On March 17 and March 18, 2026, Canonical, NVD, Qualys, and multiple security news outlets all converged on the same core message: CVE-2026-3888 is a real, high-severity local privilege escalation flaw in Ubuntu’s snapd stack, and under the right conditions it can turn an ordinary local user into root. The vulnerability is tracked with a CVSS v3.1 score of 7.8, and the public descriptions consistently tie the bug to the interaction between snap-confine و systemd-tmpfiles. Canonical’s vendor notice says snapd “could be used to escalate privilege,” while NVD describes the flaw as a case where local attackers can gain root by re-creating snap’s private /tmp directory after automated cleanup. (Ubuntu)
What makes Ubuntu CVE-2026-3888 Bug more interesting than the average Linux local privilege escalation is not just the end state. Plenty of Linux privilege escalation flaws have ended in root before. What stands out here is the path. This is not a straightforward memory corruption story, and it is not a simple “one bad setuid binary” story either. Qualys’ write-up shows a privilege chain built from two components that each look defensible in isolation: snap-confine, which runs with elevated privilege to build confinement boundaries for snaps, and systemd-tmpfiles, which runs as root to create and clean temporary directories on a schedule. The failure happens in the handoff between them. (كواليس)
That distinction matters because it changes how defenders should think about risk. Engineers often look at a local privilege escalation and mentally downgrade it because it is “not remote.” They look again at the attack complexity and see “high,” then downgrade it one more time because the exploit requires a 10-day or 30-day timing window. That is the wrong instinct for many real environments. In a world of shared workstations, developer desktops, contractor endpoints, persistent browser footholds, malicious extensions, exposed lab access, and stolen low-privilege sessions, a delayed privilege escalation can still be operationally devastating. CVE-2026-3888 is exactly the sort of bug that turns an apparently modest foothold into total host compromise. (كواليس)
The most visible public news framing today leaned into that direct outcome by describing the issue as a bug that lets attackers “gain root” via a “systemd cleanup timing exploit.” That framing is sharp and readable, but the primary sources add the nuance that matters for defenders: the bug is specifically in how snapd handles operations in snap’s private temporary directory when systemd-tmpfiles is configured to clean stale content. Canonical also adds an important scoping detail that many quick news summaries flatten: default Ubuntu Desktop installations are the main concern for 24.04 LTS and 25.10, but Canonical pushed hardening across older supported releases as well because non-default configurations there could also be vulnerable. (أخبار القراصنة)
If you are a security engineer, there are really five questions worth answering. What exactly is vulnerable. How does the exploit chain work in practice. Which Ubuntu releases and snapd builds do you need to care about. What should you patch or change right now. And how should you place this bug in the longer history of Linux and Ubuntu local root vulnerabilities. This guide is written around those five questions, with direct defensive commands, version tables, and a comparison set of related CVEs that help explain why this one deserves more attention than a casual reading of “local plus delayed” might suggest. (Ubuntu)
Ubuntu CVE-2026-3888 Bug, The short version security teams need first
Before getting into the exploit path, it helps to compress the whole issue into one defensible summary. CVE-2026-3888 is a local privilege escalation in snapd on Ubuntu. The issue arises when systemd-tmpfiles automatically cleans stale content inside snap’s private temporary directory structure, after which an unprivileged attacker can re-create a deleted directory in a way that subverts privileged work later performed by snap-confine. NVD classifies the weakness as CWE-268, privilege chaining, which is a useful description because the exploit is not a single broken permission check so much as a path that chains scheduled cleanup, writable temporary state, namespace setup, bind mounts, and privileged execution. (NVD)
