Why this vulnerability keeps showing up in real incident queues
CVE-2023-43208 matters for one simple reason: it collapses an assumption that quietly underpins many healthcare and integration deployments—“the interface engine is internal, trusted, and boring.” In affected NextGen Healthcare Mirth Connect versions, an attacker can reach a dangerous parsing and deserialization path before authentication, enabling unauthenticated remote code execution in environments that treat the system like infrastructure rather than an exposed service. Multiple authoritative sources converge on the same high-level facts: it is a critical, pre-auth RCE, fixed in the 4.4.1 line, and it was later treated as an actively exploited vulnerability by government catalogs. (NVD)
On May 20, 2024, CISA added CVE-2023-43208 to the Known Exploited Vulnerabilities catalog, and NVD reflects the date added and the federal remediation due date—an unusually strong prioritization signal that the issue is not merely theoretical. (NVD)
If you operate Mirth Connect anywhere near a regulated environment—healthcare, labs, insurance integrations, or any system that processes HL7 or XML—this is not a vulnerability you “schedule.” This is one you close, and then you prove it stays closed.

The phrases engineers actually search, and what they really mean in practice
Across public writeups, alerts, and threat libraries, the highest-intent queries cluster around terms that map directly to operational work:
- Mirth Connect RCE und NextGen Mirth Connect RCE — “Is this remote code execution, and how bad is it?” (Horizon3.ai)
- unauthenticated RCE und pre-auth RCE — “Does an attacker need credentials or not?” (Horizon3.ai)
- insecure deserialization und XStream XML — “What’s the vulnerable class of bugs and how can I detect it without guessing payloads?” (Jägerin)
- patch bypass und incomplete patch — “Did we patch the earlier CVE and still remain exposed?” (Horizon3.ai)
- CISA KEV / Known Exploited Vulnerabilities — “Is this being exploited in the wild, and does leadership have to treat it as a deadline?” (NVD)
Those aren’t buzzwords. They are a checklist: identify versions, determine reachability, reduce exposure, add monitoring, verify the fix, and ensure the “patch bypass” story doesn’t repeat in your environment.
What CVE-2023-43208 is, and what is firmly established
Verified facts you can anchor on
1) Vulnerability class and severity
NVD describes CVE-2023-43208 as a deserialization of untrusted data issue in NextGen Healthcare Mirth Connect, scored critical, and tagged in relation to CISA KEV updates. (NVD)
2) Affected versions and fix line
Horizon3.ai’s disclosure summarizes that versions prior to 4.4.1 are vulnerable and urges upgrading to 4.4.1 as the patch release at the time of publication. Huntress’ threat library entry aligns with that fix boundary. (Horizon3.ai)
3) Real-world priority signal
NVD’s record includes the CISA KEV date added (2024-05-20) and a due date for action in federal contexts, and CISA’s alert confirms inclusion based on evidence of active exploitation. (NVD)
4) Patch bypass context
The UK NHS cyber alert explicitly states CVE-2023-43208 is a patch bypass of CVE-2023-37679. Horizon3.ai’s detailed writeup explains bypassing a denylist style patch by finding alternative gadget paths. (NHS England Digital)
Quick facts table for scoping and triage
| Artikel | What to know | Warum das wichtig ist |
|---|---|---|
| CVE | CVE-2023-43208 | The identifier that drives scanning, governance, and KEV workflows (NVD) |
| Auswirkungen | Unauthenticated RCE, pre-auth execution path | No creds required means perimeter mistakes become catastrophic (Jägerin) |
| Root class | Unsafe deserialization of attacker-controlled XML, XStream involvement | Payload-agnostic monitoring focuses on execution and parsing behavior (Jägerin) |
| Affected | Mirth Connect < 4.4.1 | Primary version boundary used in advisories (Horizon3.ai) |
| Priority signal | Added to CISA KEV May 20, 2024 | Strong indicator of in-the-wild exploitation and urgency (NVD) |
Why Mirth Connect amplifies the blast radius of “just another RCE”
Mirth Connect is not a random web app. It’s an integration engine often deployed as connective tissue between systems. Huntress describes it as widely used in healthcare for patient records and formats like HL7 and XML. (Jägerin)
That role amplifies risk in three predictable ways:
It often sits at a network crossroads
Even if it isn’t “domain admin,” it frequently has access to multiple data flows, credentials, and downstream systems. In healthcare, that can translate into lateral movement opportunities and data exposure far beyond the initial host.
