, CAS, or a framework bridge that hides the underlying choice? The docs page listing supported clients and authenticators is a reminder that pac4j can expose many very different auth surfaces under one brand name. (pac4j.org)
Second, identify the version and branch. Because pac4j maps versions to JDK lines, the same organization may have different patch ceilings in different services. If you cannot pin the exact version, you cannot make strong claims about exposure to CVE-2026-29000 or the OIDC fixes around CVE-2021-44878. (pac4j.org)
Third, enumerate the trust artifacts. That means cookies, bearer tokens, callback parameters, state parameters, nonce handling, metadata URLs, logout requests, and session-store behavior. Too many tests stop at “I can log in.” pac4j reviews should continue until you understand how authenticated state is created, stored, and reused. The deserialization issues around pac4j-core and integrations make this especially important. (NVD)
Fourth, test claim semantics, not just cryptography. Can you alter a role claim and see downstream privilege shifts? Can an upstream provider attribute map unexpectedly into admin access? Can a gateway-authenticated identity reach backend paths that never perform their own authorization check? The most damaging identity bugs often look “boring” at the protocol layer and catastrophic at the business layer. (جيثب)
Fifth, test callback and logout behavior. Identity systems are full of edge cases around redirect targets, post-logout paths, state reuse, and path scoping. pac4j’s release history includes fixes and hardening in these areas, which is a sign that they are worth active testing. (pac4j.org)
Sixth, trace downstream trust. After you obtain an authenticated pac4j-backed session or token, watch what the rest of the system does with it. Does it inject headers for other services? Does it create internal tokens? Does it mint sessions for admin subapps? Does it grant roles directly from external claims? This is where authentication bugs become estate-wide incidents rather than isolated login flaws. (بنليجنت)
Why pac4j Matters to Modern Attackers
The modern attacker does not need to break every service individually if they can subvert the identity fabric once. That is why libraries like pac4j are strategically attractive targets. In older threat models, defenders often focused on perimeter exposure and memory corruption. Those still matter. But the last several years have made one thing very clear: identity-layer failures can be faster, quieter, and more scalable than classic exploitation paths. A forged token, a weakly validated ID token, a poisoned session cookie, or an overtrusted SAML attribute can bypass entire classes of downstream controls. pac4j sits exactly where those mistakes become powerful. (NVD)
This is also why pac4j should matter to organizations that believe they are “just using standard SSO.” Standard protocols do not eliminate trust mistakes; they move trust mistakes into implementation and configuration. pac4j’s long public history of OIDC, SAML, JWT, CSRF, metadata, callback, and logout changes is not evidence of failure. It is evidence that identity middleware is inherently delicate and must be treated as a living security component. (pac4j.org)
Where Penligent Can Be Useful
In practice, pac4j problems are rarely discovered by reading a CVE alone. The hard part is finding where pac4j is actually present, which auth path is exposed, and whether the vulnerable or weakly configured path is reachable in a real application flow. That is the kind of work that benefits from an AI-assisted testing platform that can connect dependency clues, route behavior, callback endpoints, cookies, and token flows into one validation process rather than treating each signal in isolation. Penligent’s own public research on CVE-2026-29000 frames the issue correctly as an identity-boundary problem rather than “just another library flaw.” (بنليجنت)
That matters because identity bugs frequently hide in the gap between static dependency awareness and runtime proof. A team may know pac4j exists somewhere in the stack and still not know whether a reachable callback endpoint, JWT flow, or downstream authorization path turns it into a real exploit chain. Used well, a platform like Penligent fits naturally here: asset discovery, auth-surface mapping, exploitability validation, and evidence-backed reporting are exactly what security teams need when the vulnerable component is an authentication engine rather than a toy parser buried deep in the app. (بنليجنت)
The Bottom Line
pac4j is not famous because it is flashy. It is important because it is foundational. It gives Java teams a unified way to handle OIDC, OAuth, SAML, CAS, LDAP, JWT, and authorization across many frameworks. That is useful engineering. It is also a concentration of trust. When pac4j works correctly, it simplifies identity. When it fails, or when teams misunderstand its trust boundaries, the failure lands at the most sensitive layer in the application. (pac4j.org)
CVE-2026-29000 should be taken seriously because it shows how catastrophic a pac4j identity failure can be: a token-processing flaw in JwtAuthenticator that could let an attacker authenticate as arbitrary users, including administrators, if the deployment accepted the affected encrypted JWT path. Earlier issues such as CVE-2021-44878 and CVE-2023-25581, along with ecosystem-adjacent issues in Jooby and Druid integrations, reinforce the broader lesson. The real risk is not one protocol name or one package name. The real risk is a system that continues to trust identity after the validation assumptions have already broken. (NVD)
If you are defending a Java estate, pac4j belongs on your shortlist of libraries that deserve active review. If you are assessing a target, pac4j should change how you model the auth layer. And if you are building on it, the safest mindset is not “pac4j handles security for us.” The safest mindset is “pac4j is part of our security boundary, and we need to verify that boundary continuously.” (جيثب)
Further Reading
- pac4j official documentation
- pac4j GitHub repository
- pac4j implementations and version matrix
- pac4j JWT documentation
- pac4j official security advisory for pac4j-jwt
- NVD entry for CVE-2026-29000
- NVD entry for CVE-2021-44878
- NVD entry for CVE-2023-25581
- NVD entry for CVE-2025-31129
- NVD entry for CVE-2024-45384
- pac4j release notes
- CVE-2026-29000 in pac4j-jwt, an identity bypass hiding behind encryption
- Penligent Hacking Labs
- Burp AI in 2026, What It Actually Changes in a Real Burp Workflow