Qualys rated the issue high severity with a CVSS v3.1 score of 7.8, using the vector AV:L/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H. That score tells you almost everything you need to know if you read it the right way. The attacker needs local access and low privileges. No user interaction is required. The complexity is high because the exploit depends on a timing window created by cleanup policy. The scope is changed, which is important, because the compromise crosses a boundary between the vulnerable component and other protected resources. And the impact on confidentiality, integrity, and availability is high. That is not a “minor local bug.” It is a classic full-compromise local root condition with awkward prerequisites. (كواليس)
Canonical’s official security notice says the problem can be corrected by updating snapd, and it explicitly lists fixed package versions for Ubuntu 25.10, 24.04 LTS, 22.04 LTS, 20.04 LTS, 18.04 LTS, and 16.04 LTS. Canonical’s community security post adds another operationally useful detail: while the default-installation impact is centered on Ubuntu 24.04 LTS and Ubuntu 25.10, the same hardening was applied to older supported releases because some non-default configurations there could also be exposed. That means defenders should not dismiss older fleets just because the first news headline they saw mentioned “Ubuntu Desktop 24.04 and later.” (Ubuntu)
The public advisory trail also shows why it is worth following vendor guidance rather than only reading the first article you see. Qualys’ disclosure listed Ubuntu 24.04 LTS, Ubuntu 25.10, Ubuntu 26.04 dev, and upstream snapd versions prior to 2.75 as affected. Canonical’s later community post said the hardening would also be applied upstream in snapd 2.75.1 and listed a later Noble build, 2.73+ubuntu24.04.2, in that post, even though USN-8102-1 initially listed 2.73+ubuntu24.04.1. That does not change the vulnerability itself, but it does mean patch verification should follow the latest vendor package channel rather than a copied chart from an early article. (كواليس)
Ubuntu CVE-2026-3888 Bug, What is actually vulnerable
To understand why this bug exists, you need to understand the trust boundary around snaps on Ubuntu. snapd is the service and tooling layer that manages snap packages. Those packages are self-contained application bundles that bring their own dependencies and run inside a confinement model enforced by Linux security primitives. The component at the center of this bug is snap-confine, a privileged binary that prepares the execution environment for a snap before the application itself runs. Qualys describes it as the part that builds the sandbox, handling mount namespace isolation, AppArmor policy loading, cgroup enforcement, and seccomp filtering. Because it must cross kernel and filesystem boundaries on behalf of ordinary users, it sits in exactly the sort of privileged position where small filesystem assumptions can become major security problems. (كواليس)
The second component is systemd-tmpfiles. That service is not suspicious by itself. It exists to create, remove, and clean up temporary files and directories according to configured rules. On Ubuntu, it traverses temporary locations on a schedule and removes entries older than a defined age. Qualys’ advisory shows that on Ubuntu 24.04, /tmp cleanup was configured at 30 days in the relevant case study, while Ubuntu 25.10 used a 10-day retention interval for /tmp. The key point is that this cleanup is performed by a trusted root-owned service, independently of what snap-confine later assumes about the layout and ownership of temporary snap directories. (كواليس)
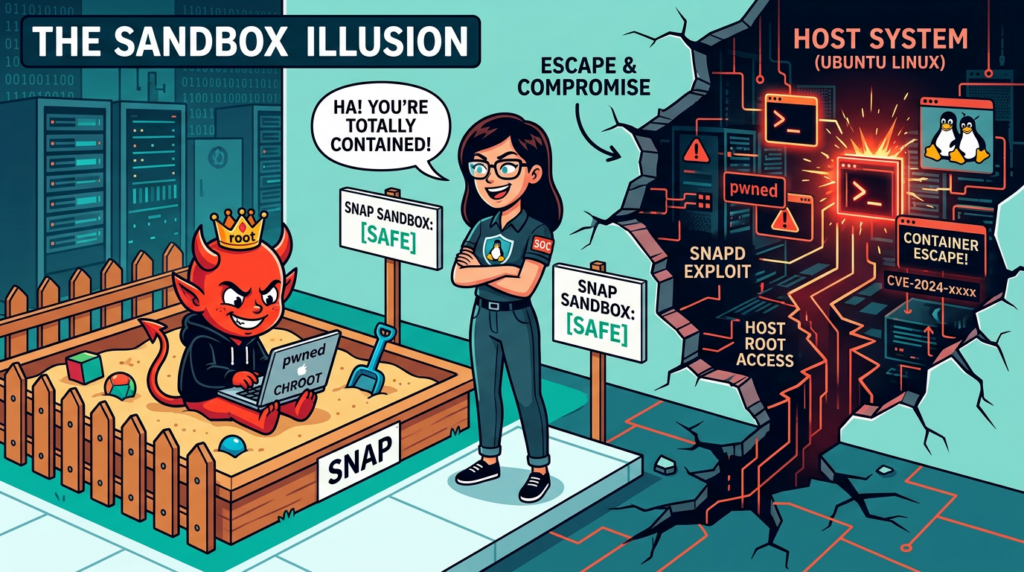
The vulnerable interaction centers on snap’s private temporary area. Qualys’ advisory shows snapd.conf creating /tmp/snap-private-tmp as a root-owned 0700 directory. Inside the snap sandbox, snap-confine also creates a per-snap temporary area and a .snap directory used to create so-called “mimics,” which are writable stand-ins used when snap needs to construct mountpoints inside otherwise read-only filesystem trees. This matters because the vulnerability is not simply “something in /tmp is writable.” The bug is that systemd-tmpfiles can remove a directory that snap-confine later treats as if it still has the expected provenance, ownership, and security meaning. An attacker who can re-create that directory before the next privileged setup phase gets to influence what snap-confine bind-mounts as root. (كواليس)