It is frequently over-privileged in the real world
Horizon3.ai notes that in many Windows deployments, Mirth Connect is commonly run as SYSTEM, turning an RCE into full host compromise immediately. (Horizon3.ai)
It is too often exposed in “temporary” ways that become permanent
Vendor support needs, remote maintenance, rushed integrations, misconfigured reverse proxies—these are the small decisions that convert an internal interface engine into an internet-facing attack surface. Once that happens, a pre-auth RCE becomes opportunistic attacker territory.
This is why CVE-2023-43208 repeatedly shows up in security conversations: it doesn’t just exploit code, it exploits deployment habits.
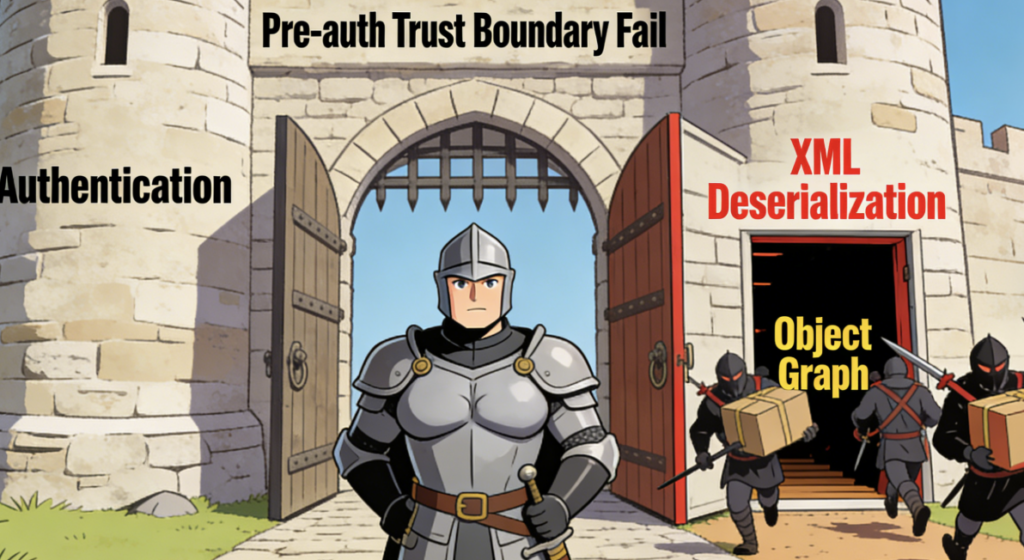
The patch-bypass story — why defenders don’t trust “we patched last time”
The NHS alert states plainly that CVE-2023-43208 bypasses a previous patch for CVE-2023-37679. (NHS England Digital)
Horizon3.ai’s writeup describes the mechanics at a defensive level: the patch introduced a denylist to block certain classes from being unmarshalled, and the bypass came from finding an alternative route that wasn’t covered by that denylist. (Horizon3.ai)
Huntress explains the underlying defensive lesson: denylisting dangerous classes is brittle in deserialization-heavy systems, and shifting to stricter allowlisting approaches is more resilient. (Jägerin)
You don’t need exploit details to understand the failure mode. If a patch is fundamentally “block a few obviously dangerous types,” it may reduce trivial exploitation while leaving the category of bug alive.
This is also why vulnerability management teams should treat patch-bypass narratives as a signal to strengthen verification: version checks alone are necessary, but not sufficient.
What actually happens technically — safe, defender-oriented explanation
Auf hohem Niveau:
- The system exposes endpoints that accept XML.
- XML is converted into Java objects using deserialization tooling. Huntress specifically references XStream and an XML payload being processed prior to password checks. (Jägerin)
- In affected versions, this path can be reached before authentication is effectively enforced, enabling pre-auth exploitation.
NVD classifies the issue under deserialization of untrusted data and documents the vulnerability in the Mirth Connect context. (NVD)
That’s the boundary failure: parsing untrusted structured input into executable object graphs before authentication. Once that boundary fails, the attacker does not need to defeat a login. They only need the service reachable.
A safe way to scope exposure — what to do in the next 30 minutes
Step 1 — Find Mirth Connect instances, internal and external
Start with your asset inventory, but assume it’s incomplete. If you have network scanning, search for the service ports you expect in your environment and then validate with application fingerprints.
If you have no inventory, treat this like an incident: find servers where Mirth Connect is installed, then verify which ones are reachable from where they shouldn’t be.