That is why NVD’s description uses the phrase “re-creating snap’s private /tmp directory.” The risky act is not simply deletion. Deletion creates the opening, but the exploit depends on re-creation plus a race during sandbox setup. In other words, the vulnerability is best understood as a lifecycle bug. A trusted service removes stale state. An unprivileged user re-creates a sensitive path. A privileged service later consumes that path under assumptions that were true when the directory was first created by the system, but are no longer true after attacker-controlled re-creation. That is precisely the kind of temporal bug defenders miss when they think only in terms of static permissions. (NVD)
Ubuntu CVE-2026-3888 Bug, How the systemd cleanup timing exploit works
Qualys published a detailed public advisory with a proof-of-concept chain, and while I am not going to reproduce exploit code here, the logic of the chain is important for defenders. The advisory begins by showing that systemd-tmpfiles traverses /tmp once per day and removes files and directories that have not been accessed or modified for the retention period. In Ubuntu 24.04, that period is 30 days for the demonstrated path; in Ubuntu 25.10, it is 10 days. Qualys then focused on the fact that snap-confine performs privileged work in /tmp/snap-private-tmp, including creating per-snap temporary structures and a .snap directory used during mount “mimic” construction. (SecLists)
The clever part is that the attacker keeps the enclosing /tmp area active while allowing the inner .snap directory to go stale. Qualys describes writing frequently to /tmp but not to /tmp/.snap inside the sandbox, then waiting until systemd-tmpfiles deletes the unmodified .snap directory while leaving the surrounding writable temporary directory intact. At that point, the attacker can re-create .snap because the enclosing /tmp is world-writable from inside the sandboxed environment. That re-created path now belongs to the attacker rather than to the original privileged setup logic. (كواليس)
From there, the exploit becomes a race during namespace and mount preparation. snap-confine creates a writable “mimic” of a path such as /usr/lib/x86_64-linux-gnu in order to later bind-mount required content into it. Qualys’ advisory explains that between the first bind mount and the later stage where files and directories are re-bound into the writable tmpfs, an attacker can swap in their own prepared directory tree under the attacker-owned .snap path. When snap-confine resumes, it ends up bind-mounting attacker-controlled files and even the dynamic loader into the sandbox as root. That gives the attacker control over code execution inside the privileged sandbox setup path. (كواليس)
One subtle and important point in the Qualys proof of concept is that “root” appears in two stages. First, the attacker gets a root shell inside the snap sandbox. That is already serious, but it is not yet unconstrained host root because AppArmor and seccomp still apply. Qualys explicitly demonstrated that at this intermediate stage the attacker’s root shell could not simply read /etc/shadow due to confinement. The final breakout came afterward by copying /بين/باش into a location allowed by the profile, marking it setuid, and then executing that SUID-root shell from outside the sandbox. That last step turns a confined root context into effective host-level root privileges. (كواليس)
That distinction is worth dwelling on because it makes the attack easier to underestimate. Some readers will hear “root in a sandbox” and assume the risk is contained. The proof-of-concept chain says otherwise. The snap sandbox did impose restrictions, but the attacker-controlled root context still had enough allowed operations to plant a setuid host executable in a permitted location and then use it outside confinement. In practice, that means the bug is not just a sandbox integrity problem. It is a full host compromise path. That is consistent with Qualys’ wording, Canonical’s remediation urgency, and the public news coverage that emphasizes root-level impact. (كواليس)
The exploit chain also explains why the attack complexity is rated high without making the vulnerability unimportant. The difficulty is not that the bug is weak or partial. The difficulty is that the attacker must win a long-timeline condition and then time a race in the mount setup sequence. Those are engineering burdens, not risk reducers. If an attacker already has a persistent local foothold, time is often much cheaper than defenders assume. Many enterprise compromises are not smash-and-grab intrusions anymore. They are quiet, patient, and stateful. This bug fits that tempo uncomfortably well.
Why the 10 to 30 day wait does not make Ubuntu CVE-2026-3888 Bug harmless
Security teams often over-trust temporal friction. If a vulnerability cannot be exploited instantly, it starts to feel like a lower priority item. That instinct is sometimes reasonable for noisy attack paths, but it is dangerous for local privilege escalations on endpoints and workstations. CVE-2026-3888 depends on a cleanup policy that runs on a schedule. That means the exploit window is delayed, not impossible. The attacker does not need user interaction once the foothold exists, and the attacker only needs low privileges. Those are exactly the conditions that matter on compromised developer laptops, student desktops, thin clients, VDI pools, contractor systems, and lab machines where attackers can survive long enough to cash in the delay. (كواليس)
Think about common incident patterns. A phishing kit lands a user-level foothold. A malicious browser extension gets installed. A junior developer account on a shared desktop is abused. A kiosk-like Ubuntu workstation in a lab is accessible to multiple users. A local web bug or SSH credential leak gives an attacker a normal shell. None of those events automatically means full host control, and many organizations comfort themselves with that boundary. CVE-2026-3888 exists precisely to collapse that comfort. If the system runs the right snap and cleanup conditions long enough, what started as an ordinary user session can become a root-owned persistence and control problem.
Another reason the delay is not a real comfort blanket is that local privilege escalation is rarely the first stage in a modern intrusion. It is usually the second or third. Initial access gets the headlines. Privilege escalation determines what the attacker can actually keep, alter, or hide. Once root is on the table, the attacker can manipulate logs, disable sensors, persist more quietly, exfiltrate credentials, tamper with application state, or weaponize the host for lateral movement. In that context, a vulnerability with a waiting period can still be central to the operation. The delay only changes campaign planning, not the strategic value of the bug. (كواليس)
There is also a platform psychology issue here. Ubuntu workstations and developer machines are often treated as trusted middle ground between hardened servers and consumer endpoints. They are where engineers build, test, browse, debug, authenticate to cloud consoles, and hold tokens. Bugs that turn ordinary local access into root on those systems deserve special attention because the business value of the machine is often far higher than its perceived exposure level. A local root bug on a production server matters. A local root bug on a developer laptop with package signing keys, SSH agents, cloud credentials, browser sessions, and internal source access may matter even more.

Ubuntu CVE-2026-3888 Bug, Affected releases and fixed versions
One of the trickiest parts of today’s coverage is that different sources emphasize different slices of the impact. NVD’s current description says the issue affects Ubuntu 16.04 LTS, 18.04 LTS, 20.04 LTS, 22.04 LTS, and 24.04 LTS. Canonical’s USN-8102-1 security notice lists fixed package versions across those same maintained lines plus Ubuntu 25.10. Canonical’s community security post then clarifies the practical exposure story: default installations of Ubuntu 24.04 LTS and Ubuntu 25.10 are directly impacted, while older supported releases received the same hardening because some non-default configurations could be vulnerable as well. Those are not contradictions. They are different levels of operational detail. (NVD)
The table below is the most useful way to read the situation as of March 18, 2026.
| Ubuntu release | Exposure framing | Official fixed package listed by Ubuntu | الملاحظات |
|---|---|---|---|
| 25.10 | Default installs impacted | 2.73+ubuntu25.10.1 | Canonical community post includes 25.10 as directly impacted in default installs. (Ubuntu Community Hub) |
| 24.04 LTS | Default installs impacted | 2.73+ubuntu24.04.1 in USN-8102-1 | Canonical community post later lists Noble 2.73+ubuntu24.04.2, so verify against the latest package channel and regression follow-up. (Ubuntu) |
| 22.04 LTS | Hardening applied for non-default exposure | 2.73+ubuntu22.04.1 | Not framed by Canonical as the main default-installation case, but patched. (Ubuntu) |
| 20.04 LTS | Hardening applied for non-default exposure | 2.67.1+20.04ubuntu1~esm1 | Ubuntu Pro fix path. (Ubuntu) |
| 18.04 LTS | Hardening applied for non-default exposure | 2.61.4ubuntu0.18.04.1+esm2 | Ubuntu Pro fix path. (Ubuntu) |
| 16.04 LTS | Hardening applied for non-default exposure | 2.61.4ubuntu0.16.04.1+esm2 | Ubuntu Pro fix path. (Ubuntu) |
Qualys also listed upstream snapd versions prior to 2.75 as vulnerable and mentioned Ubuntu 26.04 dev builds in its disclosure. Canonical’s community post later said the hardening would also be applied to upstream snapd version 2.75.1. That means engineers tracking upstream rather than distro packages should not stop at the first static version string they saw in an article. Check the current upstream security fix stream or vendor-maintained packaging for your environment. (كواليس)
There is one more practical wrinkle that deserves attention. Canonical’s USN-8102-1 says that after a standard system update, you need to reboot the computer to make all necessary changes. That is easy to overlook in fast-moving patch windows. On Linux, administrators often assume a package upgrade is enough for userland vulnerabilities. In this case, Canonical explicitly says to reboot after updating, so a compliance view that checks only package version without confirming the reboot window may overstate your true remediation status. (Ubuntu)
How to check whether a host is exposed
The fastest first pass is to inspect the installed snapd version and compare it to Canonical’s fixed builds. Canonical’s own community guidance says to run dpkg -l snapd, and that remains the right first check. On fleets, you should pair version inspection with a quick look at whether snaps are actually present and whether your tmpfiles rules still match the vulnerable cleanup behavior. (Ubuntu Community Hub)
dpkg -l snapd
snap list
If you want a slightly richer local check, inspect the relevant tmpfiles configuration and the snapd tmpfiles rule.