Step 2 — Confirm version using a non-exploit request
Horizon3.ai provides a simple version endpoint and a header that can be used for a safe check:
# Safe version check
# This does not include exploit payloads
curl -k -H 'X-Requested-With: OpenAPI' https://<host>:<port>/api/server/version
Horizon3.ai’s disclosure states that versions prior to 4.4.1 are vulnerable and urges upgrading to 4.4.1. (Horizon3.ai)
Step 3 — Classify reachability
Create an explicit reachability matrix:
- Can untrusted networks reach /api or management endpoints?
- Can user VLANs reach them?
- Can vendor VPN segments reach them?
- Can cloud ingress paths reach them?
The most common “surprise exposure” patterns come from reverse proxies, load balancers, and security groups that were configured for convenience.
Step 4 — Prioritize like KEV wants you to prioritize
KEV inclusion is a priority signal. CISA added it on May 20, 2024 based on evidence of exploitation. (CISA)
NVD records the KEV date added and required action guidance. (NVD)
In plain terms: treat internet-reachable < 4.4.1 as urgent.
Evidence of exploitation interest — why you should assume attackers have tooling
You don’t need to speculate about attacker capability. When a mature exploit module exists in a public framework, it’s a strong signal that exploitation has been productized and scanning is likely.
Rapid7’s database includes an entry for a Mirth Connect CVE-2023-43208 exploit module and references the earlier CVE-2023-37679 and patch incompleteness discovered by Horizon3.ai. (Schnell7)
Separately, Censys published analysis discussing active exploitation after CISA’s KEV inclusion, which often correlates with increased scanning and targeting. (Zensiert)
This doesn’t mean every scan succeeds. It means your environment is being measured against a known playbook.
Detection that holds up even if attackers change payloads
The best detections for this class of vulnerability don’t depend on signature matching the XML content. They depend on what happens when a Java service is abused: processes spawn, outbound connections occur, files get written, scheduled tasks appear.
Huntress highlights the practical detection approach: watch for suspicious processes spawned by the Java process, and look for unusual outbound connections. (Jägerin)
Host signals you should treat as high confidence
Java spawning a shell or interpreter
- Windows:
java.exespawningcmd.exeoderpowershell.exe - Linux:
javaspawning/bin/sh,bash,locken.,wget
Here are safe triage pivots, not final detections:
# Windows triage idea: java spawning cmd or powershell
# Requires process creation auditing or EDR visibility
Get-WinEvent -FilterHashtable @{LogName='Security'; Id=4688} |
Where-Object { $_.Message -match "Creator Process Name:\\s+.*java\\.exe" -and
$_.Message -match "New Process Name:\\s+.*(cmd\\.exe|powershell\\.exe)" } |
Select-Object -First 30
# Linux triage idea: suspicious child processes around Java
ps -eo pid,ppid,user,comm,args | egrep 'java|bash|sh|curl|wget|python|perl' | head -n 50
Network signals you should baseline and alert on
- New outbound connections from the Mirth host to unfamiliar destinations shortly after inbound API traffic
- DNS spikes or rare domains queried by the Mirth host
- Egress to IPs with no relationship to your integrations
Log signals that can help without becoming brittle
If you terminate TLS at a proxy, instrument request rate anomalies and unusual request sizes to sensitive paths. You do not need to log request bodies to gain value—metadata can be enough.
Remediation that actually closes the boundary — patching plus deployment hardening
Patch to the fix line and prove the running version
Horizon3.ai recommends upgrading to 4.4.1 and describes versions prior to 4.4.1 as vulnerable. (Horizon3.ai)
Huntress mirrors that remediation direction. (Jägerin)
Make verification explicit:
- confirm the package version on disk
- confirm the runtime-reported version via the safe API check
- confirm no old nodes remain in load balancer pools
Kill public exposure even if you patched
A patched system that remains internet reachable is still an attractive target. Patch bypass history is a reminder that defense-in-depth matters. Put management and API endpoints behind VPN and IP allowlists.
Example NGINX pattern:
# Example: restrict API access to private ranges and management networks
location /api/ {
allow 10.0.0.0/8;
allow 172.16.0.0/12;
allow 192.168.0.0/16;
deny all;
proxy_pass https://mirth_backend;
}
Remove SYSTEM or root where you can
Horizon3.ai notes SYSTEM is common for Windows deployments and increases impact. (Horizon3.ai)
Move to a dedicated least-privilege service account. If you can’t, compensate with stronger host controls and application whitelisting.