grep -R "snap-private-tmp" /usr/lib/tmpfiles.d /etc/tmpfiles.d /run/tmpfiles.d 2>/dev/null
grep -R " /tmp " /usr/lib/tmpfiles.d /etc/tmpfiles.d /run/tmpfiles.d 2>/dev/null
systemd-tmpfiles --cat-config | sed -n '/snap-private-tmp/p;/\\/tmp /p'
Those commands are useful because Qualys’ advisory explicitly tied the exploitability condition to systemd-tmpfiles cleanup of stale temporary content and showed relevant entries such as /usr/lib/tmpfiles.d/tmp.conf و /usr/lib/tmpfiles.d/snapd.conf. On affected case studies, the advisory showed 30-day cleanup for Ubuntu 24.04 and 10-day cleanup for Ubuntu 25.10, along with the root-owned D! /tmp/snap-private-tmp 0700 root root - rule. (SecLists)
You should also look at cleanup activity and package update timing if you are triaging an endpoint that may have had a long-lived foothold. The vulnerability does not produce one obvious log line saying “exploit happened here,” but you can still gather context around cleanup cadence, package versions, and reboot state.
journalctl -u systemd-tmpfiles-clean.service --since "45 days ago"
stat /usr/lib/snapd/snap-confine
uname -a
who -a
last -F | head
The point of that mini-triage is not to claim forensic proof of exploitation. It is to answer three operational questions quickly. Was the host on a vulnerable package. Has the cleanup service been running long enough for the waiting window to be relevant. And are there signs the system should be treated as higher priority because it has had long-lived interactive use or suspicious user sessions. Forensic certainty will require more than version checks. But version checks plus cleanup cadence tell you whether the exploit chain was even plausible on that machine.
For fleet-scale environments, a simple SSH loop or configuration management query is enough to identify where you should patch first. Here is a minimal shell-based inventory pattern you can adapt.
for host in $(cat hosts.txt); do
printf "\\n== %s ==\\n" "$host"
ssh -o BatchMode=yes "$host" \\
'printf "snapd version: "; dpkg-query -W -f="${Version}\\n" snapd 2>/dev/null || echo "not installed";
printf "reboot pending: "; test -f /var/run/reboot-required && echo yes || echo no;
printf "snaps installed: "; snap list 2>/dev/null | awk "NR>1{count++} END{print count+0}"'
done
That kind of inventory is not glamorous, but it is exactly how real remediation gets done. Security teams lose time when they spend the first six hours debating exploit elegance rather than answering the much simpler question of where the vulnerable package still exists.

Patching Ubuntu CVE-2026-3888 Bug, What to do right now
Canonical’s recommendation is straightforward: update the system, or at minimum update snapd, and then reboot. The community post gives both a full-package update path and a targeted package-only path. The full-package path is the better default because it reduces the chance that you remediate one issue while leaving adjacent security fixes behind. The targeted snapd upgrade is still useful for controlled change windows or narrow emergency interventions. (Ubuntu Community Hub)
sudo apt update && sudo apt upgrade
sudo reboot
If you truly need a component-scoped change:
sudo apt update
sudo apt install --only-upgrade snapd
sudo reboot
Canonical also points out that unattended-upgrades is enabled by default from Ubuntu 16.04 LTS onward, and that security patches should therefore be applied automatically within 24 hours where that service is functioning normally. That is useful, but it should not be mistaken for proof of remediation. Automatic download or installation is not the same thing as a verified patched-and-rebooted endpoint. On desktop fleets especially, security teams should confirm actual installed versions and reboot status rather than trusting that auto-updates alone closed the window. (Ubuntu Community Hub)
One nuance worth calling out for Noble operators is the follow-up versioning wrinkle. USN-8102-1 lists 2.73+ubuntu24.04.1 as the fixed package for 24.04 LTS. Canonical’s later community security post lists Noble 2.73+ubuntu24.04.2, indicating that practitioners should pay attention to the latest released fix in the channel rather than freezing on the first published advisory string. In practical terms, your runbook should say “upgrade to the latest vendor-fixed snapd for your release,” not “upgrade only to the first fixed number mentioned in a news article.” (Ubuntu)
If you need to validate after patching, do not stop at مناسب exit codes. Confirm package version, confirm reboot, and confirm that the current snapd tmpfiles configuration matches the hardened state. For example:
dpkg-query -W -f='${Package} ${Version}\\n' snapd
test -f /var/run/reboot-required && echo "reboot still pending" || echo "no reboot flag"
grep -R "snap-private-tmp" /usr/lib/tmpfiles.d /etc/tmpfiles.d /run/tmpfiles.d 2>/dev/null
These checks are simple by design. The best patch verification commands are often boring. The goal is not to simulate an exploit in production. The goal is to reduce ambiguity about whether the host is still on a risky build and risky configuration. For internet-facing servers, desktop estates, build agents, and shared research environments, that clarity matters more than cleverness.
Emergency mitigation when you cannot patch immediately
Canonical’s community security post includes a manual mitigation and explicitly says it should be treated as a last resort if security updates cannot be applied immediately. That warning matters. Hand-editing tmpfiles configuration can drift from package-managed state and may interfere with future unattended updates until the changes are reconciled. Still, when patching is blocked, the manual mitigation is worth having in the incident playbook. (Ubuntu Community Hub)
Canonical says to replace the contents of /usr/lib/tmpfiles.d/snapd.conf with the following:
D! /tmp/snap-private-tmp 0700 root root -
# Allow removing content in the private tmp folders without affecting the
# architectural structure of the folders themselves.
X /tmp/snap-private-tmp
X /tmp/snap-private-tmp/*/tmp
x /tmp/snap-private-tmp/*/tmp/.snap
Then restart the cleanup service:
sudo systemctl restart systemd-tmpfiles-clean.service
The logic of that mitigation is defensively elegant. Instead of trying to remove cleanup entirely, it changes cleanup semantics so that the content inside the private temporary folders can be removed without tearing down the directory structure that snap-confine later assumes. That is exactly what you want from a mitigation for a lifecycle bug: preserve the architectural invariant even when stale content is being cleaned. (Ubuntu Community Hub)
If you apply this mitigation under emergency conditions, document it. That sounds obvious, but it is routinely skipped in practice. Temporary changes to tmpfiles policy are the kind of thing that vanish from memory and then confuse later responders or platform engineers. Include the host list, the date, the exact file contents pushed, the service restart confirmation, and the target date for replacing the mitigation with the vendor package fix. Temporary hardening that is not tracked becomes permanent drift, and permanent drift is how future incidents get harder.
A final practical note on mitigation strategy: if a host is both high-value and plausibly exposed, and you cannot patch immediately, treat it as an incident candidate rather than just a vulnerable system. This vulnerability is not a speculative theoretical condition anymore. Canonical assigned it, NVD published it, Qualys disclosed it publicly, and patch guidance exists. If your environment also has evidence of suspicious low-privilege access on the same machine, the correct posture is not “we will patch when change control opens.” It is “we will patch, review, and potentially reimage according to the asset’s trust role.”