Segment the integration engine
Mirth Connect should not be a universal bridge. Segment it so it can only reach what it needs, and use egress policies to prevent arbitrary outbound traffic.
Treat deserialization as a category risk, not a one-off CVE
The patch-bypass narrative means you should keep monitoring even after patching. Huntress emphasizes why denylist defenses fail and why you should think in allowlist terms. (Jägerin)
CVE-2023-37679 — the related CVE that explains the “patched but still vulnerable” trap
CVE-2023-37679 is the earlier critical RCE in Mirth Connect that CVE-2023-43208 is described as bypassing in multiple alerts. (NHS England Digital)
NVD has a separate record for CVE-2023-37679 and it appears in multiple narratives about how patching evolved. (Schnell7)
Operationally, you should group them under one lesson:
- If your environment made the pre-auth parsing path reachable in the first place, the next deserialization issue will land in the same spot.
- Version upgrades are essential, but network placement, privilege boundaries, and detection are what prevent “the next CVE” from becoming an outage.
A practical verification framework — how to prove closure with evidence
If you want fewer surprise incidents, you need a repeatable proof loop. A useful model is to require evidence in three buckets:
Version evidence
- runtime version from the safe endpoint check
- configuration management state
- deployment pipeline guarantees
Exposure evidence
- firewall rules and security groups showing untrusted networks cannot reach /api
- reverse proxy rules and allowlists
- VPN enforcement for management access
Behavior evidence
- EDR queries or log rules that would trigger if Java spawns a shell
- outbound connection monitoring and alerting for the Mirth host
- baseline of expected integration destinations
Here’s a compact table that translates “we fixed it” into “we can prove it”:
| Proof category | What you capture | What it prevents |
|---|---|---|
| Version | Runtime version, package version, node inventory | Forgotten old instances, drift, partial upgrades (Horizon3.ai) |
| Exposure | Reachability tests, SGs, proxy allowlists | Accidental internet exposure, internal overexposure |
| Behavior | Process tree alerts, egress alerts, anomaly monitoring | Silent compromise, payload variations (Jägerin) |
If you manage many environments or multiple tenants, manual checks become unreliable. The most common failure pattern after a high-profile CVE is not ignorance—it’s drift: a forgotten DR node, a staging environment exposed for convenience, a newly provisioned VM that inherits old defaults.
In those cases, an AI-assisted penetration testing workflow can be used safely as a controlled verifier: enumerate targets you own, validate version and reachability, and generate evidence artifacts that support remediation and audit.
Penligent’s platform focuses on AI-driven penetration testing and verification workflows, and this particular CVE has a prior writeup published in Penligent’s own research section, which can be used as an internal reference in your remediation documentation. (Sträflich)
Authoritative internal links and references
NVD, CVE-2023-43208 detail and KEV metadata https://nvd.nist.gov/vuln/detail/CVE-2023-43208
CISA alert, KEV additions May 20, 2024 https://www.cisa.gov/news-events/alerts/2024/05/20/cisa-adds-two-known-exploited-vulnerabilities-catalog
Horizon3.ai disclosure, NextGen Mirth Connect unauthenticated RCE and fix line 4.4.1 https://horizon3.ai/attack-research/disclosures/nextgen-mirth-connect-remote-code-execution/
Horizon3.ai deep writeup, patch bypass narrative and defensive context https://horizon3.ai/attack-research/disclosures/writeup-for-cve-2023-43208-nextgen-mirth-connect-pre-auth-rce/
Huntress threat library, CVE-2023-43208 defender notes and detection ideas https://www.huntress.com/threat-library/vulnerabilities/cve-2023-43208
NHS cyber alert, explicitly states patch bypass relationship with CVE-2023-37679 https://digital.nhs.uk/cyber-alerts/2023/cc-4400
Rapid7 module entry, illustrates exploitation has been productized in public tooling https://www.rapid7.com/db/modules/exploit/multi/http/mirth_connect_cve_2023_43208/
Censys analysis, discussion of active exploitation interest around KEV inclusion https://censys.com/blog/cve-2023-43208
NextGenHealthcare Connect GitHub discussion, community discussion around mitigation approach https://github.com/nextgenhealthcare/connect/discussions/5974
Penligent prior article, CVE-2023-43208 patch bypass analysis https://www.penligent.ai/hackinglabs/cve-2023-43208-and-the-patch-bypass-that-turned-mirth-connect-into-a-high-priority-internet-facing-rce/
Penligent main site https://penligent.ai/