What Ubuntu CVE-2026-3888 Bug teaches about Linux privilege boundaries
The most important lesson of CVE-2026-3888 is that privileged boundaries are temporal as well as structural. Security engineering often focuses on static properties: who owns a file, what mode a directory has, whether a binary is setuid, whether a service runs as root, whether AppArmor or seccomp is present. Those things all matter, but they are snapshots. This bug lives in the transition between snapshots. A path is safely created by the system. Time passes. Cleanup removes it. An attacker recreates it. A privileged component returns later and trusts the path based on what it once represented rather than what it represents now. That is a lifecycle failure, not merely a permissions failure. (كواليس)
This is also a reminder that confinement systems are only as strong as their setup phases. Snap’s security model uses multiple layers: namespaces, AppArmor, seccomp, mount controls, and structured package policies. In principle, that is exactly the right defensive architecture. But any system that needs a privileged helper to assemble those controls creates a dangerous moment before confinement is fully established. snap-confine has to do highly privileged work in order to make unprivileged execution safe afterward. Bugs in that setup phase, especially bugs involving mountpoints and writable temporary state, can therefore punch above their apparent size. (كواليس)
The bug also reinforces why “world-writable but sticky” is never the end of the story. /tmp semantics have been the substrate for exploit development for decades because shared temporary state is where cleanup, race conditions, stale assumptions, and naming collisions all like to hide. In the oss-security thread responding to the Qualys disclosure, Michal Zalewski noted the long history of /tmp-related vulnerabilities and expressed frustration that distros still rely on world-writable /tmp in ways that continue to create avoidable security problems. Whether or not you agree with that broader design critique, CVE-2026-3888 gives it fresh evidence. (SecLists)
For defenders, the architectural takeaway is simple. When you assess privileged Linux software, ask three questions in addition to the usual code review questions. What filesystem structures does it assume will continue to exist with the same security meaning over time. Which of those structures can be cleaned, rotated, or re-created by another subsystem. And at what points does the privileged code consume a path name rather than a trusted file descriptor or verified inode lineage. Those questions do not just apply to snapd. They apply broadly to package systems, container runtimes, helpers for namespace setup, and any daemon that crosses trust boundaries through the filesystem.

Related CVEs that put CVE-2026-3888 in context
CVE-2026-3888 is not an isolated oddity. It belongs to a recognizable family of Linux and Ubuntu privilege escalation problems where a privileged helper, a filesystem edge, or a setuid execution path can be subverted by a lower-privileged actor. The related CVEs below are worth understanding because they show how often “small” local conditions become full root when trusted system components interact in the wrong order.
| مكافحة التطرف العنيف | What it is best remembered for | Why it matters next to CVE-2026-3888 |
|---|---|---|
| CVE-2021-44731 | A race condition in snap-confine when preparing a private mount namespace, allowing local attackers to gain root by bind-mounting attacker content into the snap private mount namespace. (NVD) | This is the closest historical cousin. It shows that snap-confine’s privileged namespace setup path has been a high-value attack surface before. |
| CVE-2022-3328 | A race condition in snap-confine’s must_mkdir_and_open_with_perms(). (NVD) | Again, the pattern is not “snaps are insecure by definition,” but that mount and directory setup during confinement is fragile and worth hard scrutiny. |
| CVE-2021-4034 | PwnKit, the famous local privilege escalation in pkexec, where environment-variable handling could lead to arbitrary code execution as root. (NVD) | This remains the archetype of why local root bugs on default Linux systems should not be casually deprioritized. |
| CVE-2023-4911 | Looney Tunables, a glibc dynamic loader bug in ld.so tied to GLIBC_TUNABLES, enabling local elevated execution through SUID binaries. (NVD) | This is relevant because Qualys’ CVE-2026-3888 proof of concept ultimately weaponizes control over the dynamic loader path inside the sandbox. |
| CVE-2023-2640 and CVE-2023-32629 | The Ubuntu OverlayFS local privilege escalation pair caused by authorization failures in Ubuntu kernel handling of privileged extended attributes. (NVD) | These are useful comparisons because they show how Ubuntu-specific packaging or kernel behavior can turn a local foothold into root even without a classic remote exploit. |
CVE-2021-44731 is the most important comparison point. NVD describes it as a race condition in the snap-confine binary while preparing a private mount namespace, allowing a local attacker to gain root by bind-mounting their own contents into the snap private mount namespace and causing arbitrary code execution. That history matters because it shows a recurring class of risk around snap confinement setup. When a privileged helper builds namespaces and mount trees on behalf of an ordinary user, path handling and timing are not peripheral implementation details. They are the core security boundary. (NVD)
CVE-2022-3328 matters for a similar reason. NVD’s description is brief, but the gist is enough: another race in snap-confine, this time in a helper that creates directories with expected permissions. Even sparse public descriptions are instructive here. The repetition tells you that the snap-confine attack surface is not theoretical. Security teams responsible for Ubuntu estates should treat new snap-confine bugs as historically informed risks, not one-off curiosities. (NVD)
PwnKit, CVE-2021-4034, is not a snap bug at all, but it belongs in this conversation because it reset defender intuition about local bugs on mainstream Linux distributions. pkexec was a setuid utility installed by default in many environments, and a local attacker could use a flaw in argument vector handling to get arbitrary code execution as root. The lesson was not just “patch polkit.” The deeper lesson was that local privilege escalation on broadly deployed default components can have enormous practical impact because low-privilege footholds are common. That exact lesson carries over to CVE-2026-3888. (NVD)
CVE-2023-4911, Looney Tunables, is another useful anchor because it reminds engineers how often the dynamic loader becomes the last step in a local root chain. NVD says the bug was a buffer overflow in glibc’s ld.so while processing GLIBC_TUNABLES, allowing local attackers to use malicious environment variables with SUID binaries to execute code with elevated privileges. The parallel to CVE-2026-3888 is not identical, but it is conceptually close enough to matter: once an attacker can influence what a privileged executable resolves and loads, the distance to root gets very short. (NVD)
The Ubuntu OverlayFS pair, CVE-2023-2640 and CVE-2023-32629, are valuable comparisons for Ubuntu-specific defenders because they illustrate a different but equally important theme. In those cases, Canonical and NVD described local privilege escalation caused by authorization failures around privileged extended attributes in Ubuntu kernel behavior. The lesson there was that distro-specific configuration and patch behavior can create root paths even when the underlying upstream architecture looks familiar. CVE-2026-3888 fits that broader Ubuntu lesson. You cannot treat “Linux local root” as a generic category and assume your distro packaging choices do not materially alter the risk. (NVD)
CVE-2026-3888 is not the kind of issue where a team only needs a CVE feed. It is the kind of issue where the real question becomes, “If an attacker lands as a low-privilege user anywhere in this environment, what does that let them reach next?” That is a chain-of-compromise question, not just a vulnerability-database question. Penligent positions itself as an AI-powered penetration testing platform focused on evidence-backed workflows, reproducible PoCs, and verified findings rather than simple vulnerability labeling. That makes it a natural fit for the validation side of bugs like this, especially when teams want to understand how a user-level foothold, host role, and surrounding exposure combine into a higher-confidence risk story. (penligent.ai)
The important distinction is that Penligent is not a substitute for vendor patching. Canonical’s fix is still the answer to CVE-2026-3888. But in environments where security teams need to prioritize remediation, validate whether a low-privilege path actually leads to meaningful compromise, or turn messy host-level conditions into something another engineer can reproduce and act on, an evidence-oriented AI pentest platform is much more useful than a static CVE list. That is especially true for mixed estates where local privilege escalation is only one stage in a larger chain that also includes exposed services, weak role boundaries, stale tokens, or risky post-exploitation routes. (Ubuntu)
Final assessment
Ubuntu CVE-2026-3888 Bug deserves to be taken seriously, even though it is not a remote code execution bug and even though it is not instantly exploitable on a freshly compromised host. The exploit path is real, the vendor and primary-source disclosures are public, the impact is full root, and the affected software sits close to default Ubuntu experience on versions that matter right now. If your environment uses Ubuntu desktops, developer workstations, build systems, or shared research machines with snaps installed, this is not a story to file under “interesting but low urgency.” It is a story about how a patient low-privilege attacker can cross the last meaningful boundary on the host. (Ubuntu)
The right response is also clear. Patch snapd to the current vendor-fixed build for your Ubuntu release. Reboot. Validate the version and reboot state. Use the manual tmpfiles mitigation only if patching is temporarily blocked. And do not stop at package management if the host is high value and may already have had a user-level foothold. For those systems, a patch is necessary, but it may not be sufficient to restore trust. (Ubuntu)
What makes this bug memorable is not just that it reaches root. It is that it reaches root through ordinary system hygiene. A cleanup service does what it was told. A confinement helper does what it was built to do. Somewhere between them, time turns safe assumptions into attacker-controlled state. That is a good definition of modern Linux privilege escalation risk.
Further reading and references
- CVE-2026-3888 on Ubuntu Security
- USN-8102-1, snapd vulnerability
- Canonical community security post for CVE-2026-3888
- Qualys advisory on CVE-2026-3888
- Qualys detailed text advisory, snap-confine plus systemd-tmpfiles
- NVD entry for CVE-2026-3888
- Penligent main platform
- AI Pentest Tool, What Real Automated Offense Looks Like in 2026
- Pentest AI Tools in 2026, What Actually Works, What Breaks
- The 2026 Ultimate Guide to AI Penetration Testing
- Pentest GPT, What It Is, What It Gets Right, and Where AI Pentesting Still Breaks